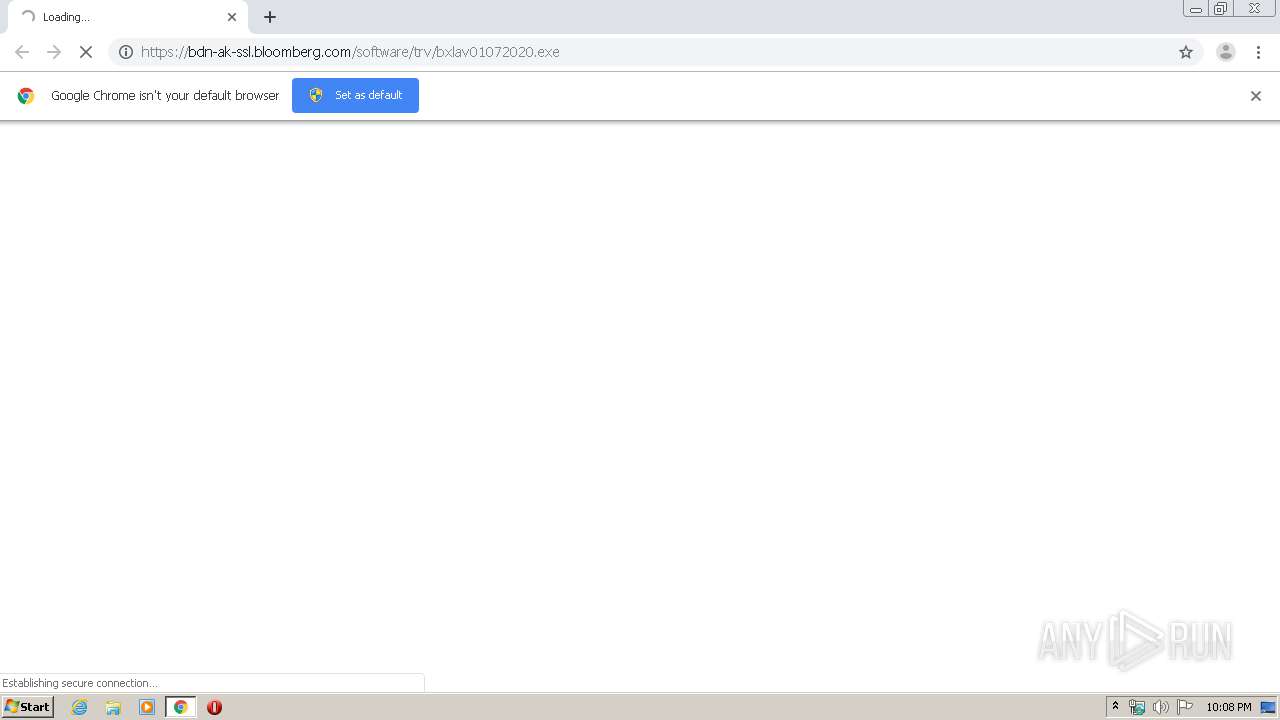
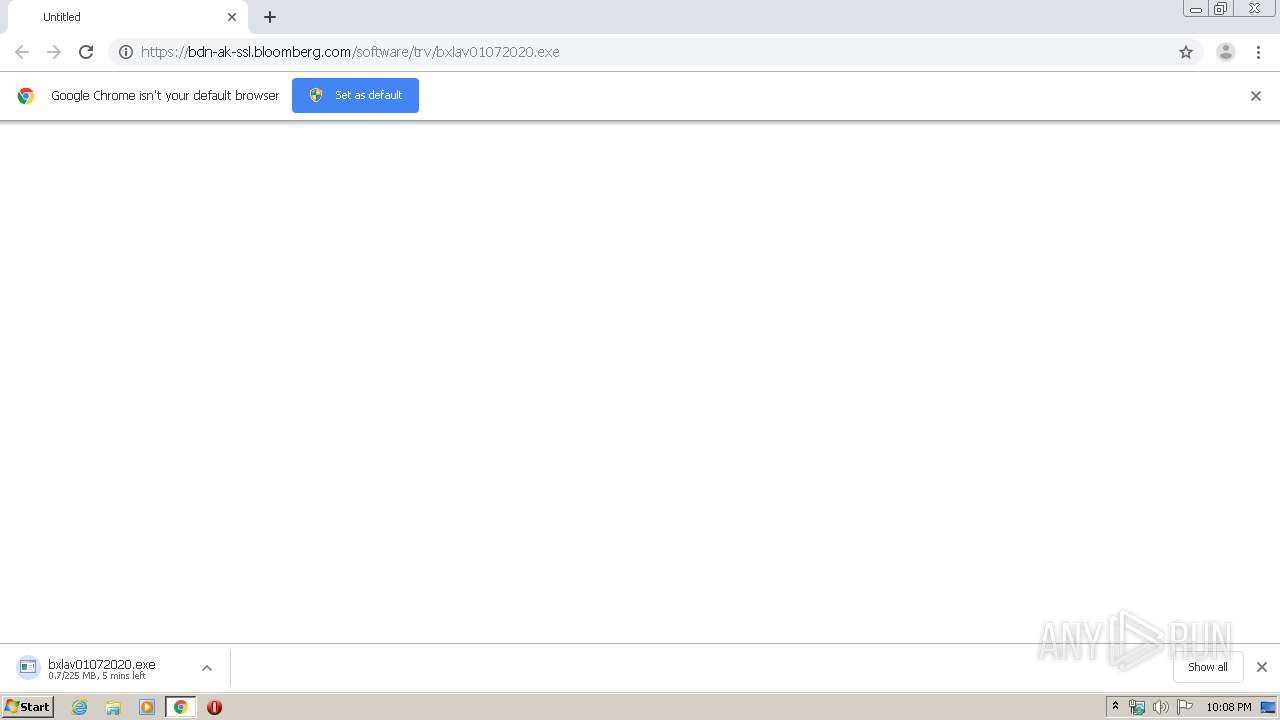
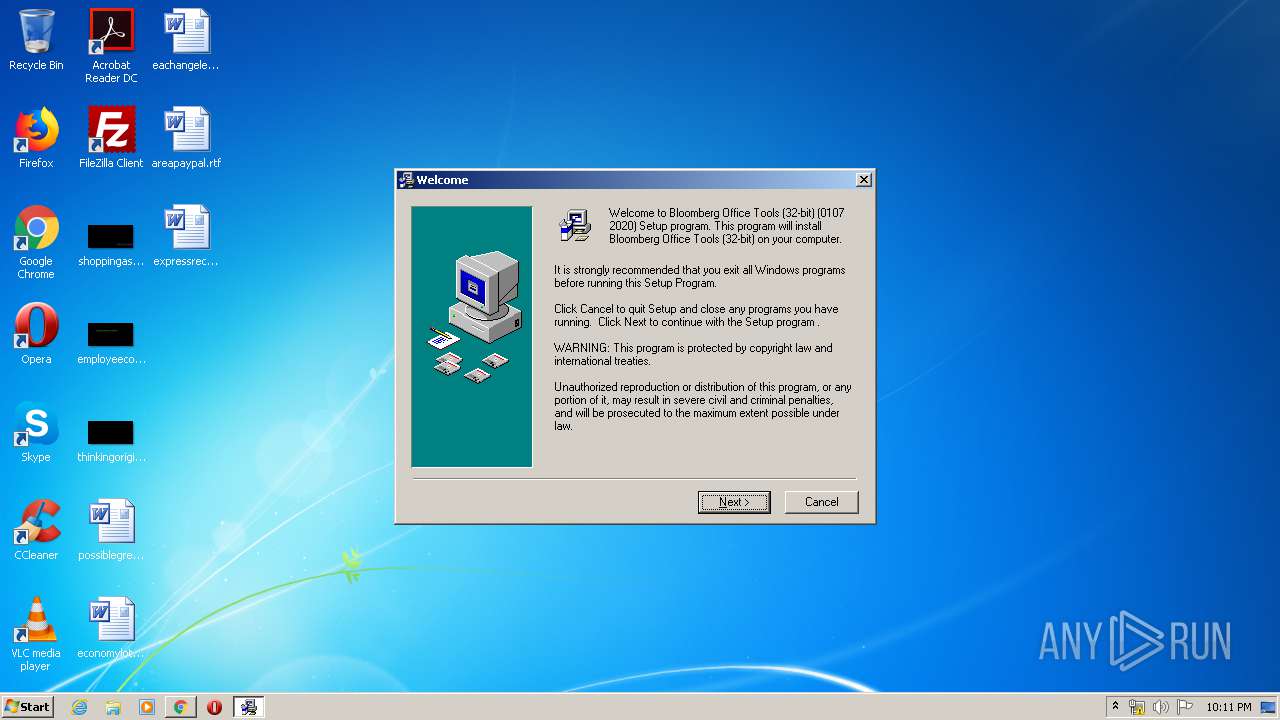
| URL: | https://bdn-ak-ssl.bloomberg.com/software/trv/bxlav01072020.exe |
| Full analysis: | https://app.any.run/tasks/66f87919-c88c-44b9-85cd-dab0a043abb2 |
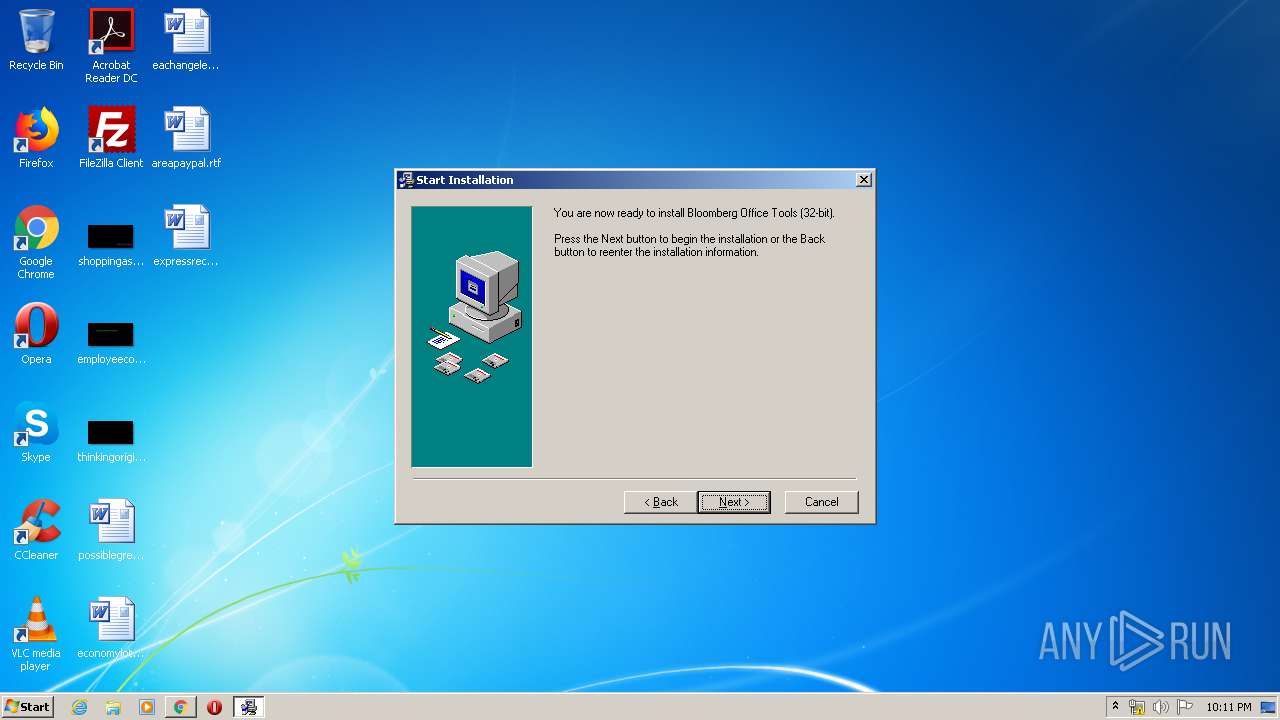
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2020, 22:08:27 |
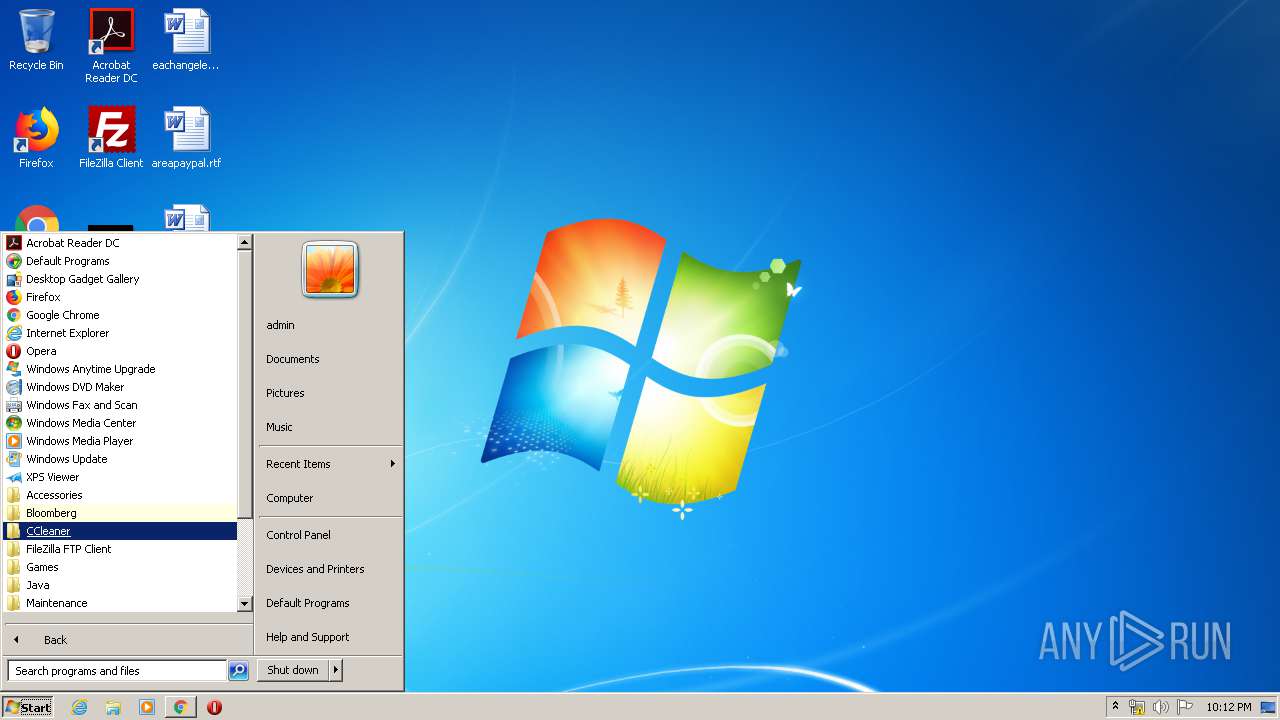
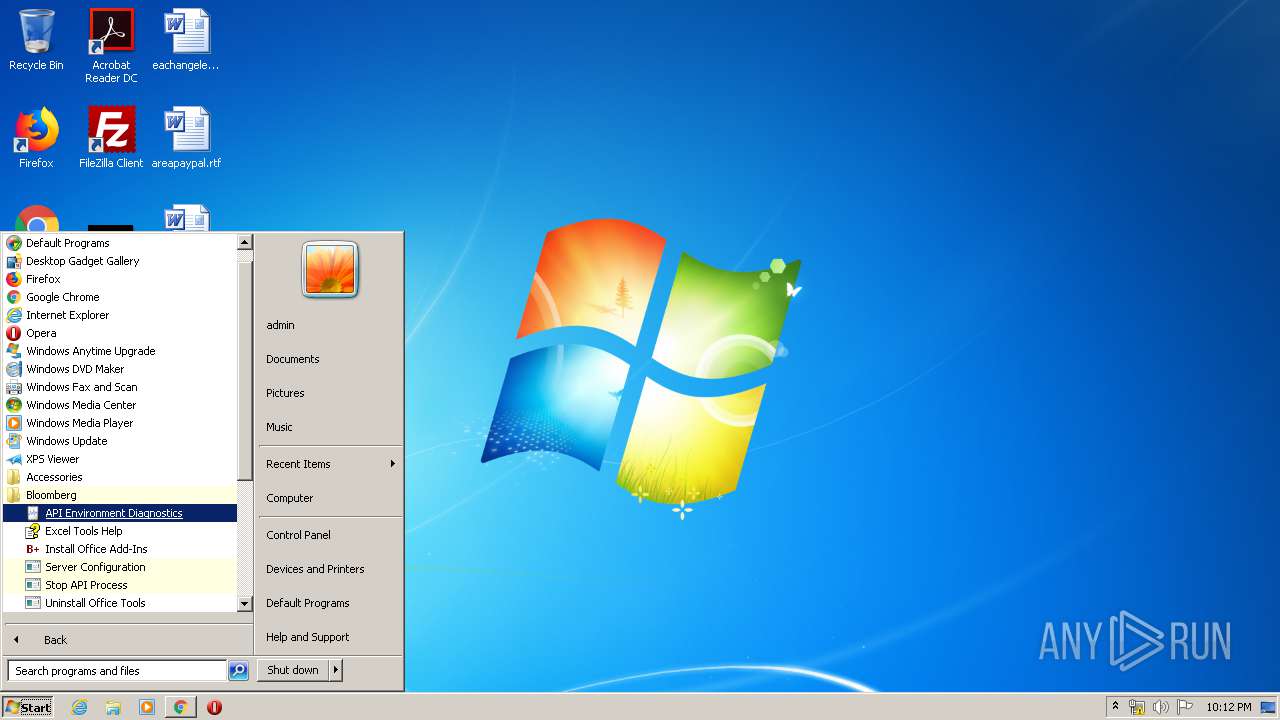
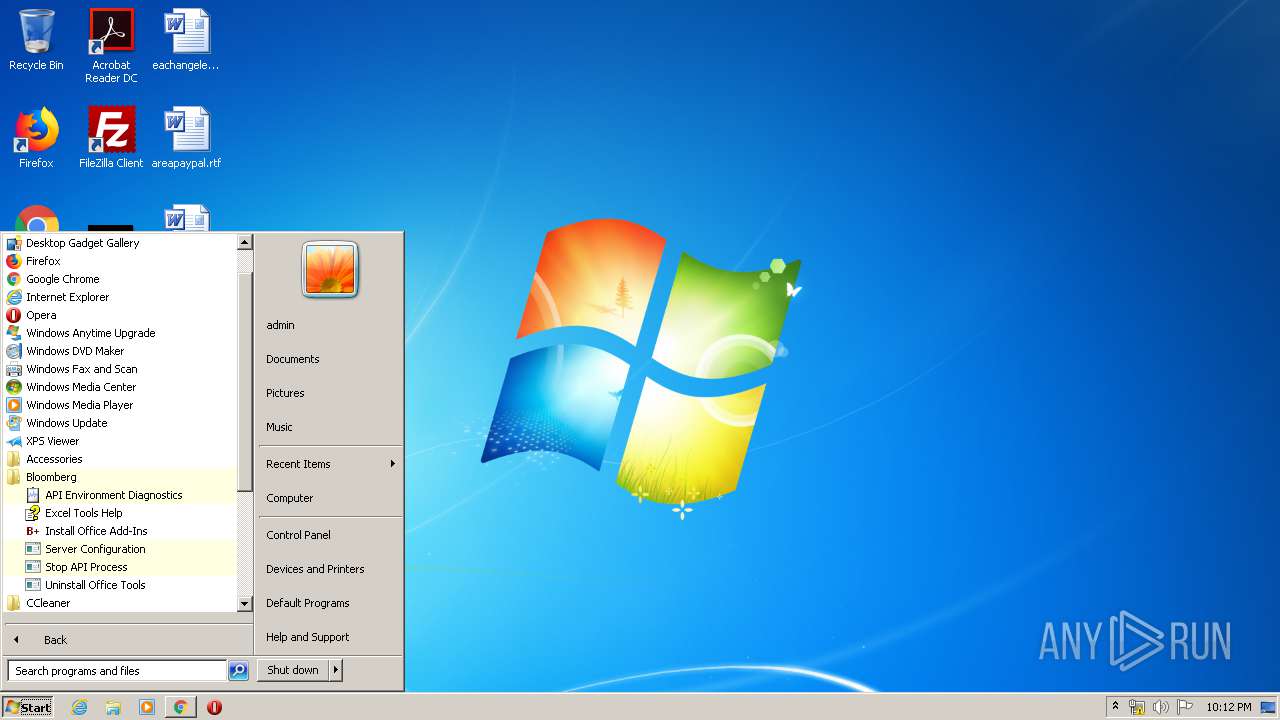
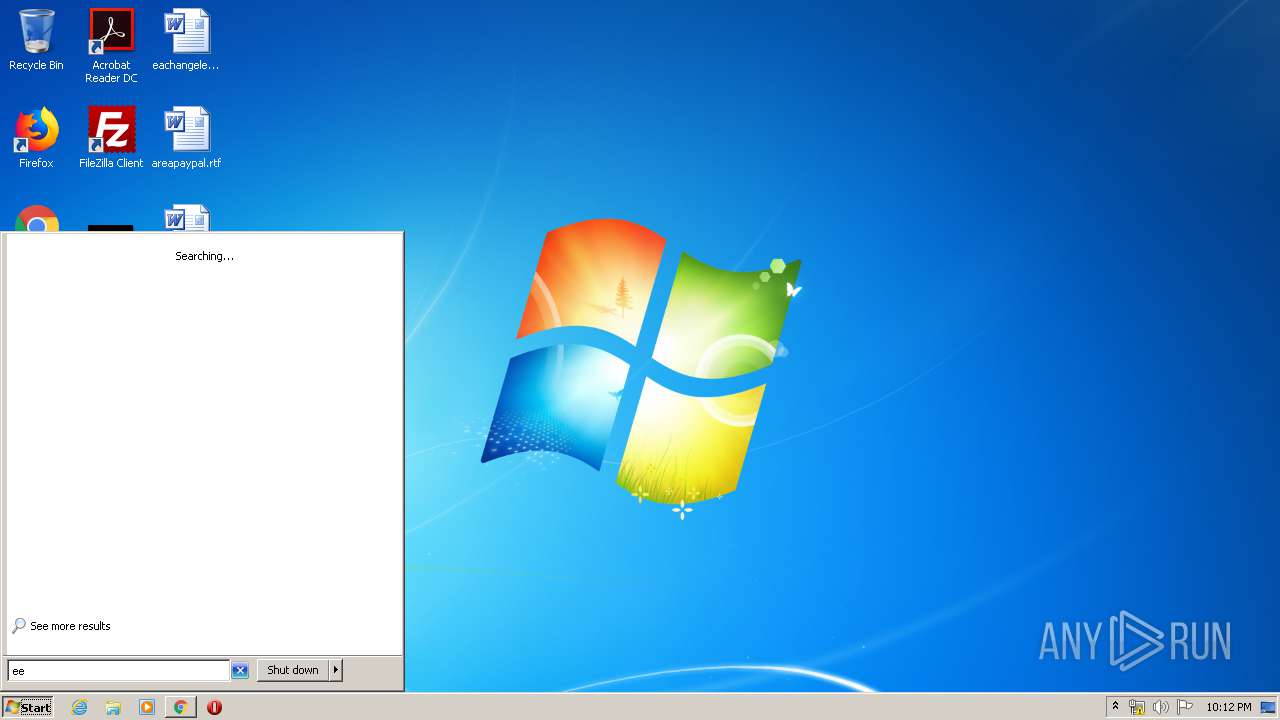
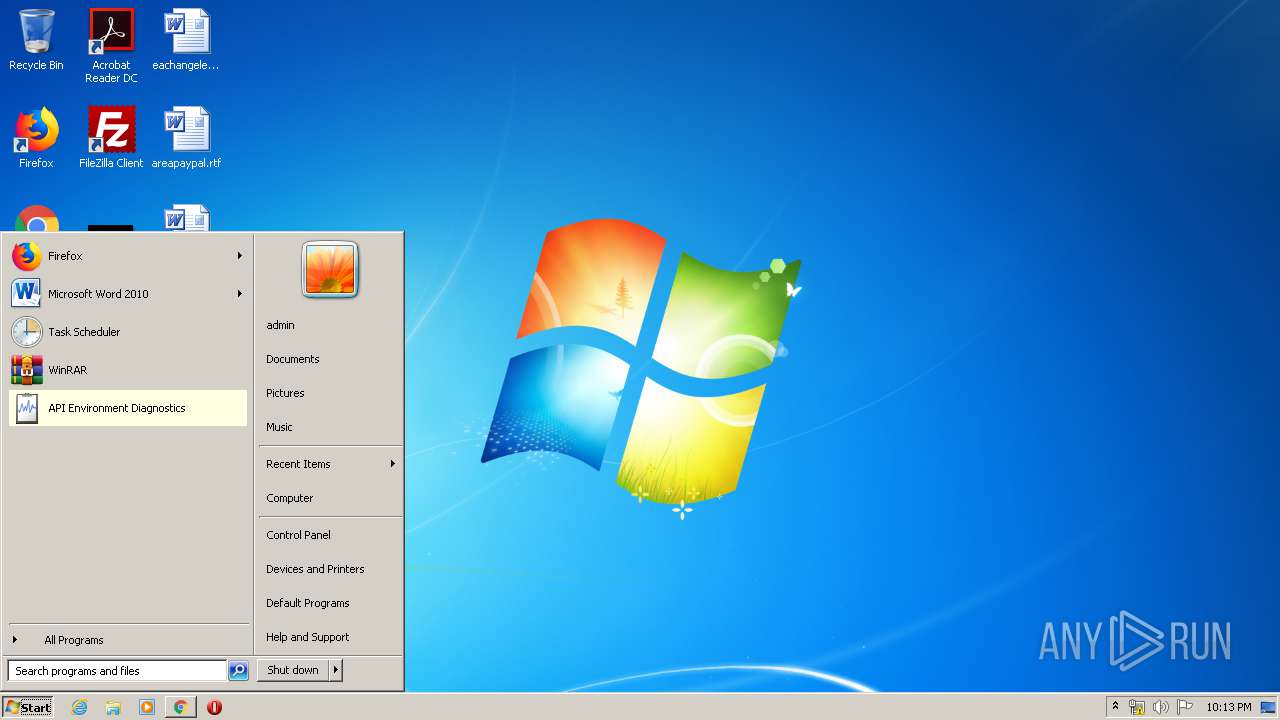
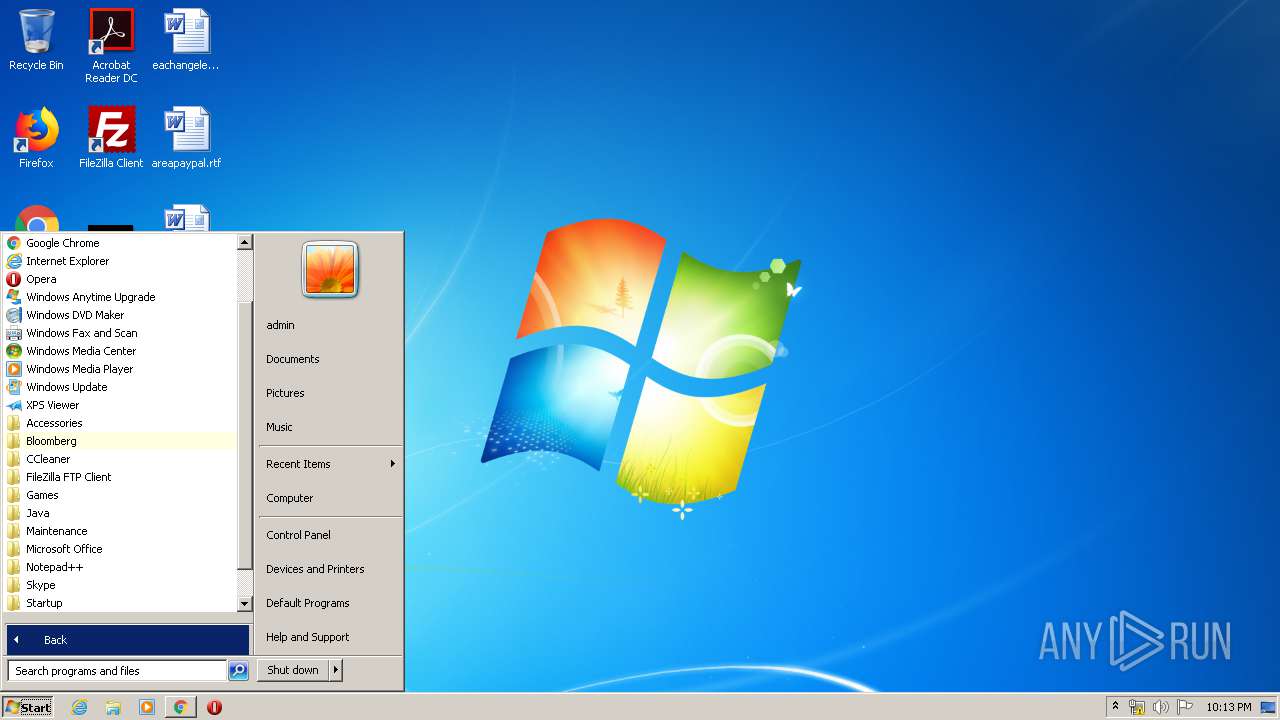
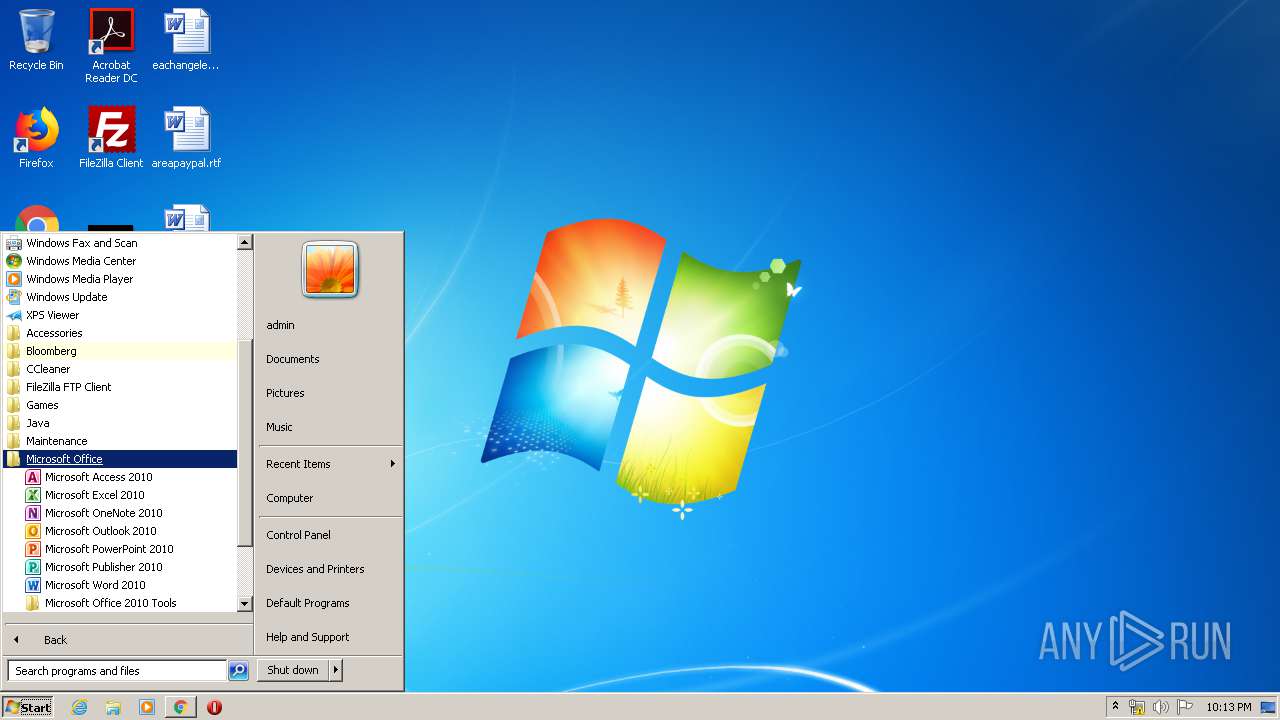
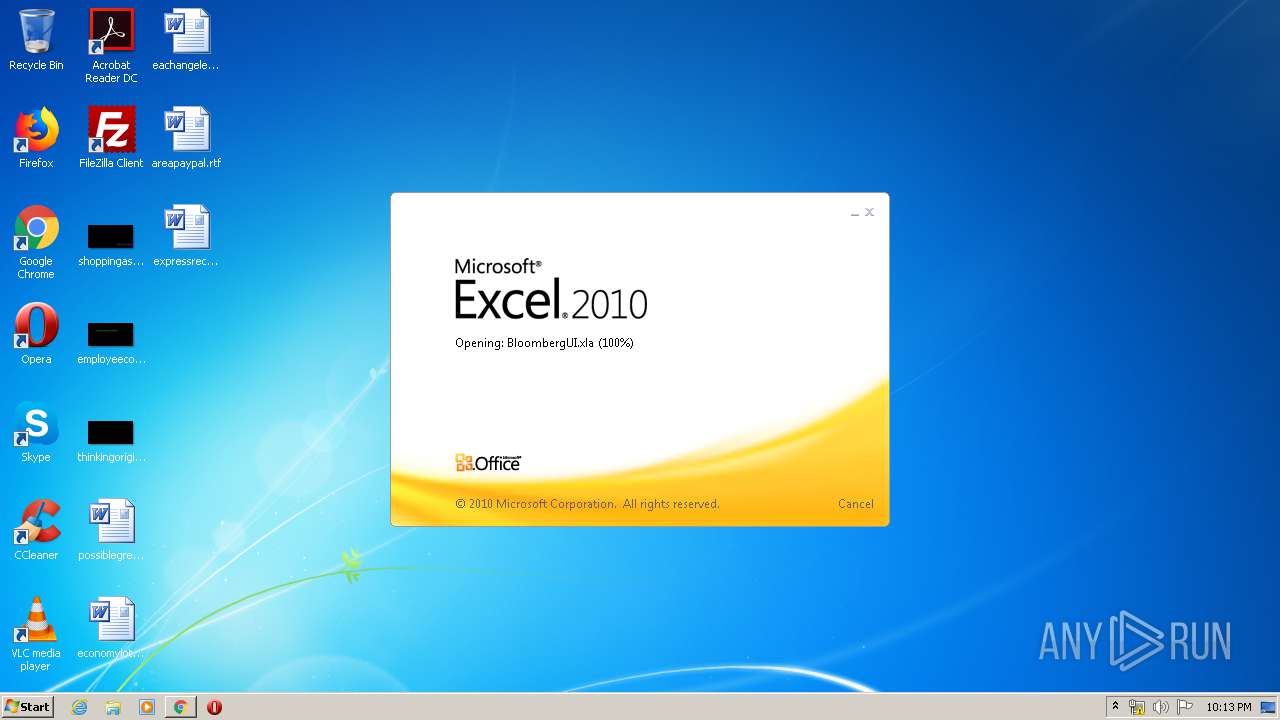
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 55324DC953AC3A5B4FF565BF8515EEC0 |
| SHA1: | 0B5174E0200CB203731D4F223F645B3AD2EA1AE6 |
| SHA256: | 800661AEEFADF6860603A4852A5617F0176529FF524242992837CB7B62005A2A |
| SSDEEP: | 3:N8tnvz/6WKMoTX5:2tnvBs |
MALICIOUS
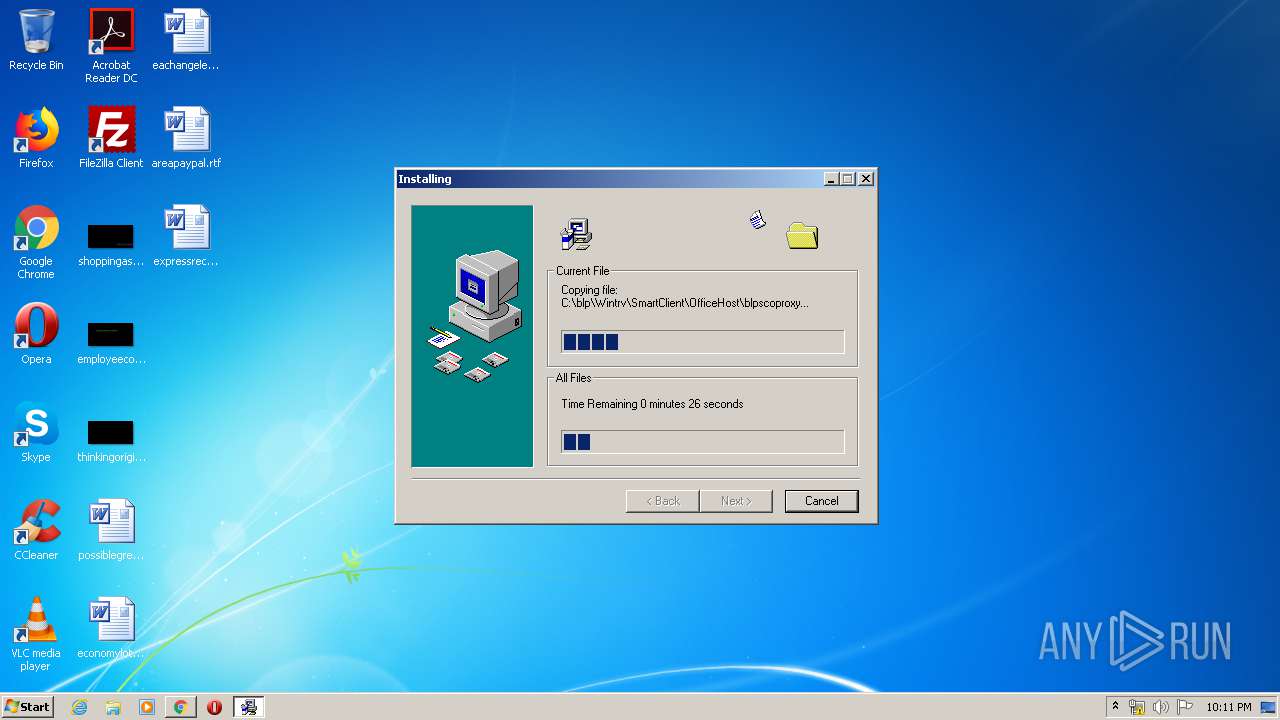
Application was dropped or rewritten from another process
- bxlav01072020.exe (PID: 252)
- bxlav01072020.exe (PID: 3176)
- GLB951A.tmp (PID: 916)
- instadd.exe (PID: 4848)
- instadd.exe (PID: 4520)
- instadd.exe (PID: 2876)
- BBAddIn.exe (PID: 4268)
- bxladiag.exe (PID: 3812)
- instadd.exe (PID: 5404)
- instadd.exe (PID: 3764)
- instadd.exe (PID: 1676)
- instadd.exe (PID: 6024)
- instadd.exe (PID: 4884)
- instadd.exe (PID: 4908)
- scanver.exe (PID: 4284)
- scanver.exe (PID: 5204)
- scanver.exe (PID: 6112)
- scanver.exe (PID: 3180)
- scanver.exe (PID: 6020)
- scanver.exe (PID: 3796)
- scanver.exe (PID: 5580)
- scanver.exe (PID: 4856)
- bbund.exe (PID: 3716)
- bbund.exe (PID: 740)
- scanver.exe (PID: 5756)
- bbund.exe (PID: 3332)
- blpwebview.exe (PID: 5584)
- blpwebview.exe (PID: 4632)
- blpwebview.exe (PID: 4680)
- blpwebview.exe (PID: 5976)
- blpwebview.exe (PID: 6100)
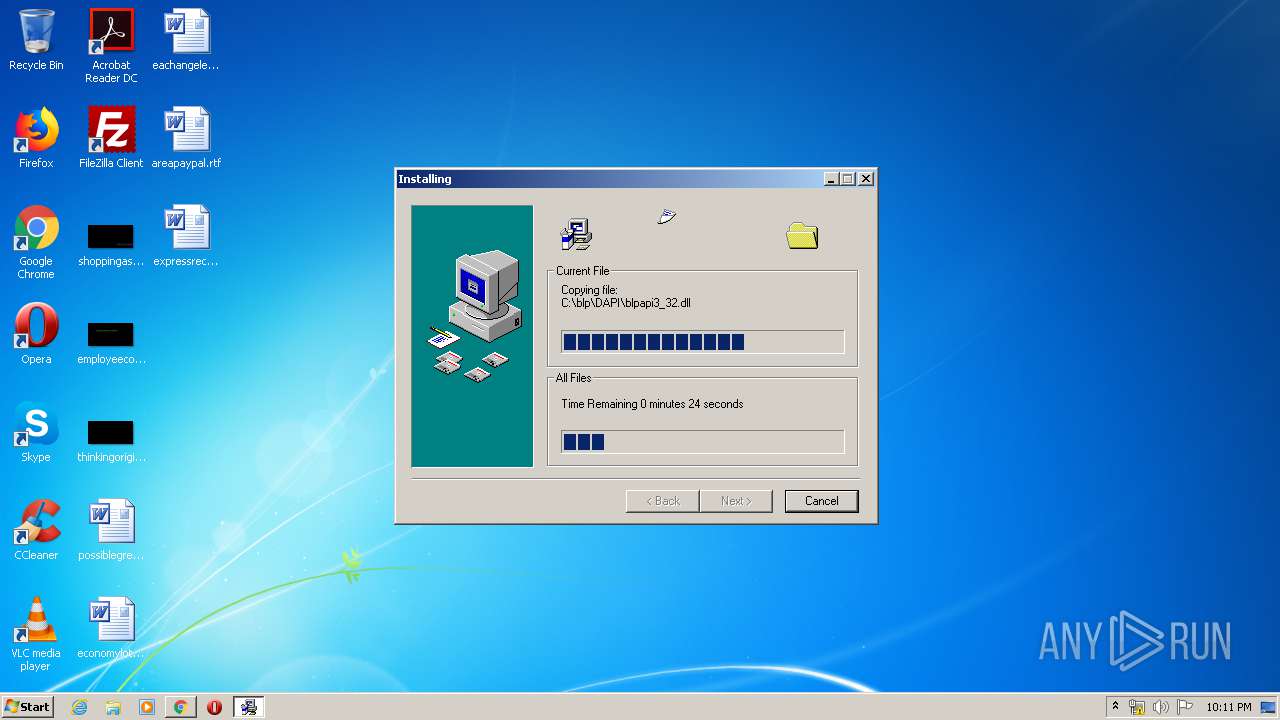
Registers / Runs the DLL via REGSVR32.EXE
- GLB951A.tmp (PID: 916)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3848)
- GLB951A.tmp (PID: 916)
- regsvr32.exe (PID: 744)
- regsvr32.exe (PID: 3584)
- regsvr32.exe (PID: 3020)
- regsvr32.exe (PID: 572)
- regsvr32.exe (PID: 3916)
- scanver.exe (PID: 5204)
- scanver.exe (PID: 4284)
- scanver.exe (PID: 4856)
- scanver.exe (PID: 6112)
- scanver.exe (PID: 3180)
- regsvr32.exe (PID: 1140)
- regsvr32.exe (PID: 3808)
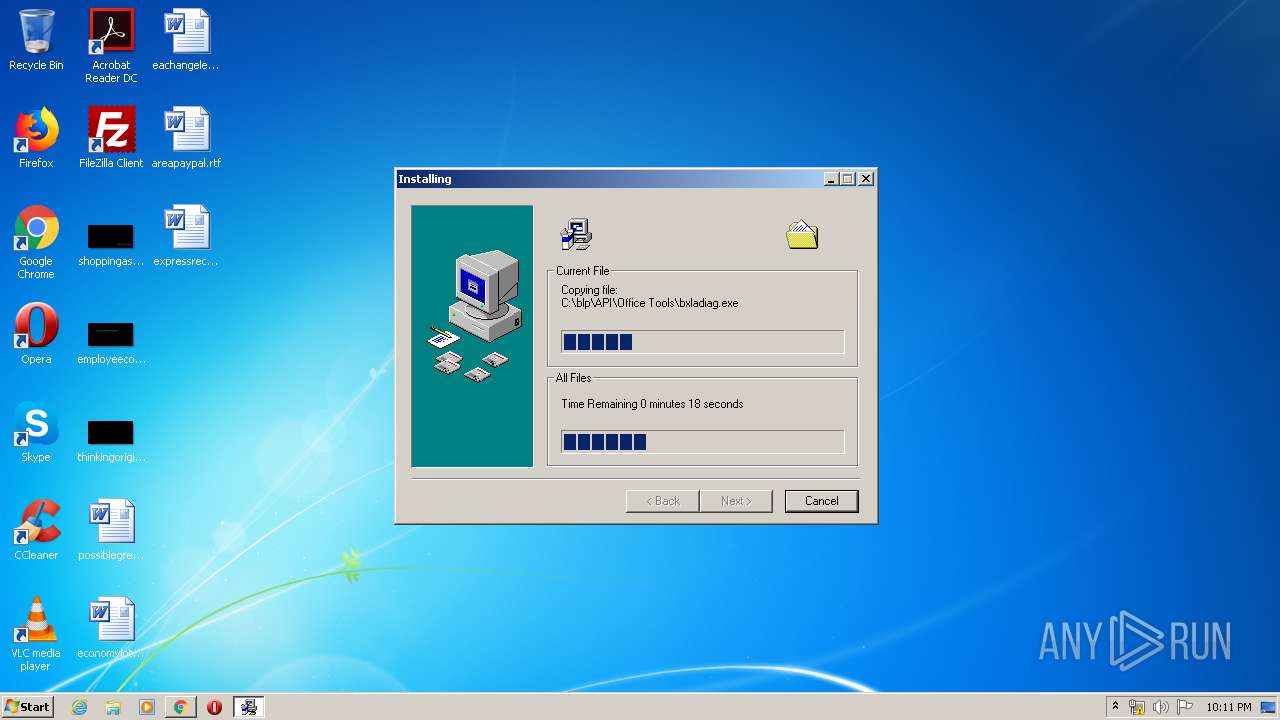
- bxladiag.exe (PID: 3812)
- scanver.exe (PID: 3796)
- scanver.exe (PID: 5756)
- scanver.exe (PID: 6020)
- blpwebview.exe (PID: 6100)
- blpwebview.exe (PID: 4632)
- blpwebview.exe (PID: 4680)
- EXCEL.EXE (PID: 1548)
- blpwebview.exe (PID: 5976)
- blpwebview.exe (PID: 5584)
Writes file to Word startup folder
- instadd.exe (PID: 4908)
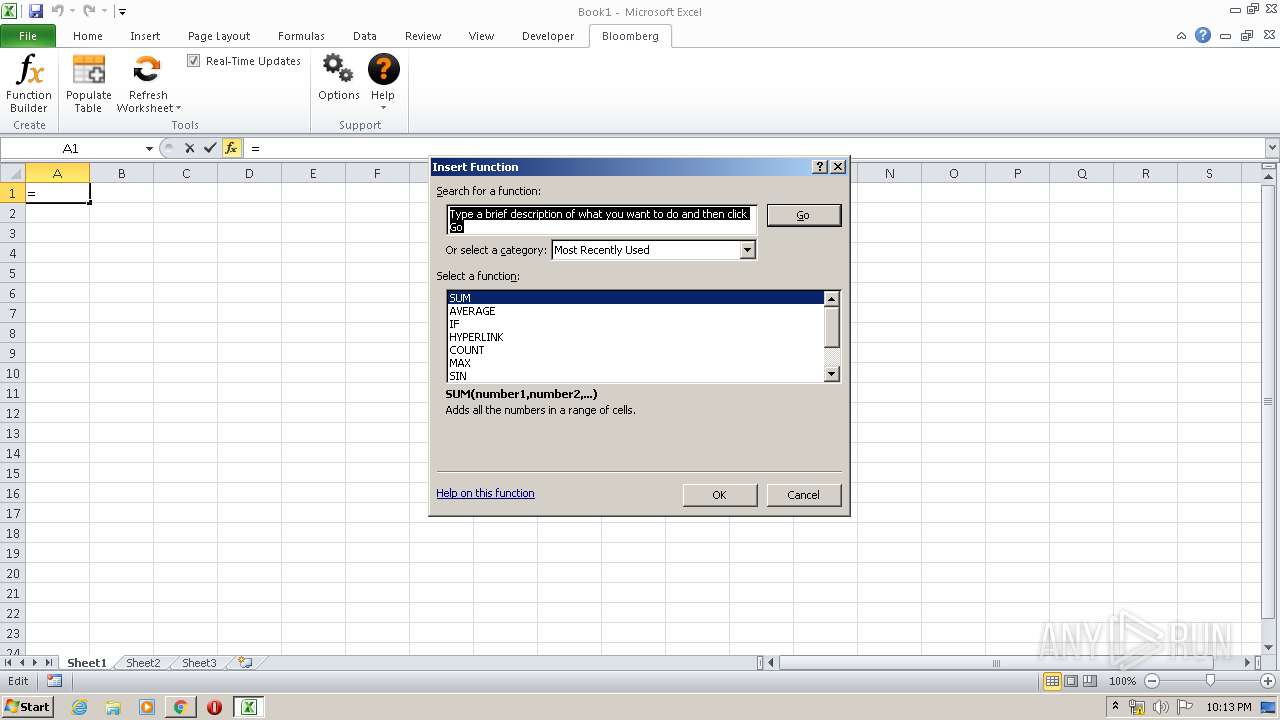
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1548)
SUSPICIOUS
Removes files from Windows directory
- GLB951A.tmp (PID: 916)
Creates COM task schedule object
- regsvr32.exe (PID: 3584)
- regsvr32.exe (PID: 744)
- regsvr32.exe (PID: 3020)
- regsvr32.exe (PID: 3808)
- regsvr32.exe (PID: 572)
- regsvr32.exe (PID: 3848)
- regsvr32.exe (PID: 1140)
Executable content was dropped or overwritten
- bxlav01072020.exe (PID: 252)
- chrome.exe (PID: 3172)
- expand.exe (PID: 2892)
- expand.exe (PID: 3240)
- expand.exe (PID: 2360)
- expand.exe (PID: 2540)
- expand.exe (PID: 3228)
- expand.exe (PID: 3372)
- expand.exe (PID: 1564)
- expand.exe (PID: 1632)
- expand.exe (PID: 3428)
- expand.exe (PID: 3568)
- expand.exe (PID: 3044)
- expand.exe (PID: 5152)
- expand.exe (PID: 5800)
- expand.exe (PID: 6140)
- expand.exe (PID: 5260)
- expand.exe (PID: 5828)
- expand.exe (PID: 5128)
- expand.exe (PID: 5028)
- BLPWEB~1.EXE (PID: 3924)
- expand.exe (PID: 4272)
- GLB951A.tmp (PID: 916)
- expand.exe (PID: 5656)
- expand.exe (PID: 2856)
- expand.exe (PID: 4100)
Creates files in the Windows directory
- GLB951A.tmp (PID: 916)
- expand.exe (PID: 3784)
Creates a software uninstall entry
- GLB951A.tmp (PID: 916)
Starts application with an unusual extension
- bxlav01072020.exe (PID: 252)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3172)
Creates files in the program directory
- GLB951A.tmp (PID: 916)
Starts CMD.EXE for commands execution
- GLB951A.tmp (PID: 916)
- bxladiag.exe (PID: 3812)
Creates files in the user directory
- instadd.exe (PID: 4908)
Application launched itself
- blpwebview.exe (PID: 4680)
Reads internet explorer settings
- hh.exe (PID: 5640)
INFO
Reads the hosts file
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3172)
- blpwebview.exe (PID: 4680)
- blpwebview.exe (PID: 5976)
Dropped object may contain Bitcoin addresses
- GLB951A.tmp (PID: 916)
- expand.exe (PID: 1468)
- expand.exe (PID: 1712)
- expand.exe (PID: 1784)
- BLPWEB~1.EXE (PID: 3924)
Reads Internet Cache Settings
- chrome.exe (PID: 3172)
Application launched itself
- chrome.exe (PID: 3172)
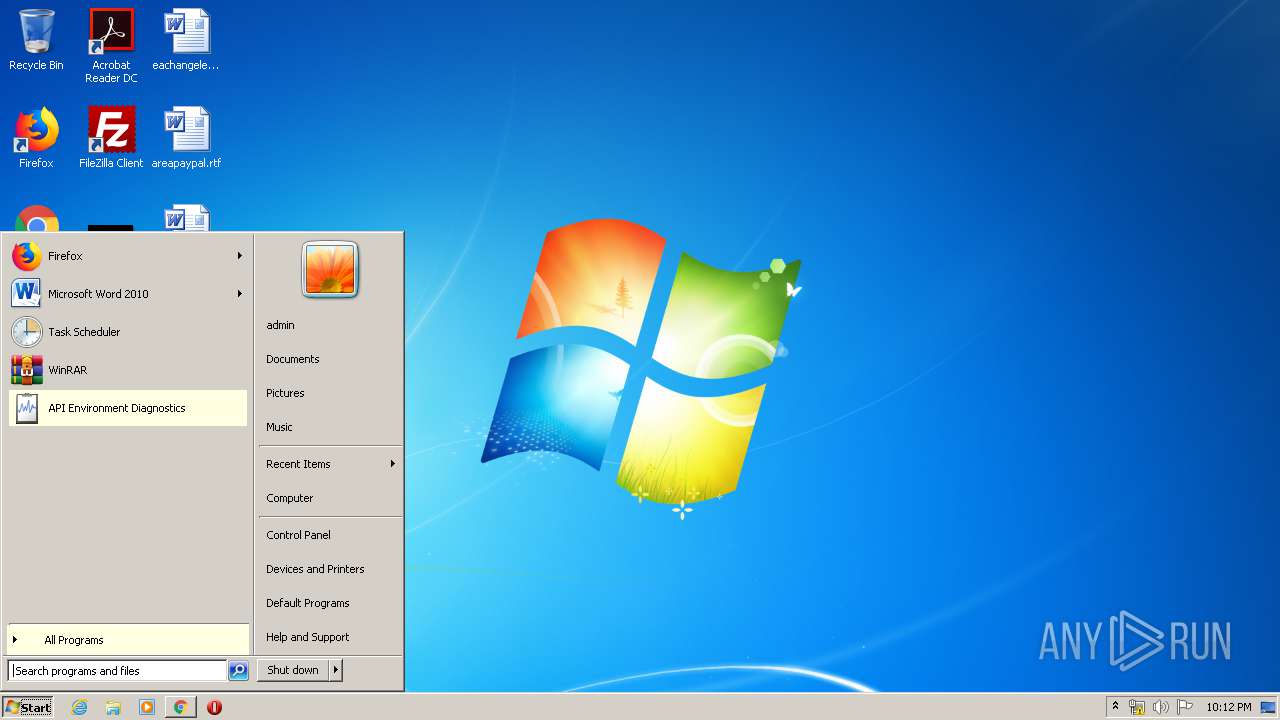
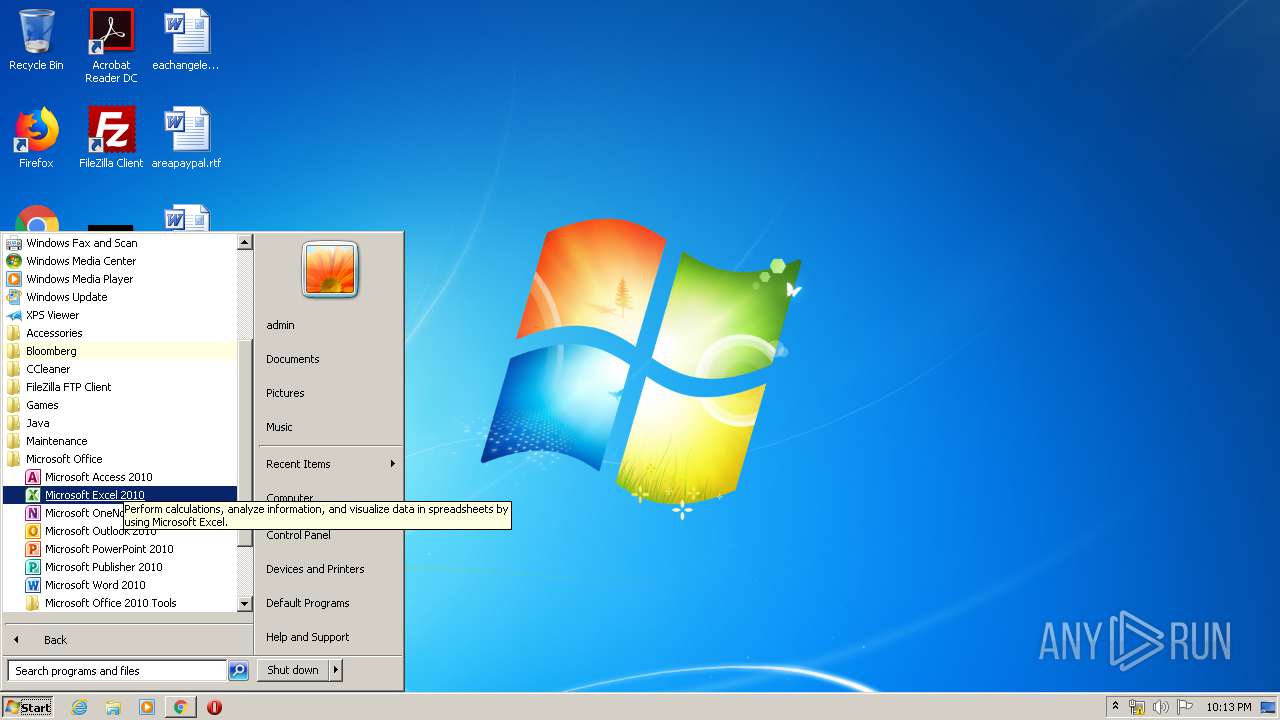
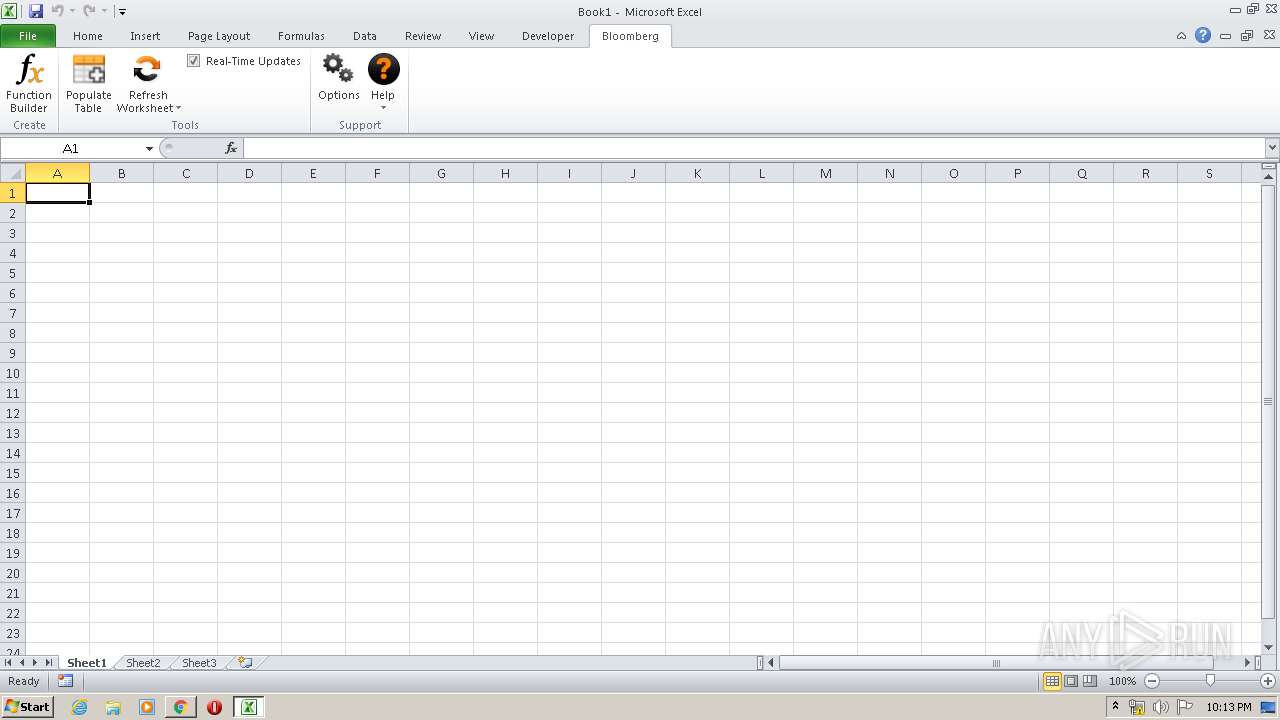
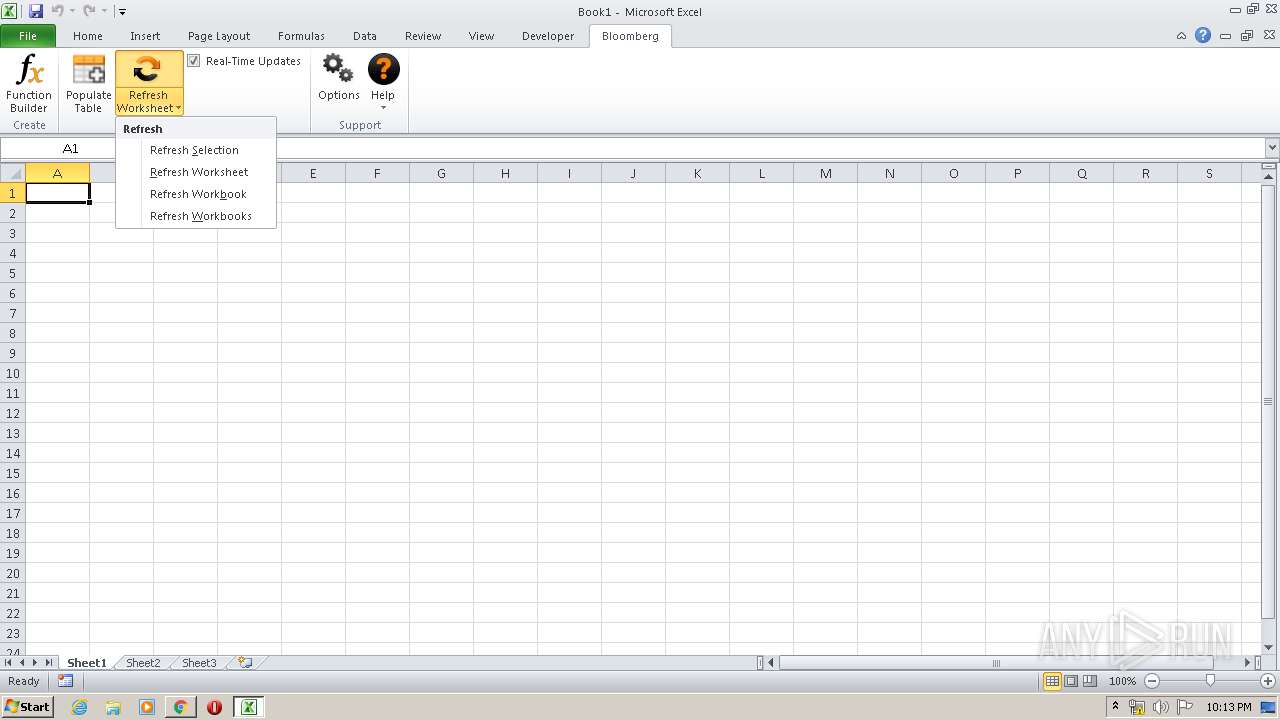
Manual execution by user
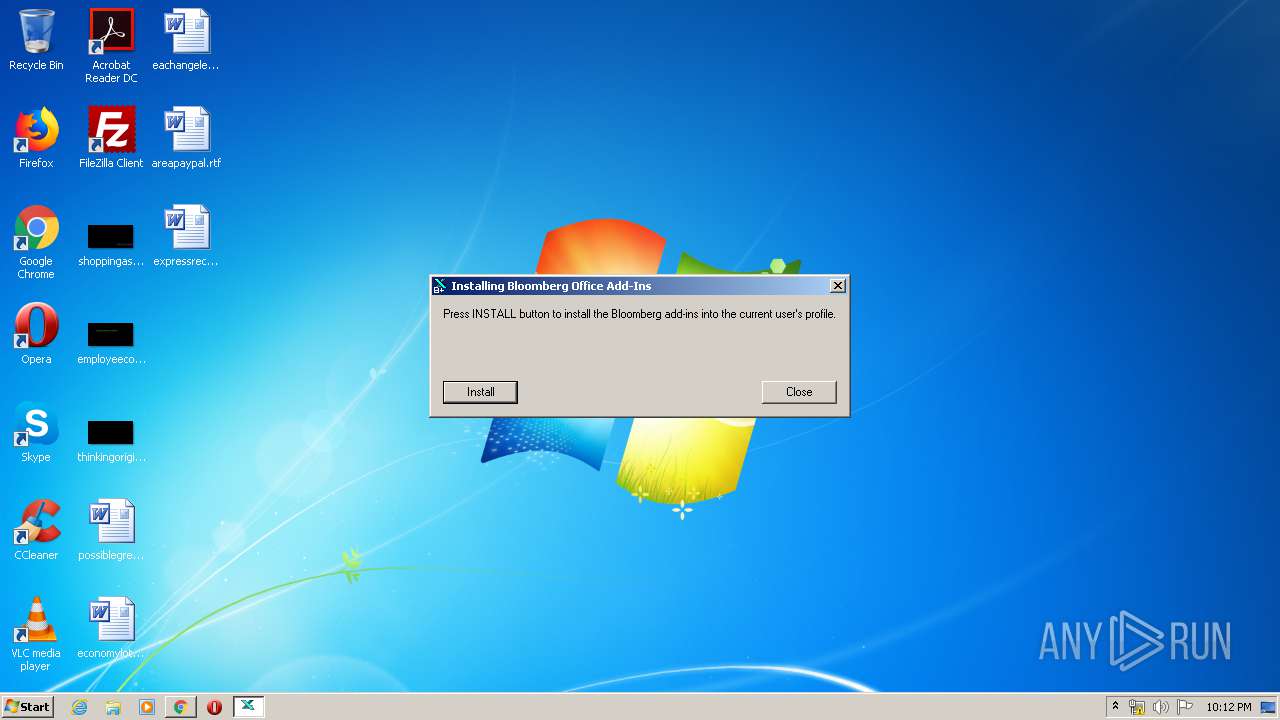
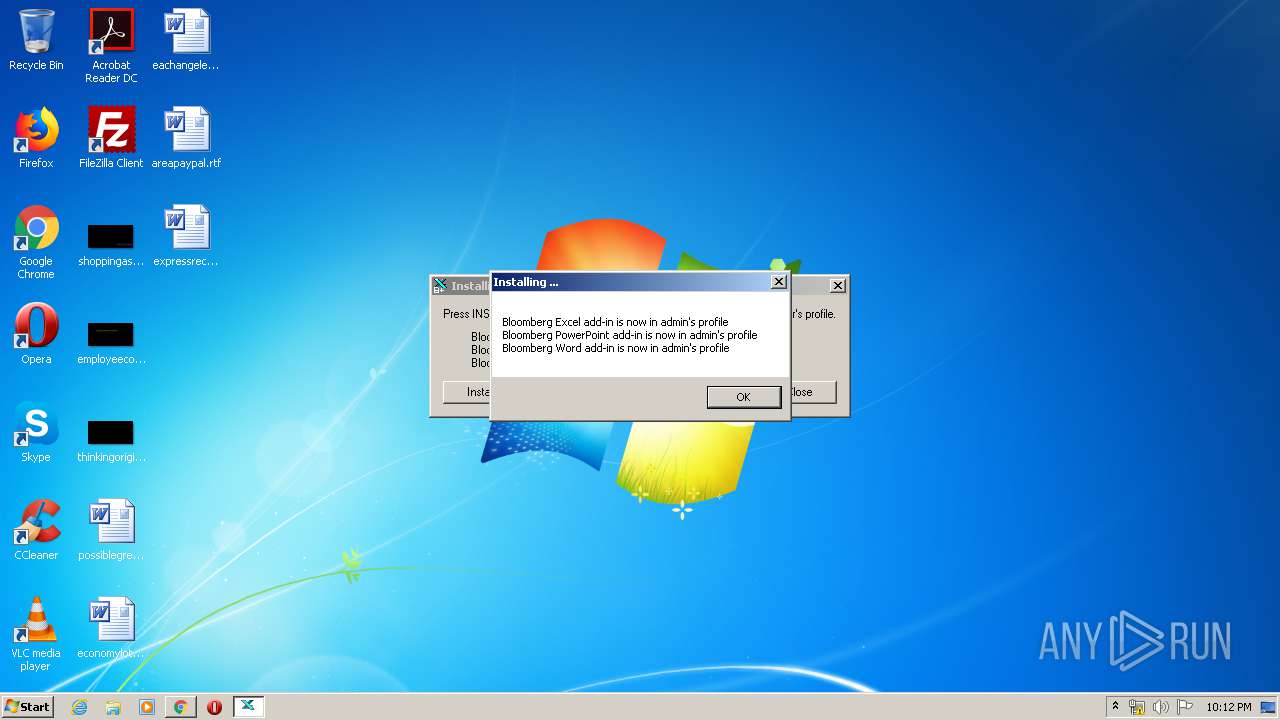
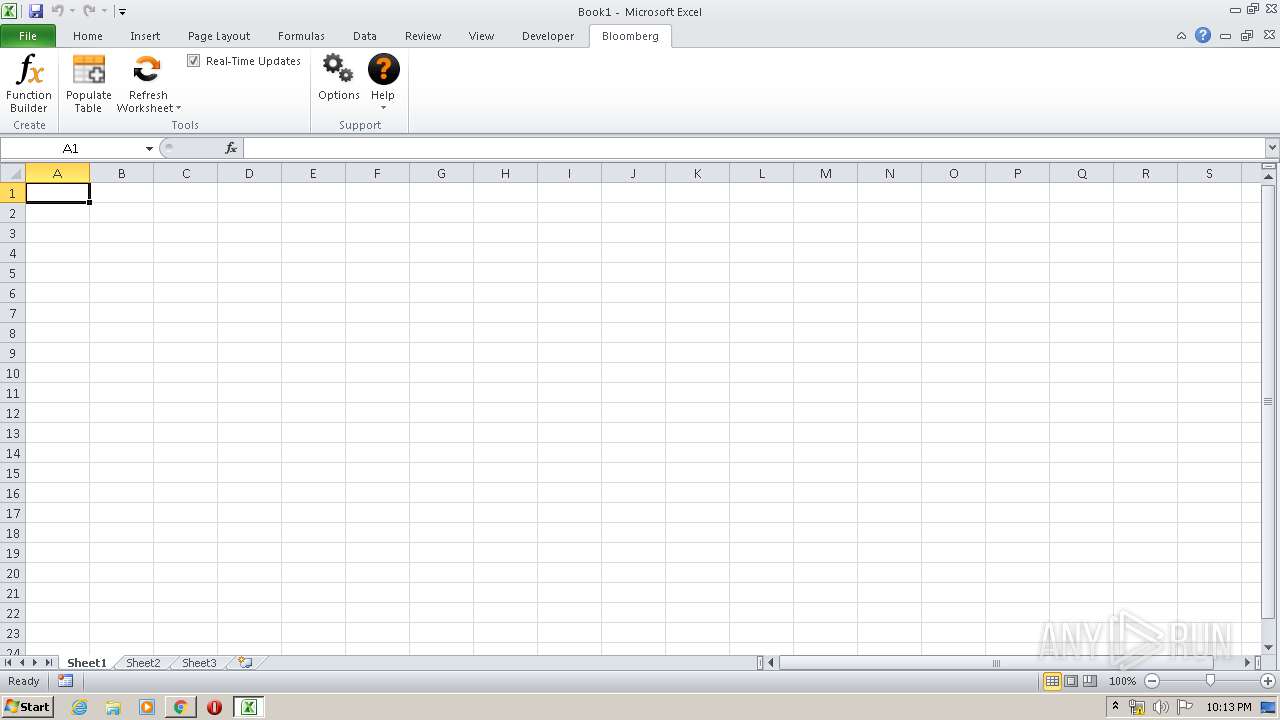
- BBAddIn.exe (PID: 4268)
- EXCEL.EXE (PID: 1548)
Reads settings of System Certificates
- chrome.exe (PID: 3880)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1548)
Creates files in the user directory
- EXCEL.EXE (PID: 1548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
437
Monitored processes
221
Malicious processes
20
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\bad055a89e2e8ac38b98aafd96d333fad6052b56.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\bad055a89e2e8ac38b98aafd96d333fad6052b56.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 252 | "C:\Users\admin\Downloads\bxlav01072020.exe" | C:\Users\admin\Downloads\bxlav01072020.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 272 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\3444662ef0d338144ce6b51e9e1ec010128dd9bd.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\3444662ef0d338144ce6b51e9e1ec010128dd9bd.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\a049698662ab5c3244cf22bcd048d831621462bd.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\a049698662ab5c3244cf22bcd048d831621462bd.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\7dd2470ba5cf70c471daeebe3426cd3a6bea53a9.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\7dd2470ba5cf70c471daeebe3426cd3a6bea53a9.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\1dd3cfc51c4688c1df2ab34778c9142841bb81d1.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\1dd3cfc51c4688c1df2ab34778c9142841bb81d1.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\7dab768d7753ba2b9c5f66b2f2283e8626c525f5.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\7dab768d7753ba2b9c5f66b2f2283e8626c525f5.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 564 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\4ff6925537bf341bd8385a6b7e3dd5808890b3e7.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\4ff6925537bf341bd8385a6b7e3dd5808890b3e7.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | "C:\Windows\System32\regsvr32.exe" /s /i /n bofaddin.dll | C:\Windows\System32\regsvr32.exe | GLB951A.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | expand.exe "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\ae65776a013728d5cb929a0df8e3ddf5eaebeda6.b_" "C:\blp\API\Office Tools\xofgeoldfdmekeholjboiieohnfcnobmb\ae65776a013728d5cb929a0df8e3ddf5eaebeda6.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 817
Read events
1 992
Write events
718
Delete events
107
Modification events
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3172-13228783721416625 |
Value: 259 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3172-13228783721416625 |
Value: 259 | |||
Executable files
259
Suspicious files
84
Text files
515
Unknown types
278
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E6EA769-C64.pma | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4ec49a69-1357-411d-909a-c305e8d35adc.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e43.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
16
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3880 | chrome.exe | GET | 200 | 173.194.137.72:80 | http://r3---sn-aigzrn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.203.46.135&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1584310213&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3880 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3880 | chrome.exe | GET | 200 | 173.194.135.106:80 | http://r5---sn-aigzrn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=85.203.46.135&mm=28&mn=sn-aigzrn7z&ms=nvh&mt=1584310213&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3880 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3880 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 23.14.94.22:443 | bdn-ak-ssl.bloomberg.com | Akamai International B.V. | NL | whitelisted |
3880 | chrome.exe | 216.58.208.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 173.194.135.106:80 | r5---sn-aigzrn7z.gvt1.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 173.194.137.72:80 | r3---sn-aigzrn76.gvt1.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
bdn-ak-ssl.bloomberg.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GLB951A.tmp | Create subfolder:Office Tools SUCCESS |
GLB951A.tmp | Create subfolder:activex SUCCESS |
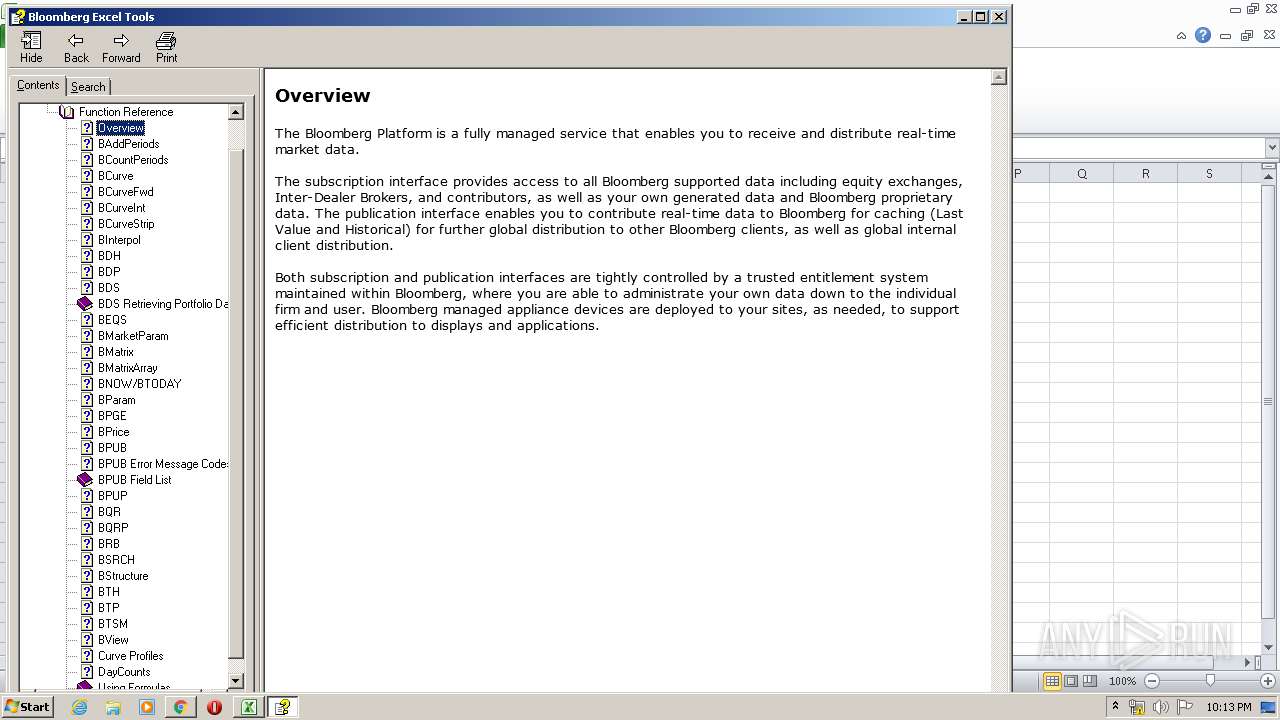
regsvr32.exe | bof::Addin::DLL_PROCESS_ATTACH complete. |
regsvr32.exe | bof::Addin::DLL_PROCESS_DETACH complete. |
EXCEL.EXE | bof::Addin::DLL_PROCESS_ATTACH complete. |
EXCEL.EXE | bof: OfficeService::CTOR exit |
EXCEL.EXE | bof: OfficeService::CTOR entry |
EXCEL.EXE | bof::UIHostServiceStateMachine::SafeStateTransition FROM: STOPPED TO: STARTING |
EXCEL.EXE | bof::UIComponentProxyContainer ctor at entry. |
EXCEL.EXE | bof::UIHostServiceAdapterContainer ctor entry |