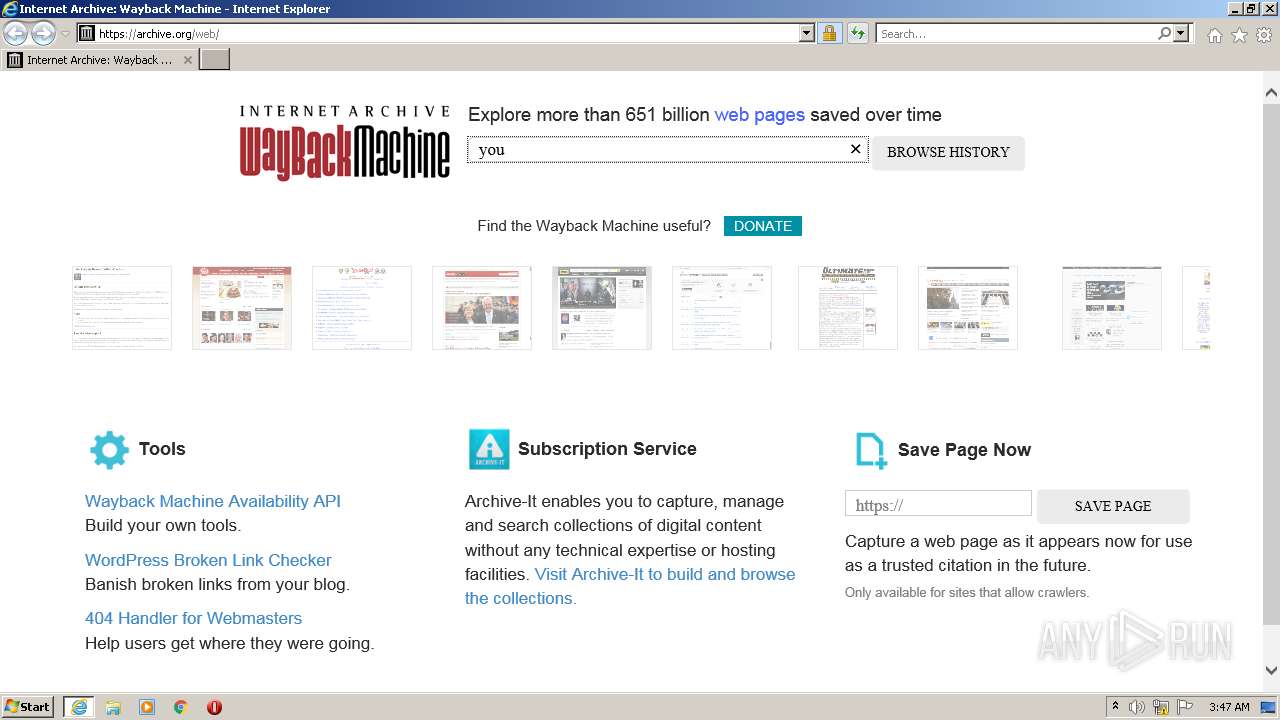
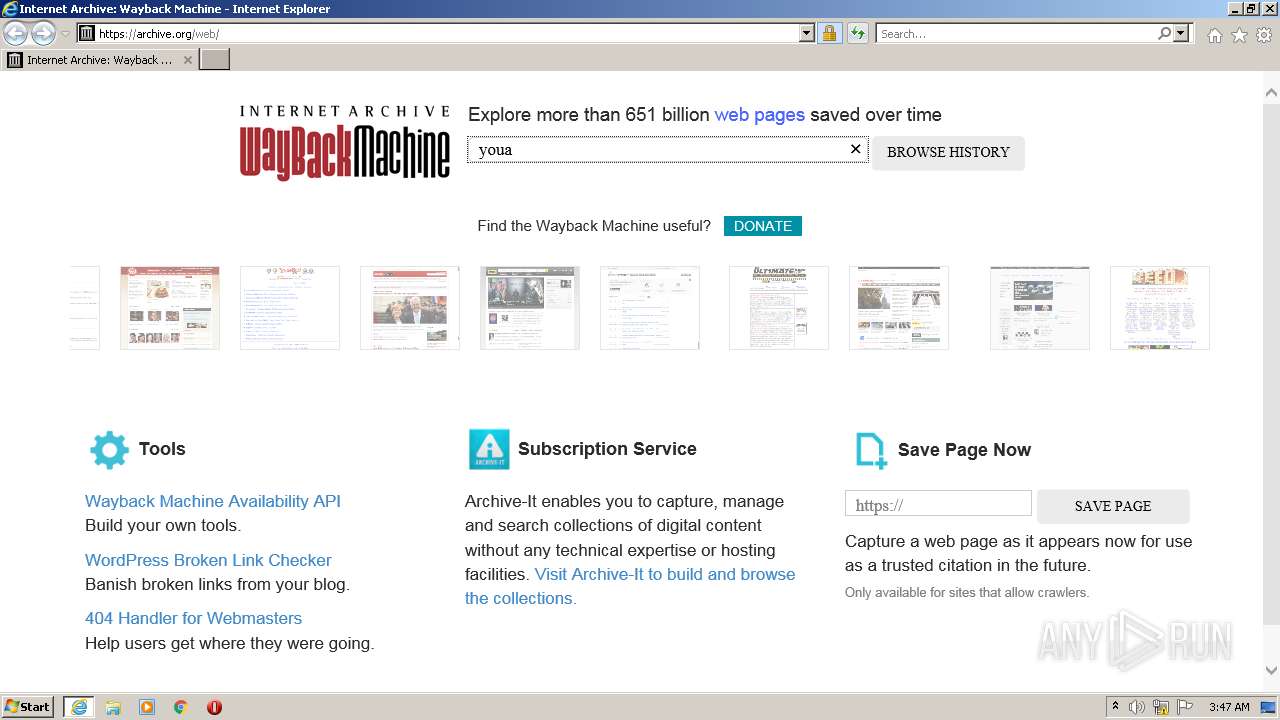
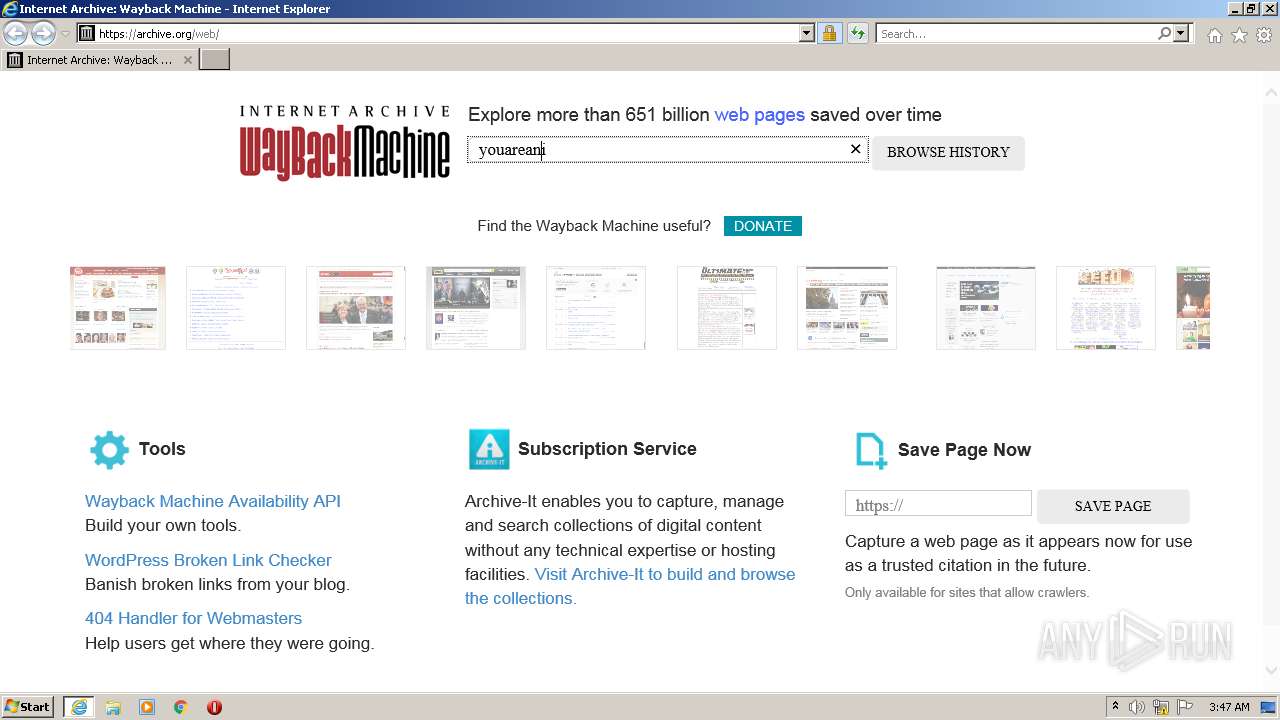
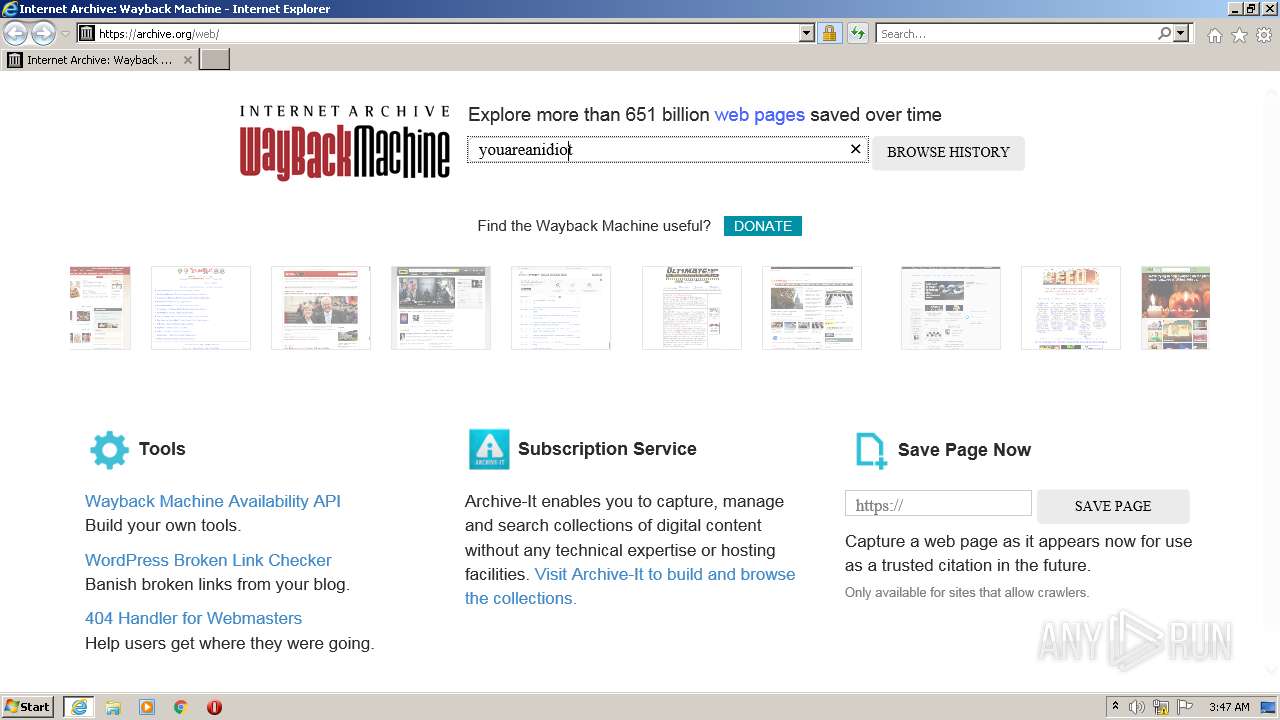
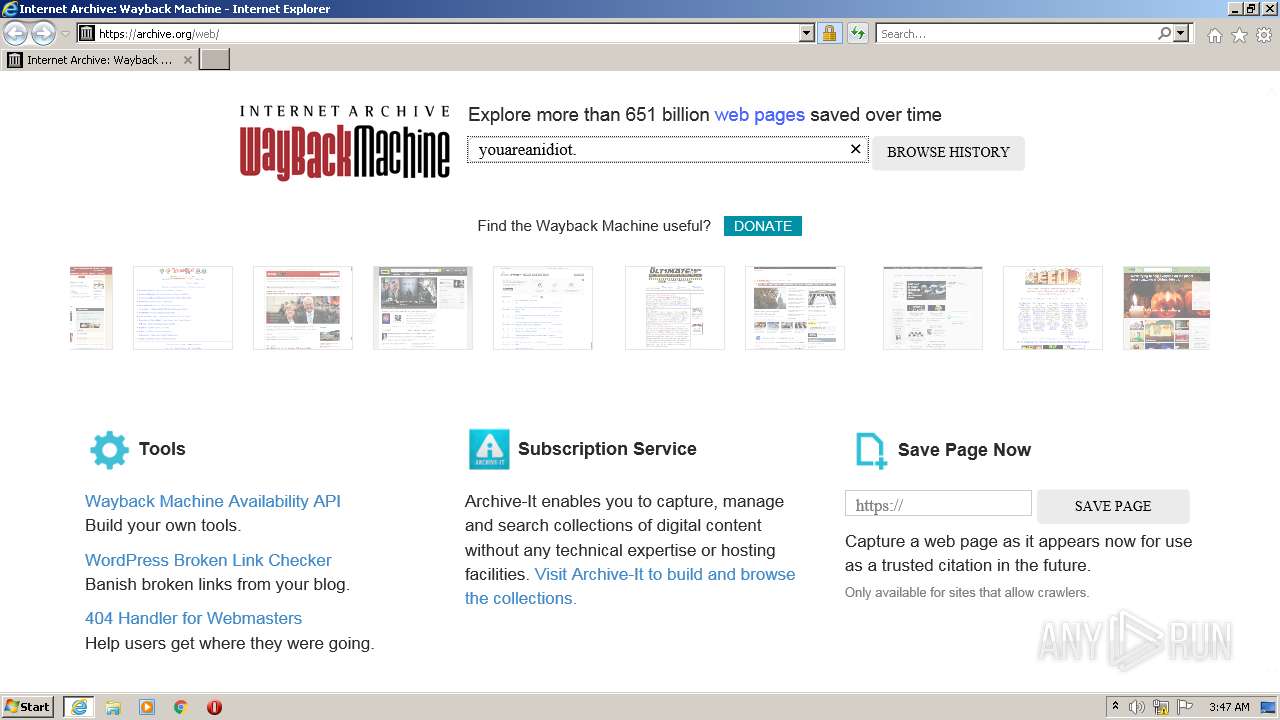
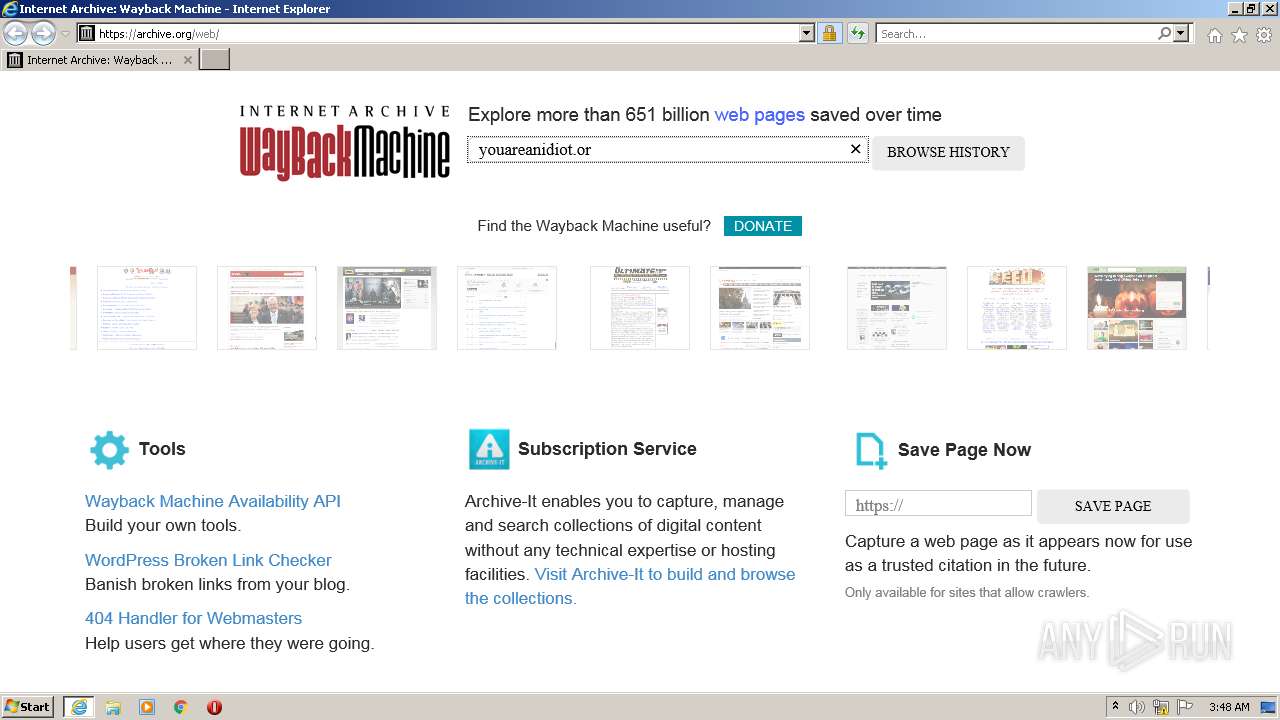
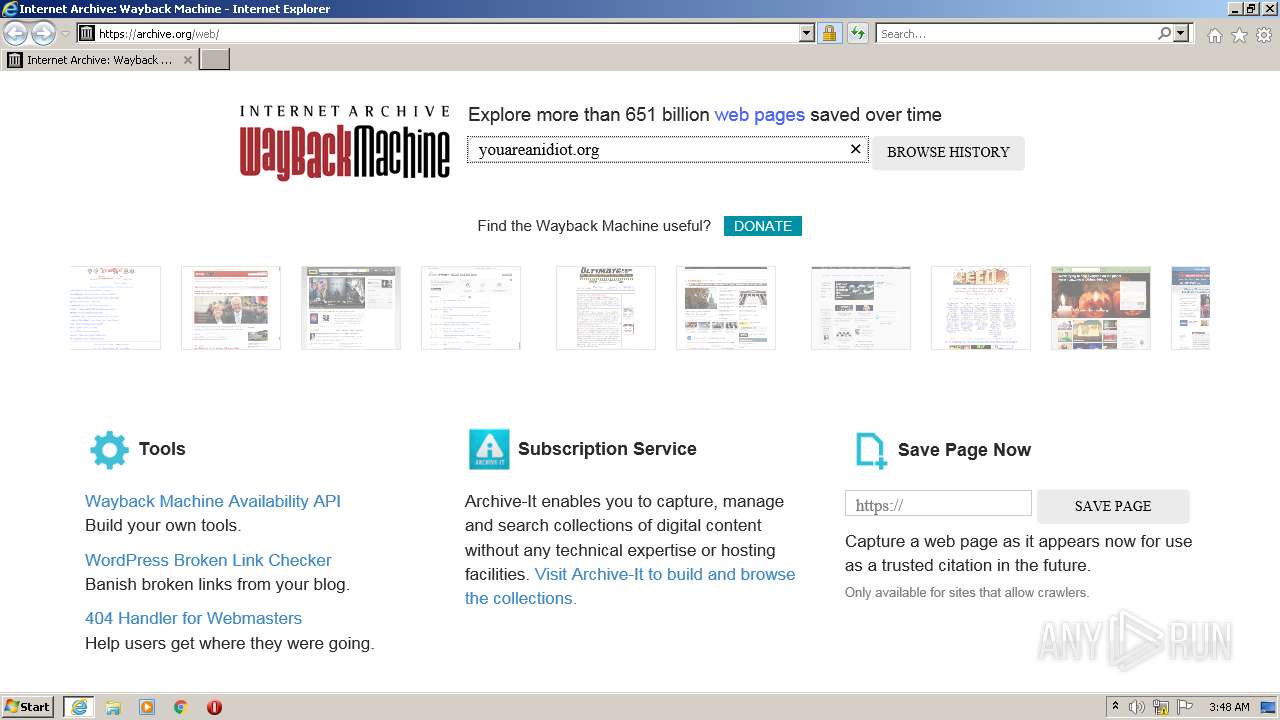
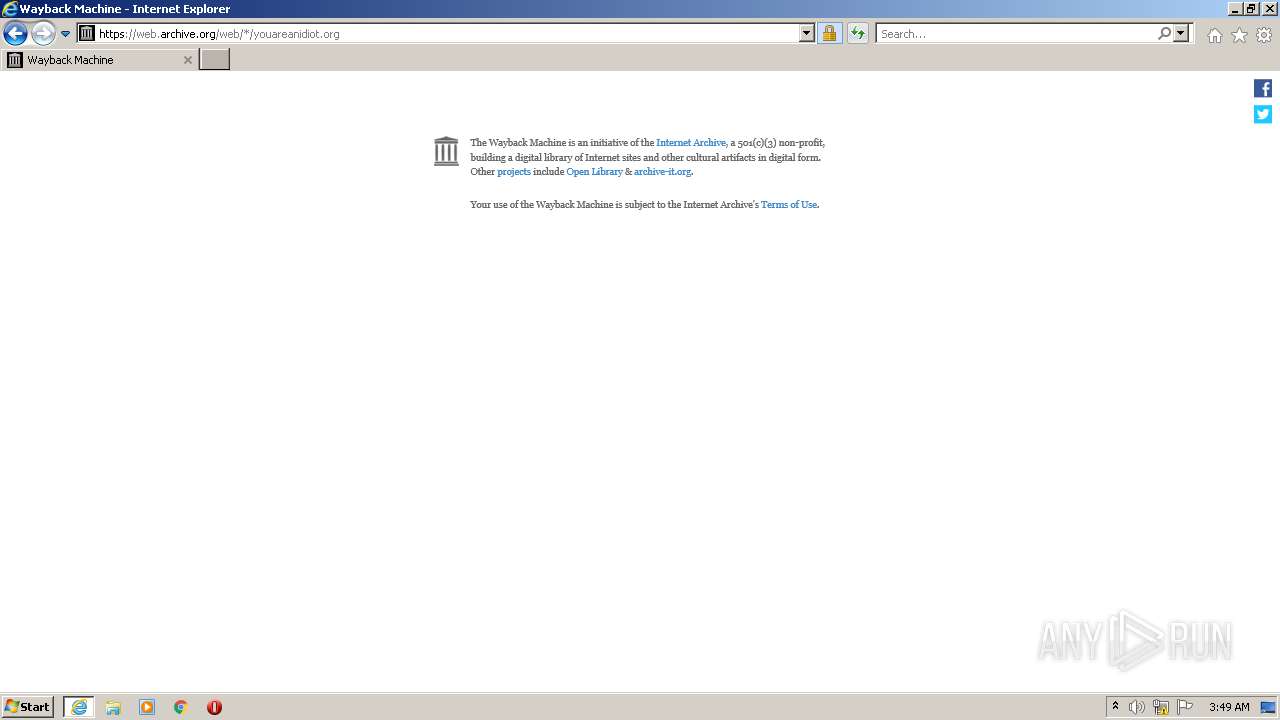
| URL: | https://archive.org/web/ |
| Full analysis: | https://app.any.run/tasks/49e0b297-2c57-4a3d-b435-3c29049a2025 |
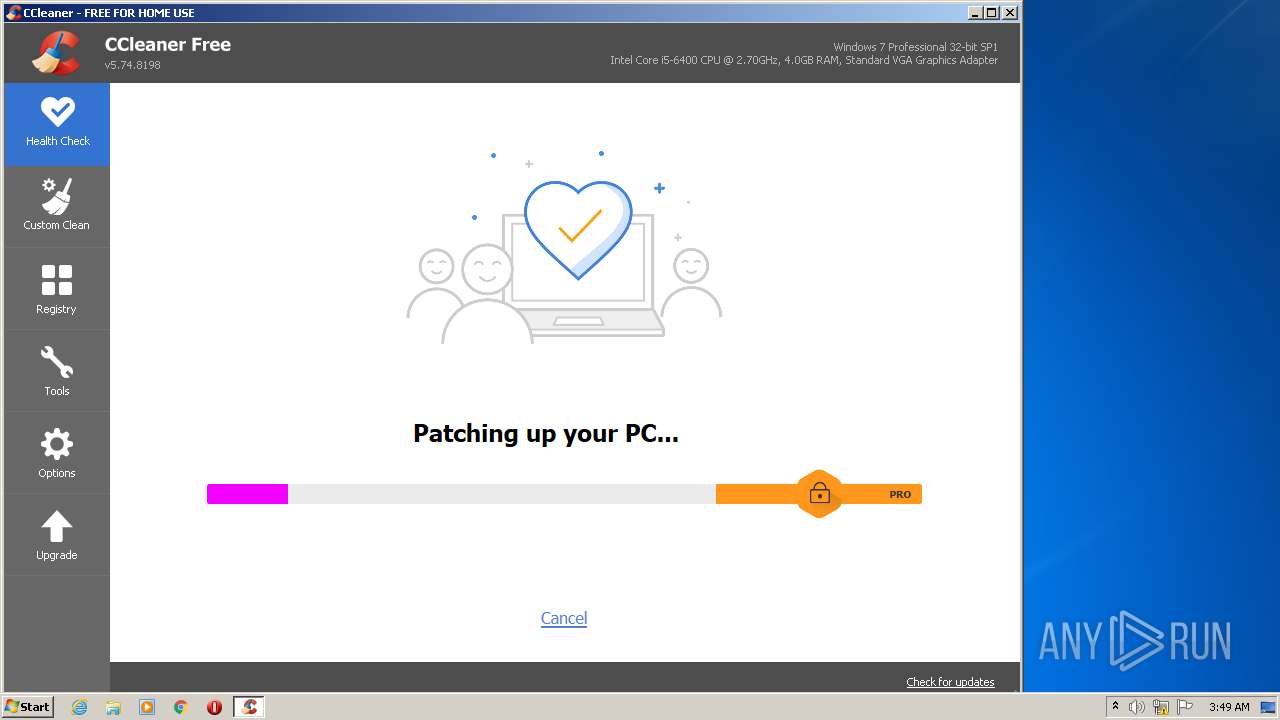
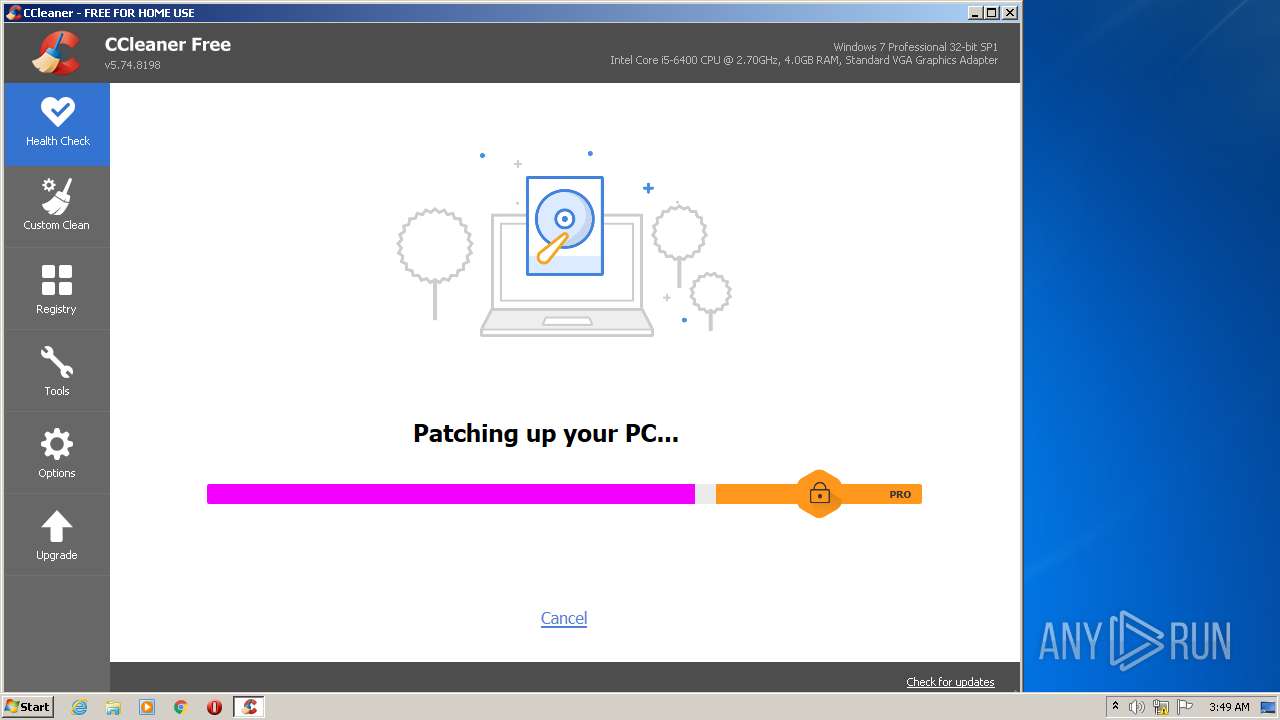
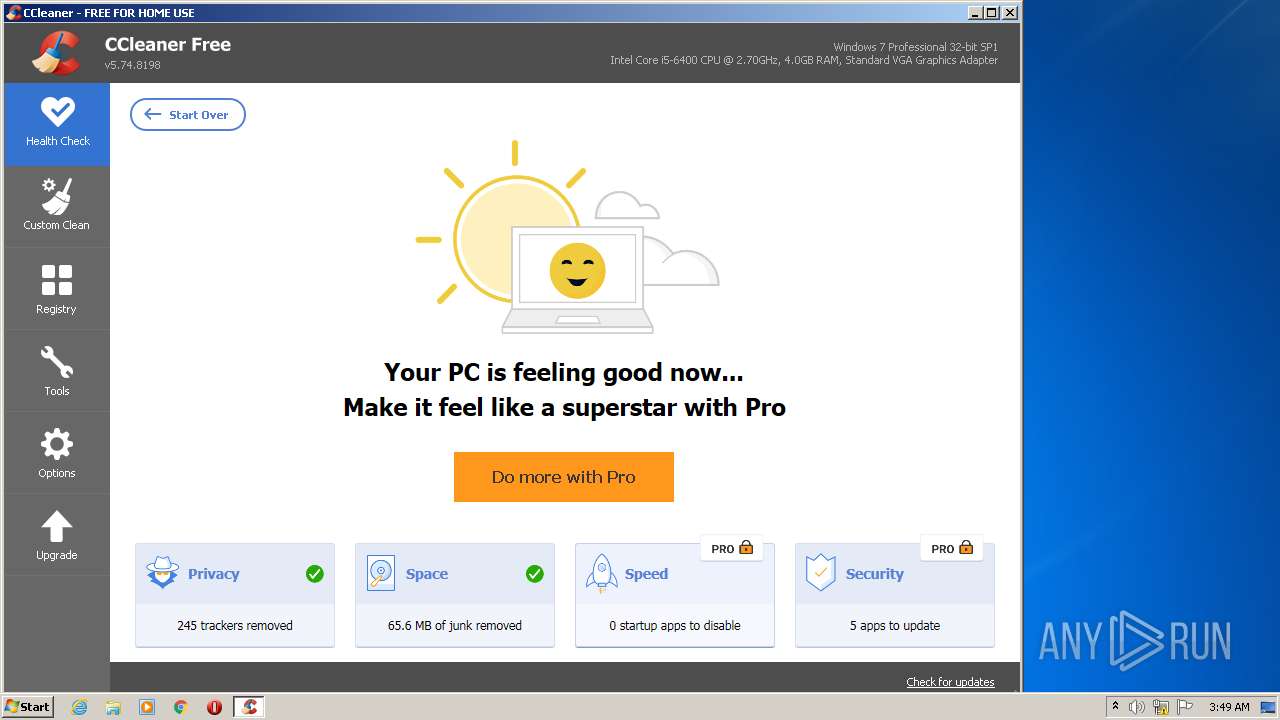
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2022, 03:47:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 015A973BB319D7EF37520B715CE85BCF |
| SHA1: | 8780CAD1966EBF1D2987C79FB3553D8135F8E176 |
| SHA256: | 802BDD65302972489FF289258A7A9B6239ED8FEC21DA027420BB34CE9F8418BE |
| SSDEEP: | 3:N8MFXJen:2MFX8n |
MALICIOUS
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 3576)
- CCleaner.exe (PID: 2192)
Drops executable file immediately after starts
- CCleaner.exe (PID: 2192)
Loads dropped or rewritten executable
- CCleaner.exe (PID: 2192)
Changes settings of System certificates
- CCleaner.exe (PID: 2192)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 2192)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2192)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3892)
Reads Environment values
- CCleaner.exe (PID: 3576)
- CCleaner.exe (PID: 2192)
Checks supported languages
- CCleaner.exe (PID: 3576)
- CCleaner.exe (PID: 2192)
Reads the computer name
- CCleaner.exe (PID: 3576)
- CCleaner.exe (PID: 2192)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 2192)
Reads CPU info
- CCleaner.exe (PID: 2192)
Creates files in the user directory
- CCleaner.exe (PID: 2192)
Executed via Task Scheduler
- CCleaner.exe (PID: 2192)
Creates files in the program directory
- CCleaner.exe (PID: 2192)
Drops a file that was compiled in debug mode
- CCleaner.exe (PID: 2192)
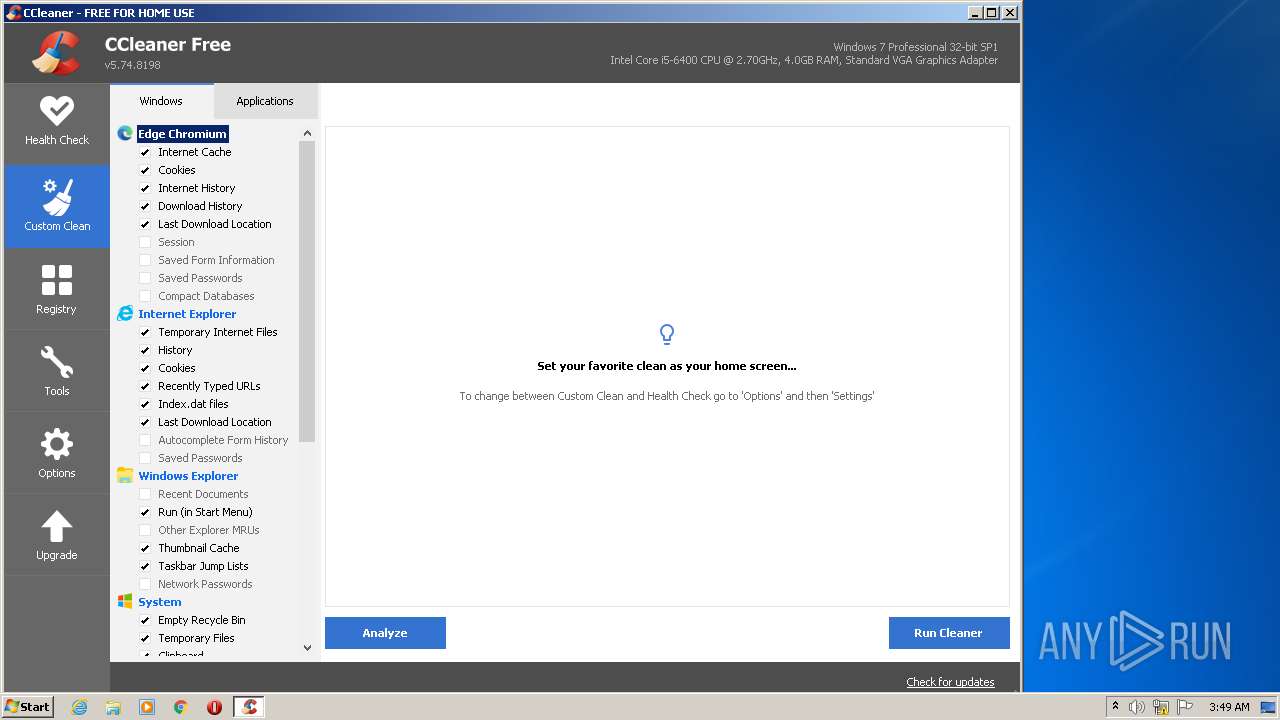
Reads internet explorer settings
- CCleaner.exe (PID: 2192)
Reads the date of Windows installation
- CCleaner.exe (PID: 2192)
Executed as Windows Service
- taskhost.exe (PID: 3660)
- taskhost.exe (PID: 3124)
- taskhost.exe (PID: 1644)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 2192)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2192)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 2192)
Removes files from Windows directory
- CCleaner.exe (PID: 2192)
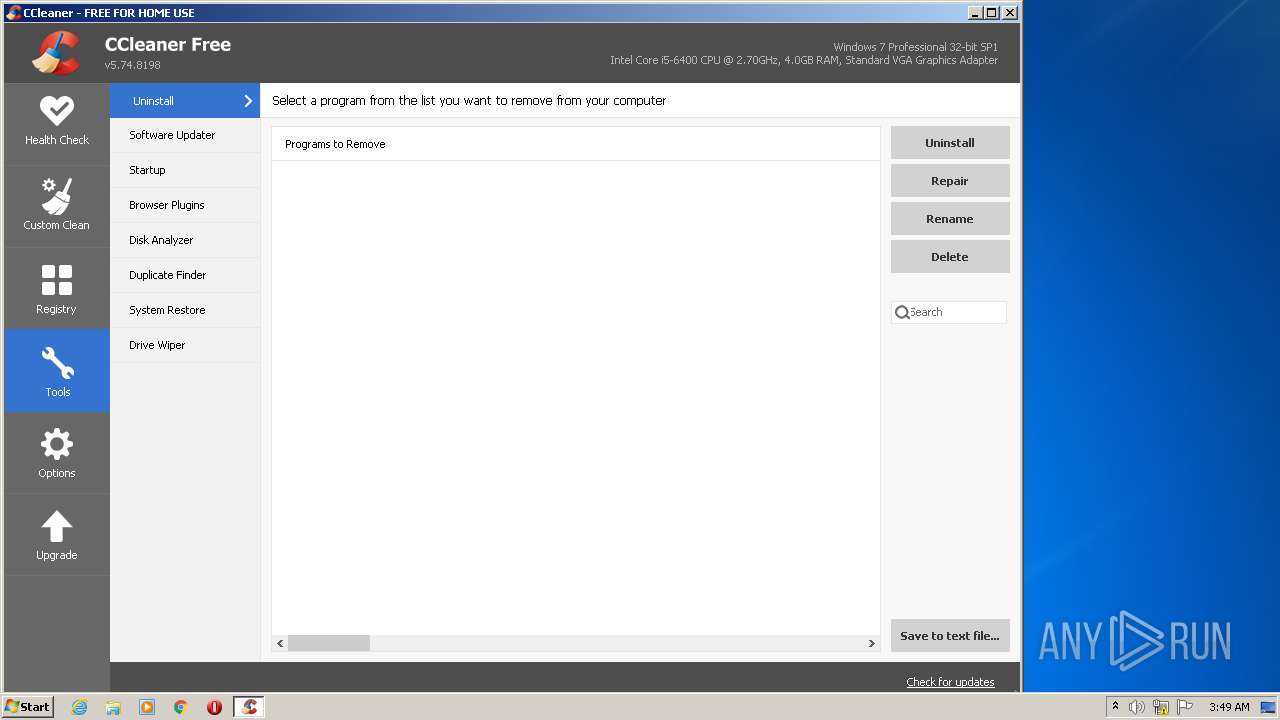
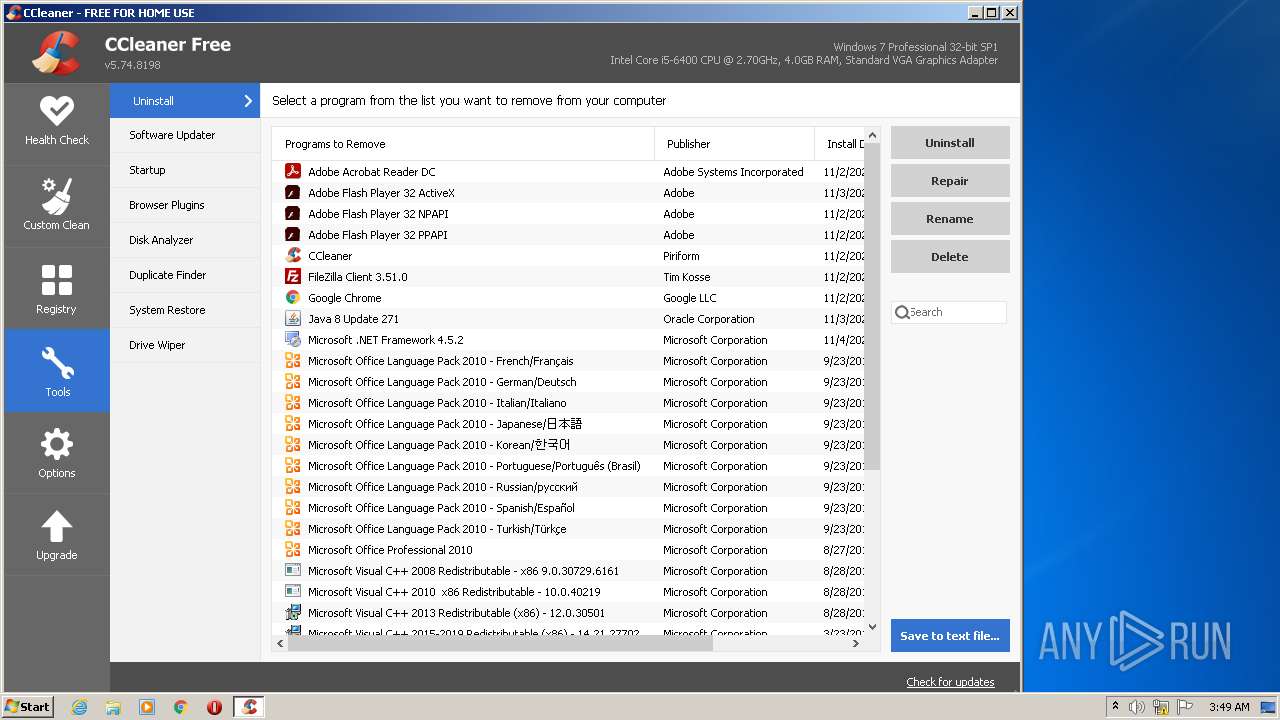
Searches for installed software
- CCleaner.exe (PID: 2192)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3464)
Checks supported languages
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 3892)
