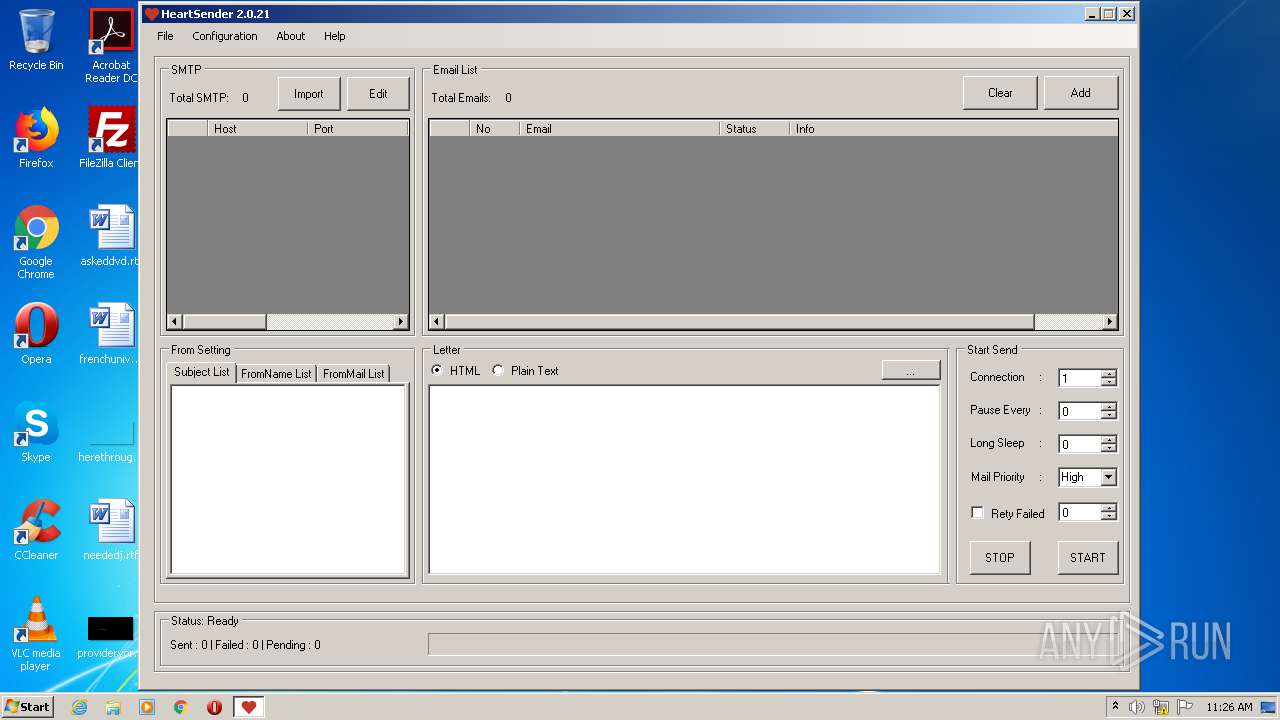
| File name: | HeartSender v2 Cracked.exe |
| Full analysis: | https://app.any.run/tasks/0465eef7-d4b1-40c2-9761-9b08418431b2 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2020, 11:25:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CFF460D66907C039C3915DD0A72001C2 |
| SHA1: | 9CA0C67270C024067F779CEA7BAC31822C06729B |
| SHA256: | 80A672691C06A4E55F23281503D1E1835D4995C1560C261E52620B8715D7A61E |
| SSDEEP: | 98304:+MCWa1mWbND/MgDb8N2ACfBDKJZ7E7FcxKCr9:cD/JDb8N2CMGoCr9 |
MALICIOUS
Application was dropped or rewritten from another process
- SVCHOST.EXE (PID: 2816)
- HEARTSENDERV2.EXE (PID: 1920)
- svchost.exe (PID: 3756)
Changes the autorun value in the registry
- SVCHOST.EXE (PID: 2816)
SUSPICIOUS
Executable content was dropped or overwritten
- HeartSender v2 Cracked.exe (PID: 2732)
- SVCHOST.EXE (PID: 2816)
Creates files in the user directory
- SVCHOST.EXE (PID: 2816)
Starts CMD.EXE for commands execution
- SVCHOST.EXE (PID: 2816)
Creates executable files which already exist in Windows
- HeartSender v2 Cracked.exe (PID: 2732)
- SVCHOST.EXE (PID: 2816)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:07:03 11:05:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 31232 |
| InitializedDataSize: | 3732480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7a0058 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jul-2011 09:05:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 03-Jul-2011 09:05:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
Bx | 0x00001000 | 0x00007842 | 0x00004800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96905 |
\x9e1 | 0x00009000 | 0x0000319E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.78984 |
\x84\x1a | 0x0000D000 | 0x00001A84 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.37957 |
\xf0\x9f8 | 0x0000F000 | 0x00389FF0 | 0x0010AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98709 |
\xaa\x13 | 0x00399000 | 0x000013AA | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.43907 |
.idata | 0x0039B000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.1679 |
.rsrc | 0x0039C000 | 0x0001A200 | 0x0001A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.89318 |
.themida | 0x003B7000 | 0x003E8000 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.loadcon | 0x0079F000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.620972 |
.boot | 0x007A0000 | 0x0025D000 | 0x0025D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95561 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.87282 | 6527 | UNKNOWN | English - United States | RT_ICON |
2 | 2.21648 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 2.3503 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 2.42639 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 2.54147 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 2.83085 | 1128 | UNKNOWN | English - United States | RT_ICON |
128 | 2.79908 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
SHELL32.dll |
kernel32.dll |
Total processes
39
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | cmd /c ""C:\Users\admin\AppData\Local\Temp\tmp25B.tmp.bat"" | C:\Windows\system32\cmd.exe | — | SVCHOST.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\Temp\HEARTSENDERV2.EXE" | C:\Users\admin\AppData\Local\Temp\HEARTSENDERV2.EXE | — | HeartSender v2 Cracked.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: HeartSender20200121 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Local\Temp\HeartSender v2 Cracked.exe" | C:\Users\admin\AppData\Local\Temp\HeartSender v2 Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\AppData\Local\Temp\SVCHOST.EXE" | C:\Users\admin\AppData\Local\Temp\SVCHOST.EXE | HeartSender v2 Cracked.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 Modules
| |||||||||||||||
| 3048 | timeout 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 Modules
| |||||||||||||||
Total events
441
Read events
400
Write events
41
Delete events
0
Modification events
| (PID) Process: | (2732) HeartSender v2 Cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2732) HeartSender v2 Cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2816) SVCHOST.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2816) SVCHOST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | svchost |
Value: "C:\Users\admin\AppData\Roaming\svchost.exe" | |||
| (PID) Process: | (3756) svchost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3756) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
6
Suspicious files
0
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\EASENDMAIL.DLL | executable | |
MD5:— | SHA256:— | |||
| 2732 | HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HEARTSENDER.PDB | pdb | |
MD5:— | SHA256:— | |||
| 2732 | HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HEARTSENDERV2.EXE | executable | |
MD5:— | SHA256:— | |||
| 2816 | SVCHOST.EXE | C:\Users\admin\AppData\Roaming\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 2816 | SVCHOST.EXE | C:\Users\admin\AppData\Local\Temp\tmp25B.tmp.bat | text | |
MD5:— | SHA256:— | |||
| 2732 | HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\SVCHOST.EXE | executable | |
MD5:— | SHA256:— | |||
| 2732 | HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HEARTSENDER.EXE.CONFIG | xml | |
MD5:15C8C4BA1AA574C0C00FD45BB9CCE1AB | SHA256:F82338E8E9C746B5D95CD2CCC7BF94DD5DE2B9B8982FFFDDF2118E475DE50E15 | |||
| 2732 | HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HTMLAGILITYPACK.DLL | executable | |
MD5:97458FB37FCBEA19B16704474E0BB747 | SHA256:EB6841497CAFAB1AAC432B09F4979997FA3314D4828BE15CDBD37F621BA38EAC | |||
| 2732 | HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\NEWTONSOFT.JSON.DLL | executable | |
MD5:6815034209687816D8CF401877EC8133 | SHA256:7F912B28A07C226E0BE3ACFB2F57F050538ABA0100FA1F0BF2C39F1A1F1DA814 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
4
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | svchost.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
3756 | svchost.exe | 41.250.185.181:66 | ghr4b4.ddns.net | MT-MPLS | MA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
ghr4b4.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1060 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1060 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
Process | Message |
|---|---|
HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\EASENDMAIL.DLL |
HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HEARTSENDER.PDB |
HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HEARTSENDER.EXE.CONFIG |
HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HEARTSENDERV2.EXE |
HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\NEWTONSOFT.JSON.DLL |
HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\HTMLAGILITYPACK.DLL |
HeartSender v2 Cracked.exe | C:\Users\admin\AppData\Local\Temp\SVCHOST.EXE |