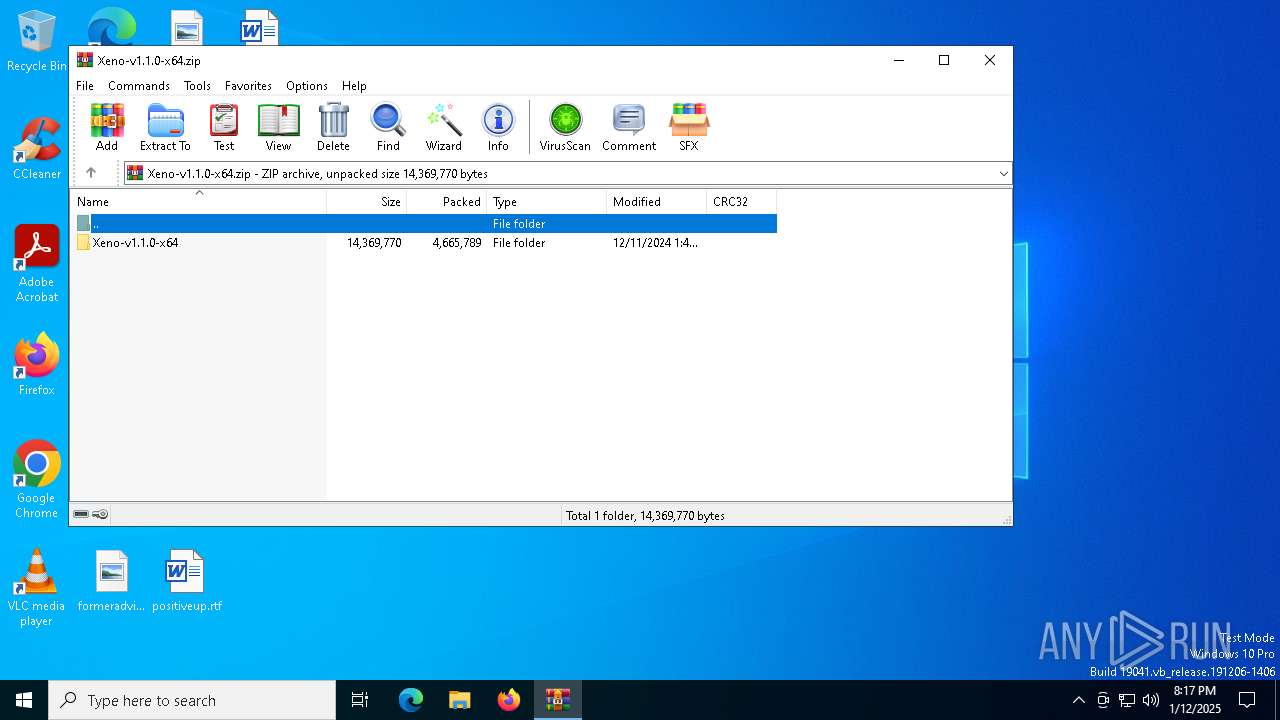
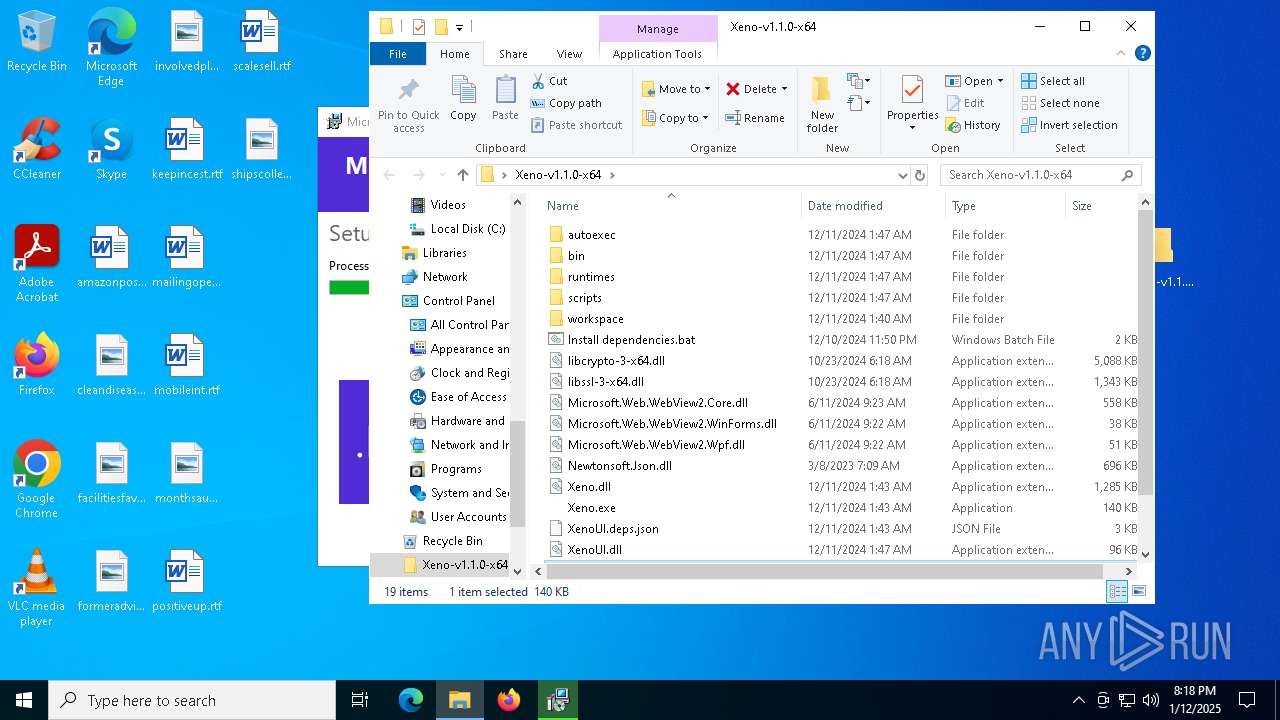
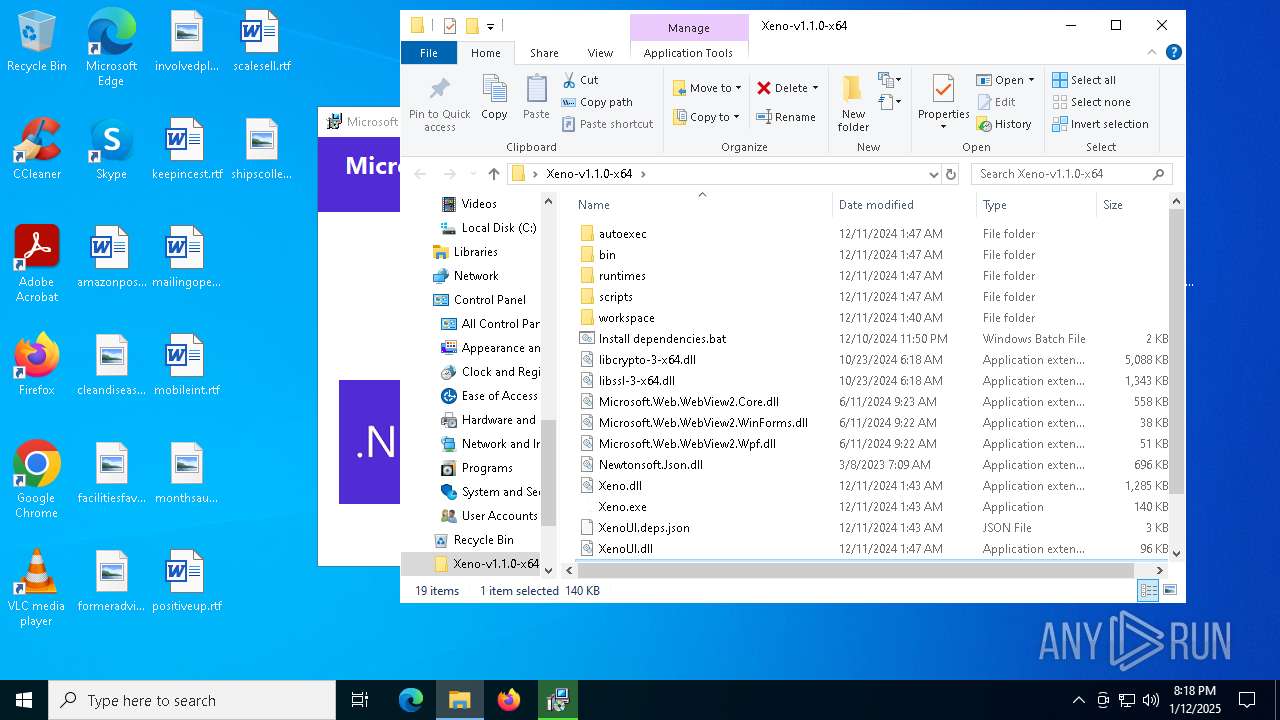
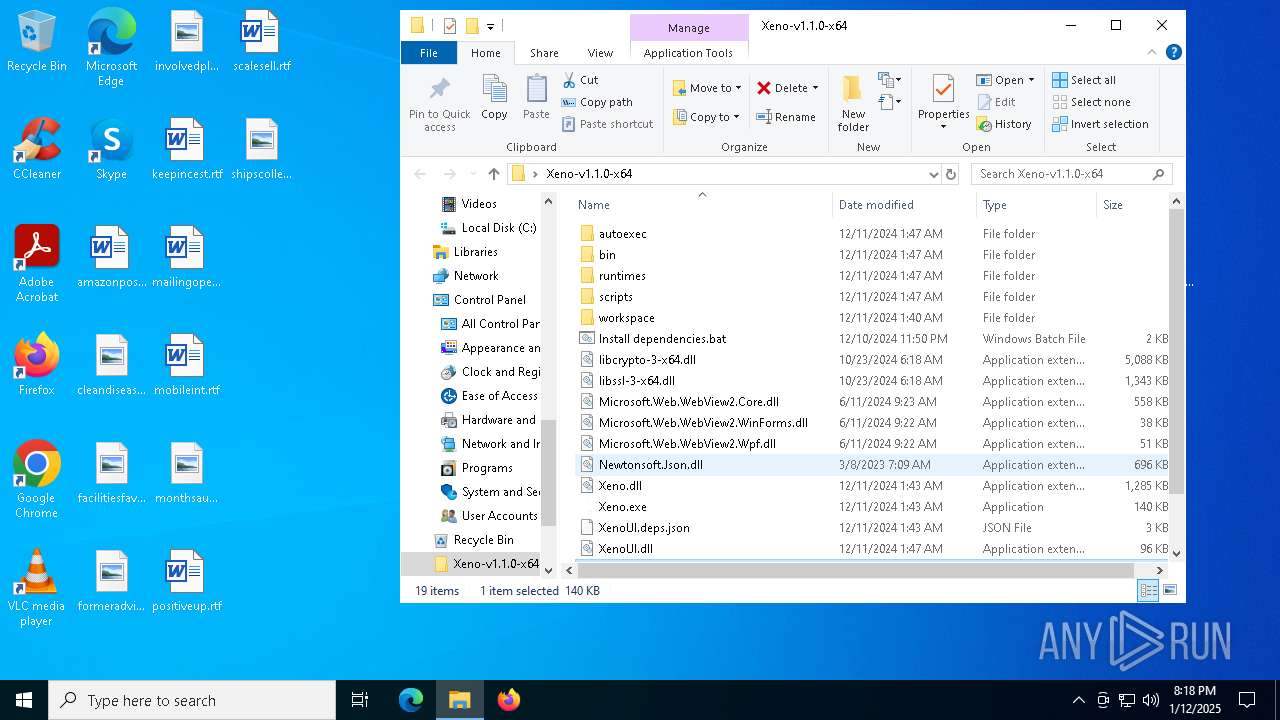
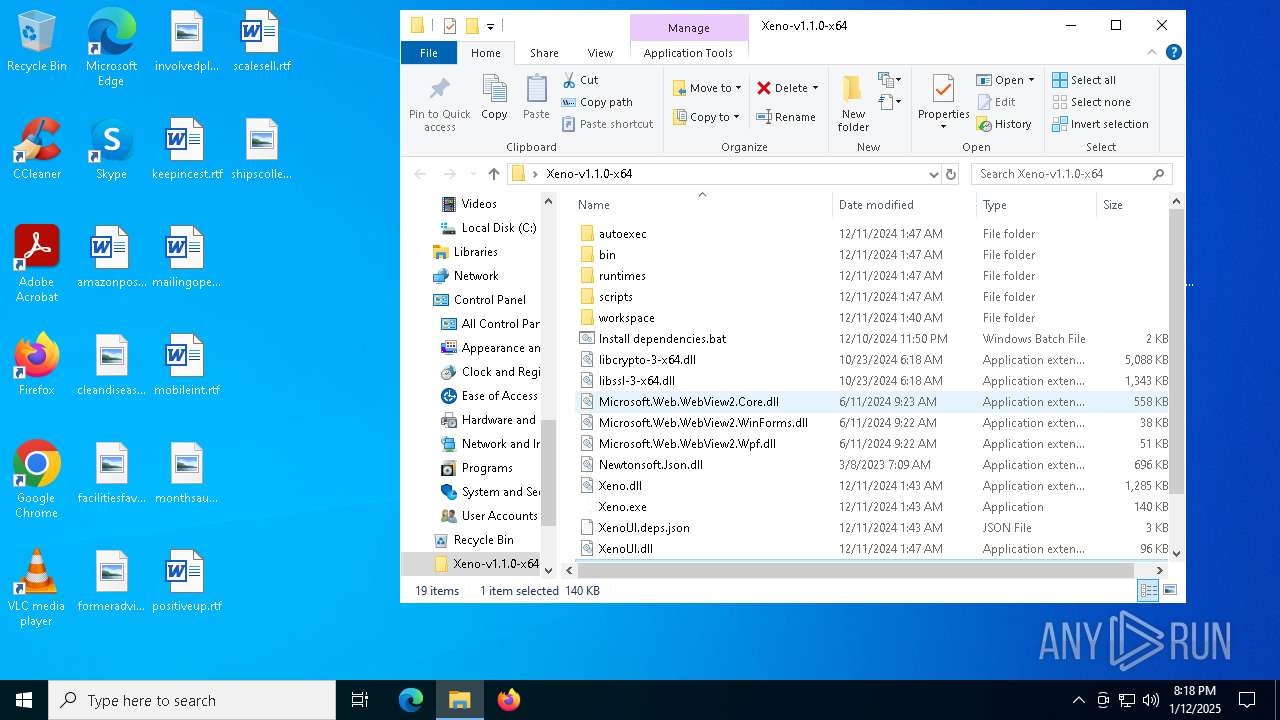
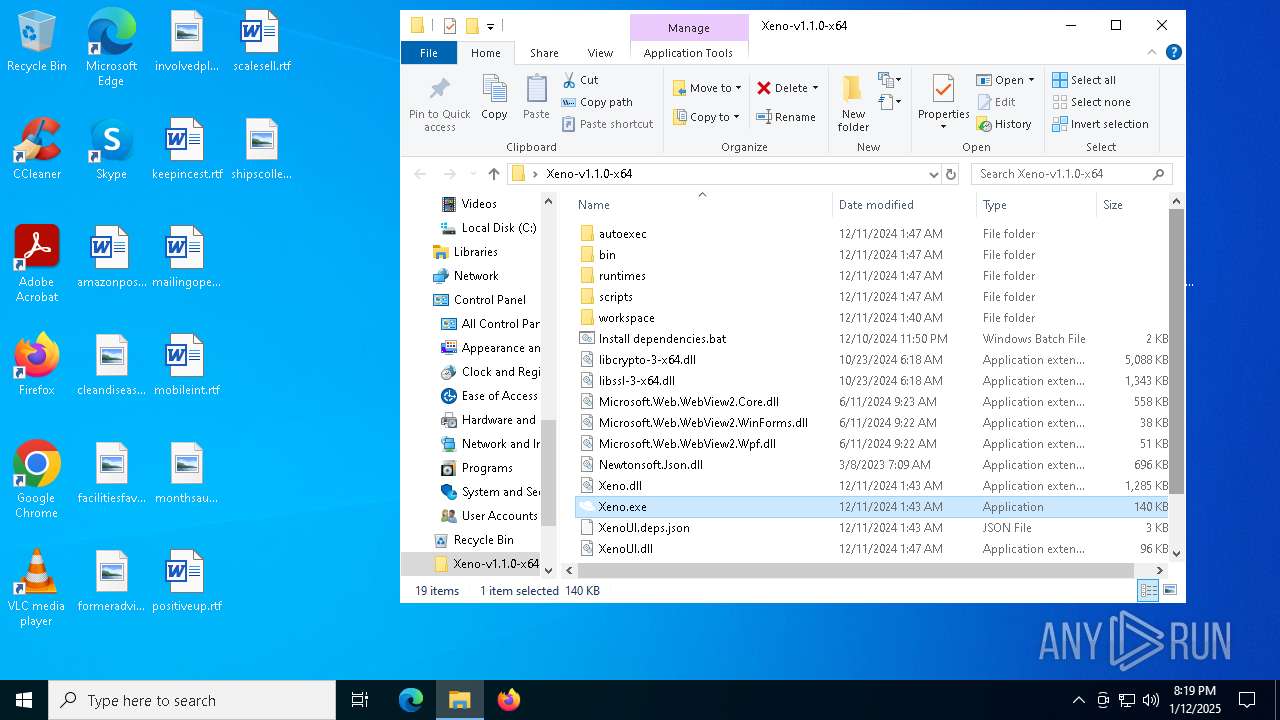
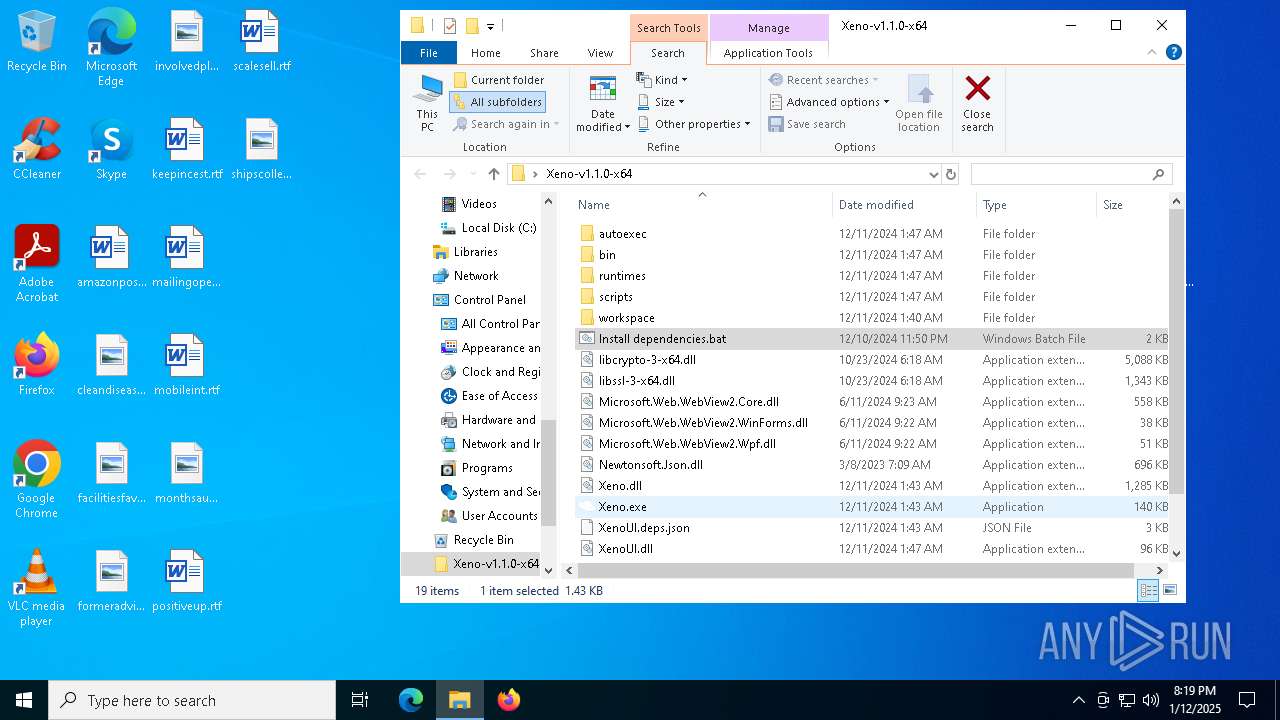
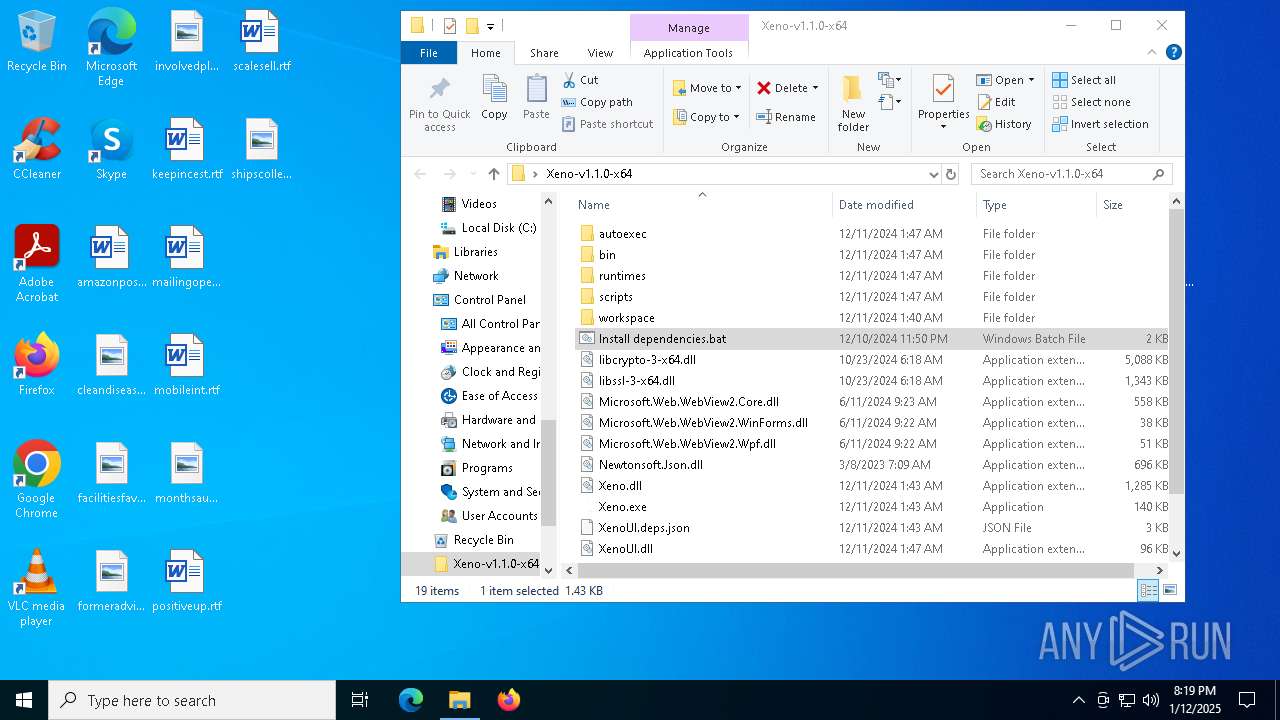
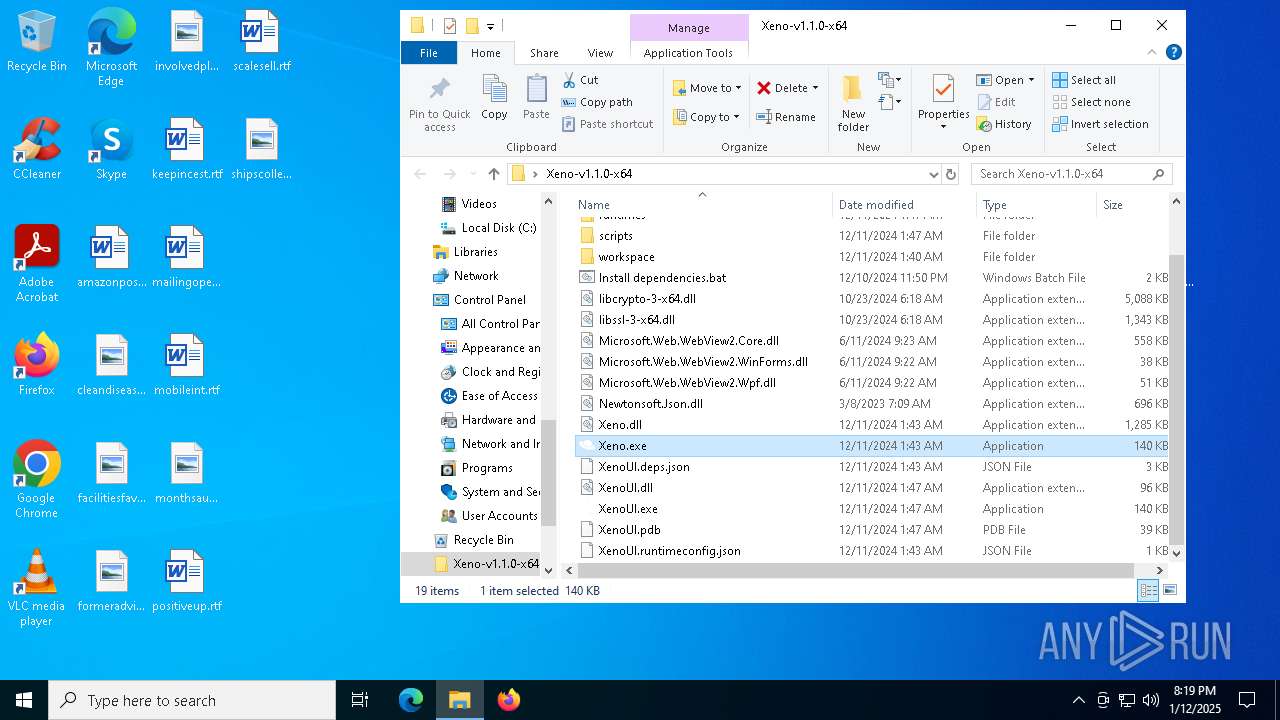
| File name: | Xeno-v1.1.0-x64.zip |
| Full analysis: | https://app.any.run/tasks/1fb2c2e0-8dcd-4777-9290-d0c3cc29dcbd |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2025, 20:17:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 93357DB14AF91A53BCAB556E80103C1C |
| SHA1: | 7643F56E7CEACE571C7000B937275F747AF659AF |
| SHA256: | 80C4016577C11791F64E2D43E1DFAD2B01ADF7276100400A4421B48DF6E6FBFE |
| SSDEEP: | 98304:ww8iS+7FqOFJMKp/+7Bh2aLziOwG6gHfKs+poLHboP8Rs4DkiyuwZcoYgngcf4kP:JJHkstrp0q |
MALICIOUS
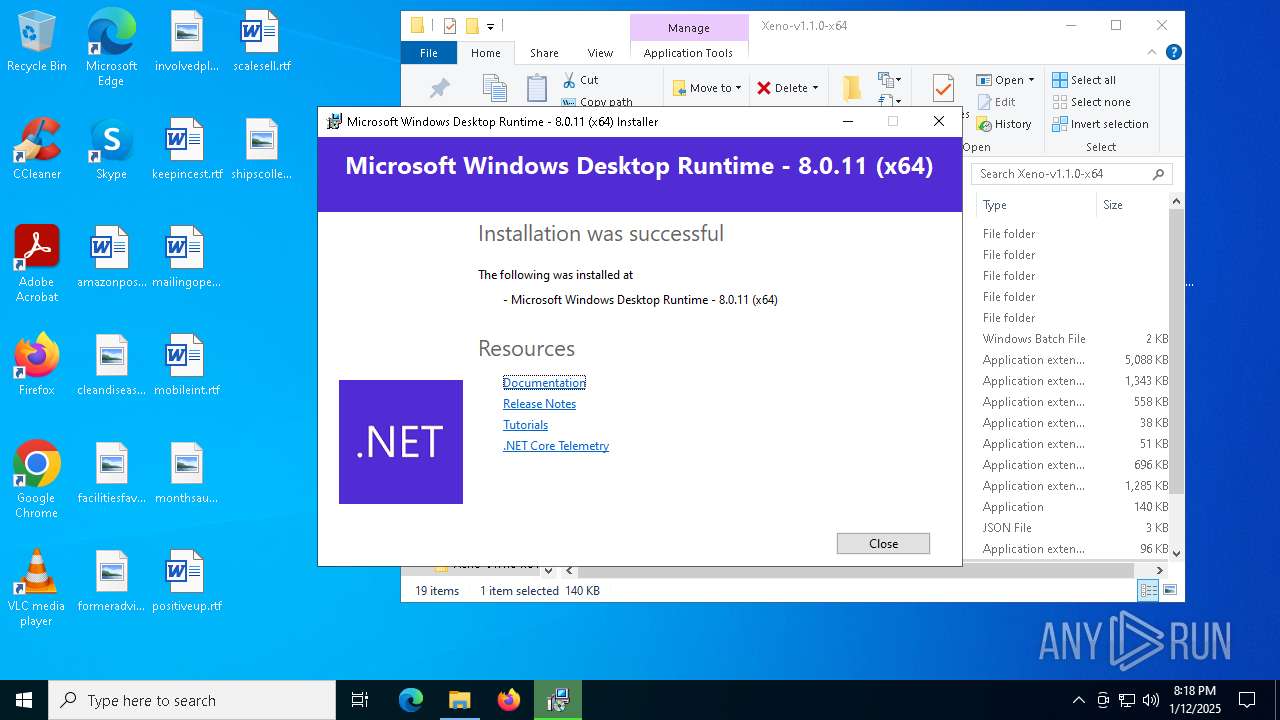
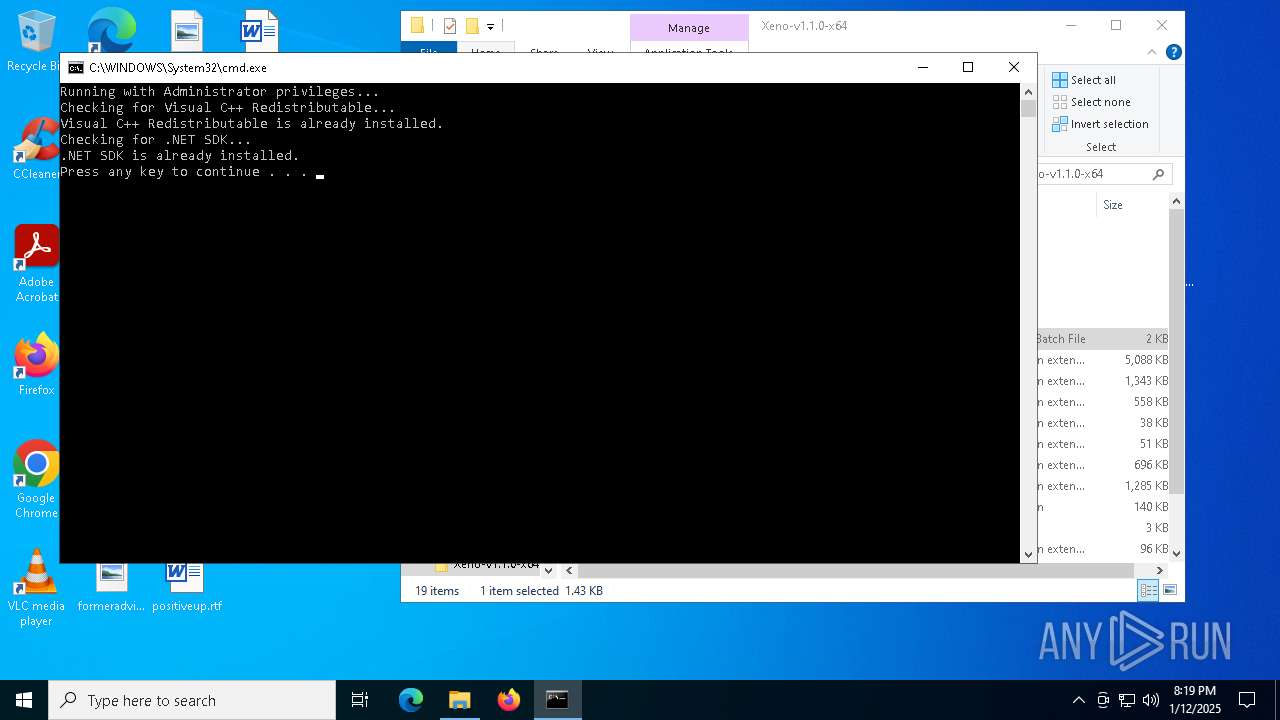
Changes the autorun value in the registry
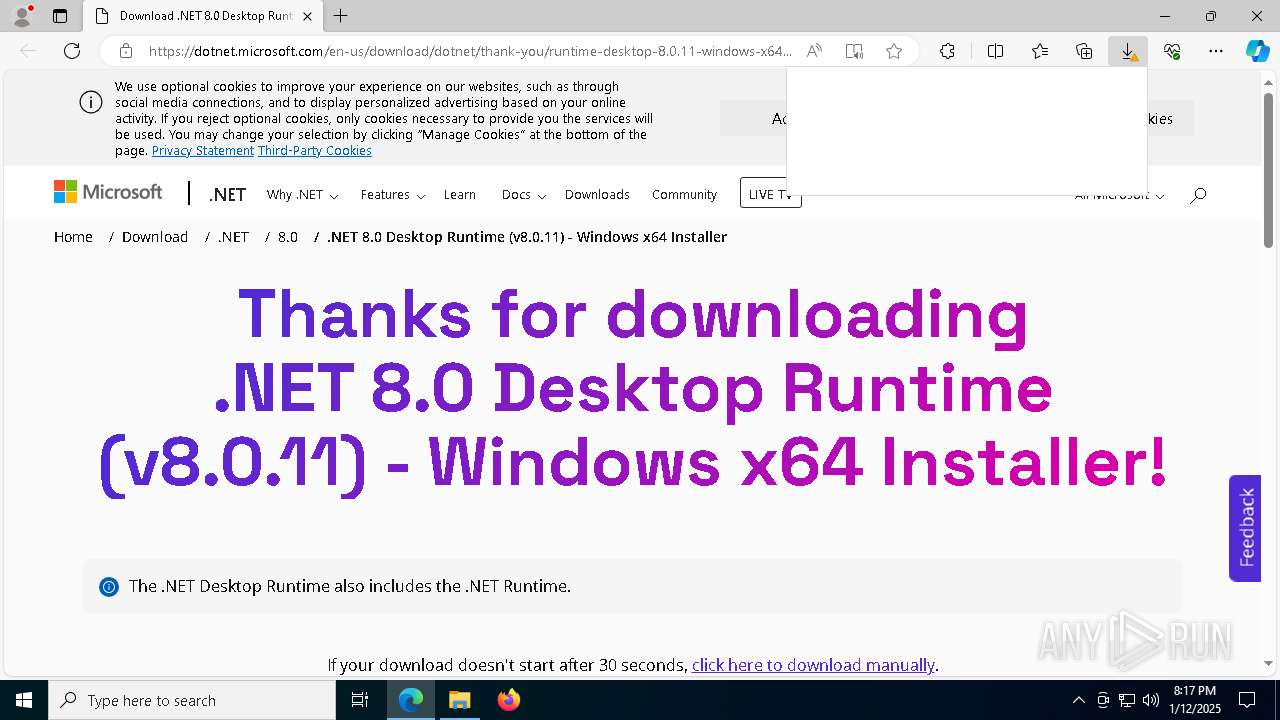
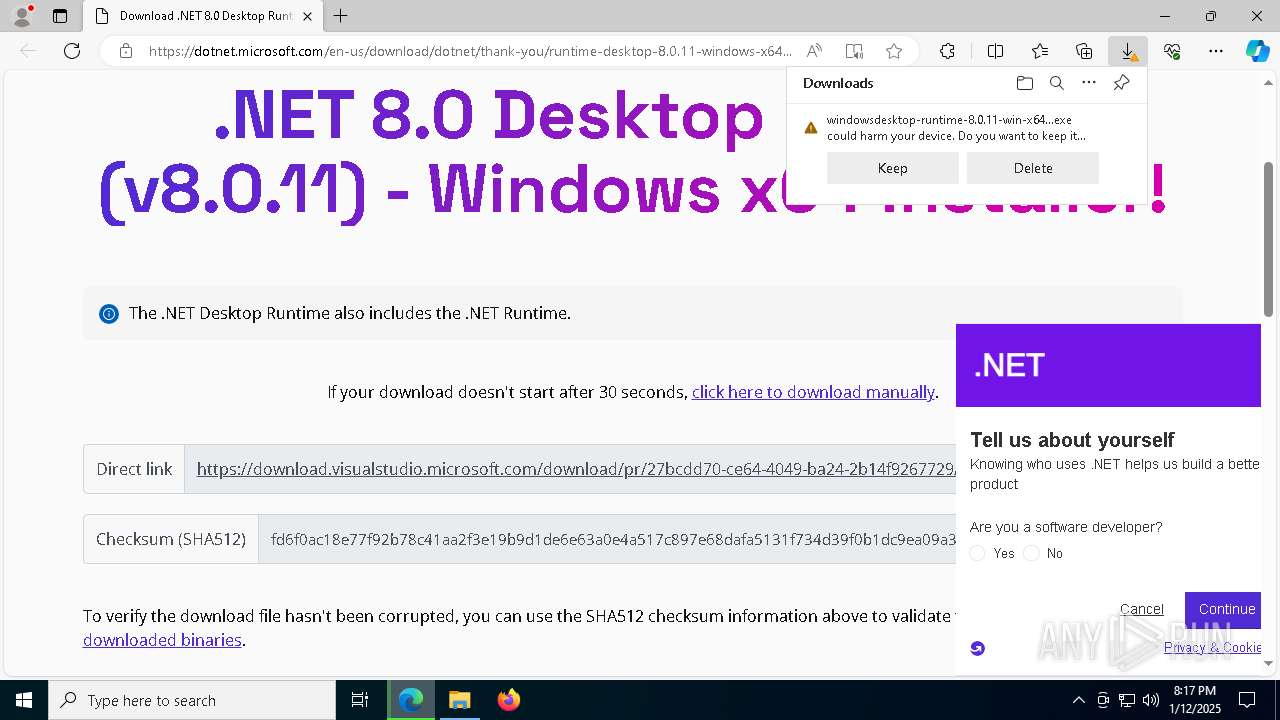
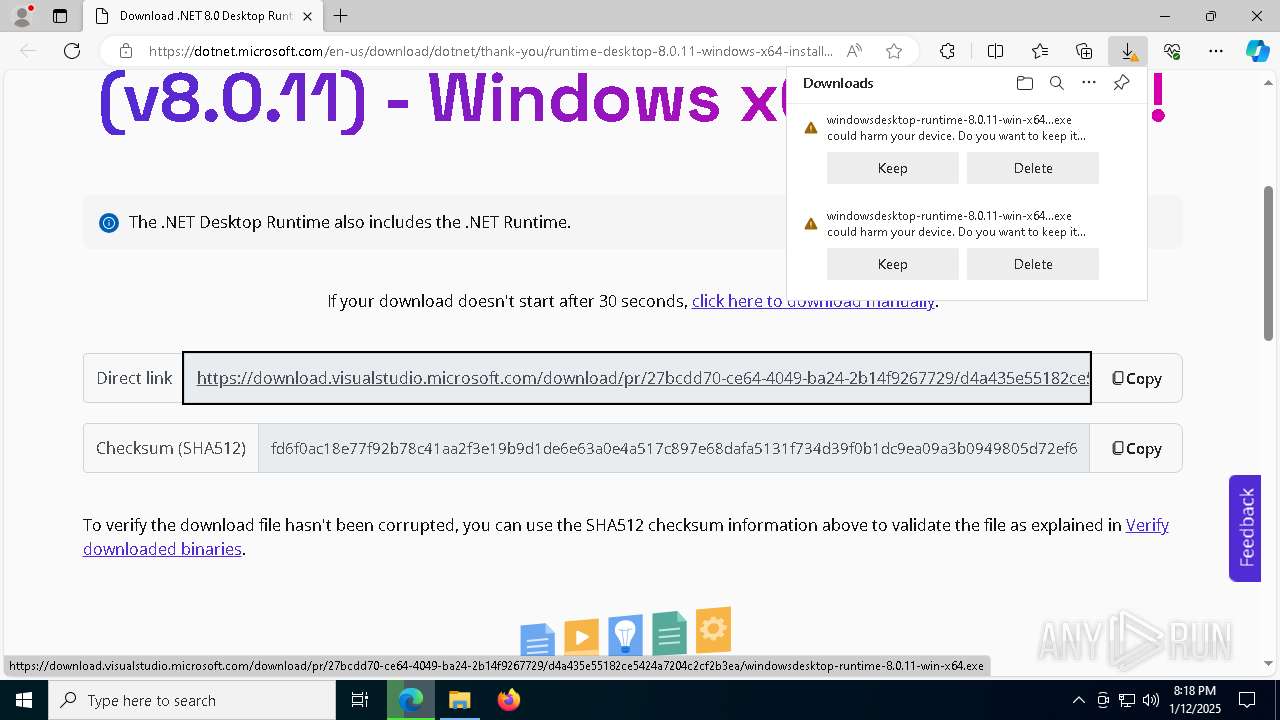
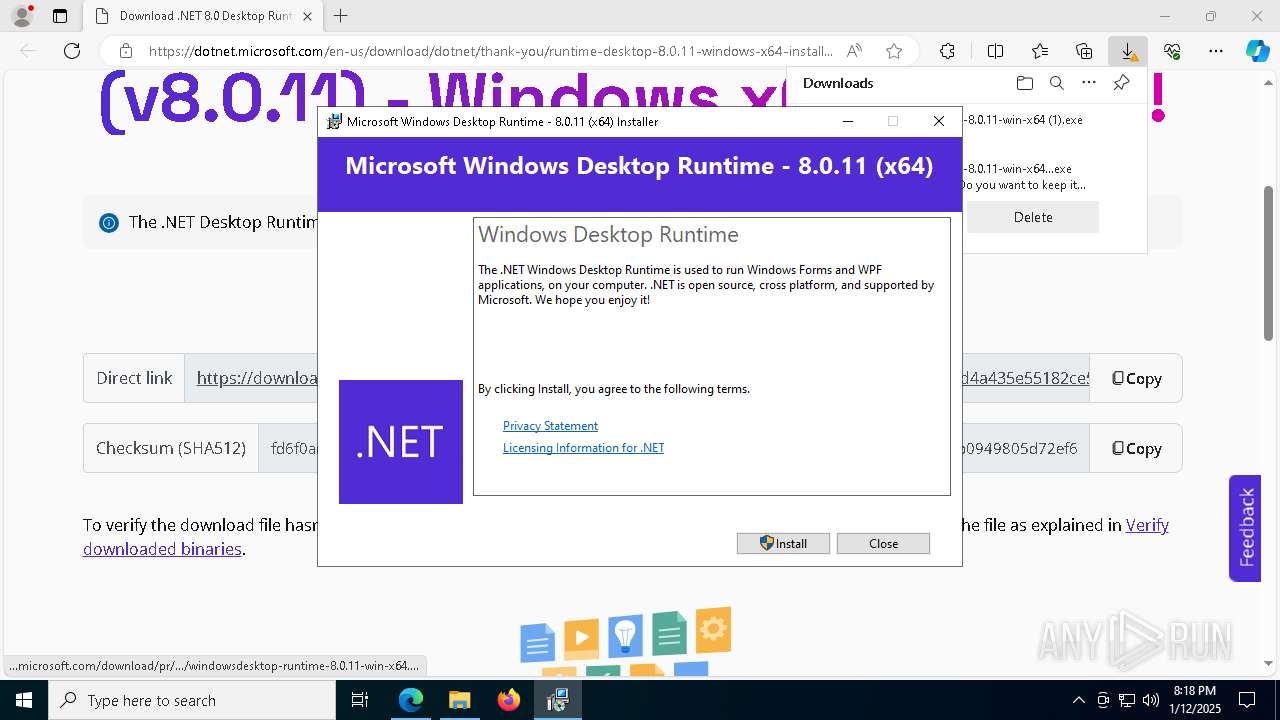
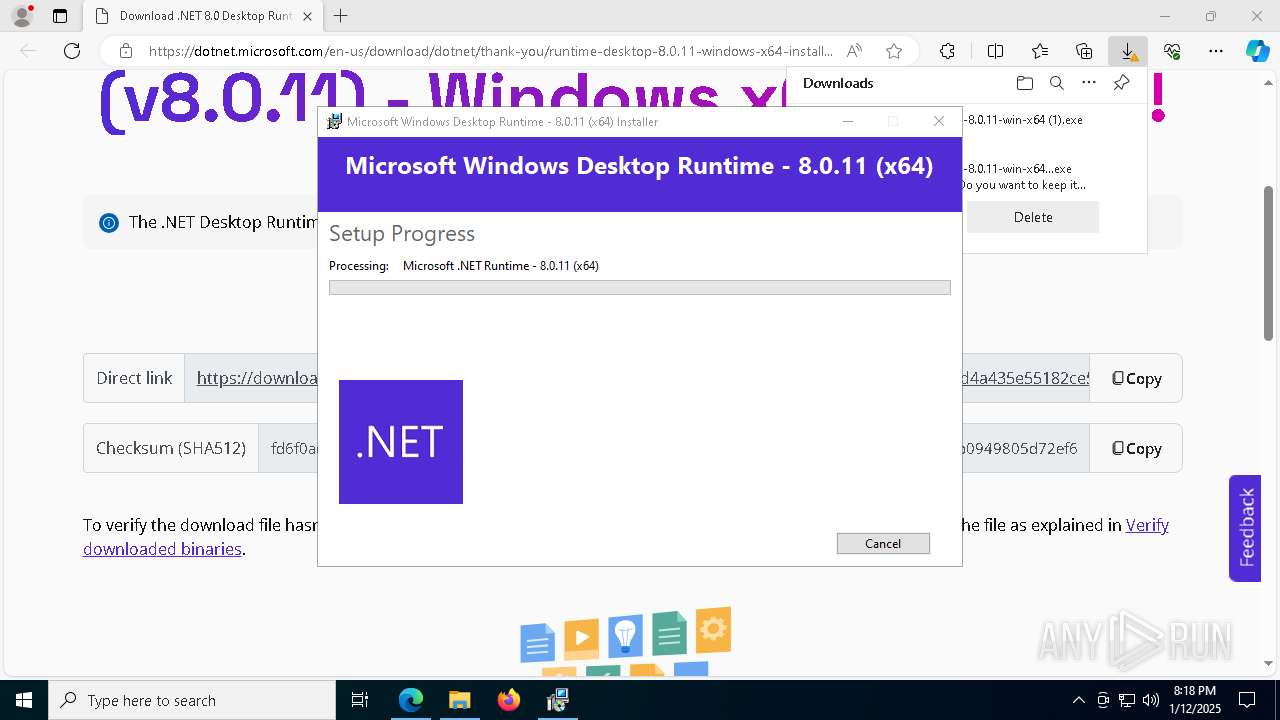
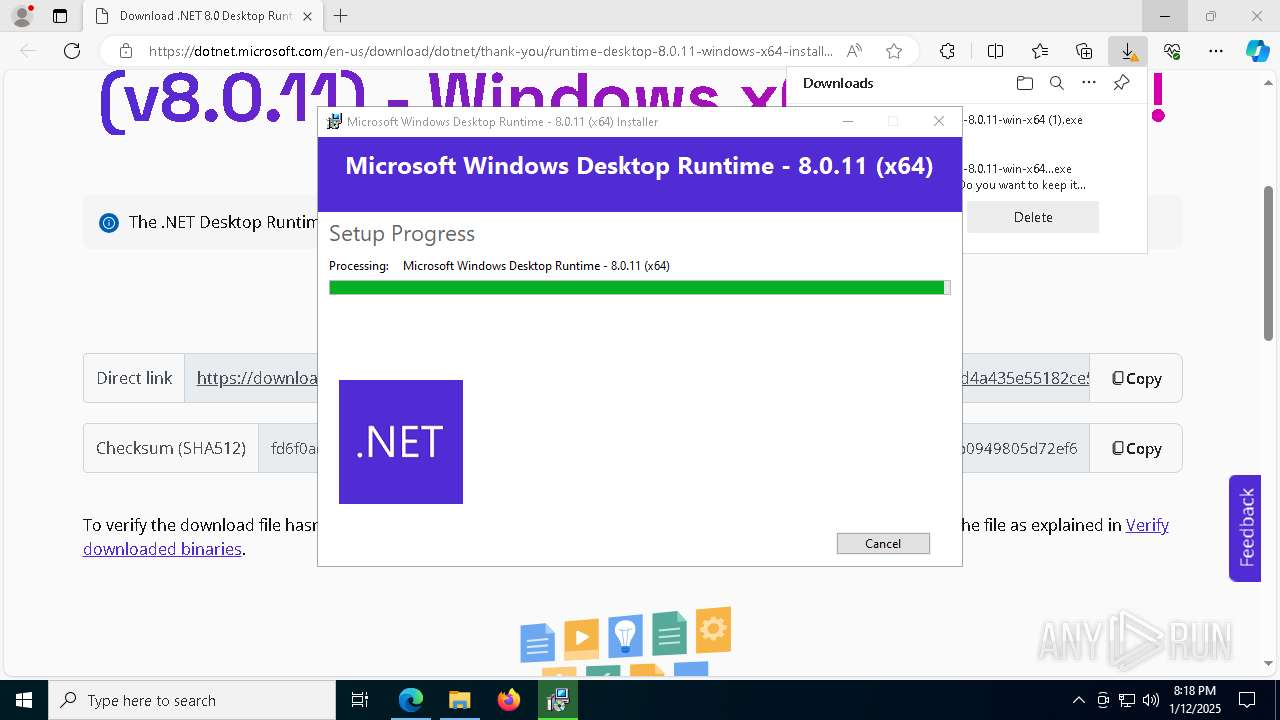
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
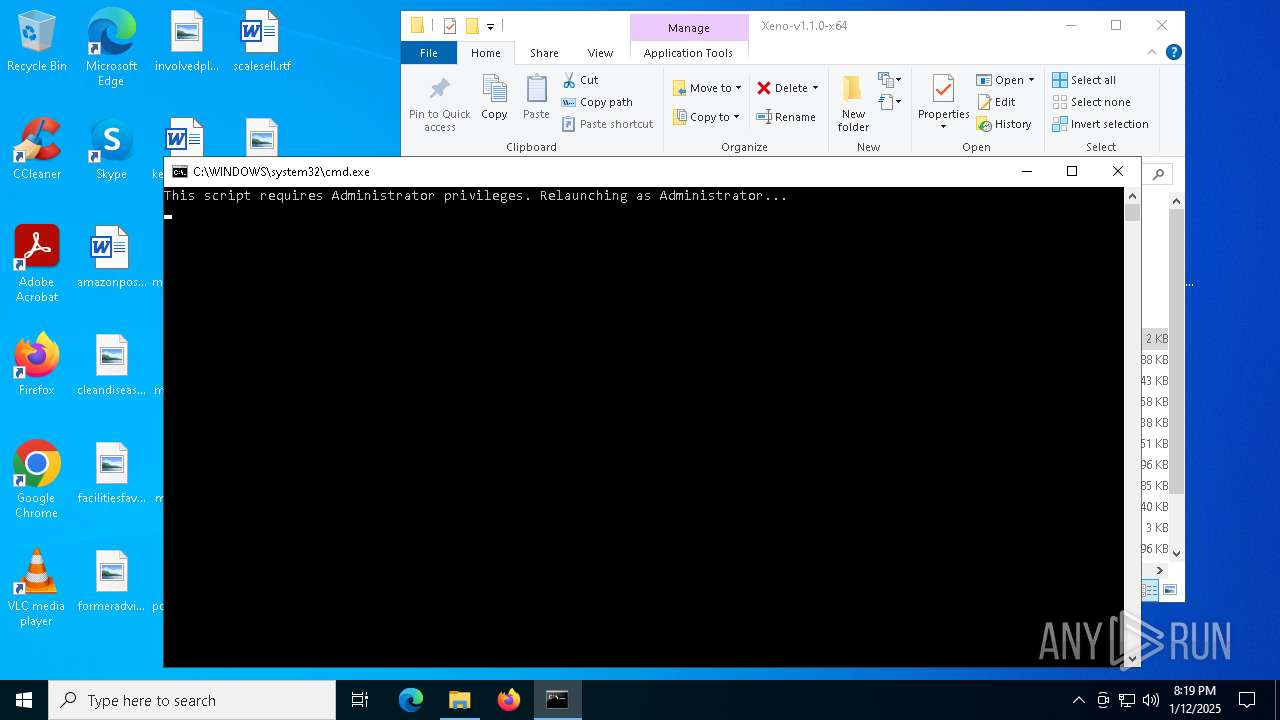
Bypass execution policy to execute commands
- powershell.exe (PID: 6084)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3984)
SUSPICIOUS
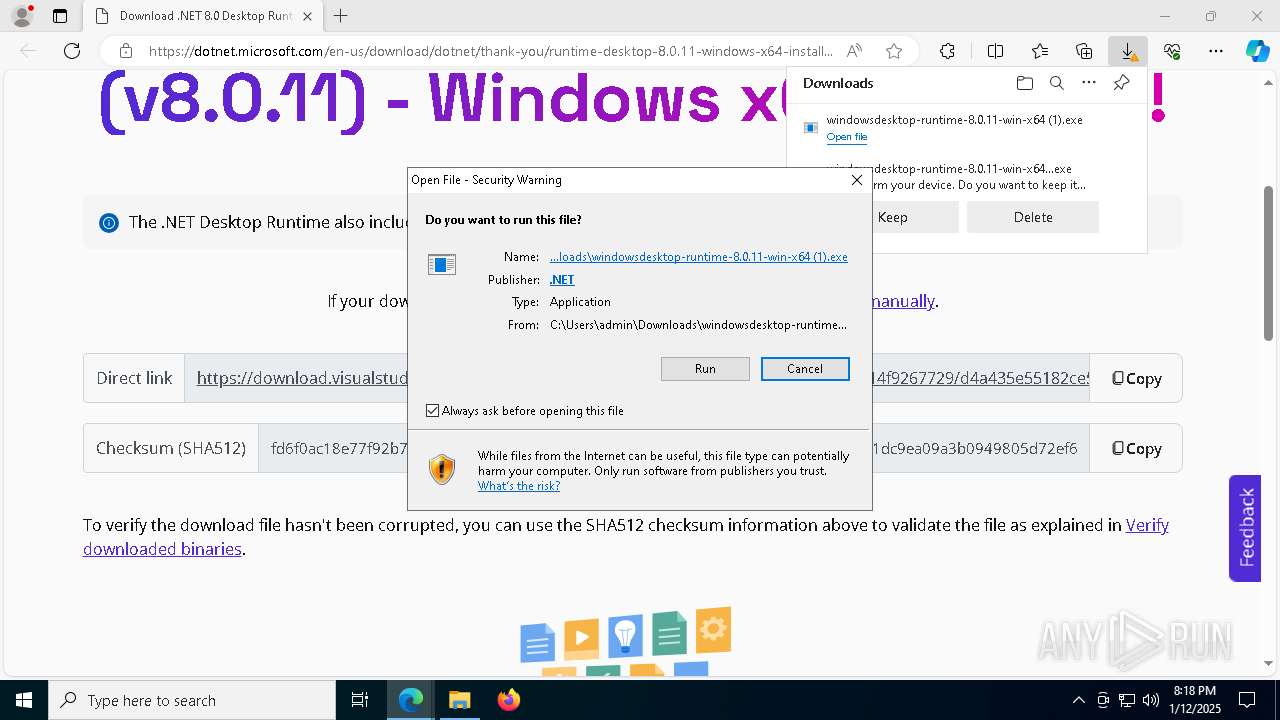
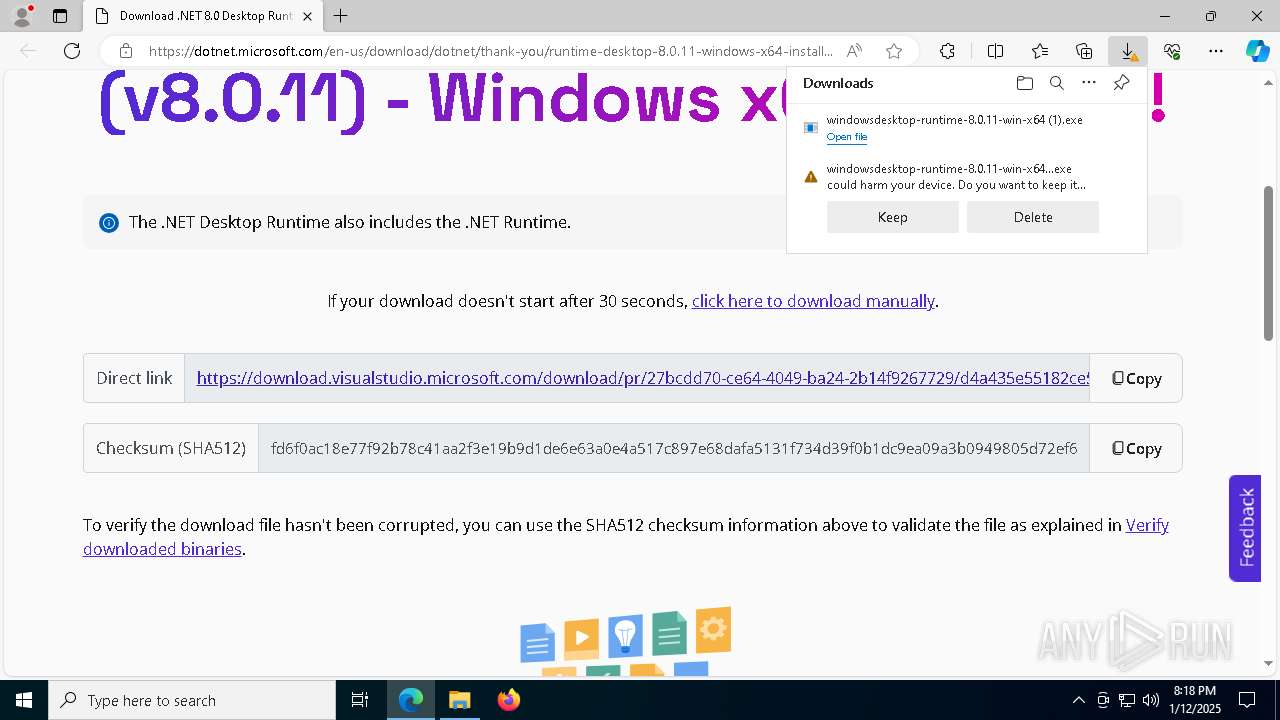
Process drops legitimate windows executable
- WinRAR.exe (PID: 6432)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 3724)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
- msiexec.exe (PID: 7580)
Reads security settings of Internet Explorer
- XenoUI.exe (PID: 3832)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- Xeno.exe (PID: 2280)
- Xeno.exe (PID: 6984)
- Xeno.exe (PID: 6676)
- XenoUI.exe (PID: 2972)
Executable content was dropped or overwritten
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 3724)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
Searches for installed software
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
Starts itself from another location
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7580)
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7580)
Checks Windows Trust Settings
- msiexec.exe (PID: 7580)
The process drops C-runtime libraries
- msiexec.exe (PID: 7580)
Executes application which crashes
- Xeno.exe (PID: 2280)
- Xeno.exe (PID: 6968)
- Xeno.exe (PID: 6984)
- Xeno.exe (PID: 7688)
- Xeno.exe (PID: 5576)
- Xeno.exe (PID: 6676)
- Xeno.exe (PID: 7828)
- Xeno.exe (PID: 7788)
- XenoUI.exe (PID: 2972)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 1540)
- net.exe (PID: 3888)
- net.exe (PID: 6748)
- cmd.exe (PID: 3984)
- cmd.exe (PID: 6972)
- net.exe (PID: 556)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6084)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3984)
Starts process via Powershell