- taskhost.exe (PID: 3660)
- taskhost.exe (PID: 3124)
- taskhost.exe (PID: 1644)
Reads the computer name
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 3892)
- taskhost.exe (PID: 3124)
- taskhost.exe (PID: 3660)
- taskhost.exe (PID: 1644)
Application launched itself
- iexplore.exe (PID: 3464)
Reads settings of System Certificates
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 3464)
- CCleaner.exe (PID: 2192)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3464)
Checks Windows Trust Settings
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 3892)
- CCleaner.exe (PID: 2192)
Creates files in the user directory
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 3464)
Reads internet explorer settings
- iexplore.exe (PID: 3892)
Changes settings of System certificates
- iexplore.exe (PID: 3464)
Manual execution by user
- CCleaner.exe (PID: 3576)
Reads the date of Windows installation
- iexplore.exe (PID: 3464)
Reads the hosts file
- CCleaner.exe (PID: 2192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1644 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 3124 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3464 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://archive.org/web/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3576 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 3660 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3464 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
40 952
Read events
40 559
Write events
312
Delete events
81
Modification events
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939111 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939111 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
86
Text files
108
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0158PGF4.txt | text | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BZISF1WX.txt | text | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AC6C86905BFF3B628C4F8B20E8F206D1_3D6BB56FA9E18ECC7DD45ACC748A3BD3 | der | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\regenerator-runtime-polyfill.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
67
DNS requests
35
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2192 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAbenfbX7OfIAhNlcNdQQzE%3D | US | der | 471 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3892 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCB%2BJkTOHdrdg%3D%3D | US | der | 1.74 Kb | whitelisted |
2192 | CCleaner.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
2192 | CCleaner.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/auto?a=0&p=cc&v=5.74.8198&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&o=6.1W3&au=0&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | text | 61 b | whitelisted |
2192 | CCleaner.exe | GET | 200 | 151.101.130.109:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.74.8198&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | text | 14 b | whitelisted |
2192 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2192 | CCleaner.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
2192 | CCleaner.exe | GET | 200 | 92.123.225.75:80 | http://ncc.avast.com/ncc.txt | unknown | text | 26 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3464 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3464 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 207.241.239.242:443 | polyfill.archive.org | Internet Archive | US | suspicious |
3892 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3464 | iexplore.exe | 207.241.224.2:443 | archive.org | Internet Archive | US | malicious |
3464 | iexplore.exe | 207.241.237.3:443 | web.archive.org | Internet Archive | US | malicious |
3892 | iexplore.exe | 207.241.237.3:443 | web.archive.org | Internet Archive | US | malicious |
3464 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3892 | iexplore.exe | 207.241.225.102:443 | analytics.archive.org | Internet Archive | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
archive.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
polyfill.archive.org |
| suspicious |
web.archive.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
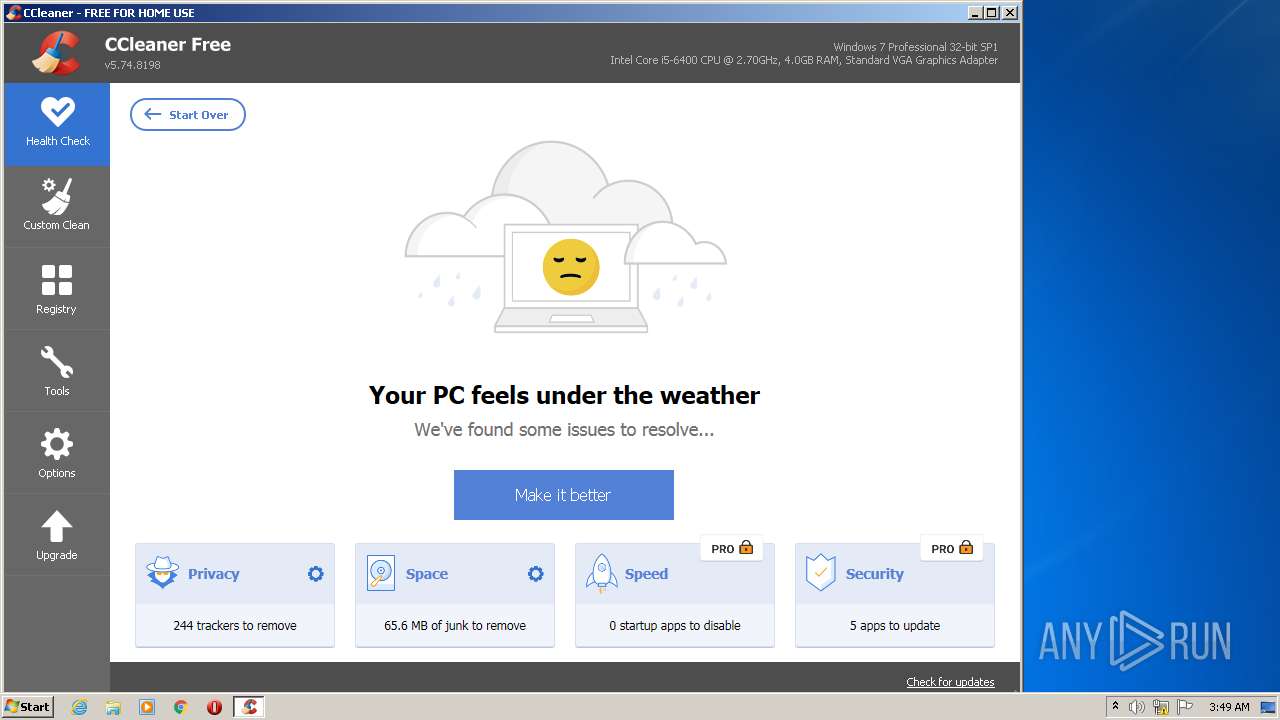
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
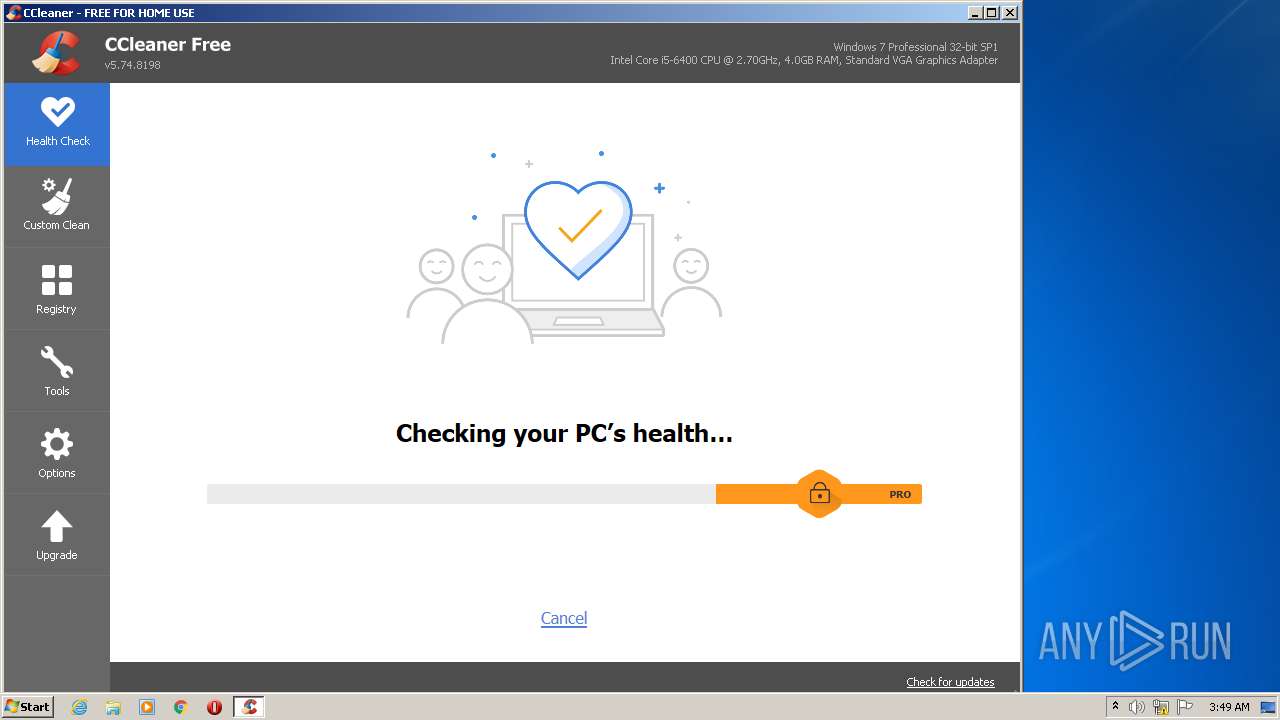
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
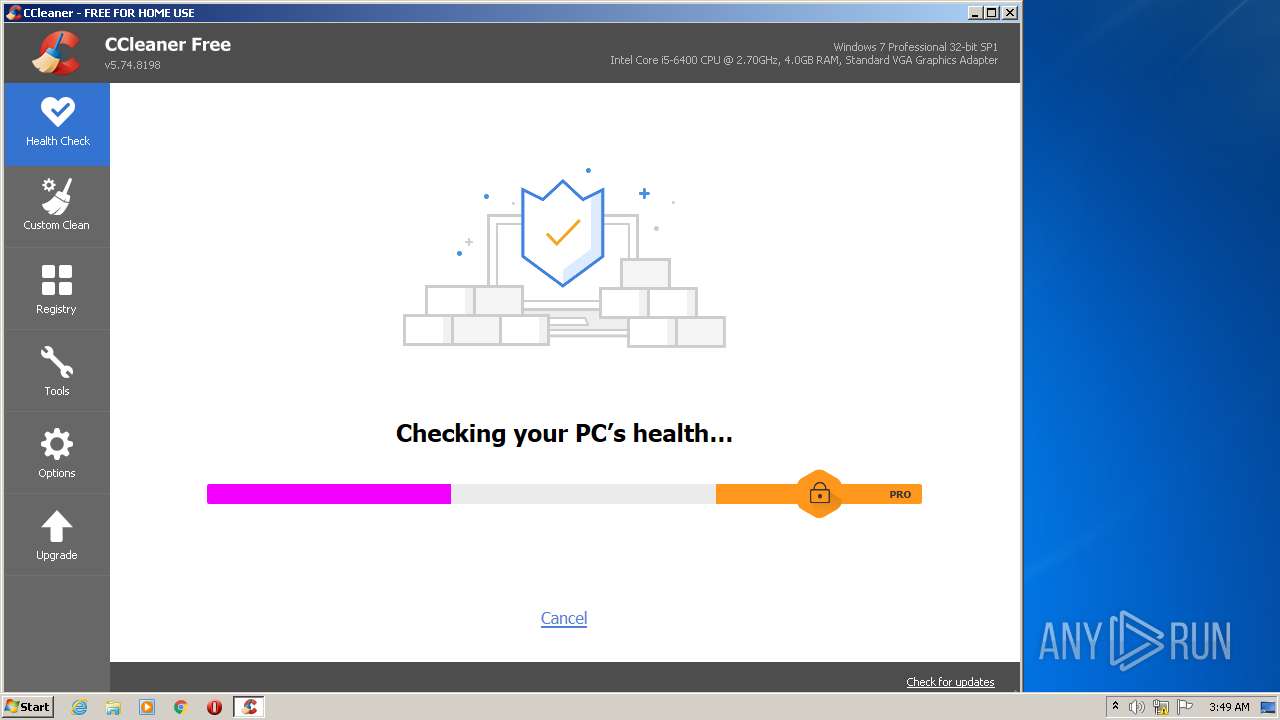
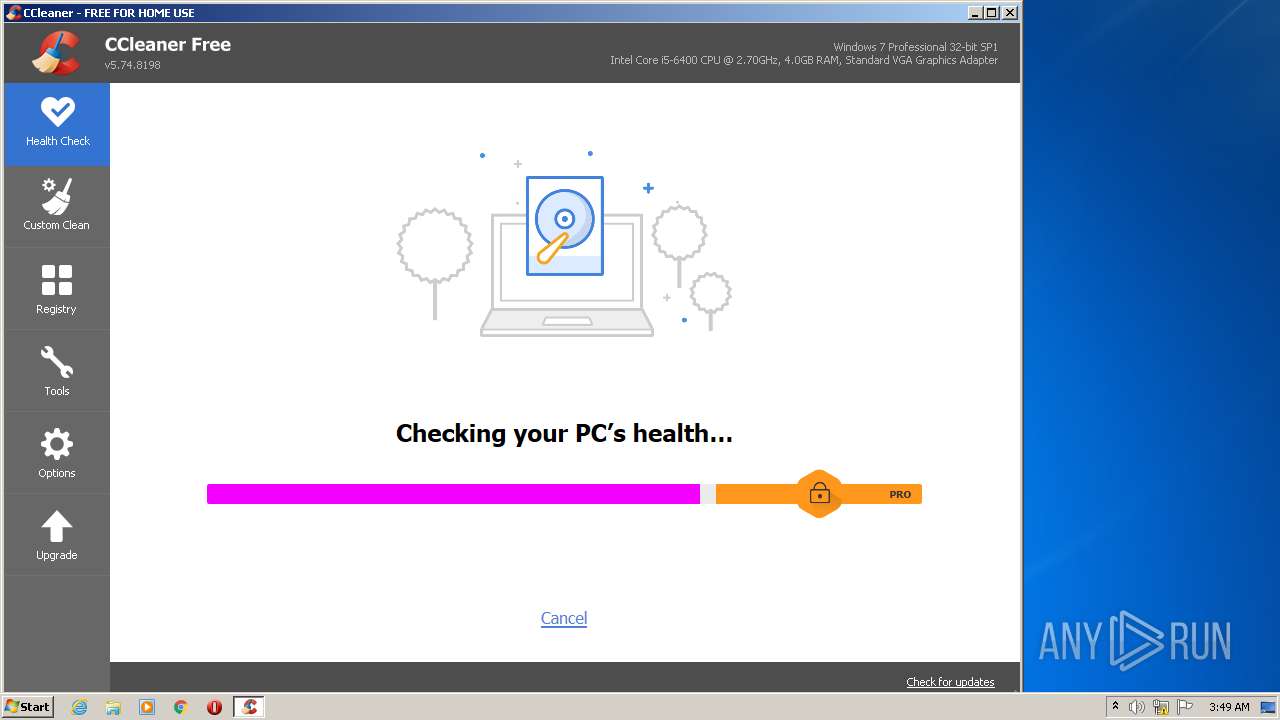
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|
CCleaner.exe | observing currentModeType changed - Preview
|