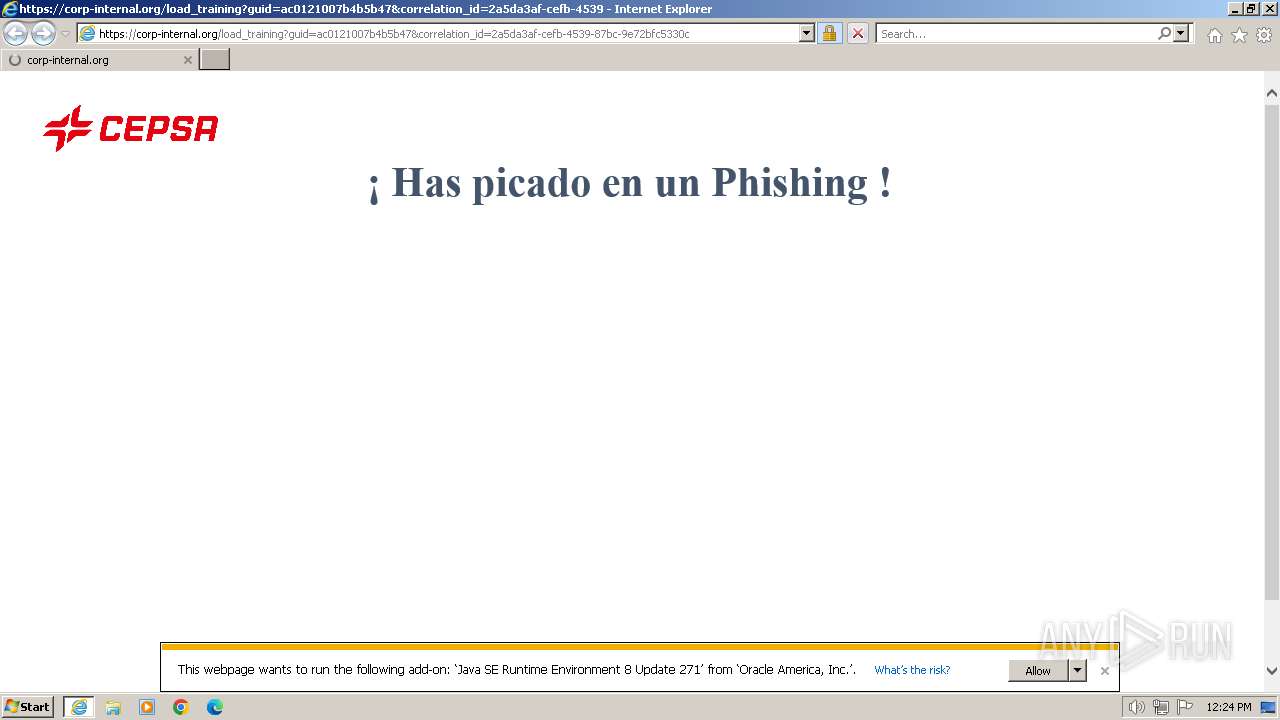
| URL: | https://corp-internal.org/370121052b4b5b85?l=121 |
| Full analysis: | https://app.any.run/tasks/80fc300f-7e58-4d84-8182-317c9a03ea27 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2024, 11:23:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B3CEF4261B6B168CEFCDA506535560EF |
| SHA1: | F81855A1BD4CE11A4DF9CB4D835A0F965DA2DC1E |
| SHA256: | 806C62A45CECB6B1371B927432B1B8988C34633AC605A624C874956B78E86F35 |
| SSDEEP: | 3:N8XyMtKImU3SpTXUn:2CMt1C5En |
MALICIOUS
No malicious indicators.SUSPICIOUS
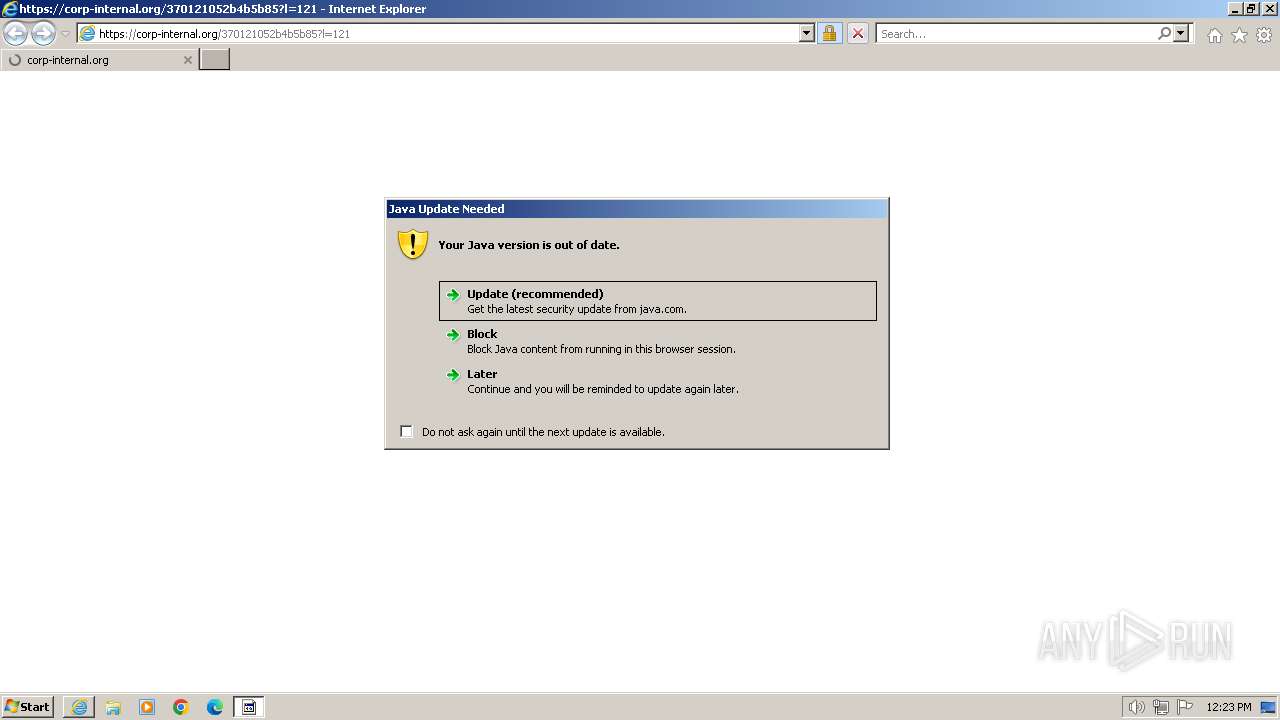
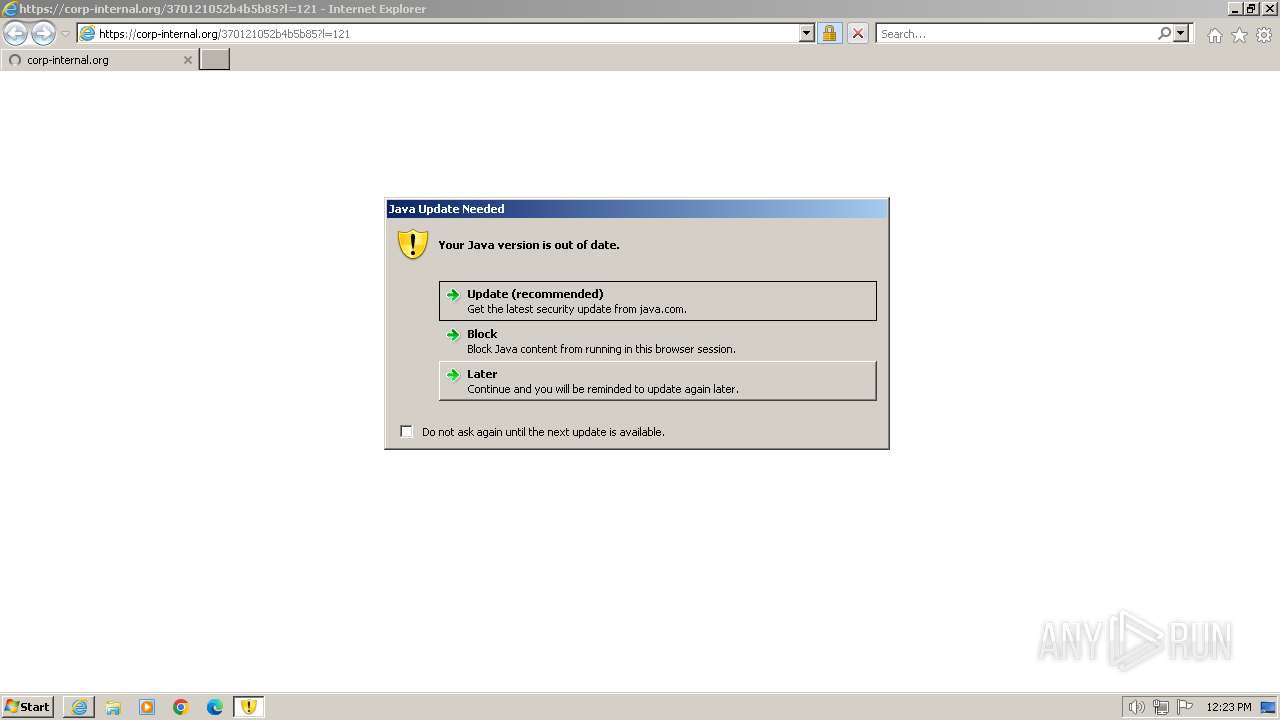
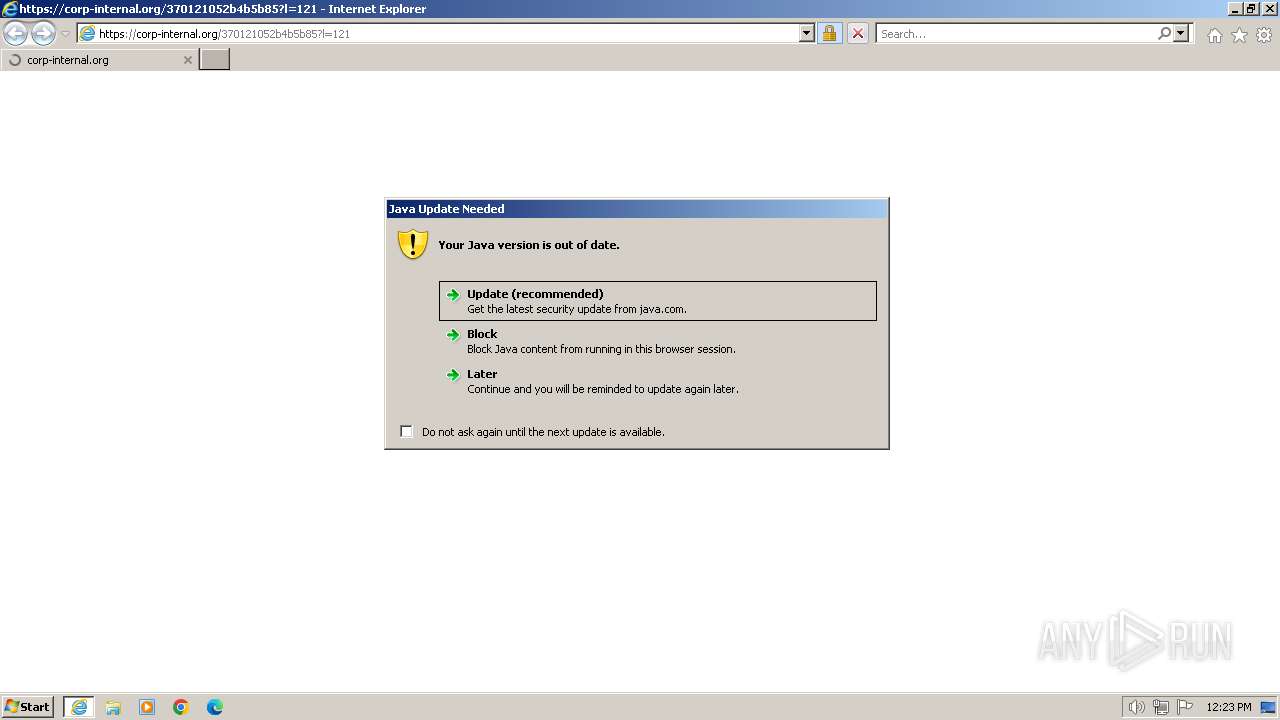
Checks for Java to be installed
- jp2launcher.exe (PID: 2028)
- javaw.exe (PID: 1560)
- javaw.exe (PID: 1900)
- javaw.exe (PID: 3404)
INFO
Checks supported languages
- jp2launcher.exe (PID: 2028)
- javaw.exe (PID: 1560)
- javaw.exe (PID: 3404)
- javaw.exe (PID: 1900)
Creates files in the program directory
- javaw.exe (PID: 1560)
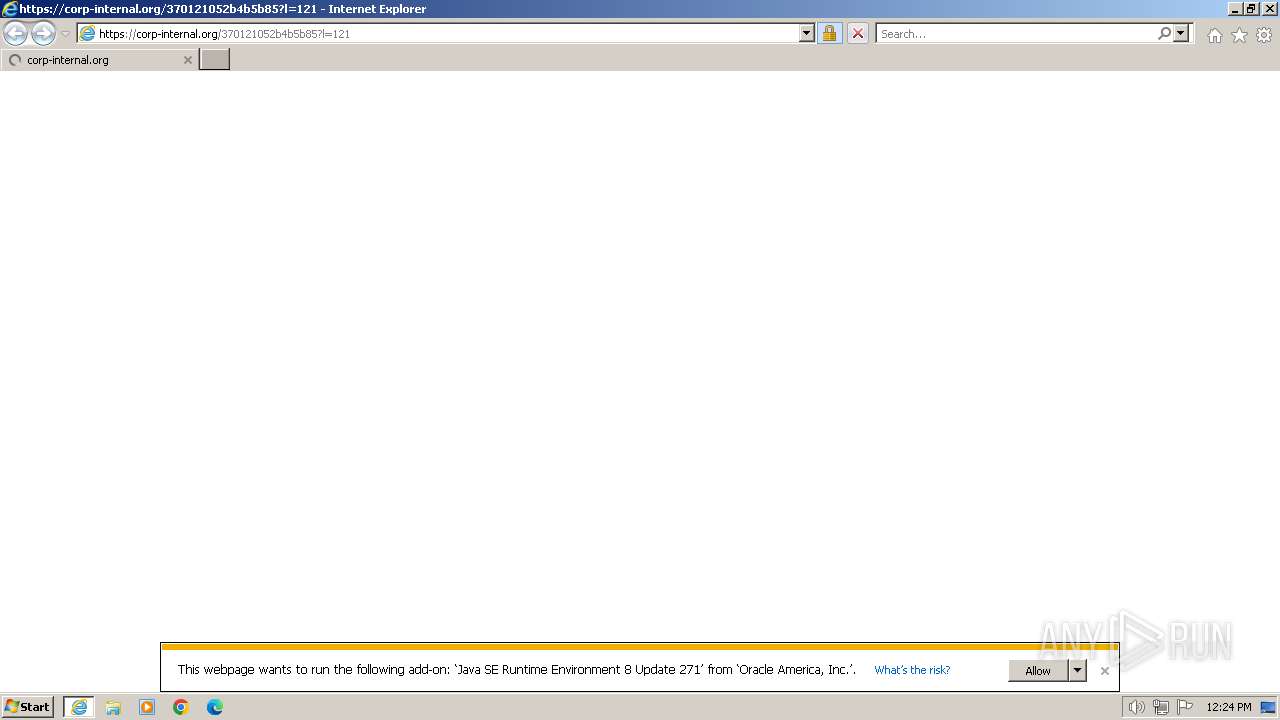
Application launched itself
- iexplore.exe (PID: 668)
Connects to unusual port
- iexplore.exe (PID: 4032)
Create files in a temporary directory
- javaw.exe (PID: 1560)
- javaw.exe (PID: 3404)
- javaw.exe (PID: 1900)
Reads the computer name
- javaw.exe (PID: 1560)
- javaw.exe (PID: 3404)
- javaw.exe (PID: 1900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
8
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://corp-internal.org/370121052b4b5b85?l=121" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1556 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.271.2" "later" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.271.2" "false" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2028 | "C:\PROGRA~1\Java\JRE18~1.0_2\bin\jp2launcher.exe" -sjed | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 3 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1713871437" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3468 | "C:\PROGRA~1\Java\JRE18~1.0_2\bin\jp2launcher.exe" -sjed | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 4032 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:668 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
23 879
Read events
23 564
Write events
271
Delete events
44
Modification events
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31102320 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31102320 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
24
Text files
31
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | der | |
MD5:FE37A80D8FFB3CE3173BF845AF6CD17F | SHA256:813A81EA0FB9D80F996DEDAAA9633E55FF4590737D6B9CB1F40DBD1870B5DFDB | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:140A68900D38C3D06DABE24403BF4133 | SHA256:268D9ECD97FC250C3F5D1A2DB1CD7FC3E5E34C12885967F270724685526CEAD4 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_056B48C93C4964C2E64C0A8958238656 | binary | |
MD5:4EB460CB701003D67A90DA4B232A39BA | SHA256:0B9759AA4C001480831AEEB08622384F1681A08F1CC6A8D66A73030D16AEC1B8 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\all[1].js | text | |
MD5:097F74FC8F861ECE148262A652AB806A | SHA256:39B4614F1C87CF0CFD1BC3375642E95825CB2018E0318A36AAD766DDB5A8CBE9 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery.min[1].js | text | |
MD5:397754BA49E9E0CF4E7C190DA78DDA05 | SHA256:C12F6098E641AACA96C60215800F18F5671039AECF812217FAB3C0D152F6ADB4 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D03E46CD585BBE111C712E6577BC5F07_95A4562DEA3FE449C14A6BEBAD97C213 | der | |
MD5:D9E89F325AD3E6457F08804B198F60C1 | SHA256:8B6586E6A18A4D95D64B8EE0405428CE3DFED1E88FCB72234C5BA00266BC5007 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\370121052b4b5b85[1].htm | html | |
MD5:1137A9A052E91C34FBDD1D7440501D20 | SHA256:FAA09C30C9BD825BF495F470B9EF86CC13F4F67120D1628AB393E559A9EC7609 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D03E46CD585BBE111C712E6577BC5F07_95A4562DEA3FE449C14A6BEBAD97C213 | binary | |
MD5:A0528515D2636F59AACCDE5C0AD6F3E3 | SHA256:B32756605B00084D24ADDB866FB1B30B38DCDC20E7C5A76EBABD2A3F4C32D4E0 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F53EB4E574DE32C870452087D92DBEBB_E1DE7EF66A6BFBDCEC2C2201A88D6C4A | der | |
MD5:9CC9C27ACA1747D7AD919268ECB39FB9 | SHA256:47C7F3F06AA8DCA00C8F1A5B1ECBE92C9ED351DA620FD9F7059DF5C0602AACE0 | |||
| 4032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:7C59AA5A3676ACC80240CCD7F2AB81E1 | SHA256:E995B888629F836748D1BCC46C94AB59B394BD4AD38D2AD03623F874F79DBBDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
49
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4032 | iexplore.exe | GET | 304 | 23.72.90.85:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?501143bdbf2f2bd6 | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 304 | 23.72.90.76:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4ebced21f09f2fa3 | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 108.138.2.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 18.245.65.219:80 | http://ocsp.r2m02.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRmbQtwnInkvkvr7BNFR%2BS2lTYPjAQUwDFSzVpQw4J8dHHOy%2Bmc%2BXrrguICEAfcfLZXtHO4pvegXkFpLJo%3D | unknown | — | — | unknown |
668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 13.224.191.223:80 | http://ocsp.r2m01.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBShdVEFnSEQ0gG5CBtzM48cPMe9XwQUgbgOY4qJEhjl%2Bjs7UJWf5uWQE4UCEAiHUOT9tNzU9ktfJpImBiA%3D | unknown | — | — | unknown |
4032 | iexplore.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEGg7fbRphwNp%2FPUBs%2BwIzLA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | iexplore.exe | 34.248.78.201:443 | corp-internal.org | AMAZON-02 | IE | unknown |
4032 | iexplore.exe | 23.72.90.76:80 | ctldl.windowsupdate.com | Akamai International B.V. | US | unknown |
4032 | iexplore.exe | 23.72.90.85:80 | ctldl.windowsupdate.com | Akamai International B.V. | US | unknown |
4032 | iexplore.exe | 108.138.2.195:80 | o.ss2.us | AMAZON-02 | US | unknown |
4032 | iexplore.exe | 18.245.39.64:80 | ocsp.rootg2.amazontrust.com | — | US | unknown |
4032 | iexplore.exe | 18.245.65.219:80 | ocsp.r2m02.amazontrust.com | — | US | unknown |
4032 | iexplore.exe | 34.248.78.201:49153 | corp-internal.org | AMAZON-02 | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
corp-internal.org |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.r2m02.amazontrust.com |
| whitelisted |
tslp.s3.amazonaws.com |
| shared |
java.com |
| whitelisted |
ocsp.r2m01.amazontrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |