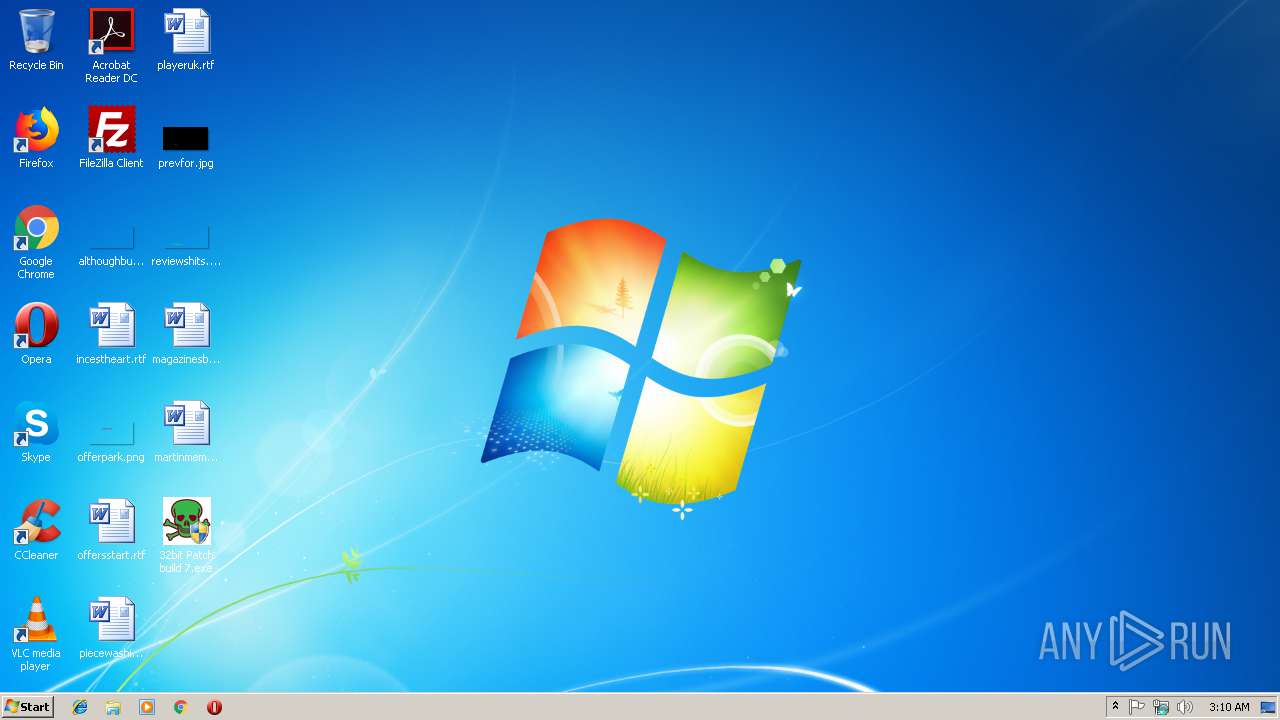
| File name: | 32bit Patch build 7.exe |
| Full analysis: | https://app.any.run/tasks/20529603-4ebc-43e9-956a-f569febe9f31 |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2018, 03:10:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C0B29BB6491D21C3492AFCE766BE503B |
| SHA1: | E1797204E35D00613031078A418DA903831D977D |
| SHA256: | 80AE207CFA64385211E3C4C5A9BAF44D808825B2BE8A1990FB68B376825597EB |
| SSDEEP: | 49152:OAI+lEX1Zkjp5zA2v6VoGDDLvwlScCC0j9V04PWT/h8WfGC7:OAI+zj0jVXLvcBc9CB/WWf17 |
MALICIOUS
No malicious indicators.SUSPICIOUS
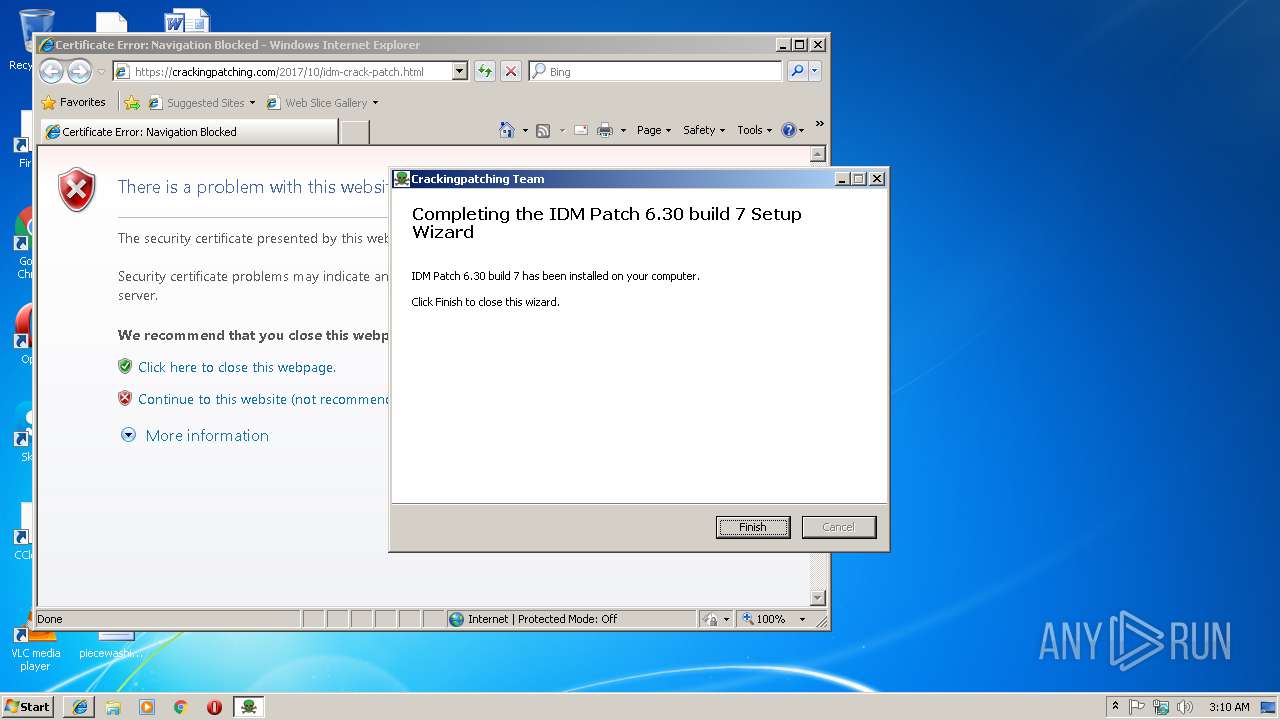
Executable content was dropped or overwritten
- 32bit Patch build 7.exe (PID: 2388)
Creates a software uninstall entry
- 32bit Patch build 7.exe (PID: 2388)
Creates files in the program directory
- 32bit Patch build 7.exe (PID: 2388)
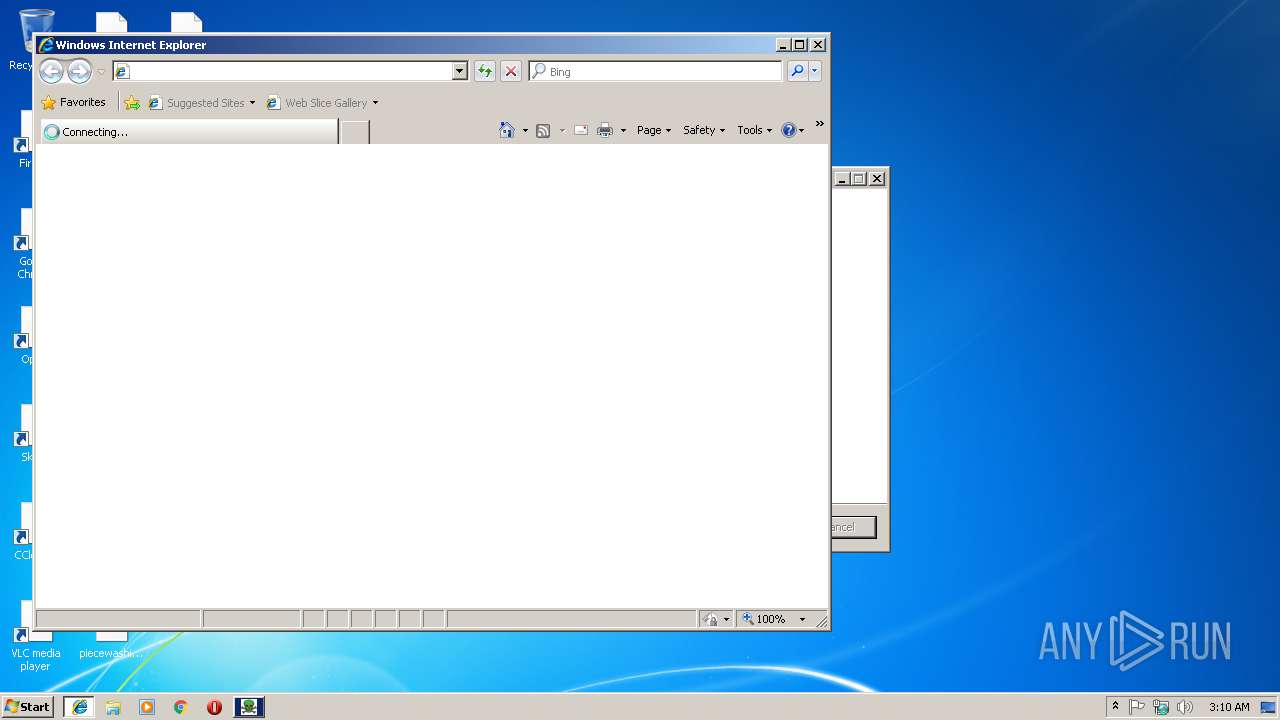
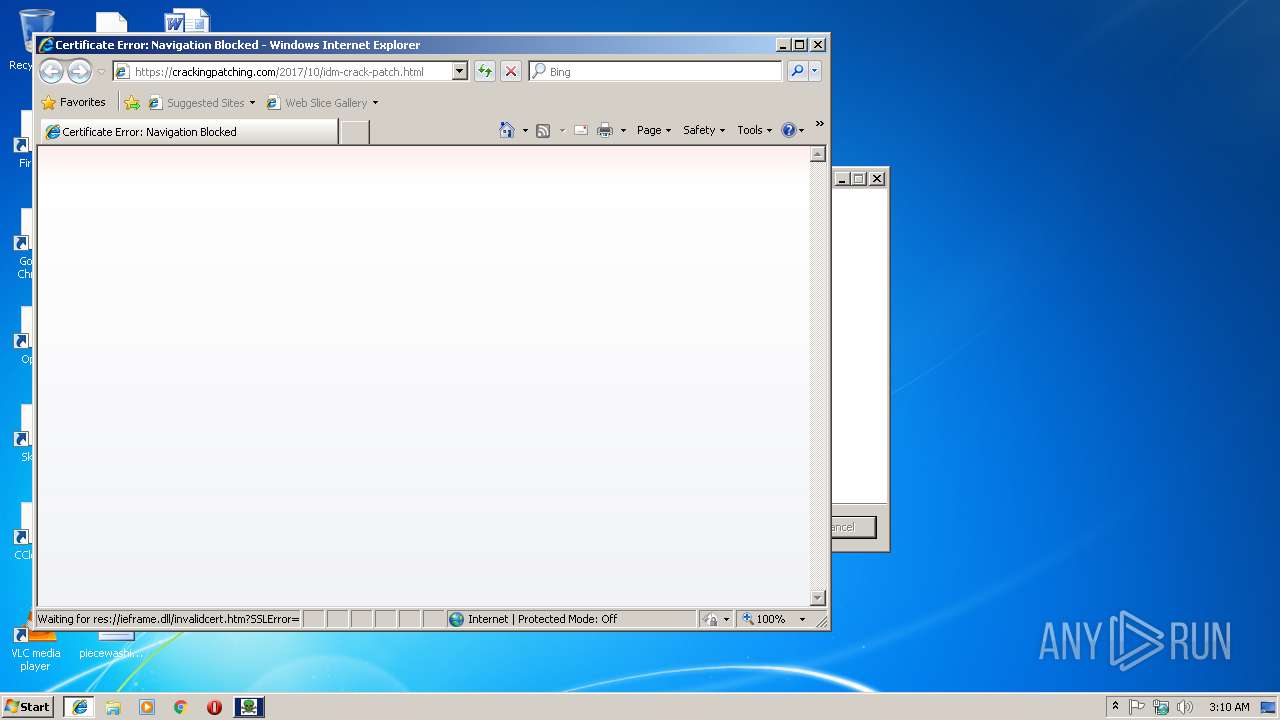
Starts Internet Explorer
- 32bit Patch build 7.exe (PID: 2388)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2444)
Reads internet explorer settings
- iexplore.exe (PID: 2444)
Changes internet zones settings
- iexplore.exe (PID: 4068)
Reads Internet Cache Settings
- iexplore.exe (PID: 2444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 314880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
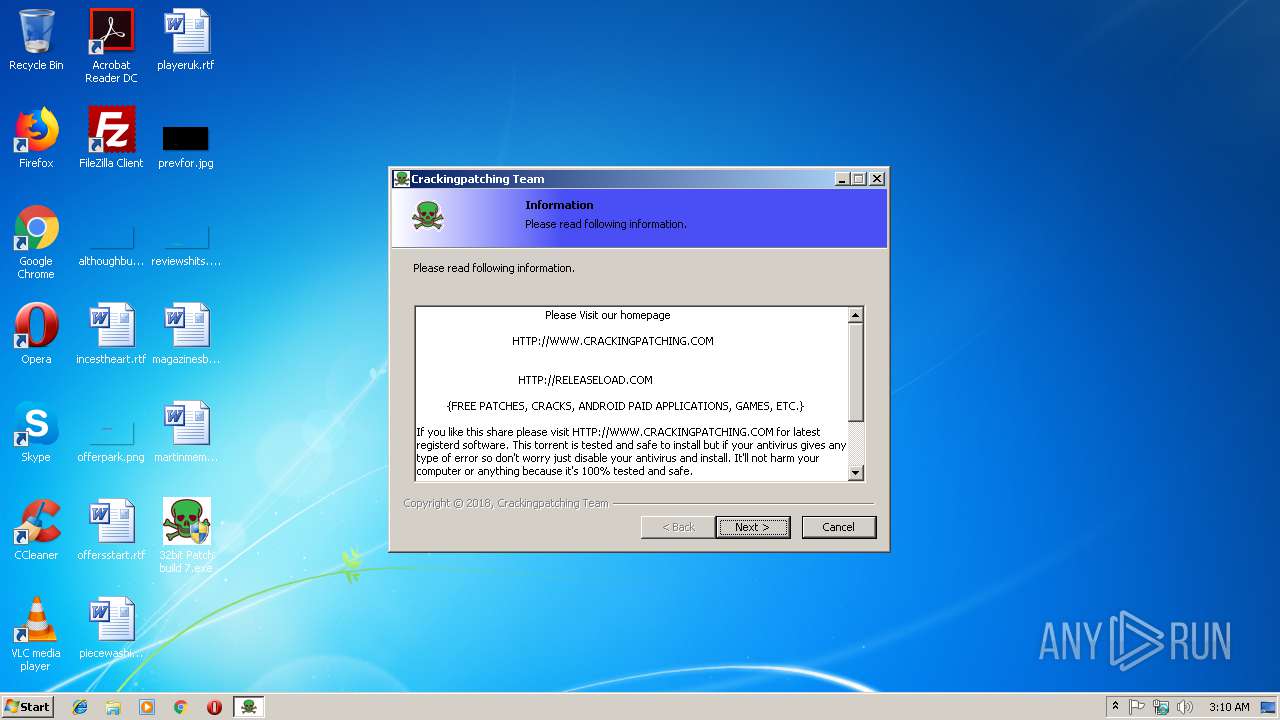
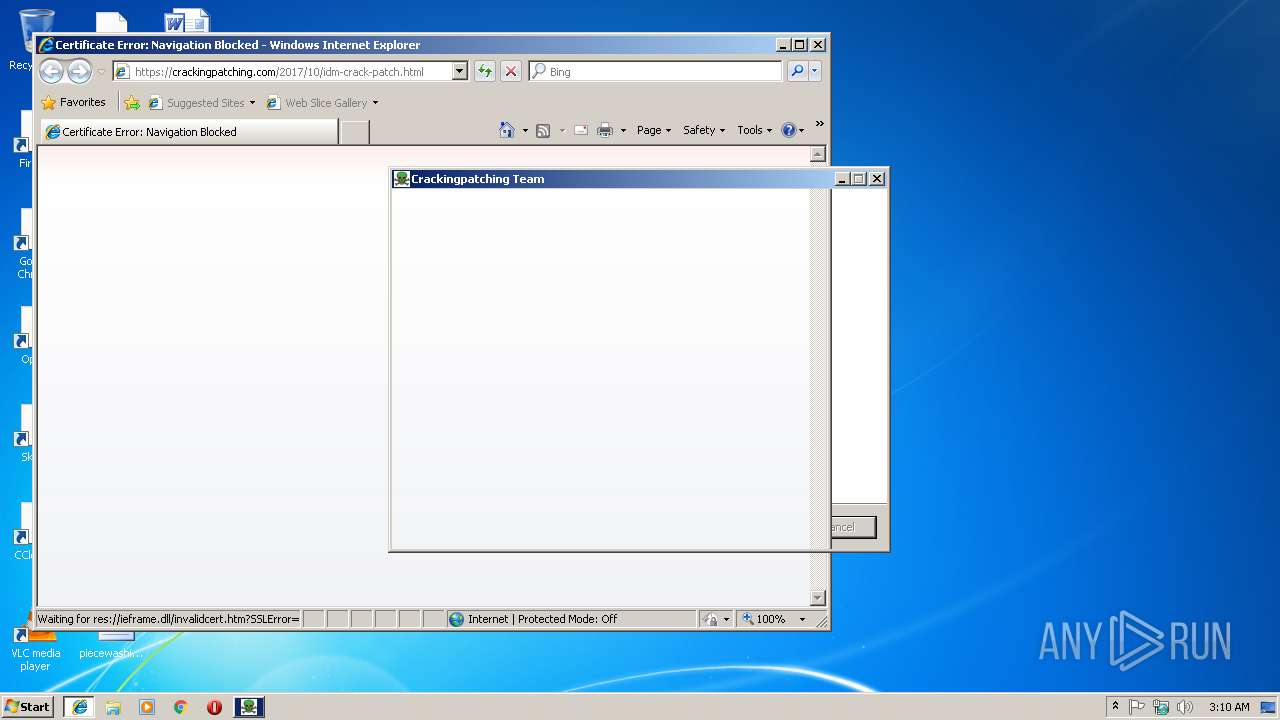
| CompanyName: | Crackingpatching.com Team |
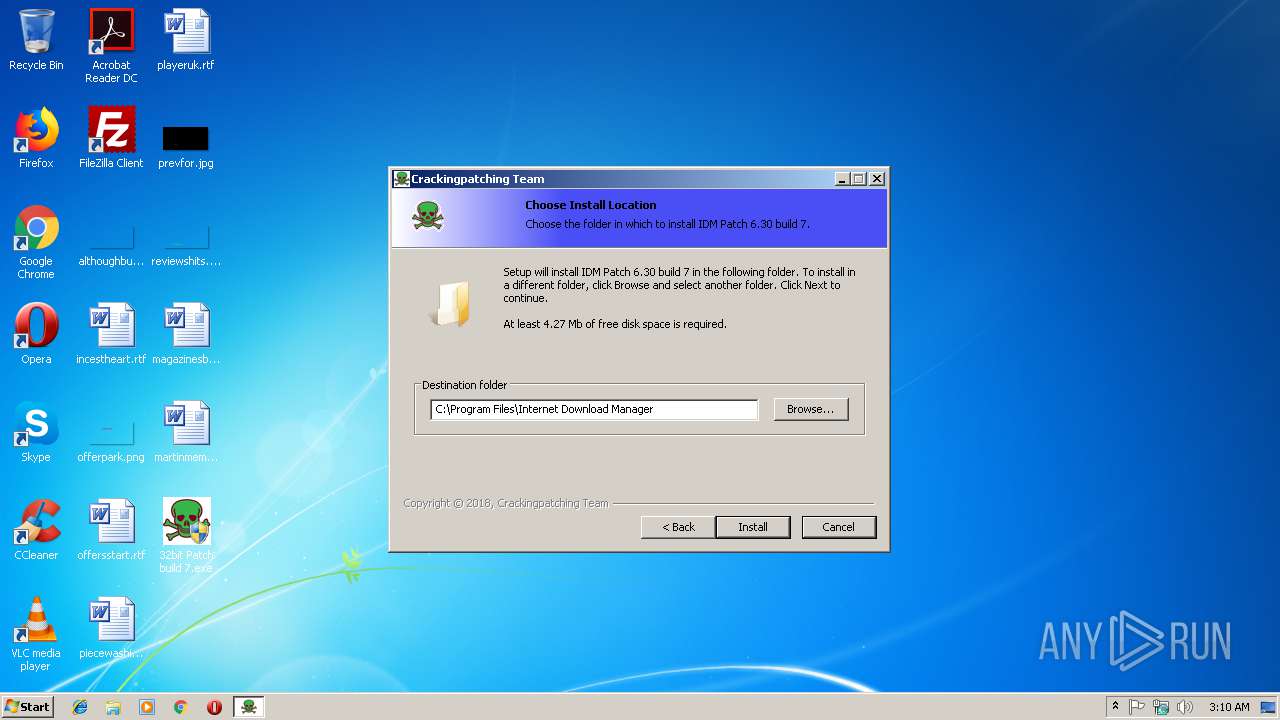
| FileDescription: | IDM Patch 6.30 build 7 6.30 build 7 Installation |
| FileVersion: | 6.30 build 7 |
| LegalCopyright: | Crackingpatching.com Team |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Crackingpatching.com Team |
| FileDescription: | IDM Patch 6.30 build 7 6.30 build 7 Installation |
| FileVersion: | 6.30 build 7 |
| LegalCopyright: | Crackingpatching.com Team |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00046F60 | 0x00047000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.14042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 5.24025 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.94231 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.73718 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.51902 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 4.05378 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.75922 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2388 | "C:\Users\admin\Desktop\32bit Patch build 7.exe" | C:\Users\admin\Desktop\32bit Patch build 7.exe | explorer.exe | ||||||||||||
User: admin Company: Crackingpatching.com Team Integrity Level: HIGH Description: IDM Patch 6.30 build 7 6.30 build 7 Installation Exit code: 0 Version: 6.30 build 7 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4068 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | "C:\Users\admin\Desktop\32bit Patch build 7.exe" | C:\Users\admin\Desktop\32bit Patch build 7.exe | — | explorer.exe | |||||||||||
User: admin Company: Crackingpatching.com Team Integrity Level: MEDIUM Description: IDM Patch 6.30 build 7 6.30 build 7 Installation Exit code: 3221226540 Version: 6.30 build 7 Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | 32bit Patch build 7.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
420
Read events
326
Write events
93
Delete events
1
Modification events
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2388) 32bit Patch build 7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | FName |
Value: Crackingpatching.com | | |||
| (PID) Process: | (2388) 32bit Patch build 7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | InstallStatus |
Value: 3 | |||
| (PID) Process: | (2388) 32bit Patch build 7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | LName |
Value: MrCracks.com | |||
| (PID) Process: | (2388) 32bit Patch build 7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | |
Value: info@tonec.com | |||
Executable files
3
Suspicious files
3
Text files
15
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | 32bit Patch build 7.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF76167EB468AA022D.TMP | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1A1A4E76069923E3.TMP | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA34F407C63E4716E.TMP | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\{A0F1DD74-033B-11E9-834A-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2388 | 32bit Patch build 7.exe | C:\Program Files\Internet Download Manager\IDMan.exe | executable | |
MD5:— | SHA256:— | |||
| 2388 | 32bit Patch build 7.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD5BF3F5113925540.TMP | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{A0F1DD73-033B-11E9-834A-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2388 | 32bit Patch build 7.exe | C:\Program Files\Internet Download Manager\IDM Patch Uninstaller 6.30 build 7.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4068 | iexplore.exe | GET | 404 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
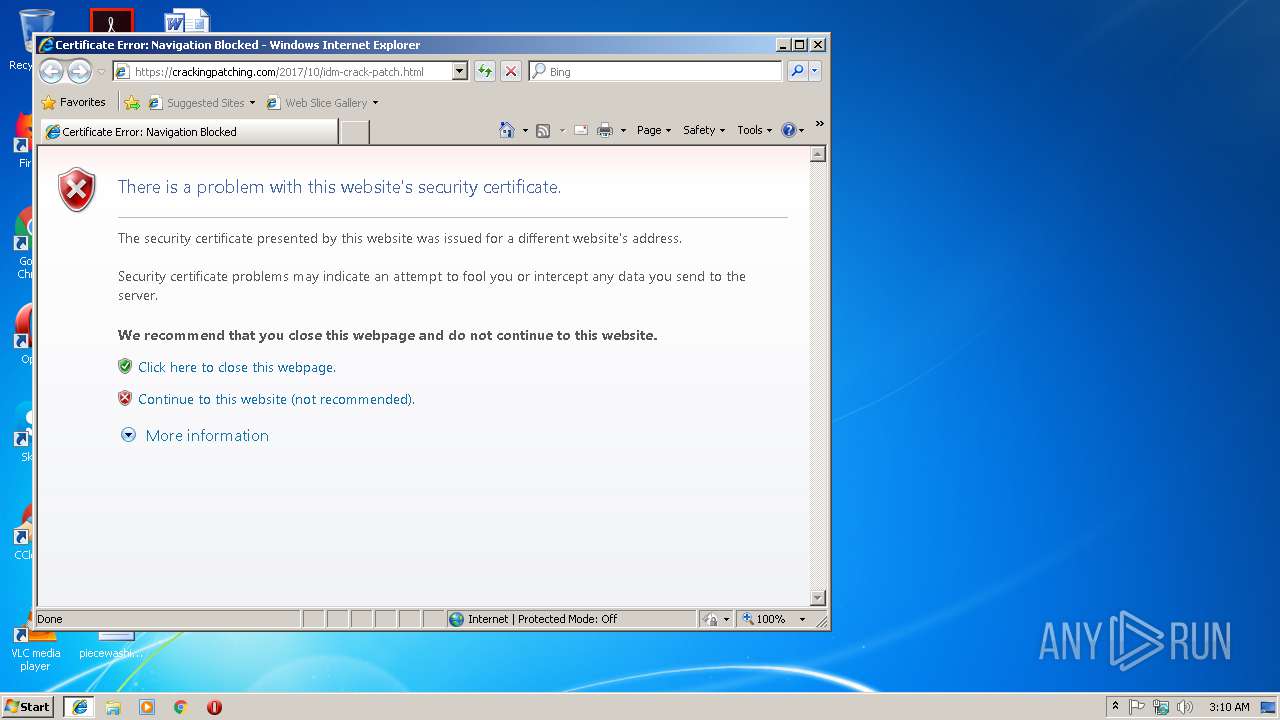
2444 | iexplore.exe | 104.18.56.24:443 | crackingpatching.com | Cloudflare Inc | US | shared |
4068 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crackingpatching.com |
| malicious |
www.bing.com |
| whitelisted |