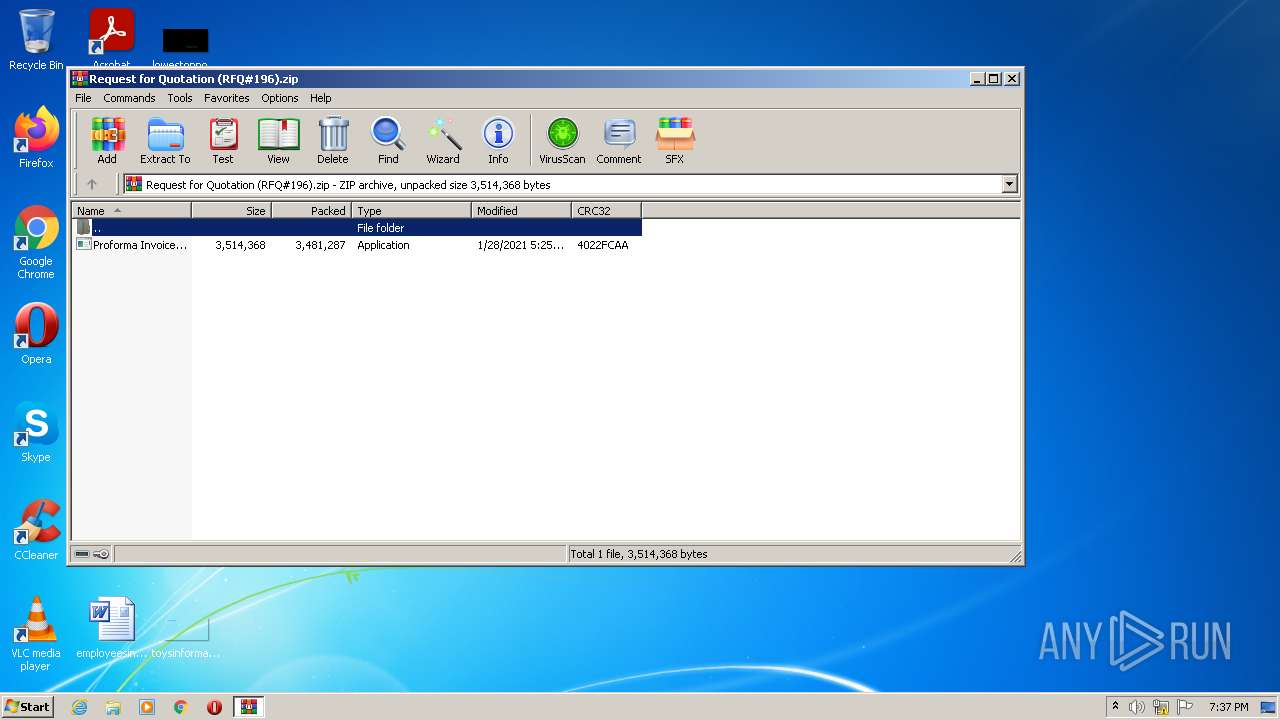
| File name: | Request for Quotation (RFQ#196).zip |
| Full analysis: | https://app.any.run/tasks/0ebb9029-8094-4e77-95d0-98c7b060e2fd |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 19:36:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D69DC6569B385C0467185D002E252D89 |
| SHA1: | 25938A66CCE0078C76A15F351CBD19C8FCC2B081 |
| SHA256: | 80239619C4CA44380C6269873A5B6B695585CCFCF278E0F2C72698658A3A6FD8 |
| SSDEEP: | 49152:pZL1zufKjTpcSPBeJJTXAlSr1/2ueI1HEafmKIDBsuN3FcTuYx/uEjF5RX:/RzvjTCVAlet2XmHxfmKIPNYx/RX |
MALICIOUS
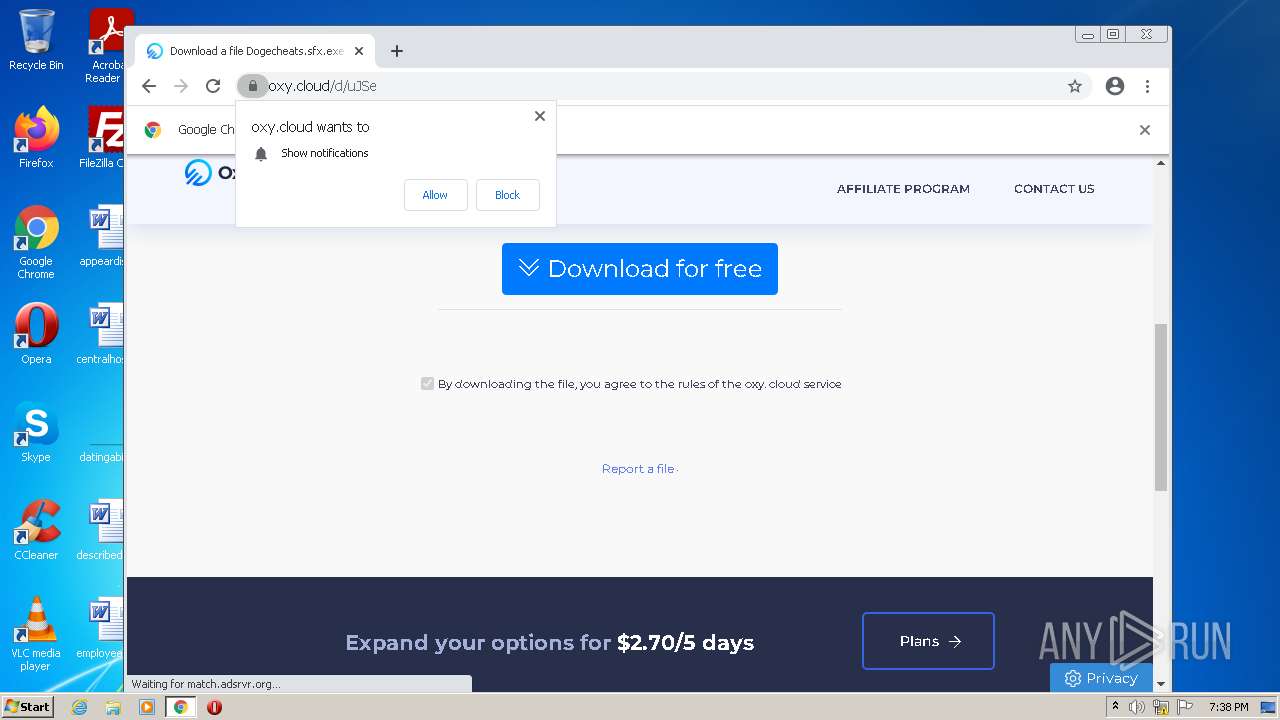
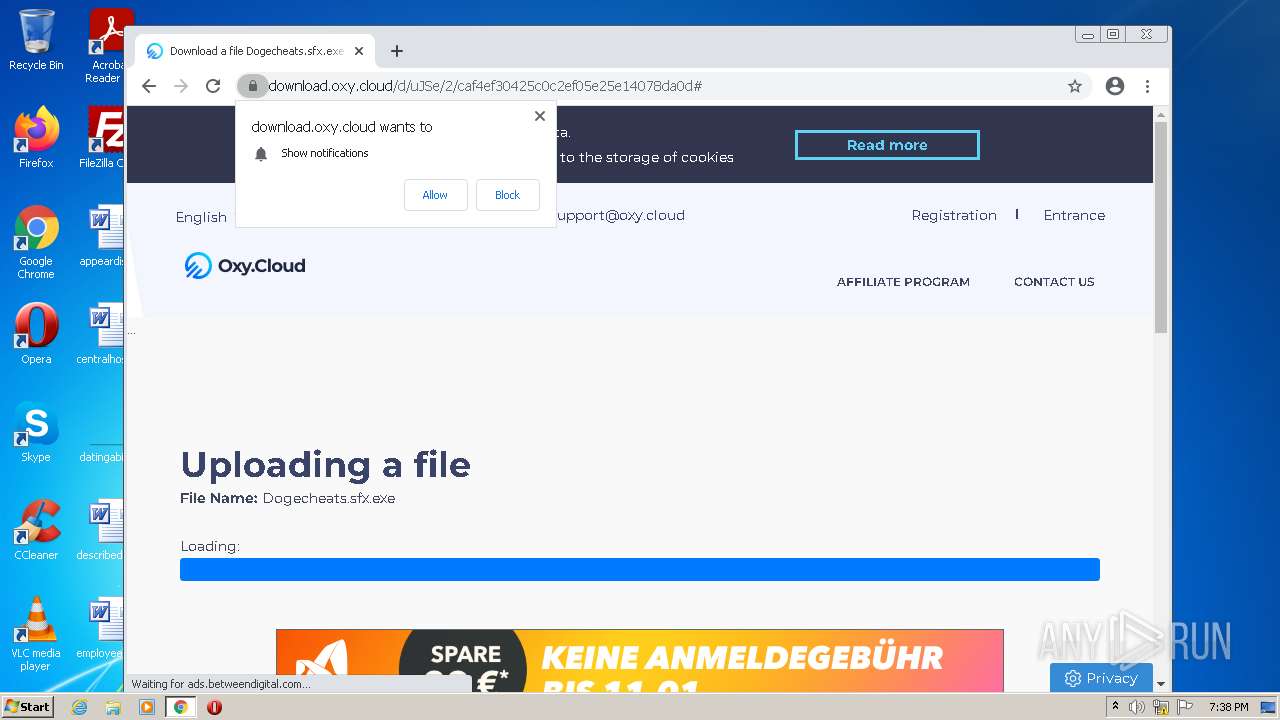
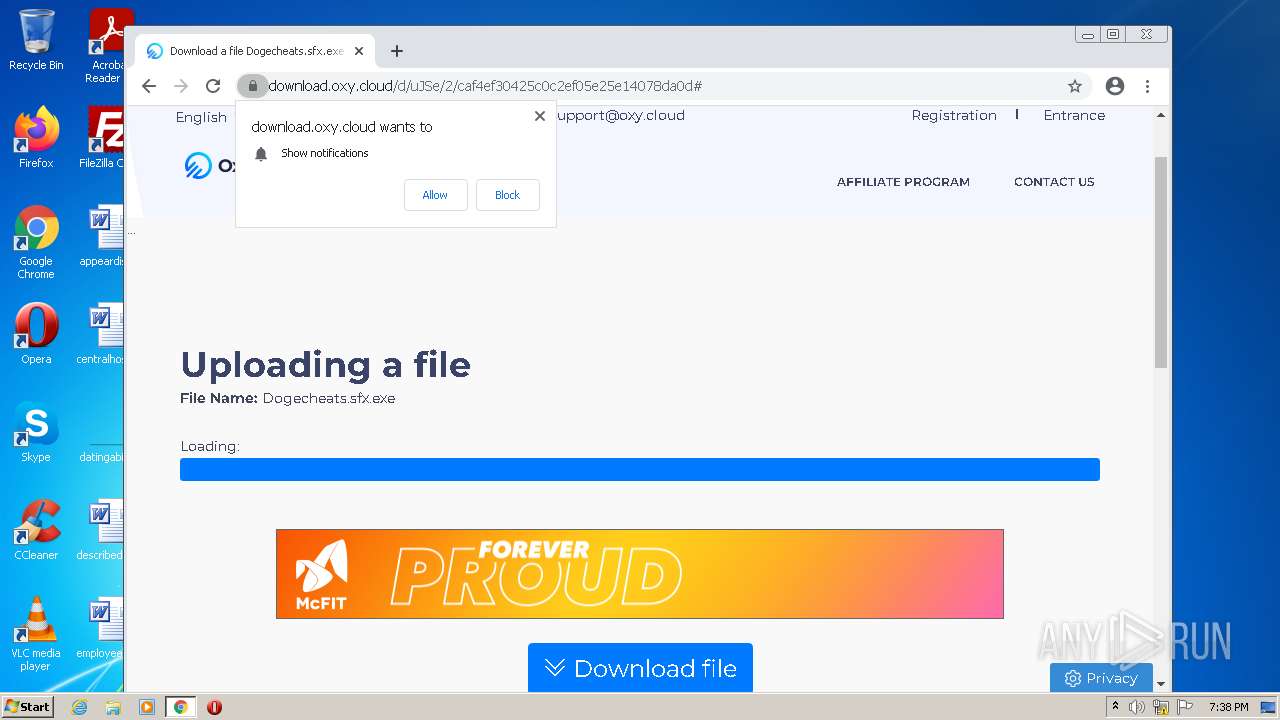
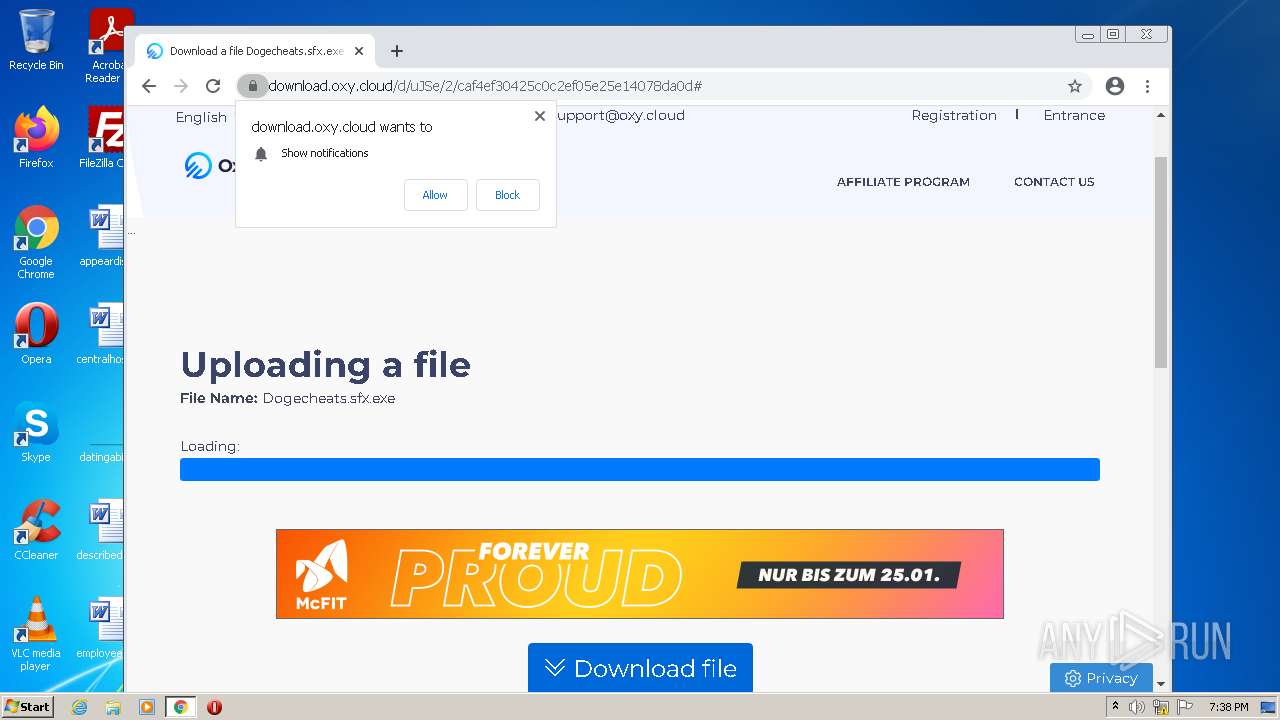
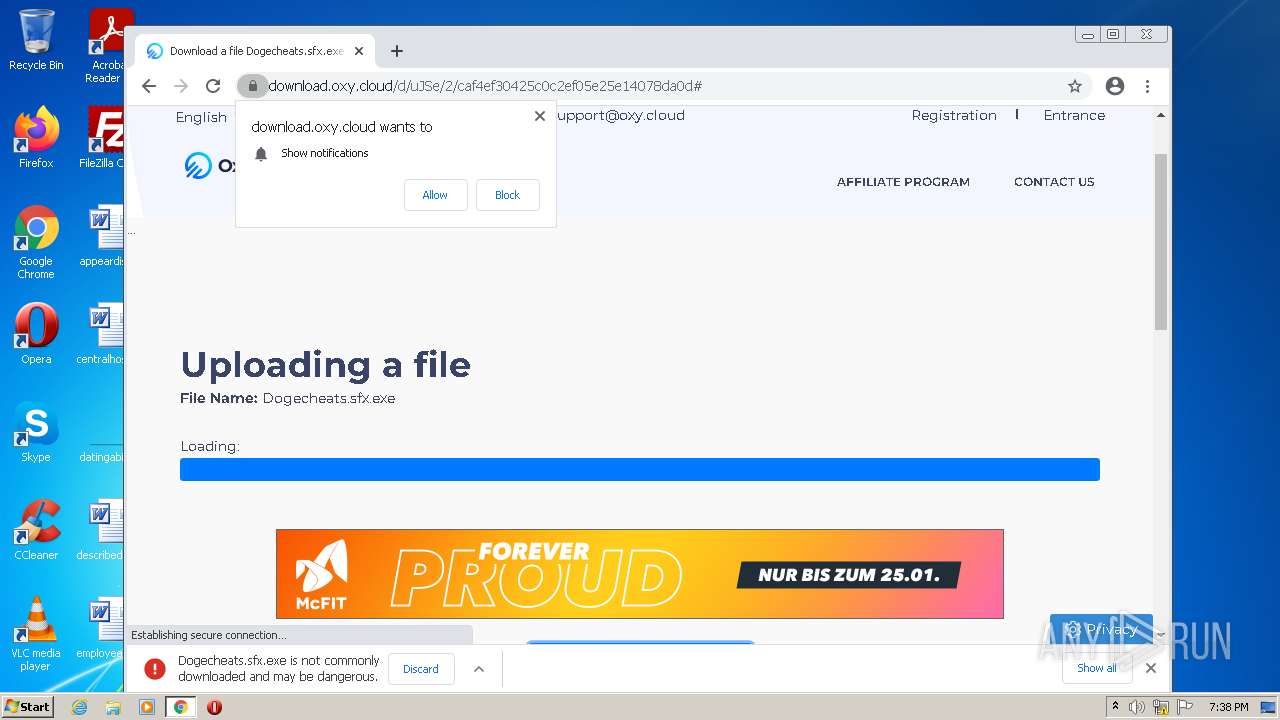
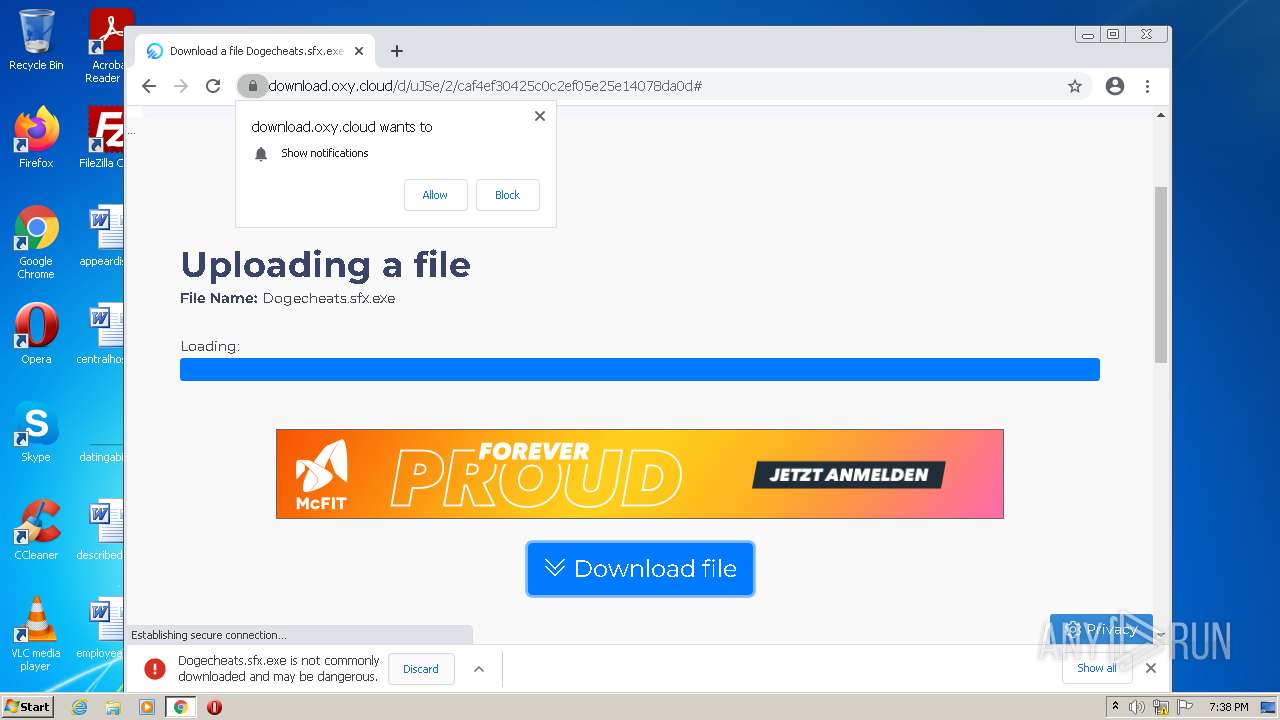
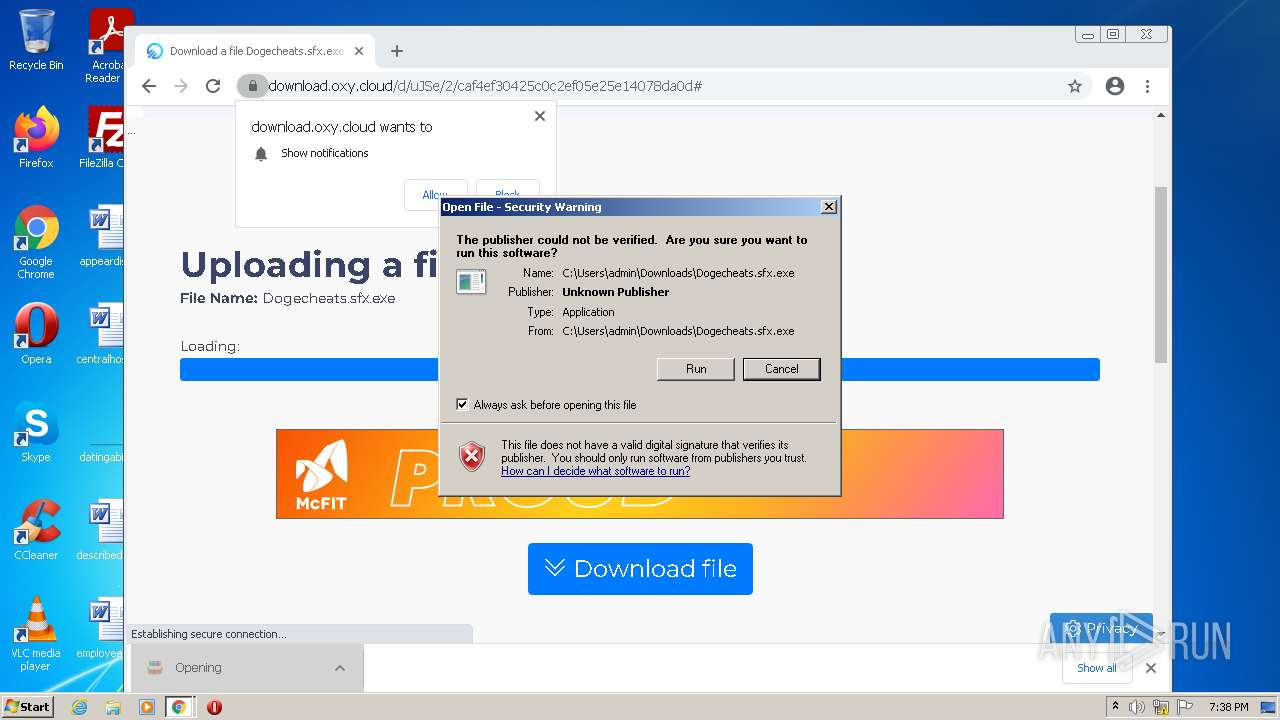
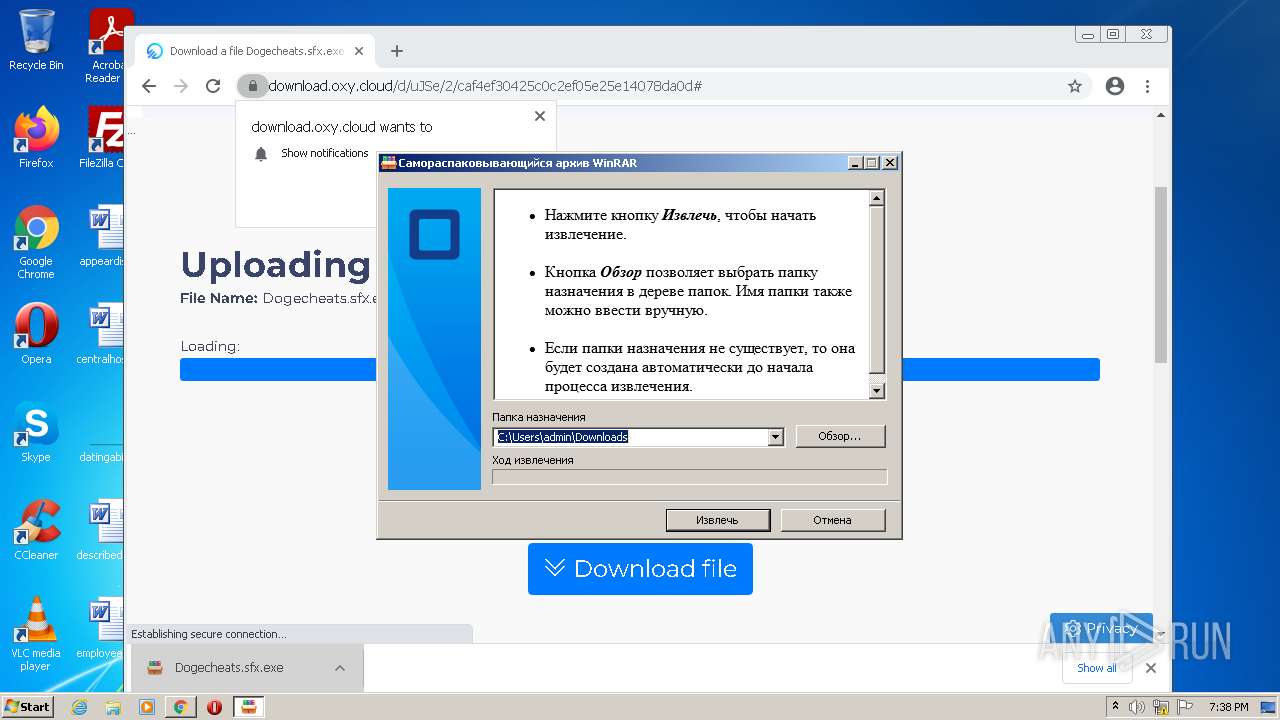
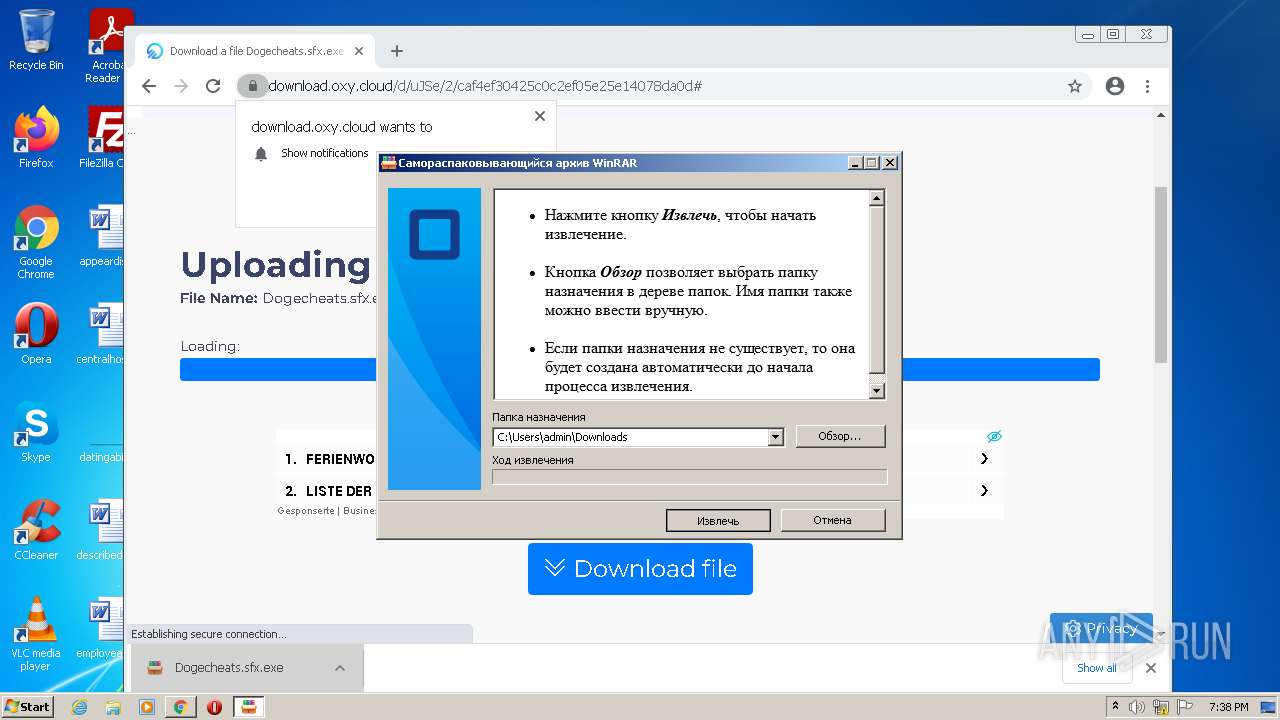
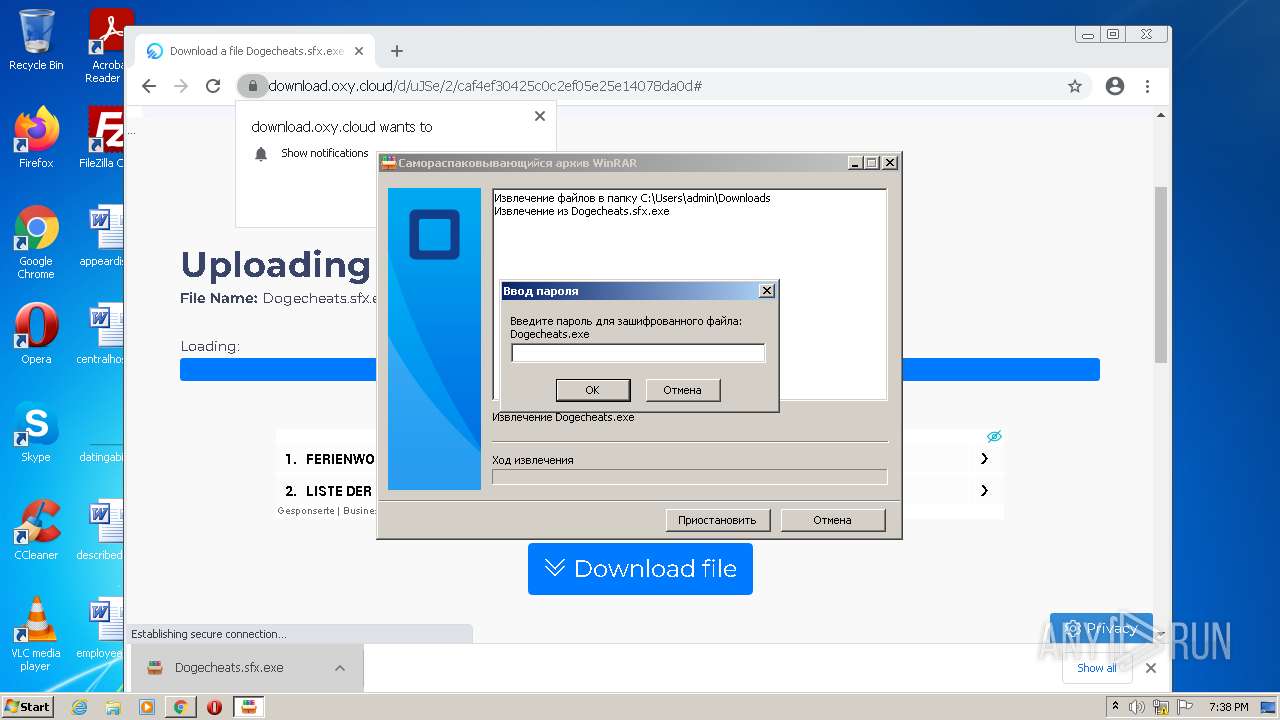
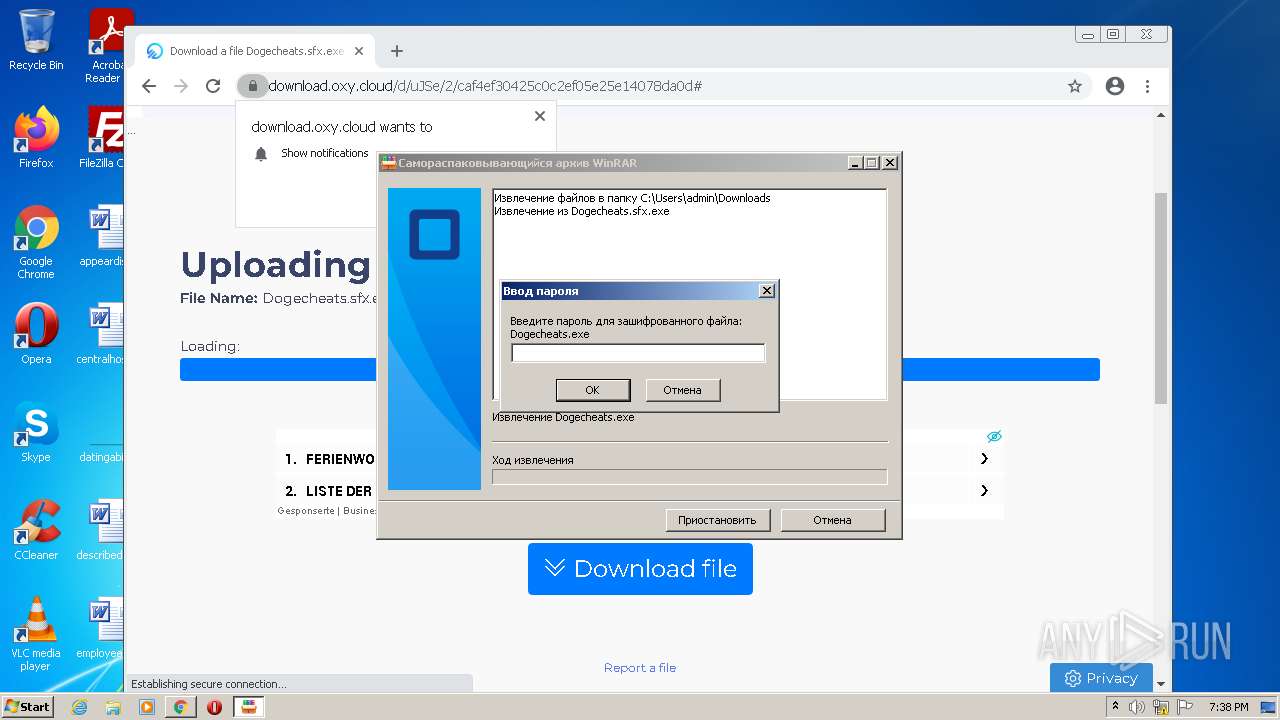
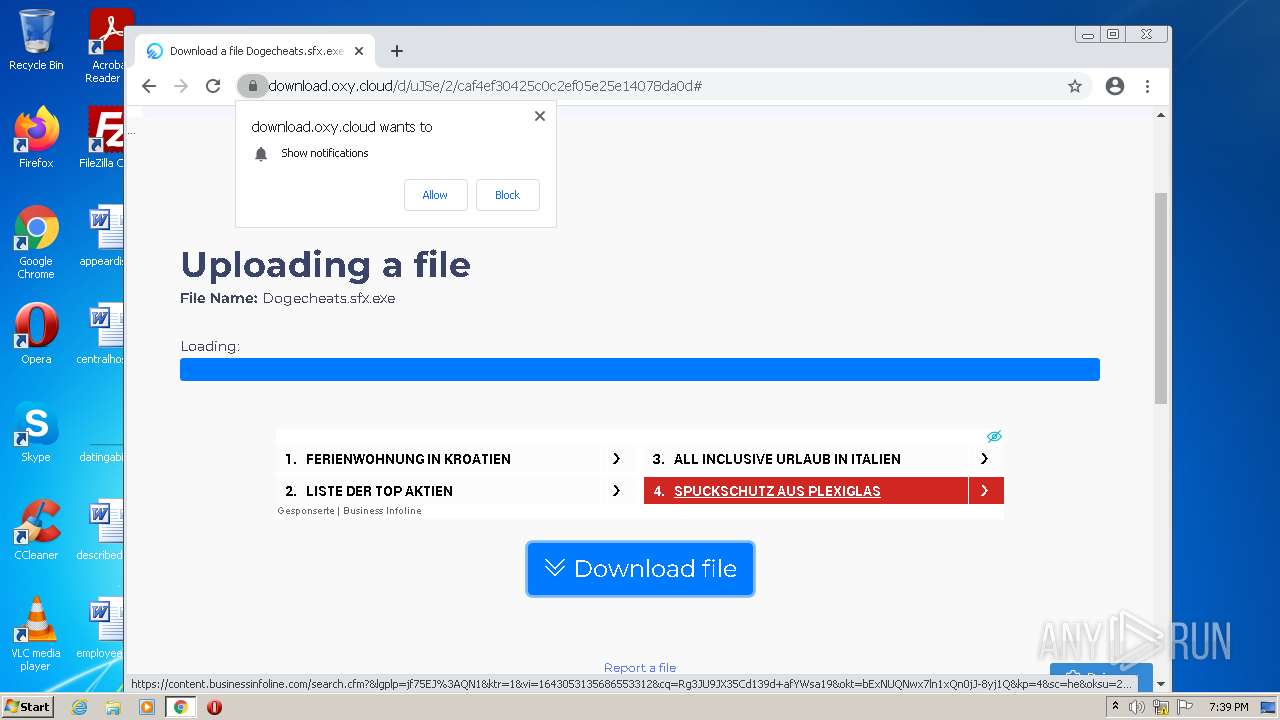
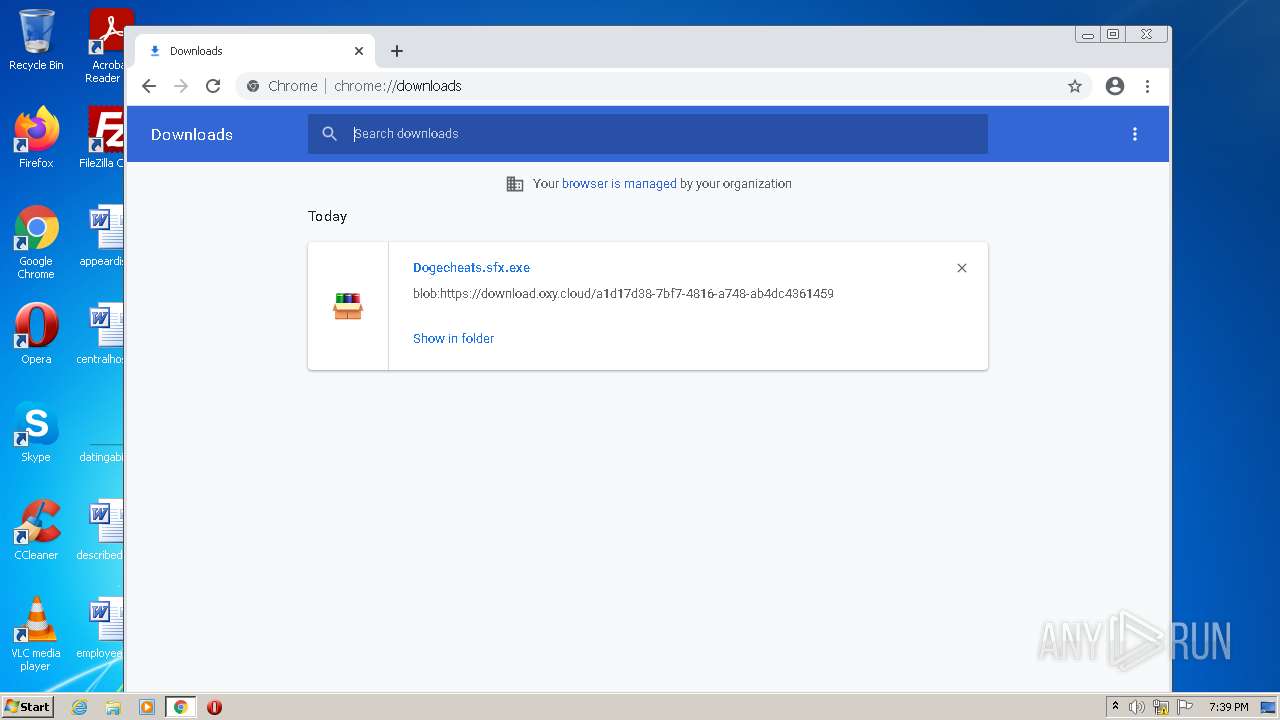
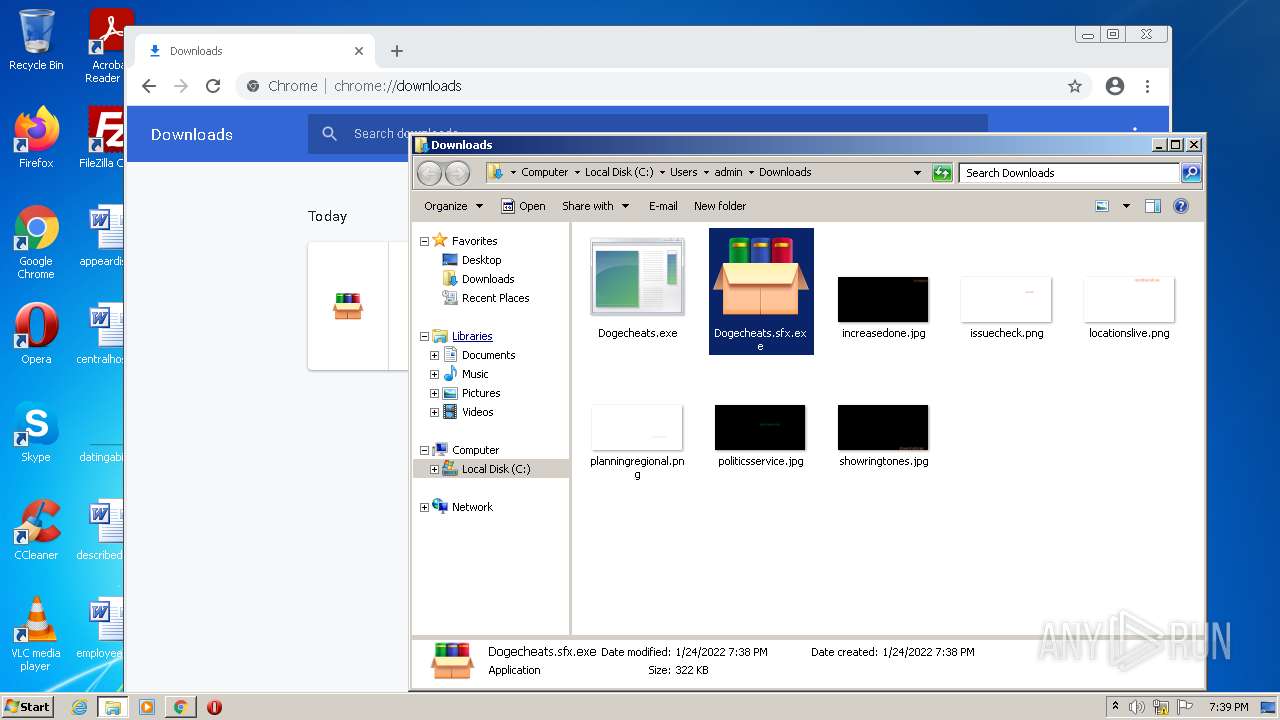
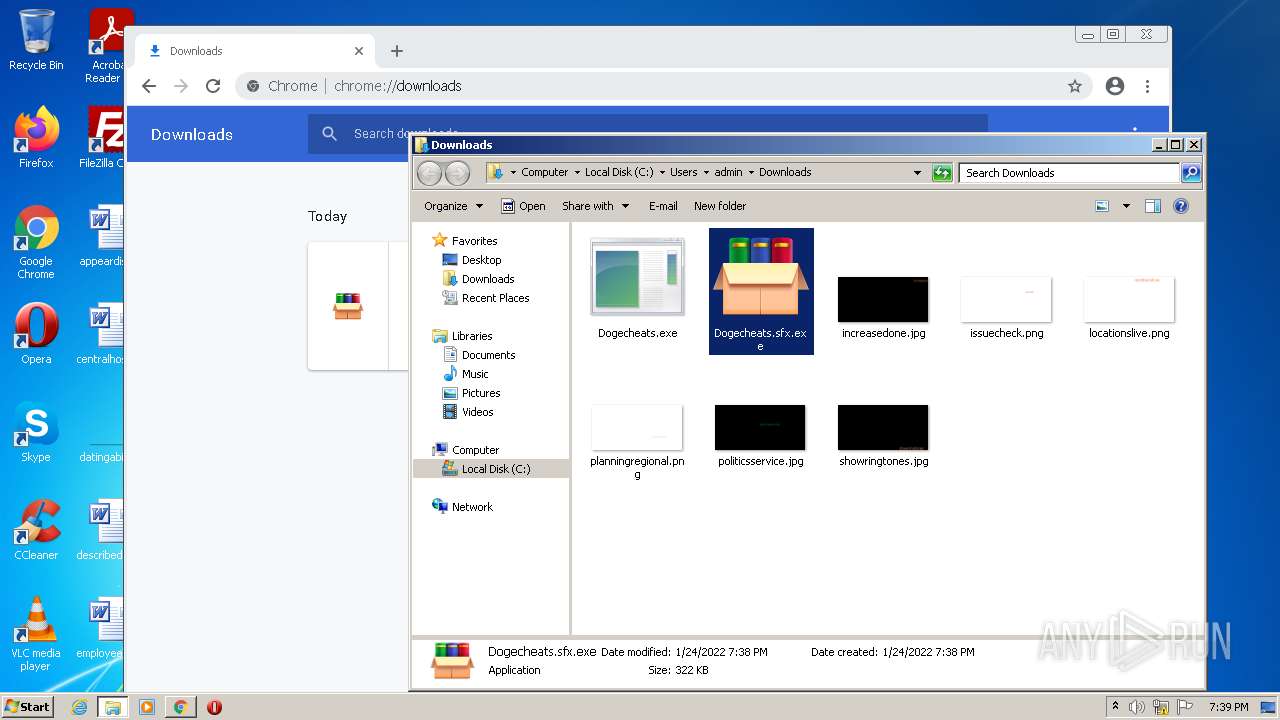
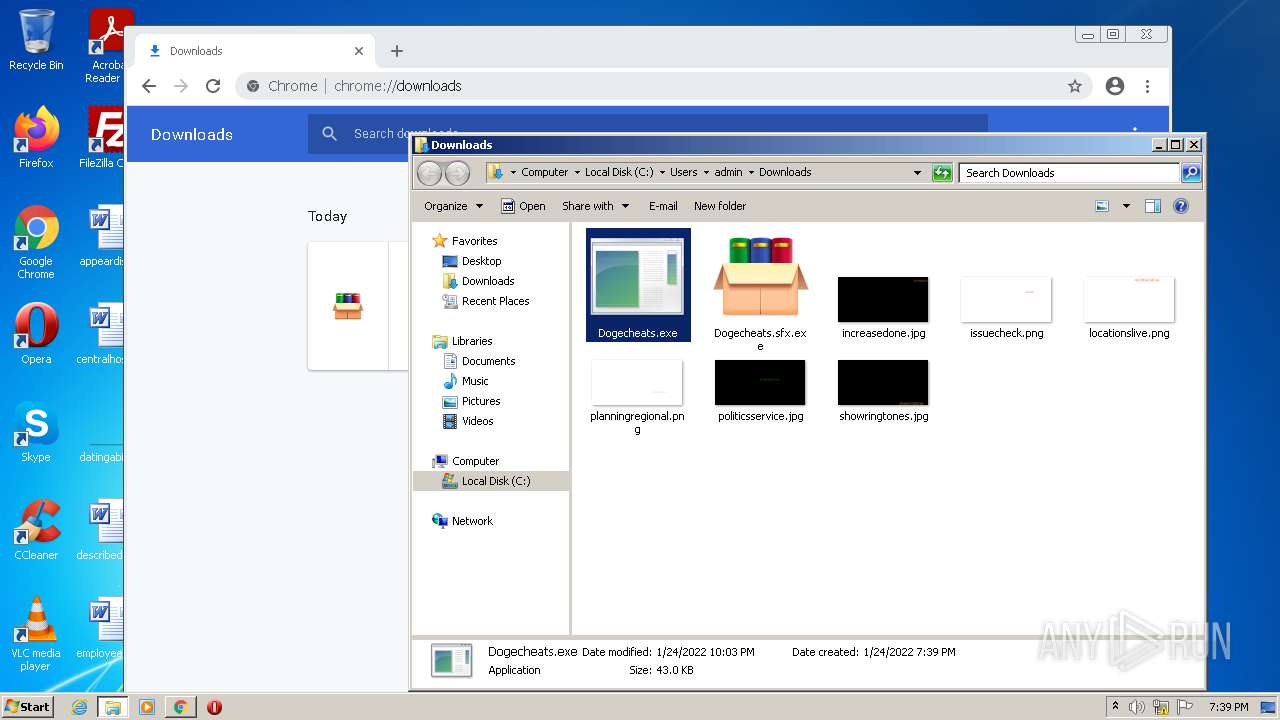
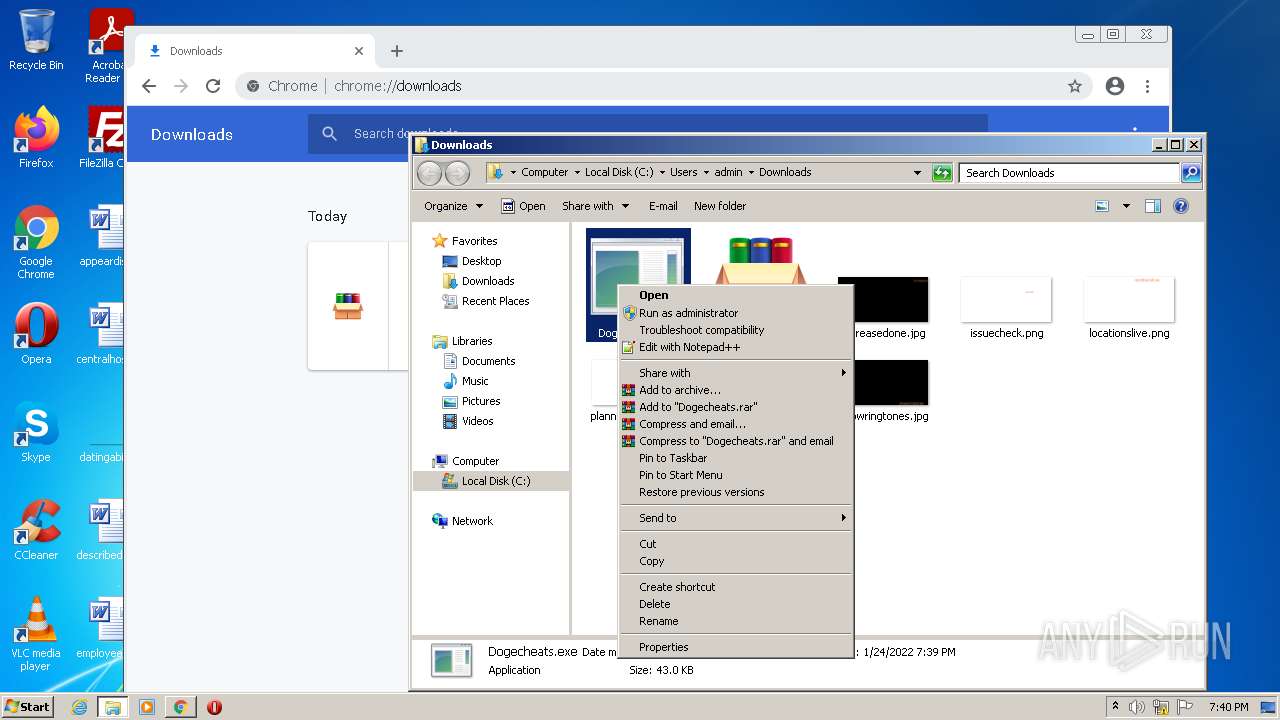
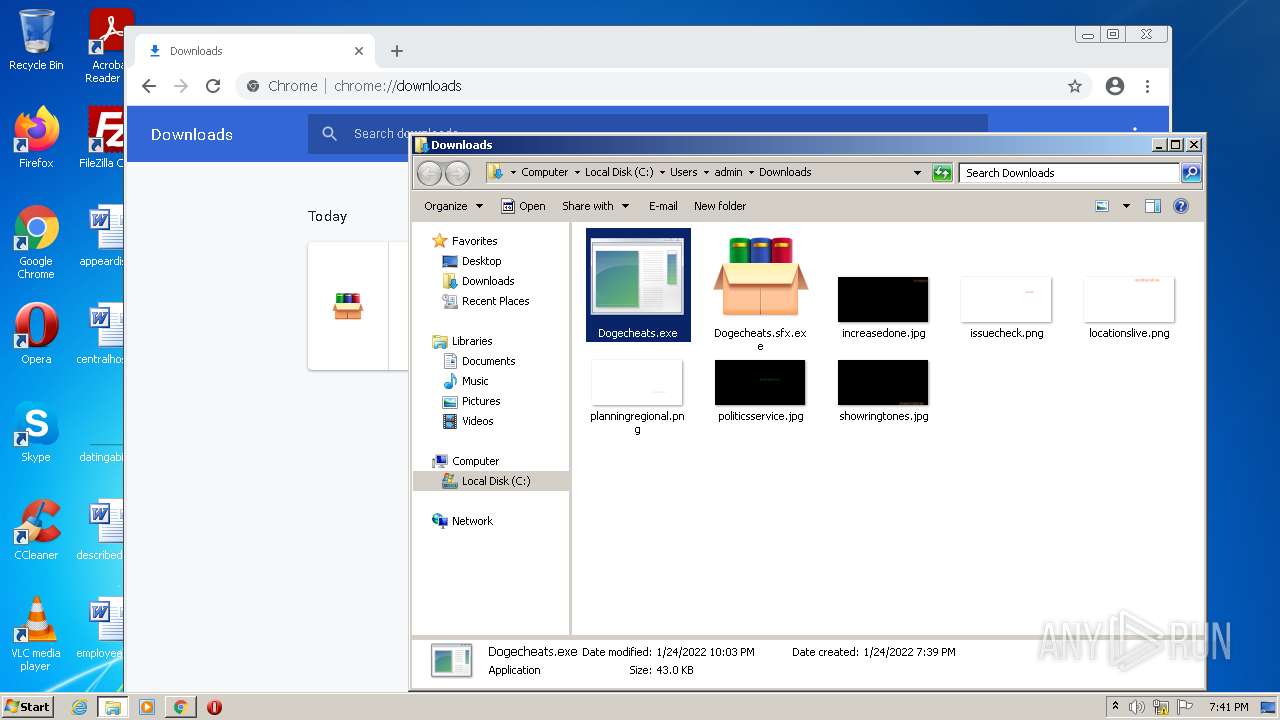
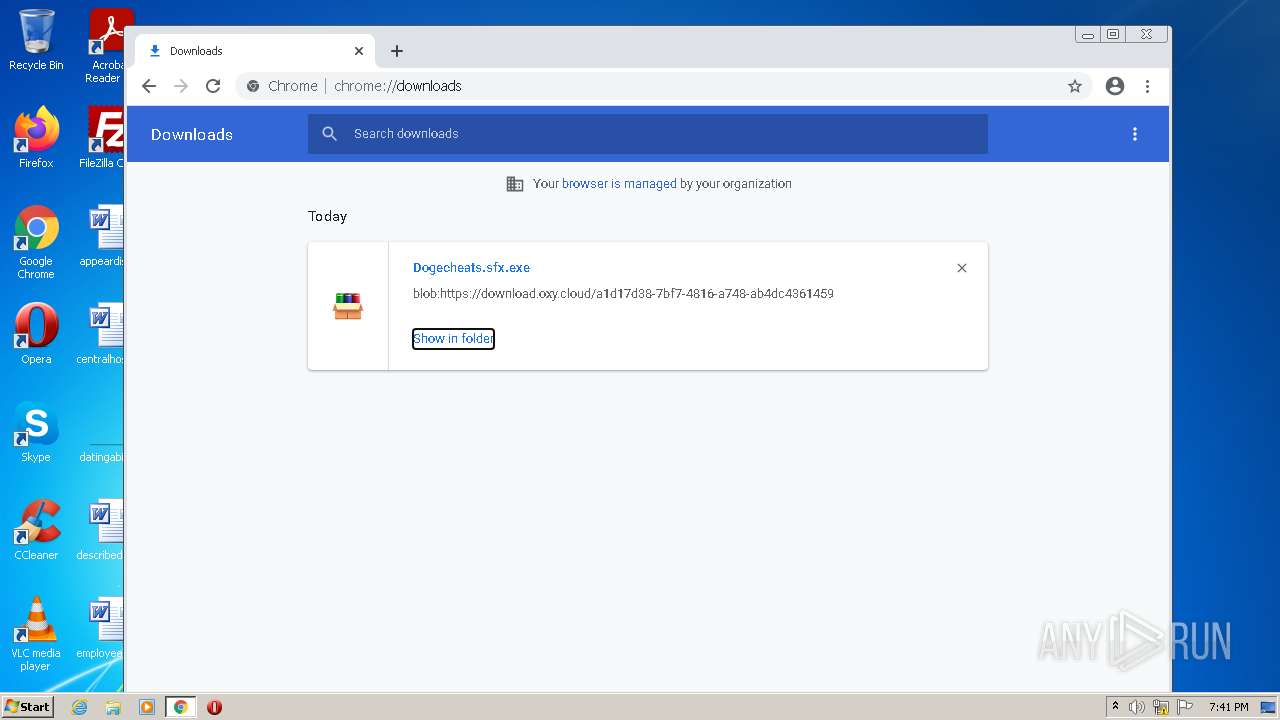
Application was dropped or rewritten from another process
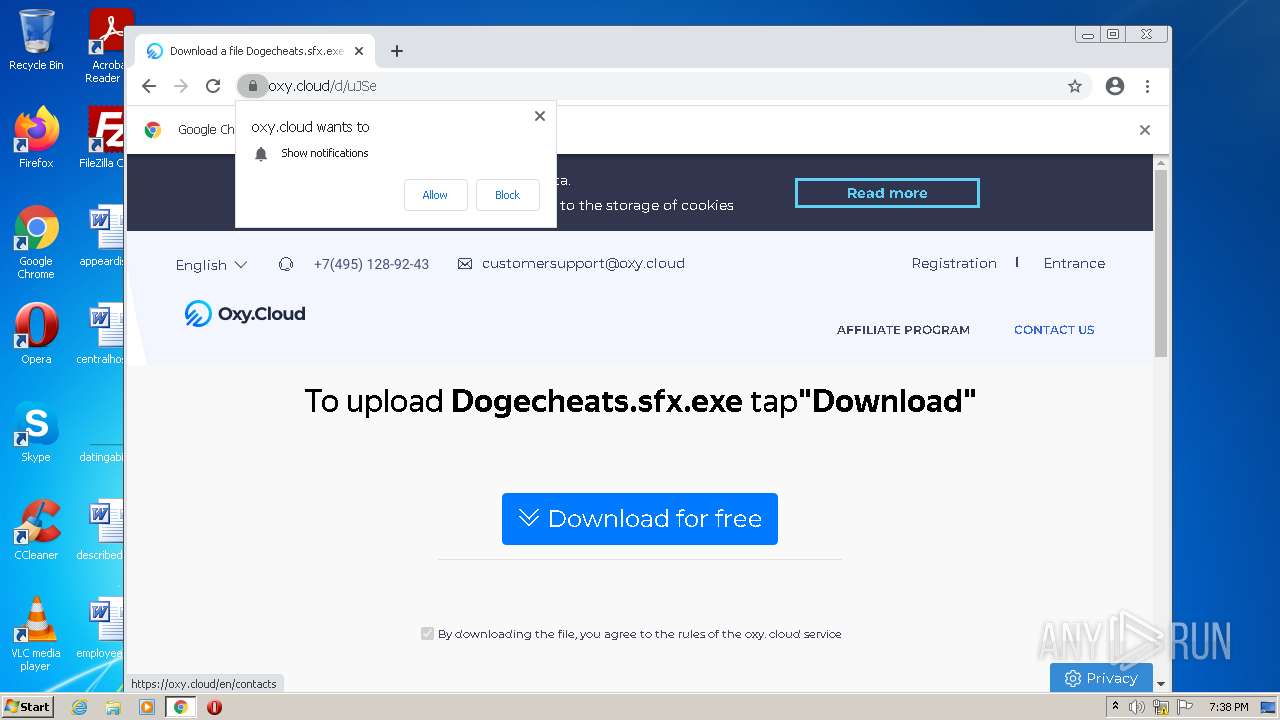
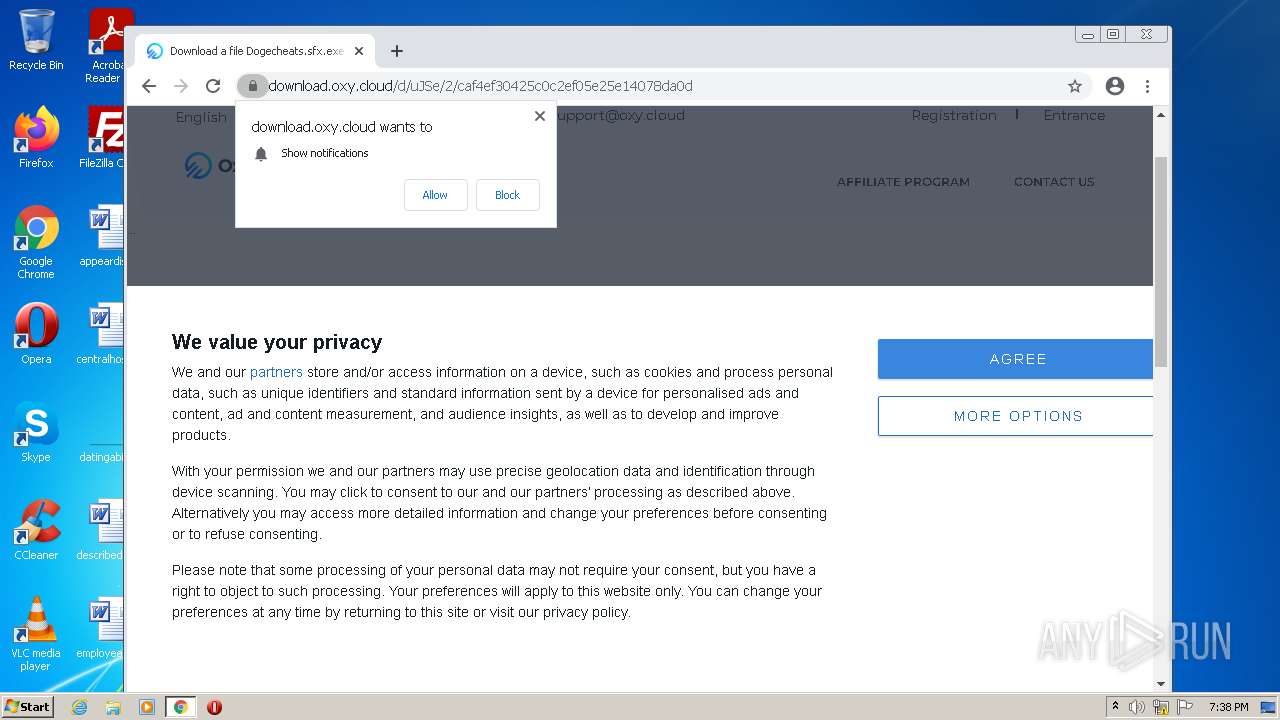
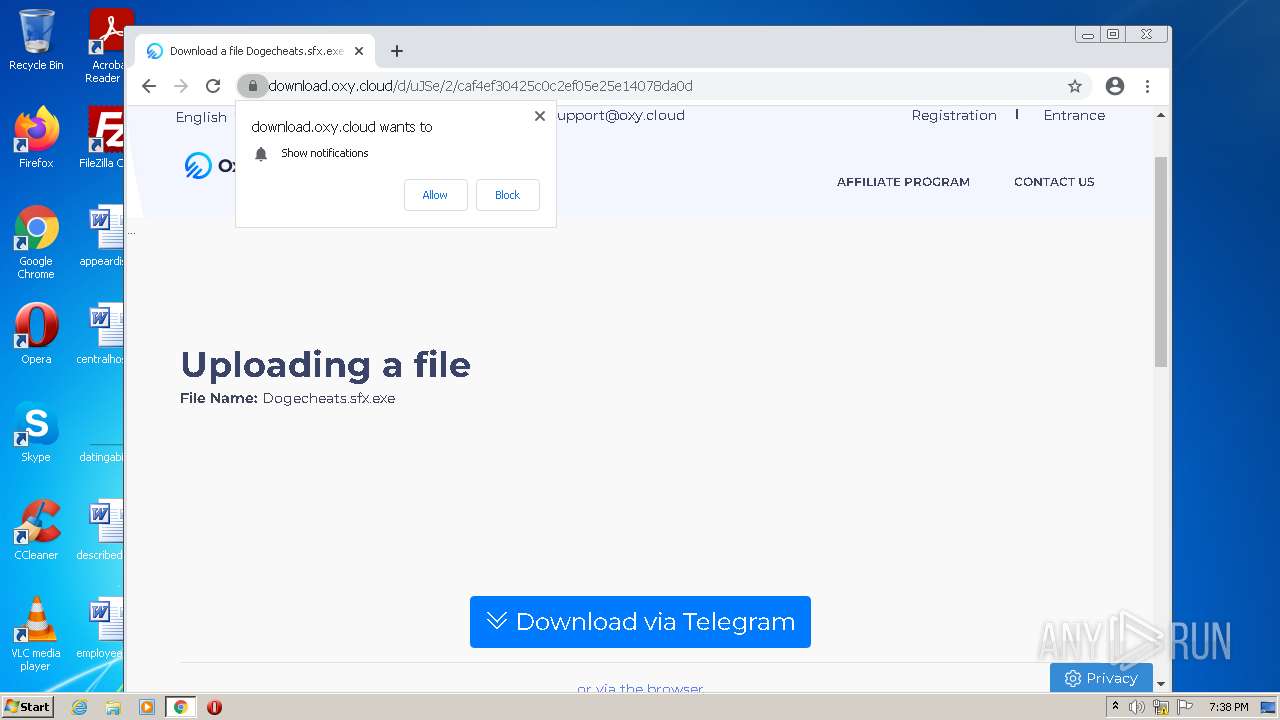
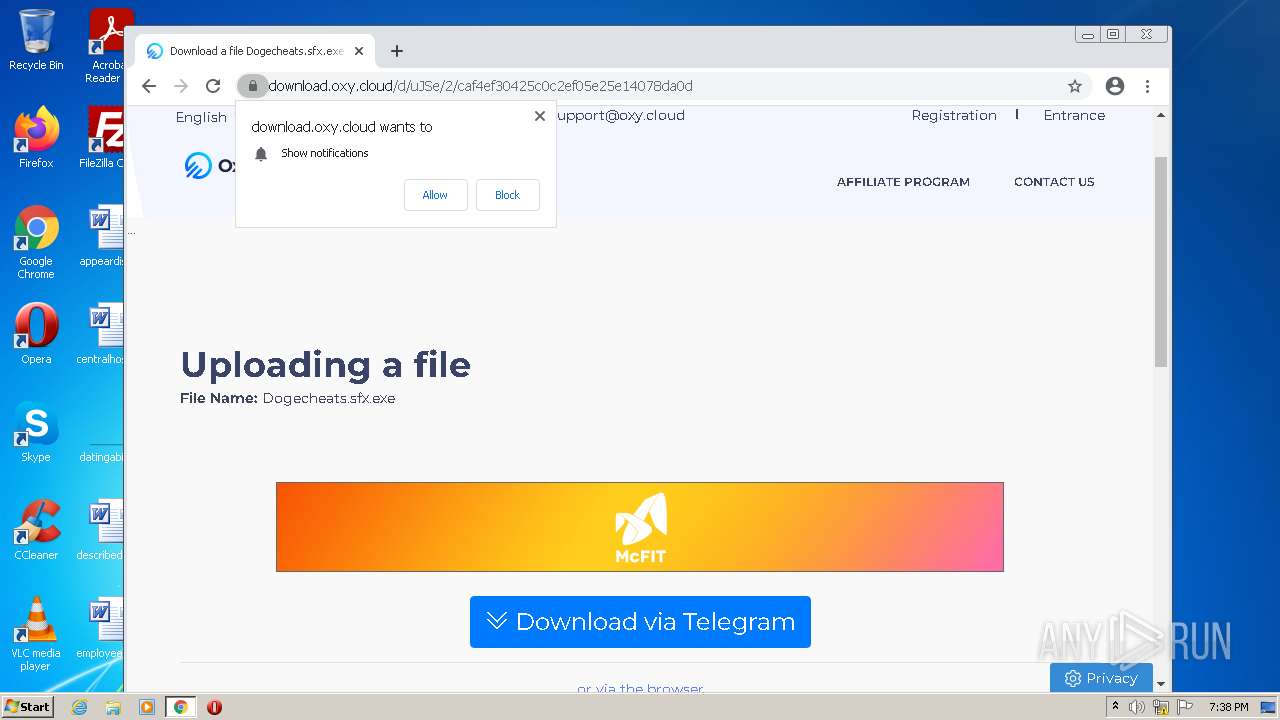
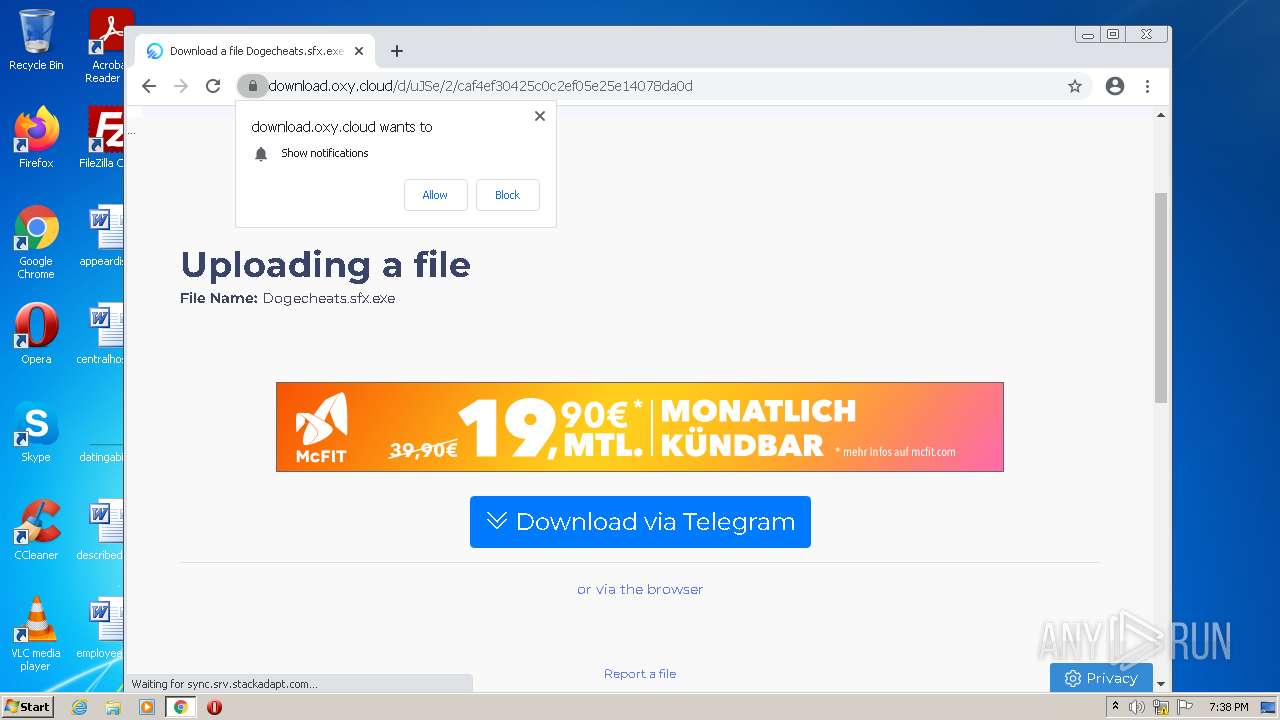
- Dogecheats.sfx.exe (PID: 1176)
- Dogecheats.exe (PID: 4308)
- Dllhost.exe (PID: 4772)
- Server.exe (PID: 3920)
- Dogecheats.exe (PID: 960)
- Dogecheats.exe (PID: 5264)
- Dogecheats.exe (PID: 3812)
- Server.exe (PID: 5524)
- Dogecheats.exe (PID: 6092)
- Server.exe (PID: 5992)
Writes to a start menu file
- Dllhost.exe (PID: 4772)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 5816)
Uses Task Scheduler to run other applications
- Dllhost.exe (PID: 4772)
Changes the autorun value in the registry
- Dllhost.exe (PID: 4772)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3552)
- Dogecheats.sfx.exe (PID: 1176)
- Dogecheats.exe (PID: 4308)
- Dllhost.exe (PID: 4772)
- Server.exe (PID: 3920)
- Dogecheats.exe (PID: 960)
- Dogecheats.exe (PID: 5264)
- Dogecheats.exe (PID: 3812)
- Server.exe (PID: 5524)
- Dogecheats.exe (PID: 6092)
- Server.exe (PID: 5992)
Checks supported languages
- WinRAR.exe (PID: 3552)
- Dogecheats.sfx.exe (PID: 1176)
- Dogecheats.exe (PID: 4308)
- Dllhost.exe (PID: 4772)
- Server.exe (PID: 3920)
- Dogecheats.exe (PID: 960)
- Dogecheats.exe (PID: 5264)
- Dogecheats.exe (PID: 3812)
- Server.exe (PID: 5524)
- Dogecheats.exe (PID: 6092)
- Server.exe (PID: 5992)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3300)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3300)
Executable content was dropped or overwritten
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3300)
- Dogecheats.sfx.exe (PID: 1176)
- Dogecheats.exe (PID: 4308)
- Dllhost.exe (PID: 4772)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 4420)
- Dogecheats.sfx.exe (PID: 1176)
Drops a file with a compile date too recent
- Dogecheats.sfx.exe (PID: 1176)
- Dogecheats.exe (PID: 4308)
- Dllhost.exe (PID: 4772)
Reads internet explorer settings
- Dogecheats.sfx.exe (PID: 1176)
Starts itself from another location
- Dogecheats.exe (PID: 4308)
Creates files in the user directory
- Dllhost.exe (PID: 4772)
Executed via Task Scheduler
- Server.exe (PID: 3920)
- Server.exe (PID: 5524)
- Server.exe (PID: 5992)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3396)
Checks supported languages
- WINWORD.EXE (PID: 3396)
- chrome.exe (PID: 1212)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 2020)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 3408)
- chrome.exe (PID: 904)
- chrome.exe (PID: 588)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 928)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 492)
- chrome.exe (PID: 872)
- chrome.exe (PID: 116)
- chrome.exe (PID: 288)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 1252)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 528)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 1816)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 2304)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 1740)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 4388)
- chrome.exe (PID: 5092)
- chrome.exe (PID: 6072)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 964)
- chrome.exe (PID: 4124)
- chrome.exe (PID: 5960)
- chrome.exe (PID: 4488)
- chrome.exe (PID: 4788)
- chrome.exe (PID: 5232)
- chrome.exe (PID: 5580)
- chrome.exe (PID: 4672)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 1332)
- chrome.exe (PID: 5952)
- chrome.exe (PID: 6028)
- chrome.exe (PID: 5976)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 4768)
- chrome.exe (PID: 3536)
- chrome.exe (PID: 5884)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 4420)
- chrome.exe (PID: 4784)
- chrome.exe (PID: 4760)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2344)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 5136)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 5844)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 5560)
- chrome.exe (PID: 4892)
- chrome.exe (PID: 5564)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 1232)
- schtasks.exe (PID: 5816)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 4688)
- chrome.exe (PID: 292)
- chrome.exe (PID: 3344)
Reads the computer name
- WINWORD.EXE (PID: 3396)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 4420)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 4892)
- schtasks.exe (PID: 5816)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 4688)
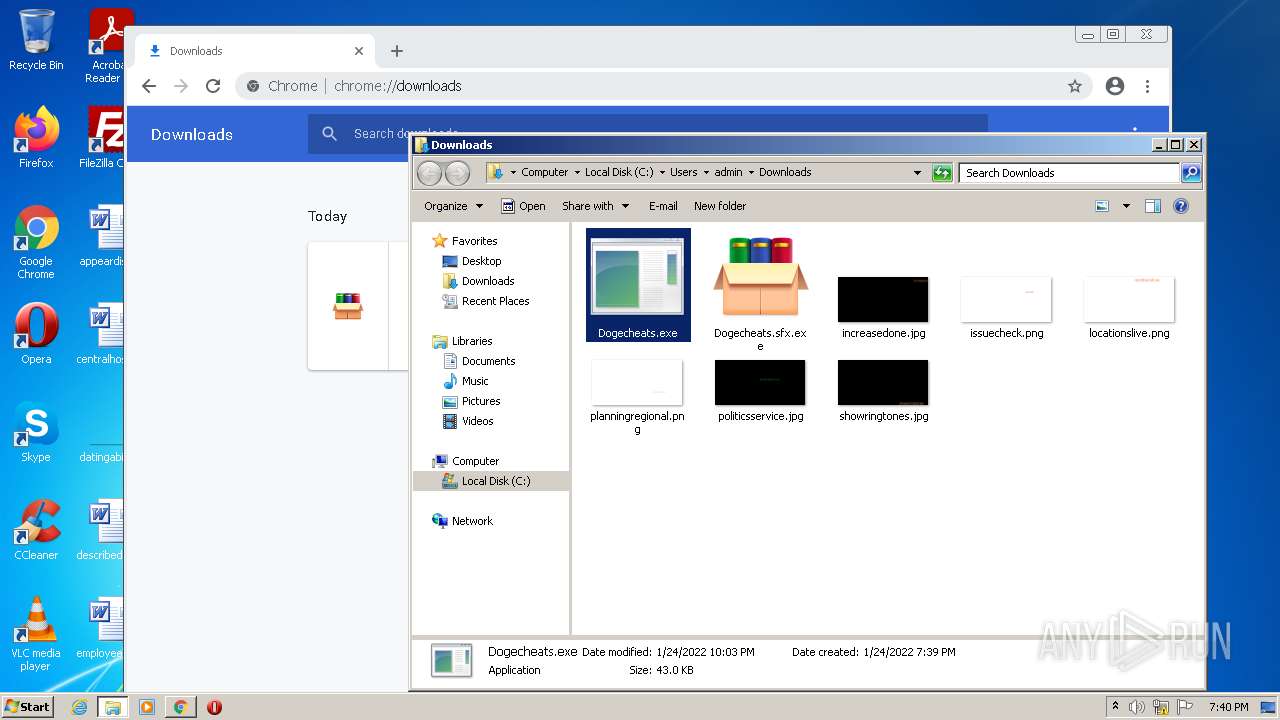
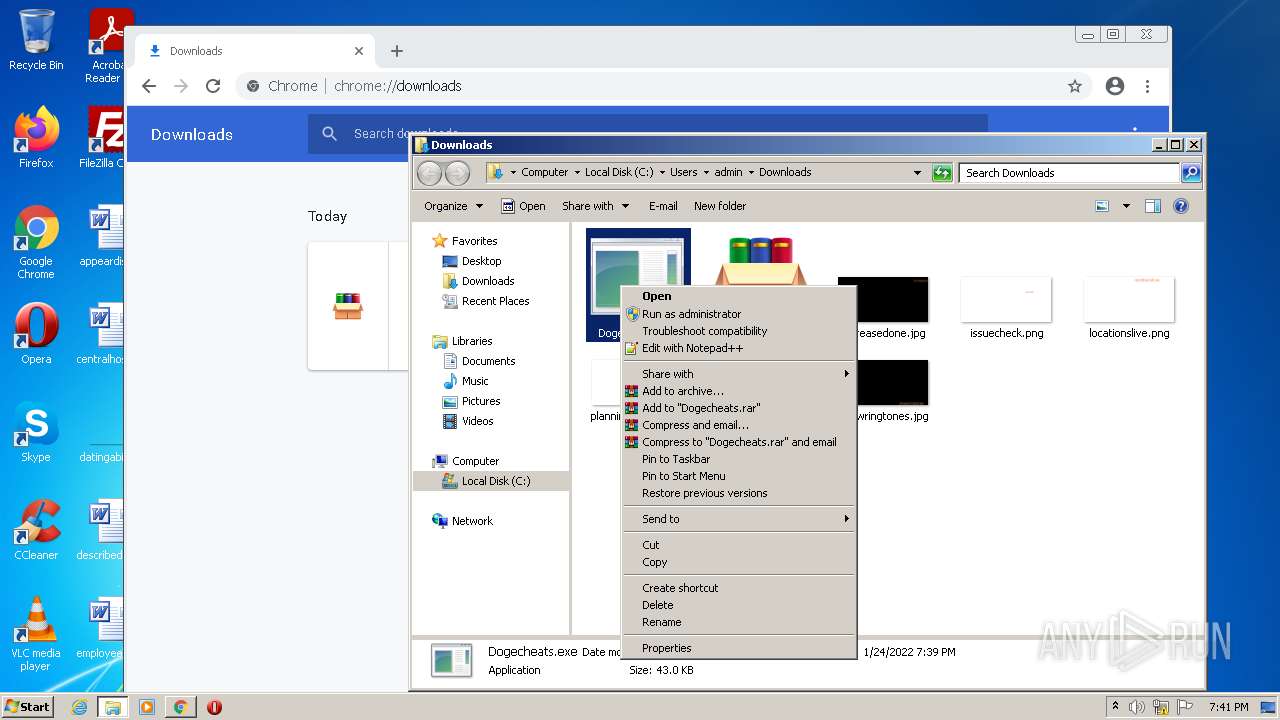
Manual execution by user
- chrome.exe (PID: 3300)
- WINWORD.EXE (PID: 3396)
- chrome.exe (PID: 2172)
- Dogecheats.exe (PID: 4308)
- Dogecheats.exe (PID: 960)
- Dogecheats.exe (PID: 5264)
- Dogecheats.exe (PID: 3812)
- Dogecheats.exe (PID: 6092)
Application launched itself
- chrome.exe (PID: 3300)
- chrome.exe (PID: 2172)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3396)
Reads the hosts file
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 1784)
Reads settings of System Certificates
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2172)
Changes settings of System certificates
- chrome.exe (PID: 3412)
Checks Windows Trust Settings
- chrome.exe (PID: 3300)
Reads the date of Windows installation
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Proforma Invoice and Bank swift-REG.PI-0086547654.exe |
|---|---|
| ZipUncompressedSize: | 3514368 |
| ZipCompressedSize: | 3481287 |
| ZipCRC: | 0x4022fcaa |
| ZipModifyDate: | 2021:01:28 09:25:18 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0009 |
| ZipRequiredVersion: | 20 |
Total processes
156
Monitored processes
109
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1012,17276791777057775018,14539443134721542097,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3708 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12350609966795919514,2275364154897060975,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\Downloads\Dogecheats.exe" | C:\Users\admin\Downloads\Dogecheats.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
44 355
Read events
43 612
Write events
590
Delete events
153
Modification events
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Request for Quotation (RFQ#196).zip | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
8
Suspicious files
311
Text files
260
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBD13.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF001F-CE4.pma | — | |
MD5:— | SHA256:— | |||
| 3396 | WINWORD.EXE | C:\Users\admin\Desktop\~$oclear.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{4999FFA6-BFF6-4CF2-AEBA-7A9DD2FA4AB0}.tmp | binary | |
MD5:— | SHA256:— | |||
| 3396 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 3396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3F1697A5-3AB9-418F-8AB6-76FE37DDD62A}.tmp | dbf | |
MD5:— | SHA256:— | |||
| 3396 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\proclear.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3396 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF125396.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1254b0.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
331
DNS requests
237
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 200 | 74.125.108.167:80 | http://r2---sn-2gb7sn7y.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.202.16&mm=28&mn=sn-2gb7sn7y&ms=nvh&mt=1643052982&mv=m&mvi=2&pl=24&rmhost=r3---sn-2gb7sn7y.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
3412 | chrome.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 555 b | whitelisted |
876 | svchost.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
876 | svchost.exe | GET | 206 | 74.125.108.167:80 | http://r2---sn-2gb7sn7y.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.202.16&mm=28&mn=sn-2gb7sn7y&ms=nvh&mt=1643052982&mv=m&mvi=2&pl=24&rmhost=r3---sn-2gb7sn7y.gvt1.com&shardbypass=yes | US | binary | 5.63 Kb | whitelisted |
876 | svchost.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
876 | svchost.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
876 | svchost.exe | GET | 206 | 74.125.108.167:80 | http://r2---sn-2gb7sn7y.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.202.16&mm=28&mn=sn-2gb7sn7y&ms=nvh&mt=1643052982&mv=m&mvi=2&pl=24&rmhost=r3---sn-2gb7sn7y.gvt1.com&shardbypass=yes | US | binary | 20.7 Kb | whitelisted |
876 | svchost.exe | GET | 206 | 74.125.108.167:80 | http://r2---sn-2gb7sn7y.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=45.86.202.16&mm=28&mn=sn-2gb7sn7y&ms=nvh&mt=1643052982&mv=m&mvi=2&pl=24&rmhost=r3---sn-2gb7sn7y.gvt1.com&shardbypass=yes | US | binary | 9.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3412 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 142.250.184.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 142.250.185.68:443 | www.google.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 142.250.186.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 142.250.181.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3412 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
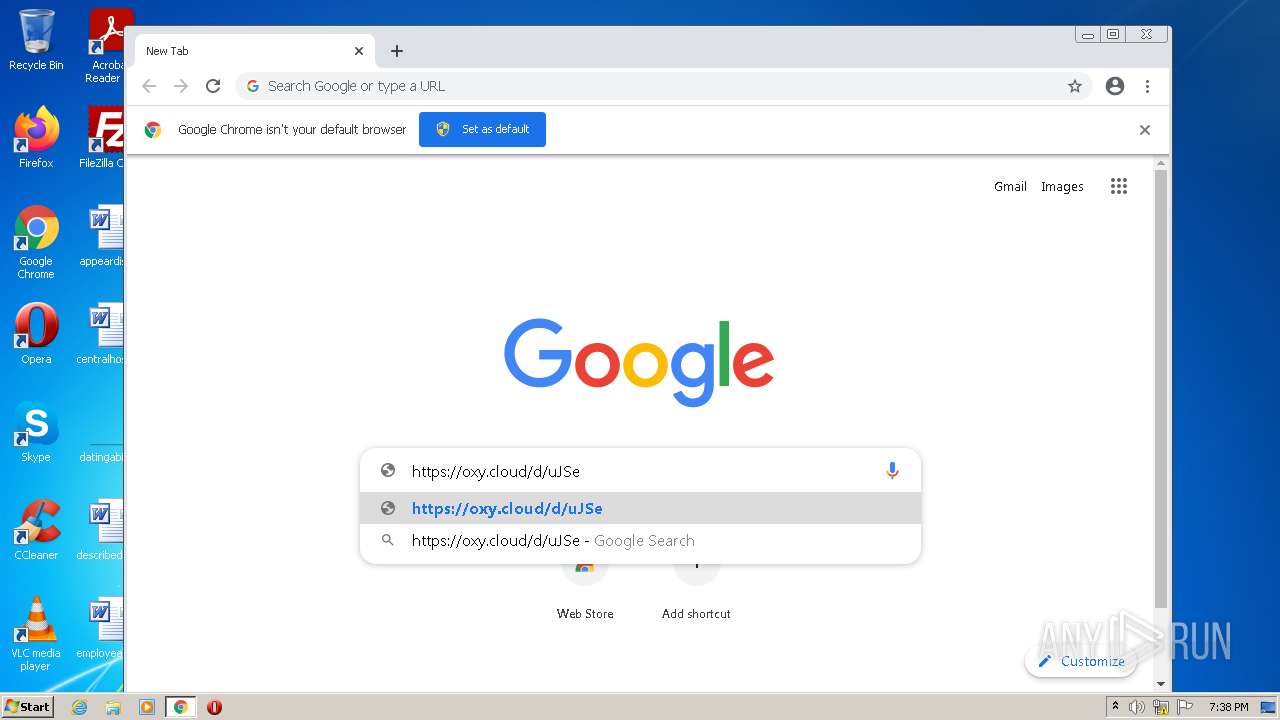
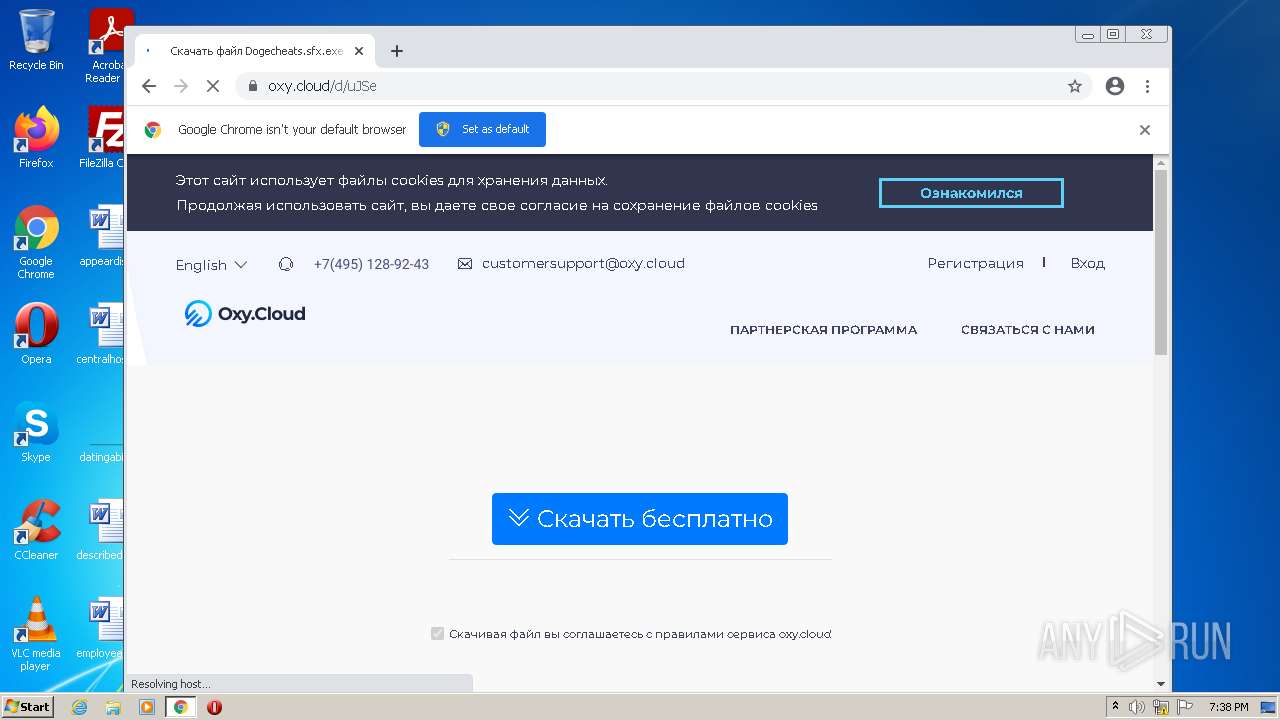
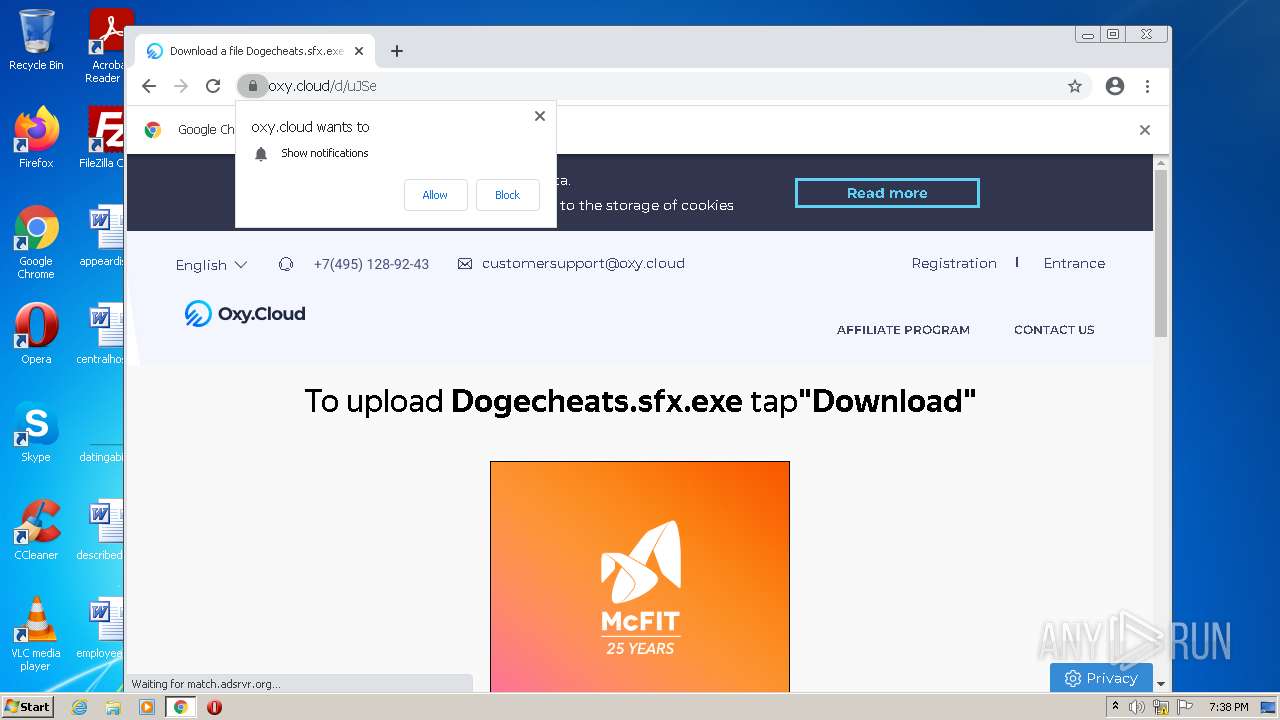
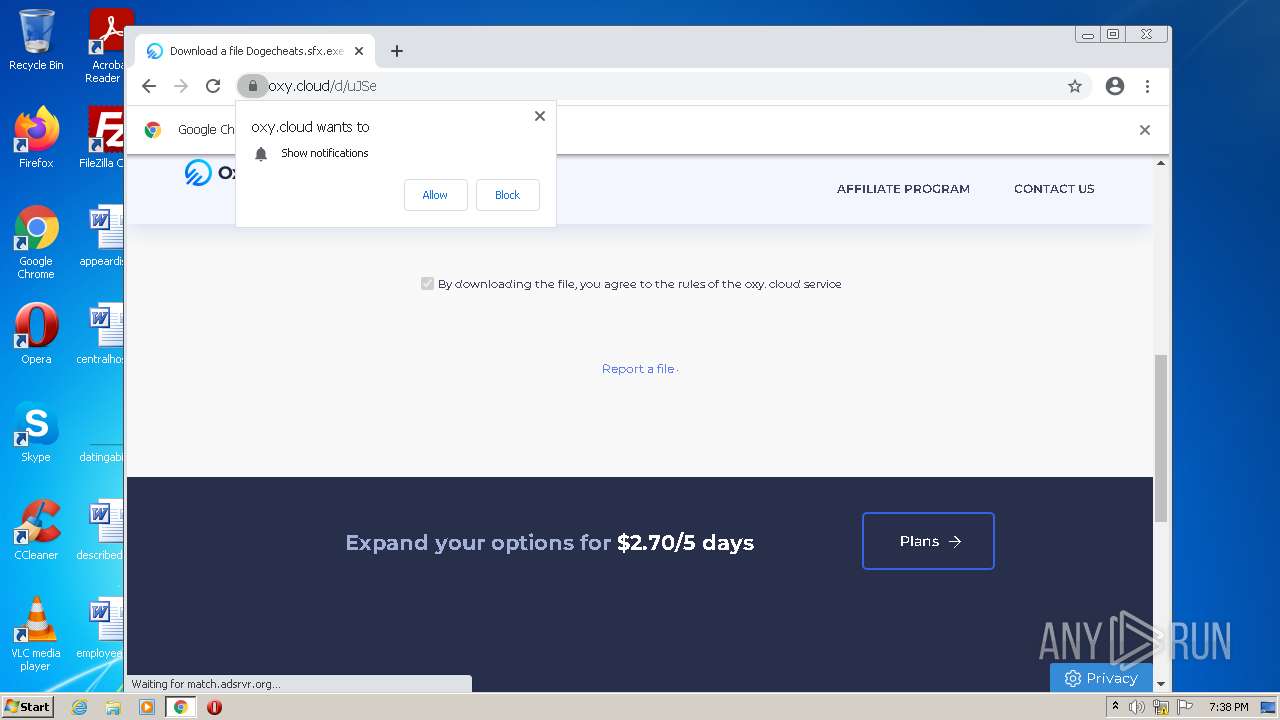
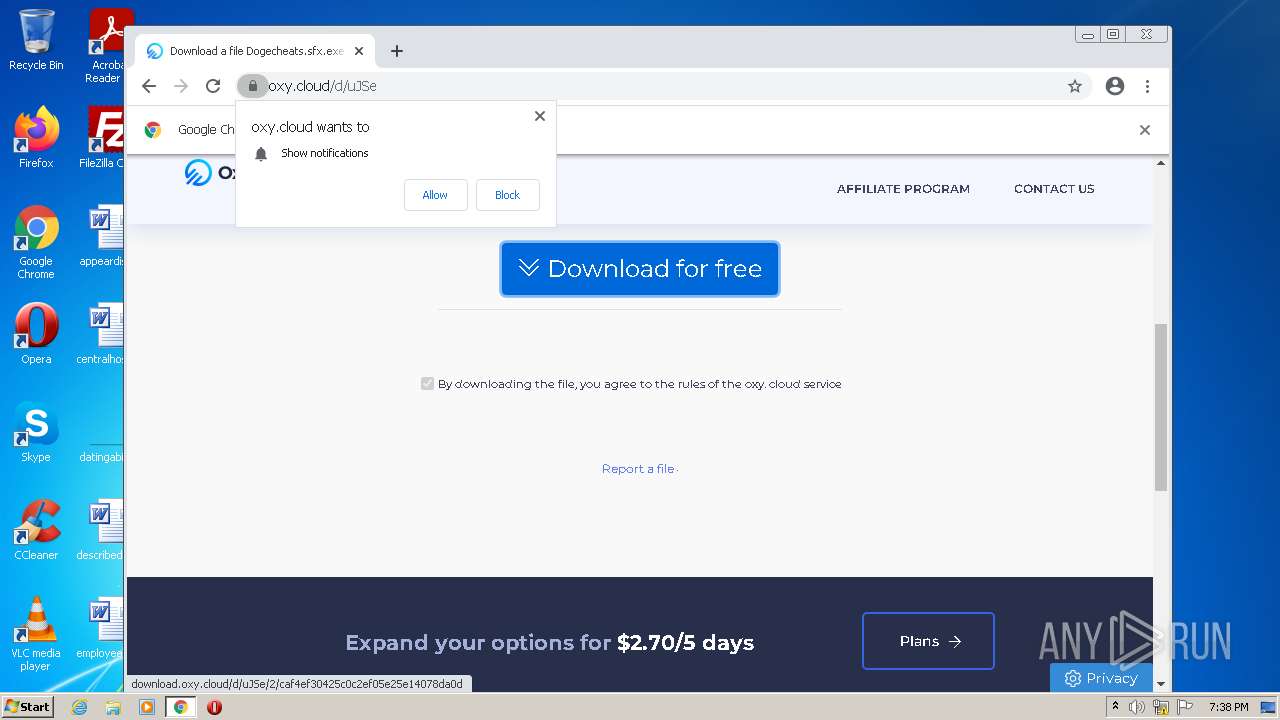
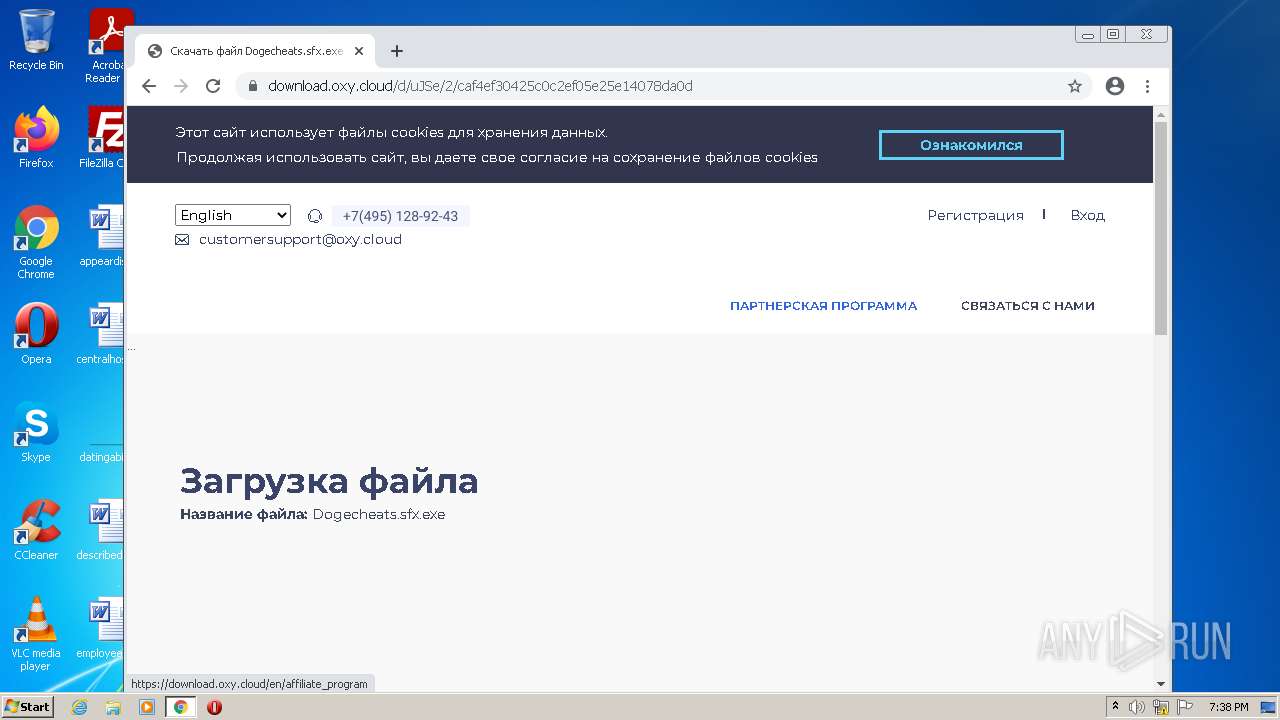
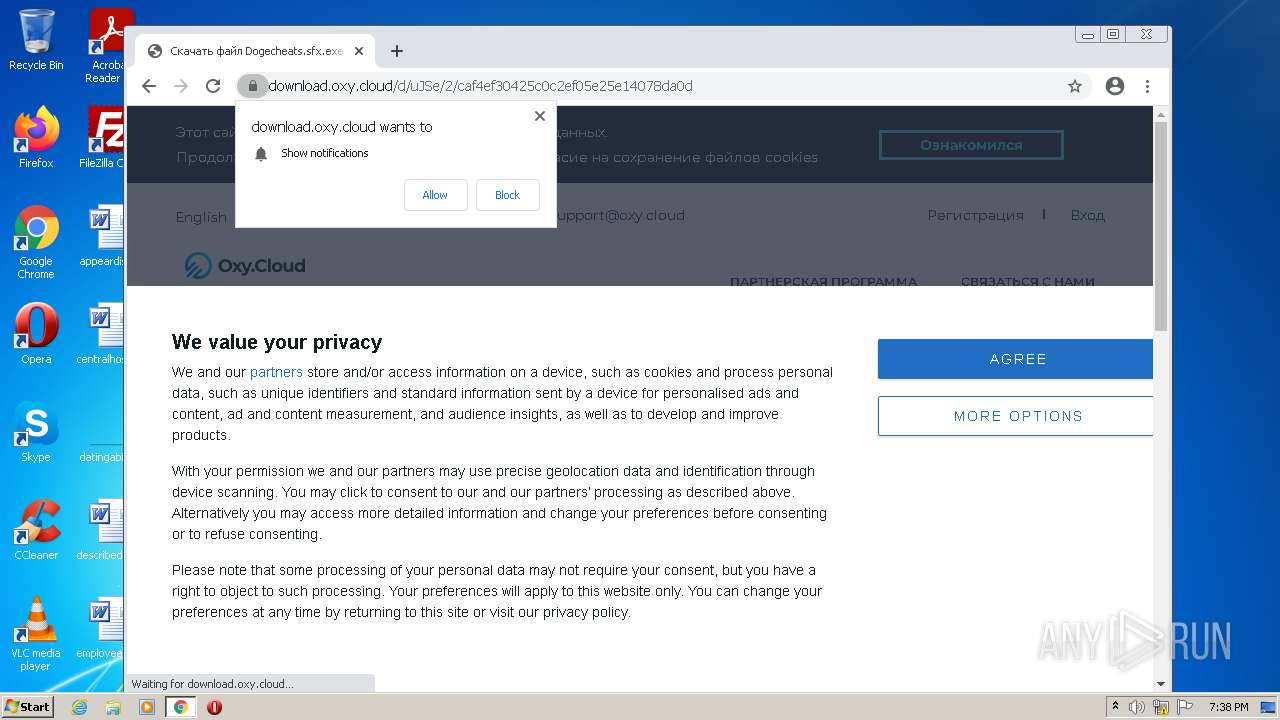
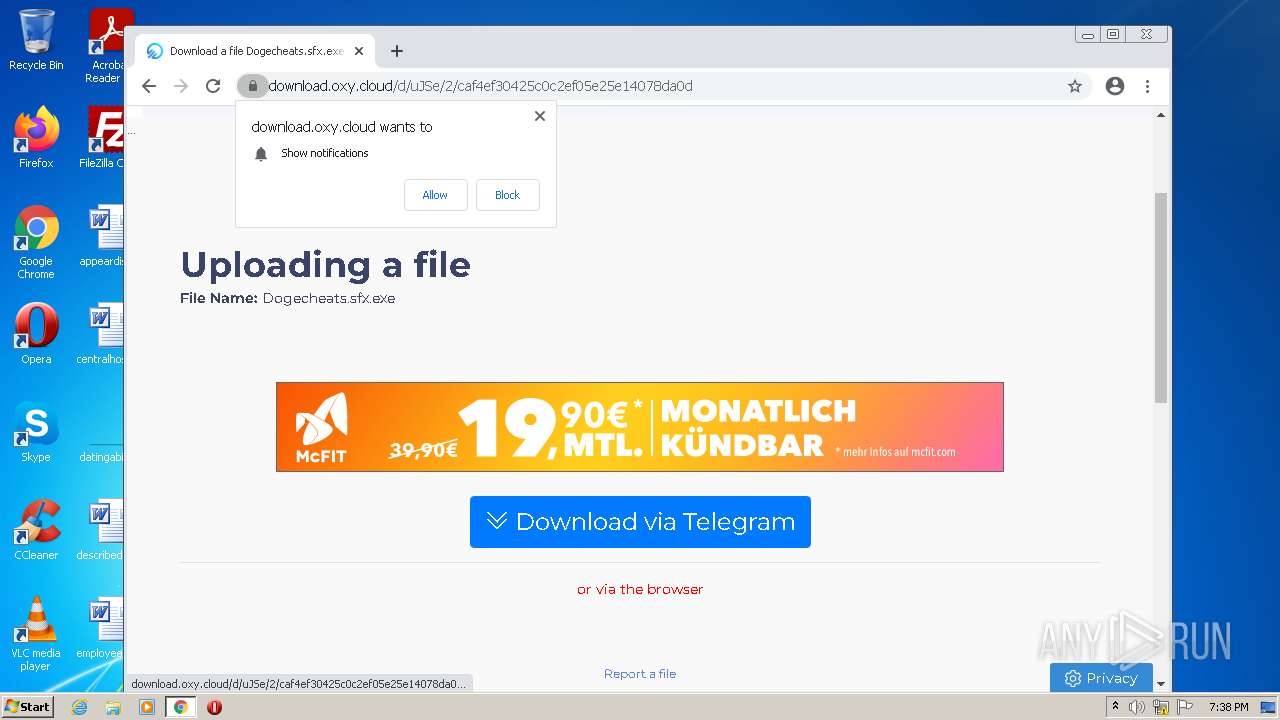
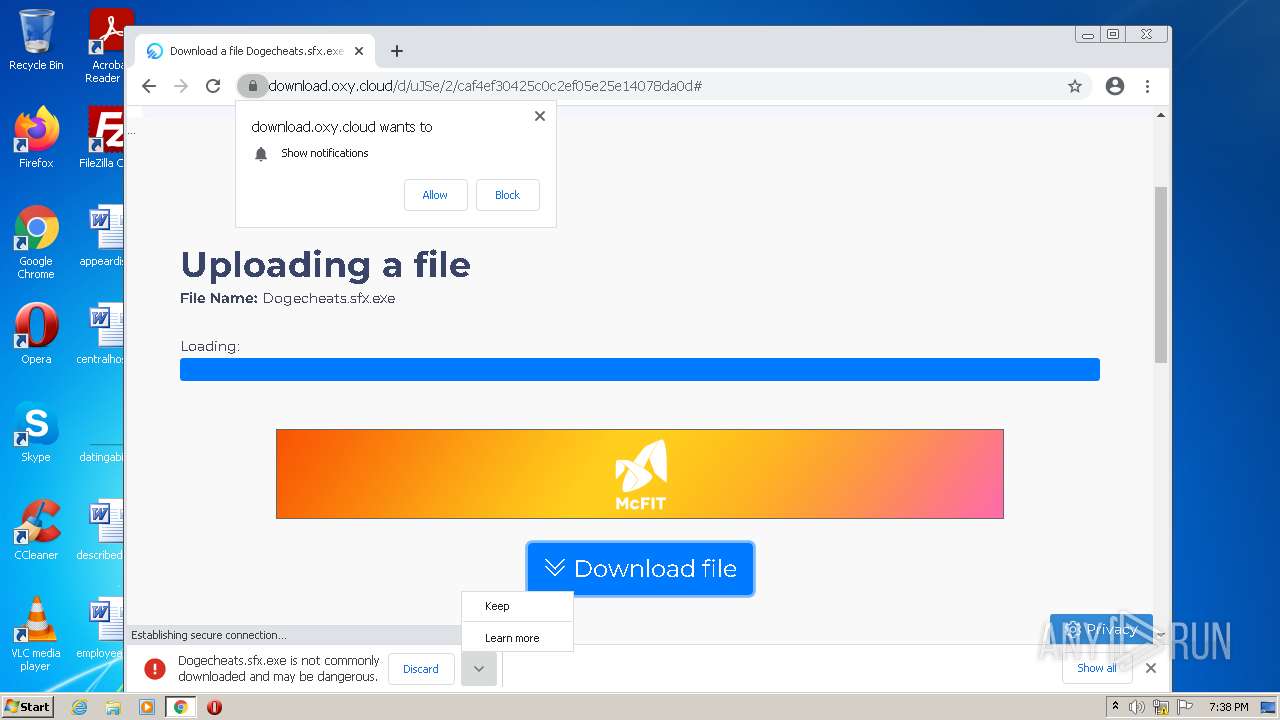
3412 | chrome.exe | 185.178.208.179:443 | oxy.cloud | Ddos-guard Ltd | RU | suspicious |
3412 | chrome.exe | 67.27.157.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3412 | chrome.exe | 104.107.160.24:443 | contextual.media.net | GTT Communications Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
oxy.cloud |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |