| File name: | asdf.exe |
| Full analysis: | https://app.any.run/tasks/daf1ed08-cf89-437f-ab49-f9653ddf1a62 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 22:35:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E80AED3B66C6DED20262D38D060BF920 |
| SHA1: | BEF2DB1FAB0DAFF7F72E61325638FF7263D83BEC |
| SHA256: | 8096BDAE9763CB3A7FCF900636D8971F433DE76CA97DBA6F7DB0718EF61155D4 |
| SSDEEP: | 6144:3sNZ+1TMNzqewJd1Qi7plGXsO1hcqApdfaLP2TCv0mS:qYMFJwJ9fKsGc3pdCLeTCv0h |
MALICIOUS
Loads dropped or rewritten executable
- asdf.exe (PID: 3008)
- asdf.exe (PID: 2956)
- iexplore.exe (PID: 3048)
- iexplore.exe (PID: 2492)
- svchost.exe (PID: 848)
SUSPICIOUS
Executable content was dropped or overwritten
- asdf.exe (PID: 3008)
Application launched itself
- asdf.exe (PID: 3008)
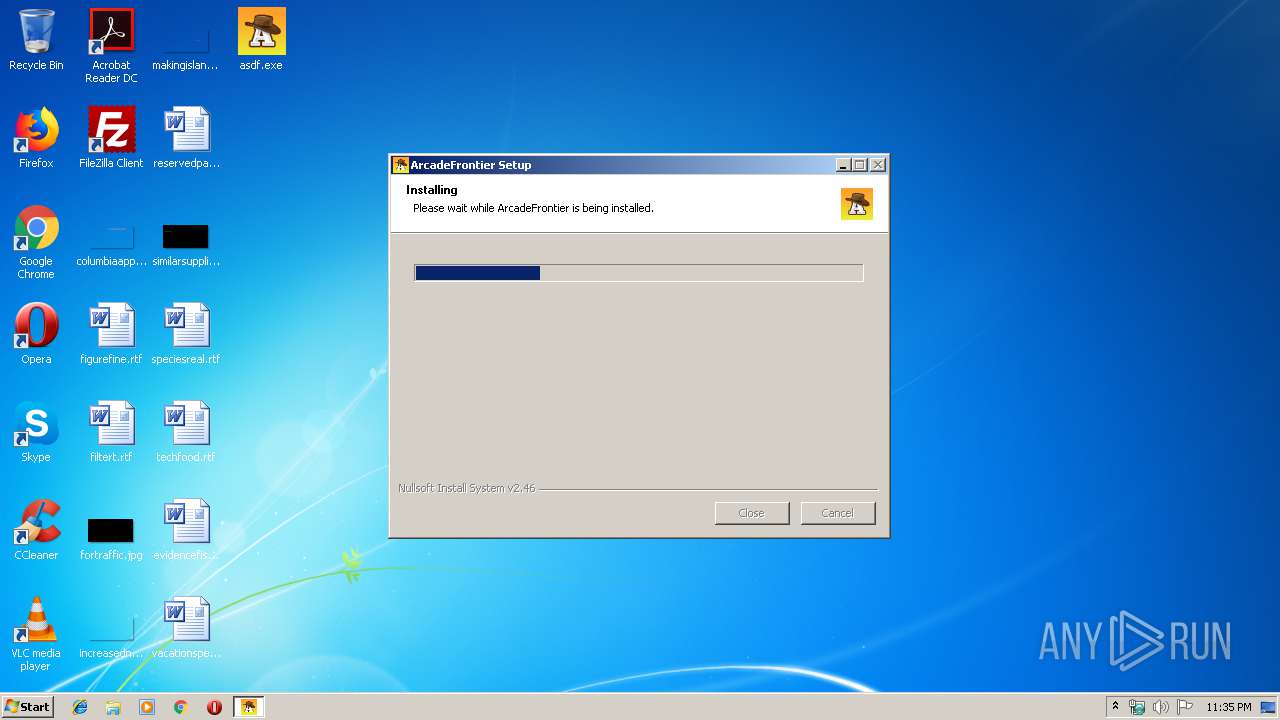
Creates a software uninstall entry
- asdf.exe (PID: 3008)
Creates COM task schedule object
- asdf.exe (PID: 3008)
Starts Internet Explorer
- asdf.exe (PID: 3008)
INFO
Application launched itself
- iexplore.exe (PID: 2492)
Changes internet zones settings
- iexplore.exe (PID: 2492)
Creates files in the user directory
- iexplore.exe (PID: 3048)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3088)
Reads Internet Cache Settings
- iexplore.exe (PID: 3048)
- iexplore.exe (PID: 2492)
Reads internet explorer settings
- iexplore.exe (PID: 3048)
Reads settings of System Certificates
- iexplore.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.4801.0 |
| ProductVersionNumber: | 4.0.4801.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | ArcadeFrontier Installer |
| FileVersion: | 4.0.4801.0 |
| LegalCopyright: | Copyright (C) 2015 |
| ProductName: | ArcadeFrontier Installer |
| ProductVersion: | 4.0.4801.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| FileDescription: | ArcadeFrontier Installer |
| FileVersion: | 4.0.4801.0 |
| LegalCopyright: | Copyright (C) 2015 |
| ProductName: | ArcadeFrontier Installer |
| ProductVersion: | 4.0.4801.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00032000 | 0x000041BB | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.61425 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04103 | 1807 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88018 | 21 | UNKNOWN | English - United States | RT_RCDATA |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
39
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | asdf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\Desktop\asdf.exe" /A | C:\Users\admin\Desktop\asdf.exe | asdf.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ArcadeFrontier Installer Exit code: 0 Version: 4.0.4801.0 Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\Desktop\asdf.exe" | C:\Users\admin\Desktop\asdf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ArcadeFrontier Installer Exit code: 0 Version: 4.0.4801.0 Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2492 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3088 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
686
Read events
573
Write events
112
Delete events
1
Modification events
| (PID) Process: | (3008) asdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3008) asdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2956) asdf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{3F5E4F4E-9EC1-4DAB-81DA-CB72DC9F57C6} |
| Operation: | write | Name: | |
Value: ArcadeFrontier | |||
| (PID) Process: | (2956) asdf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{3F5E4F4E-9EC1-4DAB-81DA-CB72DC9F57C6} |
| Operation: | write | Name: | NoExplorer |
Value: 1 | |||
| (PID) Process: | (848) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 2 | |||
| (PID) Process: | (848) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
| (PID) Process: | (3008) asdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\ArcadeFrontier |
| Operation: | write | Name: | DisplayName |
Value: ArcadeFrontier | |||
| (PID) Process: | (3008) asdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\ArcadeFrontier |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\ArcadeFrontier\unarfront.exe" | |||
| (PID) Process: | (3008) asdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\ArcadeFrontier |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Users\admin\AppData\Local\ArcadeFrontier\unarfront.exe" | |||
| (PID) Process: | (3008) asdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\ArcadeFrontier |
| Operation: | write | Name: | SupportLink |
Value: http://www.arcadefrontier.com | |||
Executable files
5
Suspicious files
0
Text files
15
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | asdf.exe | C:\Users\admin\AppData\Local\Temp\nsg17C.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 2956 | asdf.exe | C:\Users\admin\AppData\Local\Temp\nsg17B.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | asdf.exe | C:\Users\admin\AppData\Local\Temp\nszFCC8.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
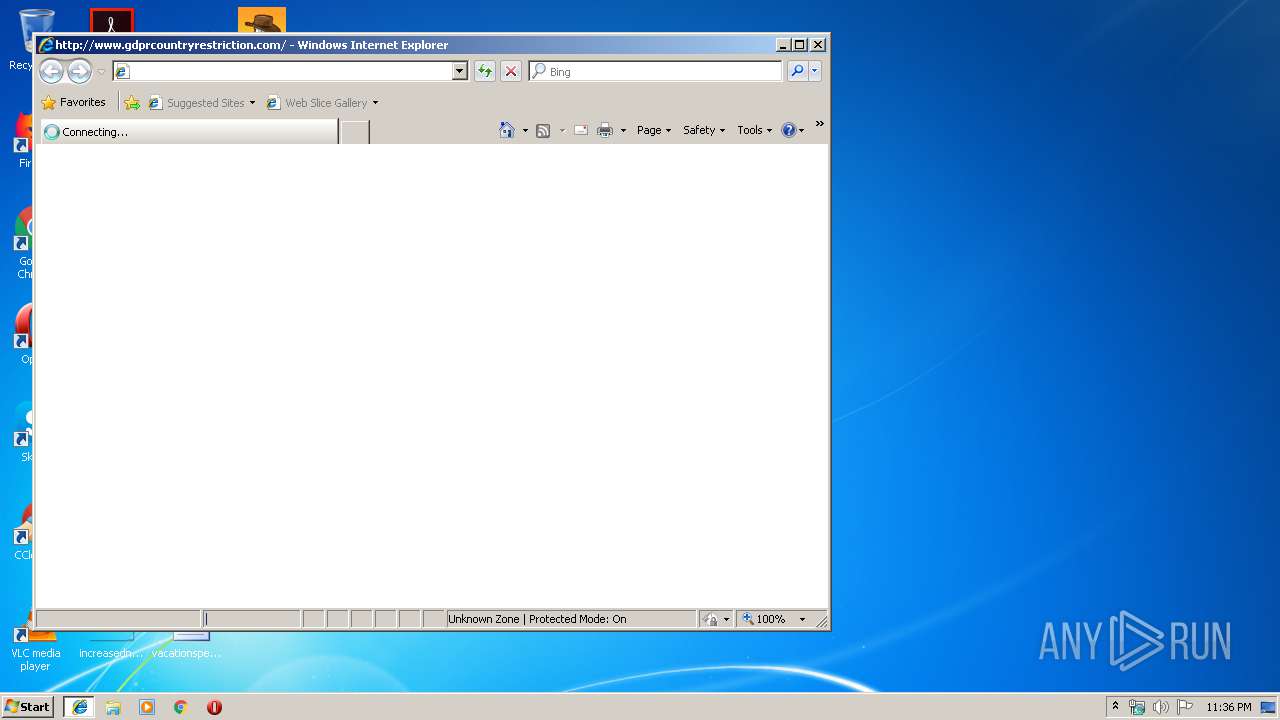
| 3048 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\524936BW\gdprcountryrestriction_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3008 | asdf.exe | C:\Users\admin\AppData\Local\ArcadeFrontier\arfront.exe | executable | |
MD5:— | SHA256:— | |||
| 3008 | asdf.exe | C:\Users\admin\AppData\Local\ArcadeFrontier\unarfront.exe | executable | |
MD5:— | SHA256:— | |||
| 3008 | asdf.exe | C:\Users\admin\AppData\Local\ArcadeFrontier\arfront.dll | executable | |
MD5:— | SHA256:— | |||
| 3048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@gdprcountryrestriction[2].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
6
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
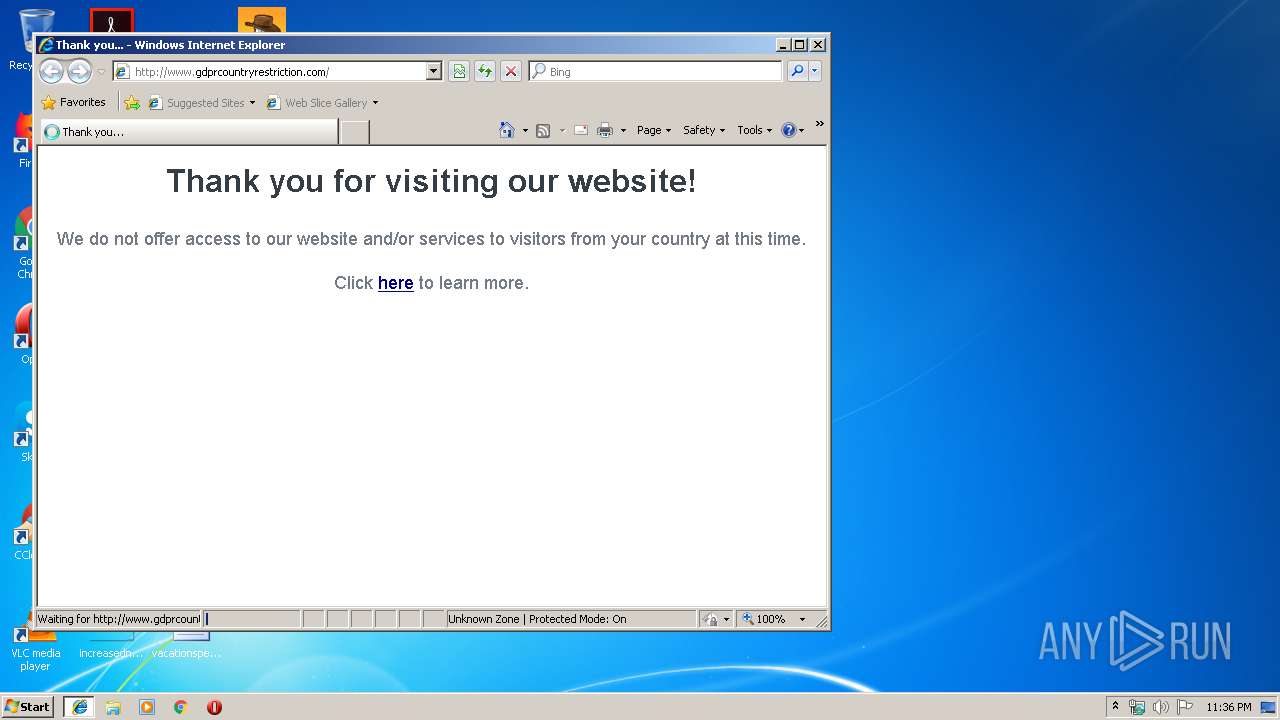
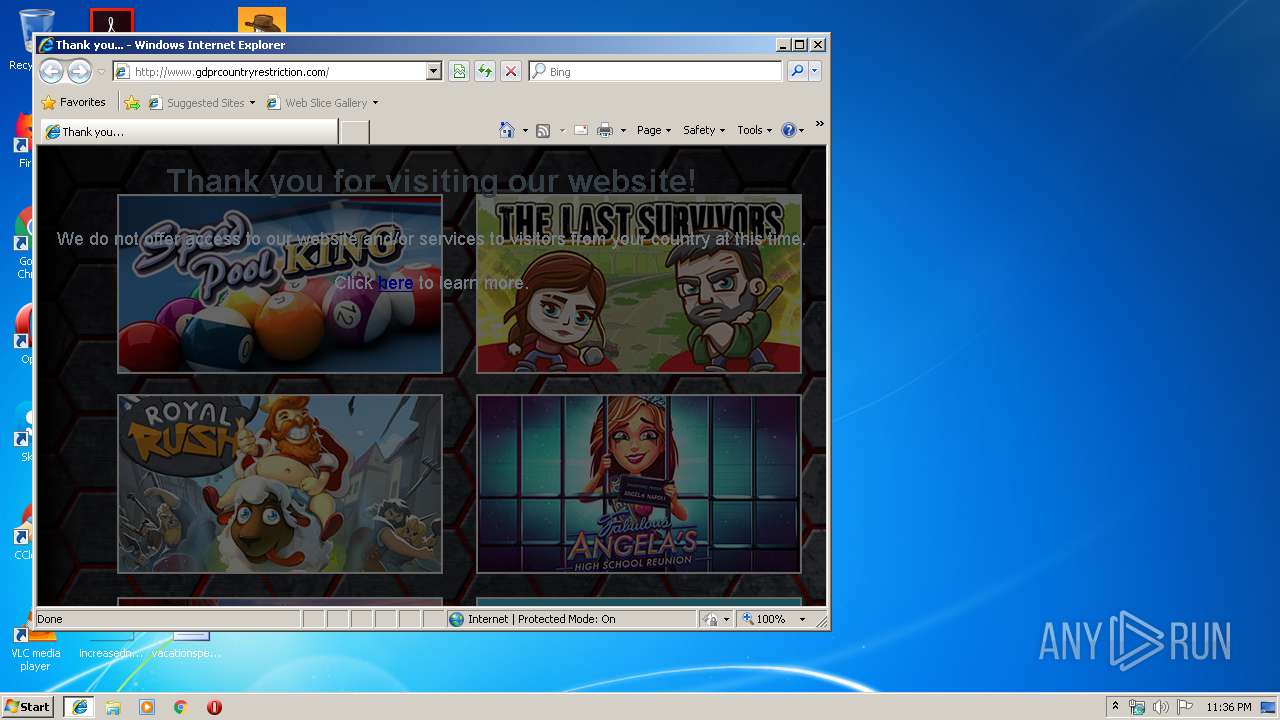
3048 | iexplore.exe | GET | 302 | 74.120.19.104:80 | http://e1.arcadefrontier.com/front/ithankyou?s=s%2F%2Ft78LN5rTm7uLE%2BuLBzODPxMHB1v%2FMyA | US | — | — | malicious |
3048 | iexplore.exe | GET | 200 | 74.120.19.115:80 | http://www.gdprcountryrestriction.com/ | US | html | 1.10 Kb | whitelisted |
3048 | iexplore.exe | POST | 302 | 74.120.19.16:80 | http://cf.arcadefrontier.com/bcf | US | — | — | unknown |
2492 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3048 | iexplore.exe | GET | 200 | 74.120.19.115:80 | http://www.gdprcountryrestriction.com/img/bg-photo.jpg | US | image | 671 Kb | whitelisted |
3048 | iexplore.exe | POST | 200 | 74.120.19.16:80 | http://cf.arcadefrontier.com/bcf | US | binary | 265 b | unknown |
2492 | iexplore.exe | GET | 404 | 74.120.19.115:80 | http://www.gdprcountryrestriction.com/favicon.ico | US | html | 209 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2492 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3048 | iexplore.exe | 74.120.19.104:80 | e1.arcadefrontier.com | — | US | malicious |
3048 | iexplore.exe | 74.120.19.115:80 | www.gdprcountryrestriction.com | — | US | malicious |
3048 | iexplore.exe | 216.58.207.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3048 | iexplore.exe | 74.120.19.16:80 | cf.arcadefrontier.com | — | US | unknown |
3048 | iexplore.exe | 216.58.205.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2492 | iexplore.exe | 74.120.19.115:80 | www.gdprcountryrestriction.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
e1.arcadefrontier.com |
| malicious |
www.gdprcountryrestriction.com |
| whitelisted |
cf.arcadefrontier.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3048 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |