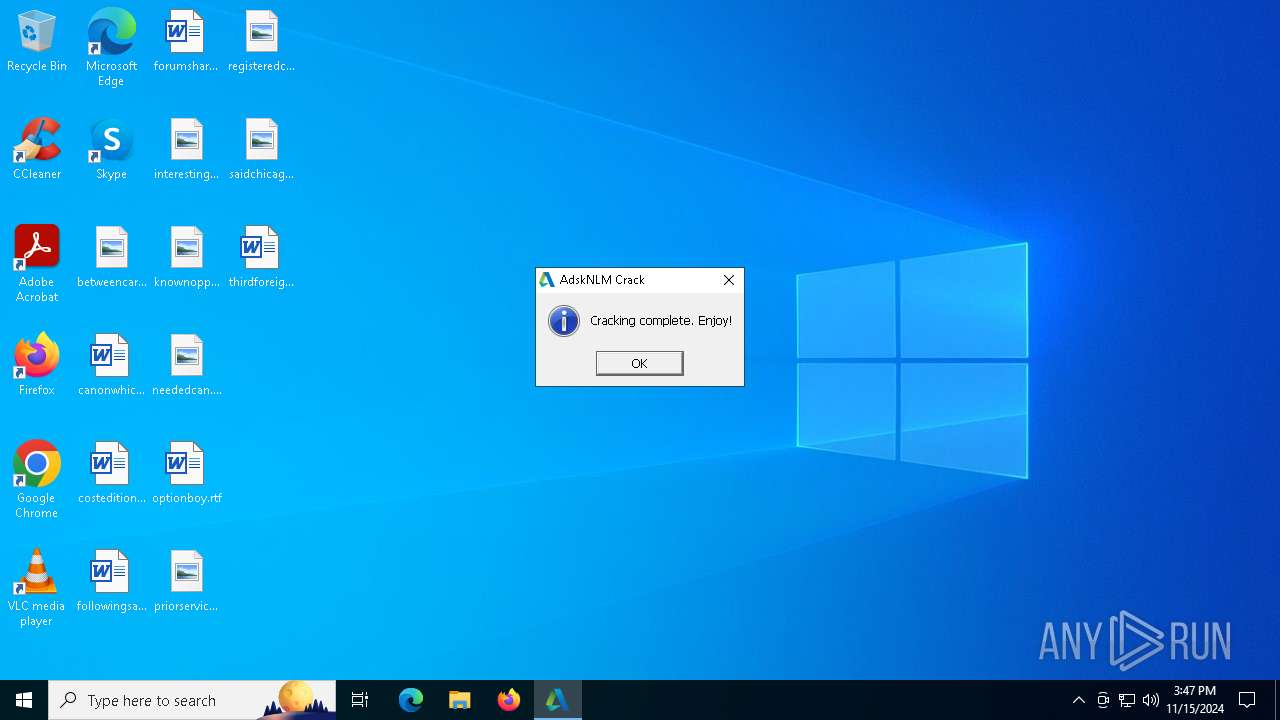
| File name: | AdskNLM.exe |
| Full analysis: | https://app.any.run/tasks/145884d5-555f-4c0f-a022-55be95595c02 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2024, 15:46:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 2AD373B0BB3B07764D79EB89CE66C0CC |
| SHA1: | 6B14B7CFAD1C2238EAFB7FD3435476B634B09F69 |
| SHA256: | 80C4927FD58F442598589E1A29D47C6F5251A55FD78E865C06B2FD78765C9AE4 |
| SSDEEP: | 98304:a4/JRKNzyUjS9zZB7T4R7IepI3shp5Cam5Im8yoqHNQTw380P7sFrMQQIqz9r0MC:ApYbBxoY9fOWJv0IsKe/Oq1 |
MALICIOUS
Executing a file with an untrusted certificate
- adskflex.exe (PID: 7372)
SUSPICIOUS
Reads security settings of Internet Explorer
- AdskNLM.exe (PID: 6152)
- AdskNLM.exe (PID: 6132)
- AdskNLM.exe (PID: 6368)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 3604)
- AdskNLM.exe (PID: 1792)
- AdskNLM.exe (PID: 5616)
- AdskNLM.exe (PID: 6956)
- AdskNLM.exe (PID: 6292)
Application launched itself
- AdskNLM.exe (PID: 1156)
- AdskNLM.exe (PID: 6152)
- cmd.exe (PID: 700)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 6276)
- lmgrd.exe (PID: 6644)
Reads the date of Windows installation
- AdskNLM.exe (PID: 6132)
- AdskNLM.exe (PID: 6368)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 3604)
- AdskNLM.exe (PID: 1792)
- AdskNLM.exe (PID: 5616)
- AdskNLM.exe (PID: 6956)
- AdskNLM.exe (PID: 6152)
Starts SC.EXE for service management
- AdskNLM.exe (PID: 6132)
- AdskNLM.exe (PID: 6392)
- AdskNLM.exe (PID: 6044)
- AdskNLM.exe (PID: 4072)
- AdskNLM.exe (PID: 5400)
- AdskNLM.exe (PID: 6276)
- AdskNLM.exe (PID: 300)
Uses TASKKILL.EXE to kill process
- AdskNLM.exe (PID: 6368)
- AdskNLM.exe (PID: 1712)
- AdskNLM.exe (PID: 6900)
- AdskNLM.exe (PID: 528)
- AdskNLM.exe (PID: 5240)
- AdskNLM.exe (PID: 6232)
Starts CMD.EXE for commands execution
- AdskNLM.exe (PID: 6752)
- cmd.exe (PID: 700)
- AdskNLM.exe (PID: 3604)
- AdskNLM.exe (PID: 1792)
- AdskNLM.exe (PID: 5616)
- AdskNLM.exe (PID: 5080)
- AdskNLM.exe (PID: 5512)
- AdskNLM.exe (PID: 1344)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 1712)
- AdskNLM.exe (PID: 4568)
- AdskNLM.exe (PID: 6728)
- AdskNLM.exe (PID: 7632)
- AdskNLM.exe (PID: 7864)
- AdskNLM.exe (PID: 7744)
- AdskNLM.exe (PID: 7920)
- AdskNLM.exe (PID: 6692)
- AdskNLM.exe (PID: 7100)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 5588)
- AdskNLM.exe (PID: 7148)
- cmd.exe (PID: 6276)
- AdskNLM.exe (PID: 4548)
- AdskNLM.exe (PID: 7820)
- AdskNLM.exe (PID: 2140)
- AdskNLM.exe (PID: 6556)
- AdskNLM.exe (PID: 6292)
- AdskNLM.exe (PID: 6956)
Process copies executable file
- cmd.exe (PID: 700)
- cmd.exe (PID: 7972)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2588)
- AdskNLM.exe (PID: 1156)
Uses REG/REGEDIT.EXE to modify registry
- AdskNLM.exe (PID: 1156)
- AdskNLM.exe (PID: 4548)
- AdskNLM.exe (PID: 1568)
- AdskNLM.exe (PID: 7720)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 7572)
- AdskNLM.exe (PID: 5580)
- AdskNLM.exe (PID: 4680)
- AdskNLM.exe (PID: 7268)
- AdskNLM.exe (PID: 8052)
- AdskNLM.exe (PID: 5660)
- AdskNLM.exe (PID: 7536)
- AdskNLM.exe (PID: 3700)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6608)
- cmd.exe (PID: 1248)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 7904)
Executes as Windows Service
- lmgrd.exe (PID: 6644)
INFO
Reads the computer name
- AdskNLM.exe (PID: 6152)
- AdskNLM.exe (PID: 1156)
- AdskNLM.exe (PID: 6132)
- AdskNLM.exe (PID: 6368)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 3604)
- AdskNLM.exe (PID: 1792)
- AdskNLM.exe (PID: 5616)
- AdskNLM.exe (PID: 6956)
- AdskNLM.exe (PID: 6292)
Checks supported languages
- AdskNLM.exe (PID: 6152)
- AdskNLM.exe (PID: 6368)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 3604)
- AdskNLM.exe (PID: 1792)
- AdskNLM.exe (PID: 5616)
- AdskNLM.exe (PID: 6956)
- AdskNLM.exe (PID: 6292)
- AdskNLM.exe (PID: 1156)
- AdskNLM.exe (PID: 6132)
The process uses the downloaded file
- AdskNLM.exe (PID: 6152)
Process checks computer location settings
- AdskNLM.exe (PID: 6368)
- AdskNLM.exe (PID: 6132)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 3604)
- AdskNLM.exe (PID: 1792)
- AdskNLM.exe (PID: 5616)
- AdskNLM.exe (PID: 6956)
- AdskNLM.exe (PID: 6152)
Changes file name
- cmd.exe (PID: 7792)
- cmd.exe (PID: 6644)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3972)
Application launched itself
- msiexec.exe (PID: 3972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2018:05:21 01:49:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 130560 |
| InitializedDataSize: | 308736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20360 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.0.0 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | MAGNiTUDE & m0nkrus |
| FileDescription: | Autodesk 2020-2024 Cracked NLM Installer |
| FileVersion: | 9.0.0.0 |
| InternalName: | AdskNLM |
| LegalCopyright: | Copyright © 2022-2024 MAGNiTUDE & m0nkrus |
| OriginalFileName: | AdskNLM.exe |
| PrivateBuild: | November 15, 2024 |
| ProductName: | Autodesk Cracked NLM |
| ProductVersion: | 9.0.0.0 |
Total processes
312
Monitored processes
177
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "sc" start AdskNLM | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 528 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "taskkill" /f /im AdskIdentityManager.exe | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 700 | "C:\Windows\System32\cmd.exe" /c echo D | xcopy /hkry "C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version.dll" "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\Current\AdskLicensingAgent" | C:\Windows\System32\cmd.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 700 | "C:\Windows\System32\cmd.exe" /c if exist "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\11.1.1.17\AdskLicensingAgent\AdskLicensingAgent.exe" ( echo F | xcopy /hkry "C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version_old.dll" "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\11.1.1.17\AdskLicensingAgent\version.dll" ) | C:\Windows\System32\cmd.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 860 | "C:\Windows\System32\cmd.exe" /c if exist "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\12.0.0.6529\AdskLicensingAgent\AdskLicensingAgent.exe" ( echo F | xcopy /hkry "C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version_old.dll" "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\12.0.0.6529\AdskLicensingAgent\version.dll" ) | C:\Windows\System32\cmd.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 860 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | "C:\Windows\System32\reg.exe" add "HKLM\SOFTWARE\WOW6432Node\FLEXlm License Manager\AdskNLM" /v "License" /d "C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\licenses.lic" /f | C:\Windows\System32\reg.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxelevation | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | AdskNLM.exe | ||||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Version: 9.0.0.0 Modules
| |||||||||||||||
| 1248 | "C:\Windows\System32\cmd.exe" /c if exist "C:\WINDOWS\System32\wbem\WMIC.exe" ( wmic product where name="Autodesk Network License Manager" call uninstall /nointeractive ) else ( powershell.exe -ExecutionPolicy ByPass -command ". 'C:\Users\admin\AppData\Local\Temp\Adsk-NLM\delnowmic.ps1'" ) | C:\Windows\System32\cmd.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 870
Read events
31 756
Write events
103
Delete events
11
Modification events
| (PID) Process: | (6164) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Autodesk Access |
Value: | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 840F0000C640399F7537DB01 | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 9F76A50BB5797AC5B5D7C81D4360CBB4F3EEB2FA7AB6078401472ABAB68195E5 | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\97788.rbs |
Value: 31143797 | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\97788.rbsLow |
Value: | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\81BF366C285907D49B7353E3A4430E23 |
| Operation: | write | Name: | 58619EB42361CF745B368A5A246C66C4 |
Value: C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmtools.exe | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\8173ED65A0469D84F83C28CABA6DBA17 |
| Operation: | write | Name: | 58619EB42361CF745B368A5A246C66C4 |
Value: C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmgrd.exe | |||
| (PID) Process: | (3972) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\B186121C4388C52458A34775468C77D0 |
| Operation: | write | Name: | 58619EB42361CF745B368A5A246C66C4 |
Value: C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmutil.exe | |||
Executable files
14
Suspicious files
16
Text files
7
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm11-19-4-1-ipv4-ipv6-win64.msi | — | |
MD5:— | SHA256:— | |||
| 3972 | msiexec.exe | C:\Windows\Installer\97785.msi | — | |
MD5:— | SHA256:— | |||
| 1156 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\licenses.lic | text | |
MD5:D9D6B5F04B221D487558FD8CA2C721BD | SHA256:028C07BFD58B6007044964846BEDAC29CBB4104690E4C48131612FE9F0FF1D8D | |||
| 1156 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm.mst | binary | |
MD5:29810BAB1EF69A3D26872093EF09372B | SHA256:90E413CD675EE085C441DF6327F6661A3459F4E109E0684B1A361C050D672BDB | |||
| 1156 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version_old.dll | executable | |
MD5:51F0E19B4CF164ECBA9A006C4CF3B2A5 | SHA256:6F13E52D797A732435C8BB456BE08C64D0B6FADEA29F85486F4B44559D6CC95F | |||
| 1156 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\UnNamed.json | binary | |
MD5:BA3088F87EDFCCEB1E084C971DB40601 | SHA256:E0371582686D18B48EDB9E956057B52AA97DE8C034EE79AAB10FFB5331711651 | |||
| 1156 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version.dll | executable | |
MD5:44774FAFD716FA45C7A0CCB3B14D59A6 | SHA256:4739ABFF4DA13A27F2421452007C9D2340BF4F9E9A601EF0EC9F1B9D64D1D365 | |||
| 3972 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:F63CA9FC735147772452E76BFD0B7B8D | SHA256:A2AEFAA5B962B2A78ED9BA2A3DE018B491AAC859CF638024D1E7441A8A05926A | |||
| 3972 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_713A6544EFB2EFA6D8AB75FCC7811104 | der | |
MD5:40A5BC658BC04AEACA72BD1B886611B0 | SHA256:DB30B722DDAC25F63E949BB9D1F94D475C0690197F1381233C98DD2CFA2FC43D | |||
| 1156 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\adskflex.exe | executable | |
MD5:E974687B0135A662623056078A8E58E1 | SHA256:82BE4EC8BA546EBF1E3448976D06E163E9C4E258301CFCEB9CE8A2D76ECBD6AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
50
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6088 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7312 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7036 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.16.204.152:443 | — | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 23.218.209.163:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6492 | WmiPrvSE.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |