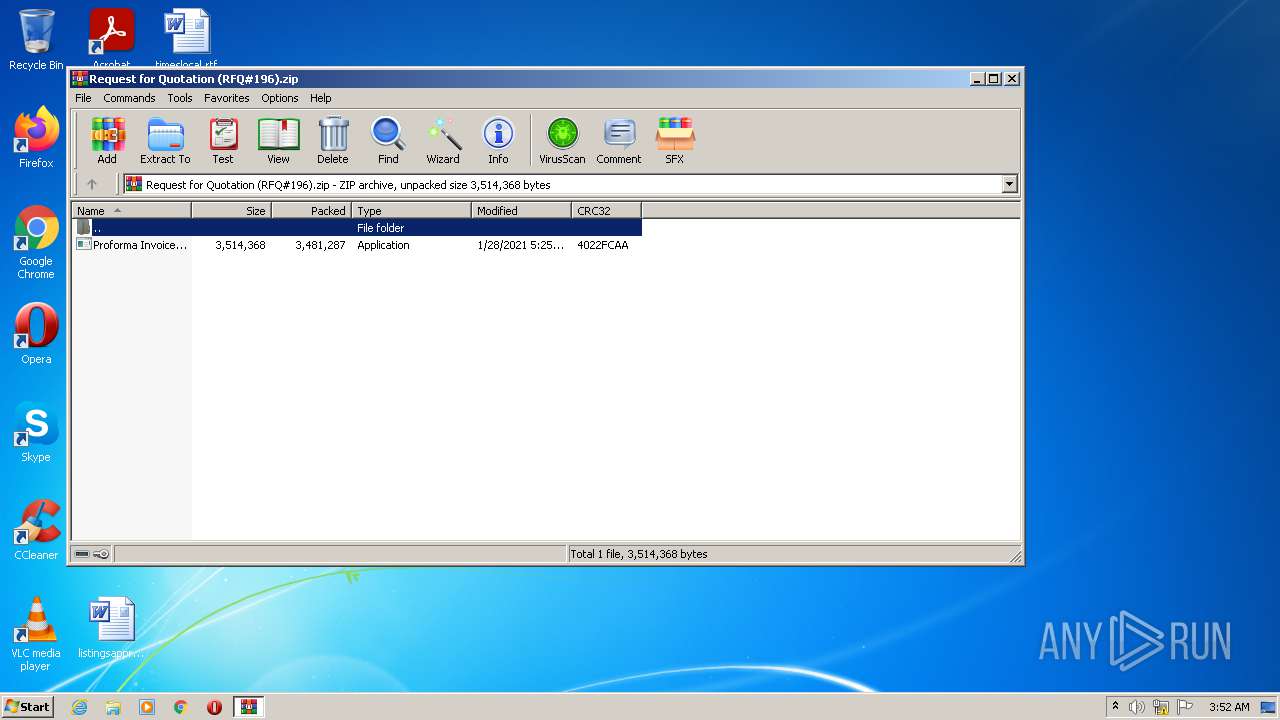
| File name: | Request for Quotation (RFQ#196).zip |
| Full analysis: | https://app.any.run/tasks/b4e9ad42-3597-4d54-a890-725ef3e6cfb4 |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2021, 02:52:20 |
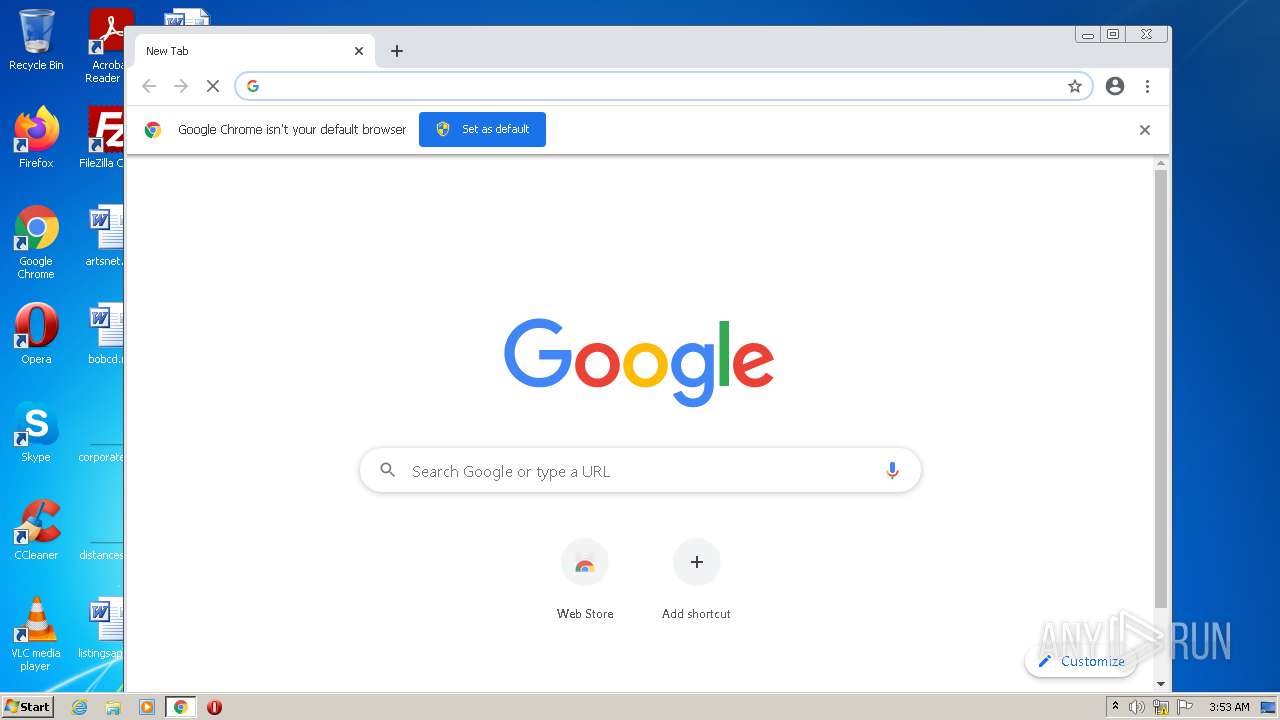
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D69DC6569B385C0467185D002E252D89 |
| SHA1: | 25938A66CCE0078C76A15F351CBD19C8FCC2B081 |
| SHA256: | 80239619C4CA44380C6269873A5B6B695585CCFCF278E0F2C72698658A3A6FD8 |
| SSDEEP: | 49152:pZL1zufKjTpcSPBeJJTXAlSr1/2ueI1HEafmKIDBsuN3FcTuYx/uEjF5RX:/RzvjTCVAlet2XmHxfmKIPNYx/RX |
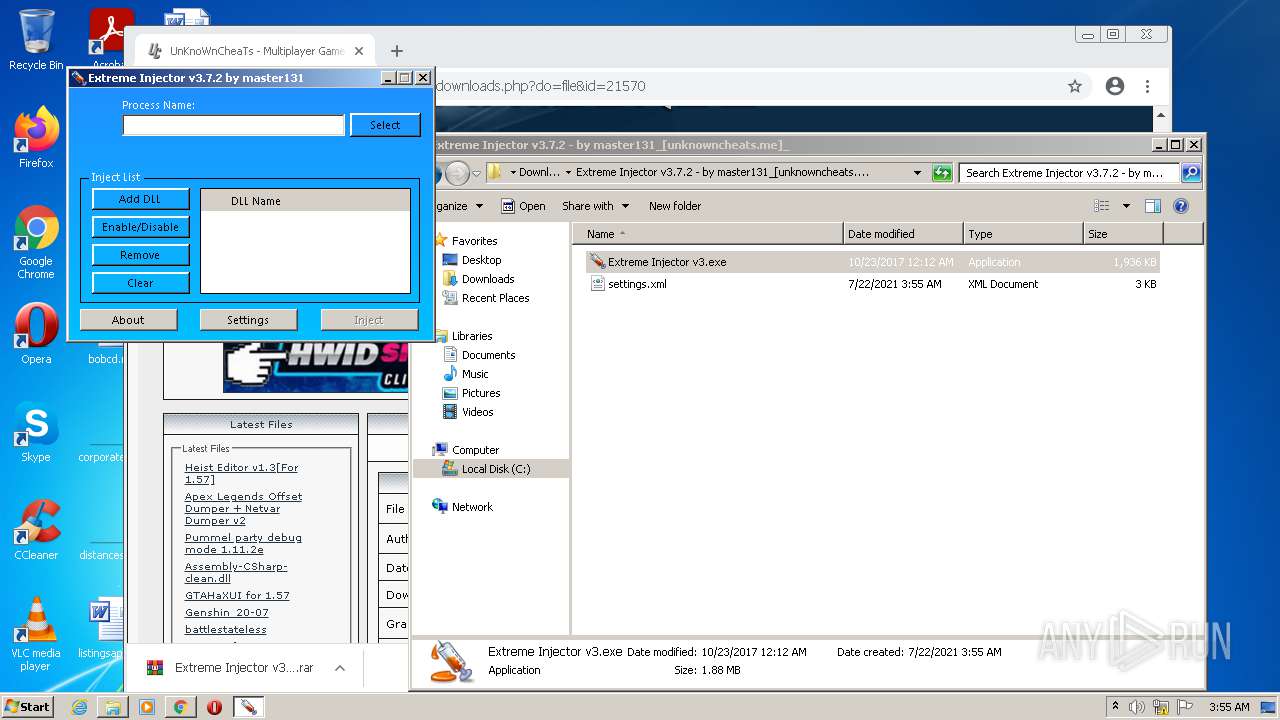
MALICIOUS
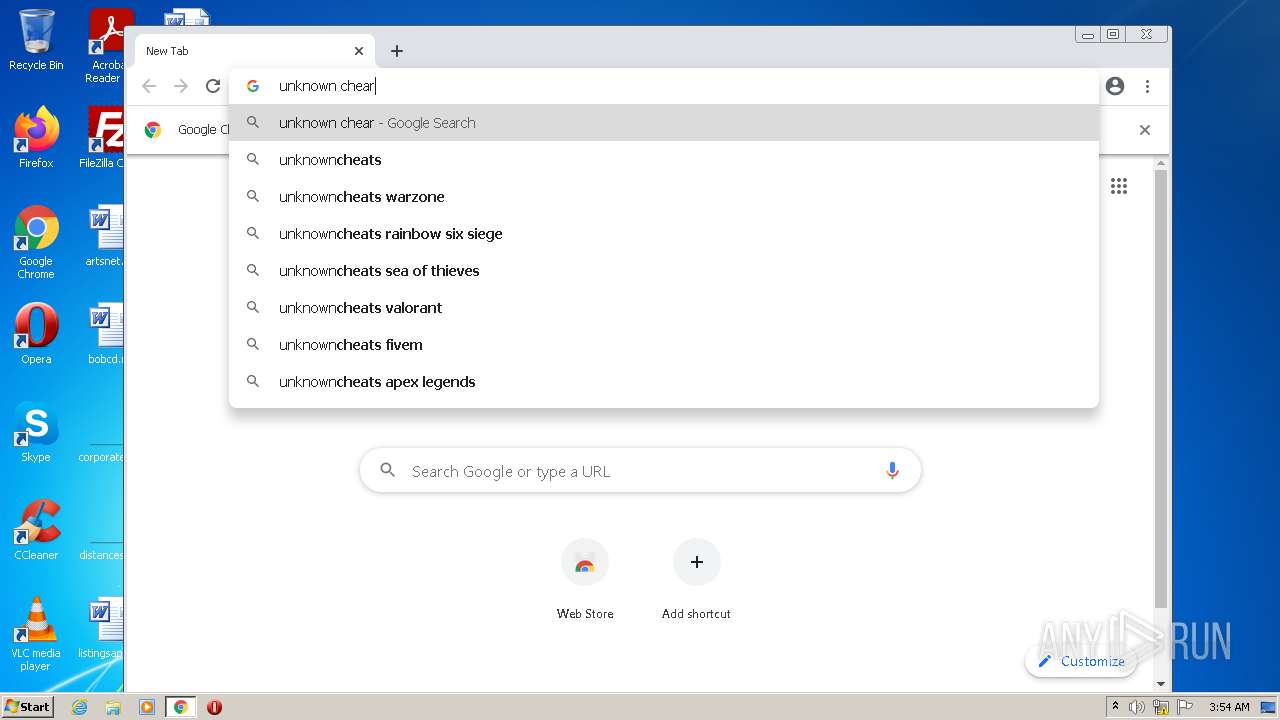
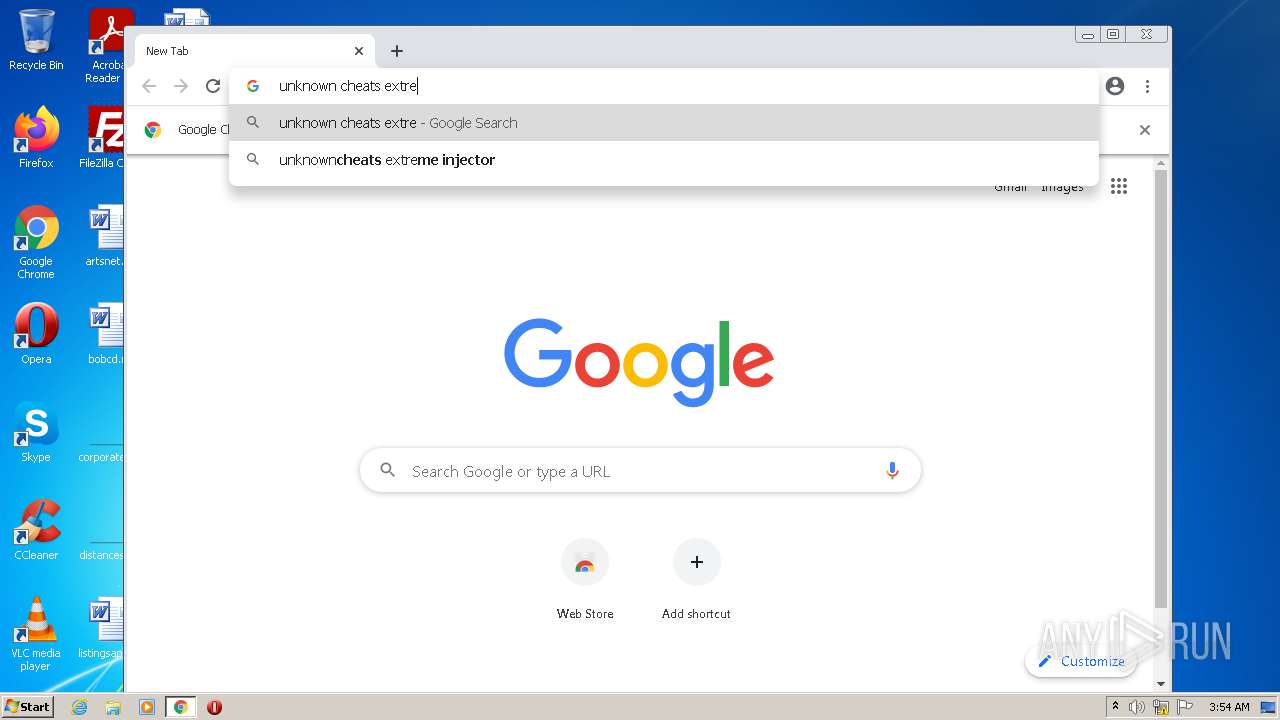
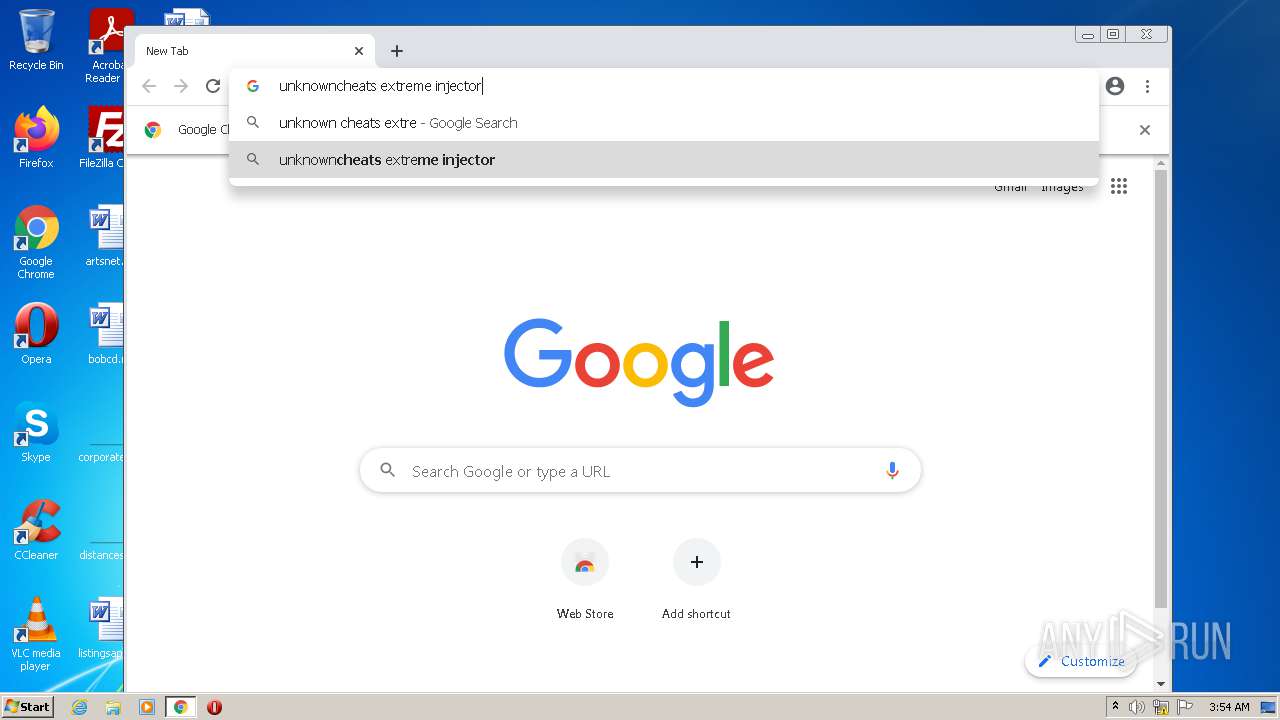
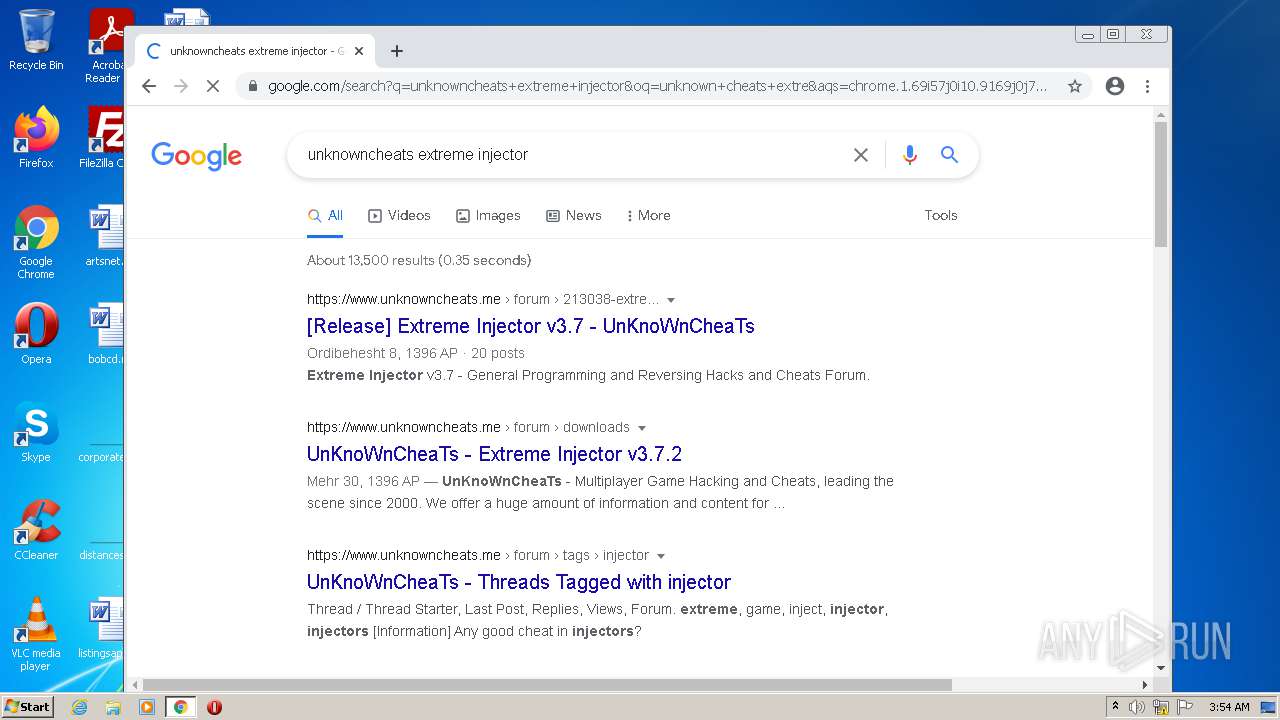
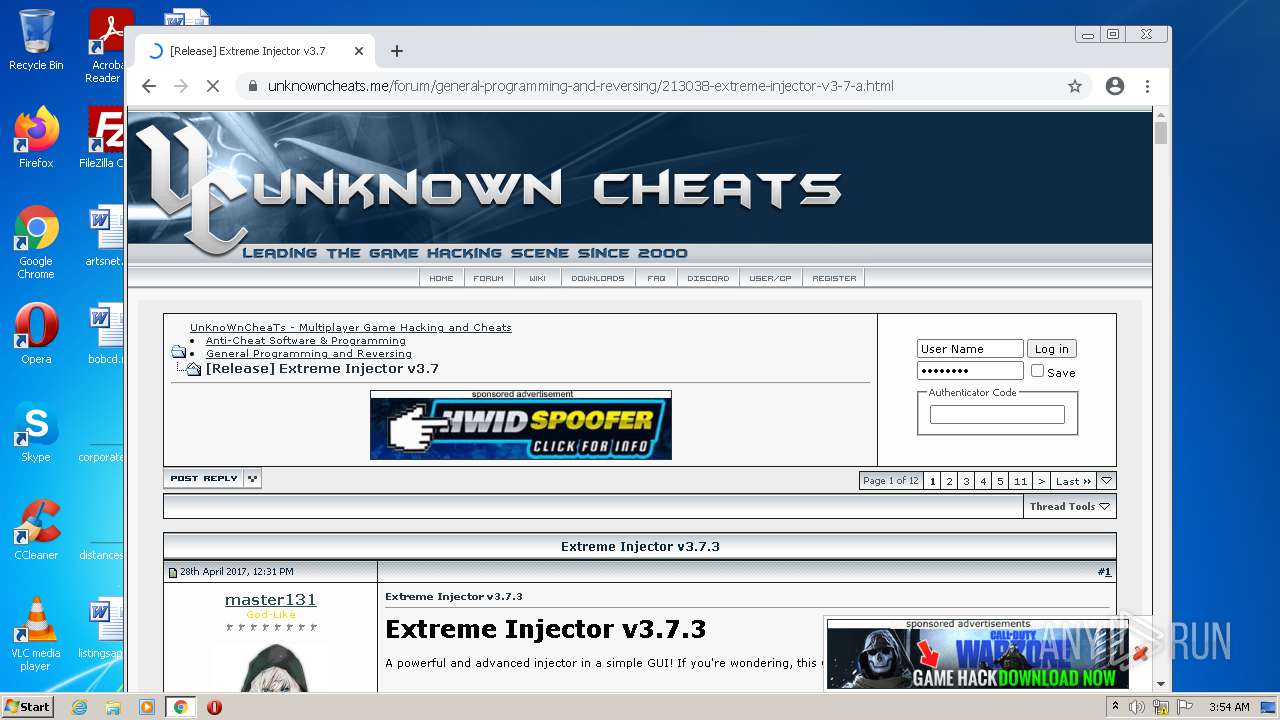
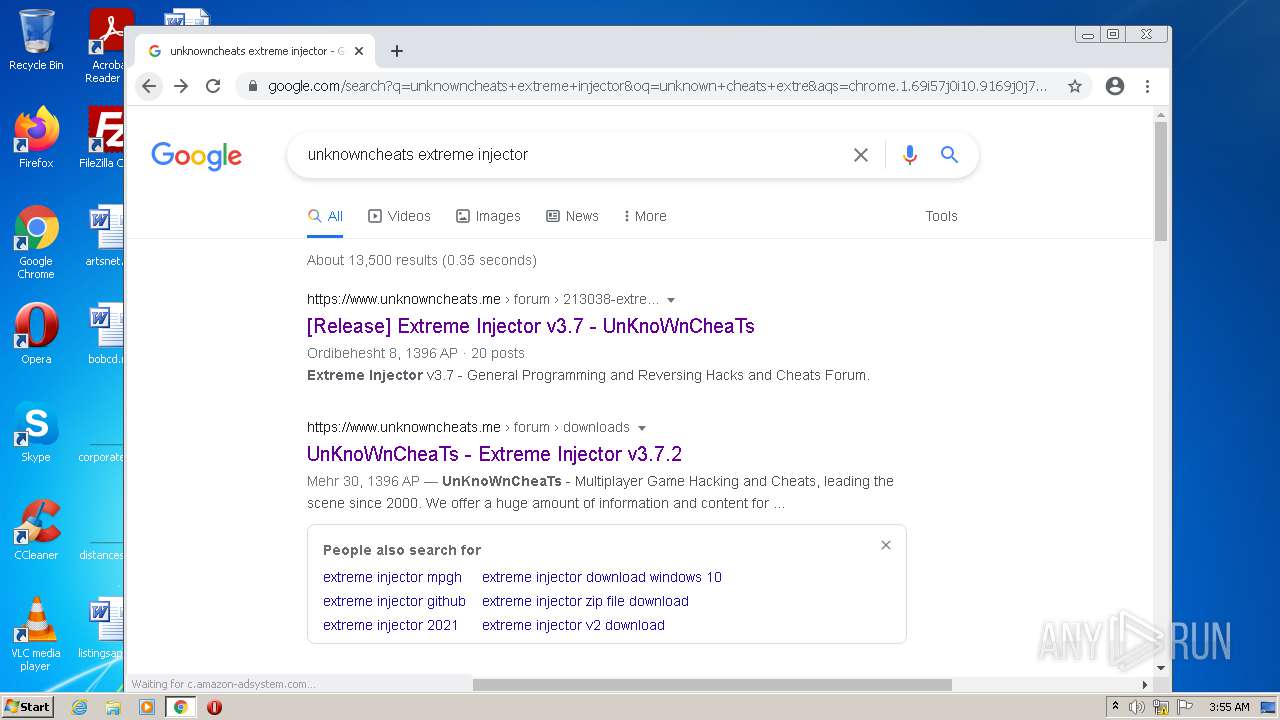
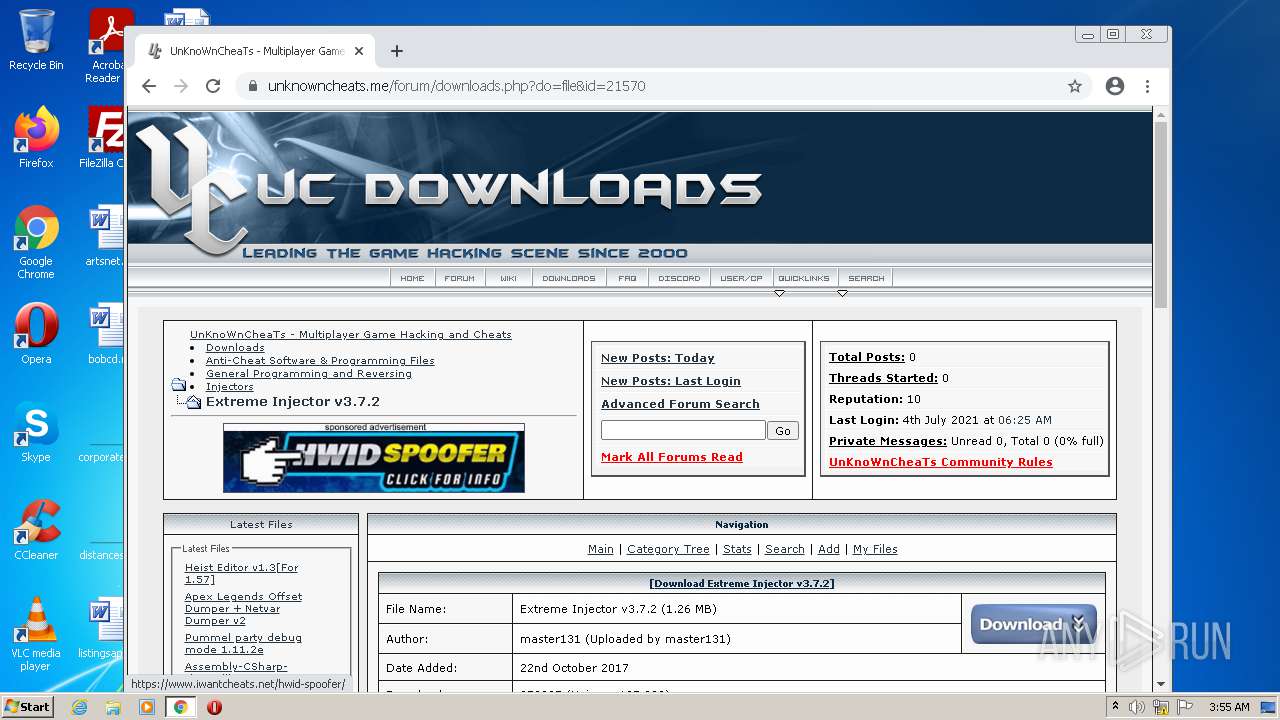
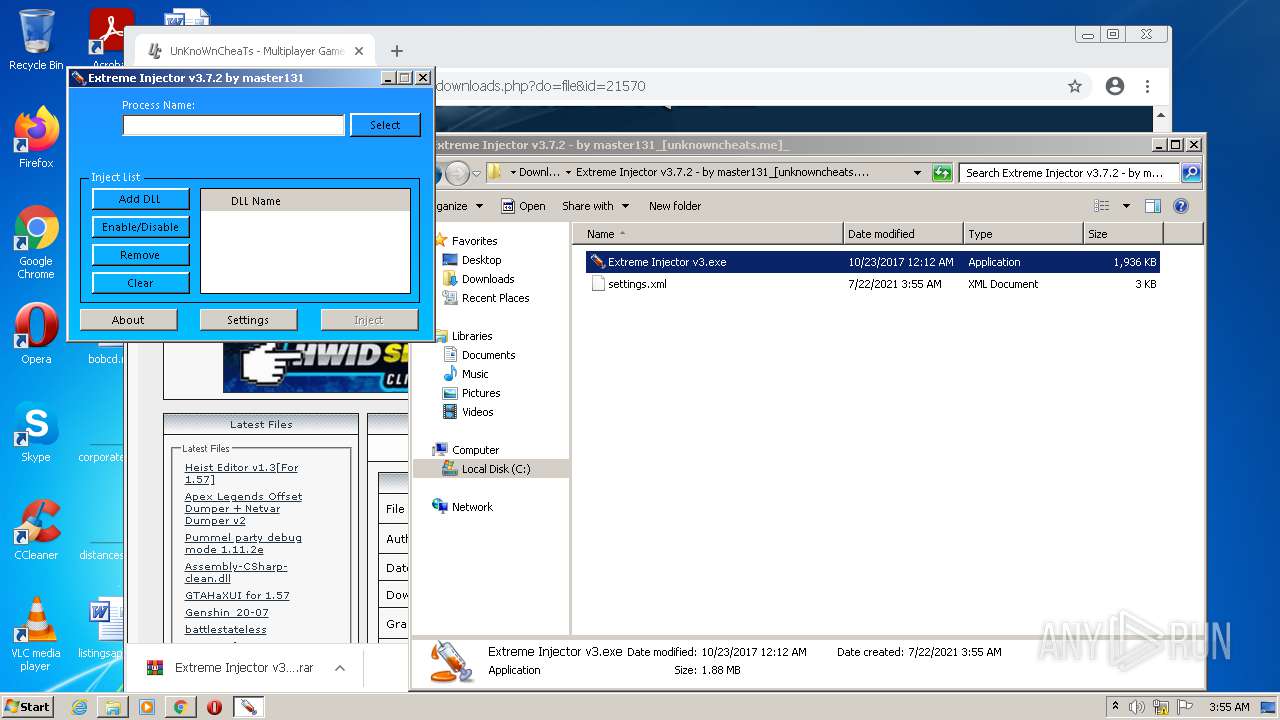
Drops executable file immediately after starts
- chrome.exe (PID: 3200)
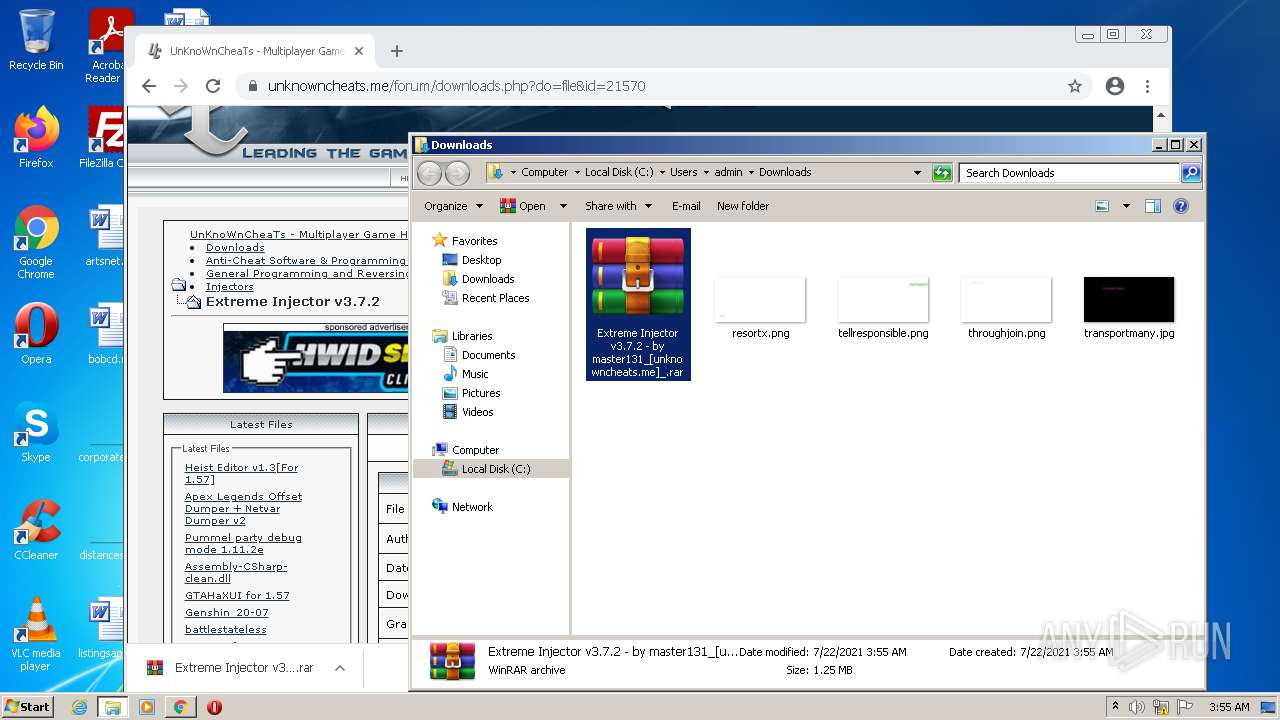
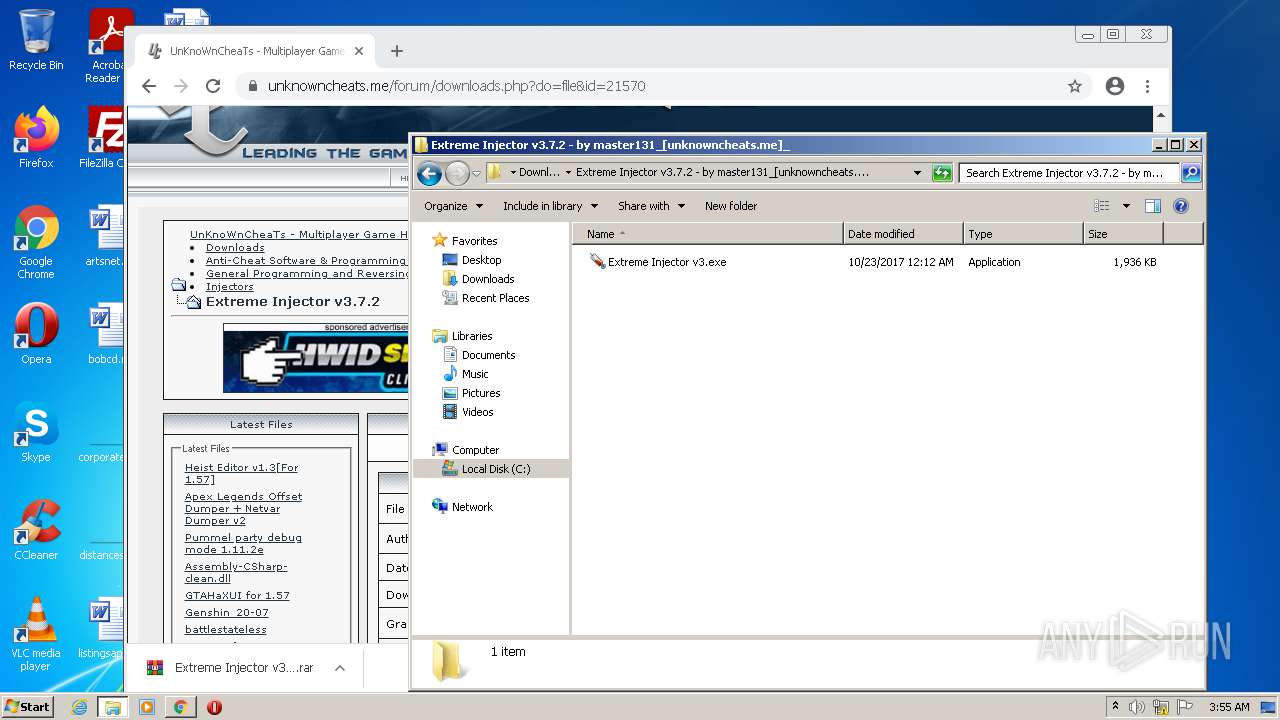
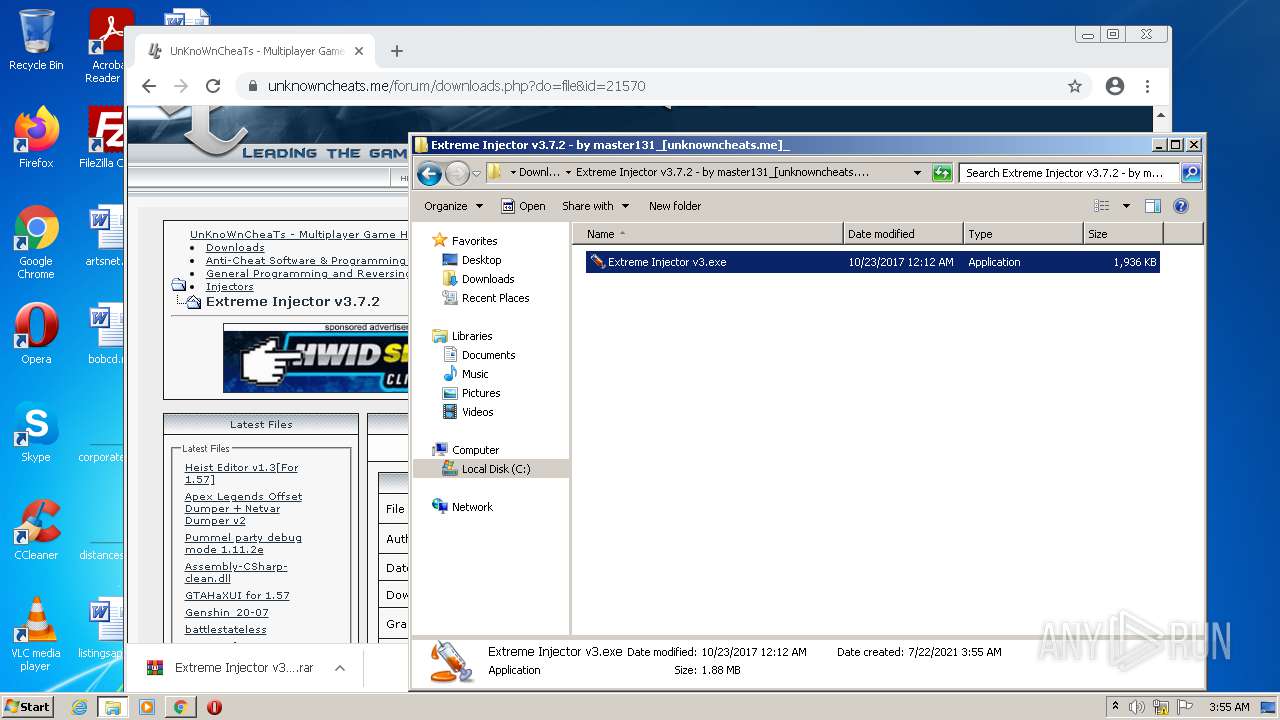
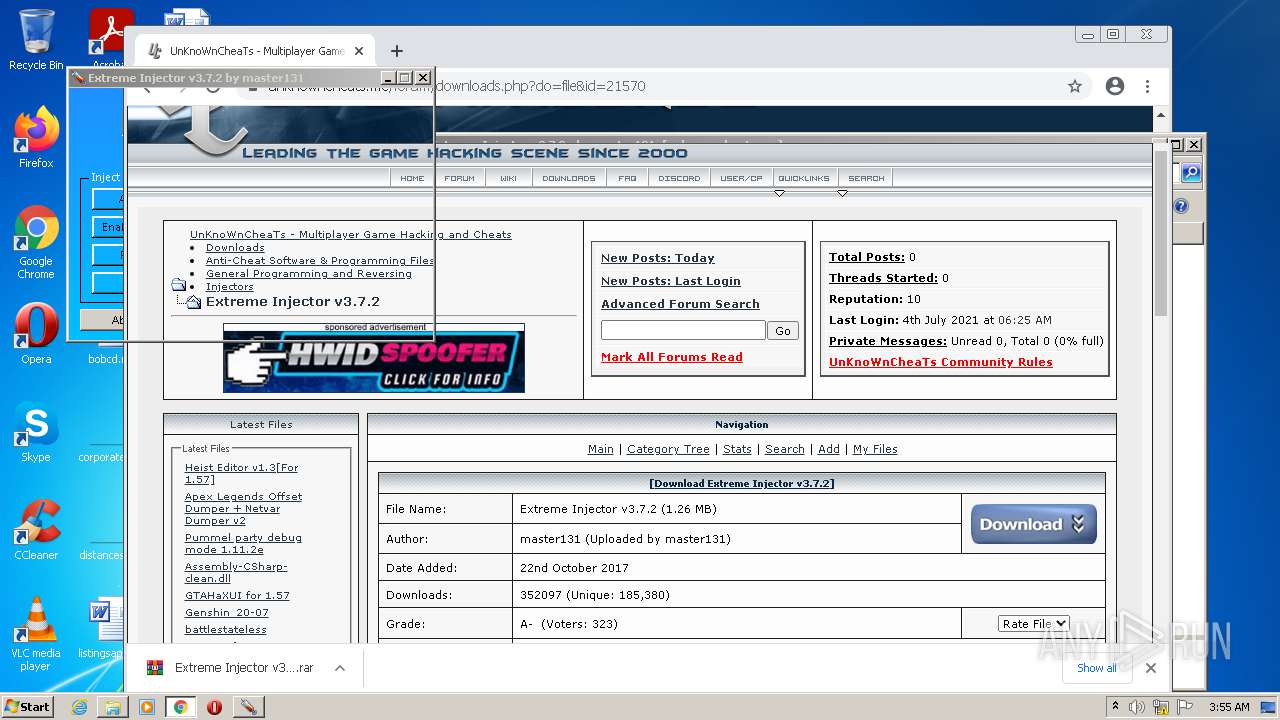
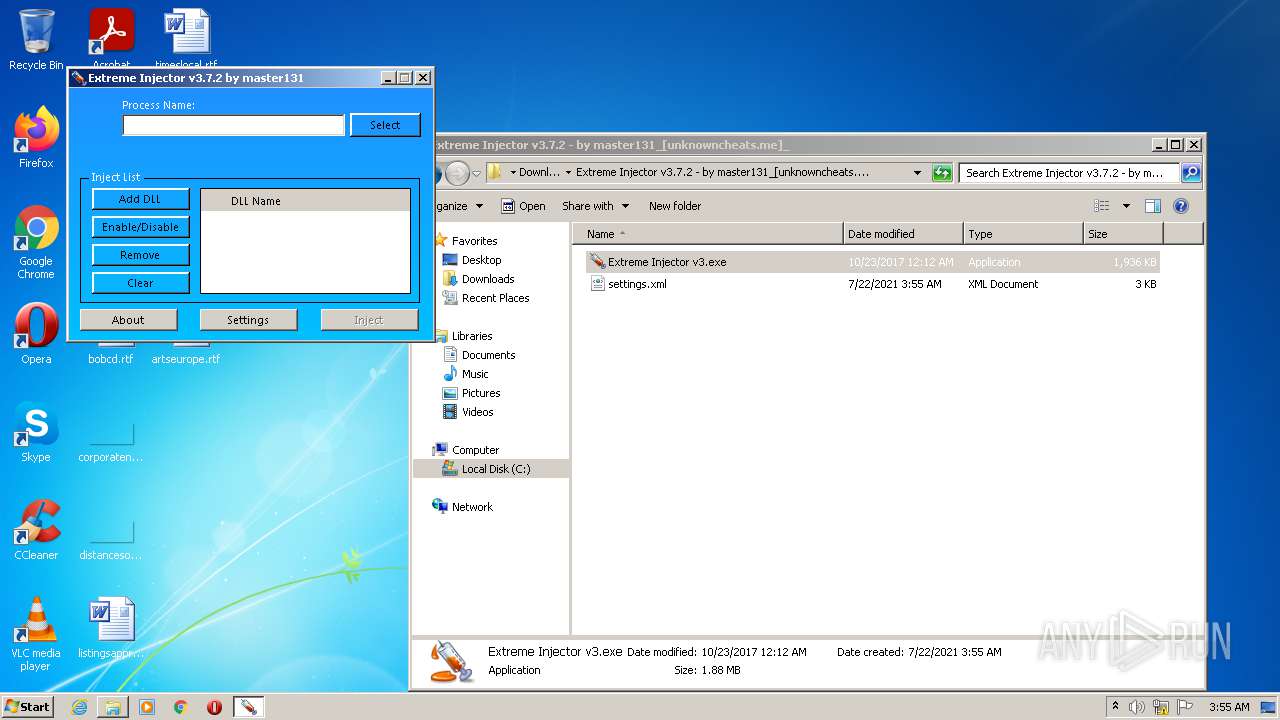
Application was dropped or rewritten from another process
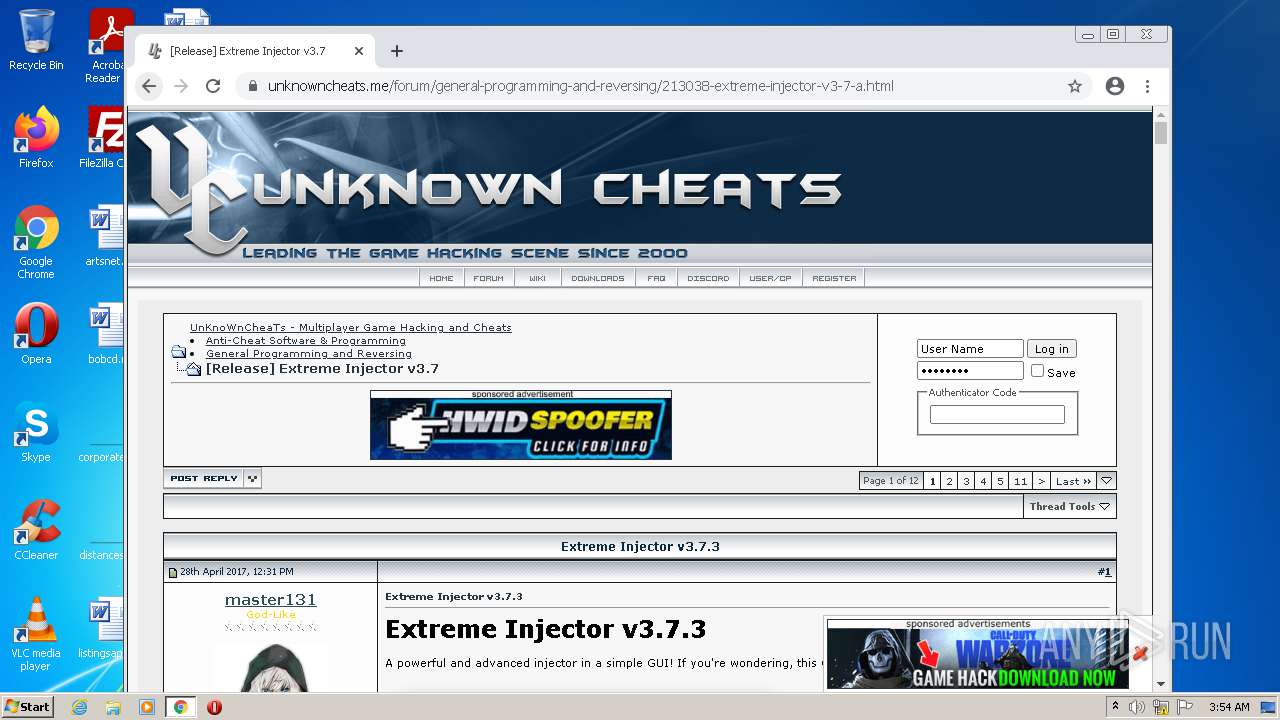
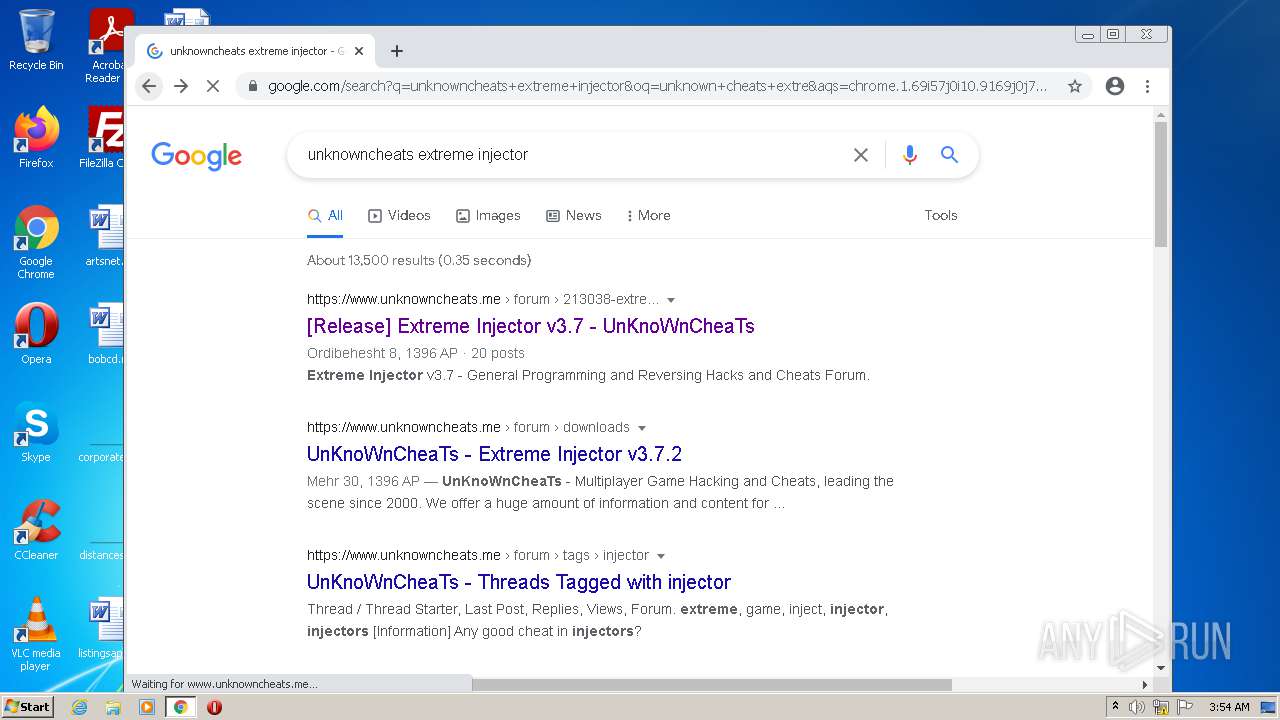
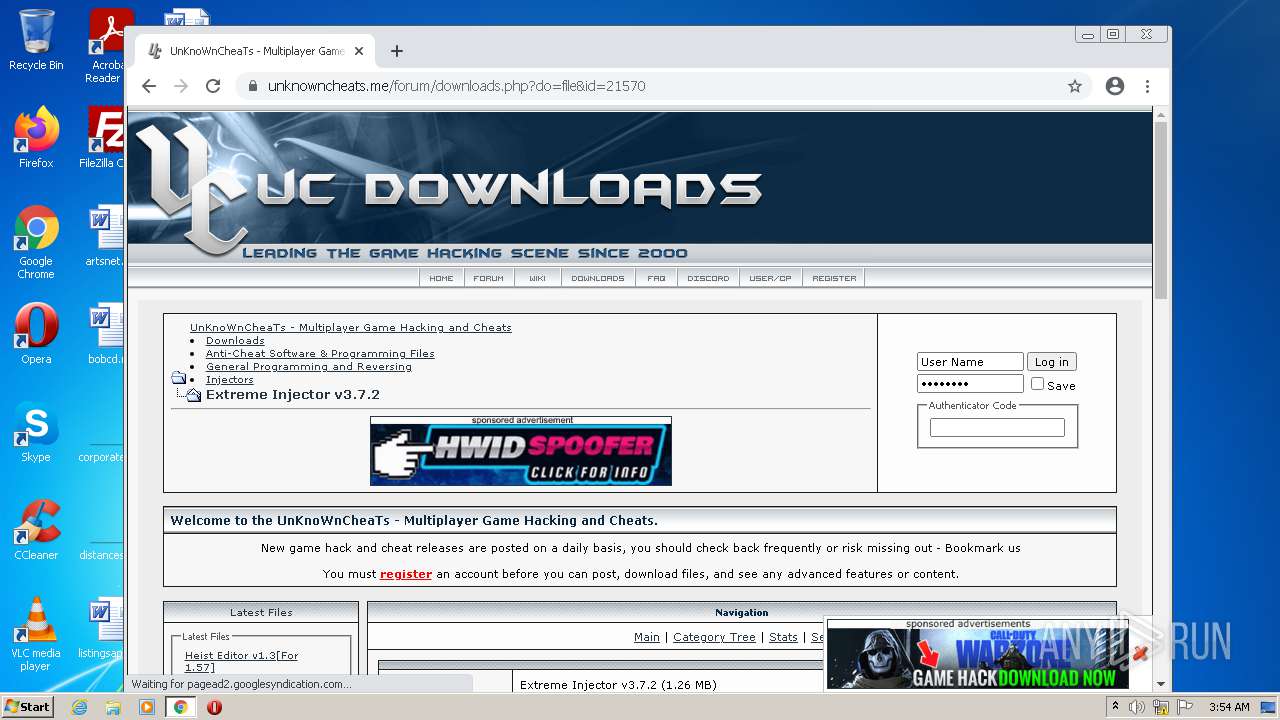
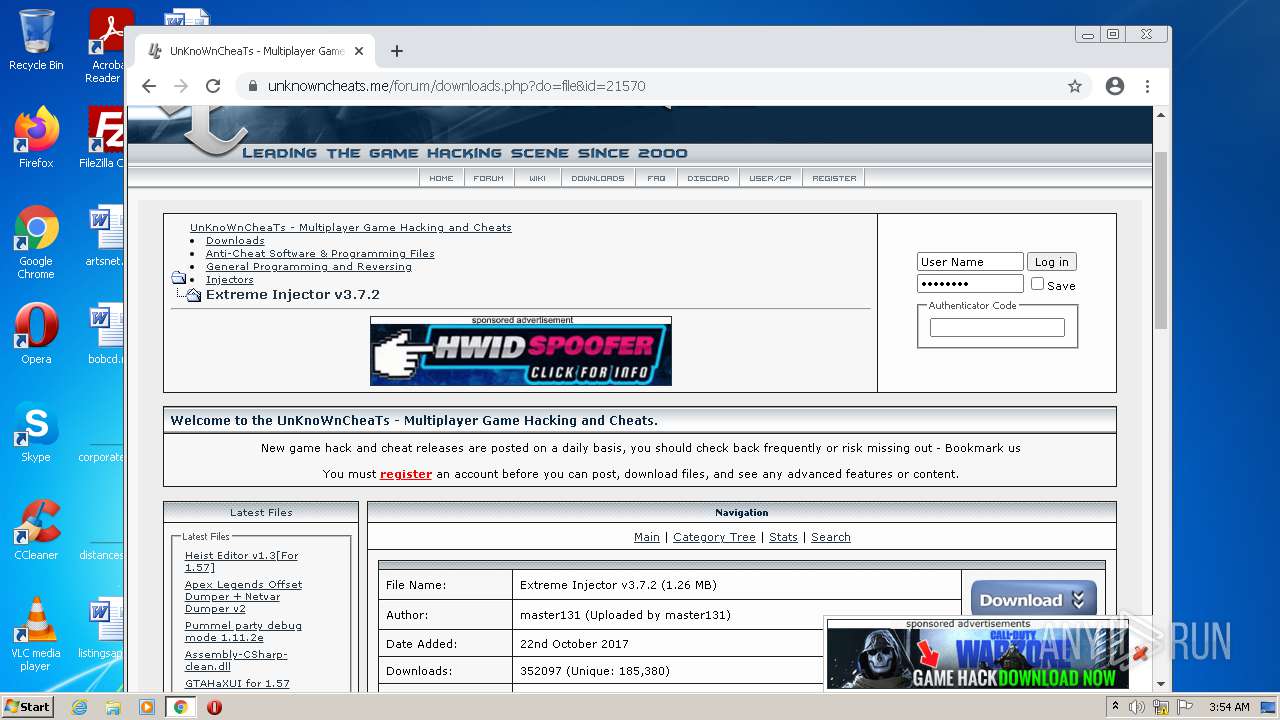
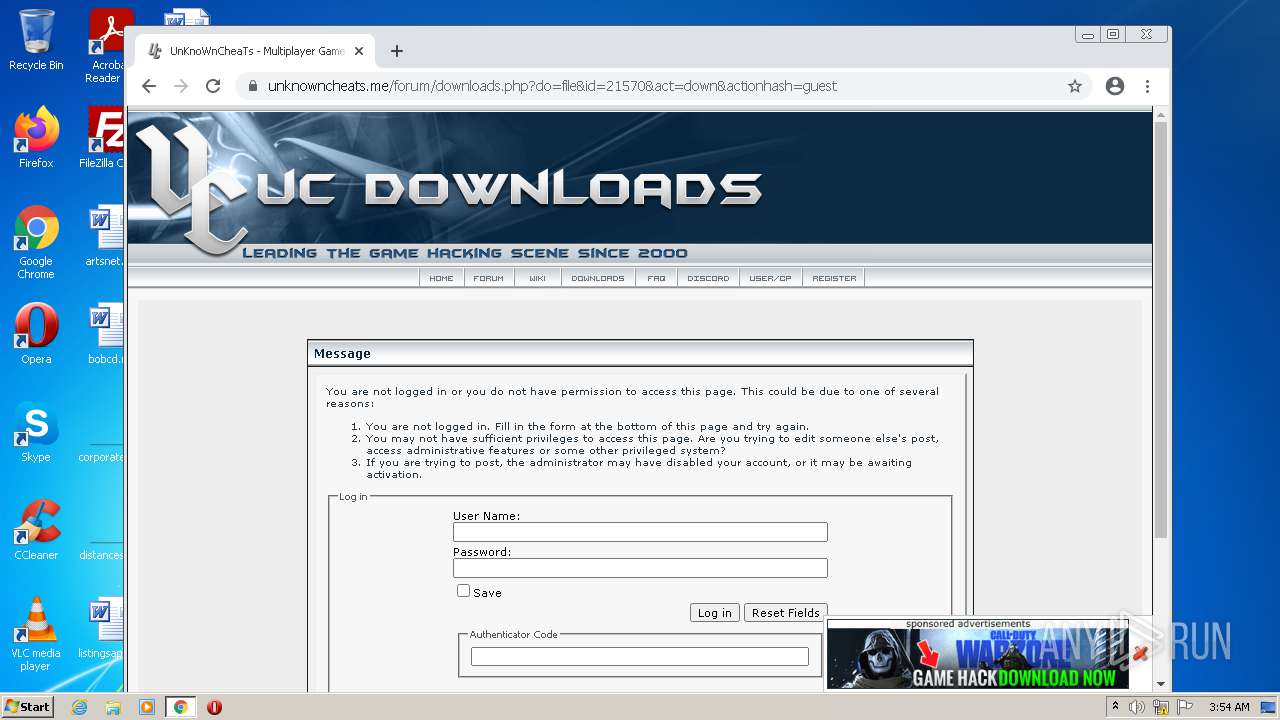
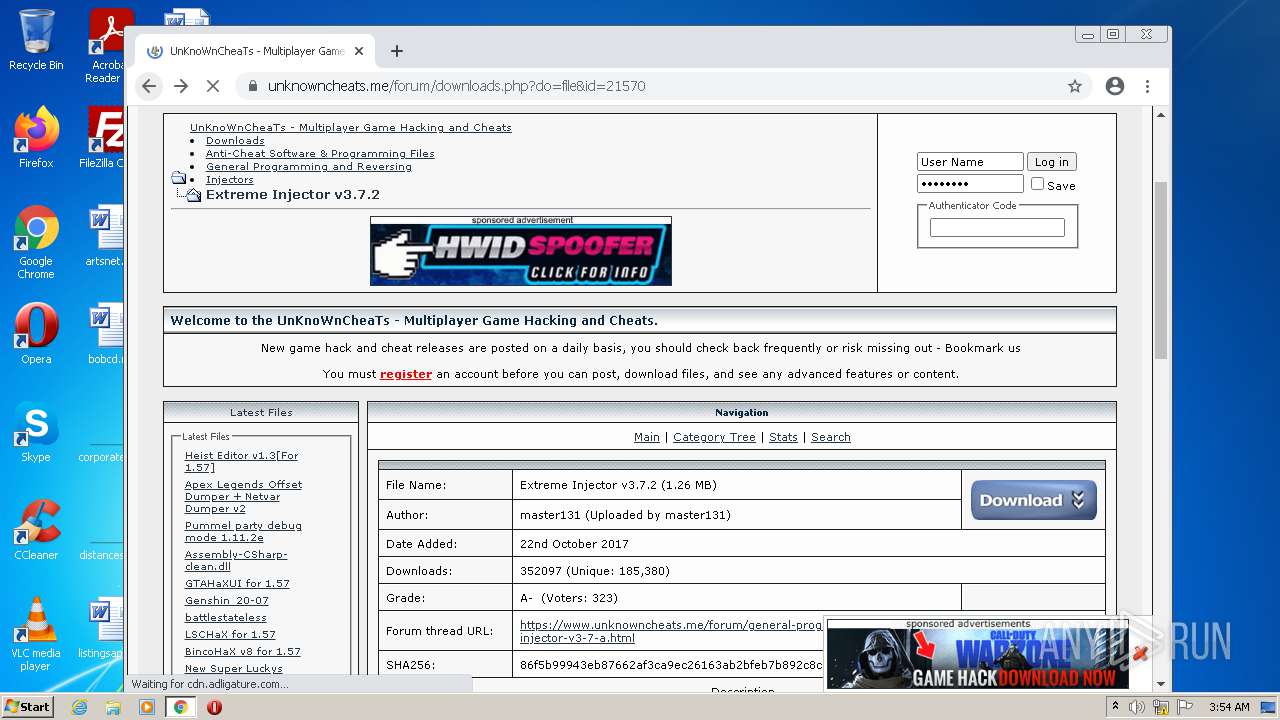
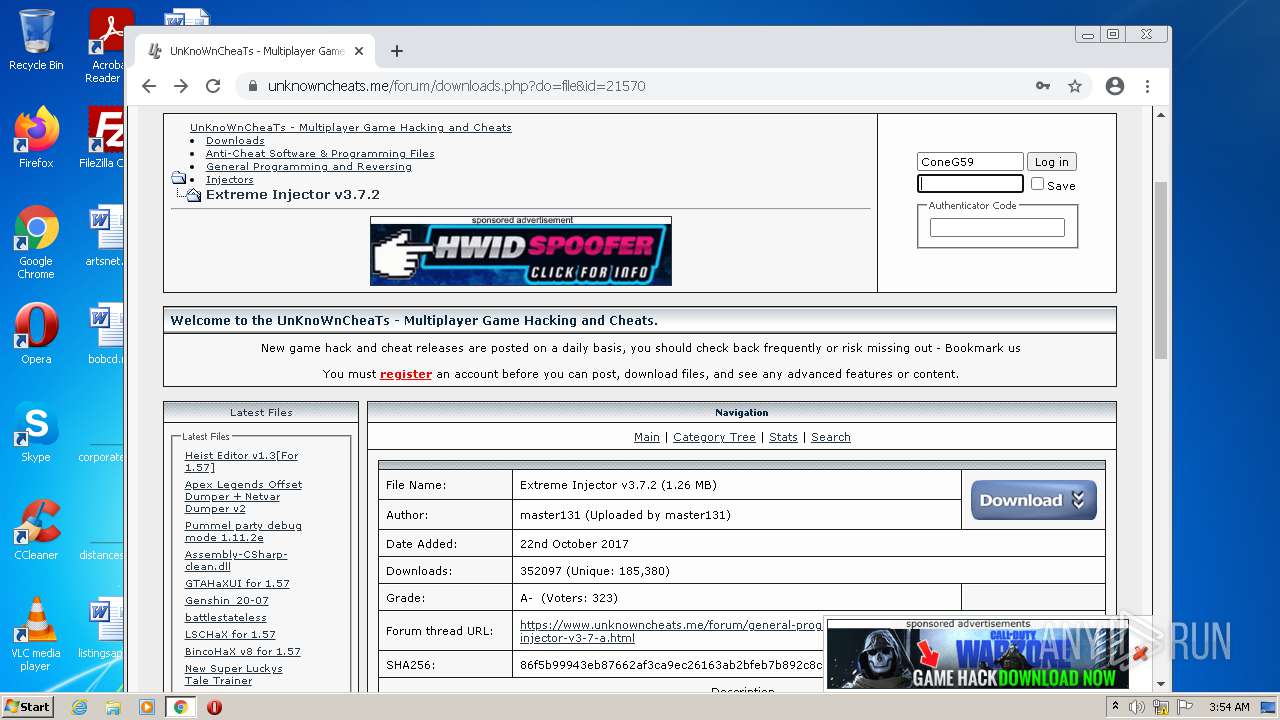
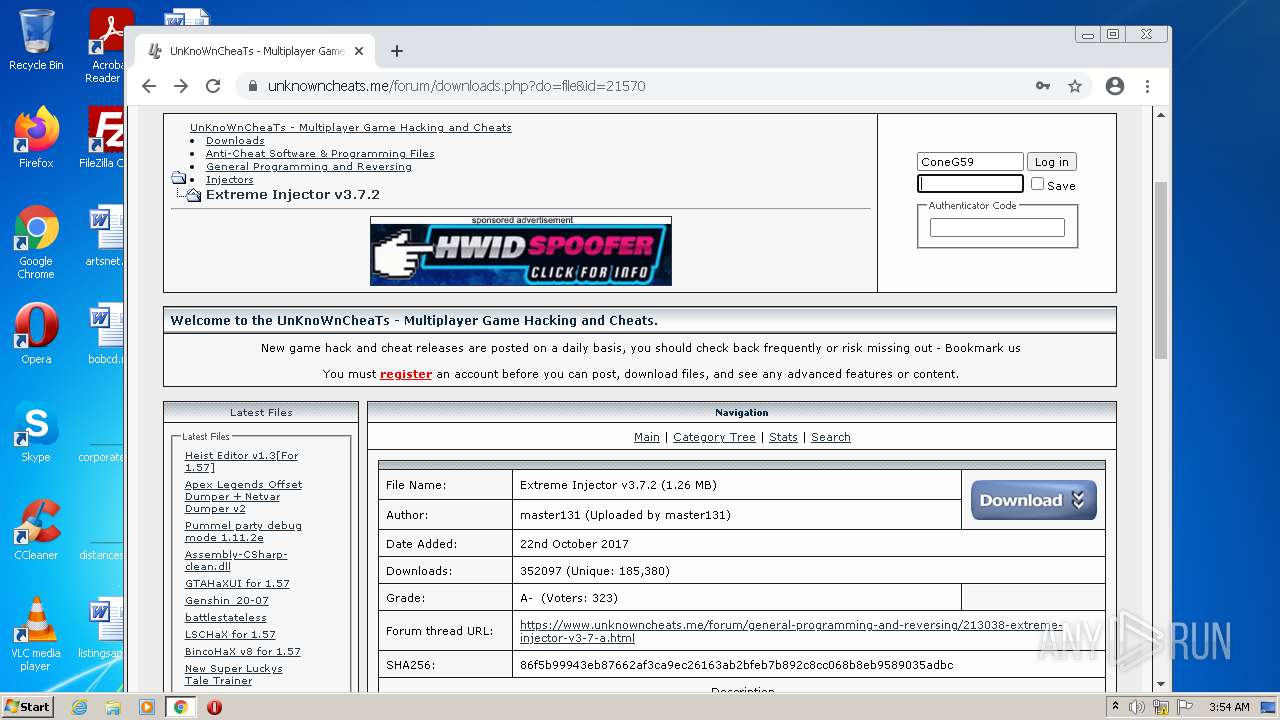
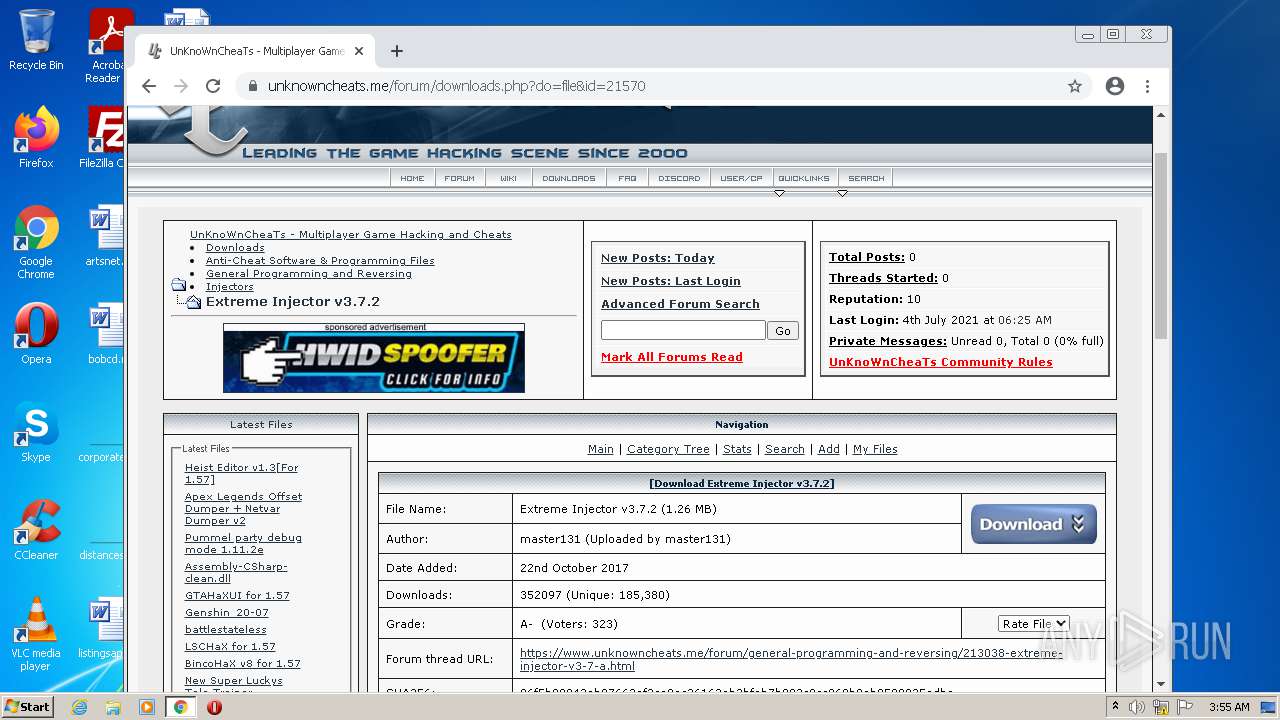
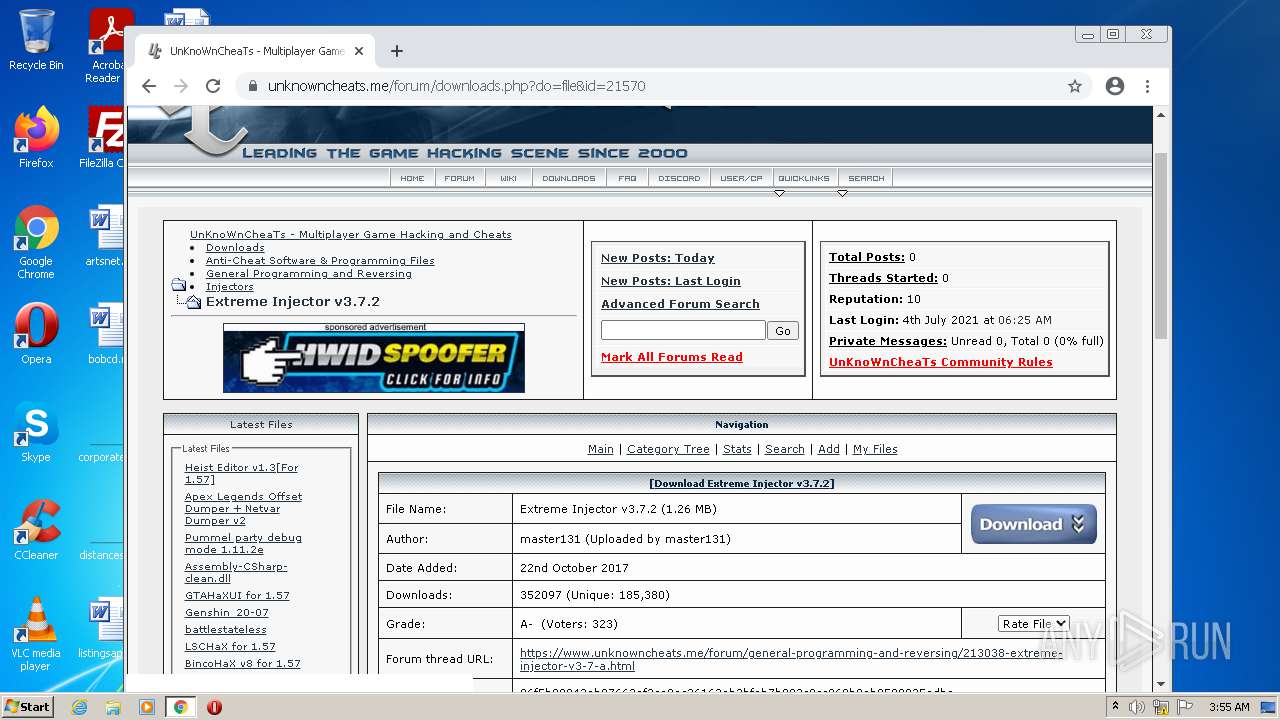
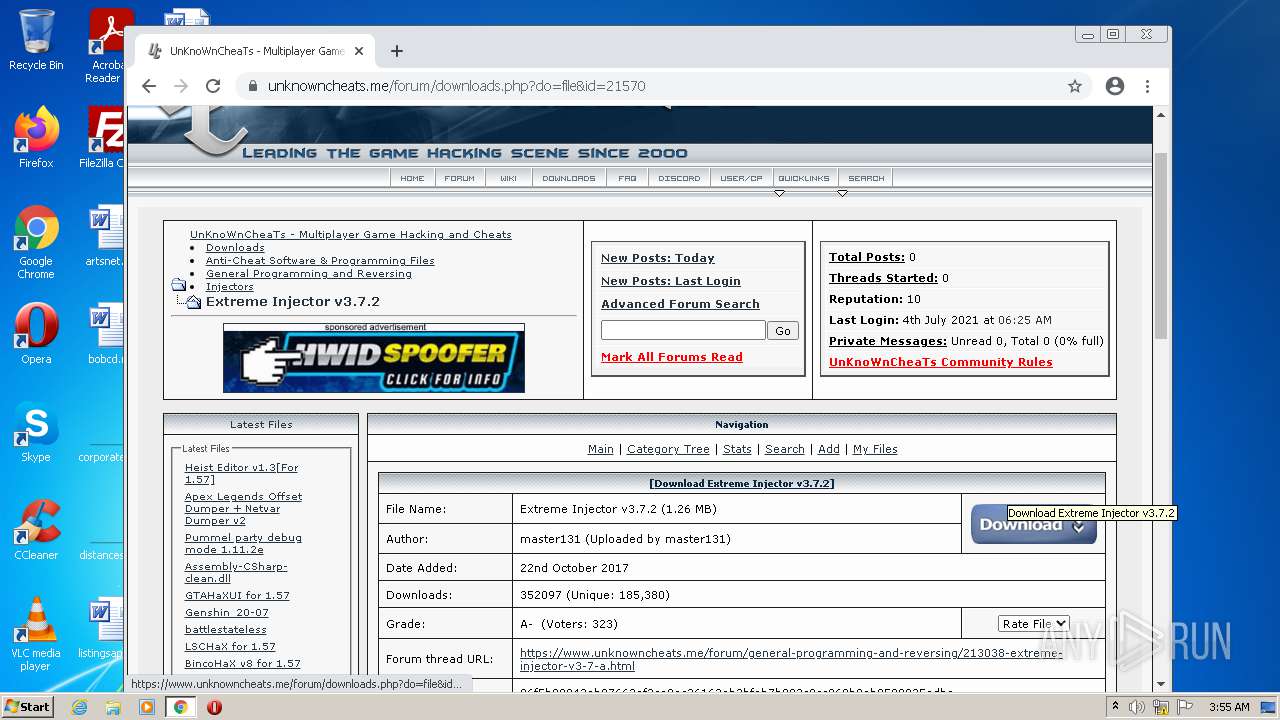
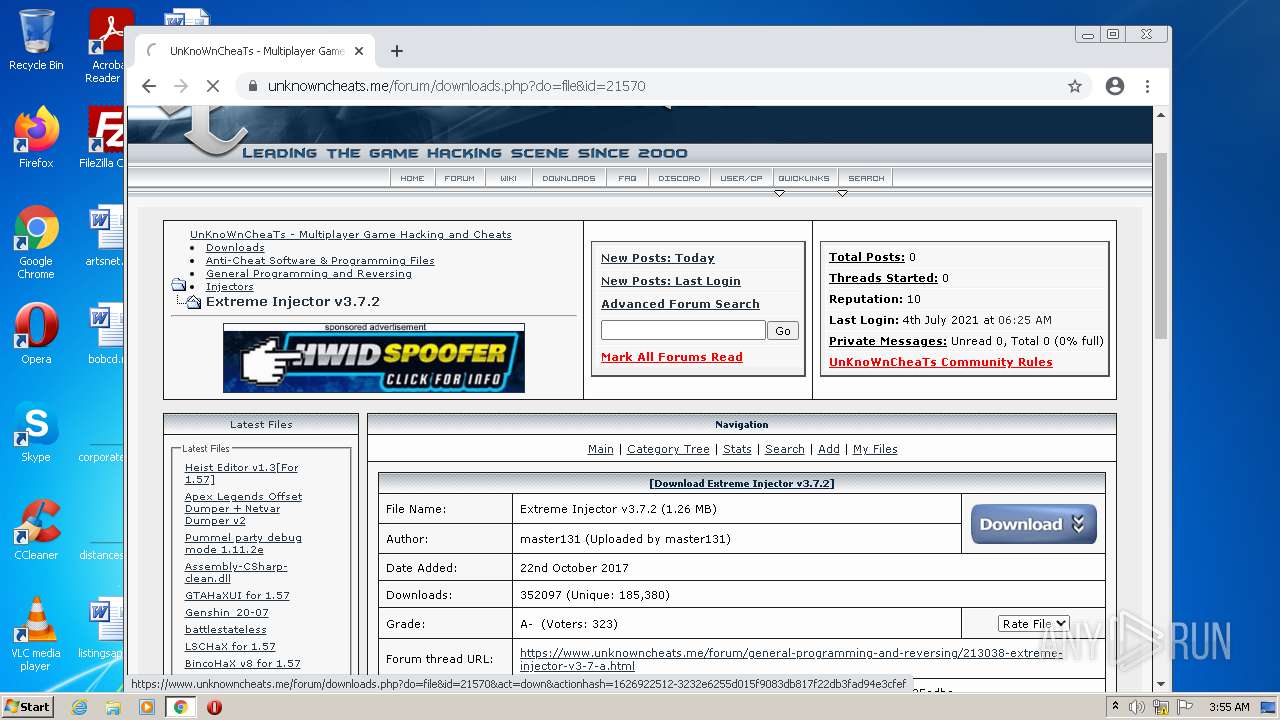
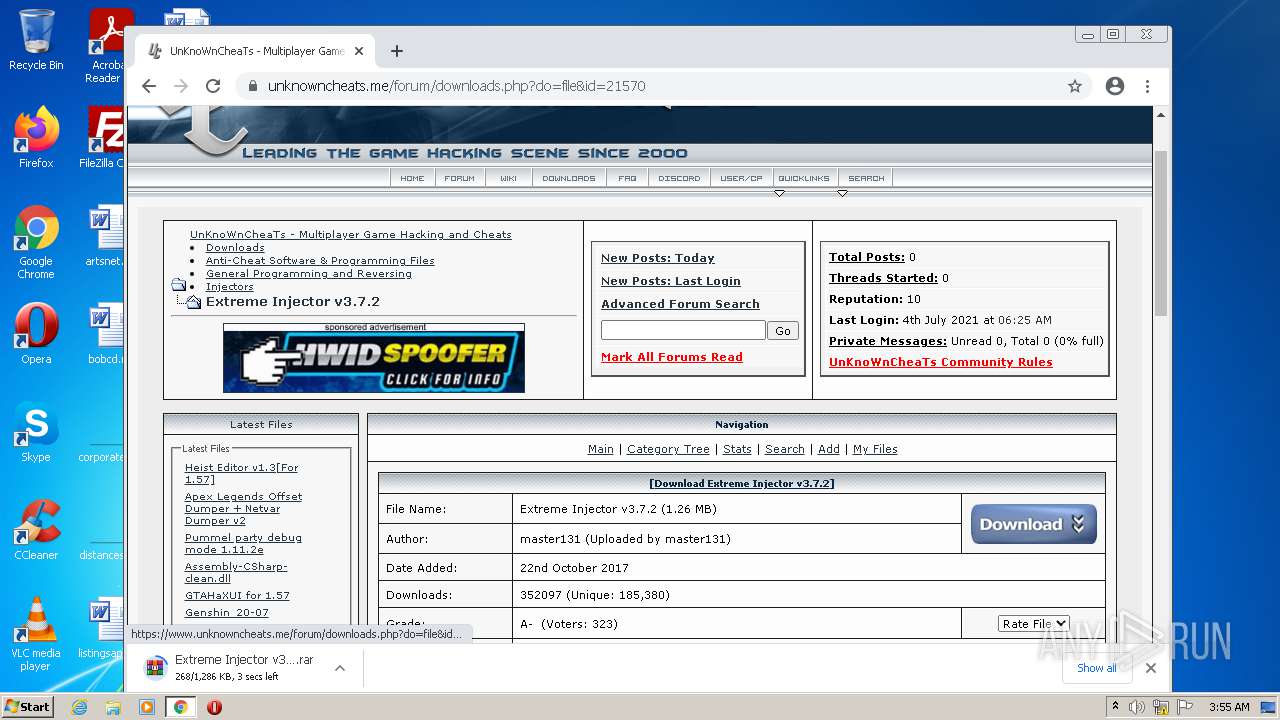
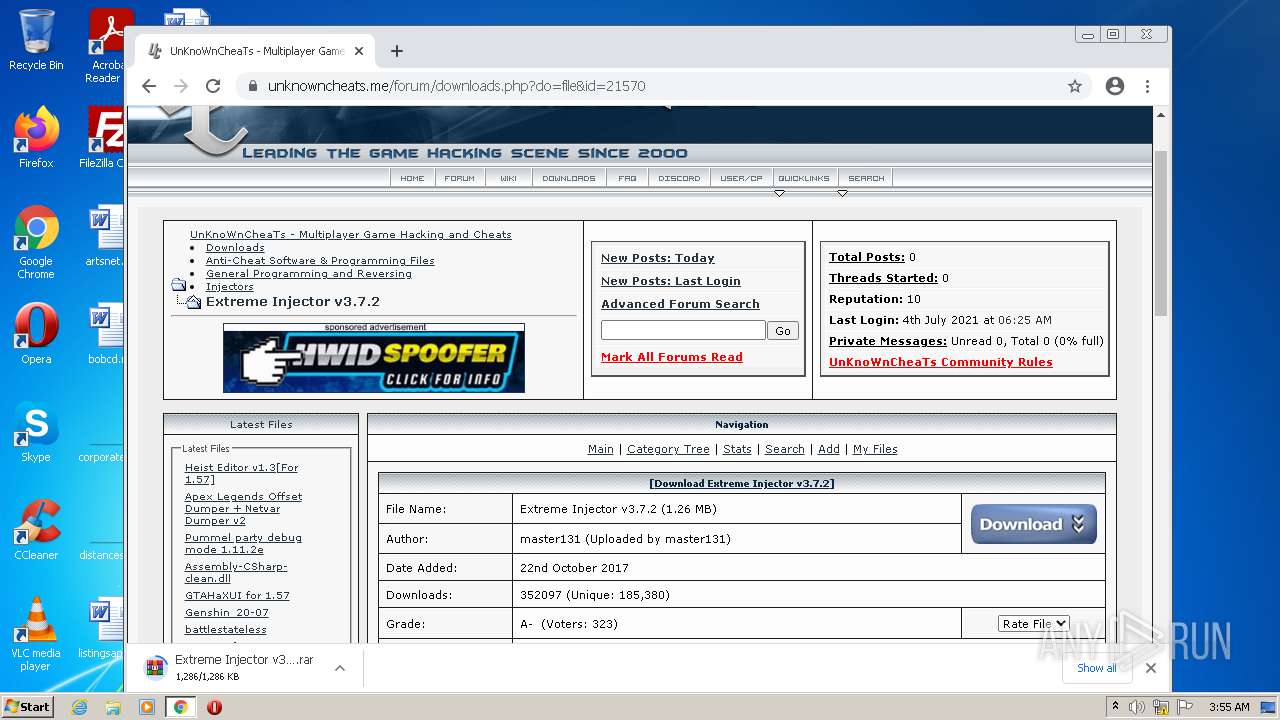
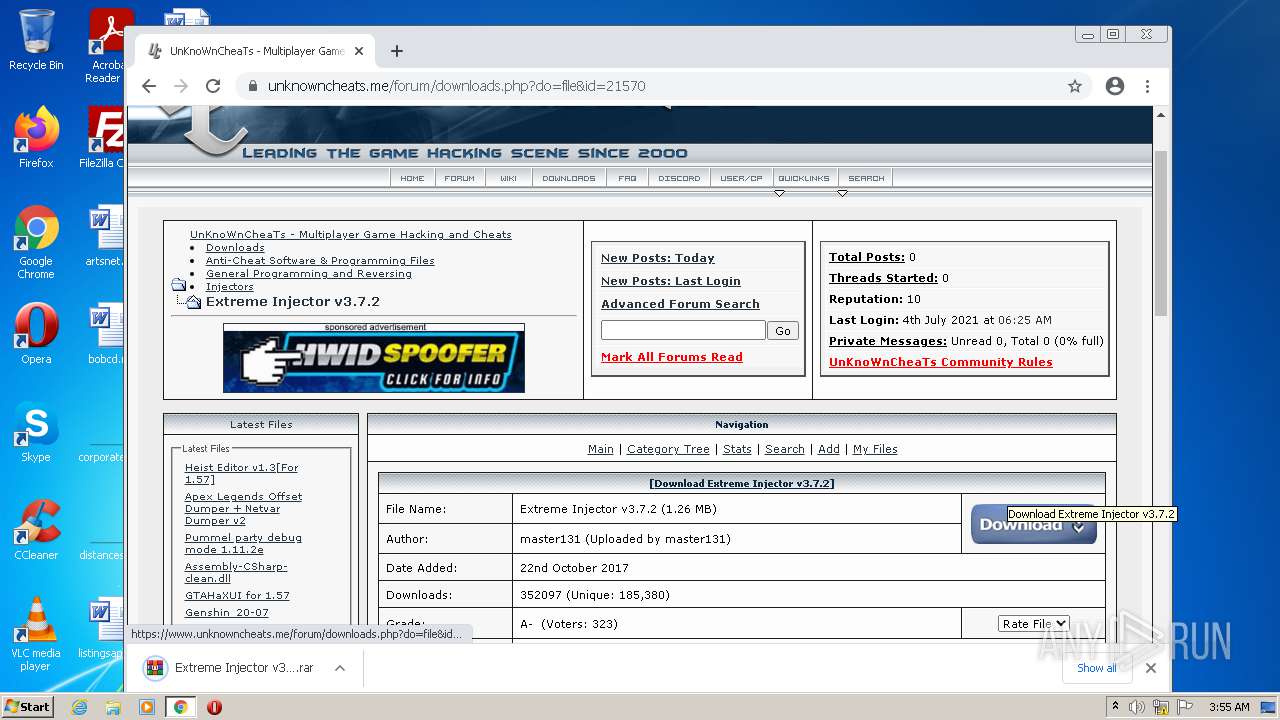
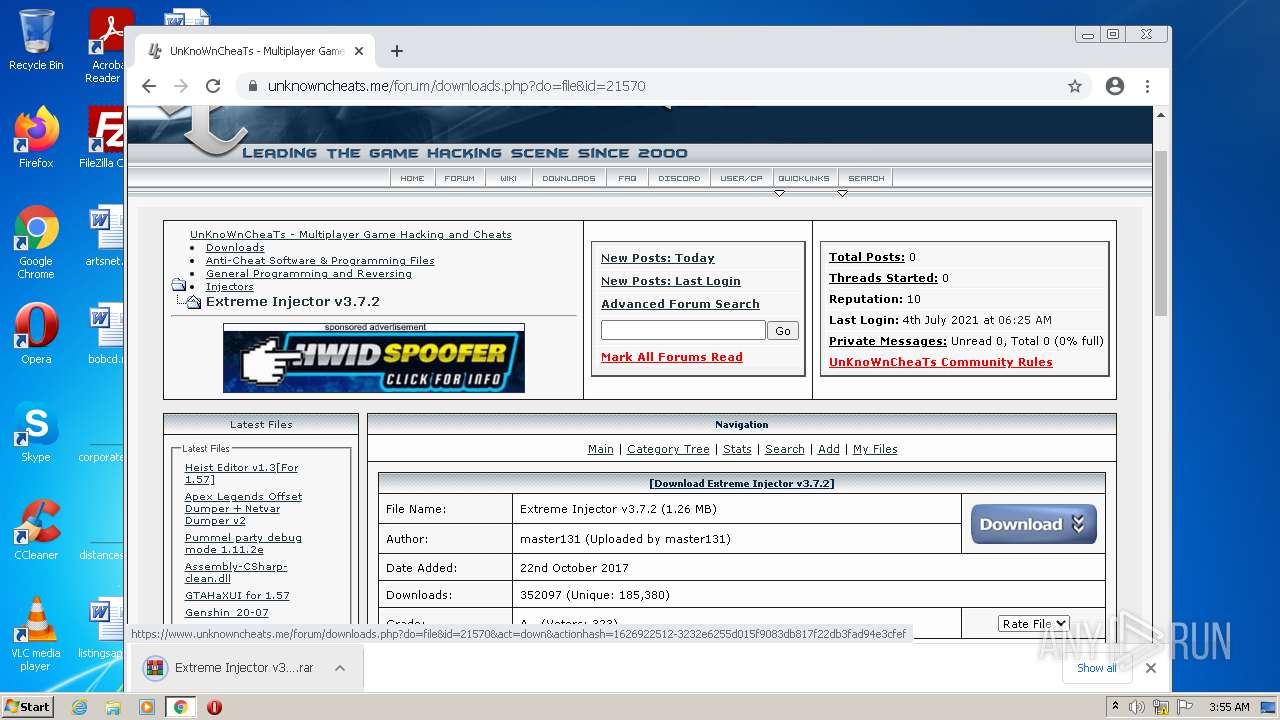
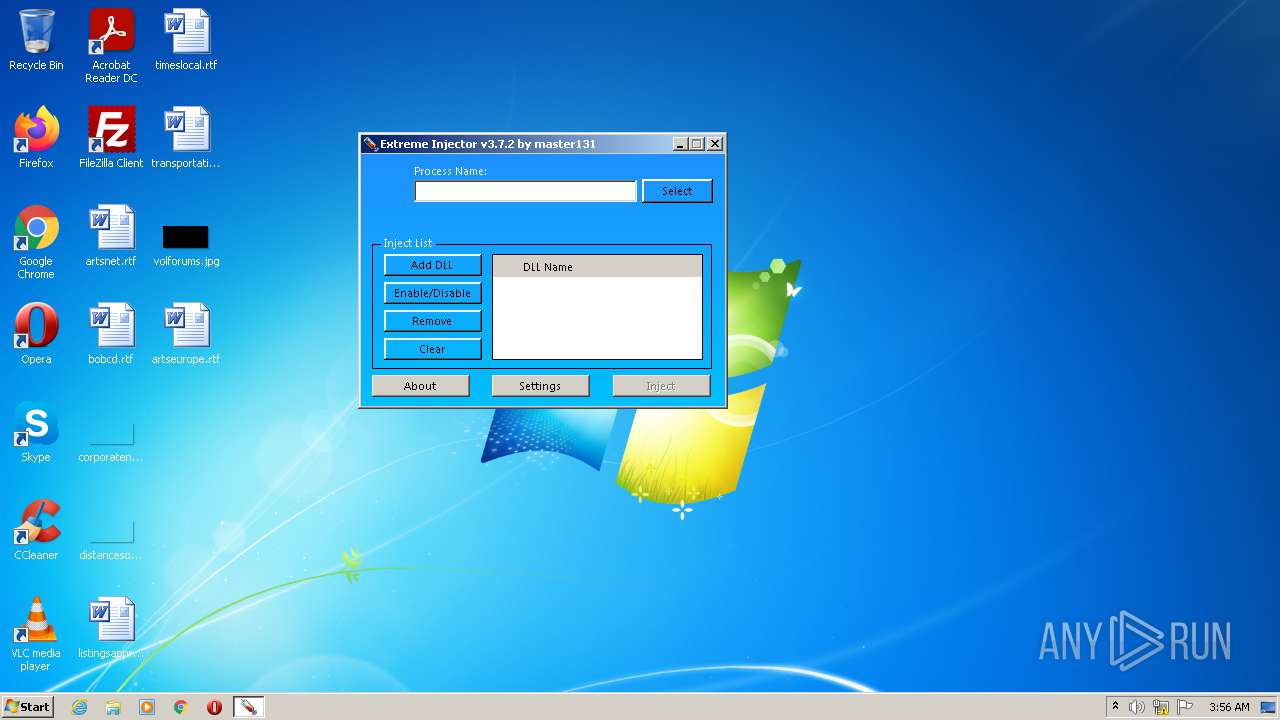
- Extreme Injector v3.exe (PID: 3220)
- Extreme Injector v3.exe (PID: 3788)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3736)
- WinRAR.exe (PID: 900)
- Extreme Injector v3.exe (PID: 3220)
- Extreme Injector v3.exe (PID: 3788)
Checks supported languages
- WinRAR.exe (PID: 3736)
- WinRAR.exe (PID: 900)
- Extreme Injector v3.exe (PID: 3220)
- Extreme Injector v3.exe (PID: 3788)
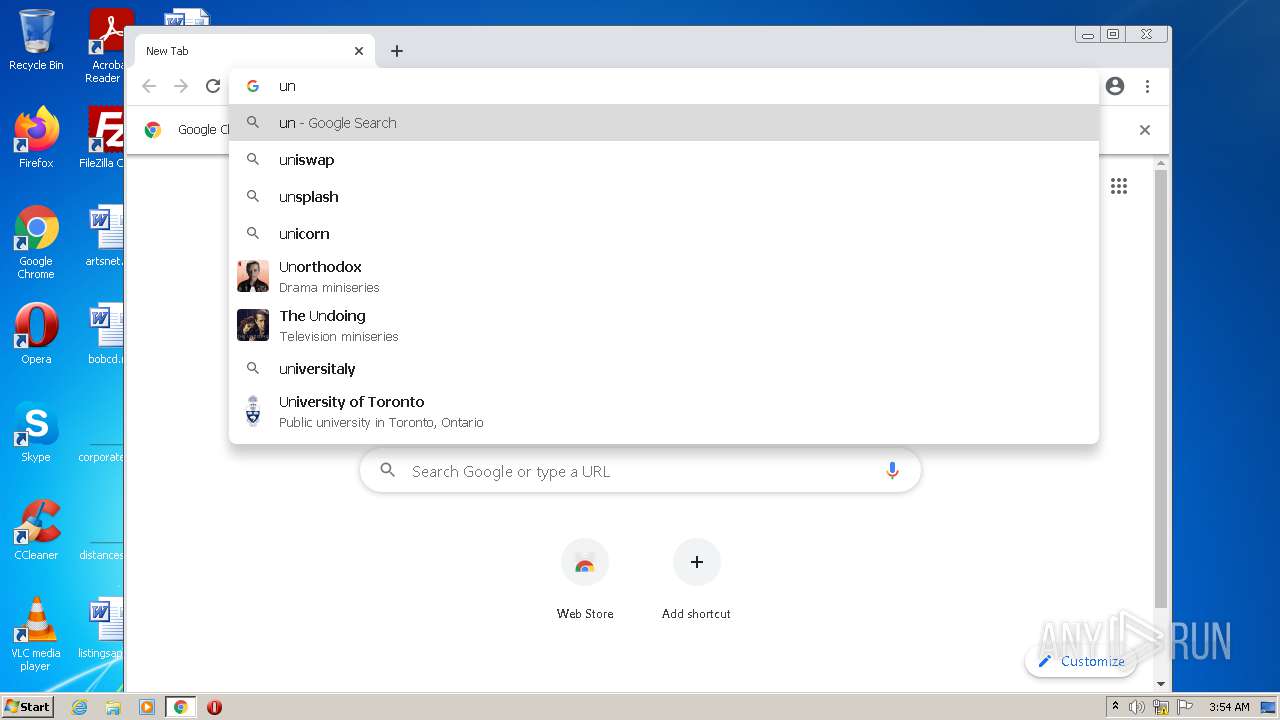
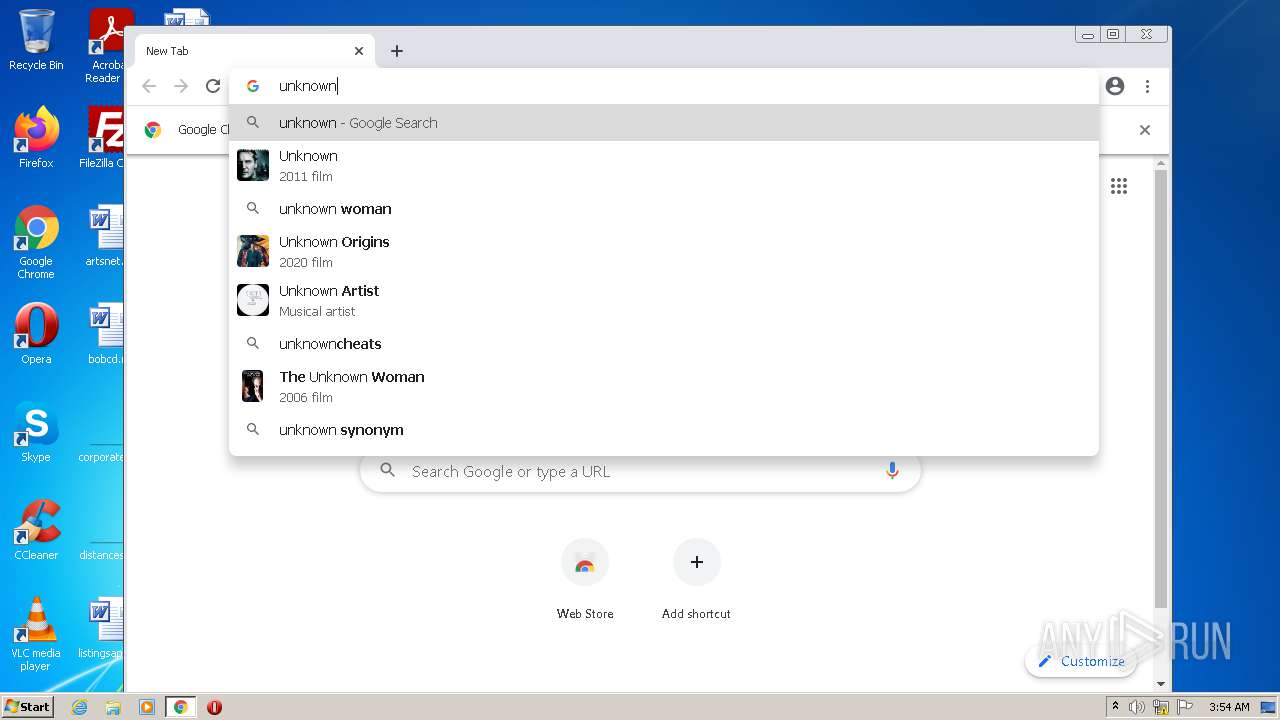
Modifies files in Chrome extension folder
- chrome.exe (PID: 2116)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3200)
Executable content was dropped or overwritten
- chrome.exe (PID: 3200)
- WinRAR.exe (PID: 900)
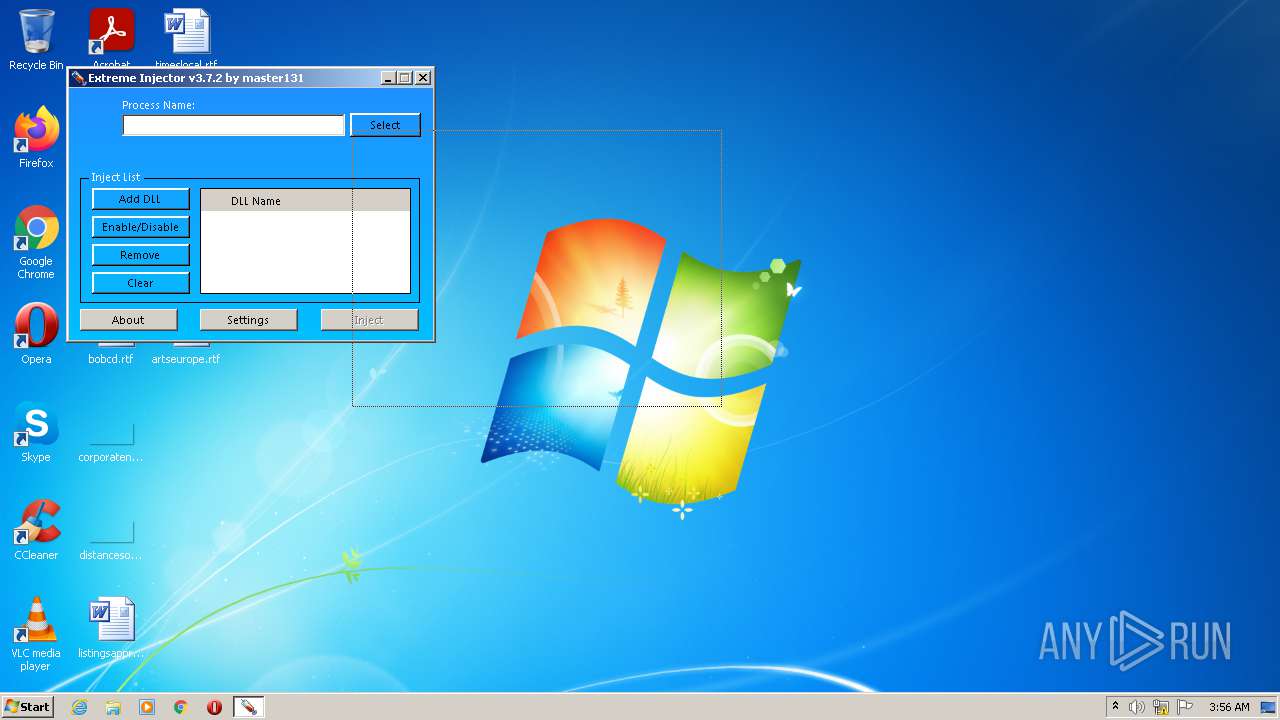
Application launched itself
- Extreme Injector v3.exe (PID: 3220)
Reads Environment values
- Extreme Injector v3.exe (PID: 3788)
INFO
Checks supported languages
- chrome.exe (PID: 2116)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 324)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 976)
- chrome.exe (PID: 2264)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 2272)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 1000)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 788)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 1892)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 1544)
- chrome.exe (PID: 900)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2812)
Reads the hosts file
- chrome.exe (PID: 2116)
- chrome.exe (PID: 3148)
Application launched itself
- chrome.exe (PID: 2116)
Reads the computer name
- chrome.exe (PID: 2116)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 900)
- chrome.exe (PID: 3400)
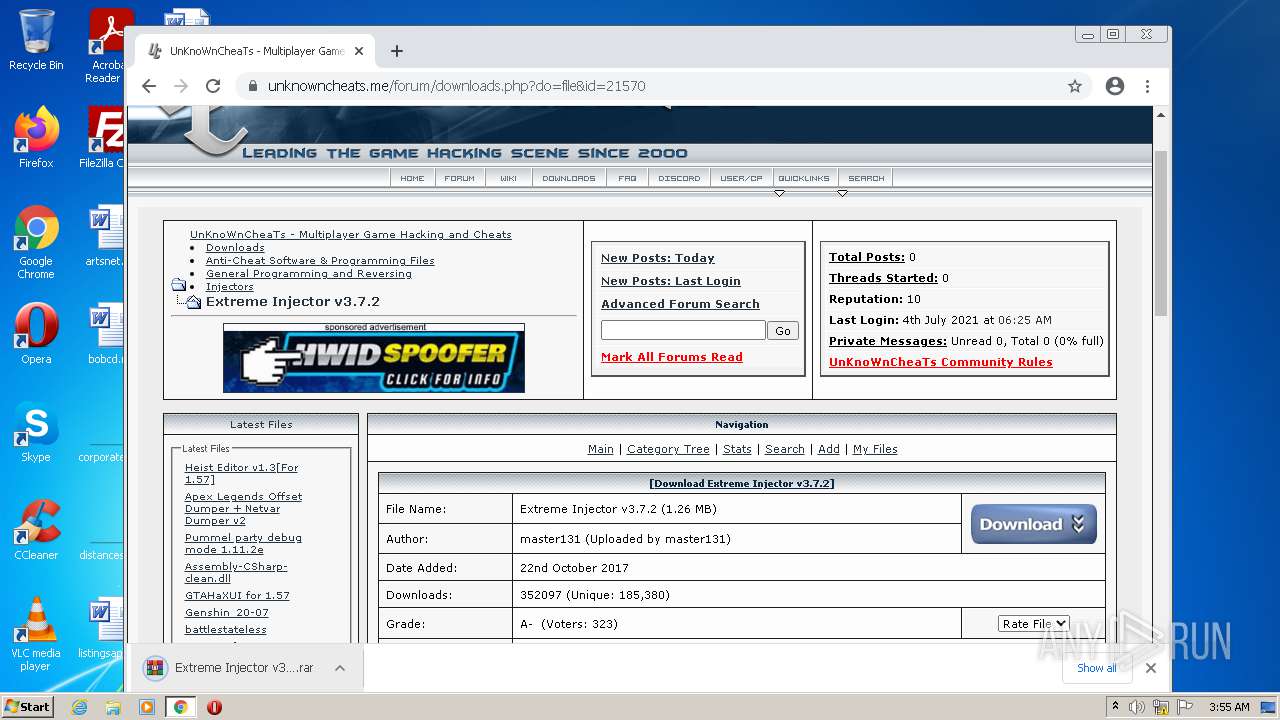
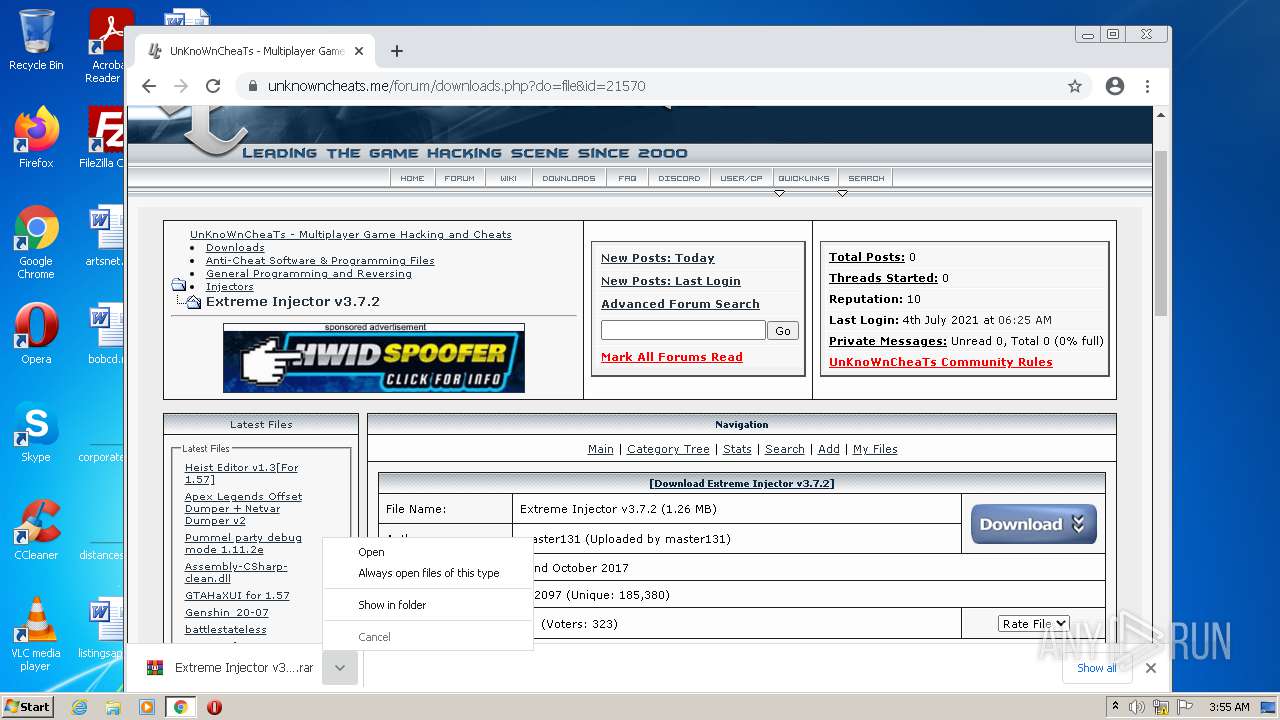
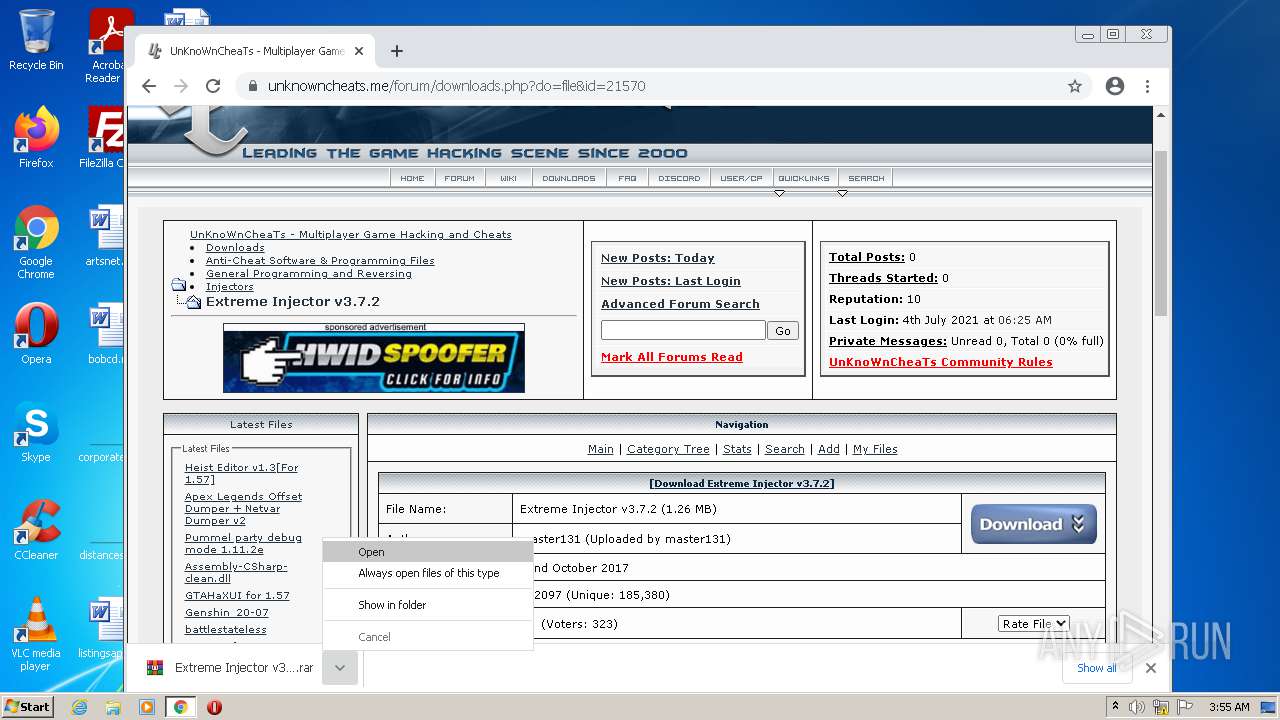
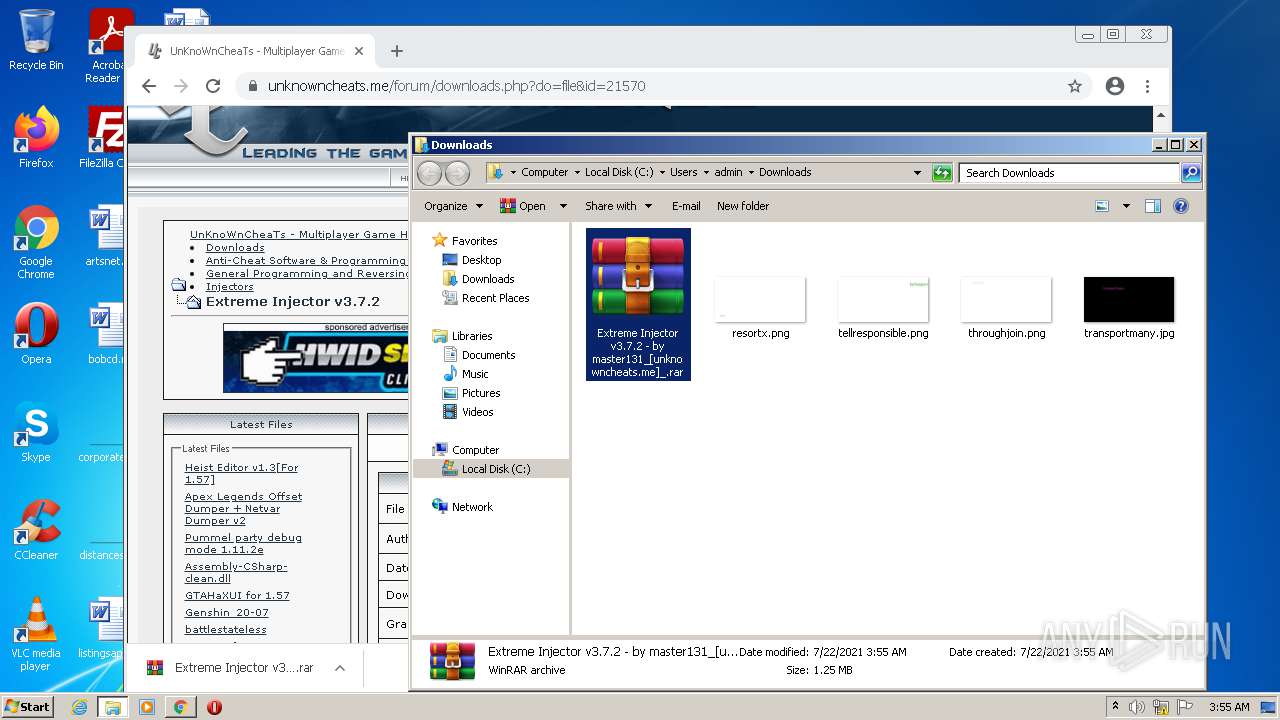
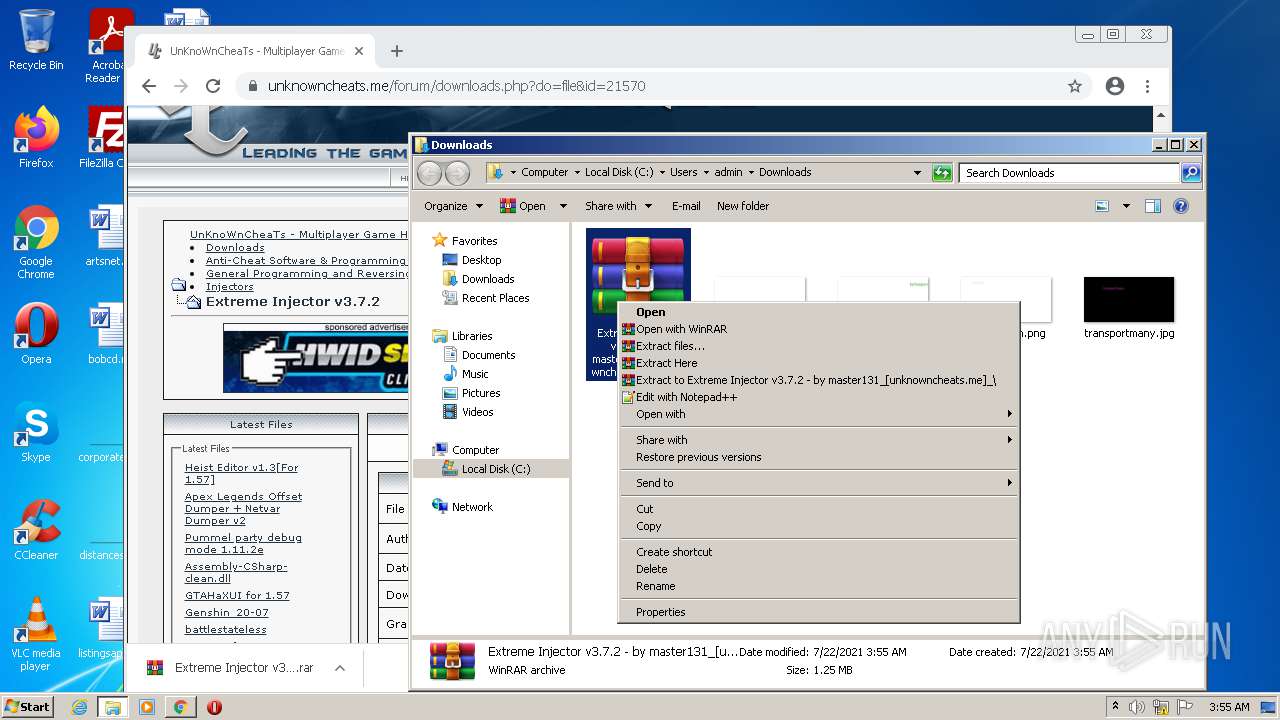
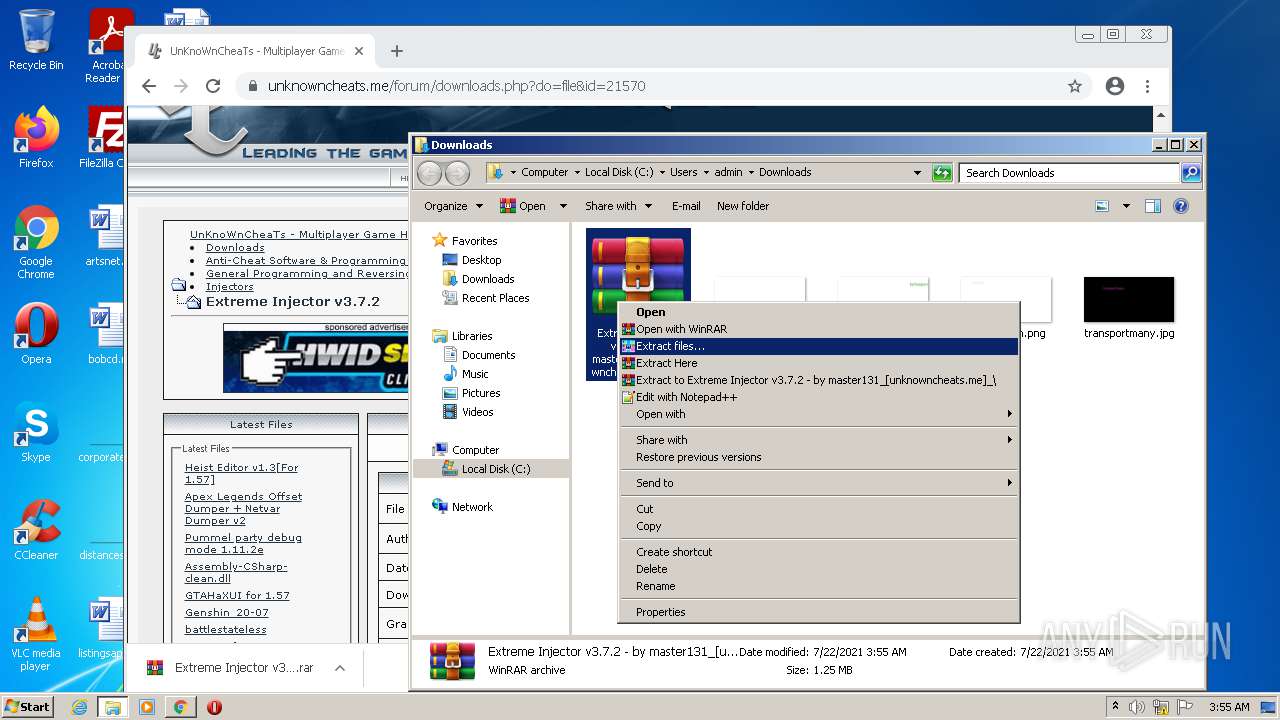
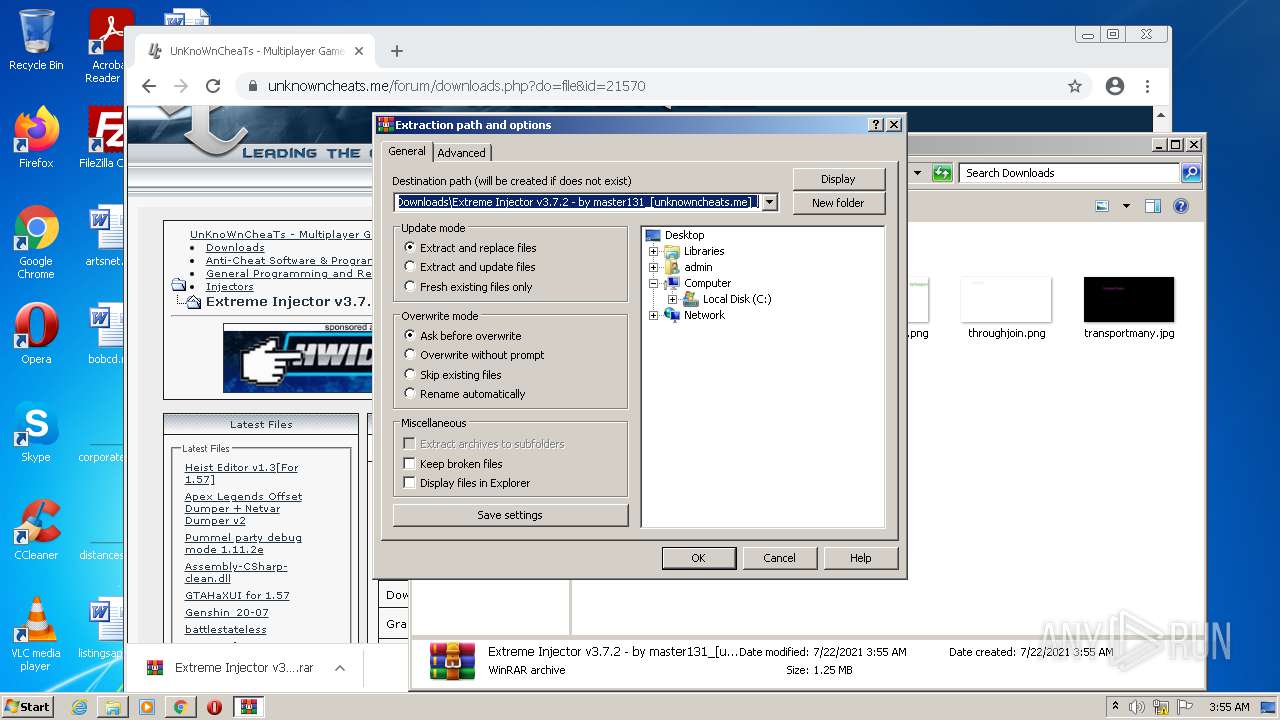
Manual execution by user
- chrome.exe (PID: 2116)
- WinRAR.exe (PID: 900)
- Extreme Injector v3.exe (PID: 3220)
Reads settings of System Certificates
- chrome.exe (PID: 3148)
Reads the date of Windows installation
- chrome.exe (PID: 3592)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Proforma Invoice and Bank swift-REG.PI-0086547654.exe |
|---|---|
| ZipUncompressedSize: | 3514368 |
| ZipCompressedSize: | 3481287 |
| ZipCRC: | 0x4022fcaa |
| ZipModifyDate: | 2021:01:28 09:25:18 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0009 |
| ZipRequiredVersion: | 20 |
Total processes
101
Monitored processes
58
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3876 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
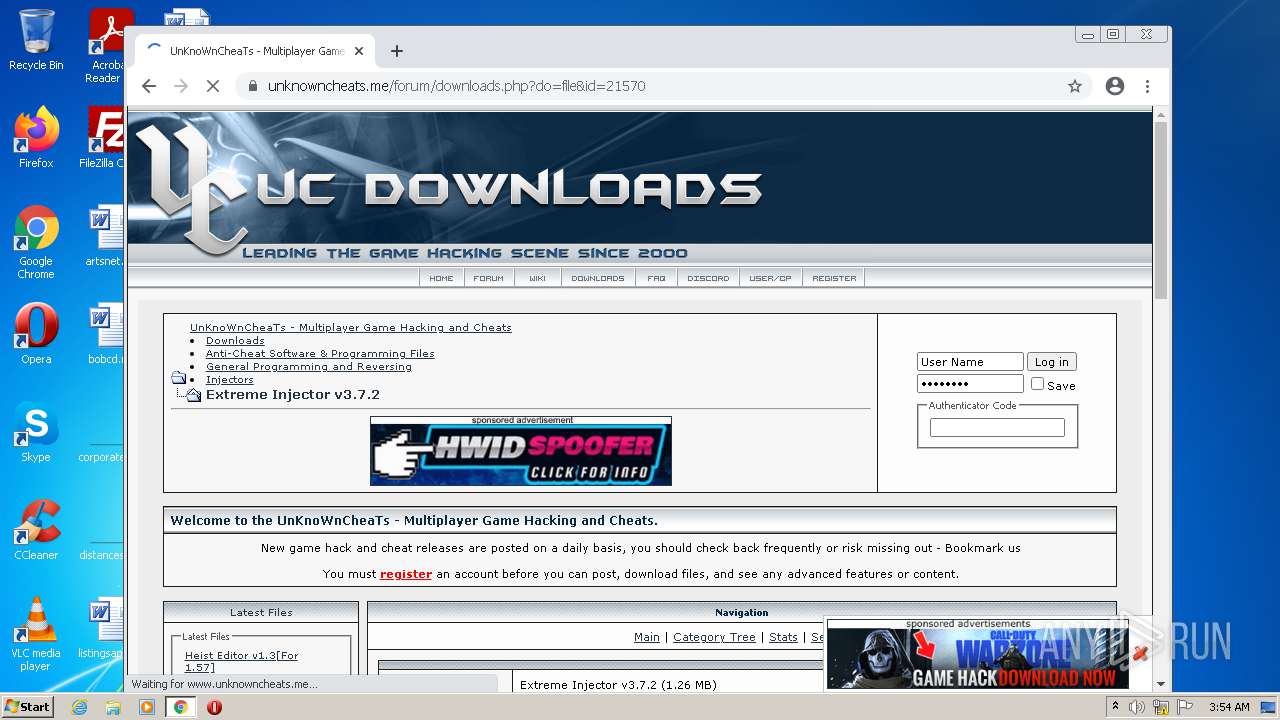
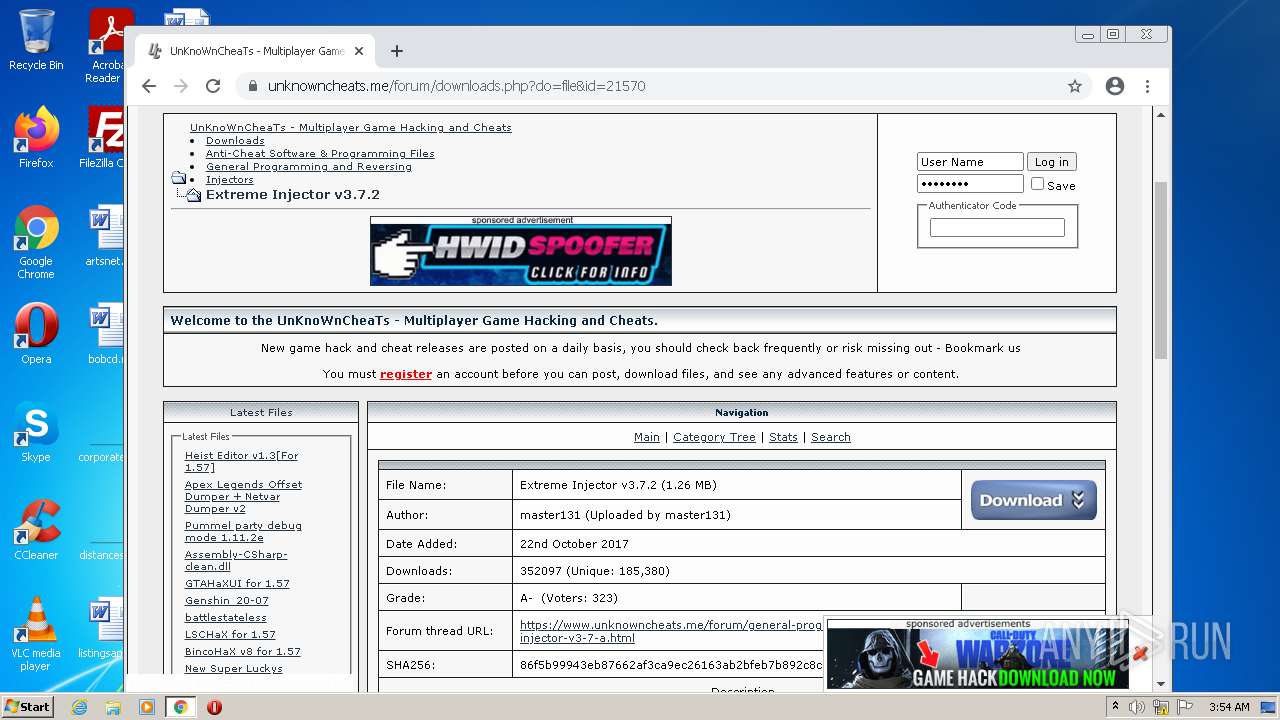
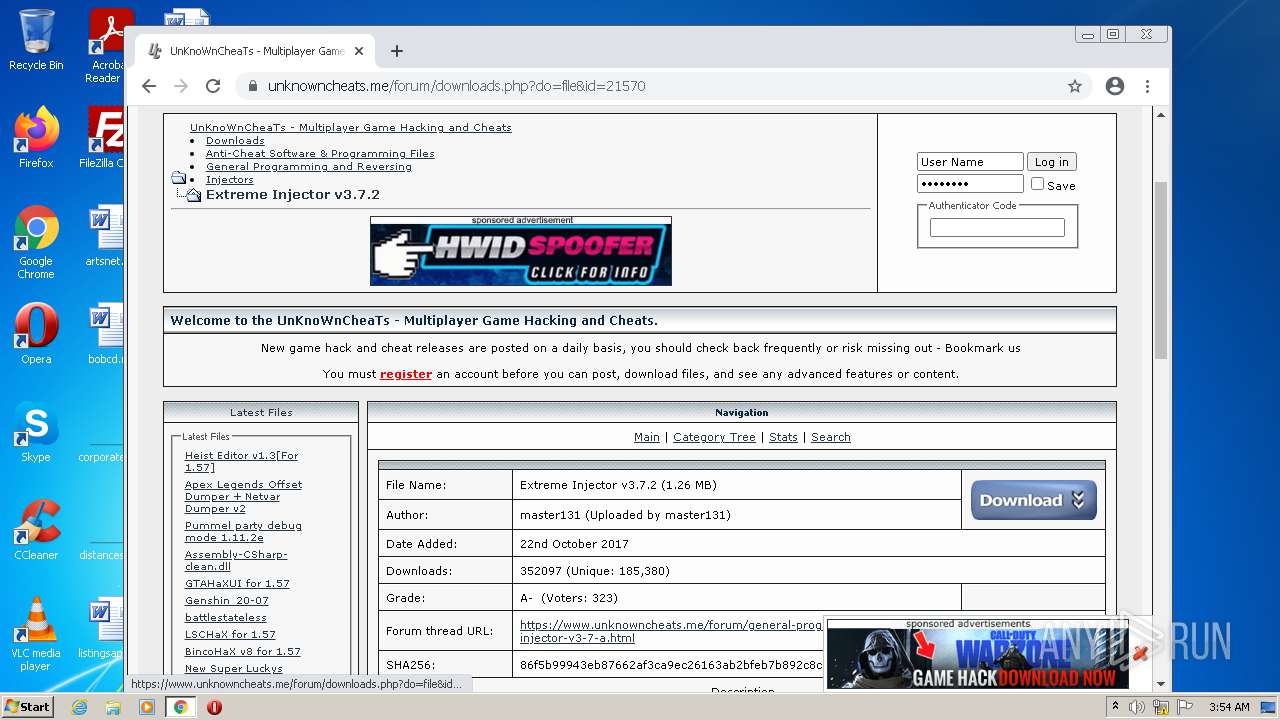
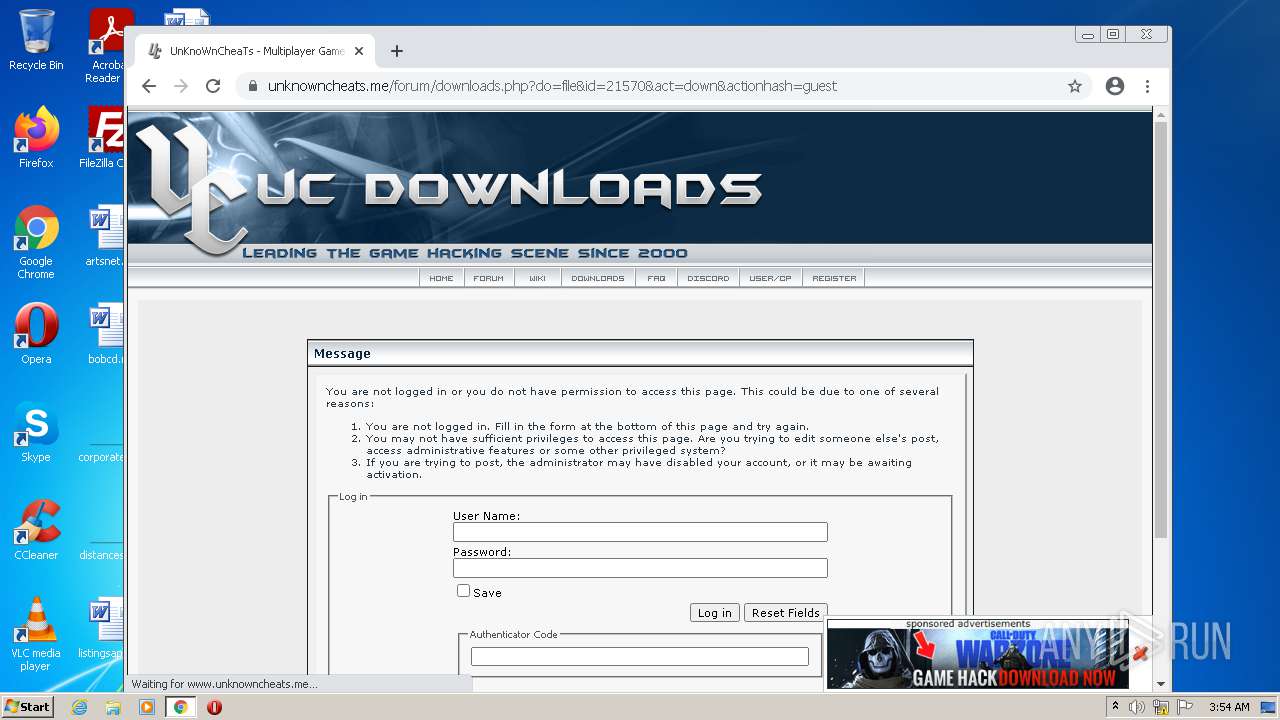
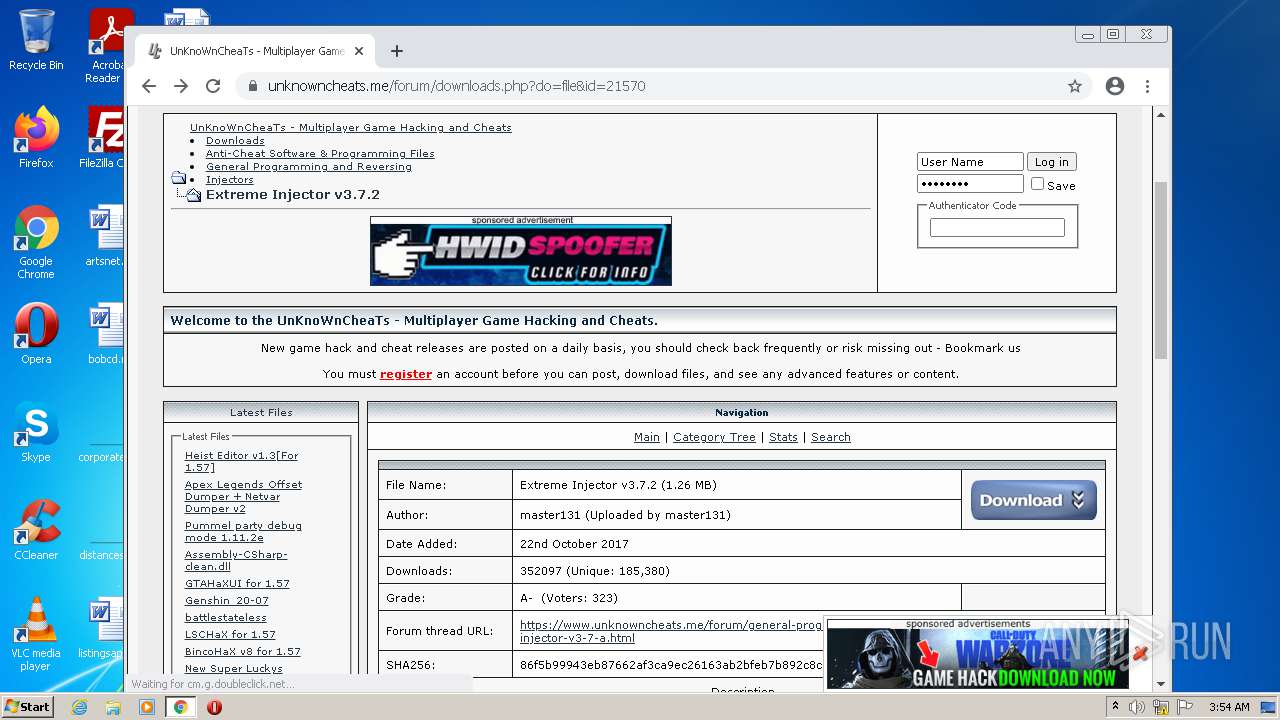
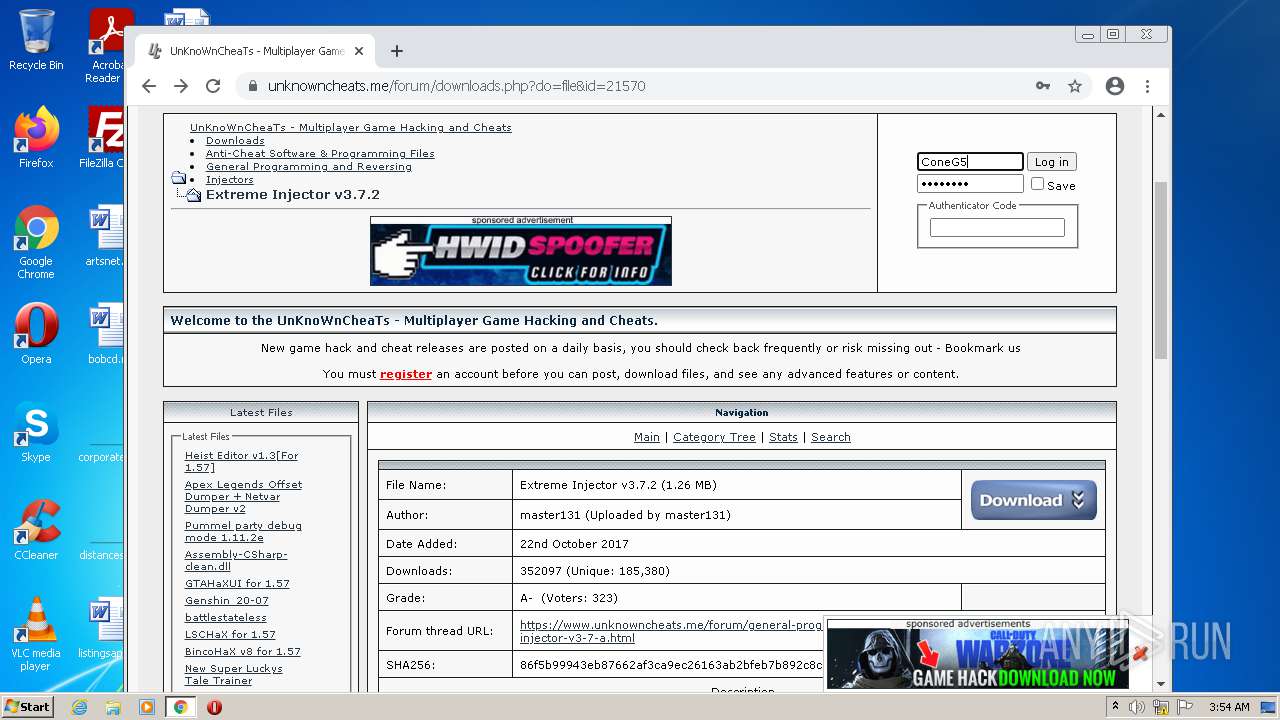
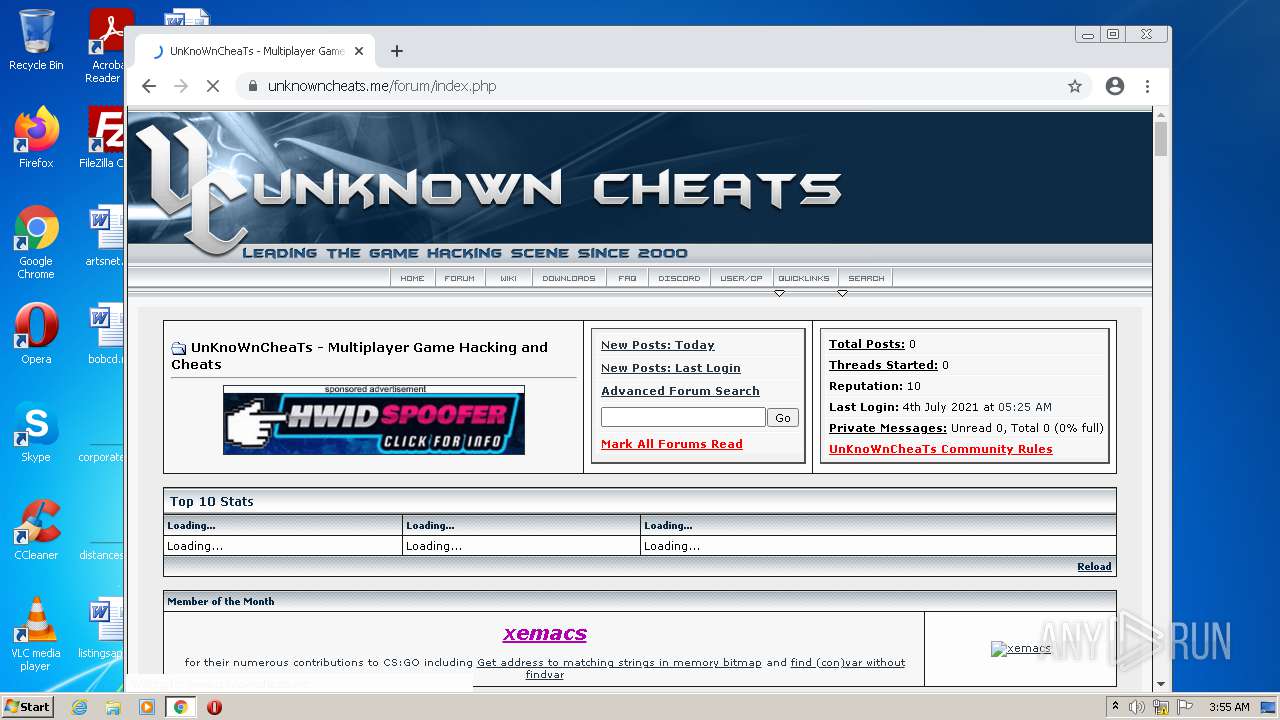
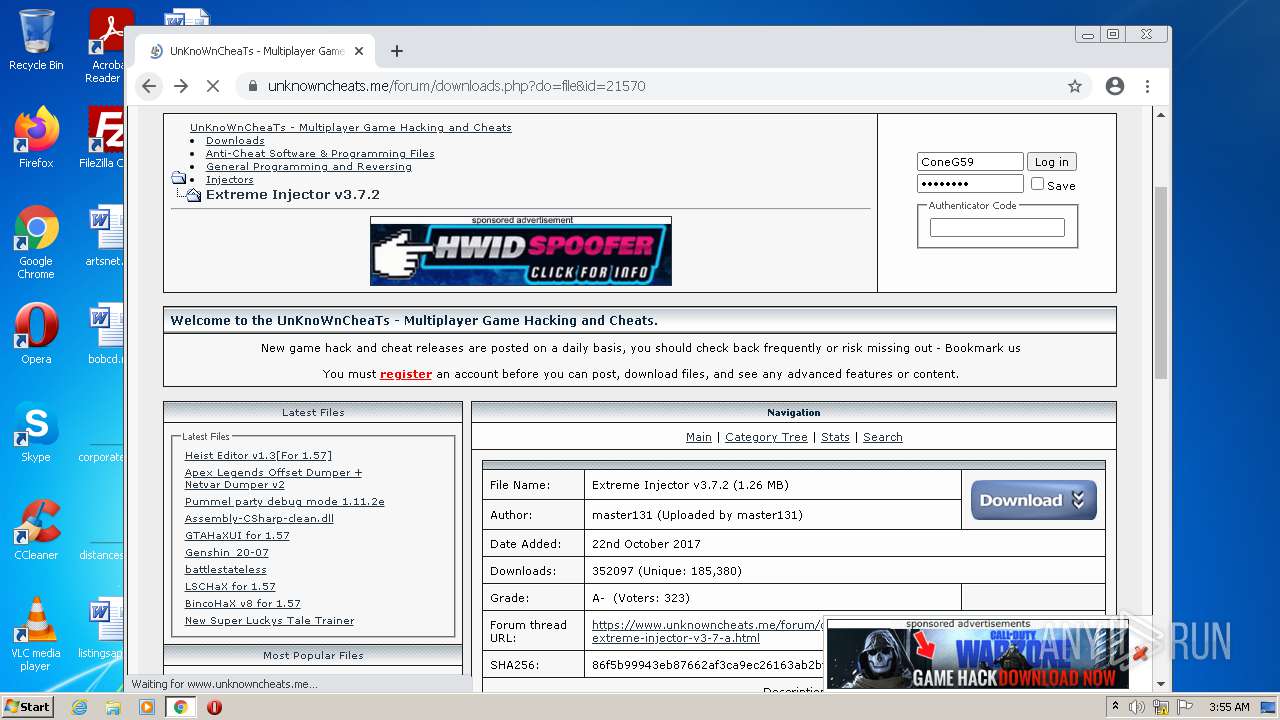
