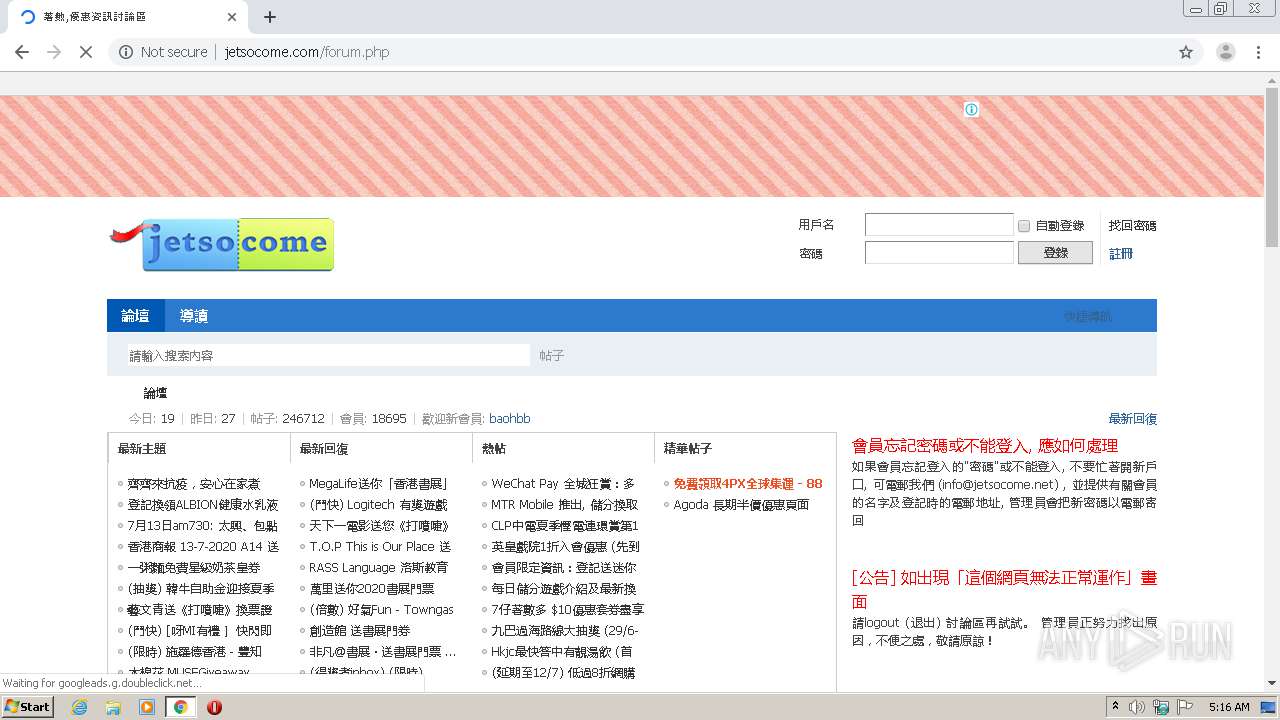
| URL: | https://jetsocome.com |
| Full analysis: | https://app.any.run/tasks/fe01ce90-c974-4539-afb6-842760a15ae3 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 04:15:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 76E5F04968F2305ABB78E858005BF500 |
| SHA1: | C1EB671E4437E6D148D1F101545B089672146220 |
| SHA256: | 80B4422F7261290B49D96BB4E75D1DC2AA8530610F50A8FAF8150C18E26BADE5 |
| SSDEEP: | 3:N8WT92n:21n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1580)
INFO
Application launched itself
- chrome.exe (PID: 1580)
Reads the hosts file
- chrome.exe (PID: 3976)
- chrome.exe (PID: 1580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1042122106813705662 --mojo-platform-channel-handle=4220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7365617495972101155 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18094142356594001097 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16790177036388948261 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13025381614527474003 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16756377488530881444 --mojo-platform-channel-handle=4312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6306102737612776948 --mojo-platform-channel-handle=4296 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12837942036024066657 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4428372244974564000 --mojo-platform-channel-handle=4236 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,9131650286852733878,16632401419469579957,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11095030066507488603 --mojo-platform-channel-handle=3864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
611
Read events
515
Write events
91
Delete events
5
Modification events
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1580-13239087348480750 |
Value: 259 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1580) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
98
Text files
172
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0BDFF5-62C.pma | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7a3d331c-2d04-4607-9df3-63d3cee19a23.tmp | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF1074b5.TMP | text | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF10761c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
194
TCP/UDP connections
109
DNS requests
61
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3976 | chrome.exe | GET | 301 | 104.199.180.119:80 | http://jetsocome.com/ | US | — | — | suspicious |
3976 | chrome.exe | GET | 204 | 172.217.22.99:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
3976 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
3976 | chrome.exe | GET | 200 | 104.199.180.119:80 | http://jetsocome.com/static/js/forum.js?p2x | US | text | 6.69 Kb | suspicious |
3976 | chrome.exe | GET | 200 | 104.199.180.119:80 | http://jetsocome.com/forum.php | US | html | 11.0 Kb | suspicious |
3976 | chrome.exe | GET | 200 | 104.199.180.119:80 | http://jetsocome.com/static/js/common.js?p2x | US | text | 17.3 Kb | suspicious |
3976 | chrome.exe | GET | 200 | 104.199.180.119:80 | http://jetsocome.com/data/cache/style_1_common.css?p2x | US | text | 14.8 Kb | suspicious |
3976 | chrome.exe | GET | 301 | 203.86.235.77:80 | http://ad.unimhk.com/show.php?id=njzkztixntgyzjex&sz=300 | HK | html | 269 b | unknown |
3976 | chrome.exe | GET | 200 | 104.199.180.119:80 | http://jetsocome.com/data/cache/style_1_forum_index.css?p2x | US | text | 1.15 Kb | suspicious |
3976 | chrome.exe | GET | 301 | 203.86.235.77:80 | http://ad.unimhk.com/show.php?id=njzkztixntgyzjex&sz=728 | HK | html | 269 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 172.217.18.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 172.217.18.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 209.85.226.73:80 | r4---sn-5hnekn7k.gvt1.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 162.255.119.204:443 | jetsocome.com | Namecheap, Inc. | US | suspicious |
3976 | chrome.exe | 172.217.22.3:443 | www.google.nl | Google Inc. | US | whitelisted |
3976 | chrome.exe | 104.199.180.119:80 | jetsocome.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jetsocome.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r4---sn-5hnekn7k.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r3---sn-5hne6nsd.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3976 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3976 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
3976 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |