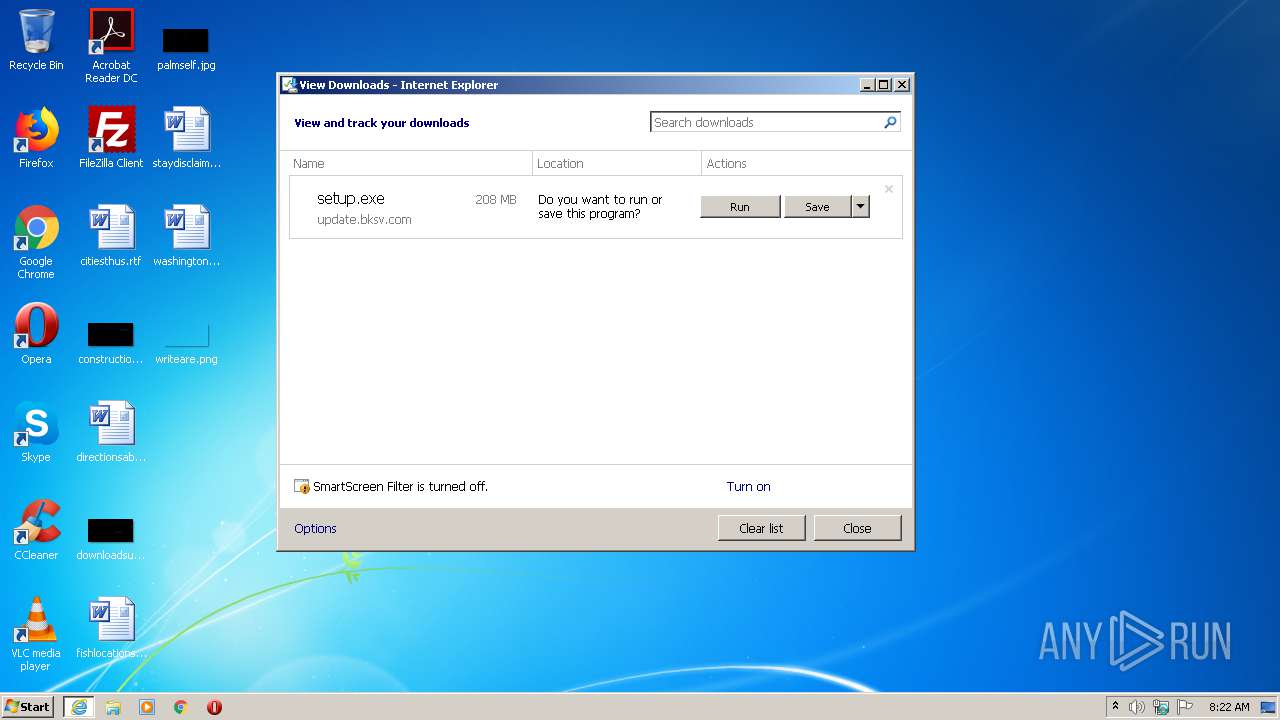
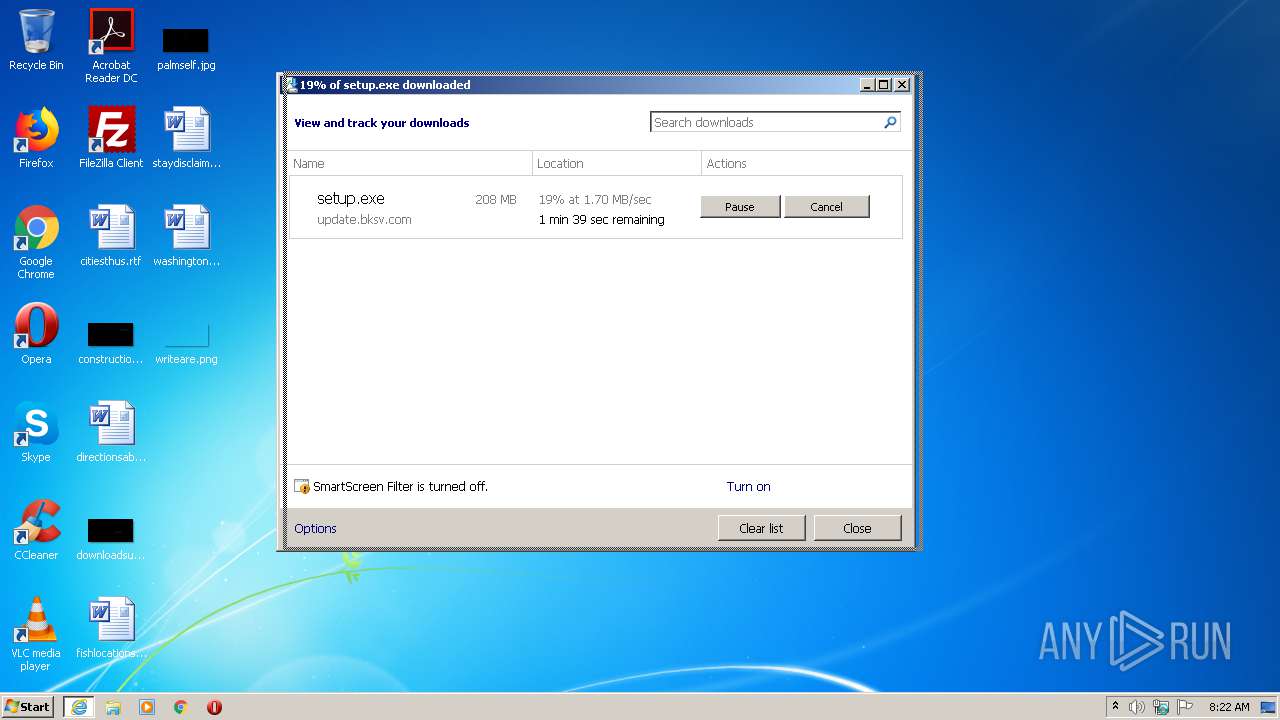
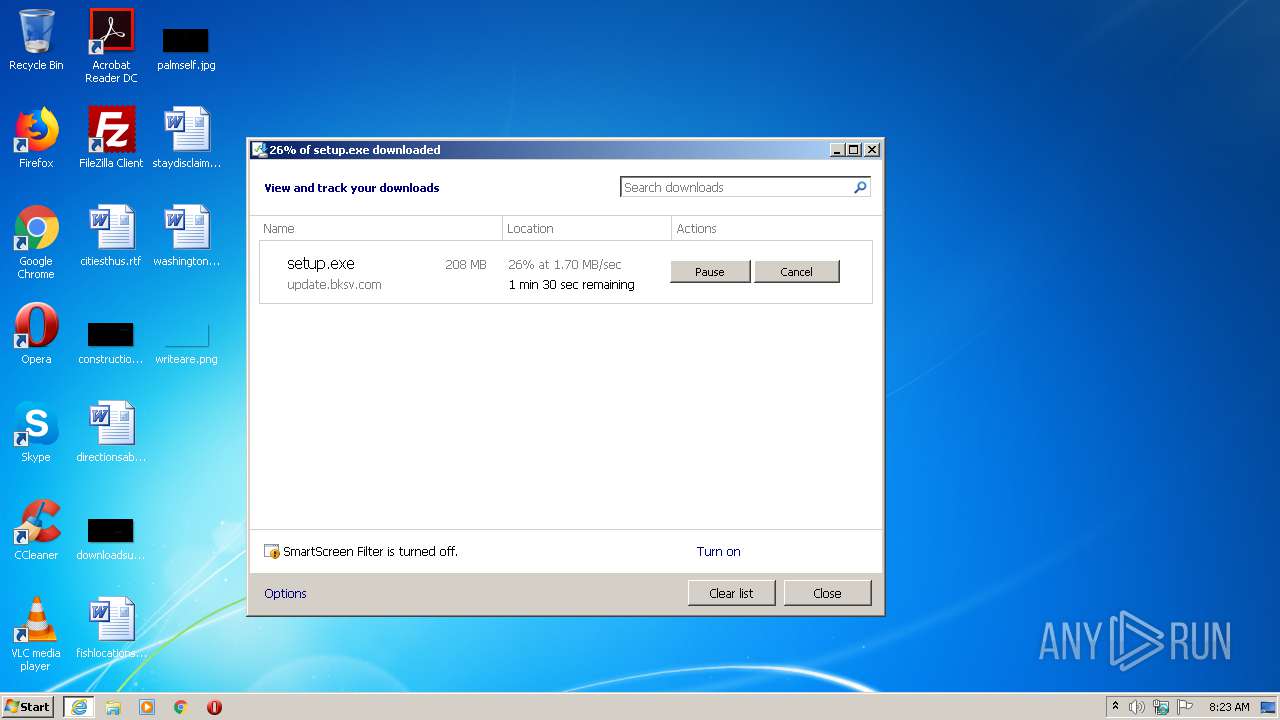
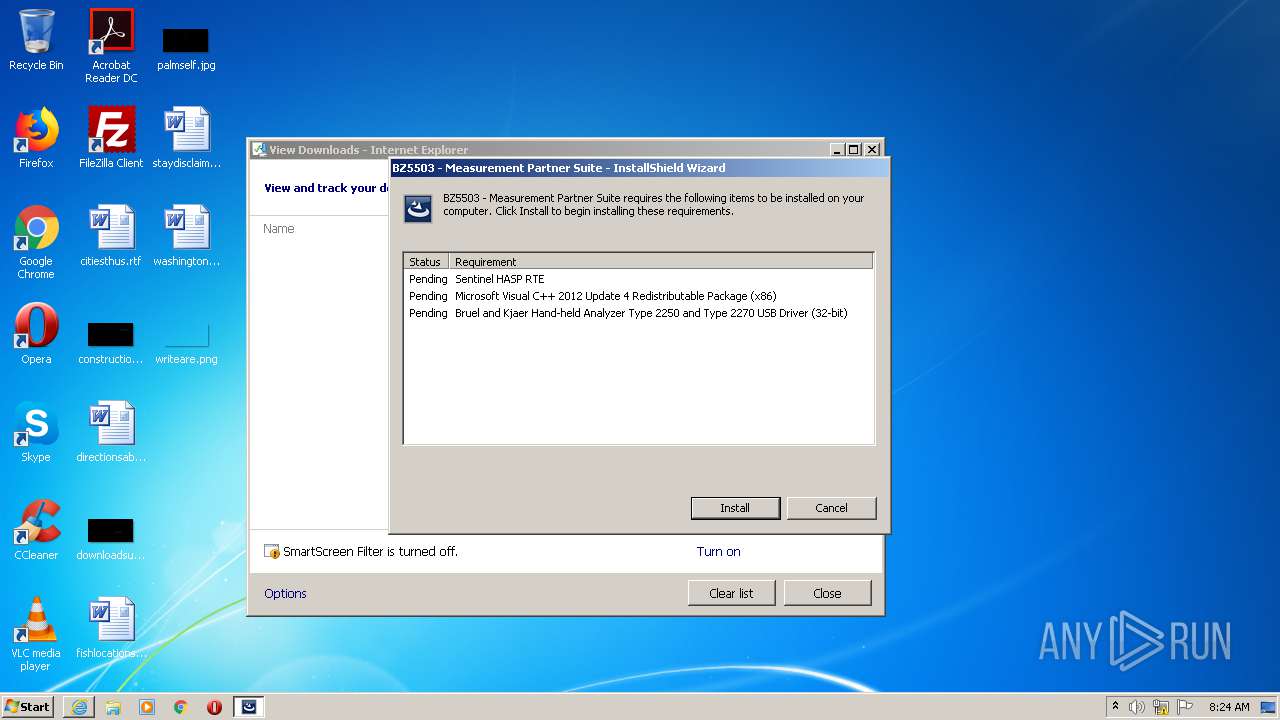
| URL: | https://update.bksv.com/BZ5503/Latest/setup.exe |
| Full analysis: | https://app.any.run/tasks/0be6f9f8-c6e4-48dd-9486-13711acc5713 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2020, 07:22:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 62D6522516C5DE6FC61C47614E9B2BA3 |
| SHA1: | 929BEC1AECF13F6CFFCE4B5348C8FE6FB11CF3A4 |
| SHA256: | 80BAAABB13D24BA0771070B6A8D4A3ADE7B782157E840DDE1163E6D40CECE5FE |
| SSDEEP: | 3:N8vRAjQz2/Qh4A:2vjmu4A |
MALICIOUS
Changes the autorun value in the registry
- setup.exe (PID: 2240)
- vcredist_x86.exe (PID: 2944)
Loads dropped or rewritten executable
- haspdinst.exe (PID: 2728)
- vcredist_x86.exe (PID: 720)
- MsiExec.exe (PID: 2780)
- BZ5503.exe (PID: 3768)
- BZ5503AnalysisHelper.exe (PID: 2028)
- UsbComm.exe (PID: 1980)
Application was dropped or rewritten from another process
- haspdinst.exe (PID: 2728)
- hasplms.exe (PID: 660)
- vcredist_x86.exe (PID: 2944)
- vcredist_x86.exe (PID: 720)
- setup.exe (PID: 3864)
- wdreg_gui.exe (PID: 3432)
- wdreg_gui.exe (PID: 3112)
- BZ5503.exe (PID: 3768)
- BZ5503AnalysisHelper.exe (PID: 2028)
- UsbComm.exe (PID: 1980)
Actions looks like stealing of personal data
- setup.exe (PID: 2240)
Changes settings of System certificates
- msiexec.exe (PID: 2136)
- MSIEXEC.EXE (PID: 2776)
Drops known malicious document
- msiexec.exe (PID: 2136)
- msiexec.exe (PID: 2136)
SUSPICIOUS
Creates files in the Windows directory
- DrvInst.exe (PID: 2792)
- haspdinst.exe (PID: 2728)
- DrvInst.exe (PID: 3460)
- DrvInst.exe (PID: 1620)
- DrvInst.exe (PID: 1532)
- msiexec.exe (PID: 2136)
- wdreg_gui.exe (PID: 3432)
- DrvInst.exe (PID: 752)
- DrvInst.exe (PID: 2008)
- MsiExec.exe (PID: 2780)
Executable content was dropped or overwritten
- setup.exe (PID: 2240)
- DrvInst.exe (PID: 2792)
- haspdinst.exe (PID: 2728)
- DrvInst.exe (PID: 3460)
- vcredist_x86.exe (PID: 720)
- vcredist_x86.exe (PID: 2944)
- setup.exe (PID: 3864)
- MsiExec.exe (PID: 3524)
- msiexec.exe (PID: 2136)
- DrvInst.exe (PID: 2008)
Creates files in the driver directory
- DrvInst.exe (PID: 2792)
- DrvInst.exe (PID: 3460)
- DrvInst.exe (PID: 1620)
- haspdinst.exe (PID: 2728)
- DrvInst.exe (PID: 1532)
- DrvInst.exe (PID: 752)
- DrvInst.exe (PID: 2008)
Executed via COM
- DrvInst.exe (PID: 2792)
- DrvInst.exe (PID: 3460)
- DrvInst.exe (PID: 1620)
- DrvInst.exe (PID: 1532)
- DrvInst.exe (PID: 752)
- DrvInst.exe (PID: 2008)
Removes files from Windows directory
- DrvInst.exe (PID: 2792)
- DrvInst.exe (PID: 1620)
- DrvInst.exe (PID: 3460)
- DrvInst.exe (PID: 1532)
- haspdinst.exe (PID: 2728)
- DrvInst.exe (PID: 752)
- DrvInst.exe (PID: 2008)
Executed as Windows Service
- hasplms.exe (PID: 660)
- vssvc.exe (PID: 3480)
Creates files in the program directory
- hasplms.exe (PID: 660)
- vcredist_x86.exe (PID: 2944)
- MsiExec.exe (PID: 2780)
- BZ5503AnalysisHelper.exe (PID: 2028)
- BZ5503.exe (PID: 3768)
Uses NETSH.EXE for network configuration
- haspdinst.exe (PID: 2728)
Application launched itself
- vcredist_x86.exe (PID: 2944)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 2944)
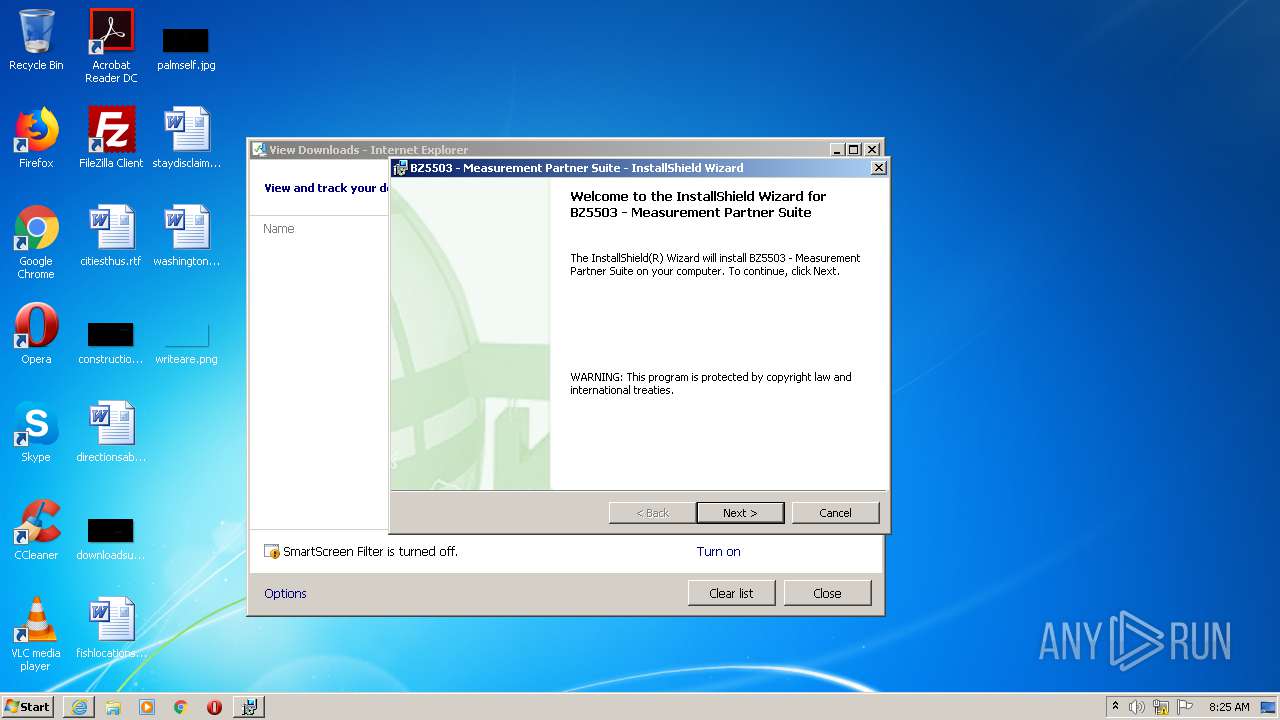
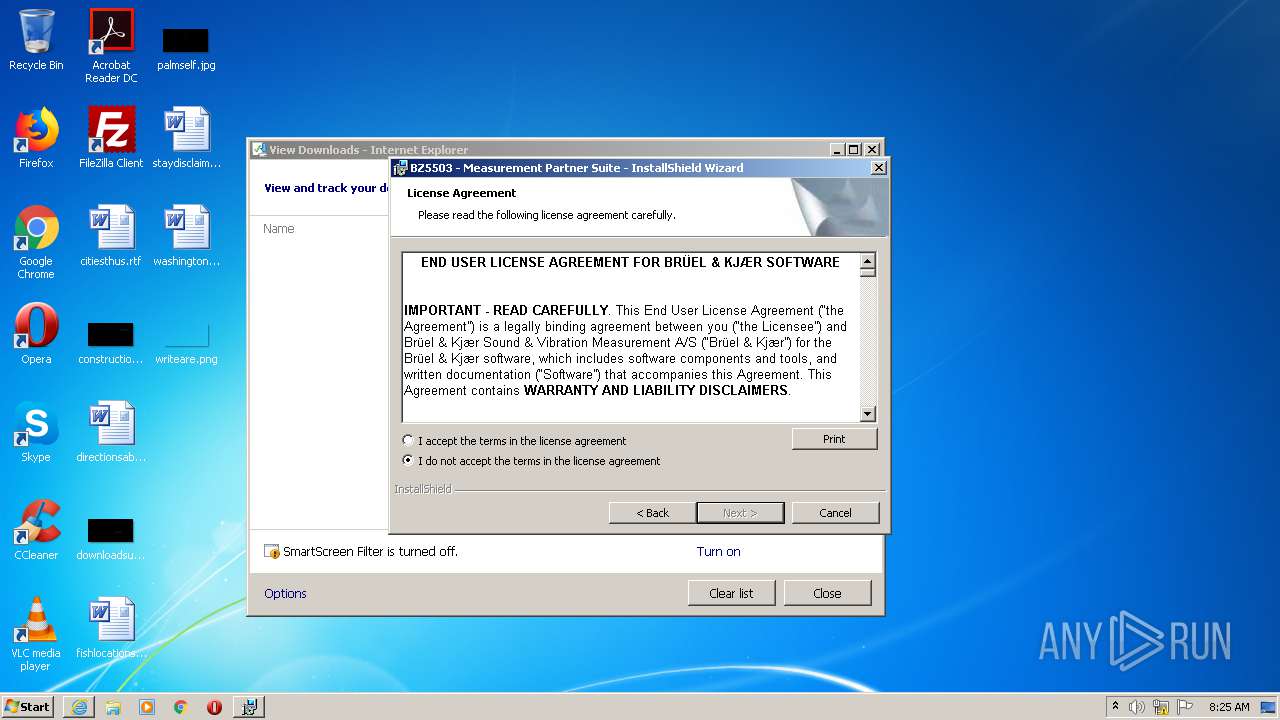
Starts Microsoft Installer
- setup.exe (PID: 3864)
- setup.exe (PID: 2240)
Adds / modifies Windows certificates
- MSIEXEC.EXE (PID: 2776)
- msiexec.exe (PID: 2136)
Modifies the open verb of a shell class
- msiexec.exe (PID: 2136)
Creates COM task schedule object
- MsiExec.exe (PID: 2780)
- msiexec.exe (PID: 2136)
Changes IE settings (feature browser emulation)
- BZ5503.exe (PID: 3768)
Searches for installed software
- vcredist_x86.exe (PID: 2944)
- vcredist_x86.exe (PID: 720)
Reads Environment values
- BZ5503.exe (PID: 3768)
Creates files in the user directory
- BZ5503.exe (PID: 3768)
INFO
Application launched itself
- iexplore.exe (PID: 1736)
- msiexec.exe (PID: 2136)
Reads Internet Cache Settings
- iexplore.exe (PID: 1736)
- iexplore.exe (PID: 1400)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1736)
Changes internet zones settings
- iexplore.exe (PID: 1736)
Creates files in the user directory
- iexplore.exe (PID: 1736)
Reads settings of System Certificates
- DrvInst.exe (PID: 3460)
- iexplore.exe (PID: 1736)
- msiexec.exe (PID: 2136)
Changes settings of System certificates
- DrvInst.exe (PID: 1532)
- DrvInst.exe (PID: 2792)
- iexplore.exe (PID: 1736)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 1532)
- DrvInst.exe (PID: 2792)
- iexplore.exe (PID: 1736)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3480)
Creates a software uninstall entry
- msiexec.exe (PID: 2136)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3168)
Searches for installed software
- msiexec.exe (PID: 2136)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2136)
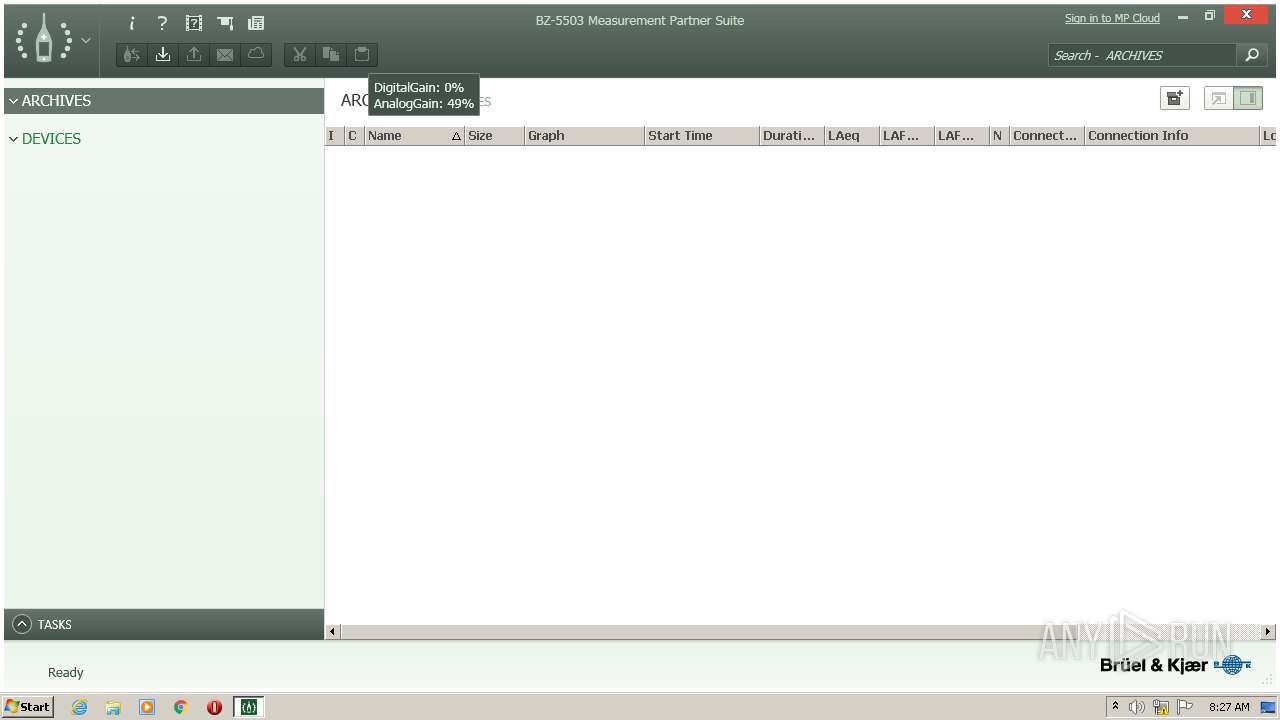
Manual execution by user
- BZ5503.exe (PID: 3768)
Creates files in the program directory
- msiexec.exe (PID: 2136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
29
Malicious processes
14
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | C:\Windows\system32\hasplms.exe -run | C:\Windows\system32\hasplms.exe | services.exe | ||||||||||||
User: SYSTEM Company: SafeNet Inc. Integrity Level: SYSTEM Description: Sentinel LDK License Manager Service Exit code: 0 Version: 15.0.1.36539 Modules
| |||||||||||||||
| 720 | "C:\Users\admin\AppData\Local\Temp\{C4AD3BD7-A2D1-47C2-9842-FA51EFC1DACA}\{BF2F04CD-3D1F-444e-8960-D08EBD285C3F}\vcredist_x86.exe" /q -burn.unelevated BurnPipe.{21E5AE46-79EF-413F-9C93-C5AA6CACFFDD} {2CEC5862-366D-40A2-9E53-E043D3EE0E77} 2944 | C:\Users\admin\AppData\Local\Temp\{C4AD3BD7-A2D1-47C2-9842-FA51EFC1DACA}\{BF2F04CD-3D1F-444e-8960-D08EBD285C3F}\vcredist_x86.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 752 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{665c5130-6171-6250-8eac-89153a525231}\usb2250.inf" "0" "6f7cb5407" "000005C4" "WinSta0\Default" "000005AC" "208" "C:\Users\admin\AppData\Local\Temp\{C1D45D9E-8001-4920-8D24-0AA800A0B2CB}" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1736 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1532 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{175ecdb9-ee61-03a7-0c74-b917e4e9f34b}\akspccard.inf" "0" "62250386f" "00000494" "WinSta0\Default" "000004B4" "208" "C:\Windows\system32\setup\aladdin" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{17a37038-3cf1-3e31-7861-273afd4dbe36}\aksusb.inf" "0" "686f4dfd7" "00000558" "WinSta0\Default" "000004BC" "208" "C:\Windows\system32\setup\aladdin\hasphl" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://update.bksv.com/BZ5503/Latest/setup.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1980 | 3768 | C:\Program Files\Bruel and Kjaer\ENV\BZ5503\UsbComm.exe | — | BZ5503.exe | |||||||||||
User: admin Company: Brüel & Kjær Sound & Vibration Measurement A/S Integrity Level: MEDIUM Description: Provides access to BkUsb hosts Exit code: 0 Version: 4.7.6.244 Modules
| |||||||||||||||
| 2008 | DrvInst.exe "2" "211" "ROOT\HAND-HELD_DEVICES\0000" "C:\Windows\INF\oem8.inf" "usb2250.inf:DeviceList:DriverInstall:10.1.0.0:*windrvr6" "62c2a9b4f" "000005C4" "000005E0" "000005E4" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | "DataFlow\BZ5503AnalysisHelper.exe" 1320 1324 | C:\Program Files\Bruel and Kjaer\ENV\BZ5503\DataFlow\BZ5503AnalysisHelper.exe | — | BZ5503.exe | |||||||||||
User: admin Company: Brüel & Kjær Sound & Vibration Measurement A/S Integrity Level: MEDIUM Description: BZ5503AnalysisHelper Exit code: 0 Version: 4.8.0.3 Modules
| |||||||||||||||
Total events
22 922
Read events
6 588
Write events
13 618
Delete events
2 716
Modification events
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4166877456 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30818039 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
496
Suspicious files
104
Text files
319
Unknown types
67
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAAB9.tmp | — | |
MD5:— | SHA256:— | |||
| 1400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAABA.tmp | — | |
MD5:— | SHA256:— | |||
| 1400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\setup[1].exe | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC408.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC409.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verC449.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\DT0T2ZY5.txt | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\L94TCZ6H.txt | — | |
MD5:— | SHA256:— | |||
| 1400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\setup.exe.o7ki43n.partial | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD6C2715196AEAE3D.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
19
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1400 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.49 Kb | whitelisted |
2944 | vcredist_x86.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
1044 | svchost.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAASWxwt68EQiA3cUAAAABJbE%3D | US | der | 1.79 Kb | whitelisted |
1736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2944 | vcredist_x86.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
1736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1044 | svchost.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | der | 813 b | whitelisted |
3768 | BZ5503.exe | GET | 200 | 212.97.131.161:80 | http://update.bksv.com/BZ5503/MPCloudConfig.xml | DK | text | 371 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1400 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
1736 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1044 | svchost.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
3768 | BZ5503.exe | 212.97.131.161:80 | update.bksv.com | Surftown A/S | DK | unknown |
2944 | vcredist_x86.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
1044 | svchost.exe | 104.18.25.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
1400 | iexplore.exe | 212.97.131.161:443 | update.bksv.com | Surftown A/S | DK | unknown |
1736 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
1736 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.bksv.com |
| unknown |
ocsp.globalsign.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
BZ5503.exe | UsbEnumerator.TheEnumerator.Connections has detected: 0 connections
|
BZ5503.exe | InstallPackageAdmin error: Exception: System.UnauthorizedAccessException: Access to the path 'C:\Program Files\Common Files\Bruel and Kjaer\SWP' is denied.
at System.IO.__Error.WinIOError(Int32 errorCode, String maybeFullPath)
at System.IO.Directory.InternalCreateDirectory(String fullPath, String path, Object dirSecurityObj, Boolean checkHost)
at System.IO.Directory.InternalCreateDirectoryHelper(String path, Boolean checkHost)
at System.IO.Directory.CreateDirectory(String path)
at BK.EnvOffice.InstallPackageManagement.Initialize(String mainFolder)
|
BZ5503.exe | ProjectPropertiesPanel
|
BZ5503.exe | MainWindow
|
BZ5503.exe | MainMenu Selected Tab: Language
|