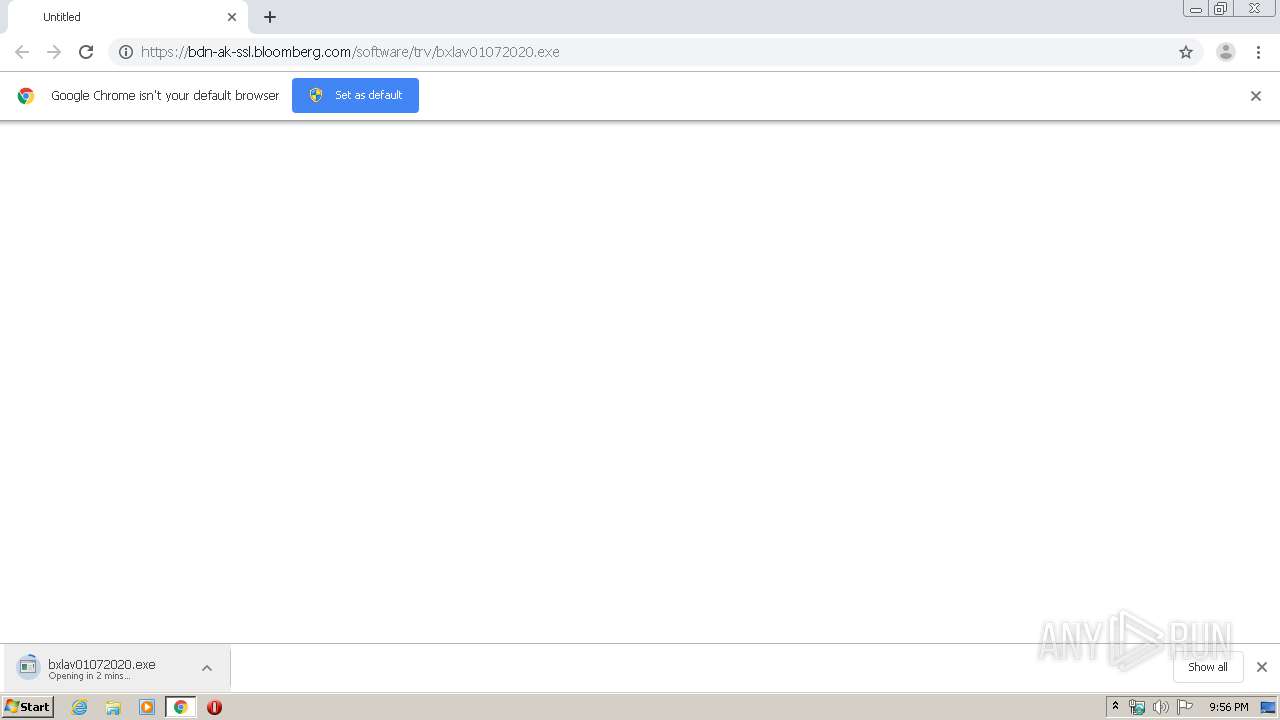
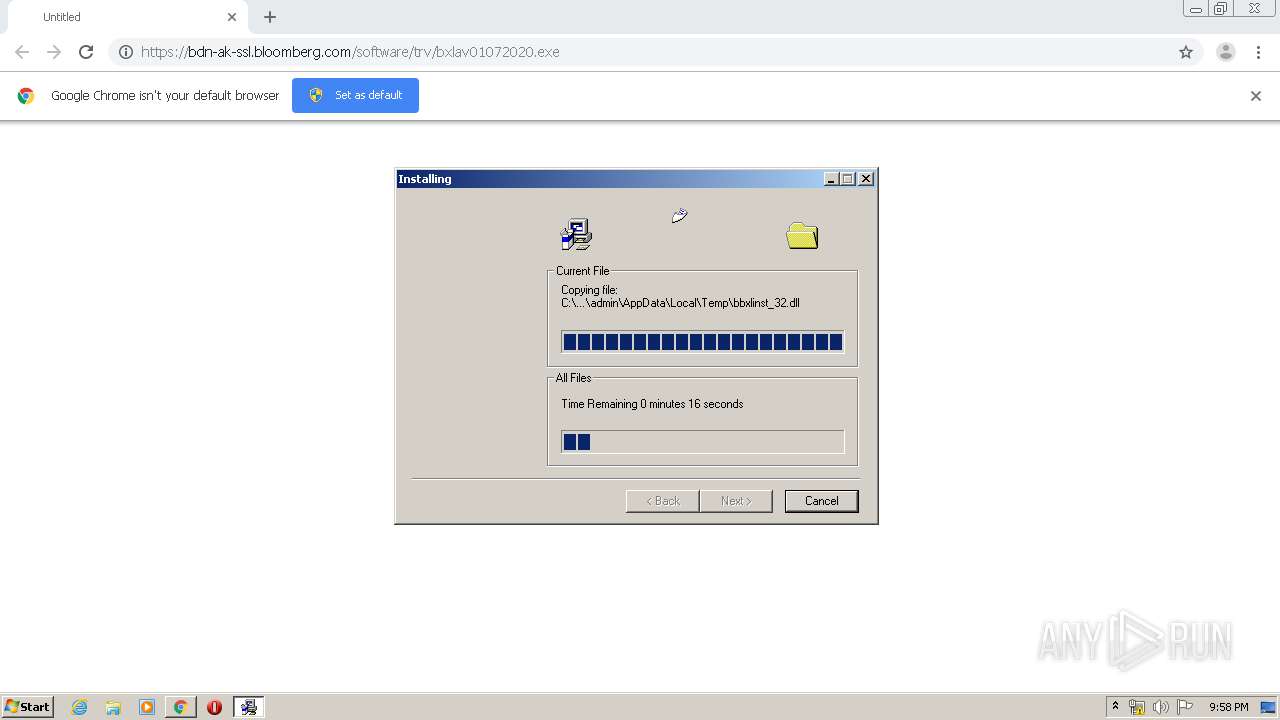
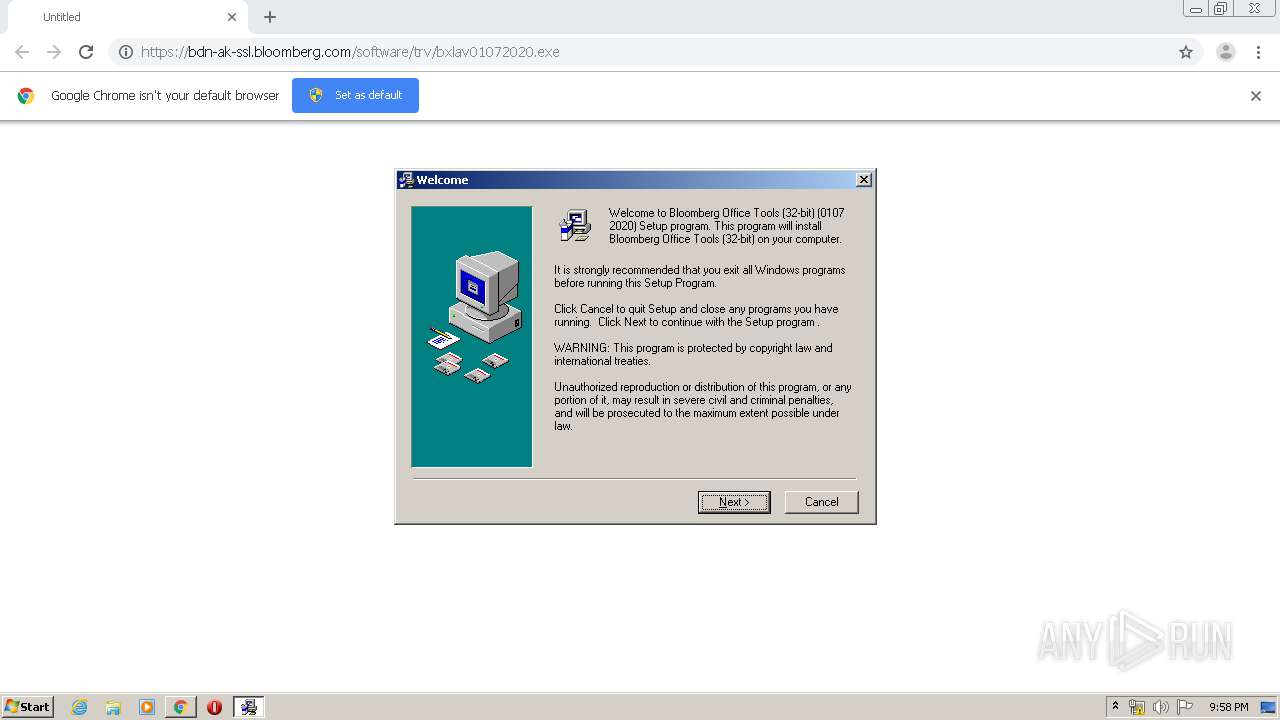
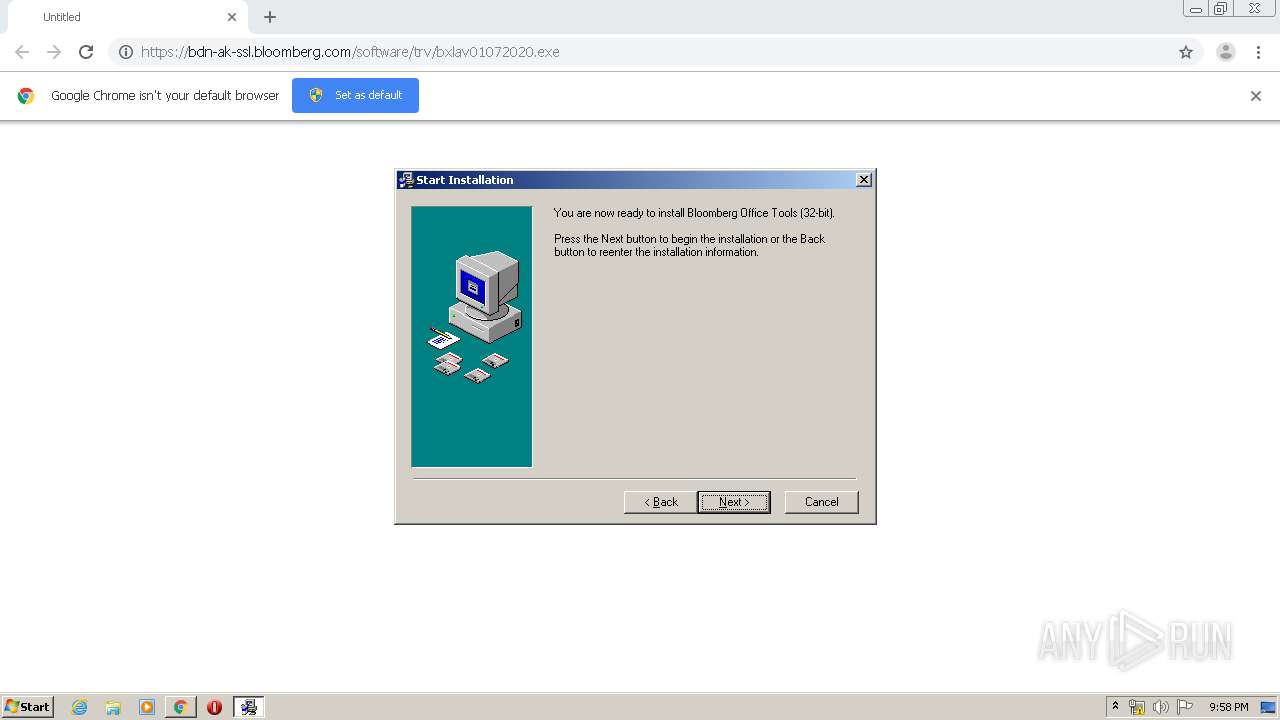
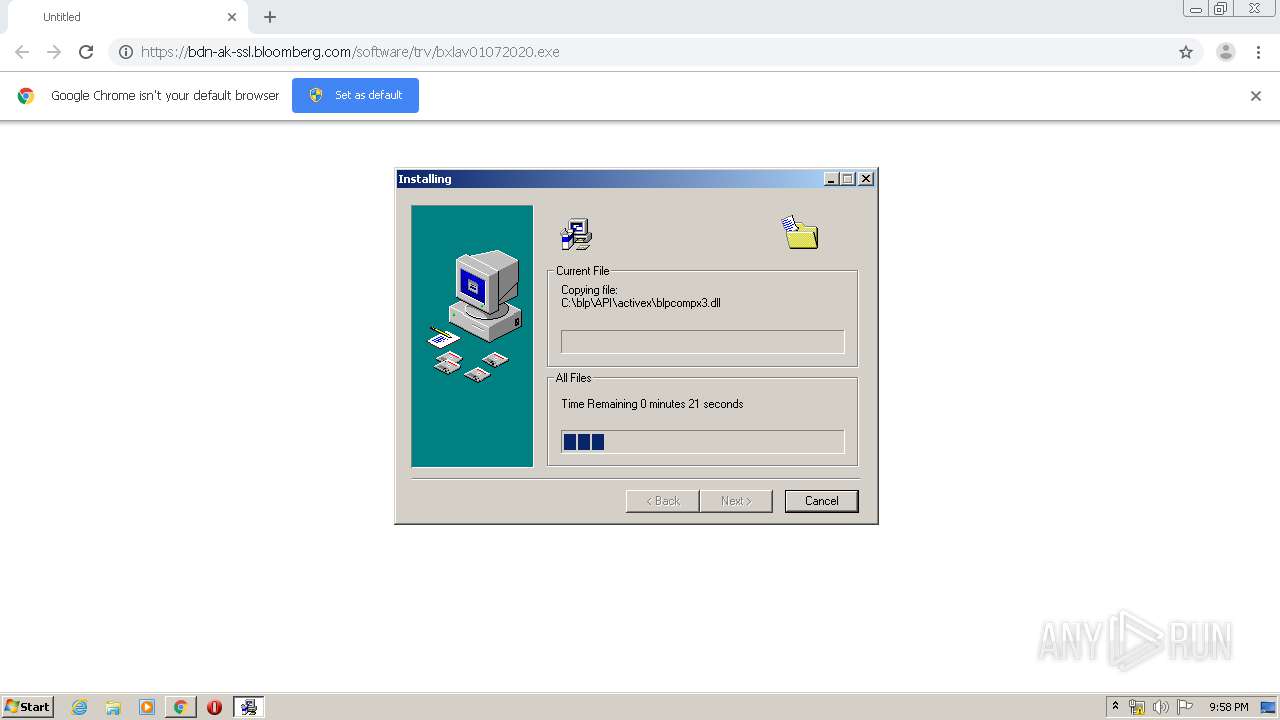
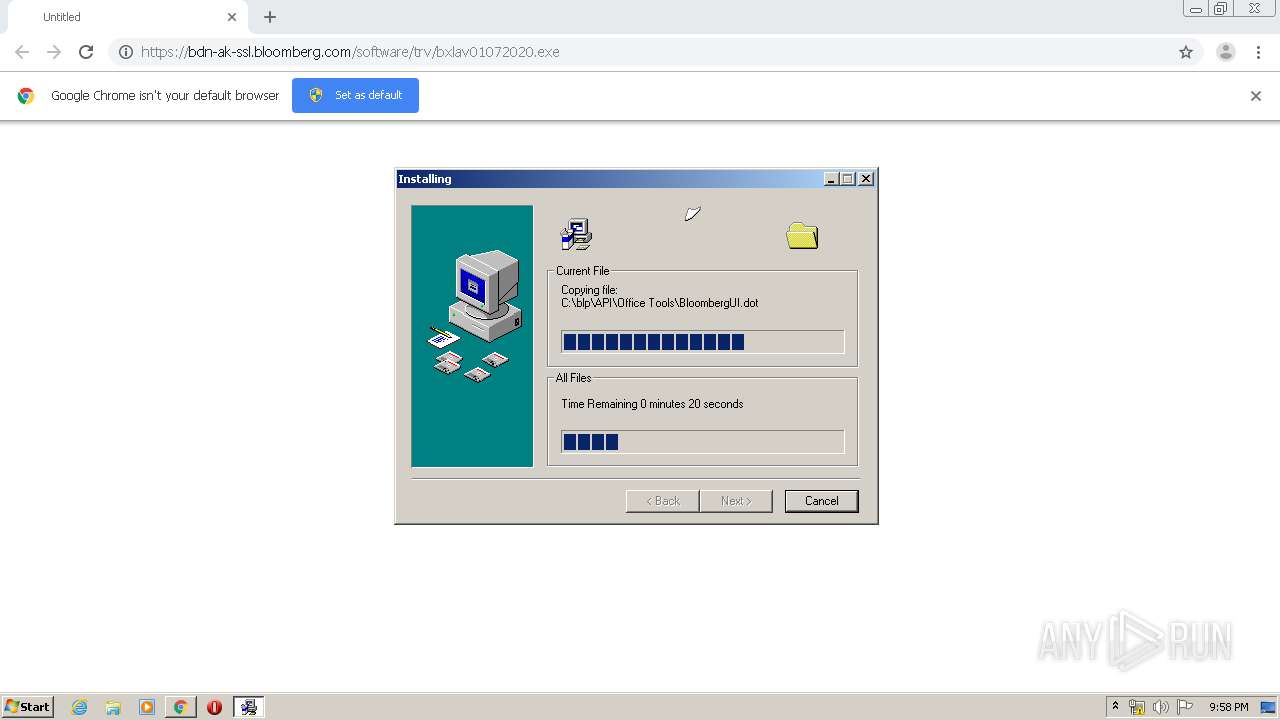
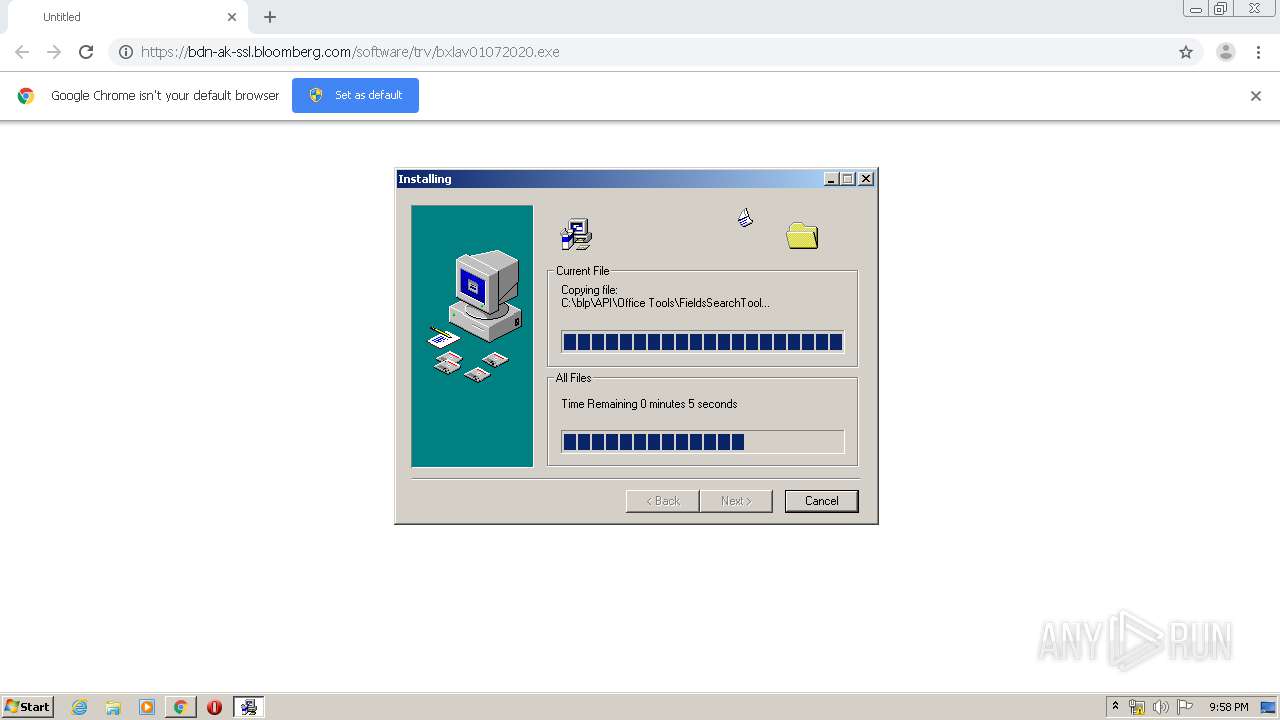
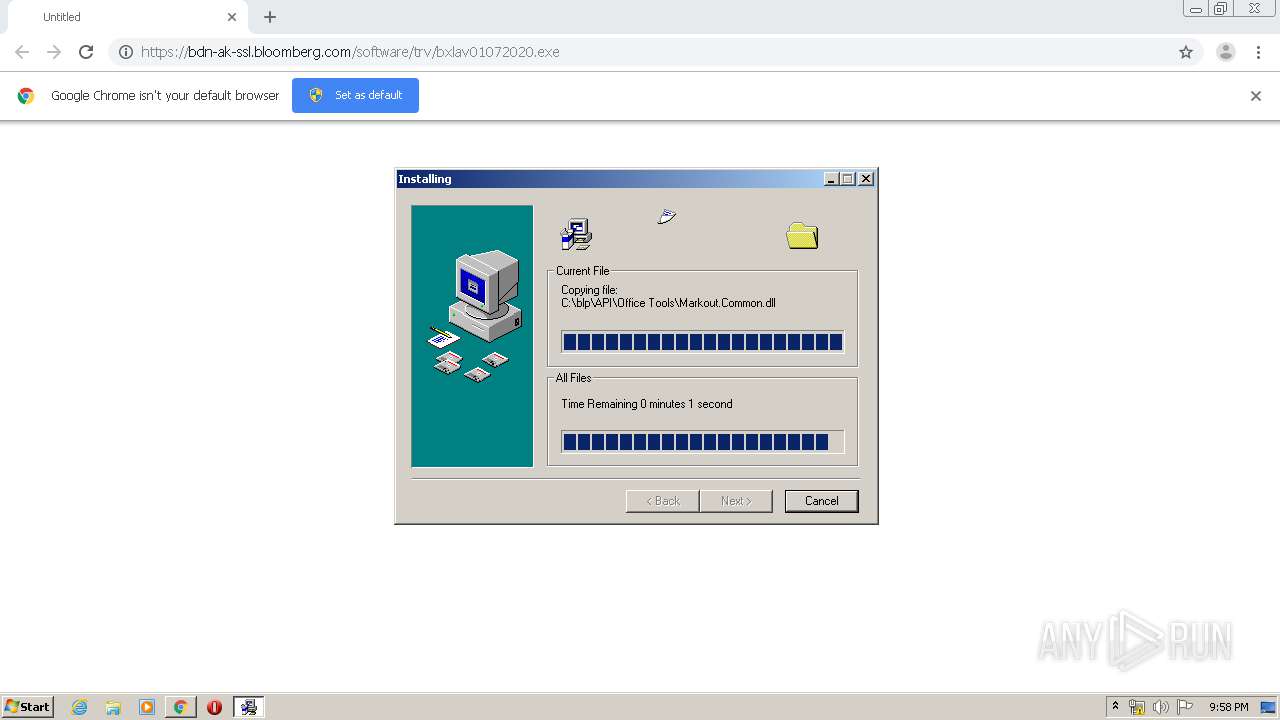
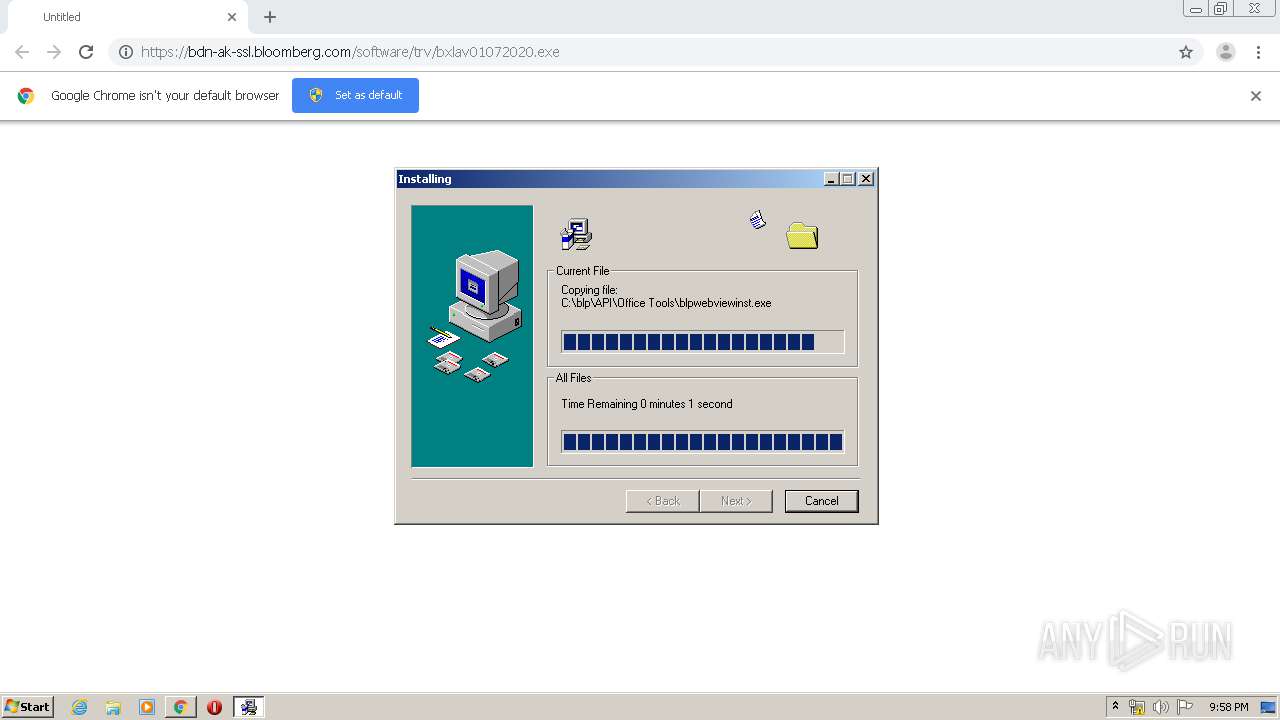
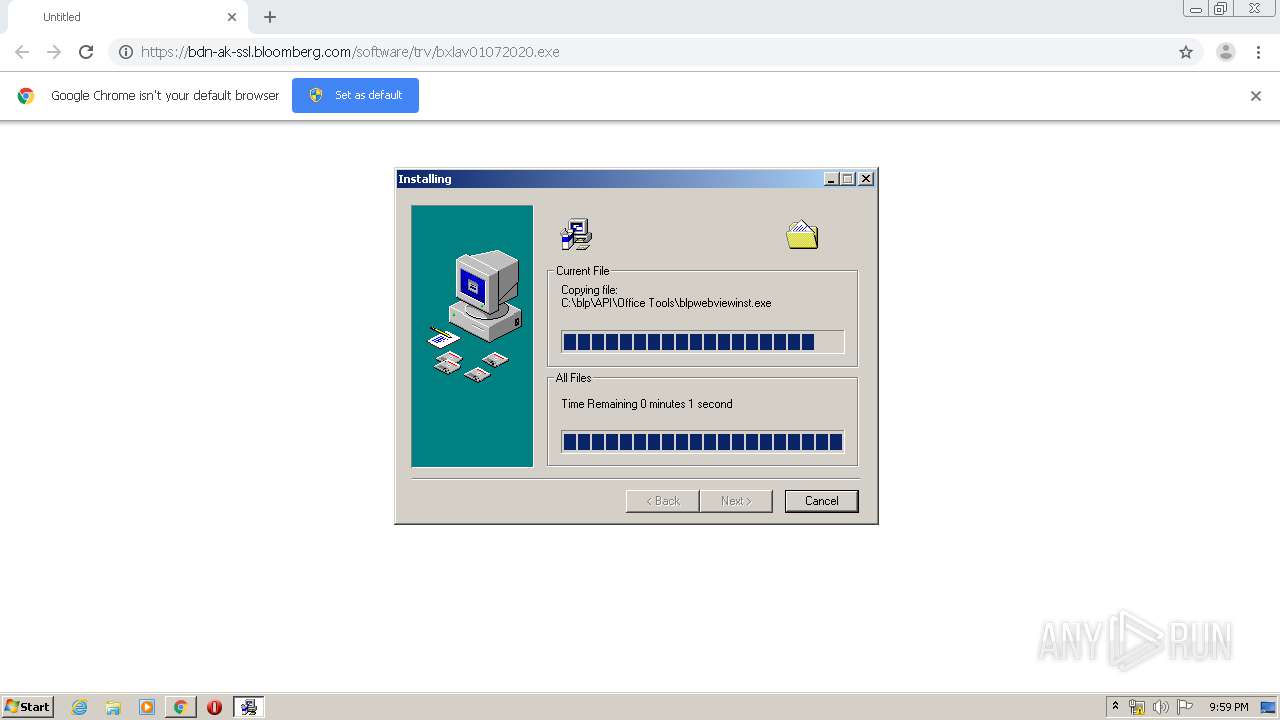
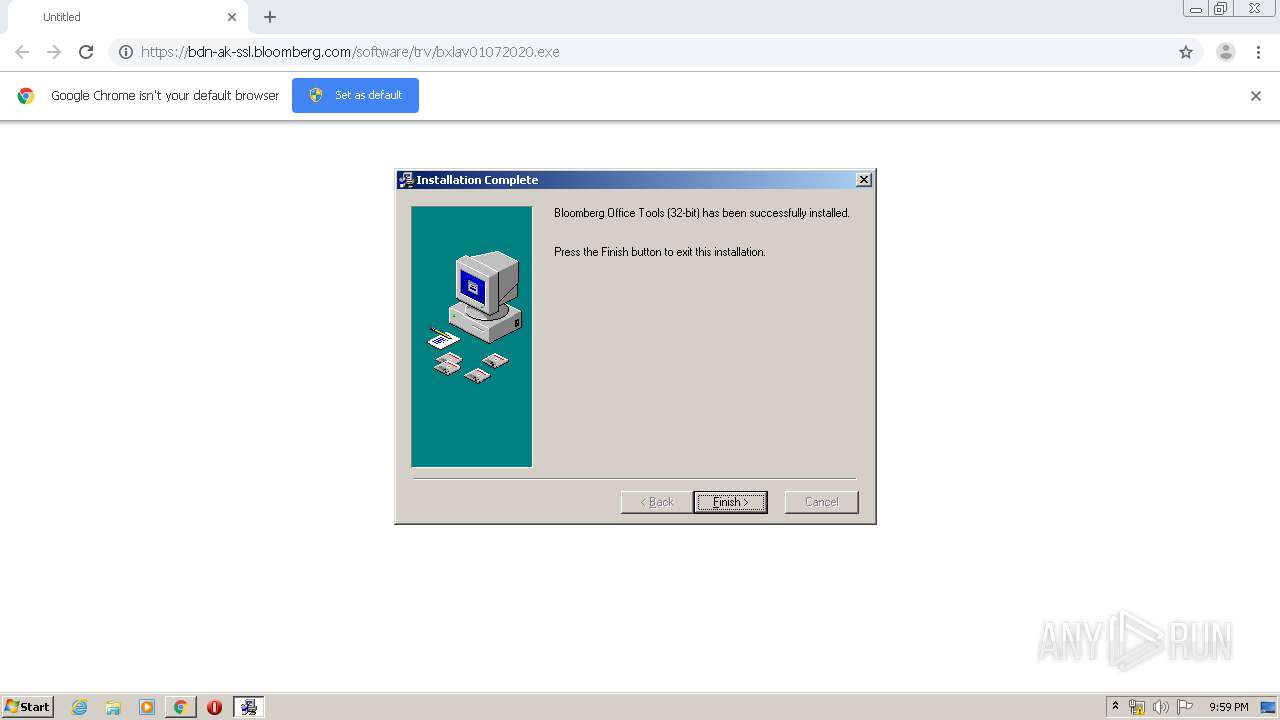
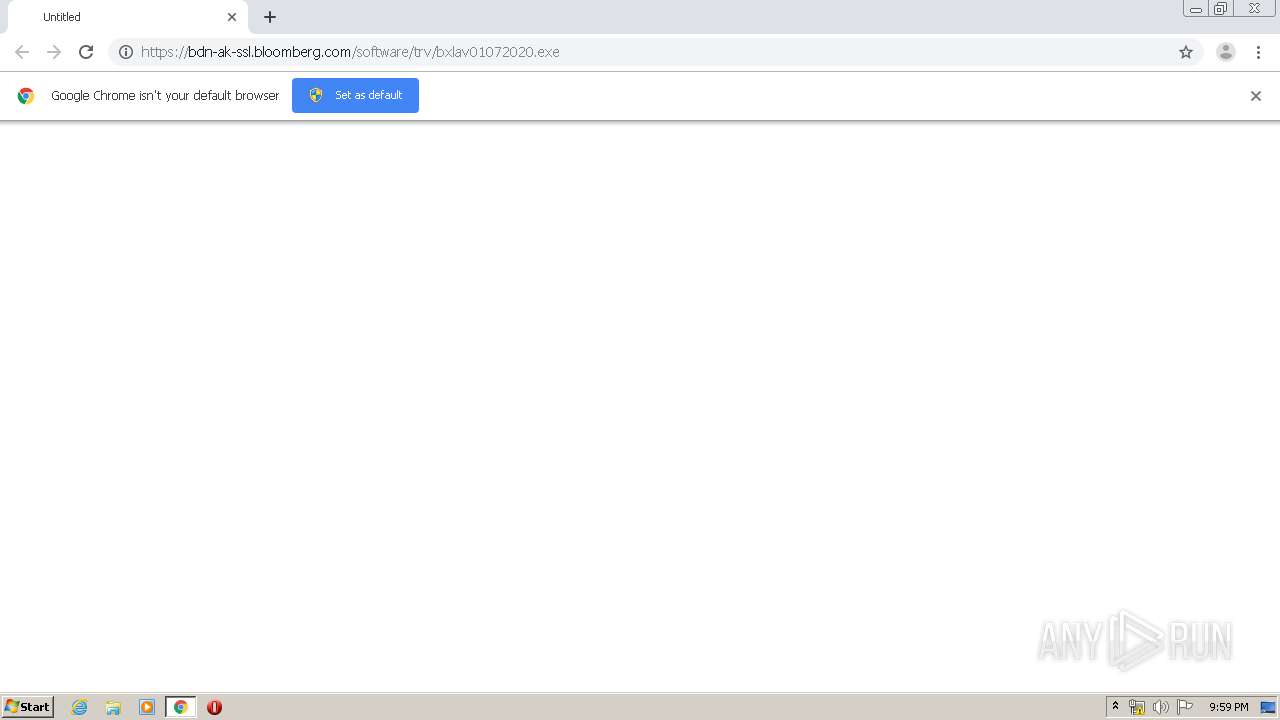
| URL: | https://bdn-ak-ssl.bloomberg.com/software/trv/bxlav01072020.exe |
| Full analysis: | https://app.any.run/tasks/05dd0020-ce85-4463-b807-d5ae1006e4e5 |
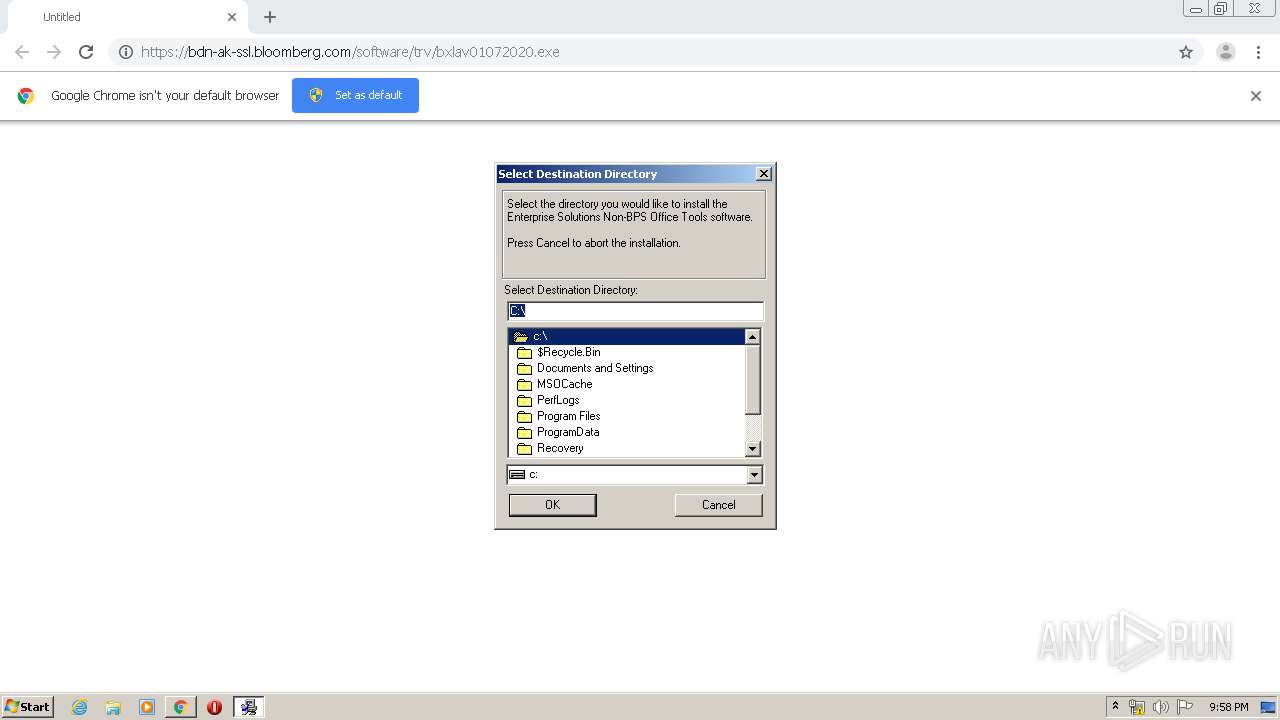
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2020, 21:55:51 |
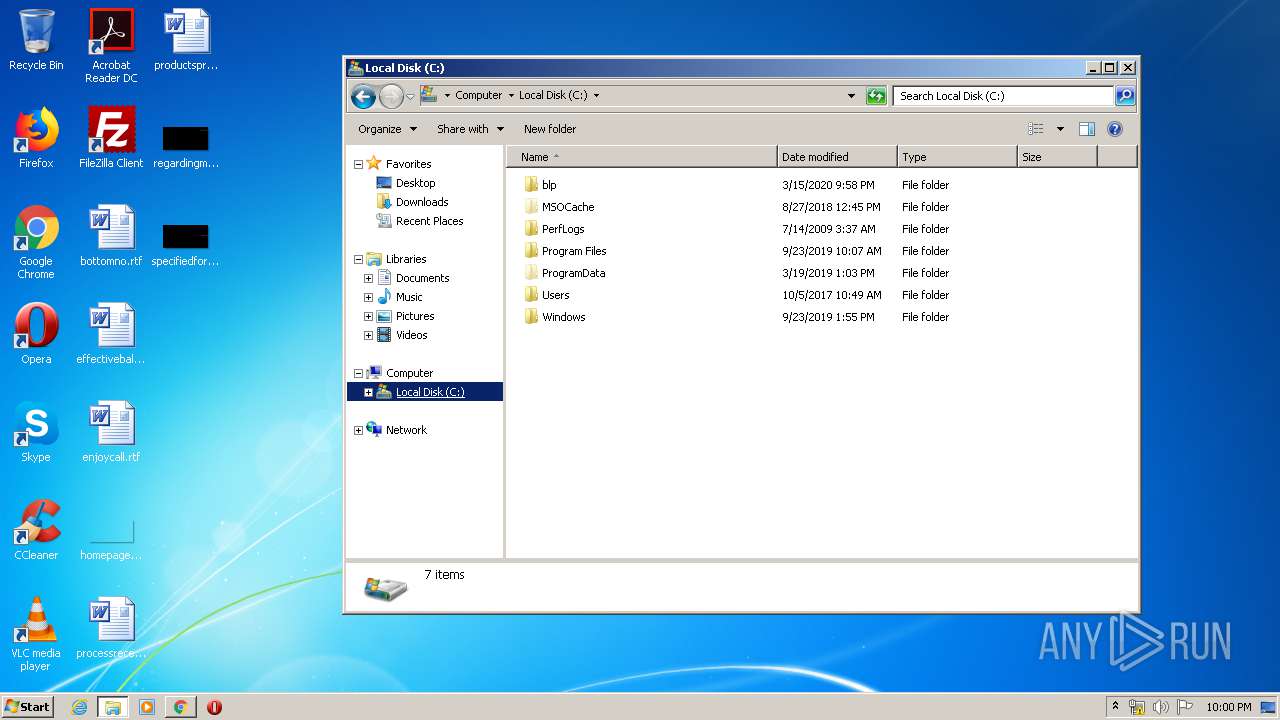
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 55324DC953AC3A5B4FF565BF8515EEC0 |
| SHA1: | 0B5174E0200CB203731D4F223F645B3AD2EA1AE6 |
| SHA256: | 800661AEEFADF6860603A4852A5617F0176529FF524242992837CB7B62005A2A |
| SSDEEP: | 3:N8tnvz/6WKMoTX5:2tnvBs |
MALICIOUS
Application was dropped or rewritten from another process
- bxlav01072020.exe (PID: 3480)
- bxlav01072020.exe (PID: 3496)
- GLB8839.tmp (PID: 3140)
- bbund.exe (PID: 664)
- bbund.exe (PID: 1840)
- bbund.exe (PID: 2428)
- instadd.exe (PID: 2936)
- instadd.exe (PID: 4628)
- instadd.exe (PID: 3548)
- bxladiag.exe (PID: 4852)
- scanver.exe (PID: 5696)
- scanver.exe (PID: 4964)
- scanver.exe (PID: 4520)
- scanver.exe (PID: 3556)
- scanver.exe (PID: 3840)
- scanver.exe (PID: 1732)
- scanver.exe (PID: 4052)
- scanver.exe (PID: 4856)
- scanver.exe (PID: 5488)
Loads dropped or rewritten executable
- GLB8839.tmp (PID: 3140)
- regsvr32.exe (PID: 2140)
- regsvr32.exe (PID: 2856)
- regsvr32.exe (PID: 3460)
- regsvr32.exe (PID: 2104)
- regsvr32.exe (PID: 3812)
- regsvr32.exe (PID: 1508)
- regsvr32.exe (PID: 3640)
- scanver.exe (PID: 5696)
- scanver.exe (PID: 4964)
- scanver.exe (PID: 3556)
- scanver.exe (PID: 3840)
- bxladiag.exe (PID: 4852)
- regsvr32.exe (PID: 2128)
- scanver.exe (PID: 5488)
- scanver.exe (PID: 1732)
- scanver.exe (PID: 4856)
- scanver.exe (PID: 4052)
Registers / Runs the DLL via REGSVR32.EXE
- GLB8839.tmp (PID: 3140)
SUSPICIOUS
Creates files in the Windows directory
- GLB8839.tmp (PID: 3140)
- expand.exe (PID: 1548)
Starts application with an unusual extension
- bxlav01072020.exe (PID: 3496)
Removes files from Windows directory
- GLB8839.tmp (PID: 3140)
Executable content was dropped or overwritten
- bxlav01072020.exe (PID: 3496)
- chrome.exe (PID: 3272)
- expand.exe (PID: 956)
- GLB8839.tmp (PID: 3140)
- expand.exe (PID: 3444)
- expand.exe (PID: 3472)
- expand.exe (PID: 2720)
- expand.exe (PID: 2452)
- expand.exe (PID: 3888)
- expand.exe (PID: 3608)
- expand.exe (PID: 2520)
- expand.exe (PID: 3796)
- expand.exe (PID: 3992)
- expand.exe (PID: 1228)
- expand.exe (PID: 3980)
- expand.exe (PID: 2716)
- expand.exe (PID: 3976)
- expand.exe (PID: 3836)
- expand.exe (PID: 744)
- expand.exe (PID: 1116)
- expand.exe (PID: 3392)
- BLPWEB~1.EXE (PID: 1092)
- expand.exe (PID: 3200)
- expand.exe (PID: 3880)
- expand.exe (PID: 2560)
- expand.exe (PID: 2924)
Creates a software uninstall entry
- GLB8839.tmp (PID: 3140)
Creates COM task schedule object
- regsvr32.exe (PID: 2856)
- regsvr32.exe (PID: 2104)
- regsvr32.exe (PID: 2140)
- regsvr32.exe (PID: 3812)
- regsvr32.exe (PID: 3460)
- regsvr32.exe (PID: 2128)
- regsvr32.exe (PID: 3640)
Creates files in the program directory
- GLB8839.tmp (PID: 3140)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3272)
Starts CMD.EXE for commands execution
- GLB8839.tmp (PID: 3140)
- bxladiag.exe (PID: 4852)
INFO
Application launched itself
- chrome.exe (PID: 3272)
Reads Internet Cache Settings
- chrome.exe (PID: 3272)
Reads the hosts file
- chrome.exe (PID: 3272)
- chrome.exe (PID: 376)
Dropped object may contain Bitcoin addresses
- GLB8839.tmp (PID: 3140)
- expand.exe (PID: 3584)
- expand.exe (PID: 2660)
- expand.exe (PID: 440)
- BLPWEB~1.EXE (PID: 1092)
Reads settings of System Certificates
- chrome.exe (PID: 376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
417
Monitored processes
207
Malicious processes
12
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | expand.exe "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\cc43315bec76167be7dfbb7dd0b6d61974204d6c.b_" "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\cc43315bec76167be7dfbb7dd0b6d61974204d6c.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | expand.exe "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\1446a0f18ceb493cfc6e18ab6a08b51e6d6aa596.b_" "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\1446a0f18ceb493cfc6e18ab6a08b51e6d6aa596.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2331122360927355038 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 404 | expand.exe "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\17608e29b17284df4a2f8af947f578275af81cd0.b_" "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\17608e29b17284df4a2f8af947f578275af81cd0.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 440 | expand.exe "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\4a8c91da0a65d097523680a441150238f865cd42.b_" "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\4a8c91da0a65d097523680a441150238f865cd42.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9521498372900101026,7792031179556000187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16198968902956164339 --mojo-platform-channel-handle=3960 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | expand.exe "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\c5380b18dd08b7936fea5a0e62330417e1be1c2a.b_" "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\c5380b18dd08b7936fea5a0e62330417e1be1c2a.b" | C:\Windows\system32\expand.exe | — | BLPWEB~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | "C:\blp\API\OFFICE~1\bbund.exe" -u "C:\blp\API\Office Tools" | C:\blp\API\OFFICE~1\bbund.exe | — | GLB8839.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Modules
| |||||||||||||||
| 744 | expand.exe "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\85e159ab2919746d1e0594e14ddf1a0c59ff5f6e.b_" "C:\blp\API\Office Tools\xofbaolfedmekehmdjgoiieohnccnanmj\85e159ab2919746d1e0594e14ddf1a0c59ff5f6e.b" | C:\Windows\system32\expand.exe | BLPWEB~1.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 729
Read events
1 110
Write events
572
Delete events
47
Modification events
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3272-13228782962031375 |
Value: 259 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3272) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
259
Suspicious files
68
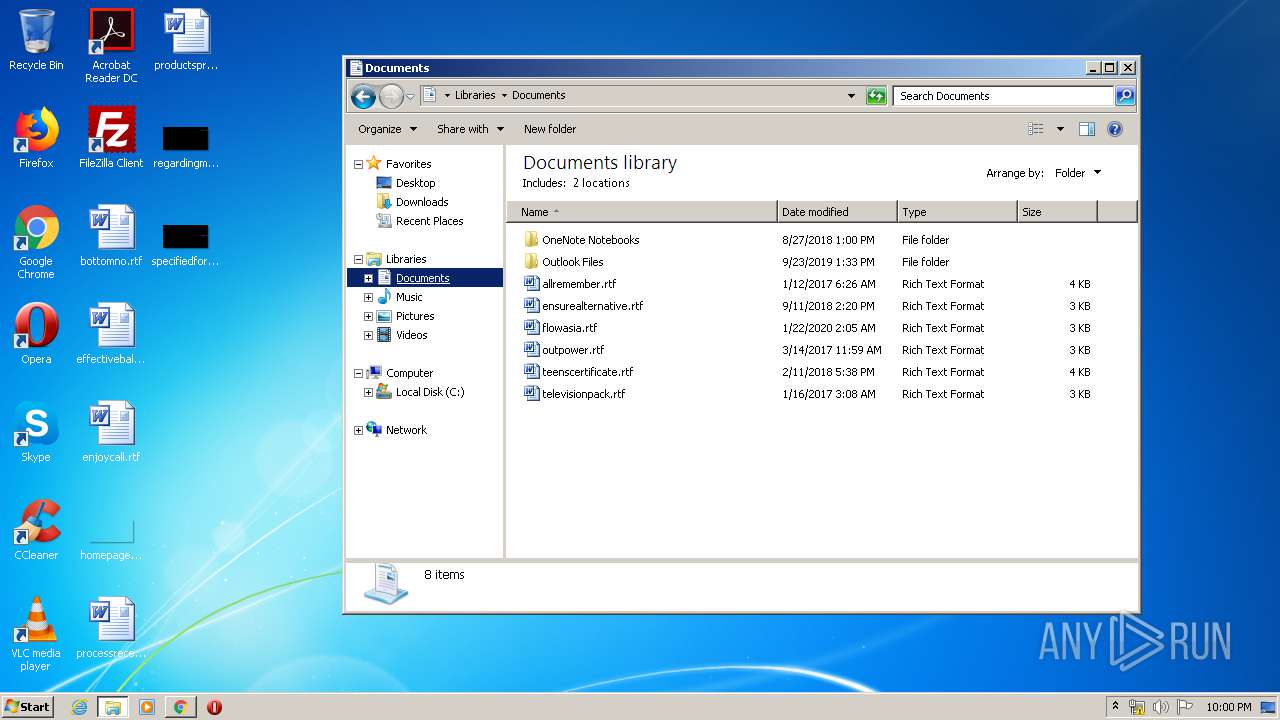
Text files
455
Unknown types
275
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E6EA472-CC8.pma | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1d06d961-e9b0-425f-87c2-29d797274c04.tmp | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa65e16.TMP | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa65e55.TMP | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa65e64.TMP | text | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3272 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa65f7d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
376 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
376 | chrome.exe | GET | 200 | 74.125.104.104:80 | http://r2---sn-2gb7sn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=84.17.36.75&mm=28&mn=sn-2gb7sn7k&ms=nvh&mt=1584309491&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
376 | chrome.exe | GET | 200 | 173.194.150.231:80 | http://r1---sn-2gb7sn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=84.17.36.75&mm=28&mn=sn-2gb7sn7s&ms=nvh&mt=1584309491&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
376 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
376 | chrome.exe | 2.20.190.220:443 | bdn-ak-ssl.bloomberg.com | Akamai International B.V. | — | unknown |
376 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 172.217.16.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 74.125.104.104:80 | r2---sn-2gb7sn7k.gvt1.com | Google Inc. | US | whitelisted |
376 | chrome.exe | 172.217.16.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bdn-ak-ssl.bloomberg.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GLB8839.tmp | Create subfolder:activex SUCCESS |
GLB8839.tmp | Create subfolder:Office Tools SUCCESS |
regsvr32.exe | bof::Addin::DLL_PROCESS_ATTACH complete. |
regsvr32.exe | bof::Addin::DLL_PROCESS_DETACH complete. |