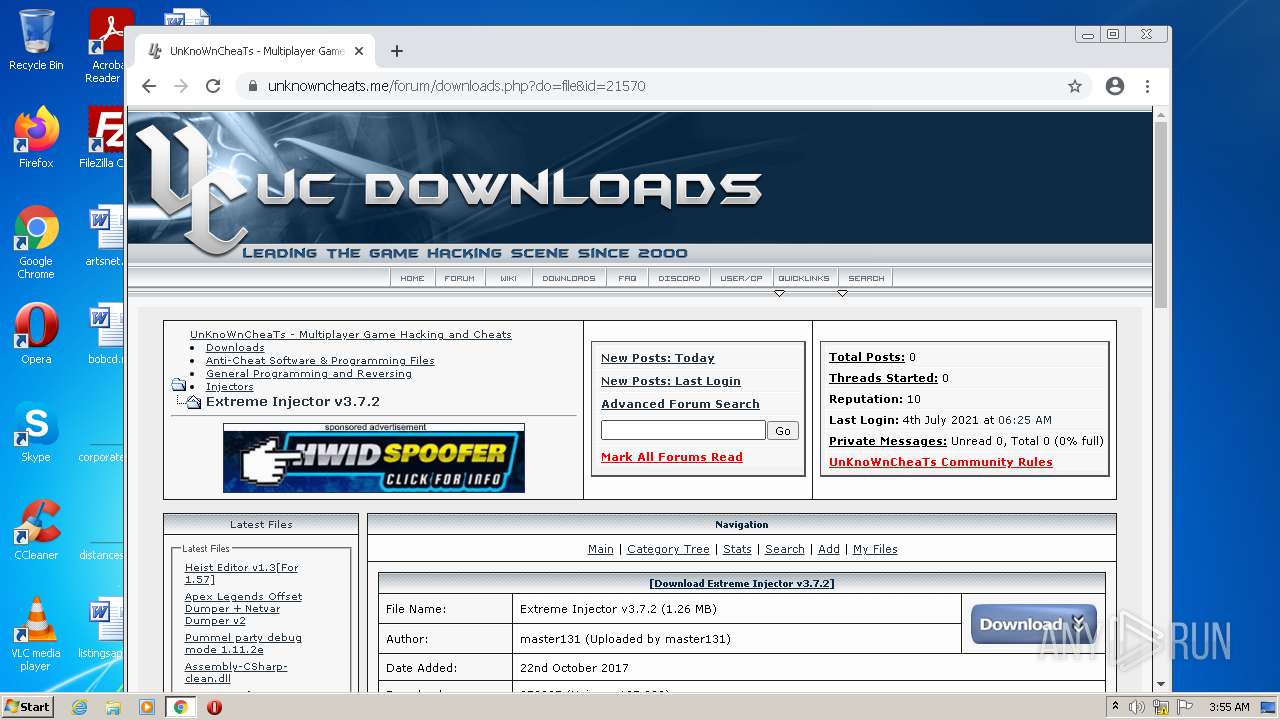
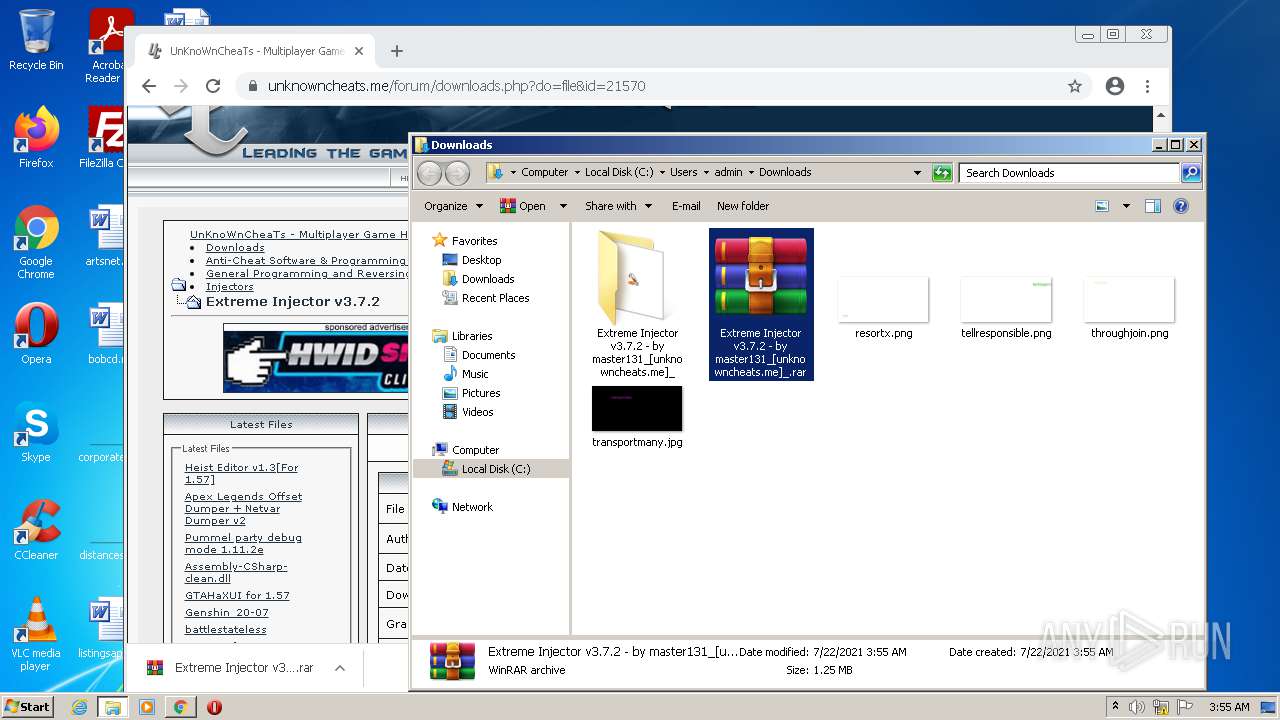
| 900 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Extreme Injector v3.7.2 - by master131_[unknowncheats.me]_.rar" "?\" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2436 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3364 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11871528438852721865,15593118255012453992,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 804
Read events
23 558
Write events
238
Delete events
8
Modification events
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Request for Quotation (RFQ#196).zip | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3736) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
2
Suspicious files
168
Text files
302
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60F8DDB8-844.pma | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\317d0a71-1820-44c8-acbe-7313c00567bb.tmp | text | |
MD5:— | SHA256:— | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF37ec68.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ff8e16e6-b00b-4c2d-b0d3-6ac8cd6b69f6.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
122
DNS requests
90
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
904 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
904 | svchost.exe | HEAD | 200 | 74.125.8.72:80 | http://r3---sn-5hneknee.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=85.203.44.65&mm=28&mn=sn-5hneknee&ms=nvh&mt=1626922032&mv=u&mvi=3&pl=25&rmhost=r1---sn-5hneknee.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
904 | svchost.exe | HEAD | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
3148 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ce6841953cd5f7af | US | compressed | 59.5 Kb | whitelisted |
3148 | chrome.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 592 b | whitelisted |
904 | svchost.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 503 b | whitelisted |
904 | svchost.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 503 b | whitelisted |
904 | svchost.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 503 b | whitelisted |
904 | svchost.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 503 b | whitelisted |
904 | svchost.exe | GET | 206 | 74.125.8.72:80 | http://r3---sn-5hneknee.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=85.203.44.65&mm=28&mn=sn-5hneknee&ms=nvh&mt=1626922032&mv=u&mvi=3&pl=25&rmhost=r1---sn-5hneknee.gvt1.com&shardbypass=yes | US | binary | 9.66 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | chrome.exe | 142.250.186.164:443 | www.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3148 | chrome.exe | 142.250.186.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.185.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.185.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.181.227:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.181.238:443 | ogs.google.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.186.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |