| File name: | invite.ics |
| Full analysis: | https://app.any.run/tasks/ceebaf21-cc08-4763-8420-9d7cfacdb863 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 00:47:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/calendar |
| File info: | vCalendar calendar file |
| MD5: | 5CEE767927F6BC797F7C2AD793D14C56 |
| SHA1: | 7AB816B3C7BBD4A7F46BA4AF67419ADEF2D811C1 |
| SHA256: | 805EF85E66D9CE218F443CF90A2B4BE4BAE944D39EF8B7A109C77AE43B7EA96B |
| SSDEEP: | 24:EsrfEniN0gAzsS4h10JkDd431Q0JkDtxpj2A7+XpA170B1fn5ICkJhp:EgfozpsSe1Iz31QIQxpqpK74f6dJhp |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 668)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 668)
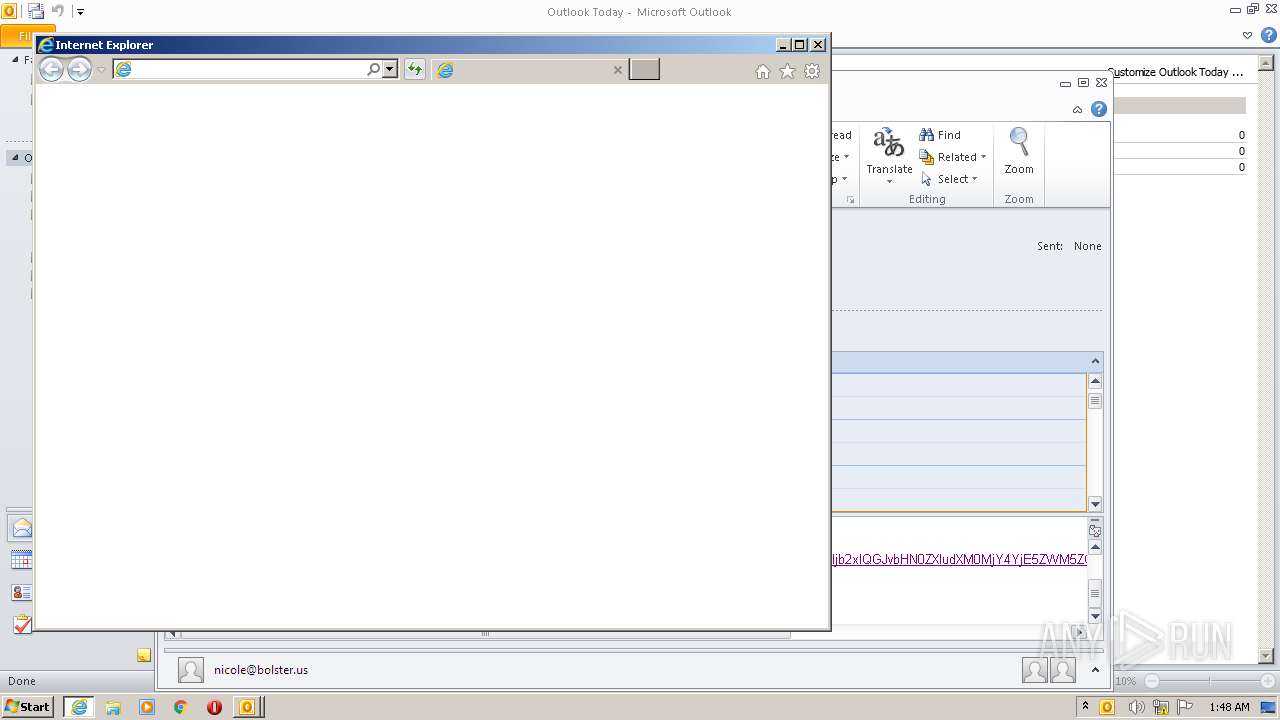
Starts Internet Explorer
- OUTLOOK.EXE (PID: 668)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 668)
- iexplore.exe (PID: 1492)
- iexplore.exe (PID: 324)
Application launched itself
- iexplore.exe (PID: 1492)
Reads internet explorer settings
- OUTLOOK.EXE (PID: 668)
- iexplore.exe (PID: 324)
Changes internet zones settings
- iexplore.exe (PID: 1492)
Reads settings of System Certificates
- iexplore.exe (PID: 324)
- iexplore.exe (PID: 1492)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1492)
Changes settings of System certificates
- iexplore.exe (PID: 1492)
Creates files in the user directory
- iexplore.exe (PID: 1492)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ics/vcs | | | iCalendar - vCalendar (100) |
|---|
EXIF
VCard
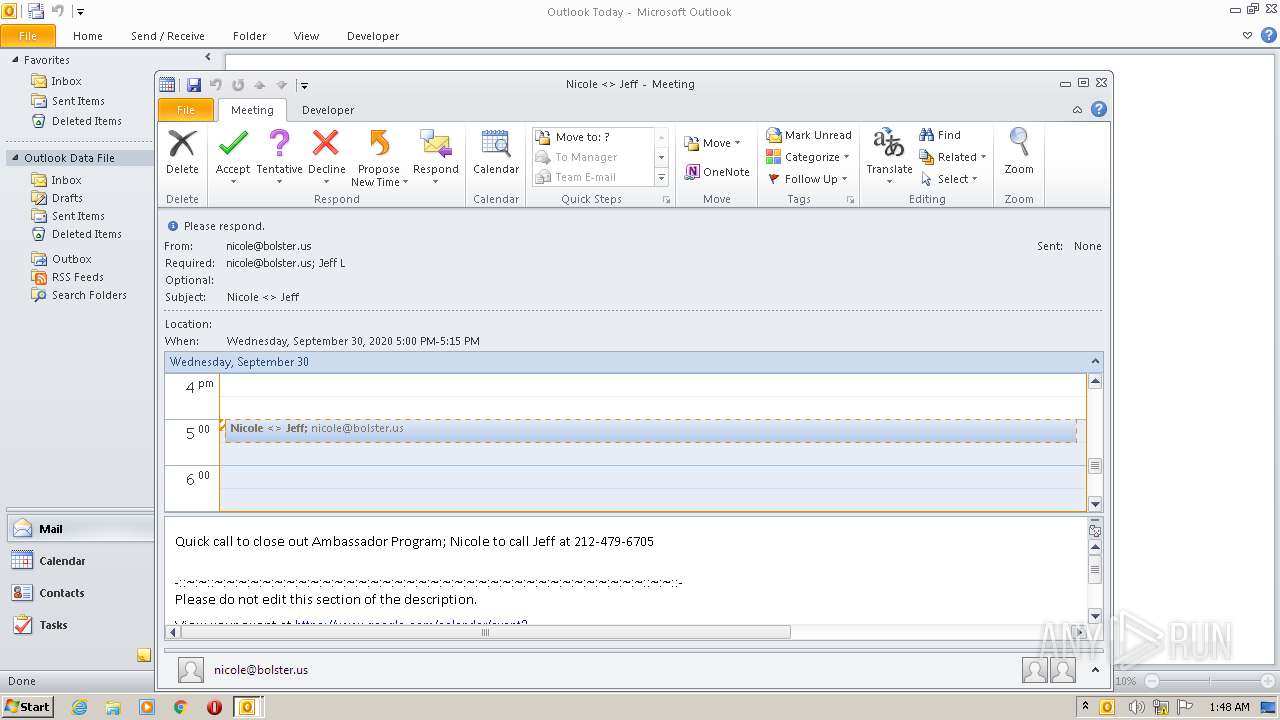
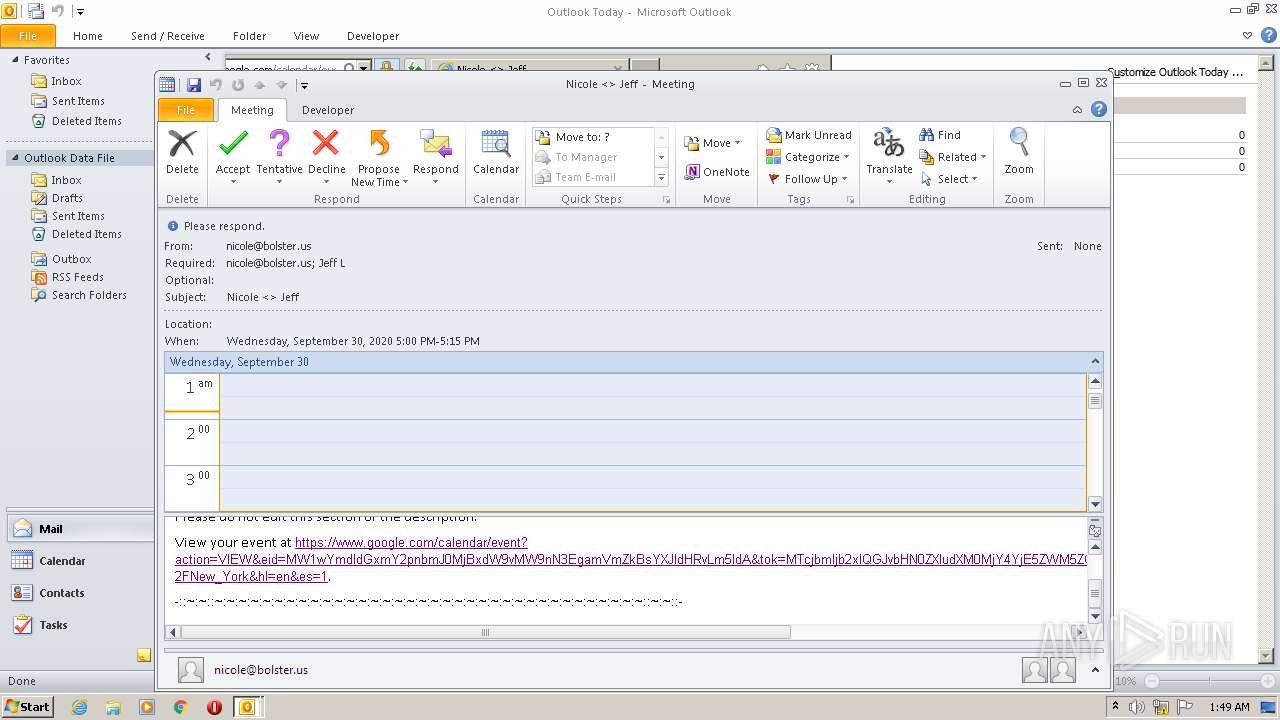
| Software: | -//Google Inc//Google Calendar 70.9054//EN |
|---|---|
| VCalendarVersion: | 2 |
| CalendarScale: | GREGORIAN |
| Method: | REQUEST |
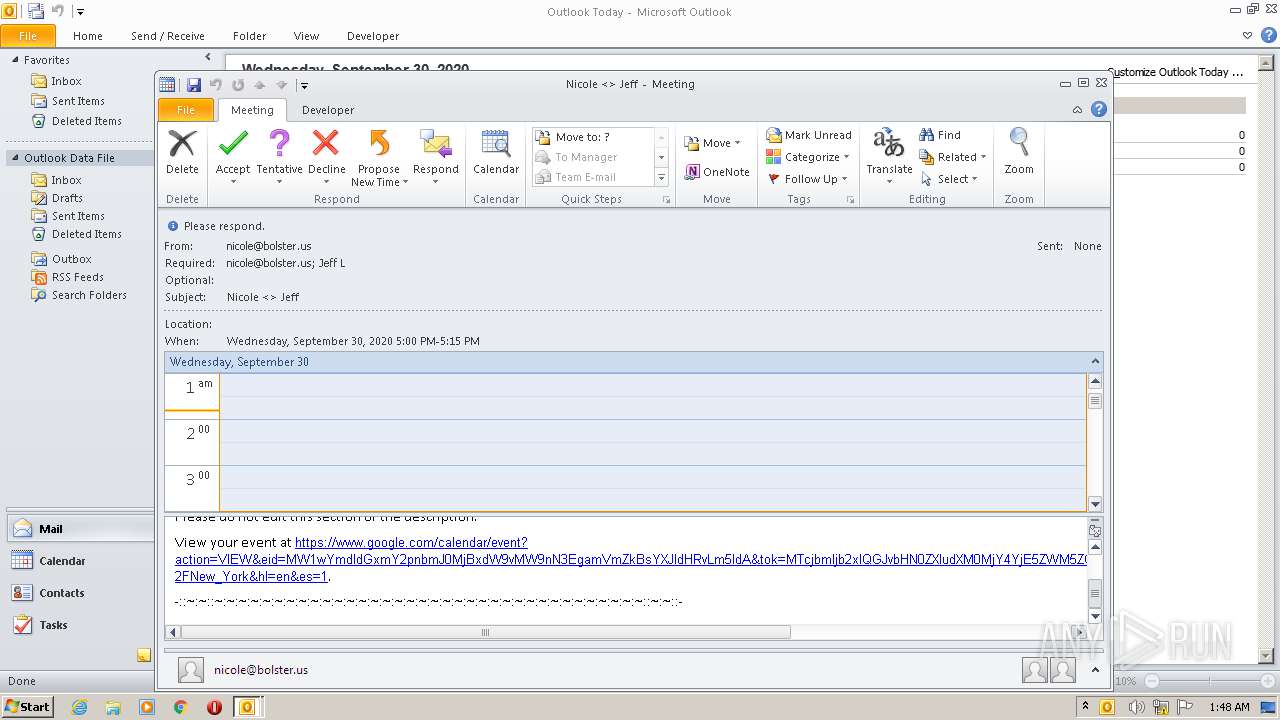
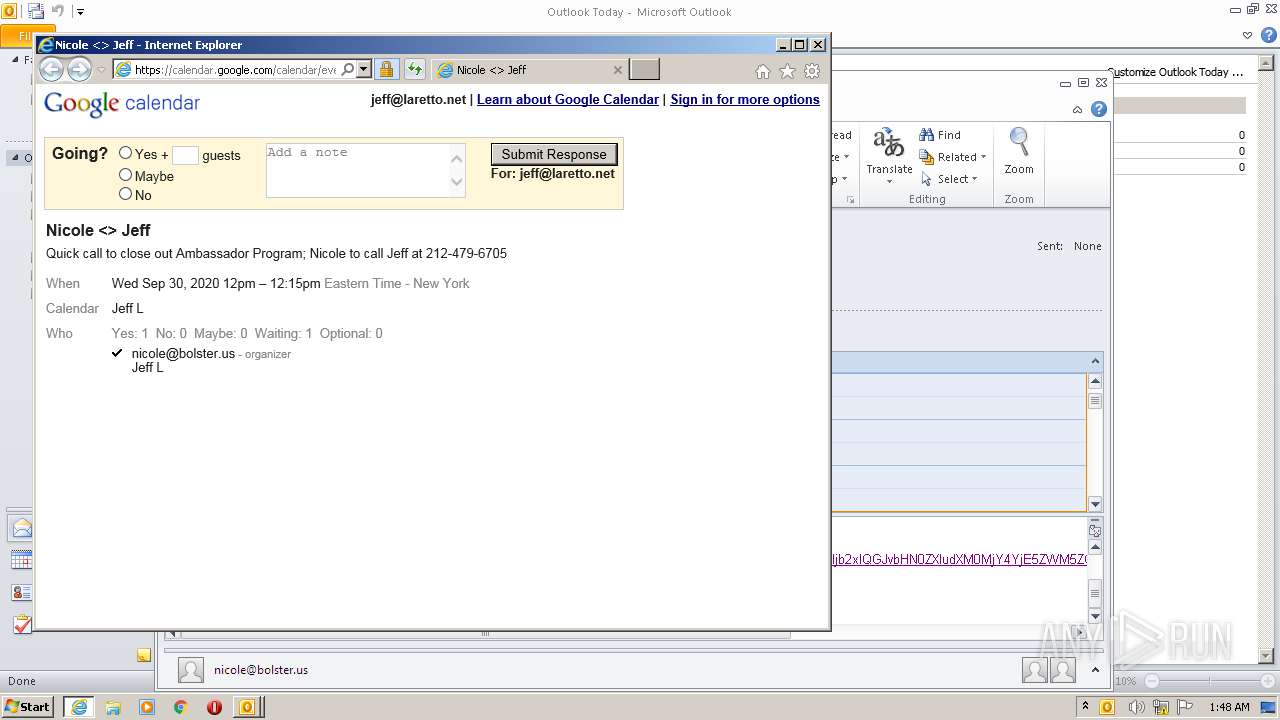
| DateTimeStart: | 2020:09:30 16:00:00Z |
| DateTimeEnd: | 2020:09:30 16:15:00Z |
| DateTimeStamp: | 2020:09:29 22:12:53Z |
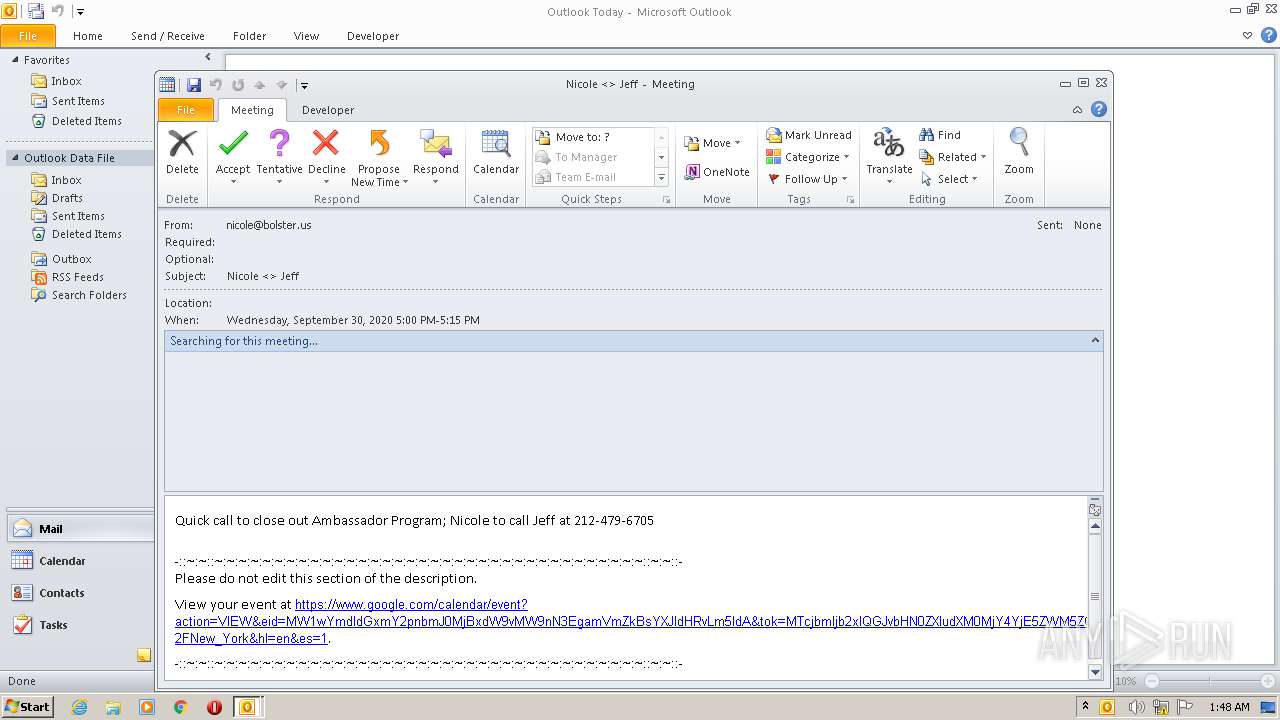
| Organizer: | mailto:nicole@bolster.us |
| UID: | 1mpbgetlfcjgnbt20quoo1og7q@google.com |
| Attendee: | mailto:jeff@laretto.net |
| Microsoft-cdo-ownerapptid: | -759146609 |
| DateCreated: | 2020:09:29 22:12:50Z |
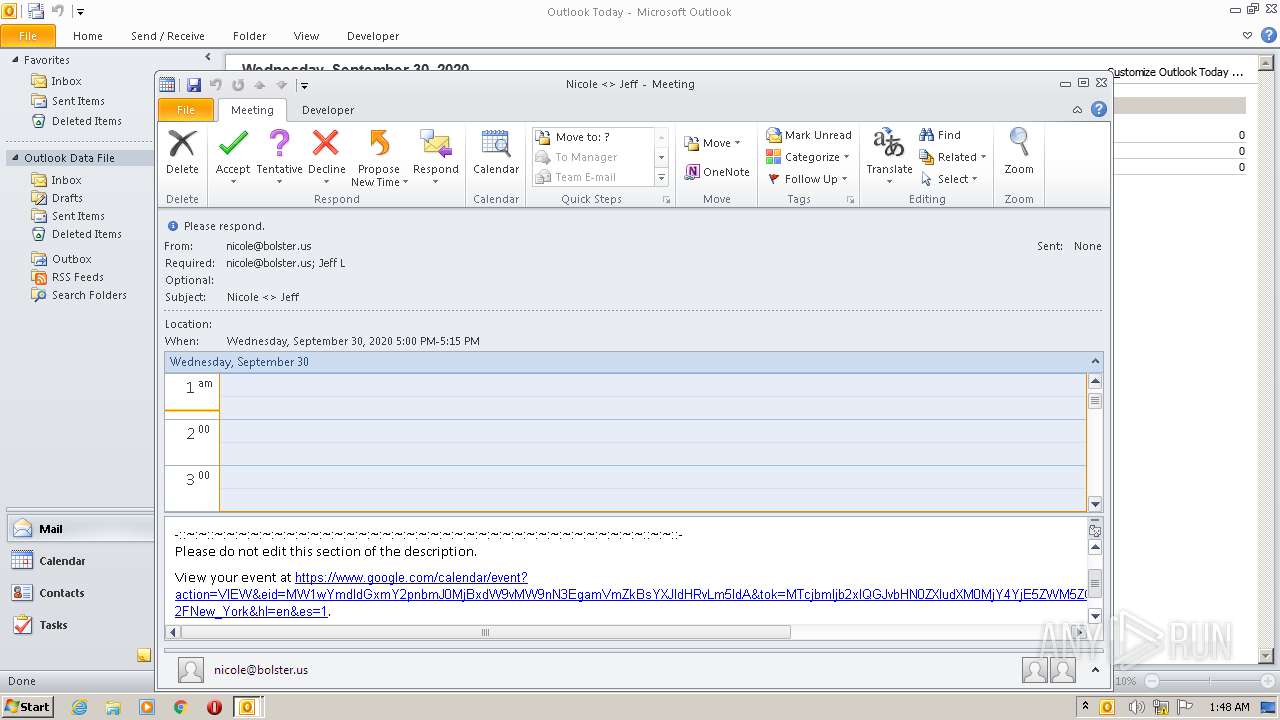
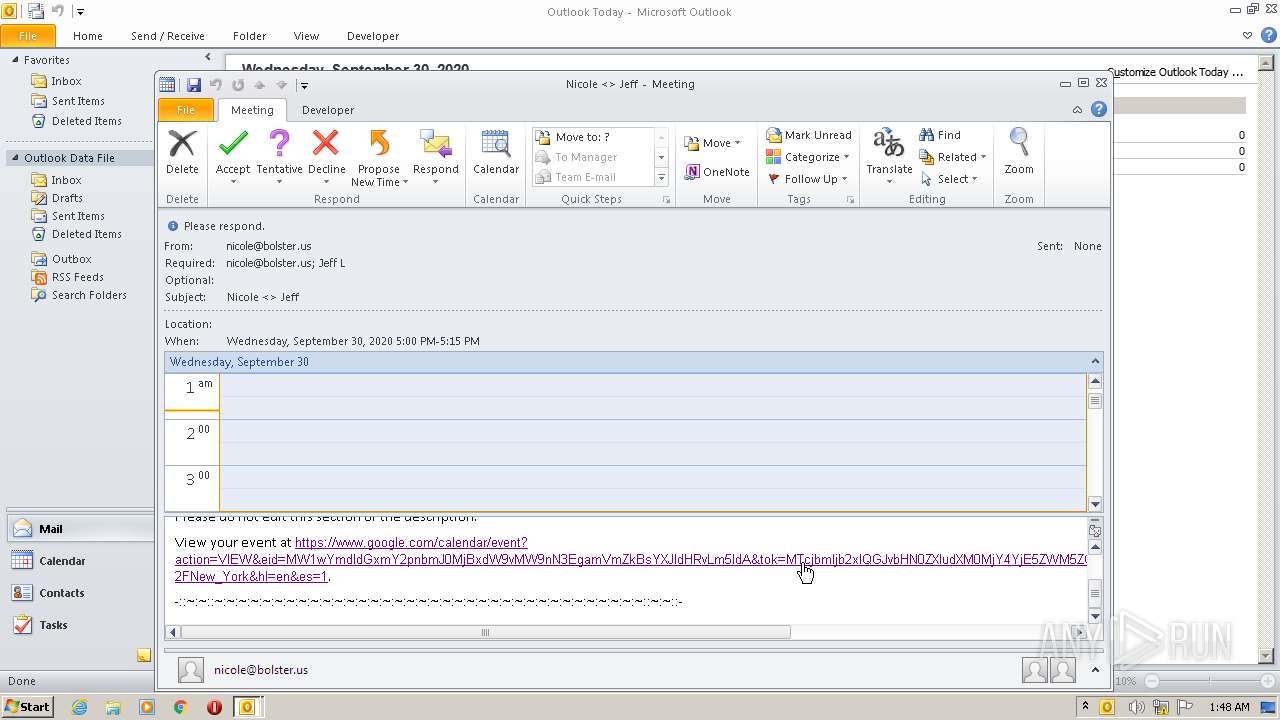
| Description: | Quick call to close out Ambassador Program; Nicole to call Jeff at 212-479-6705 -::~:~::~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~::~:~::- Please do not edit this section of the description. View your event at https://www.google.com/calendar/event?action=VIEW&eid=MW1wYmdldGxmY2pnbmJ0MjBxdW9vMW9nN3EgamVmZkBsYXJldHRvLm5ldA&tok=MTcjbmljb2xlQGJvbHN0ZXIudXM0MjY4YjE5ZWM5ZGRlZDcxMWU4OWU3Y2VhMzc1OTk2YzQzN2NhN2Vl&ctz=America%2FNew_York&hl=en&es=1. -::~:~::~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~:~::~:~::- |
| ModifyDate: | 2020:09:29 22:12:51Z |
| Location: | - |
| SequenceNumber: | - |
| Status: | CONFIRMED |
| Summary: | Nicole <> Jeff |
| TimeTransparency: | OPAQUE |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1492 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
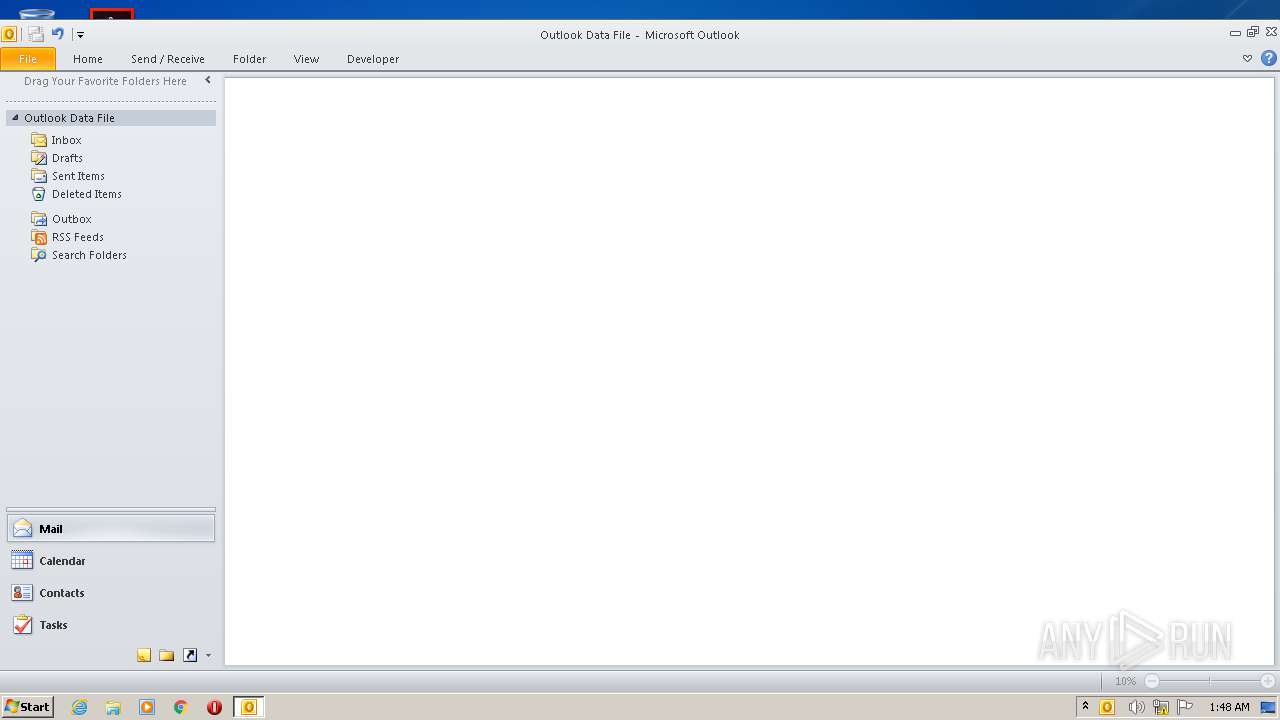
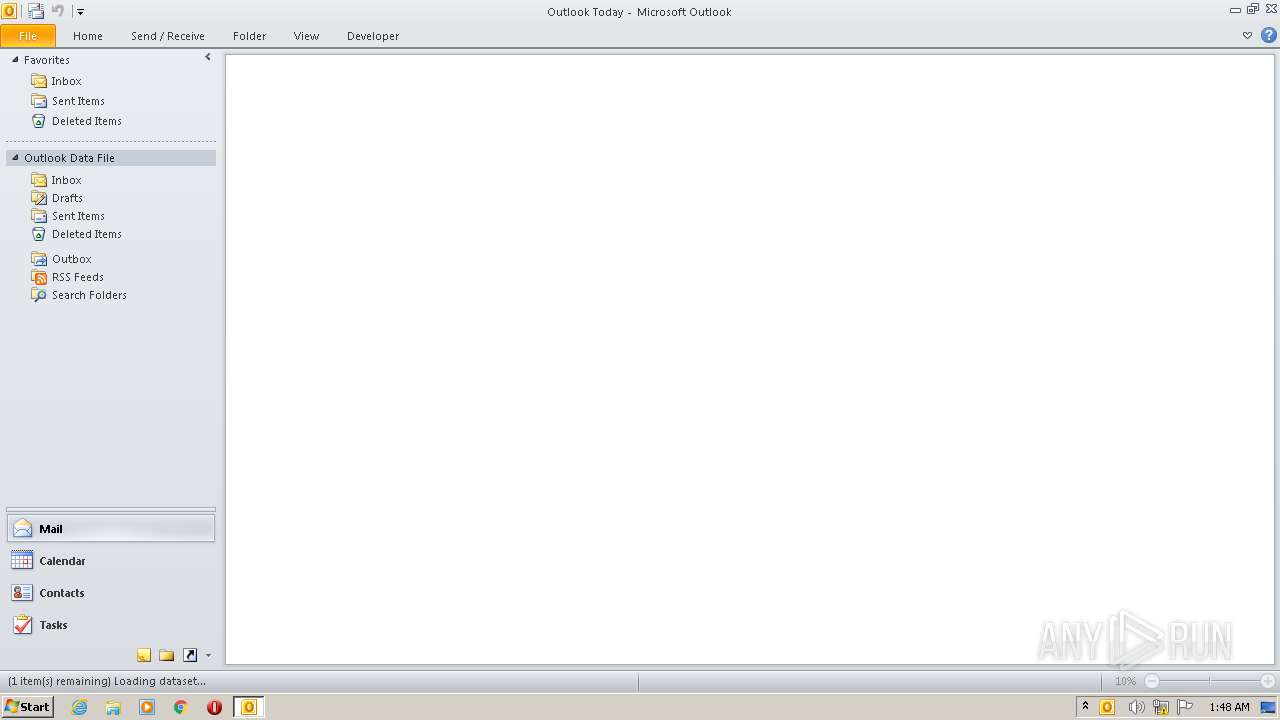
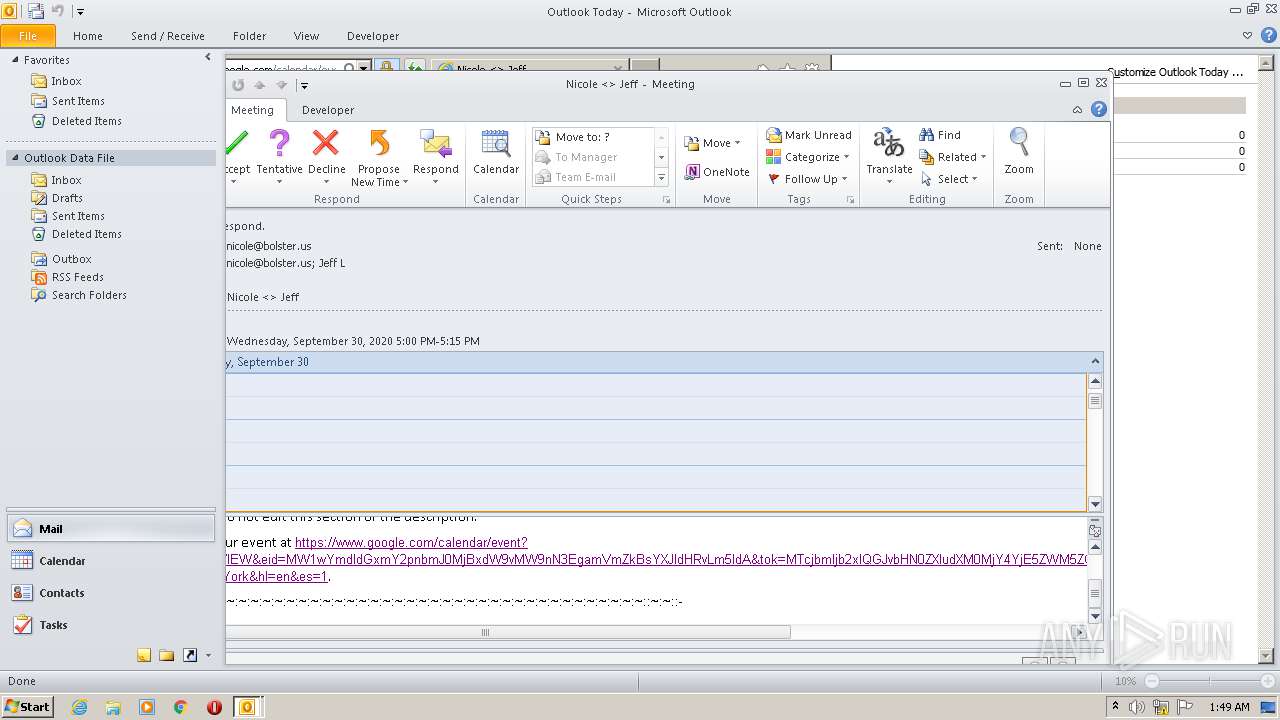
| 668 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /ical "C:\Users\admin\AppData\Local\Temp\invite.ics" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.google.com/calendar/event?action=VIEW&eid=MW1wYmdldGxmY2pnbmJ0MjBxdW9vMW9nN3EgamVmZkBsYXJldHRvLm5ldA&tok=MTcjbmljb2xlQGJvbHN0ZXIudXM0MjY4YjE5ZWM5ZGRlZDcxMWU4OWU3Y2VhMzc1OTk2YzQzN2NhN2Vl&ctz=America%2FNew_York&hl=en&es=1 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 891
Read events
2 128
Write events
723
Delete events
40
Modification events
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (668) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
28
Text files
41
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRC082.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 668 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\05J8PVOFWTP2Y0T66W7R.temp | — | |
MD5:— | SHA256:— | |||
| 668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF1078E2236CC346FD.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF29729BD72F6BA676.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Microsoft Outlook.lnk | lnk | |
MD5:— | SHA256:— | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab396.tmp | — | |
MD5:— | SHA256:— | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar397.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\be71009ff8bb02a2.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 668 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_BA2ABE0893A9A7BF7FF17EDCC6518271 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
21
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
668 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
324 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCoziyTHasflwIAAAAAekur | US | der | 472 b | whitelisted |
324 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
324 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCoziyTHasflwIAAAAAekur | US | der | 472 b | whitelisted |
324 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1056 | svchost.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAASWxwt68EQiA3cUAAAABJbE%3D | US | der | 1.75 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
324 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDOs%2FDKHsIMiAIAAAAAeksR | US | der | 472 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAKXB1YM1Knrv%2BJy8eCW2II%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
668 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
324 | iexplore.exe | 172.217.22.110:443 | calendar.google.com | Google Inc. | US | whitelisted |
324 | iexplore.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
324 | iexplore.exe | 172.217.22.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1492 | iexplore.exe | 172.217.22.110:443 | calendar.google.com | Google Inc. | US | whitelisted |
1492 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1056 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1056 | svchost.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
1056 | svchost.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
1056 | svchost.exe | 104.18.25.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
calendar.google.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
www.microsoft.com |
| whitelisted |