| File name: | 8054b3a5a0e0a19660e006eb80ada8cb2d60360cf84dc4213ba7a9f3bbb4457e |
| Full analysis: | https://app.any.run/tasks/a3294099-eb9e-4621-a110-c02ea8a654b8 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 18:25:48 |
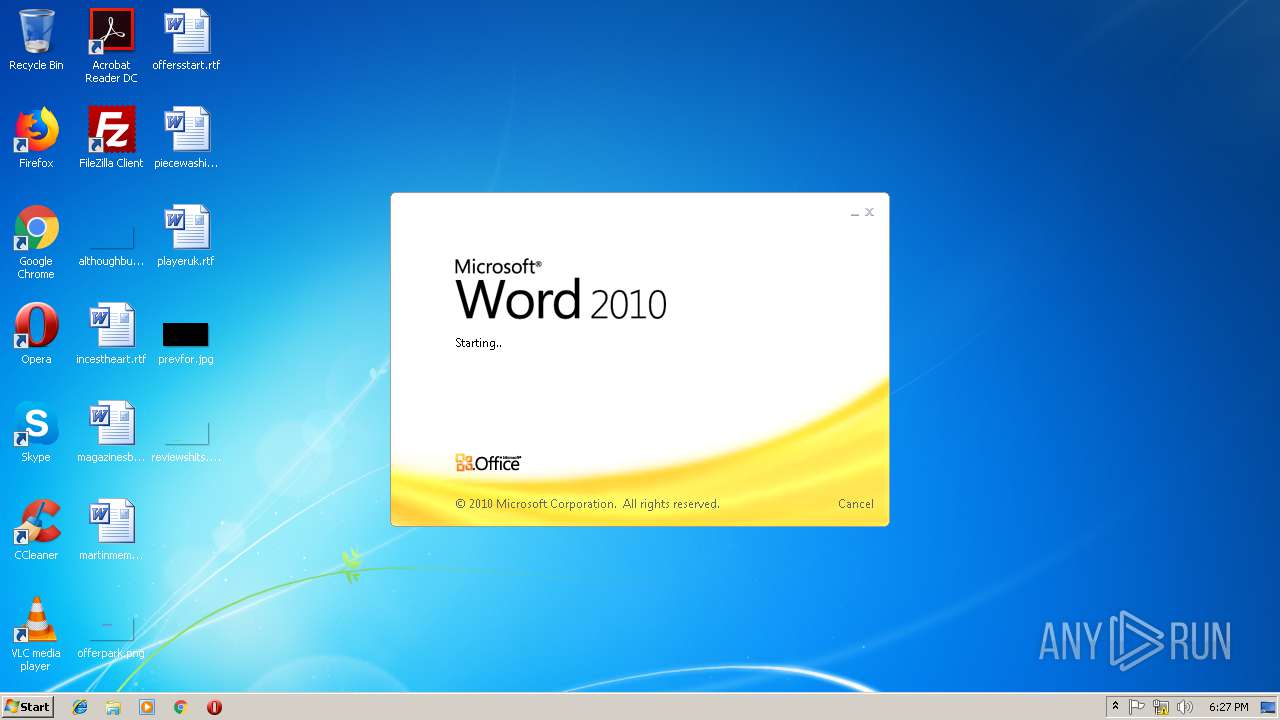
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 1CD66FBC91462CD0E8BD16BDC0B625DA |
| SHA1: | EC947CB8726D15694D5691636DA3BDD347729256 |
| SHA256: | 8054B3A5A0E0A19660E006EB80ADA8CB2D60360CF84DC4213BA7A9F3BBB4457E |
| SSDEEP: | 192:+YZEAkEDG3c+auO0rA8R4Njasykz8inchhYVKGcU:LEqGs+VPDsykz8ichhdGcU |
MALICIOUS
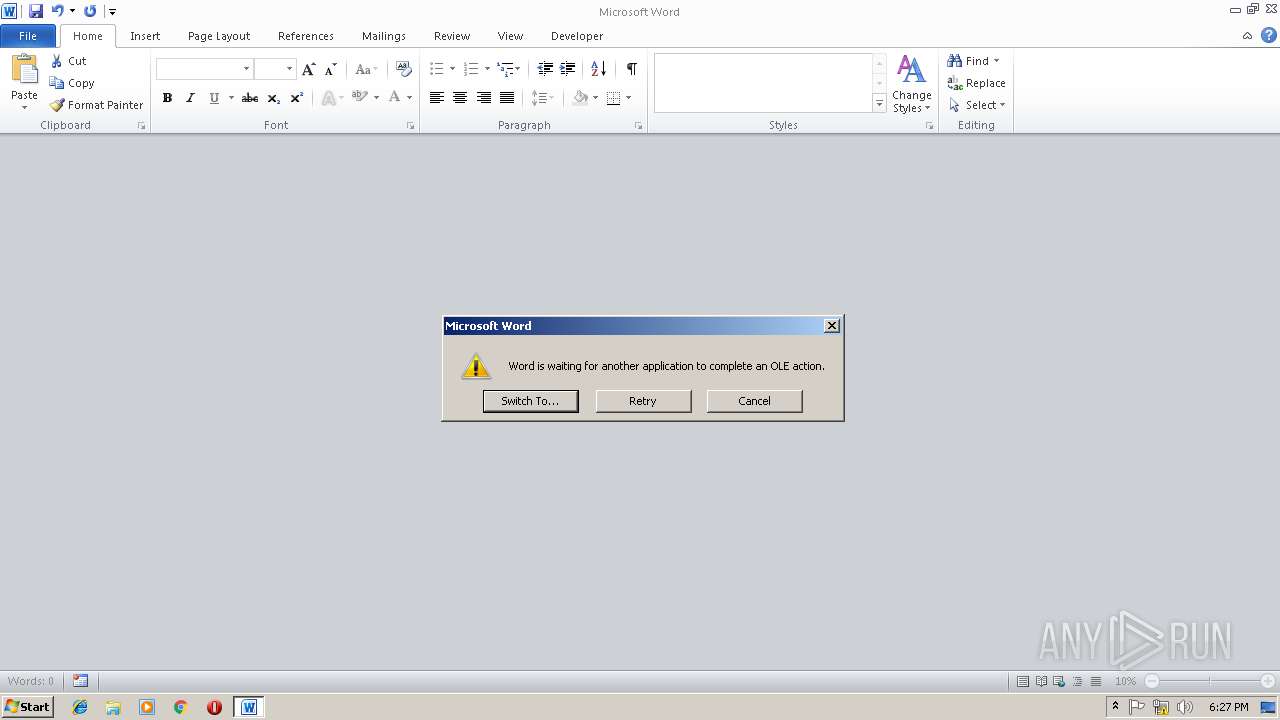
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 1676)
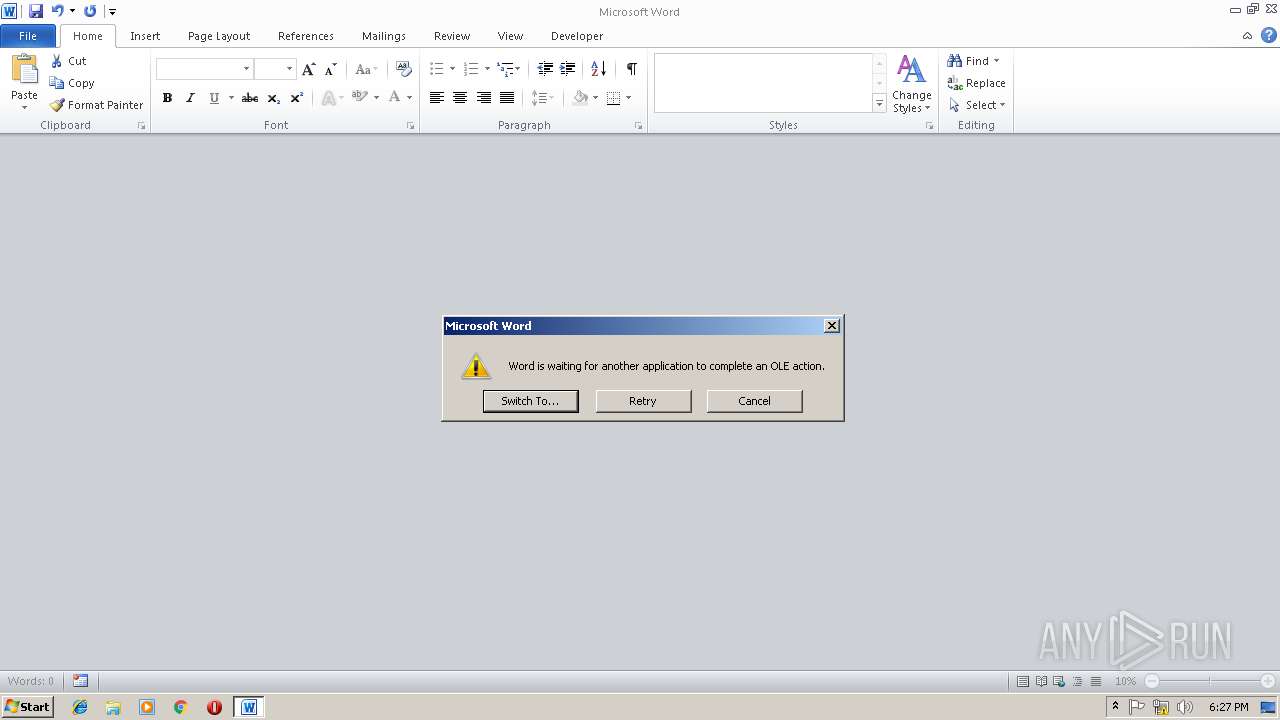
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3172)
SUSPICIOUS
Starts Microsoft Office Application
- rundll32.exe (PID: 2708)
Creates files in the user directory
- EQNEDT32.EXE (PID: 1676)
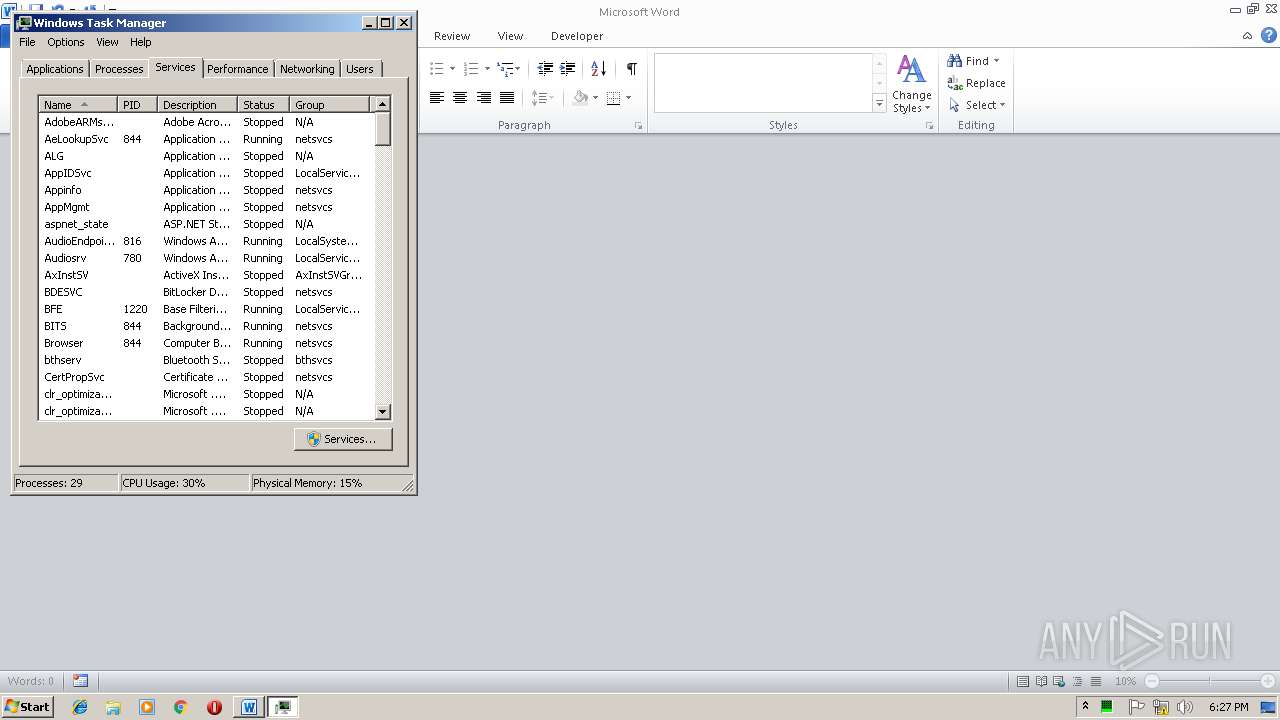
Reads internet explorer settings
- mmc.exe (PID: 2416)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3172)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
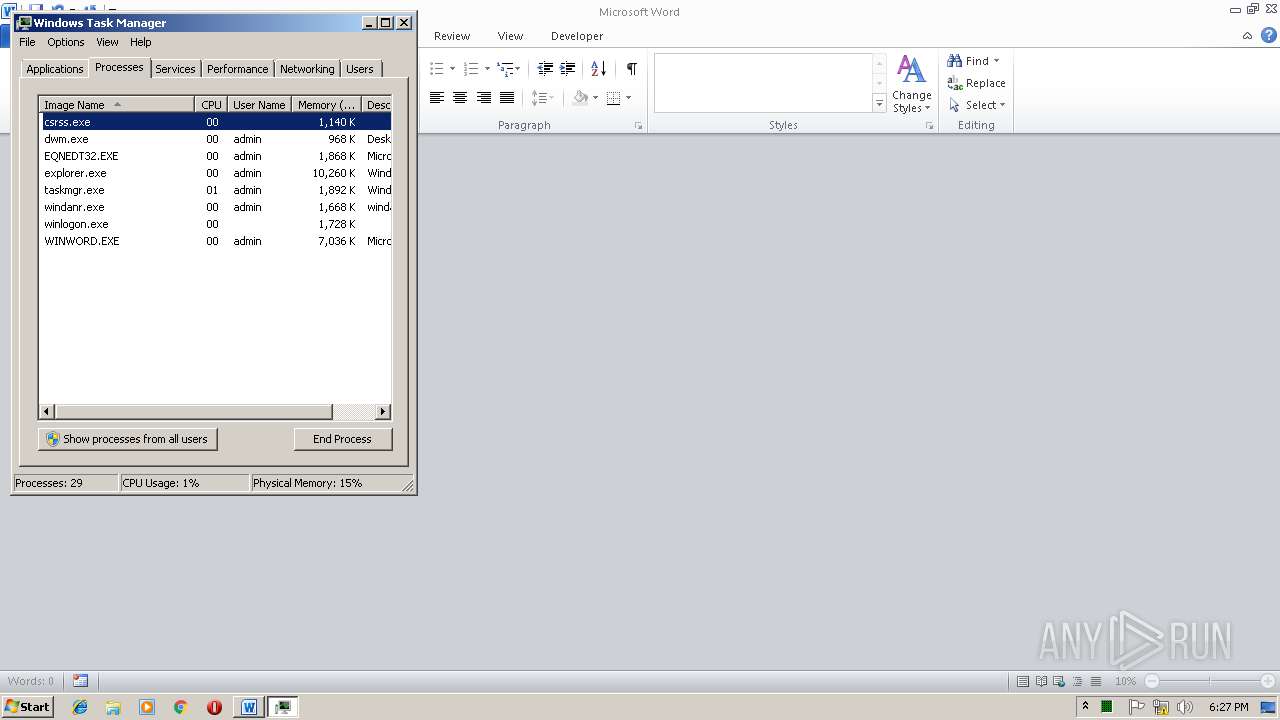
Total processes
39
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
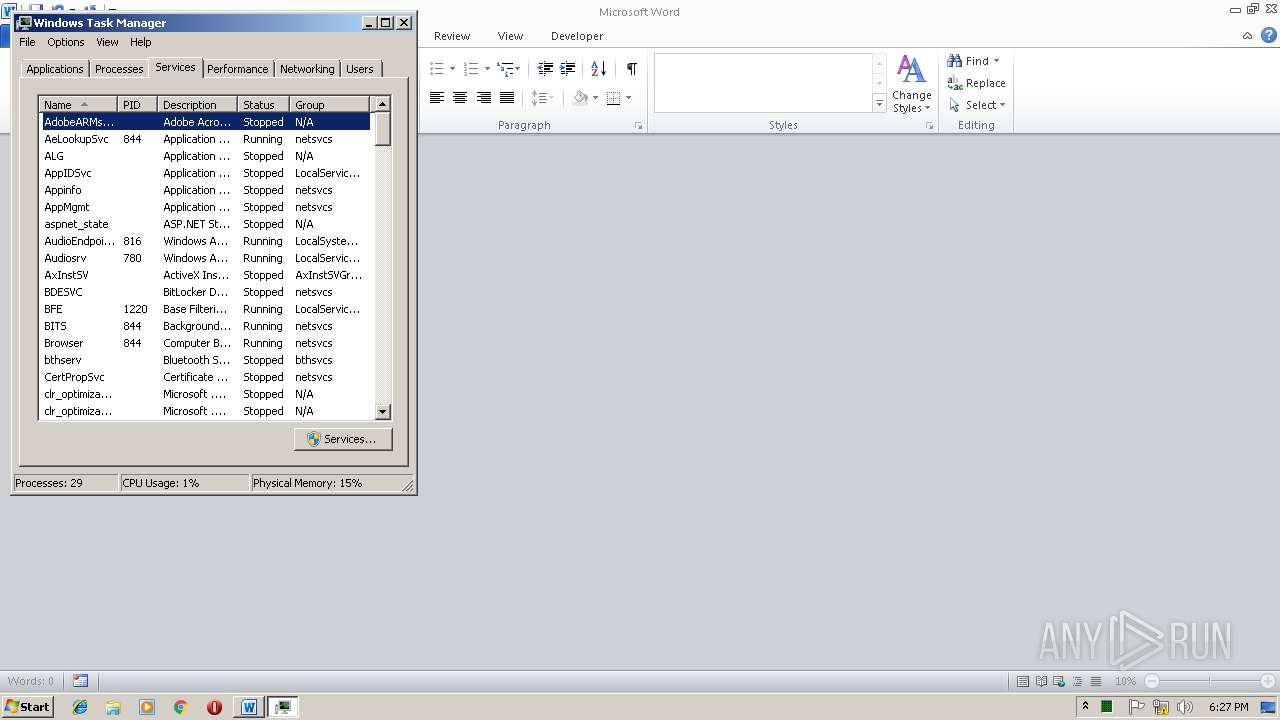
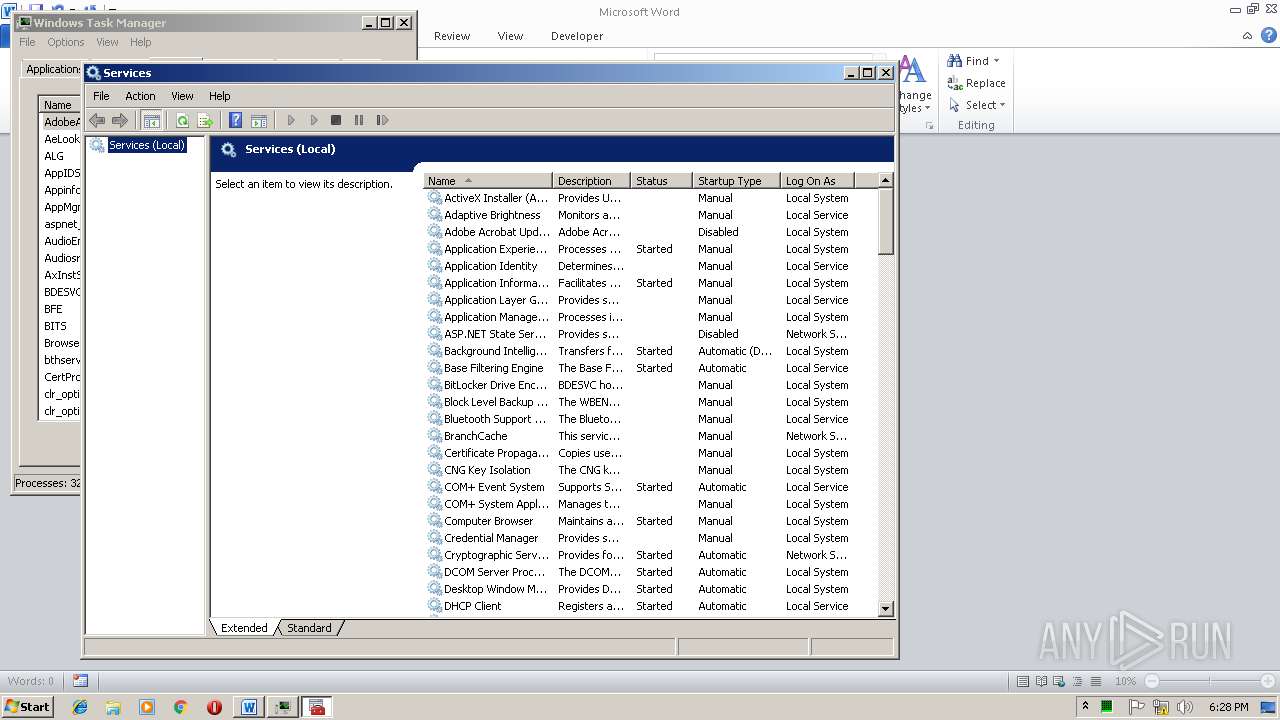
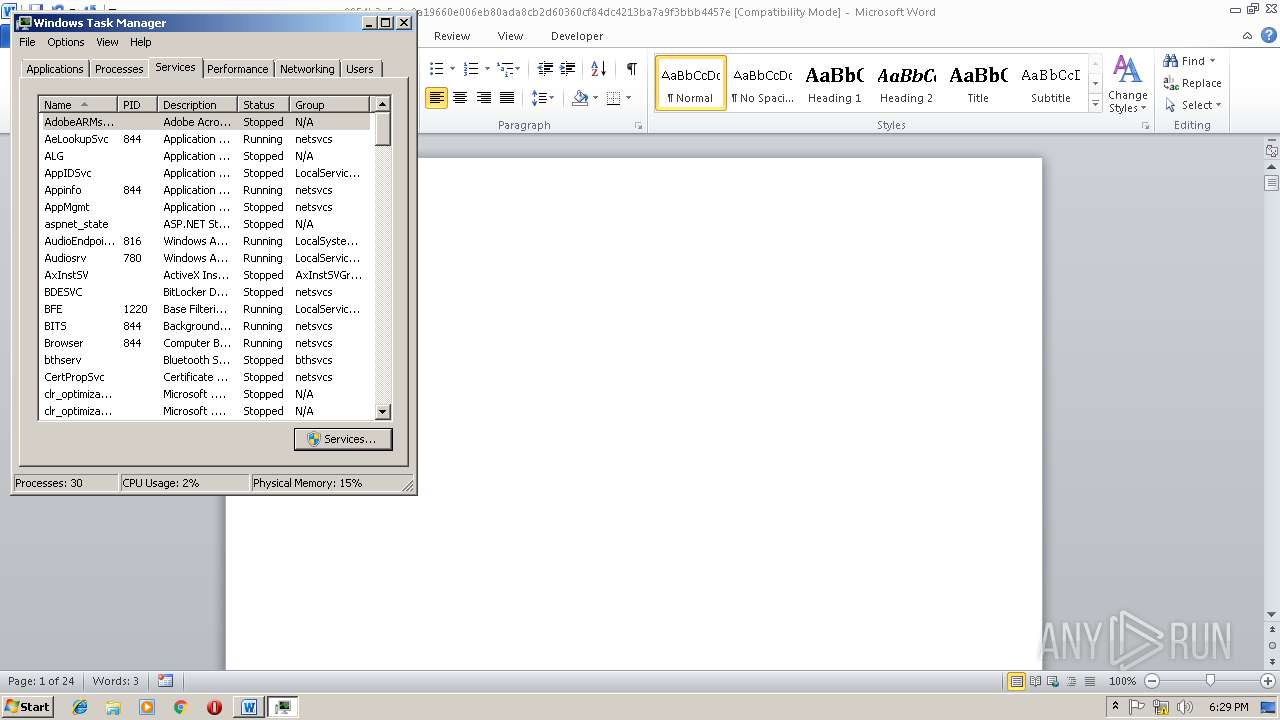
| 2416 | "C:\Windows\system32\mmc.exe" "C:\Windows\System32\services.msc" | C:\Windows\system32\mmc.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
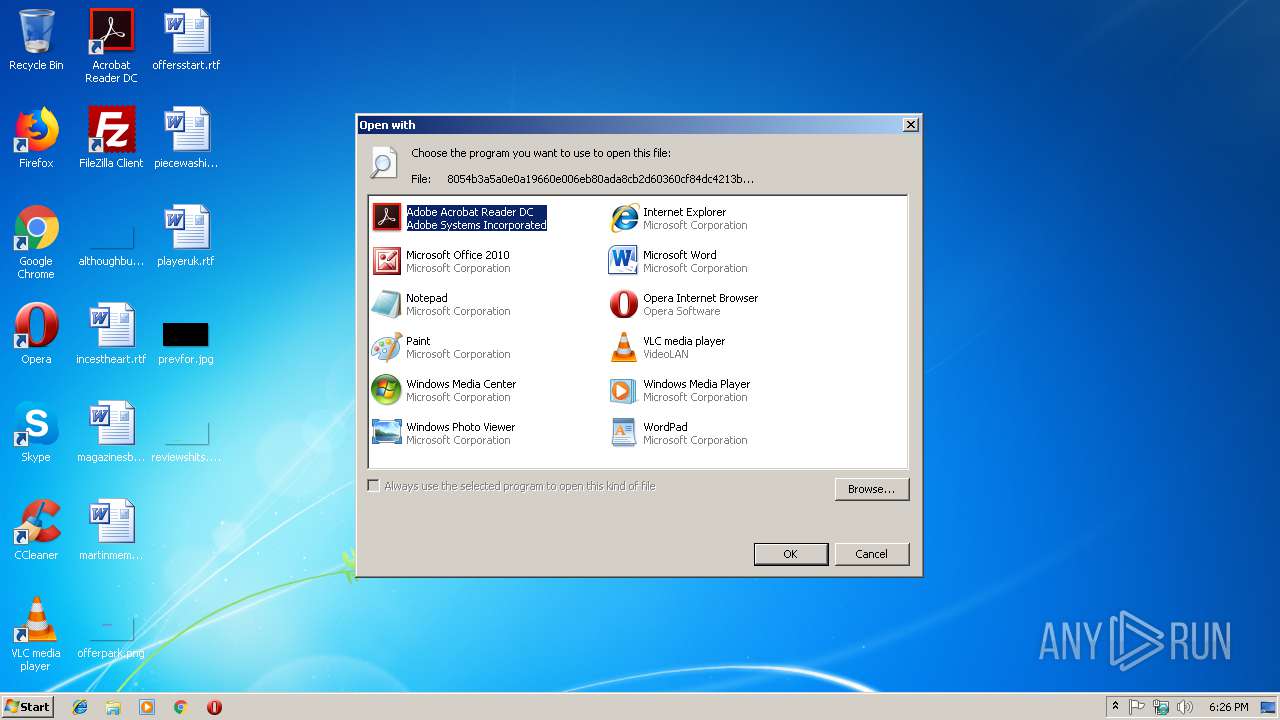
| 2708 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\8054b3a5a0e0a19660e006eb80ada8cb2d60360cf84dc4213ba7a9f3bbb4457e | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
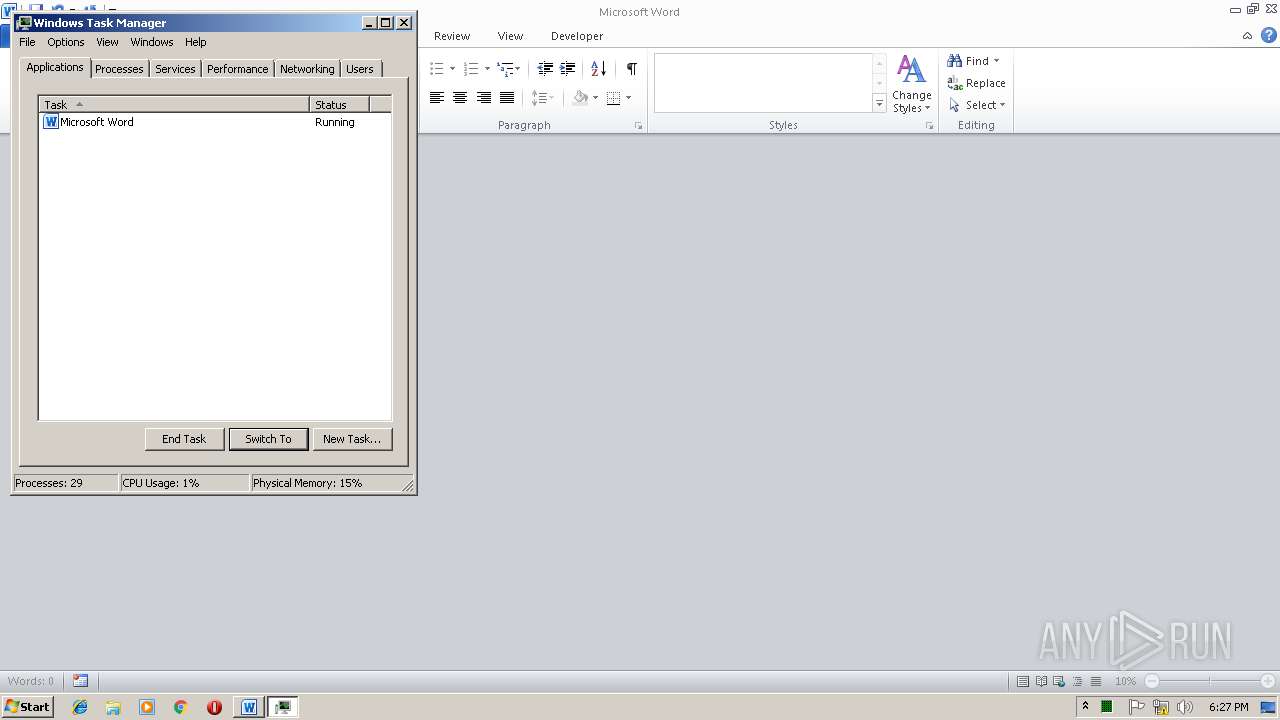
| 2972 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
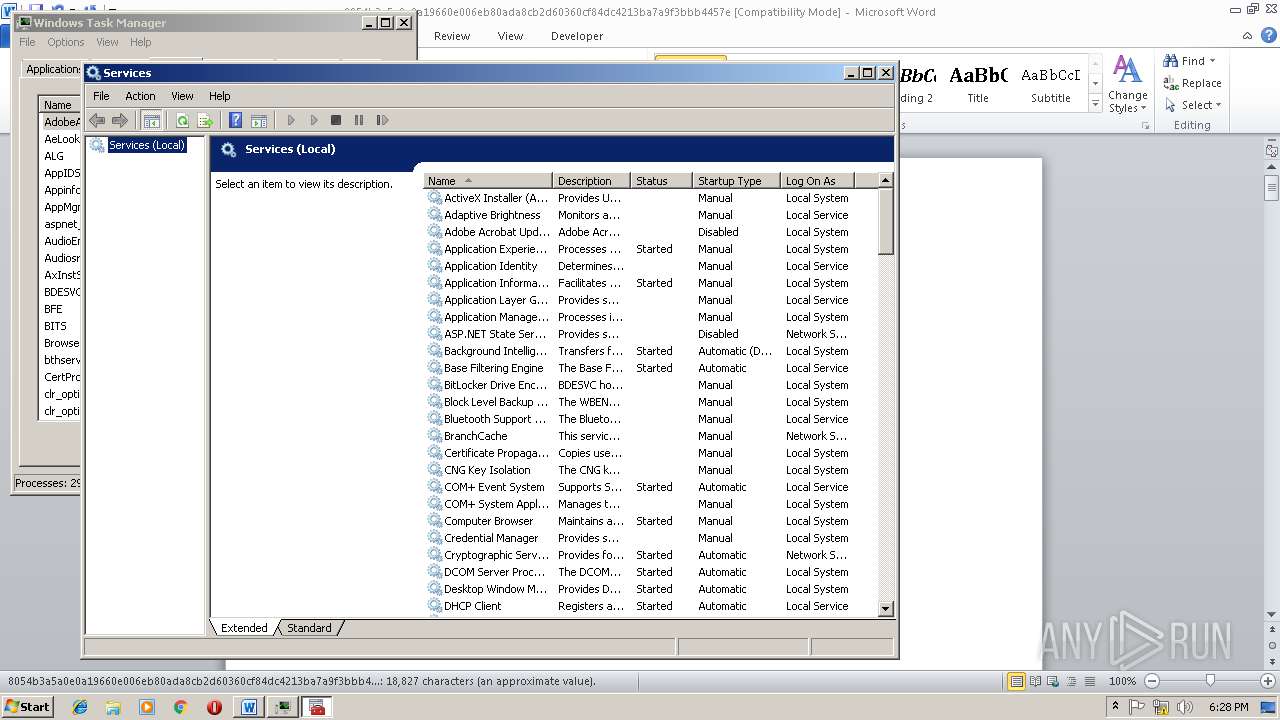
| 3172 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\8054b3a5a0e0a19660e006eb80ada8cb2d60360cf84dc4213ba7a9f3bbb4457e" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4064 | "C:\Windows\system32\mmc.exe" "C:\Windows\System32\services.msc" | C:\Windows\system32\mmc.exe | — | taskmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 775
Read events
1 340
Write events
429
Delete events
6
Modification events
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB663.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1676 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@bit[1].txt | text | |
MD5:— | SHA256:— | |||
| 3172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$54b3a5a0e0a19660e006eb80ada8cb2d60360cf84dc4213ba7a9f3bbb4457e | pgc | |
MD5:— | SHA256:— | |||
| 1676 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 2416 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\views[1] | html | |
MD5:A726593A8261930E4786375106FC6BFE | SHA256:E6BFDFBB9A0649EA9D38DE4255C355C581097E6A1035A54943260B22AD45F172 | |||
| 2416 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\views[1] | html | |
MD5:A726593A8261930E4786375106FC6BFE | SHA256:E6BFDFBB9A0649EA9D38DE4255C355C581097E6A1035A54943260B22AD45F172 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1676 | EQNEDT32.EXE | GET | — | 208.97.149.120:80 | http://www.scarpeshop.eu/v/E0.png | US | — | — | malicious |
1676 | EQNEDT32.EXE | GET | 301 | 67.199.248.10:80 | http://bit.ly/2Gn4PCa | US | html | 120 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1676 | EQNEDT32.EXE | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
1676 | EQNEDT32.EXE | 208.97.149.120:80 | www.scarpeshop.eu | New Dream Network, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
www.scarpeshop.eu |
| malicious |