- powershell.exe (PID: 6084)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3984)
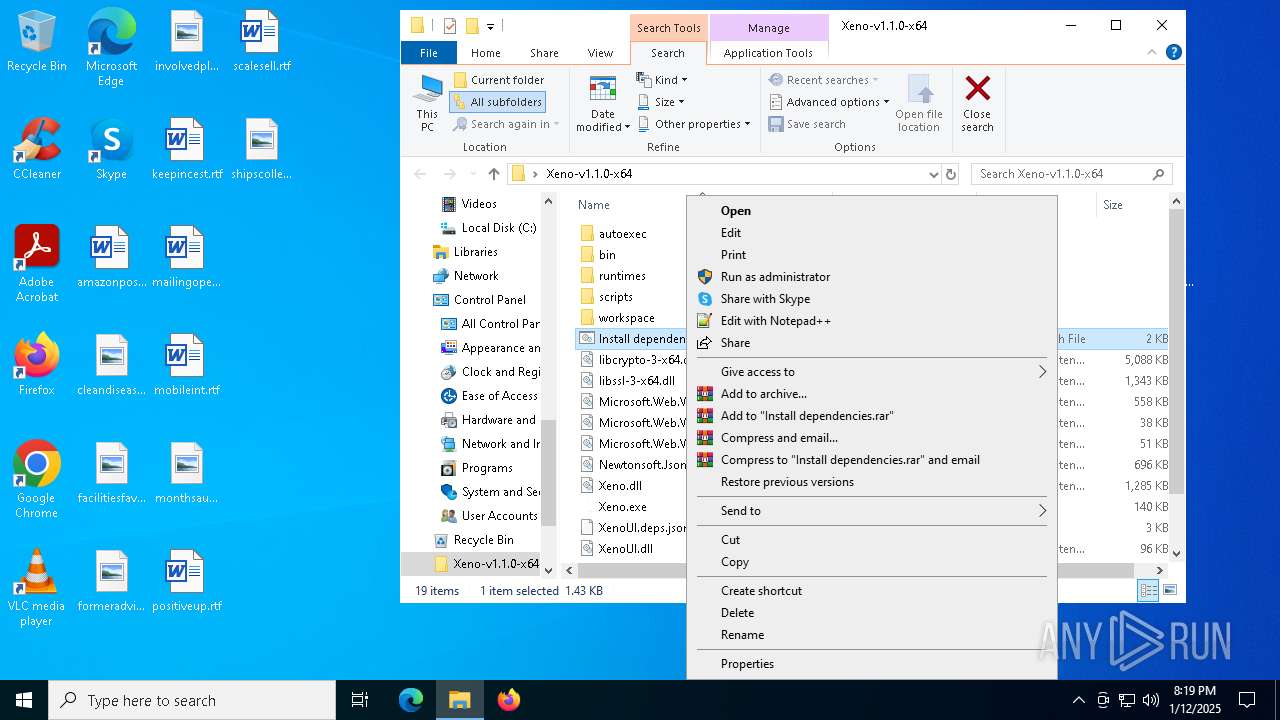
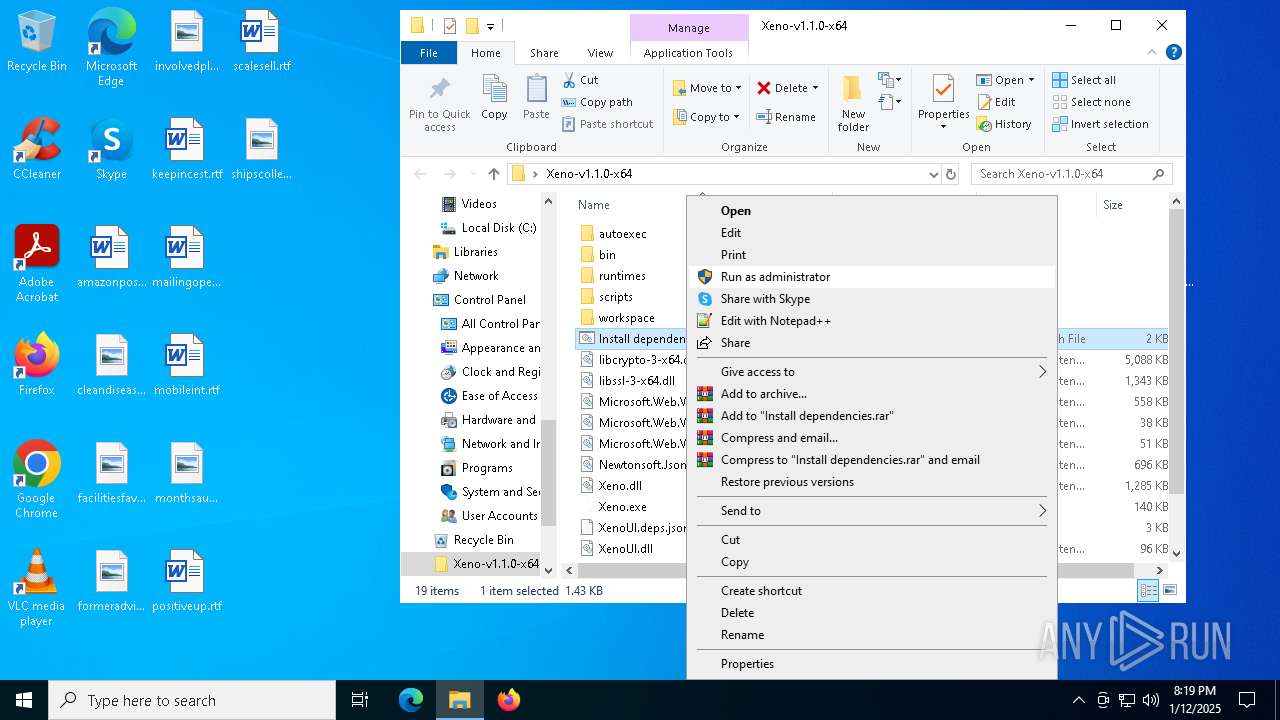
Executing commands from a ".bat" file
- powershell.exe (PID: 6084)
INFO
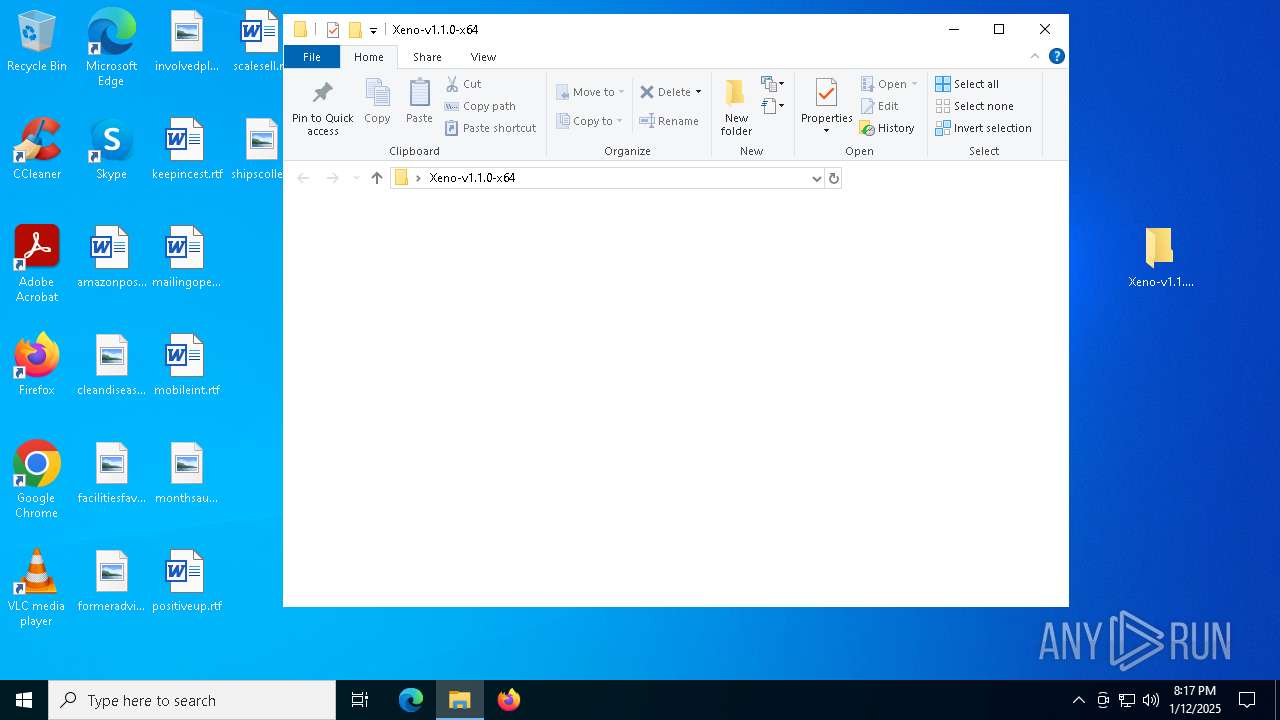
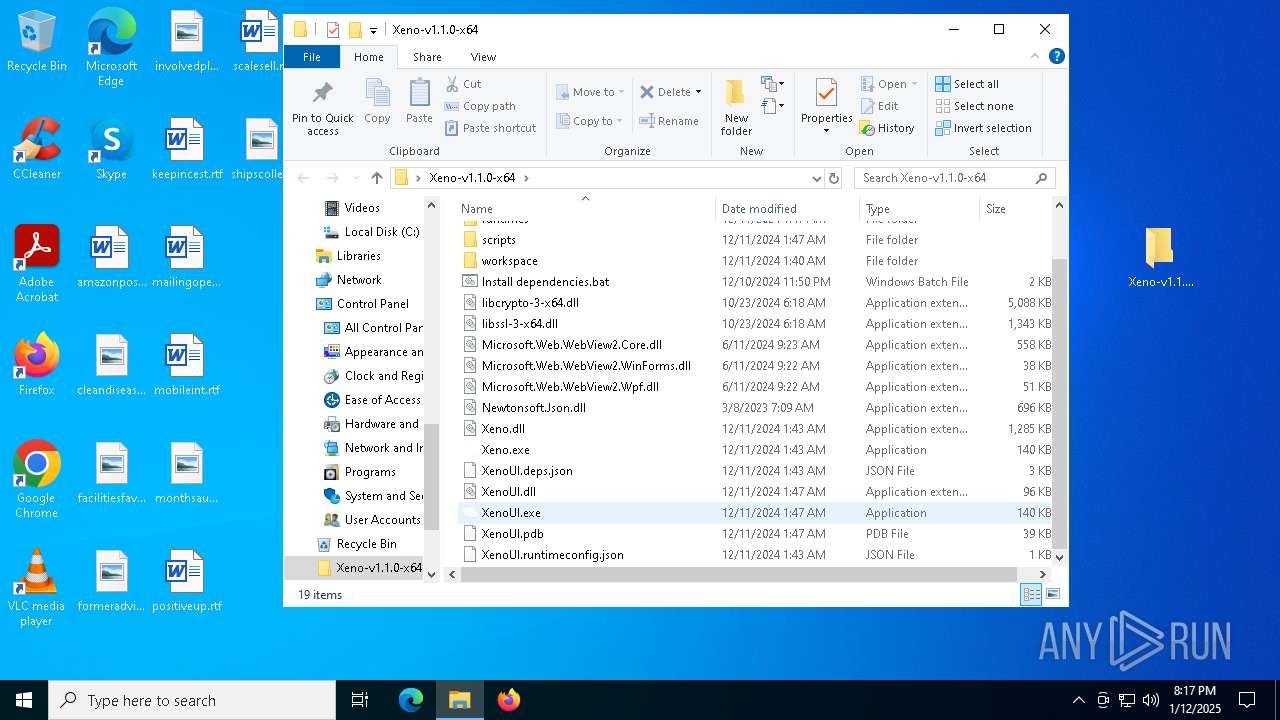
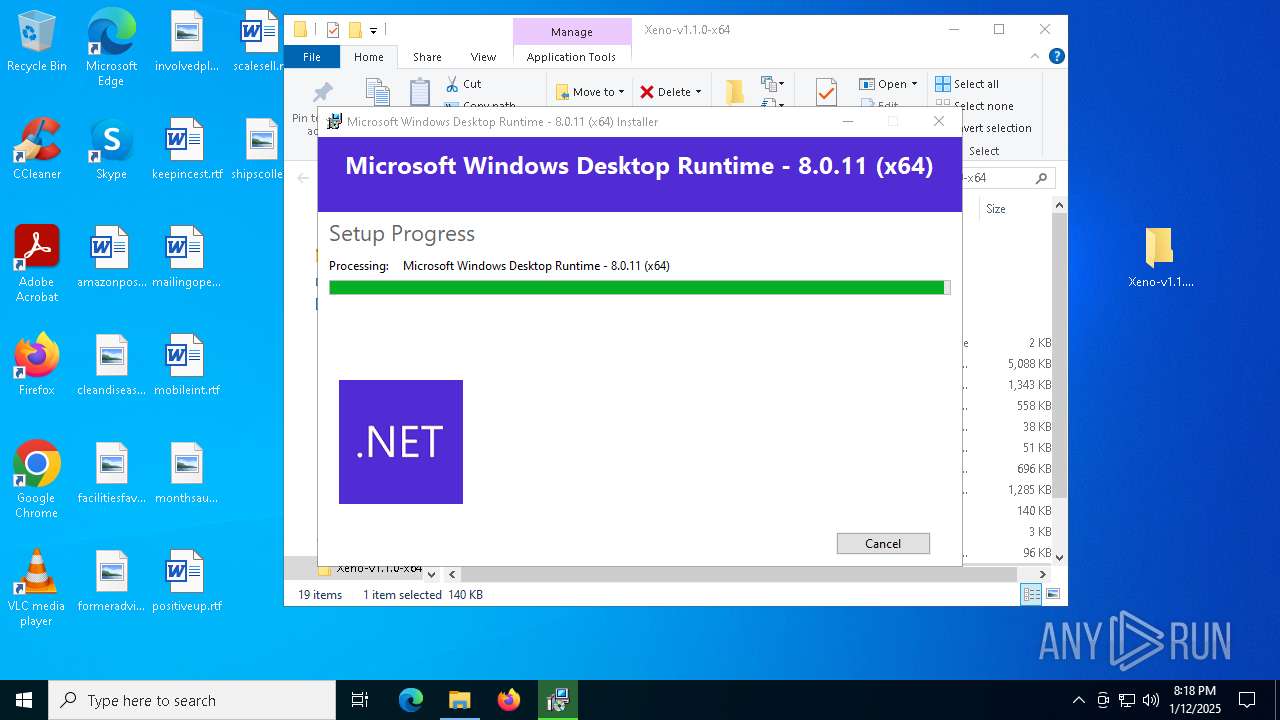
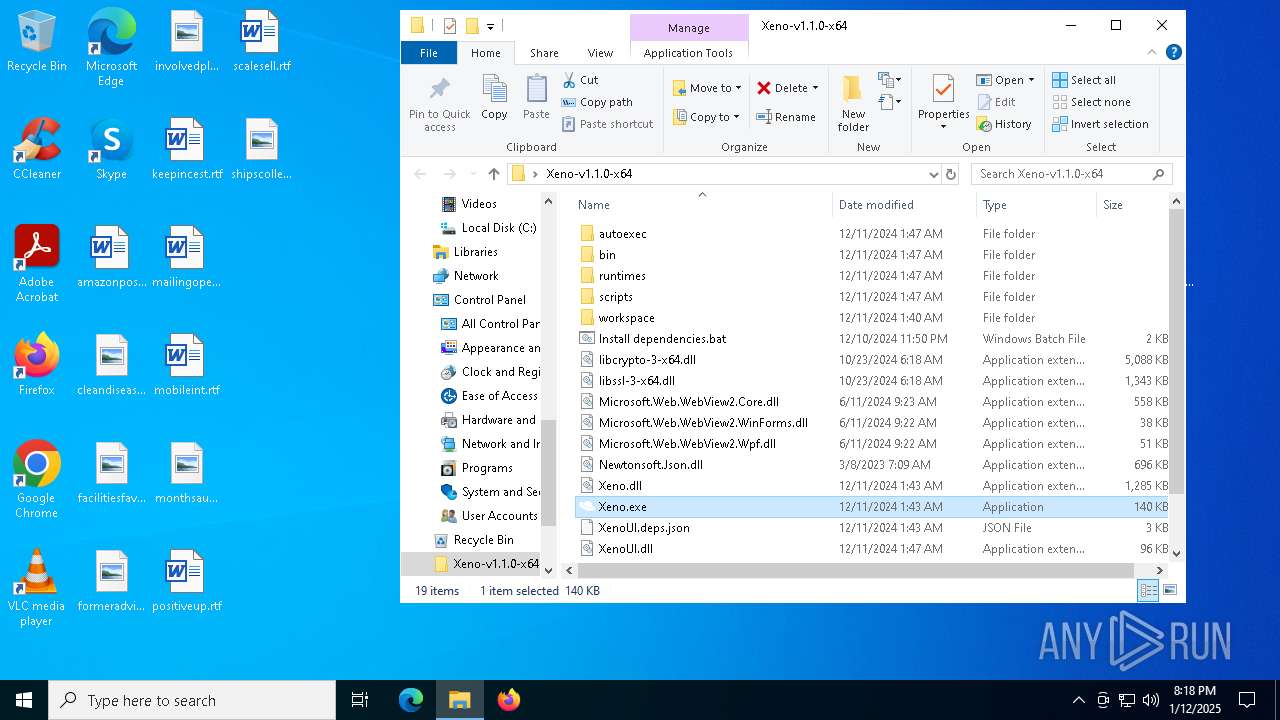
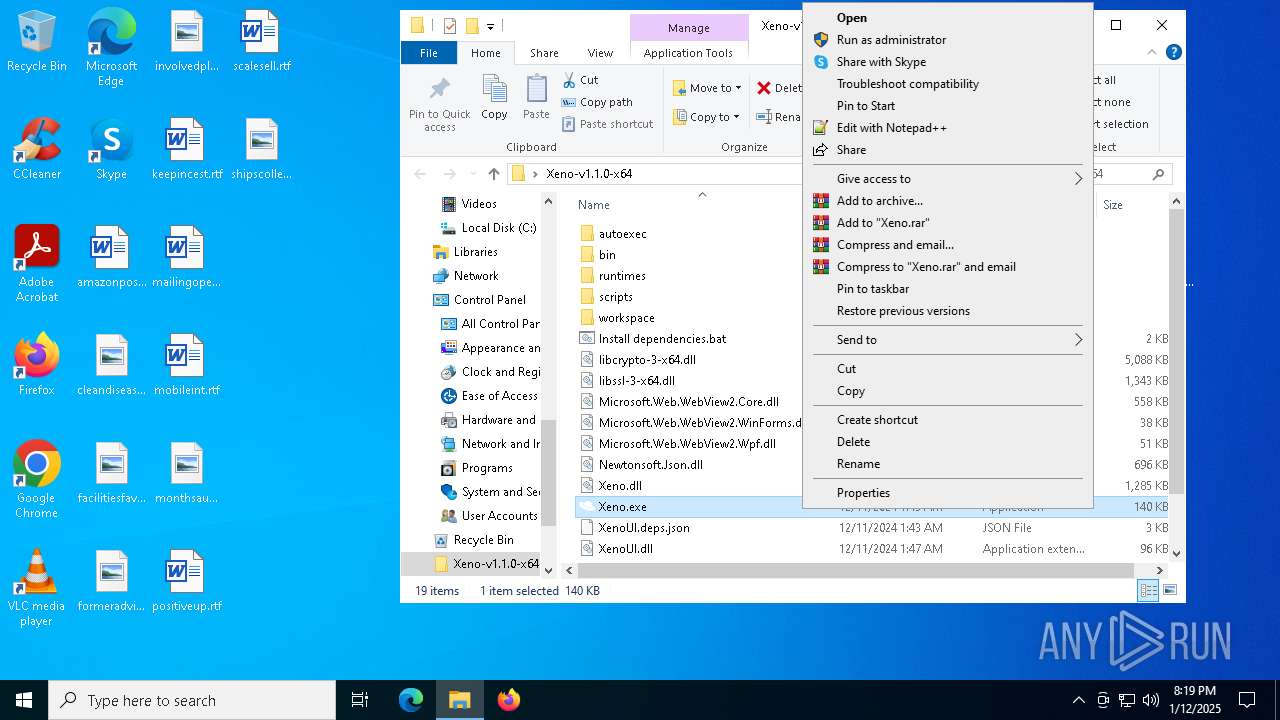
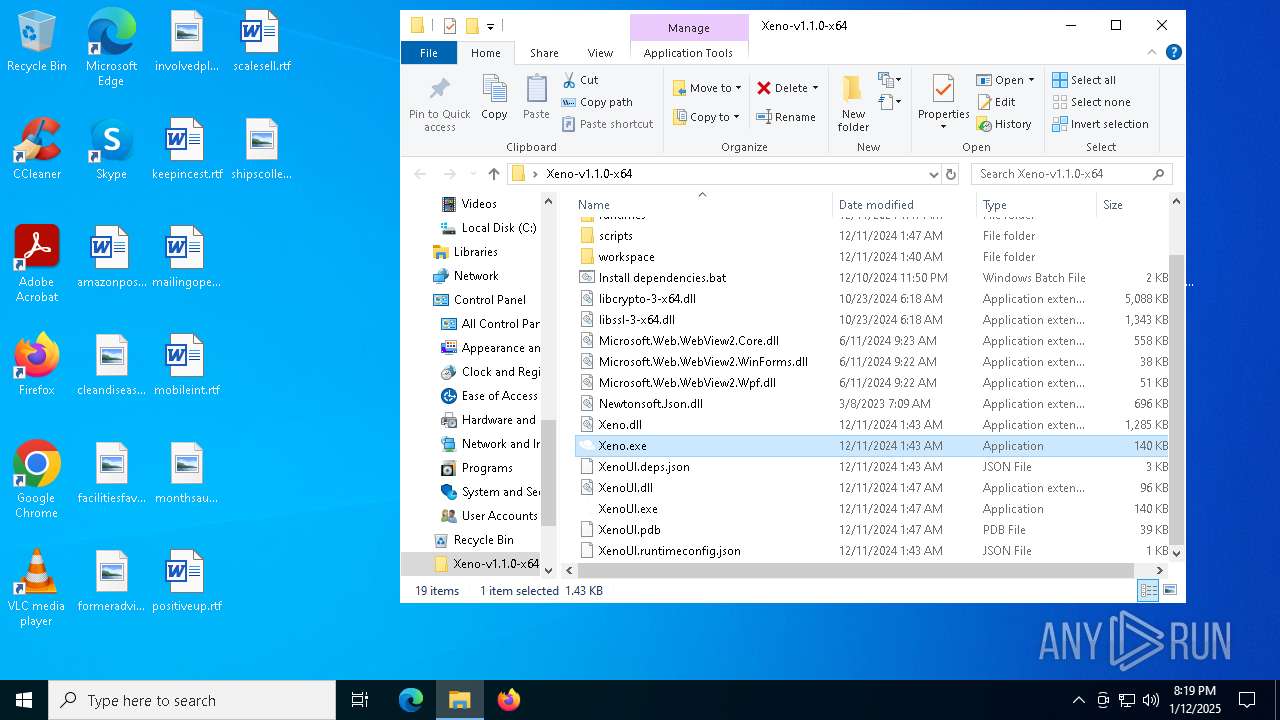
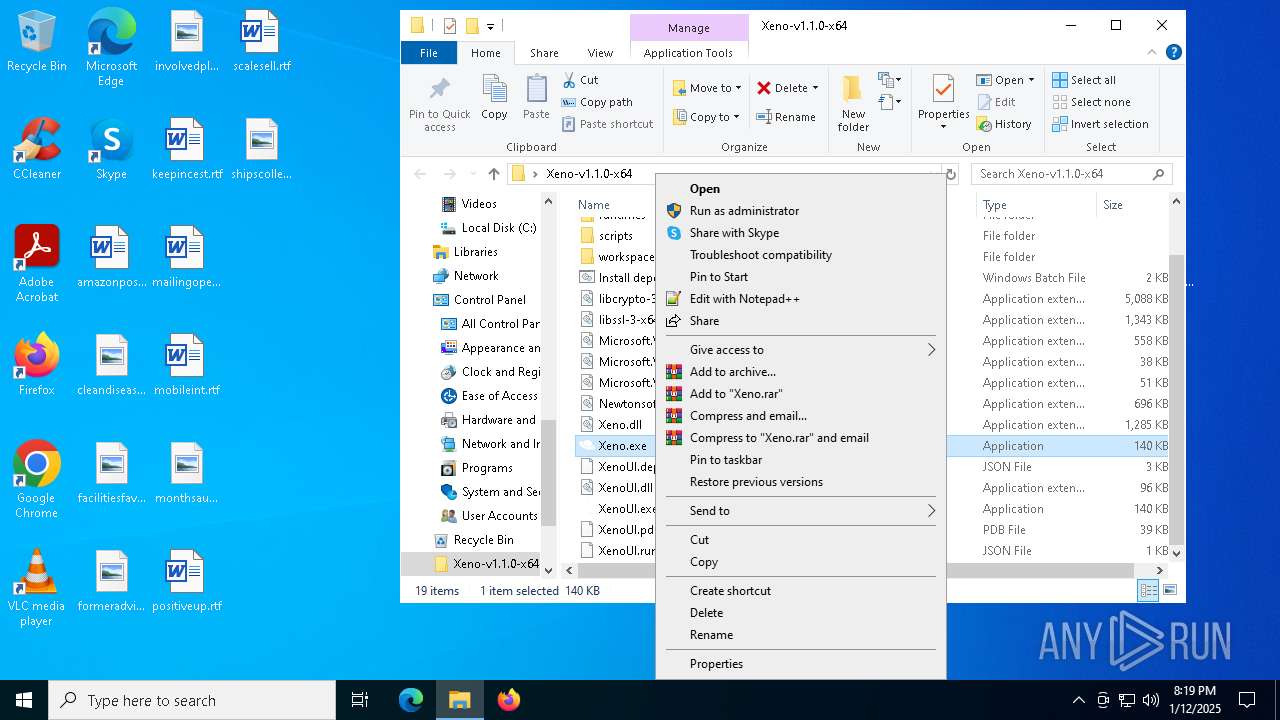
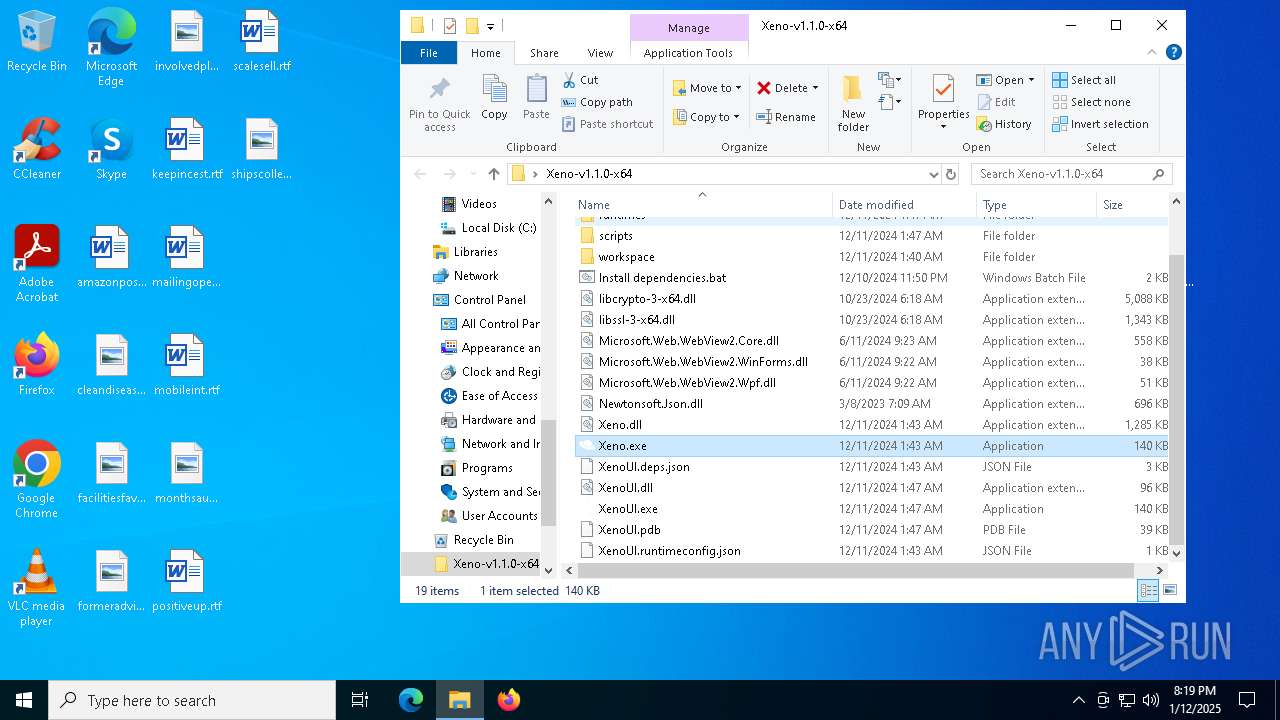
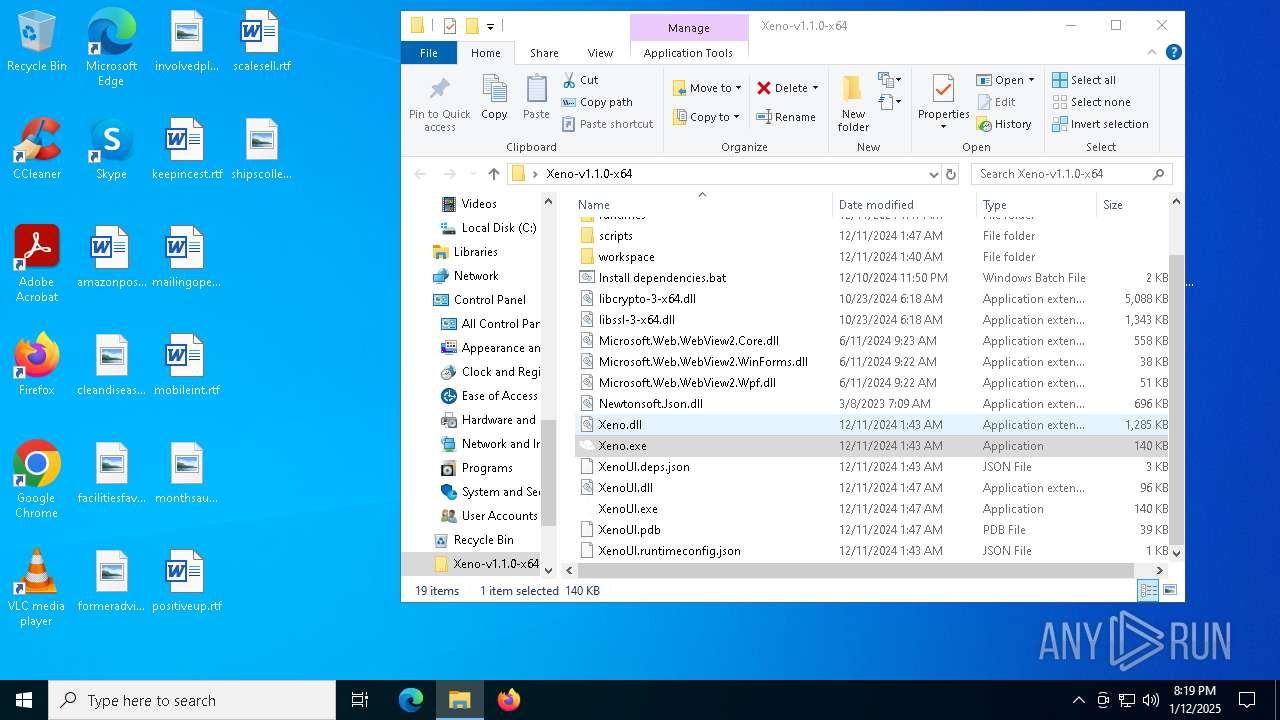
Manual execution by a user
- XenoUI.exe (PID: 3832)
- Xeno.exe (PID: 7688)
- Xeno.exe (PID: 2280)
- Xeno.exe (PID: 6968)
- Xeno.exe (PID: 6984)
- Xeno.exe (PID: 5576)
- cmd.exe (PID: 3984)
- cmd.exe (PID: 6972)
- Xeno.exe (PID: 6676)
- Xeno.exe (PID: 7828)
- Xeno.exe (PID: 7788)
- XenoUI.exe (PID: 2972)
The sample compiled with english language support
- WinRAR.exe (PID: 6432)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 3724)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
- msiexec.exe (PID: 7580)
Checks supported languages
- XenoUI.exe (PID: 3832)
- identity_helper.exe (PID: 7292)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 3724)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
- msiexec.exe (PID: 7580)
- msiexec.exe (PID: 7656)
- msiexec.exe (PID: 3420)
- msiexec.exe (PID: 7980)
- msiexec.exe (PID: 8)
- identity_helper.exe (PID: 6884)
- Xeno.exe (PID: 7688)
- Xeno.exe (PID: 6968)
- Xeno.exe (PID: 2280)
- Xeno.exe (PID: 6984)
- Xeno.exe (PID: 5576)
- dotnet.exe (PID: 7488)
- dotnet.exe (PID: 716)
- Xeno.exe (PID: 6676)
- XenoUI.exe (PID: 2972)
Reads the computer name
- XenoUI.exe (PID: 3832)
- identity_helper.exe (PID: 7292)
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- msiexec.exe (PID: 7580)
- msiexec.exe (PID: 7656)
- msiexec.exe (PID: 3420)
- msiexec.exe (PID: 8)
- msiexec.exe (PID: 7980)
- Xeno.exe (PID: 7688)
- Xeno.exe (PID: 2280)
- Xeno.exe (PID: 5576)
- Xeno.exe (PID: 7828)
- Xeno.exe (PID: 7788)
- XenoUI.exe (PID: 2972)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6432)
- msedge.exe (PID: 6292)
- msiexec.exe (PID: 7580)
The process uses the downloaded file
- WinRAR.exe (PID: 6432)
- msedge.exe (PID: 8028)
- msedge.exe (PID: 6292)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
Sends debugging messages
- XenoUI.exe (PID: 3832)
- Xeno.exe (PID: 7688)
Reads Environment values
- identity_helper.exe (PID: 7292)
Create files in a temporary directory
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 3724)
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
Process checks computer location settings
- windowsdesktop-runtime-8.0.11-win-x64 (1).exe (PID: 6436)
Reads the machine GUID from the registry
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
- msiexec.exe (PID: 7580)
Reads the software policy settings
- msiexec.exe (PID: 7580)
- WerFault.exe (PID: 4384)
- WerFault.exe (PID: 3988)
- WerFault.exe (PID: 4076)
- Xeno.exe (PID: 6984)
- Xeno.exe (PID: 6676)
- WerFault.exe (PID: 6652)
- Xeno.exe (PID: 7828)
- WerFault.exe (PID: 5308)
- WerFault.exe (PID: 7960)
Creates files in the program directory
- windowsdesktop-runtime-8.0.11-win-x64.exe (PID: 7488)
- Xeno.exe (PID: 7688)
Application launched itself
- msedge.exe (PID: 7868)
- msedge.exe (PID: 6292)
Checks proxy server information
- Xeno.exe (PID: 7688)
- Xeno.exe (PID: 2280)
- WerFault.exe (PID: 5964)
- Xeno.exe (PID: 6968)
- WerFault.exe (PID: 4384)
- Xeno.exe (PID: 5576)
- WerFault.exe (PID: 4076)
- Xeno.exe (PID: 6676)
- Xeno.exe (PID: 7788)
- WerFault.exe (PID: 6312)
- WerFault.exe (PID: 6652)
- XenoUI.exe (PID: 2972)
- WerFault.exe (PID: 7960)
Creates a software uninstall entry
- msiexec.exe (PID: 7580)
Creates files or folders in the user directory
- WerFault.exe (PID: 3988)
- WerFault.exe (PID: 4076)
- WerFault.exe (PID: 6312)
- WerFault.exe (PID: 7960)
- WerFault.exe (PID: 5308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:12:10 20:47:32 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Xeno-v1.1.0-x64/ |
Total processes
249
Monitored processes
103
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | C:\Windows\syswow64\MsiExec.exe -Embedding 8AB42EC35C9B2073419C394A13E77989 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 716 | dotnet --list-sdks | C:\Program Files\dotnet\dotnet.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Host Exit code: 0 Version: 8,0,1124,51707 @Commit: 9cb3b725e3ad2b57ddc9fb2dd48d2d17056 | |||||||||||||||
| 1144 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=3524 --field-trial-handle=2408,i,12128499273414738616,11449909190267596982,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5320 --field-trial-handle=2376,i,15625508392987347428,17640471934496124759,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
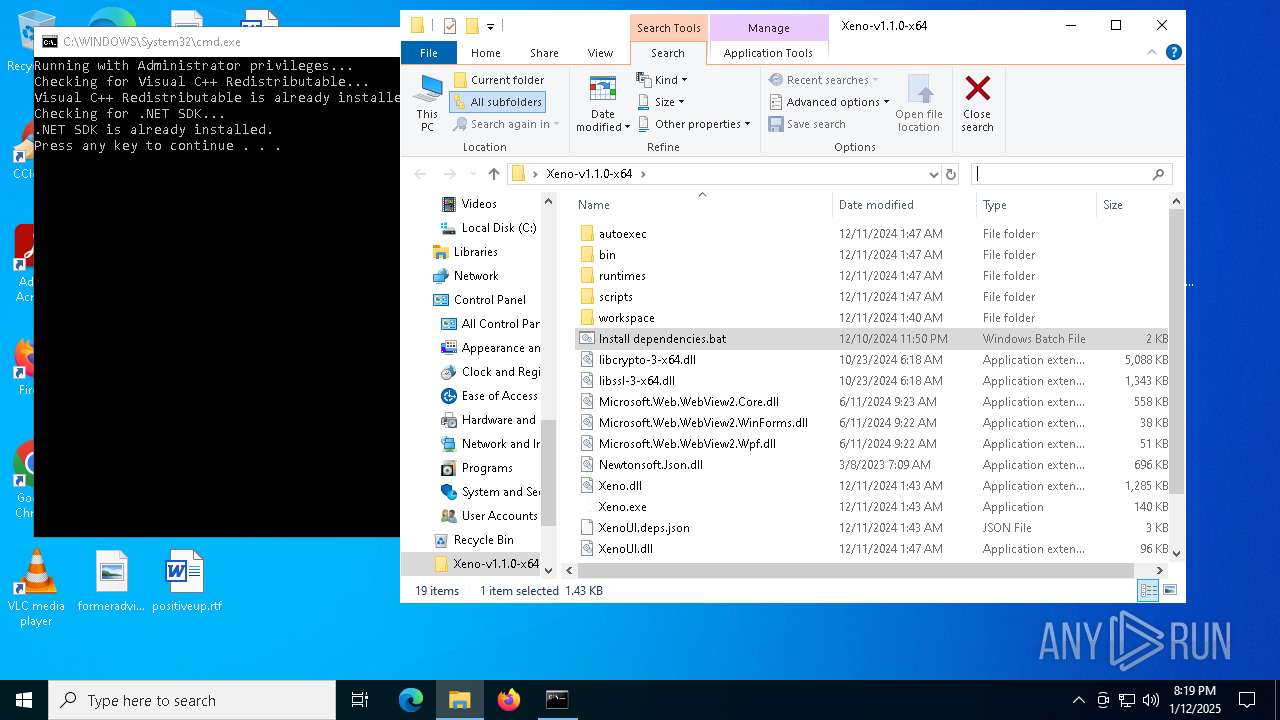
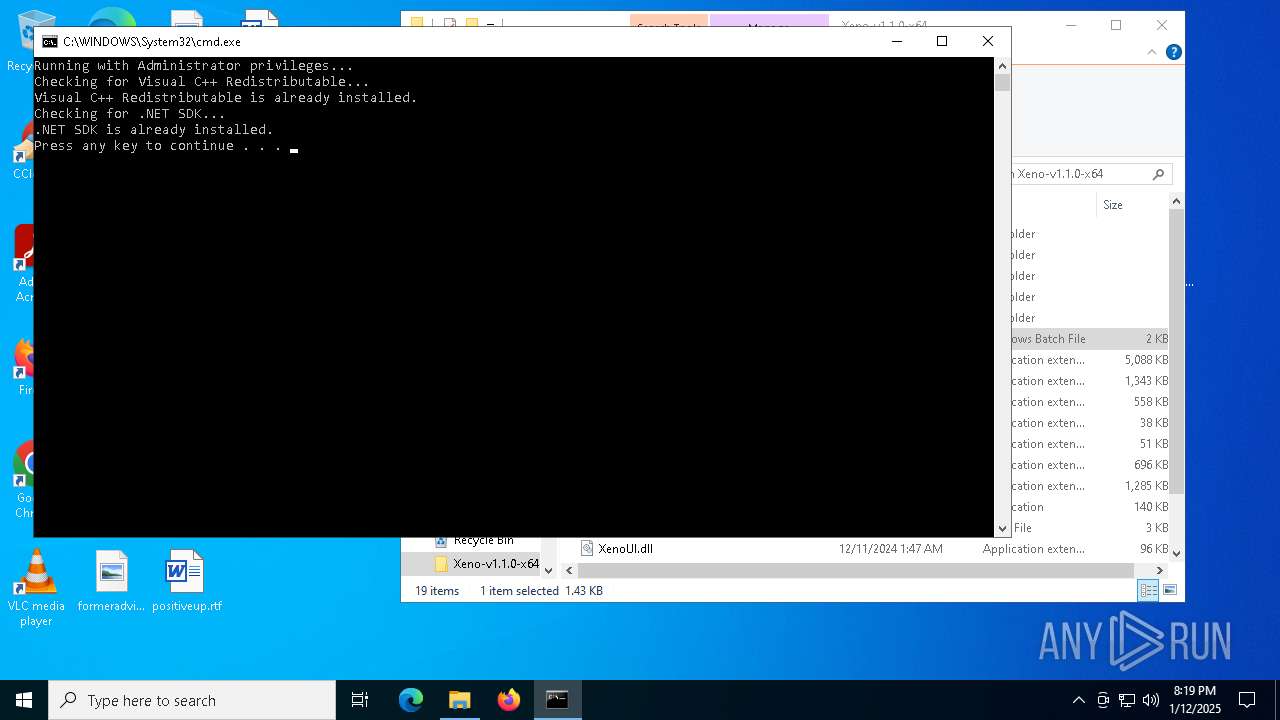
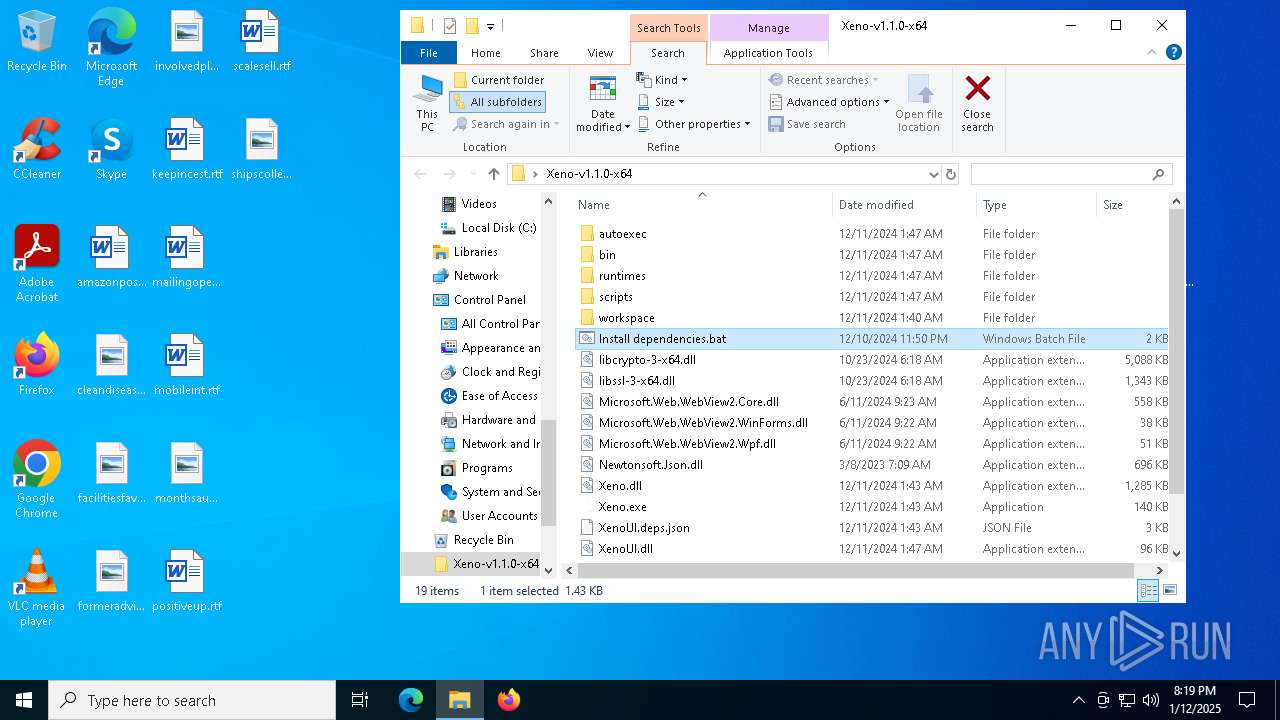
| 1540 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\Xeno-v1.1.0-x64\Install dependencies.bat" -elevated | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2280 | "C:\Users\admin\Desktop\Xeno-v1.1.0-x64\Xeno.exe" | C:\Users\admin\Desktop\Xeno-v1.1.0-x64\Xeno.exe | explorer.exe | ||||||||||||
User: admin Company: XenoUI Integrity Level: MEDIUM Description: XenoUI Exit code: 0 Version: 1.1.0 Modules
| |||||||||||||||
| 2440 | reg query "HKLM\SOFTWARE\Microsoft\VisualStudio\14.0\VC\Runtimes\x64" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5512 --field-trial-handle=2408,i,12128499273414738616,11449909190267596982,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
64 902
Read events
63 926
Write events
929
Delete events
47
Modification events
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Xeno-v1.1.0-x64.zip | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
506
Suspicious files
381
Text files
142
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\editor\editor.main.nls.zh-cn.js | text | |
MD5:05E49314CF801F5D3992B55243690EA7 | SHA256:E9ADC8FFCA9853EF6E0BD4E955AF9F395A570BC7772FC2DAC0C0FF241AAC864B | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\editor\editor.main.nls.de.js | text | |
MD5:D1FD2FB756C73970B9C5E0BA07BFF708 | SHA256:CB1C3416FF242A738C45C3B2590D7D222B159A95A69CE3B7B8D7C8D18EA70828 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\editor\editor.main.nls.ja.js | text | |
MD5:3BF851CC70F515CBBE1D39DA93E4F041 | SHA256:1F3556EA7233843B9E08B3C97B6727C533D702563E195C2090A438070DC85F0F | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\editor\editor.main.js | s | |
MD5:2DC0068CDBC03CE43A75AB0B2DF664E2 | SHA256:B604B6148F70FE9DB882CCE2A7D327B2422AD2F203A805491002A8C564E3C3FF | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\base\worker\workerMain.js | s | |
MD5:D0AC5294C58E523CDDF25BC6D785FA48 | SHA256:E90D1A8F116FA74431117A3AD78DDE16DDE060A4BF7528DFE3D5A3AD6156504B | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\editor\editor.main.nls.fr.js | text | |
MD5:1A29080733878DD44E0C118E84CD0C39 | SHA256:6ED837DC1905C06A20D102921FF06A0BDA003C5368ED0576BF7E69494E889AE8 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\index.html | html | |
MD5:001DCBB8F41CDCBF9B4D1E3A0ED4B2D2 | SHA256:F1D2C52F2803C29585B81D2EFF74C56242D27E9619EE6D38081D5604C5BB1951 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\basic-languages\lua\lua.js | s | |
MD5:EEBDA1FDD970433750C115EAE2F03865 | SHA256:AC729EFB3164F48D6B08F74D4B15060C126A30D40FB4CD4FC9CC94F2E19BD7C7 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\editor\editor.main.nls.es.js | text | |
MD5:36F546B28CA17ECE9F8EB9BCF8344E13 | SHA256:327437EE3793E9AE0686C78196B459592C282ED2E86F95CE28D32693B76D7654 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6432.36787\Xeno-v1.1.0-x64\bin\Monaco\vs\editor\editor.main.nls.js | text | |
MD5:E871D4D9539C26D7D2BF32801EBDECF0 | SHA256:5FF0084E6A7EEE82A735616239AAF2190EA9D90E89E19340831F3D590828016A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
101
DNS requests
90
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6068 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6292 | msedge.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6068 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 2.21.65.154:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
aka.ms |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
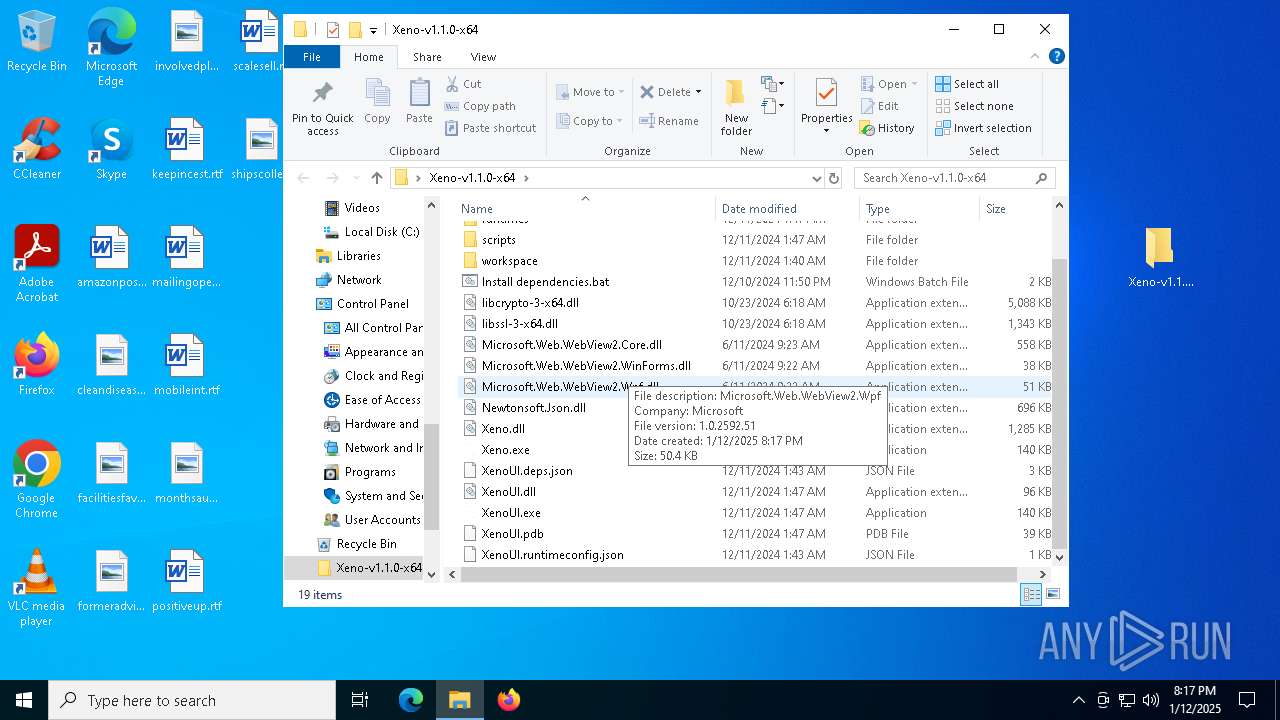
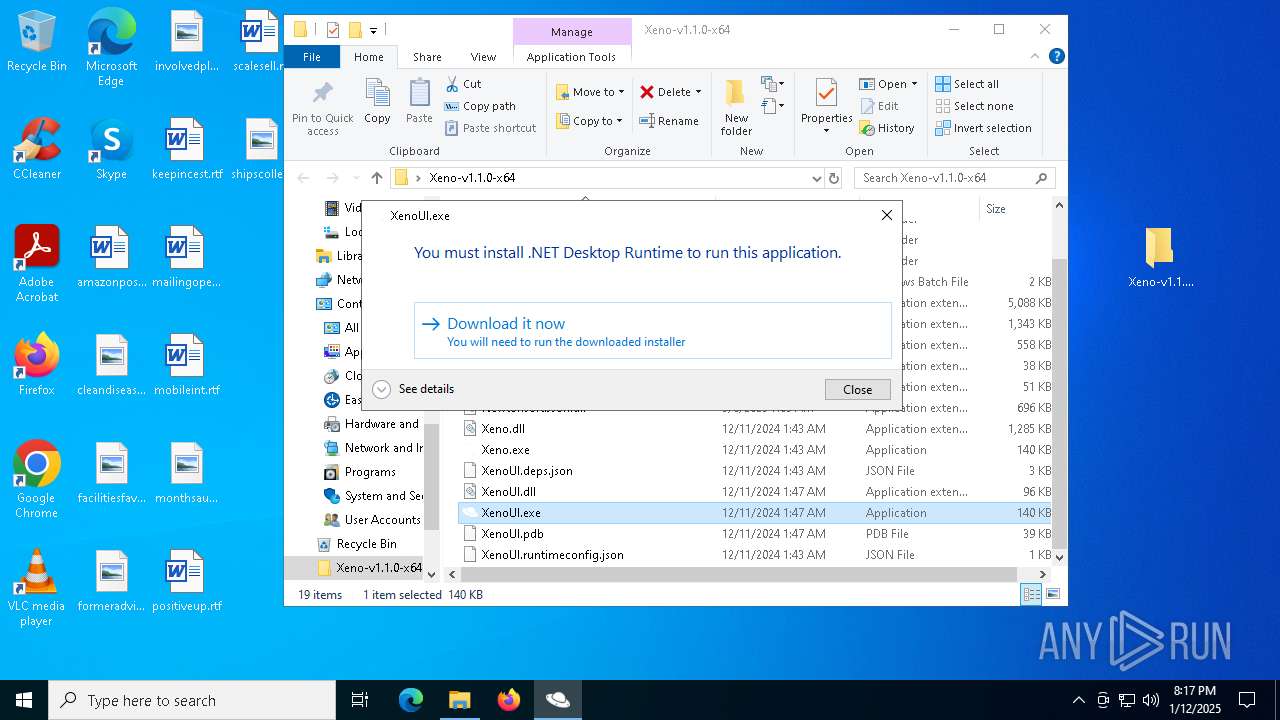
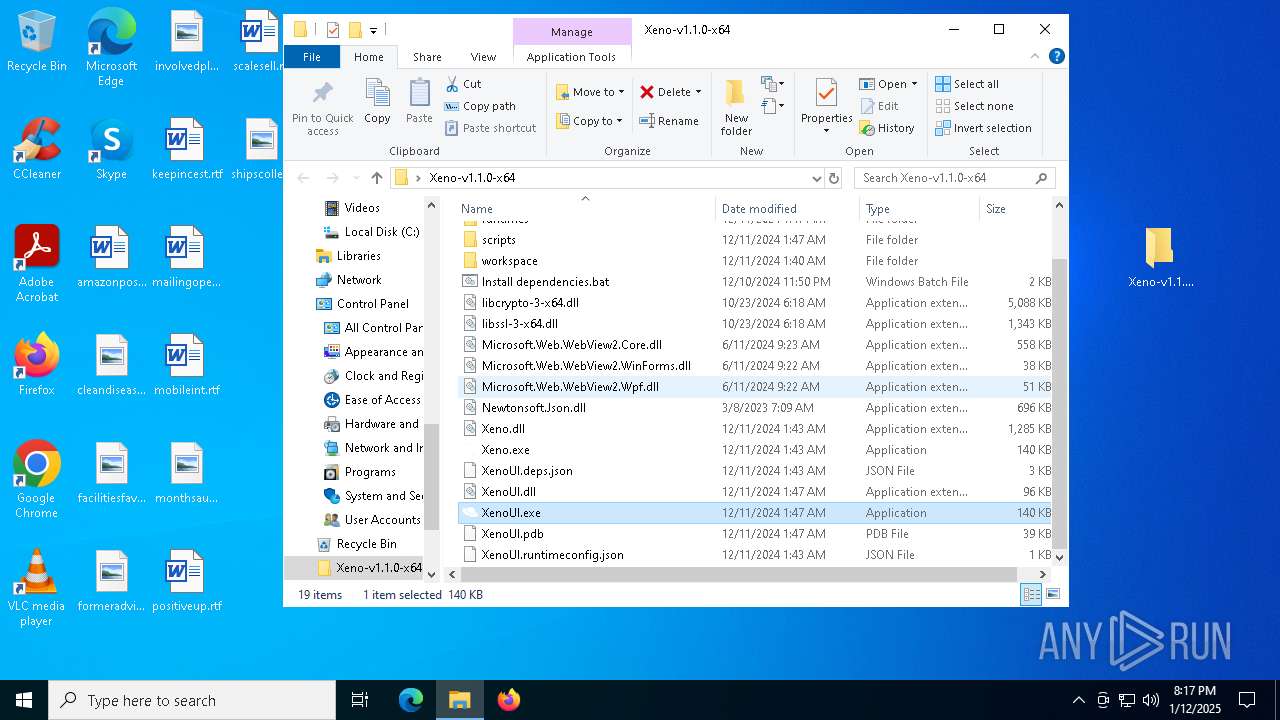
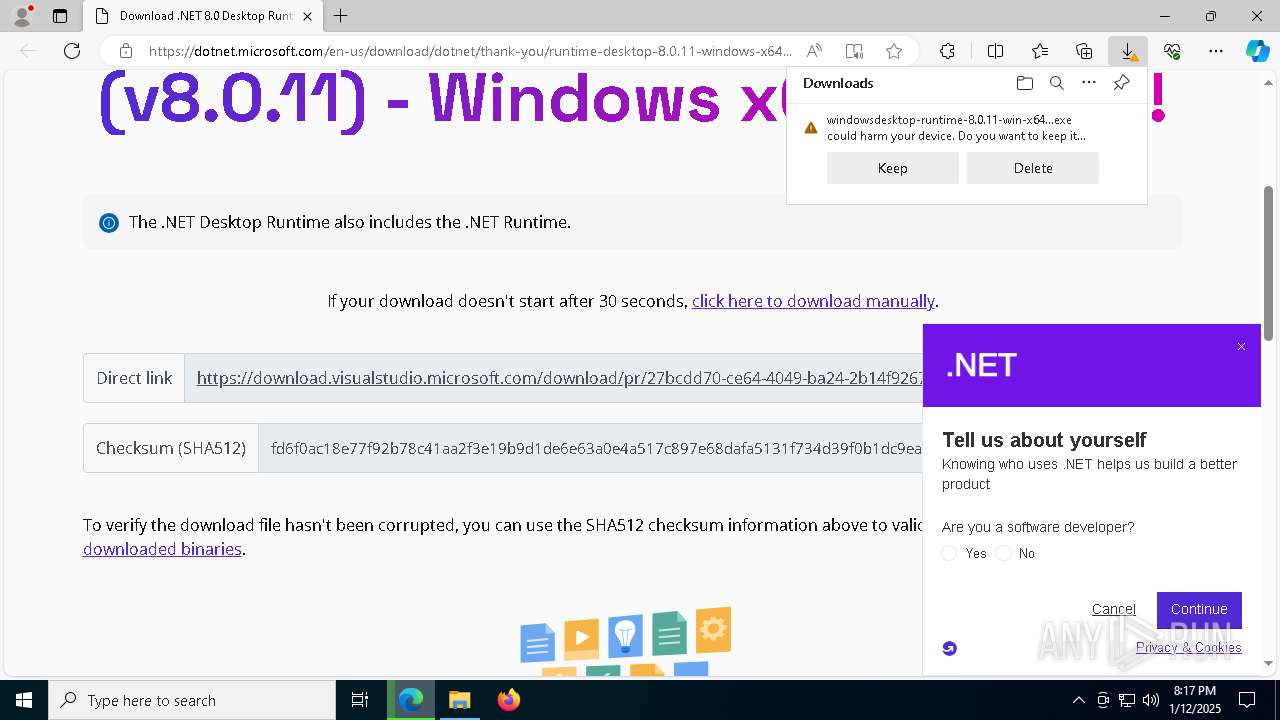
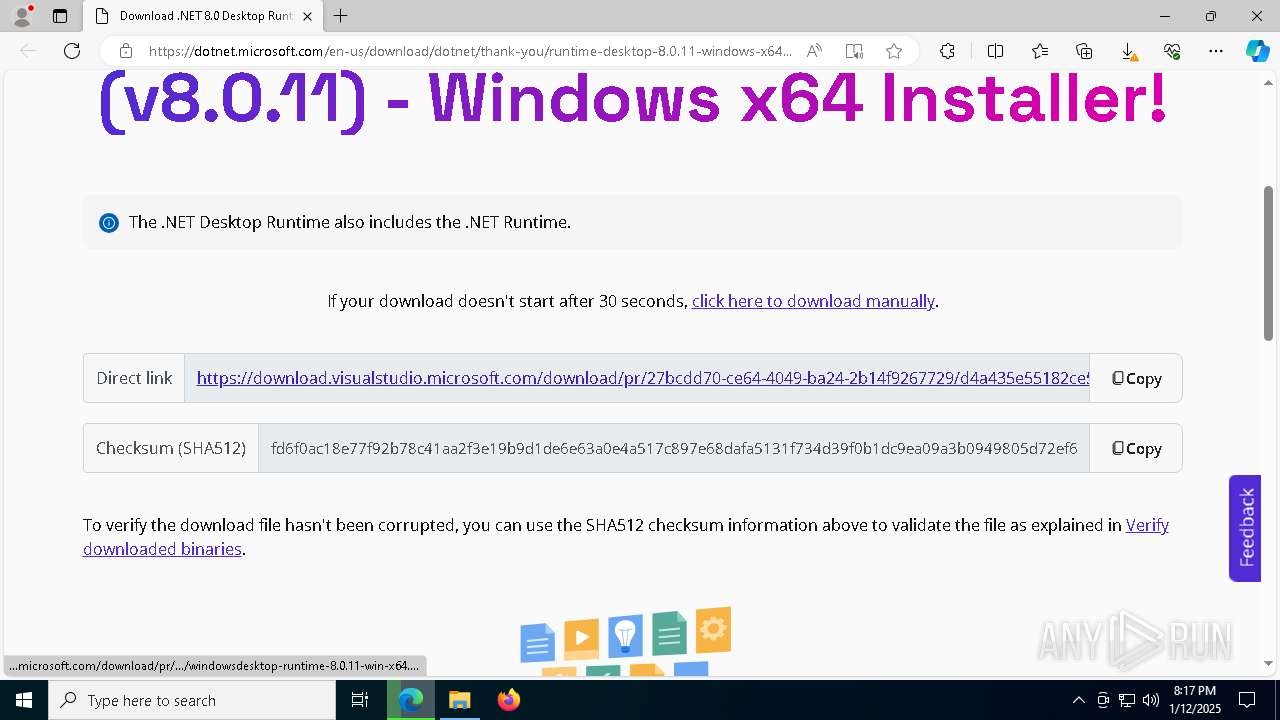
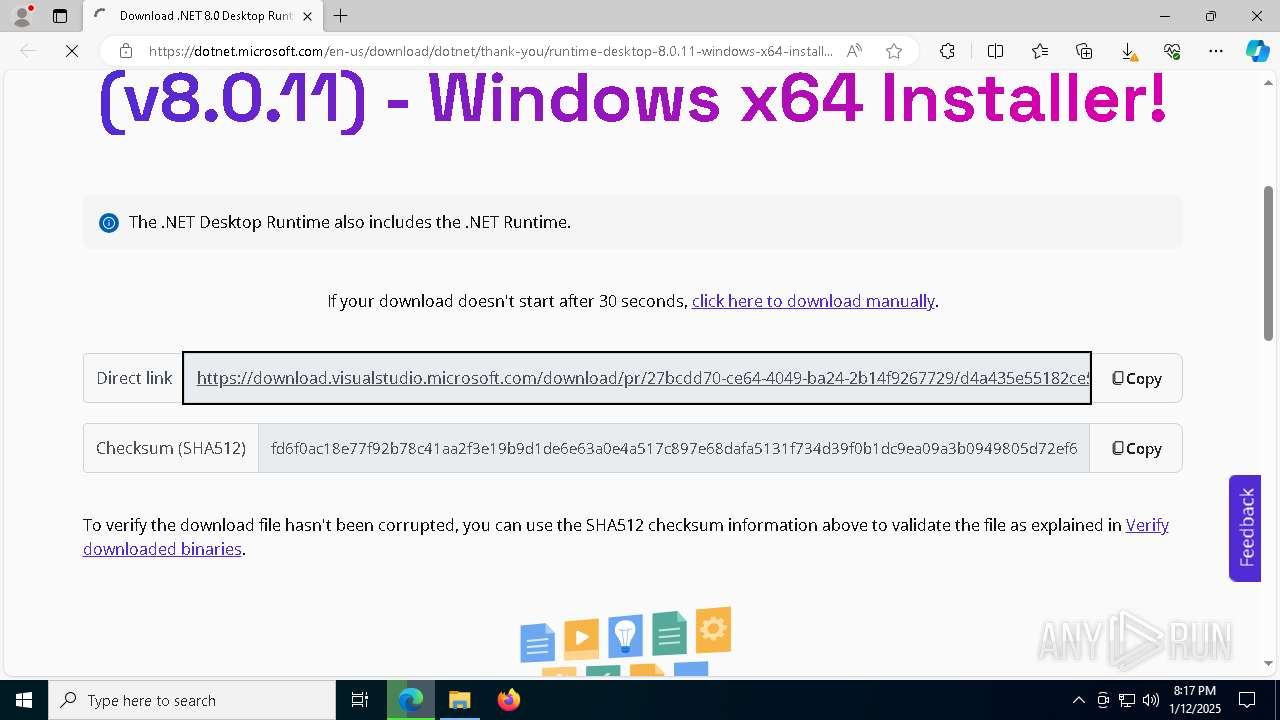
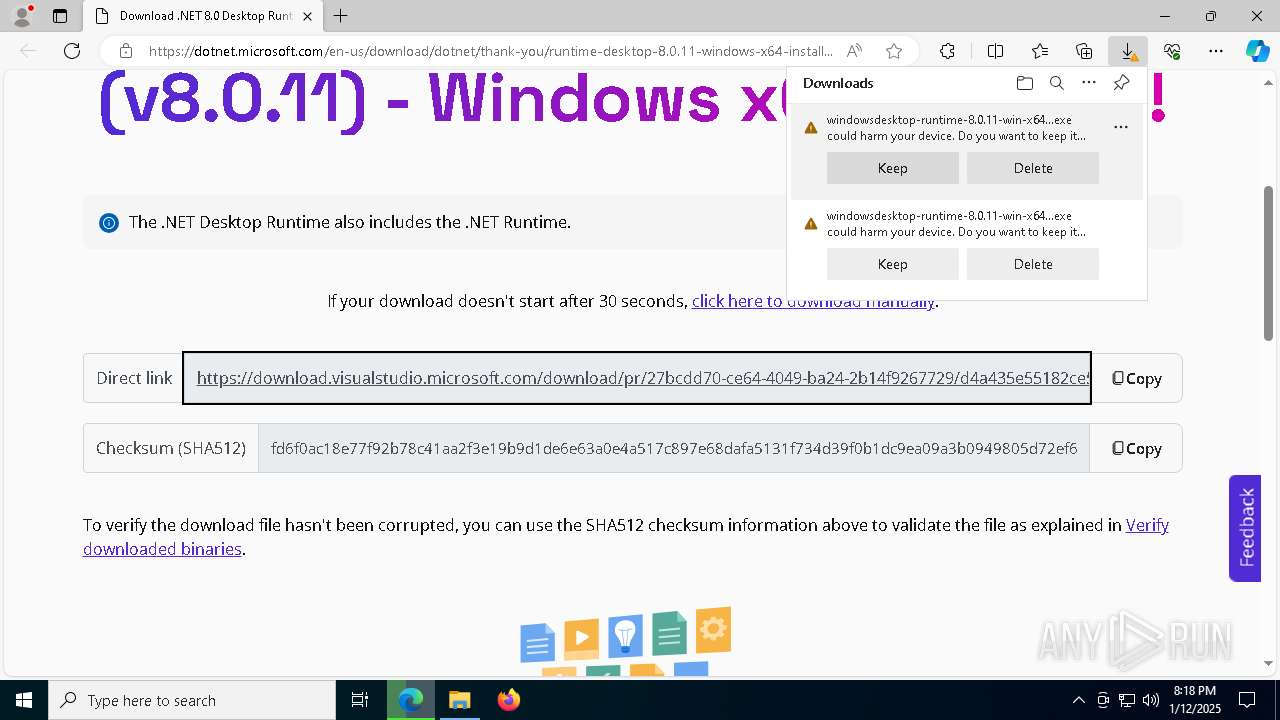
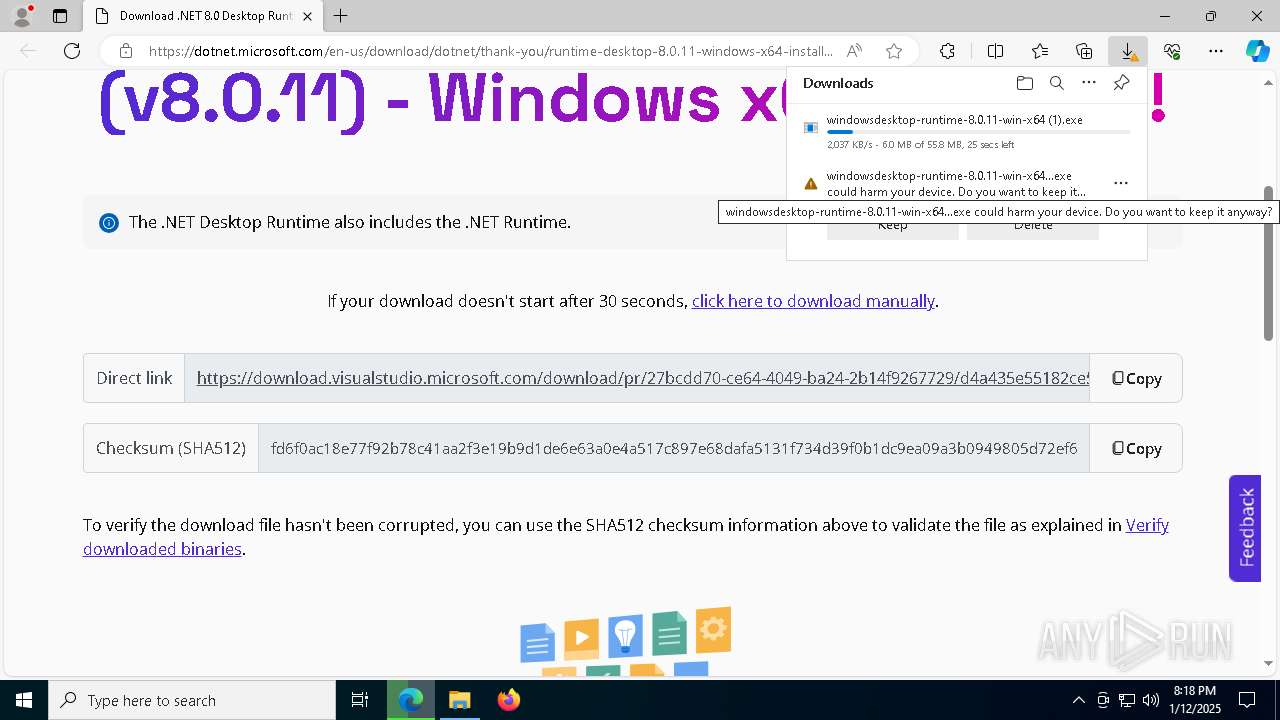
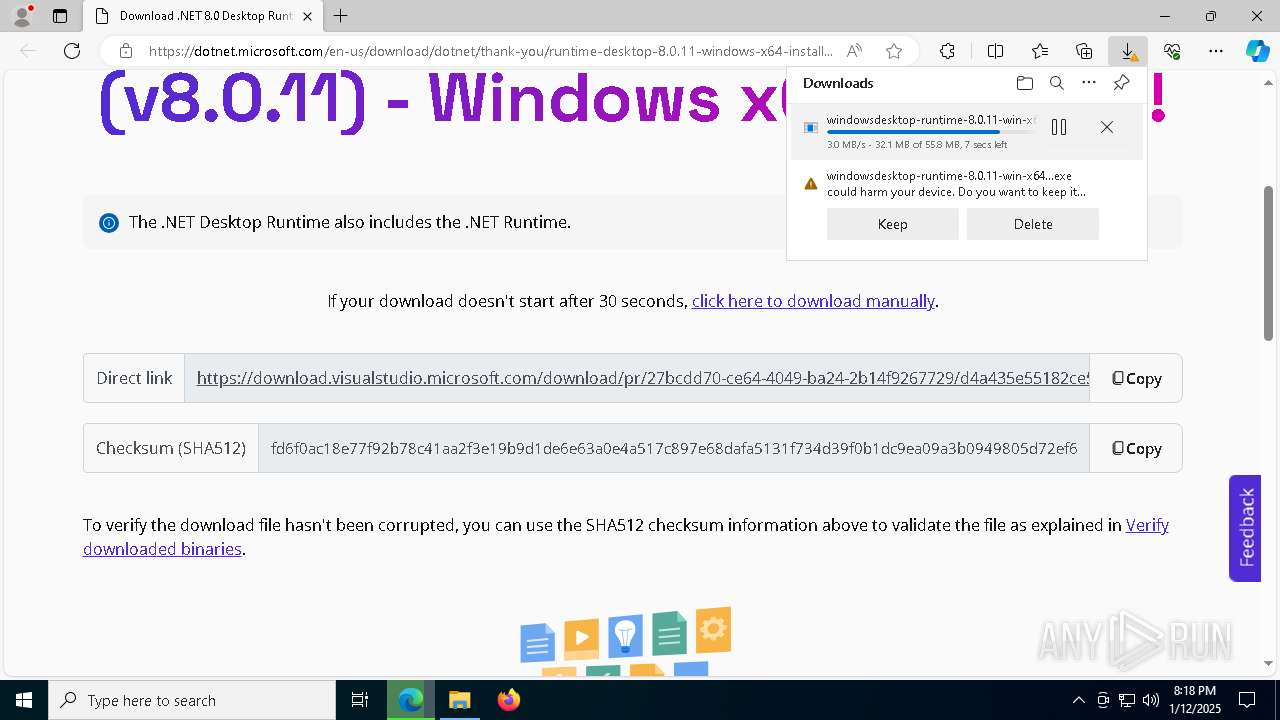
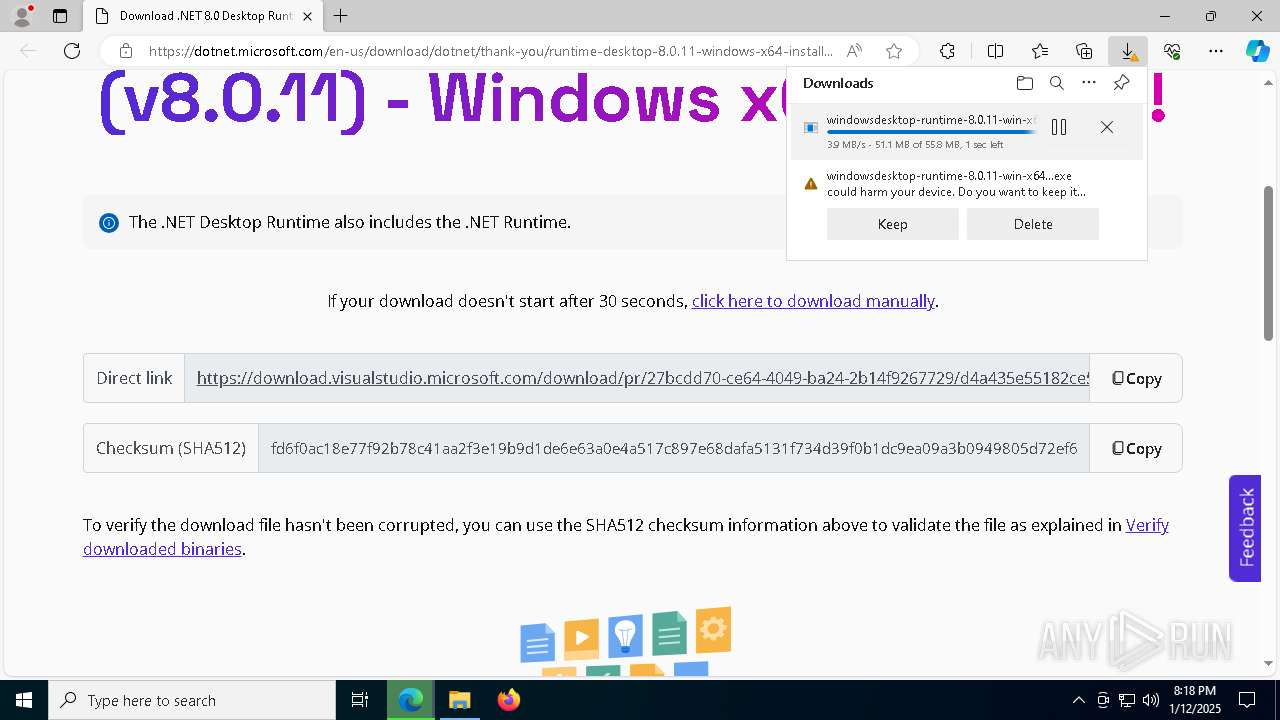
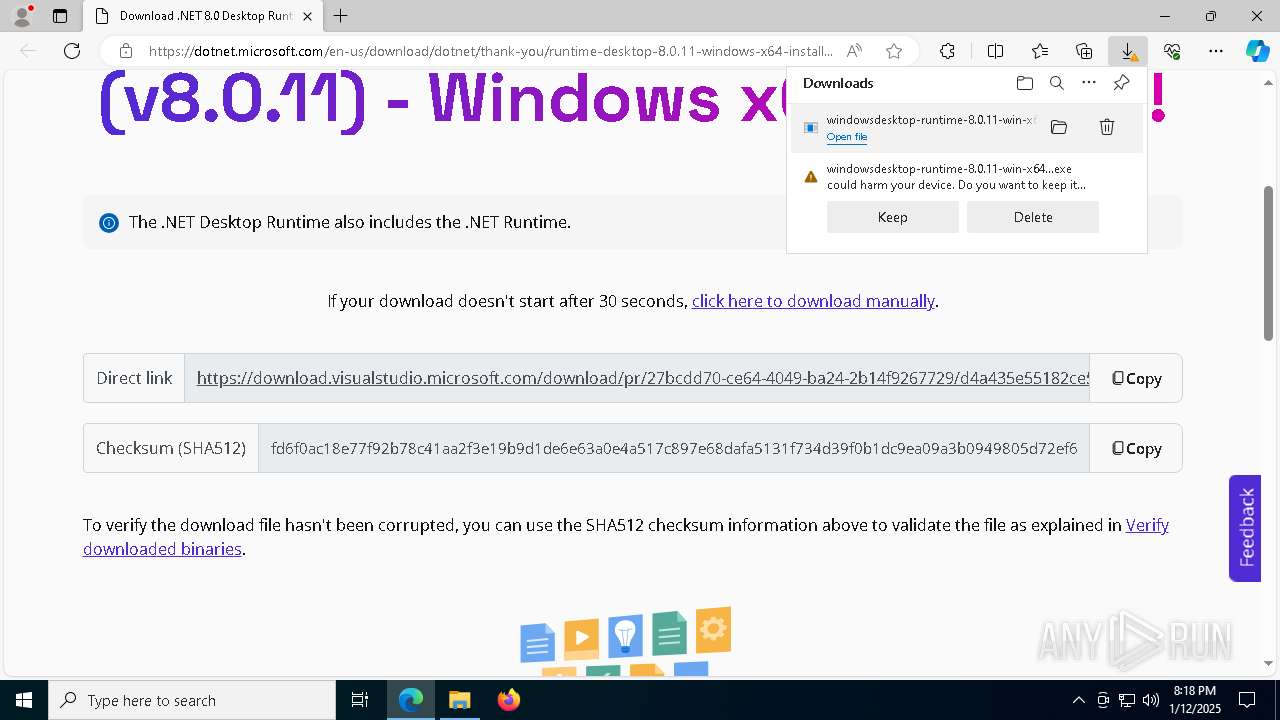
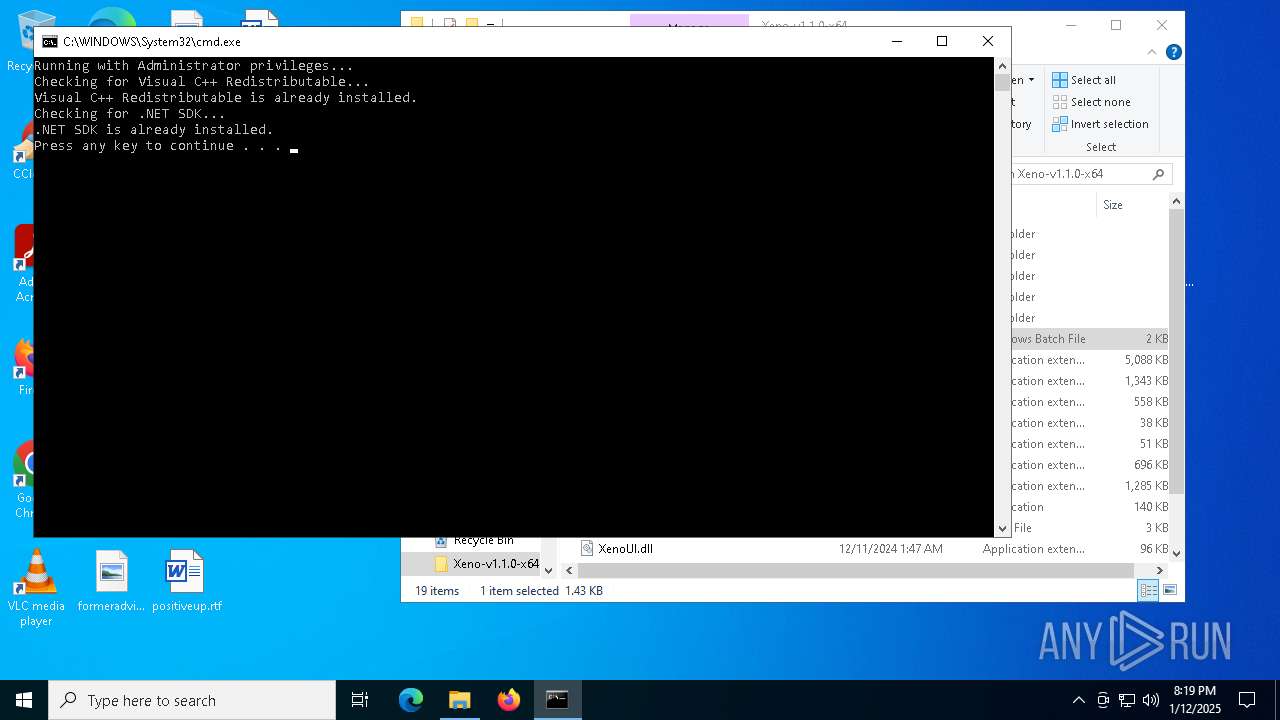
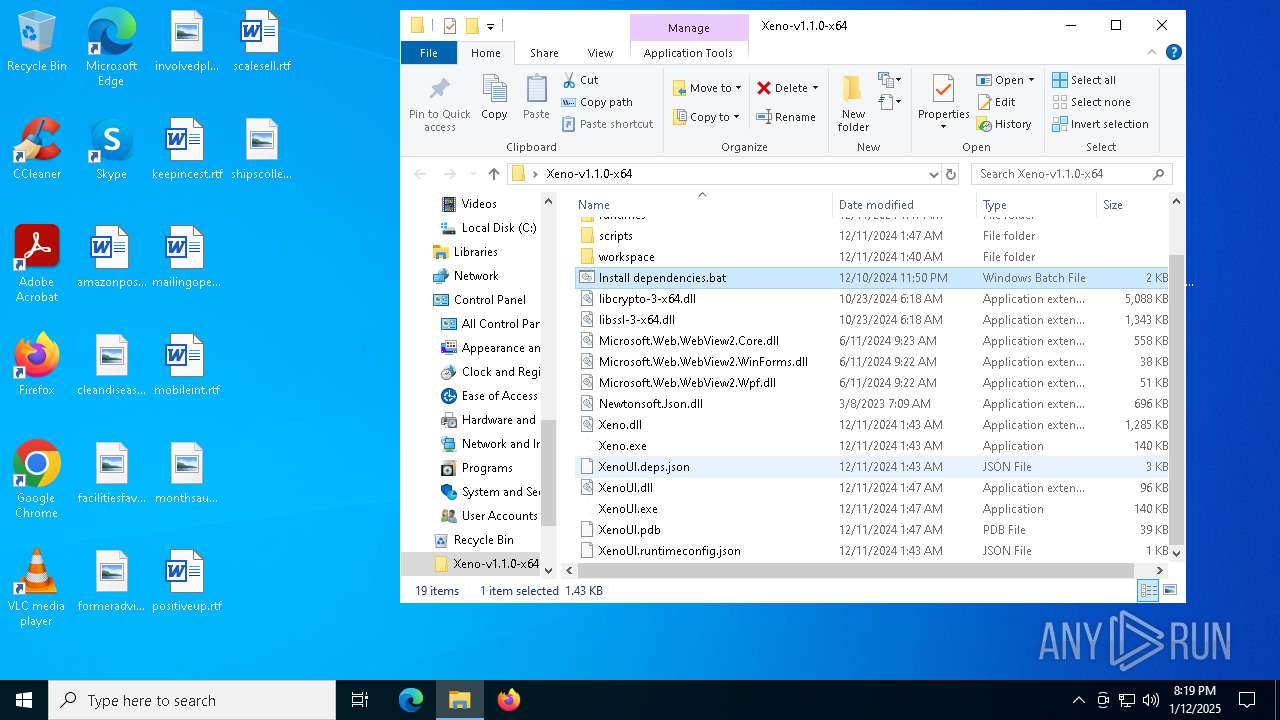
XenoUI.exe | You must install .NET to run this application.
App: C:\Users\admin\Desktop\Xeno-v1.1.0-x64\XenoUI.exe
Architecture: x64
App host version: 8.0.11
.NET location: Not found
Learn more:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.11 |
Xeno.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|