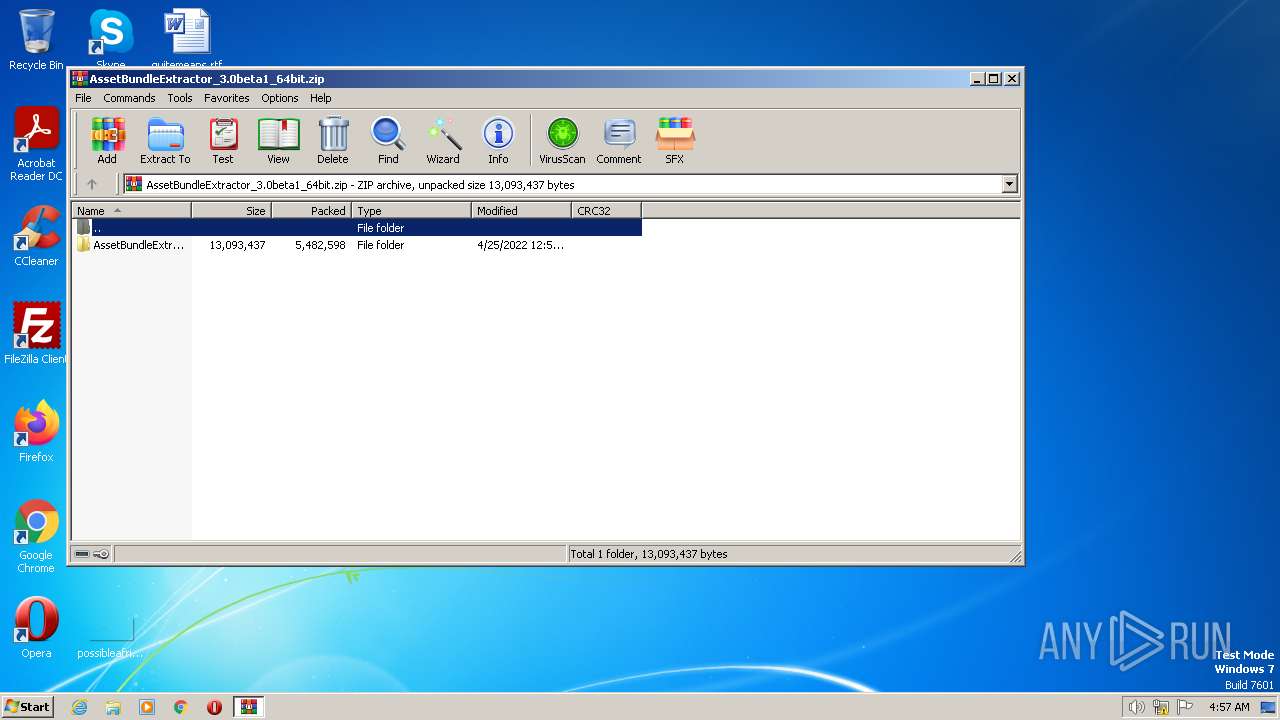
| File name: | AssetBundleExtractor_3.0beta1_64bit.zip |
| Full analysis: | https://app.any.run/tasks/db736208-a030-46c9-afc0-1c36cb6d94cd |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2023, 03:57:35 |
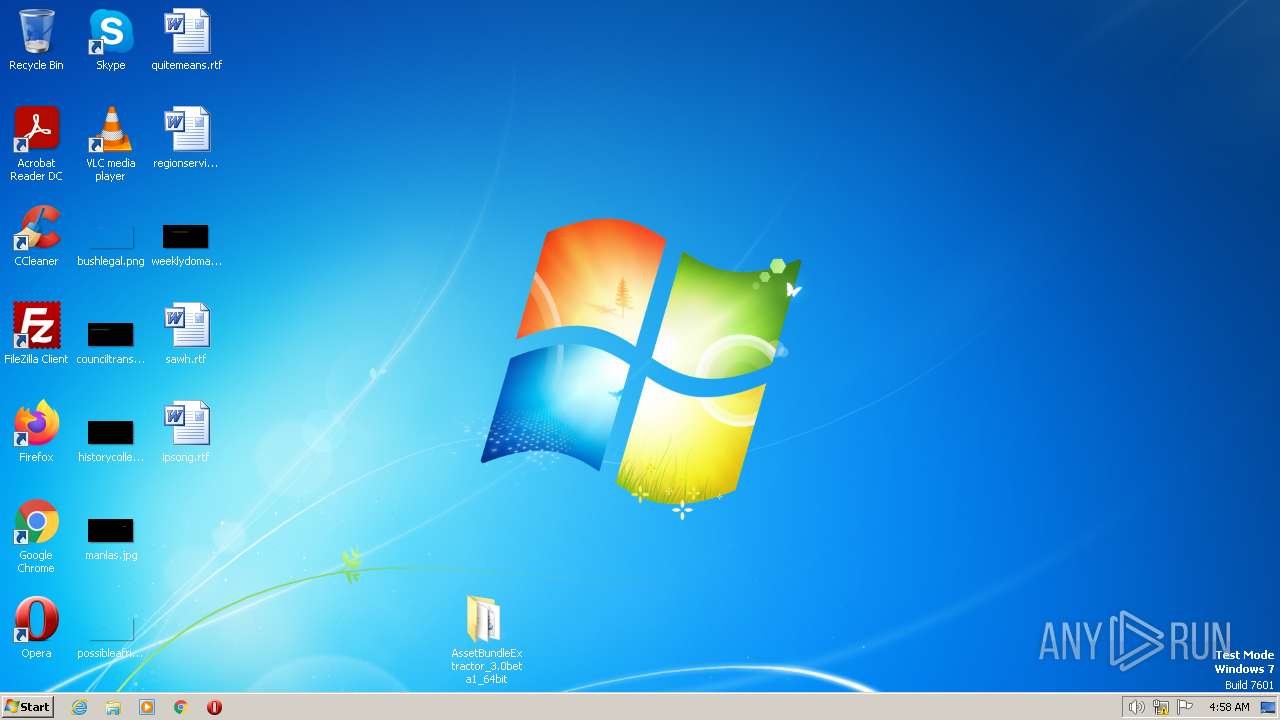
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 094474D391D64D5400D89FBE22CD77B4 |
| SHA1: | 979EB588CB498CF5AC4C771D141FAFE4BA44AF3C |
| SHA256: | 803384CFD183884A81FBB077D109B76C9A1DDDBE512E4398988C8DE81CA270A2 |
| SSDEEP: | 98304:c8xUUeKkN6WvD3VIYbvkh9HFYb4xpB7fLEhzYT6B6pfYwBtOiNCMe:lDGr3Vp8h9HOb4xjbKYULODbe |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3080)
SUSPICIOUS
No suspicious indicators.INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
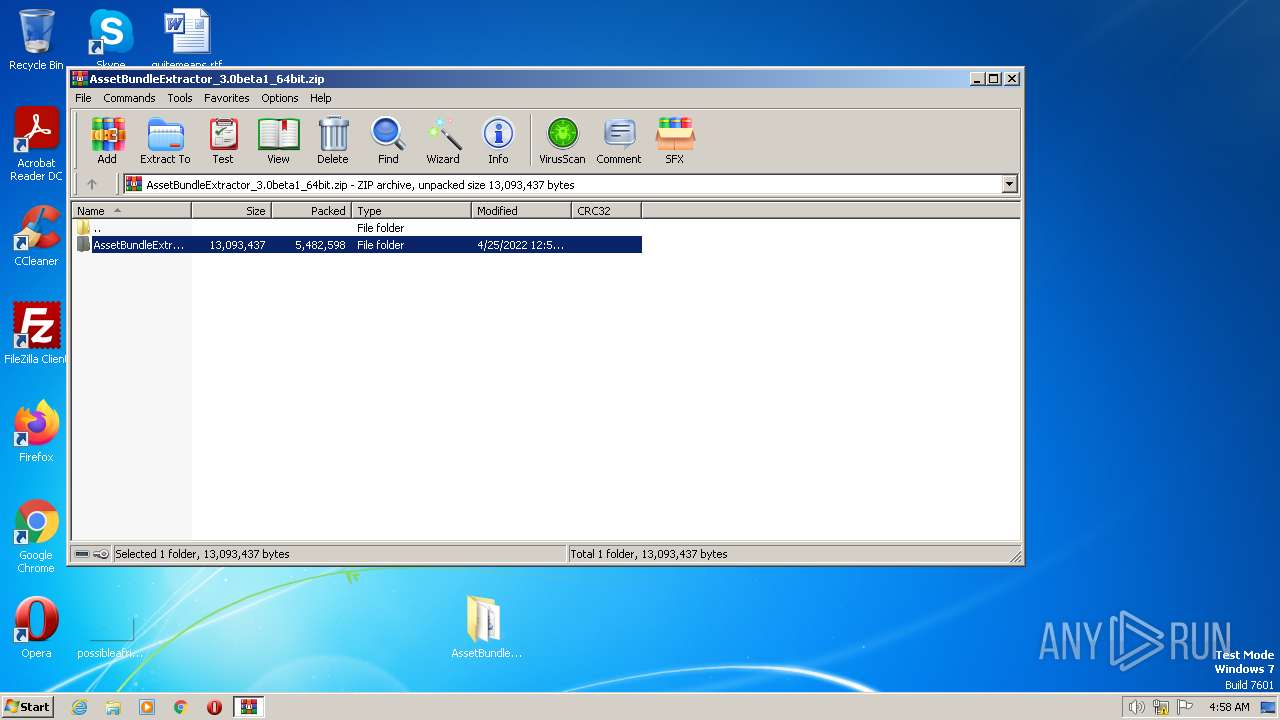
| ZipFileName: | AssetBundleExtractor_3.0beta1_64bit/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:04:25 13:57:38 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3080 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
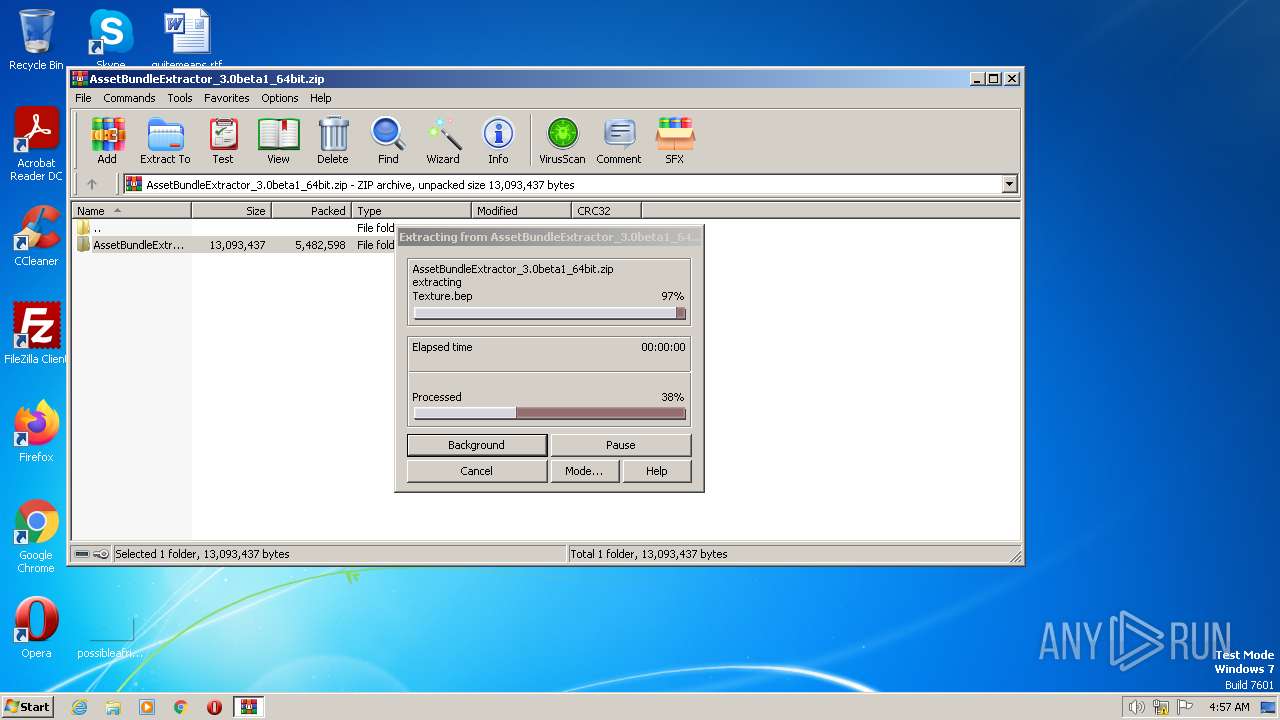
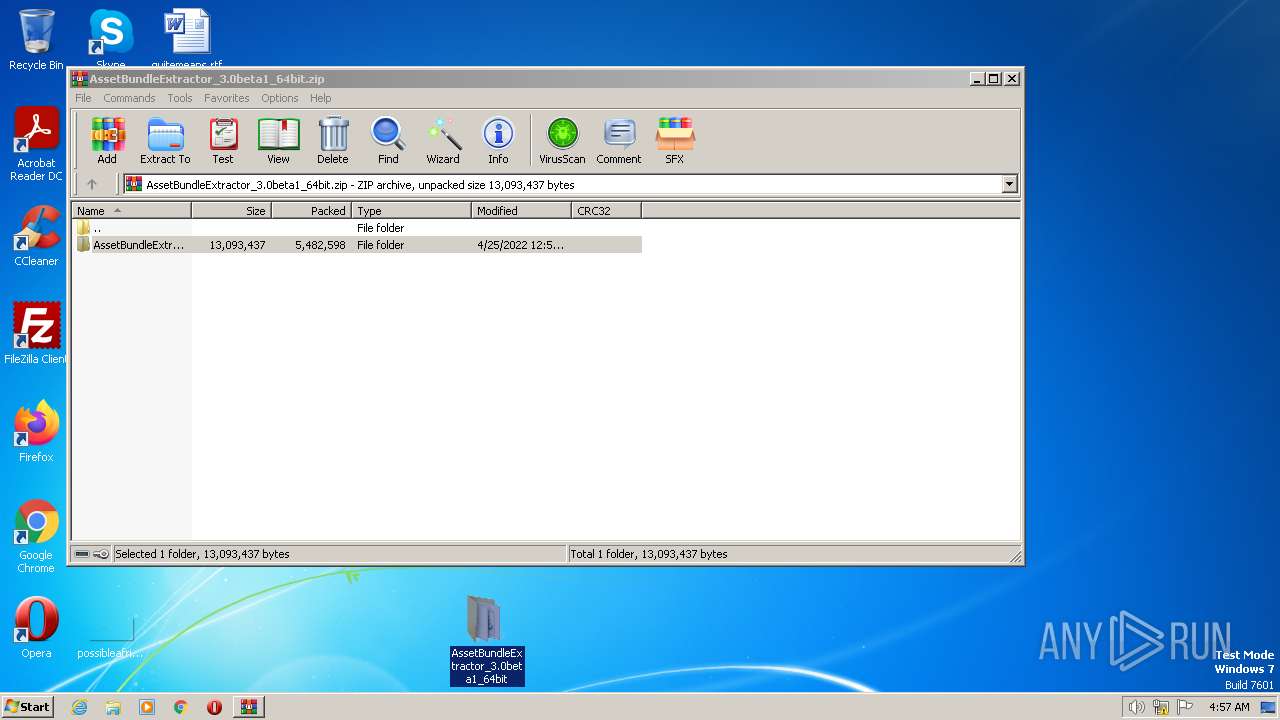
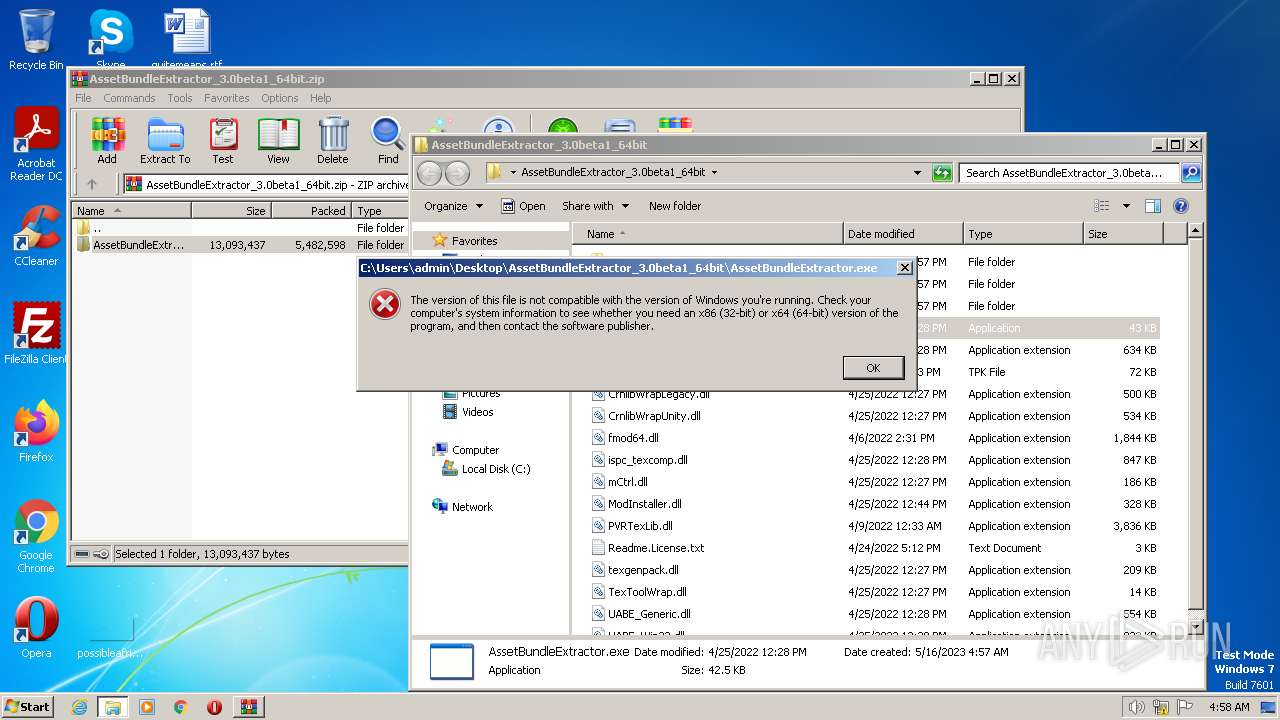
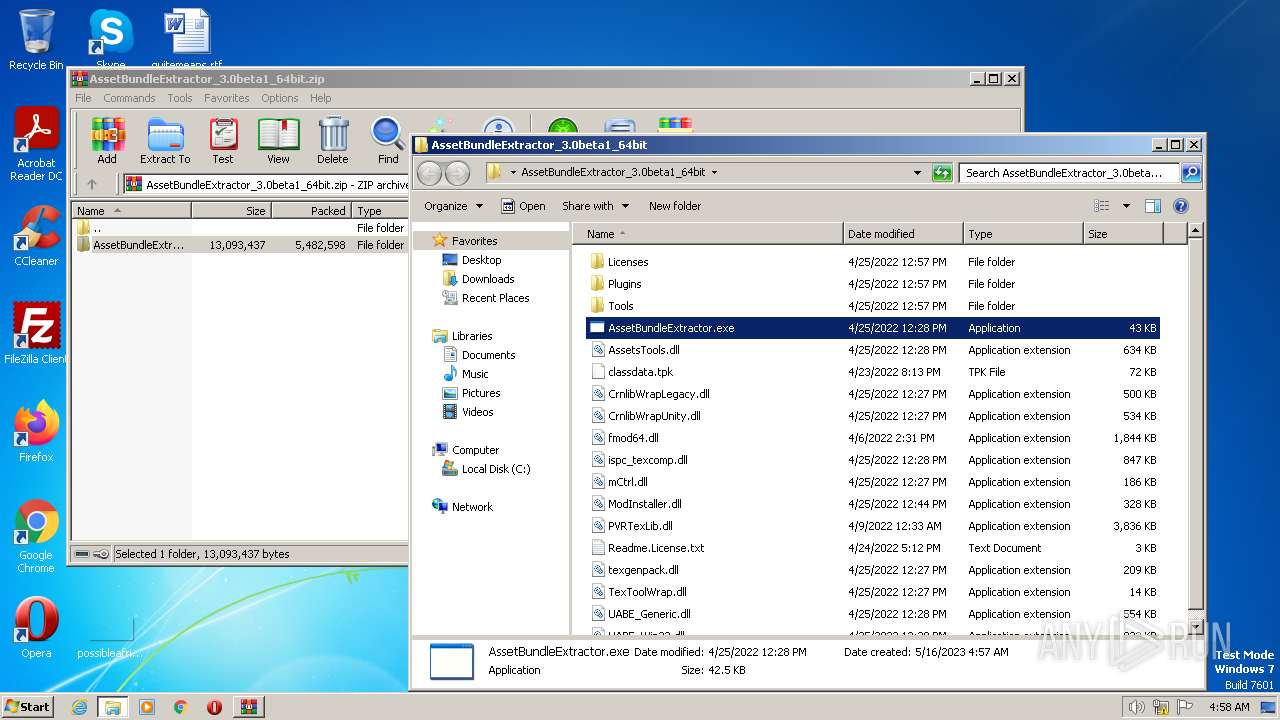
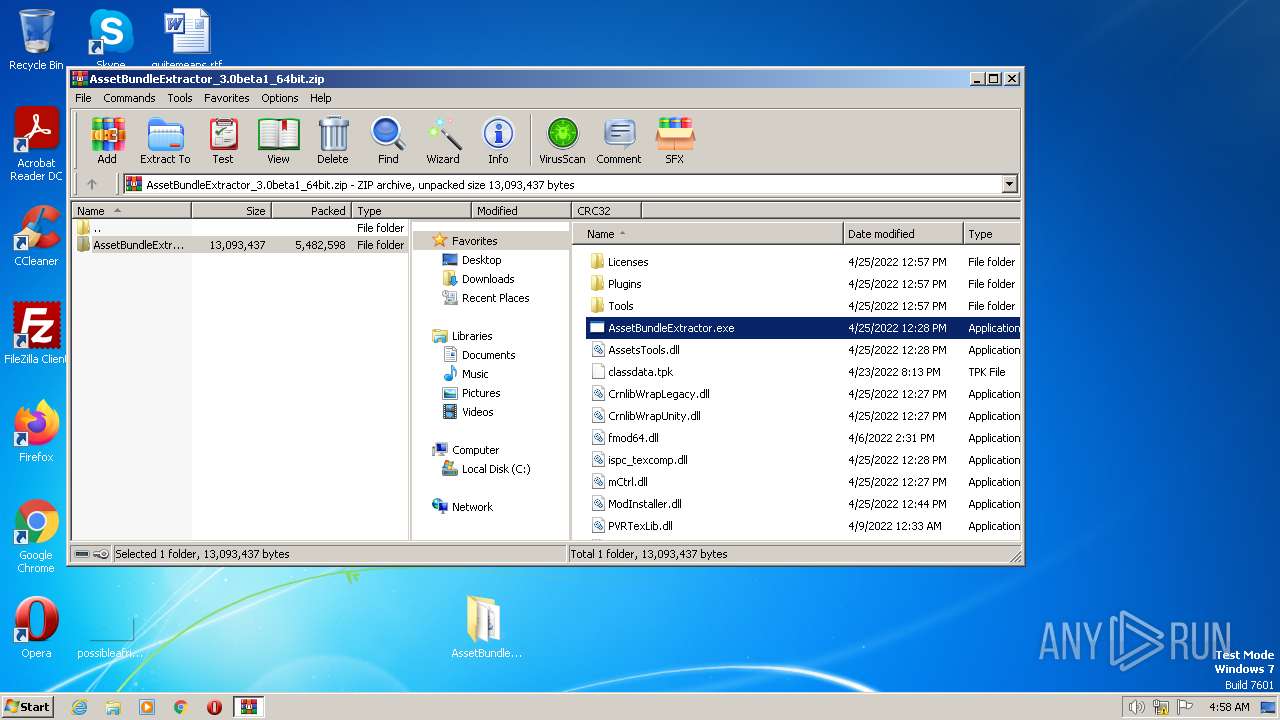
| 3944 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AssetBundleExtractor_3.0beta1_64bit.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 667
Read events
1 647
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3080) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
21
Suspicious files
1
Text files
18
Unknown types
0
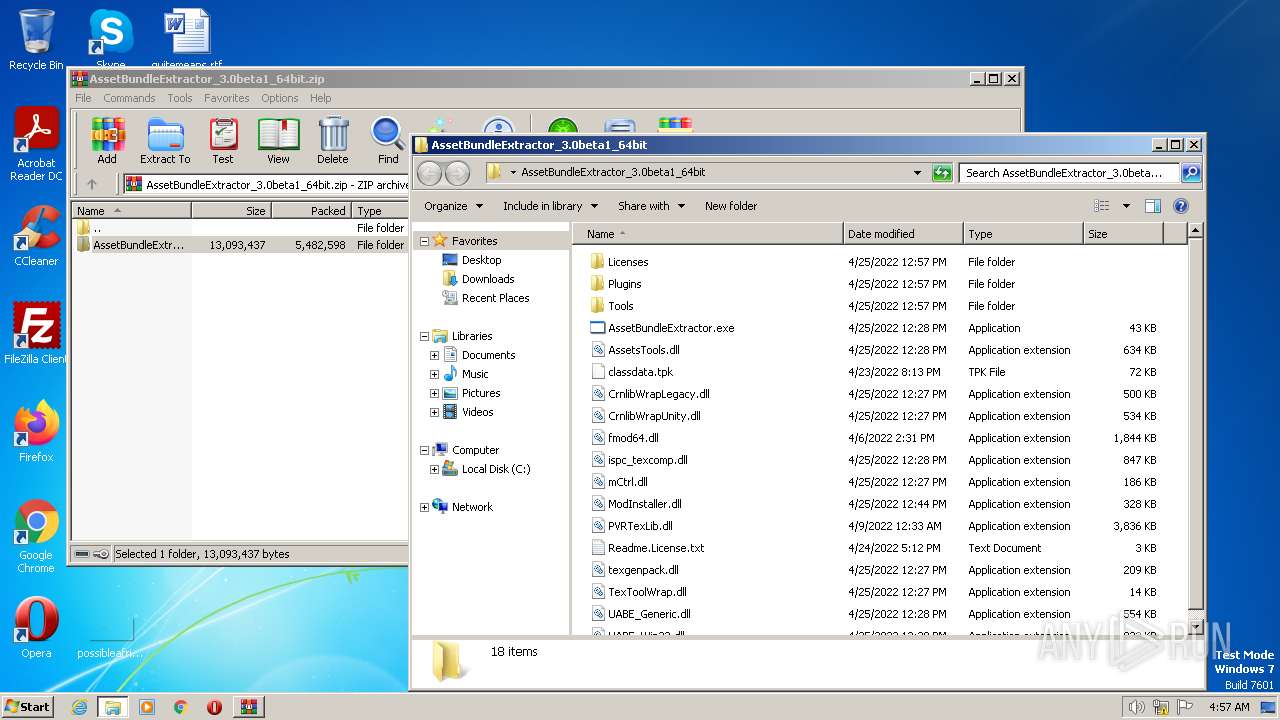
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\classdata.tpk | binary | |
MD5:53A535AE8FA3F78609E02CB8C23134CA | SHA256:8561C35F51E0F8212E3FE0820843EA0AC66EF522872898C7EBEED75442446F40 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\CrnlibWrapUnity.dll | executable | |
MD5:4C7CA65F1C1DD082655BEF11F37BC33C | SHA256:25F7B24113A86EDDBB78C705E308D3FBE47CEB534EA16BC955708D8FD2625BD3 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\AssetBundleExtractor.exe | executable | |
MD5:4B4A95CC250B63651D079C372989BE16 | SHA256:957043465AFF2255E4D11C99055609F6C1E34A9417012248EB4AFCE1BB6E5DD4 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\Licenses\half_license.txt | text | |
MD5:29145B8F7E16D6308BBA008FCF9050EE | SHA256:F1C27E7CC7AFEEF96F2A57009124E645700EB9C999E054CD013DC49FF6167E58 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\ispc_texcomp.dll | executable | |
MD5:25D5C386ED5F94C8EF30ADE870BA4070 | SHA256:D7354C120009134EBE2656FF97BCE5F0399567E63246A6CEE25DCD76E23006DF | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\Licenses\cecil_license.txt | text | |
MD5:4CC72AE97C8B623BD69A4DE2539F9728 | SHA256:62DAD7936FC1214D0187B1DD27BD68EC055AF168B7FD1989CC8E36E0E2B9A990 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\Licenses\crunch-unity-license.txt | text | |
MD5:4DF7A0E9B4515A07BE7CBEEEC06651FC | SHA256:BBC49AFBE103D3E4F792CE6609CFA18016073ADE1416F87617661452D7C8B470 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\CrnlibWrapLegacy.dll | executable | |
MD5:27212BD81469E81AC47911881358E820 | SHA256:0D8B251630B9E237A8433D7270371373FCBDEF4837FDAE7D9B14568684E2D0F6 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\Licenses\LodePNG_license.txt | text | |
MD5:BD6DFCBEE33EF692F4051BCCCA8464A2 | SHA256:58E410577C5AC33ABAF817E677BF63D2DB304419260BFFA9AB9E9B538F9854E0 | |||
| 3944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3944.46004\AssetBundleExtractor_3.0beta1_64bit\Licenses\jsmn_license.txt | text | |
MD5:D676C1CB46EB5062BB161695C3E81305 | SHA256:AEEECF333D144F9E87B9C39F0601E5DBF8929E2B5467B5BFED715B61AEBD7A4A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3272 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |