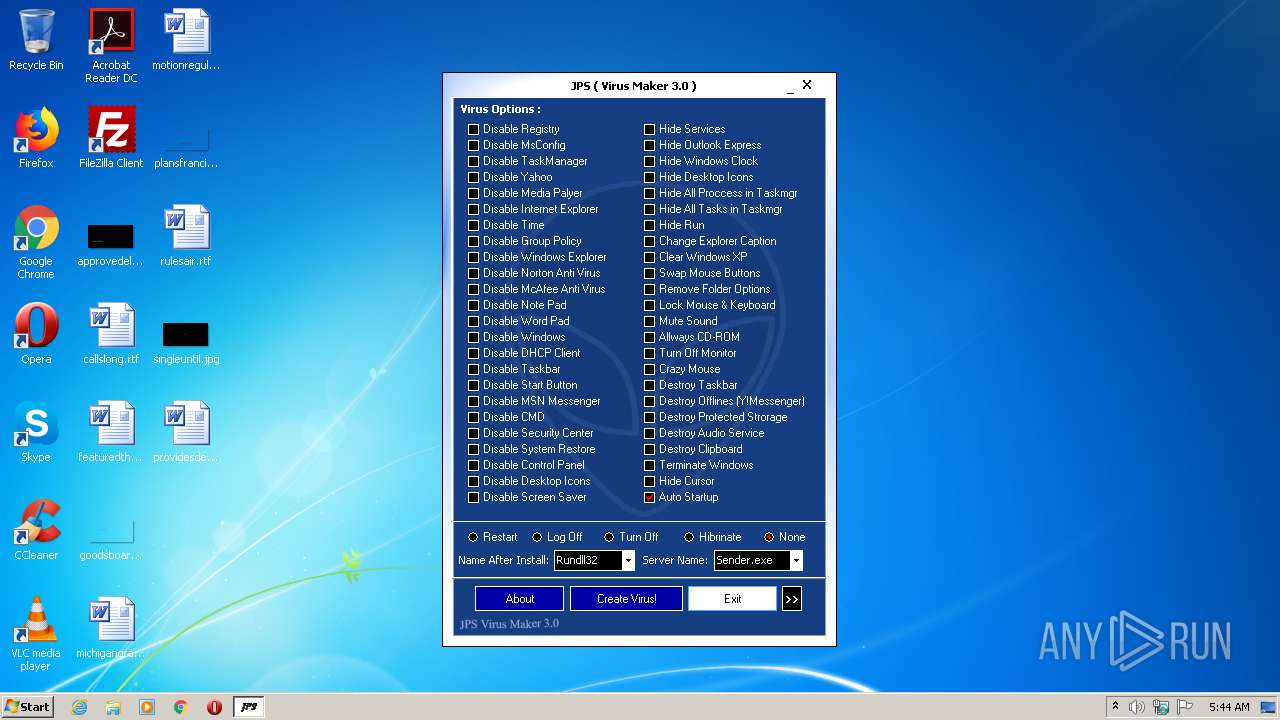
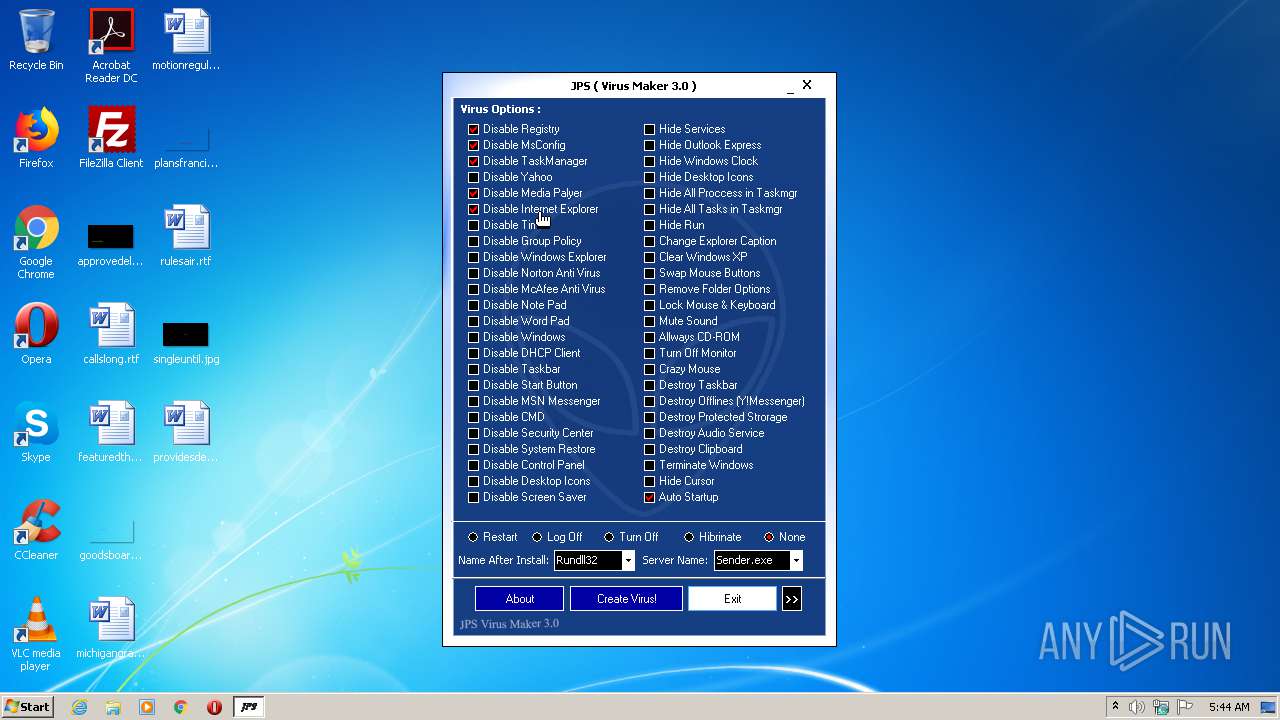
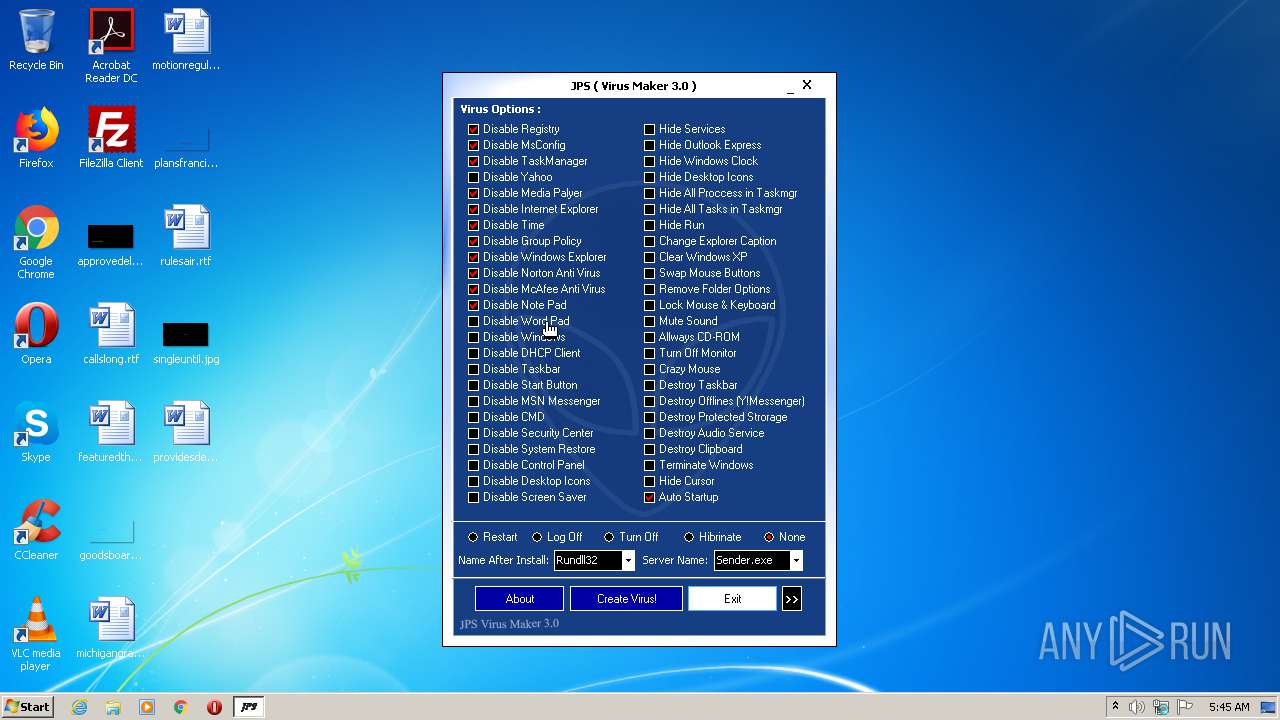
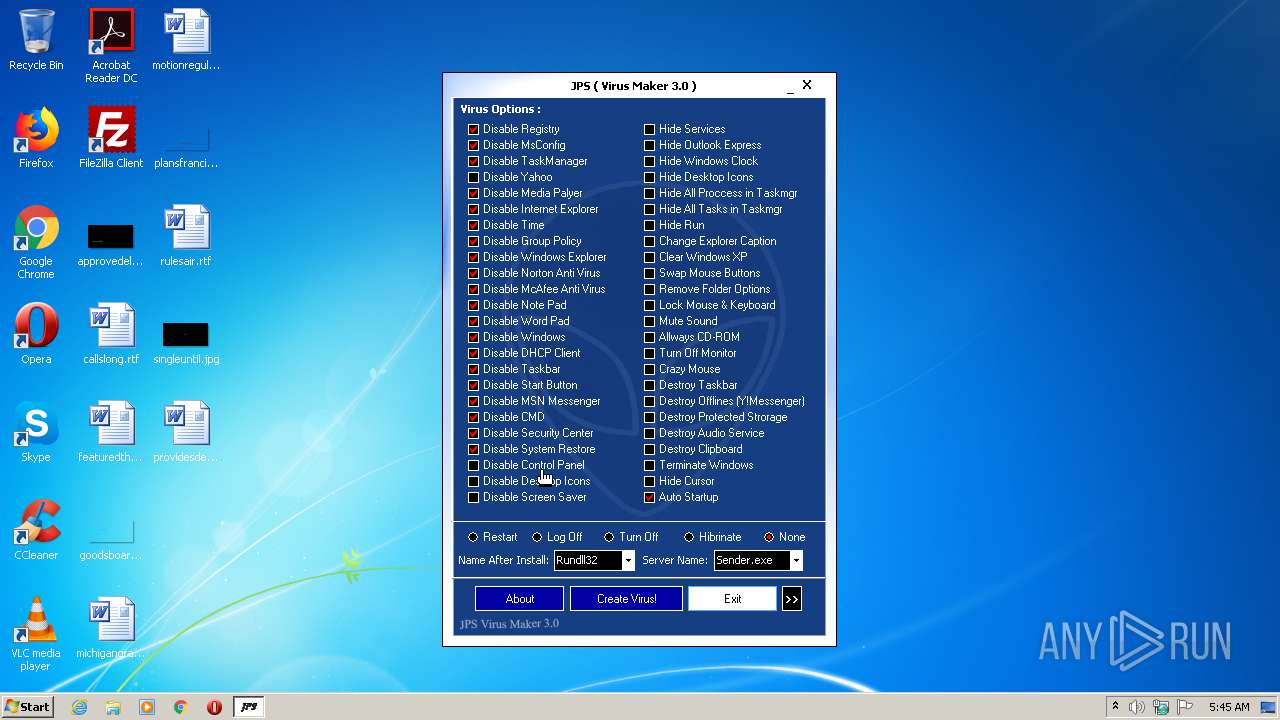
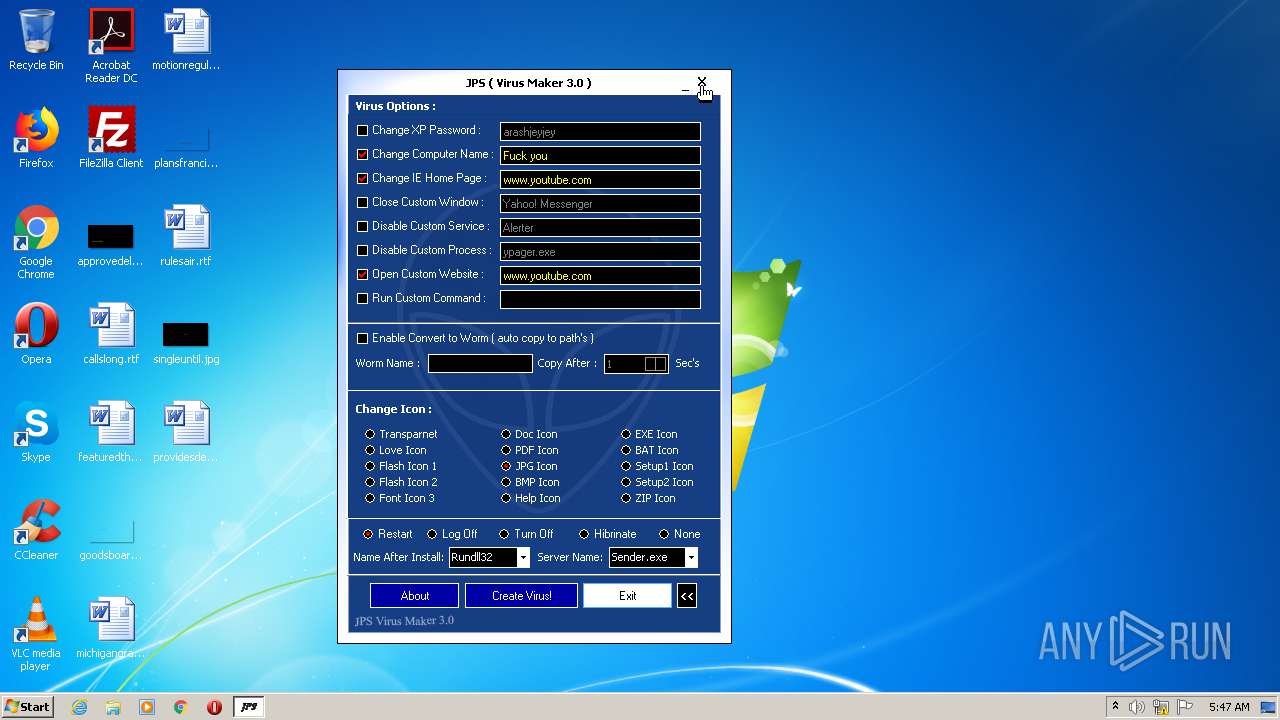
| File name: | JPS virus maker.exe |
| Full analysis: | https://app.any.run/tasks/2662d662-4ac8-420d-8f94-5b95021436c0 |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2021, 04:44:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 76DE1B882FD303A0E90CD2E80FA69804 |
| SHA1: | 67BA0C0CCC24FAC781AC8AF6A6871264F31491AA |
| SHA256: | 8003BB8BA0689932D96836CDB9F3CCAE952A59BACC3FB79289A52657342A46AB |
| SSDEEP: | 6144:sIW/xjgHP3a8Z8ht5vaRSycrRiUdJR87/9VNtUzRIjTqXxWjMjj6Me0GUvh:YJgEvyvUbRO9VNtJoj |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 3260)
Drops a file with too old compile date
- JPS virus maker.exe (PID: 1216)
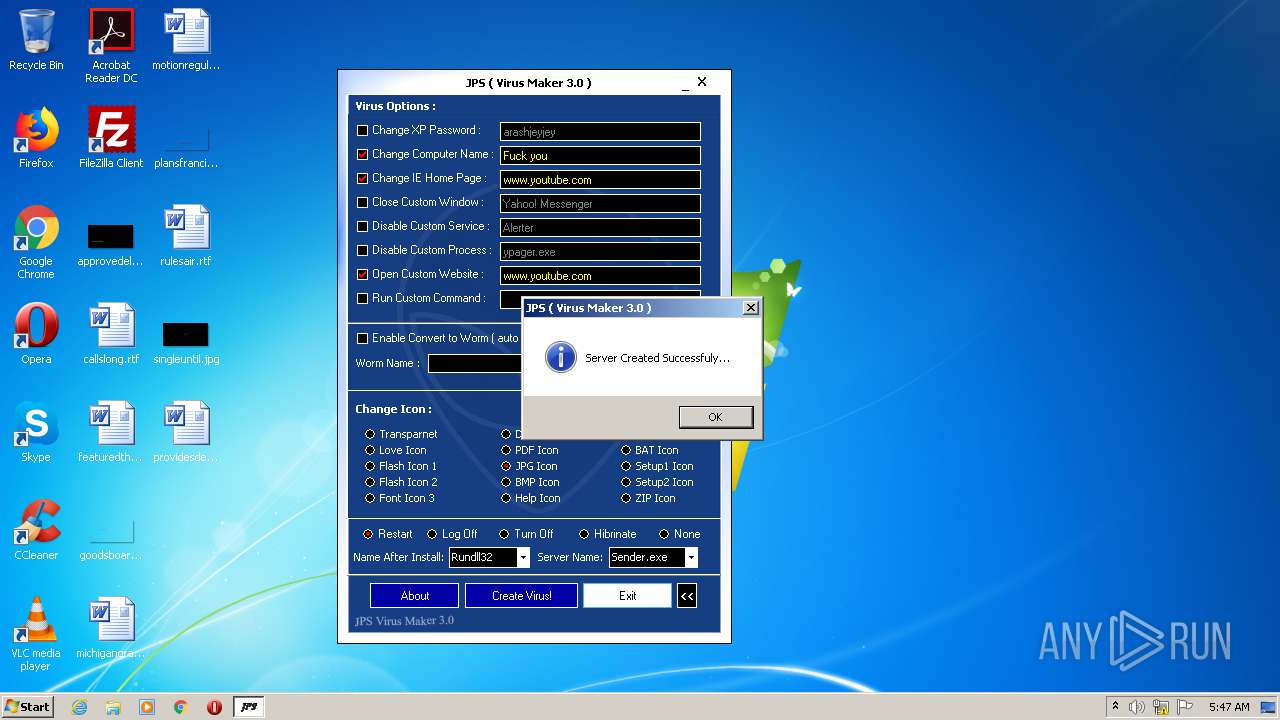
Executable content was dropped or overwritten
- JPS virus maker.exe (PID: 1216)
INFO
Manual execution by user
- explorer.exe (PID: 2436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Generic (100) |
|---|
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1057d0 |
| UninitializedDataSize: | 770048 |
| InitializedDataSize: | 8192 |
| CodeSize: | 299008 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
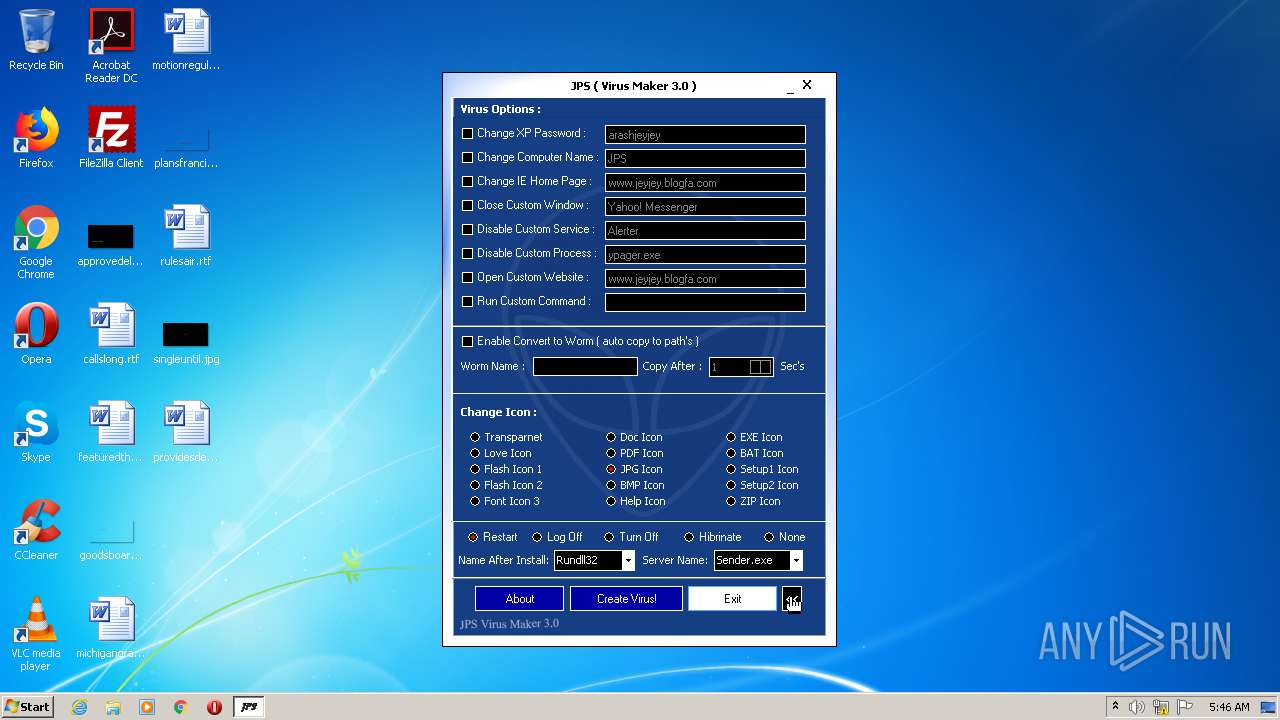
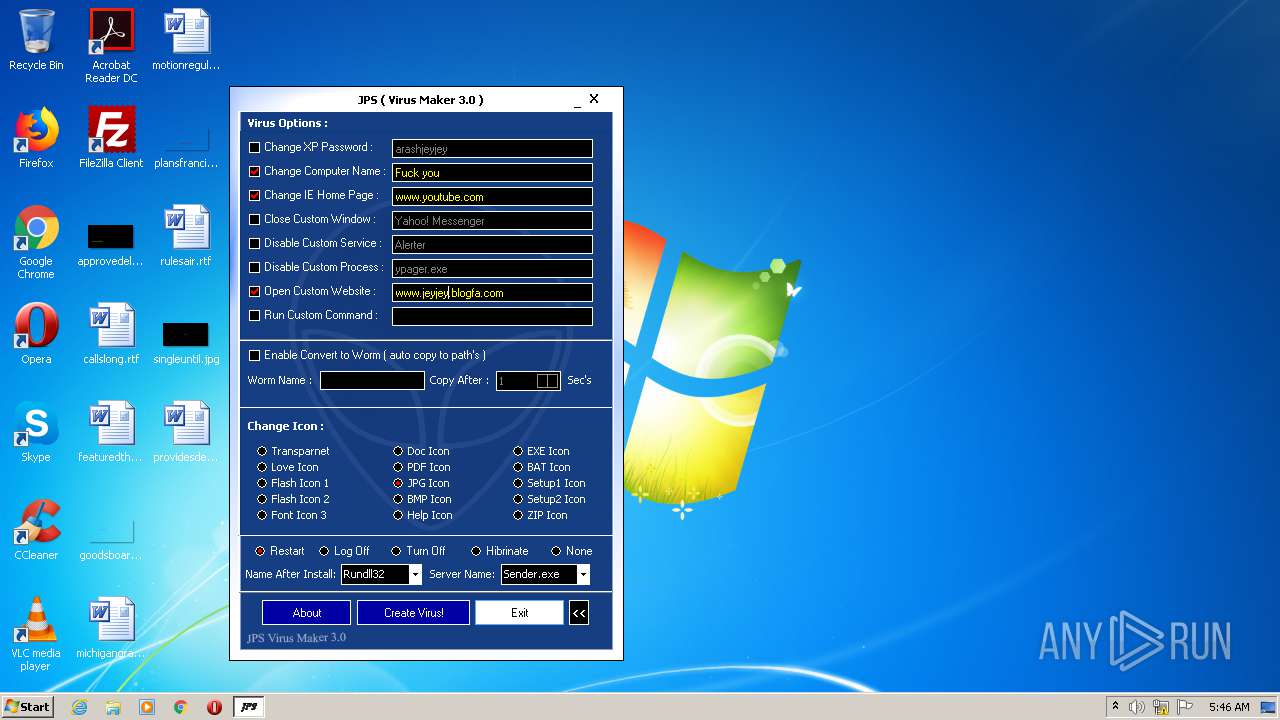
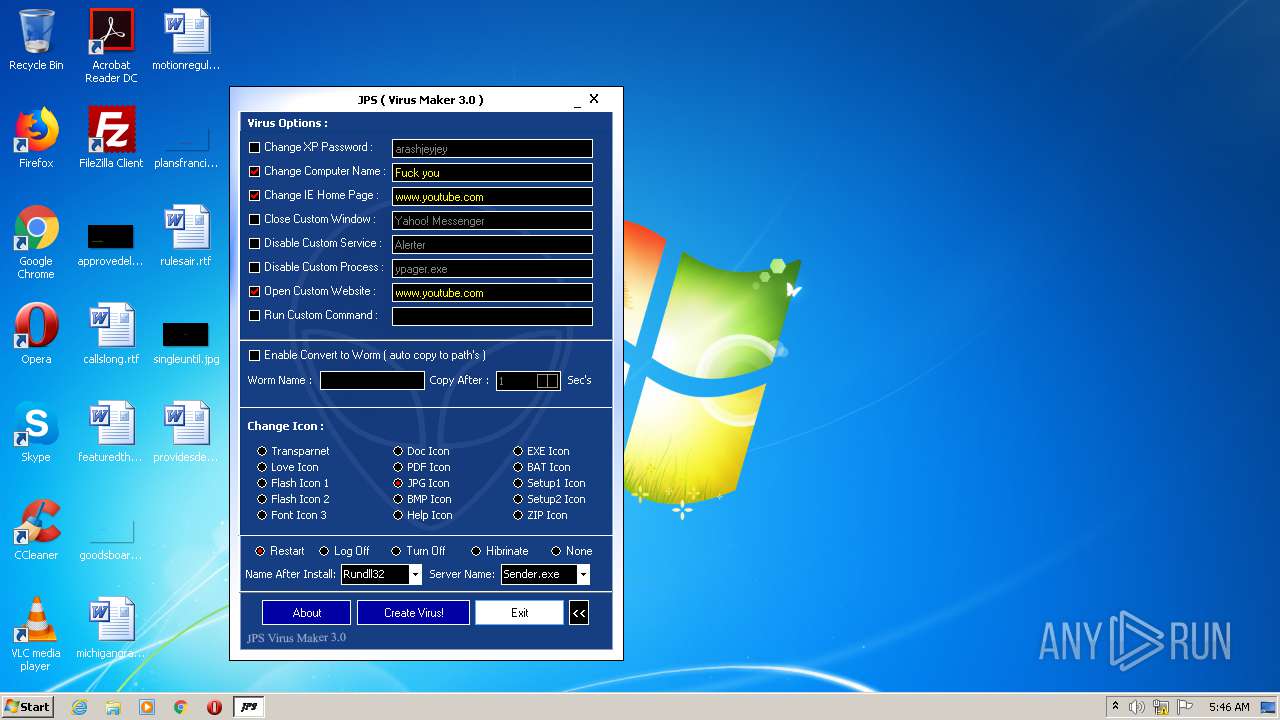
| CompanyName: | www.jeyjey.blogfa.com |
| FileDescription: | Arash Veyskarami |
| FileVersion: | 3.0.0.0 |
| InternalName: | Arashjeyjey@yahoo.com |
| LegalCopyright: | www.jeyjey.blogfa.com |
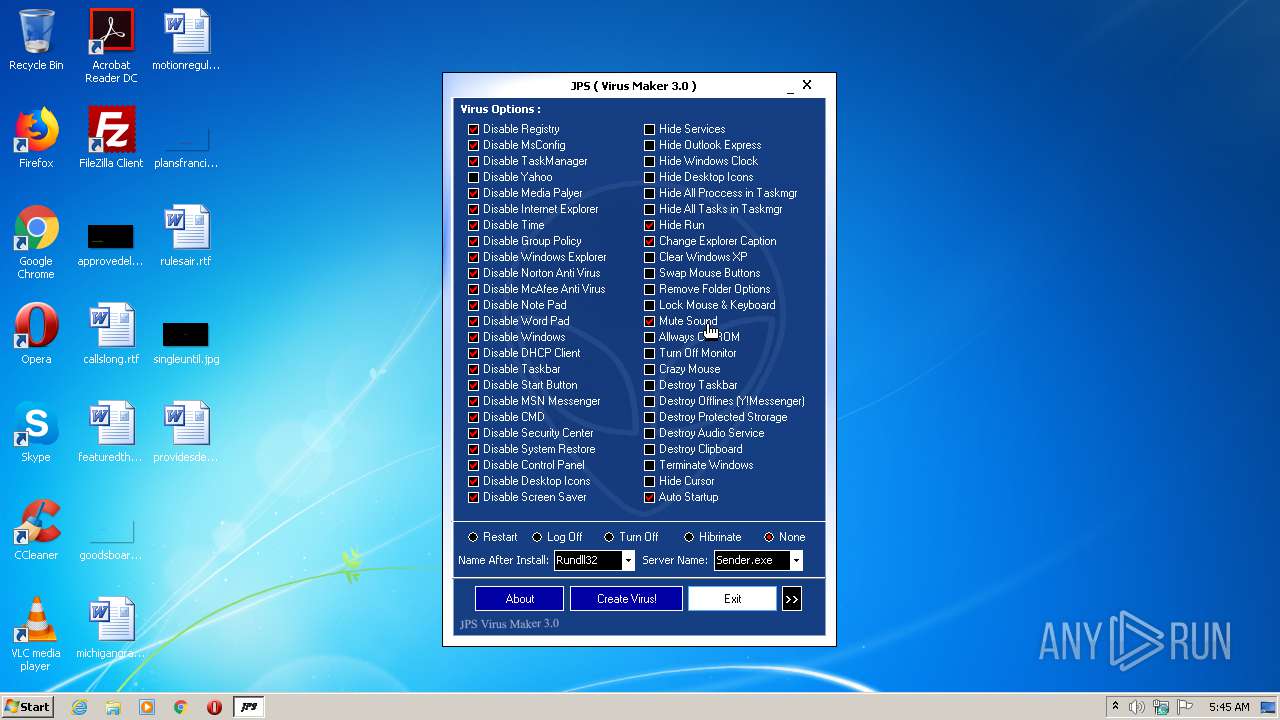
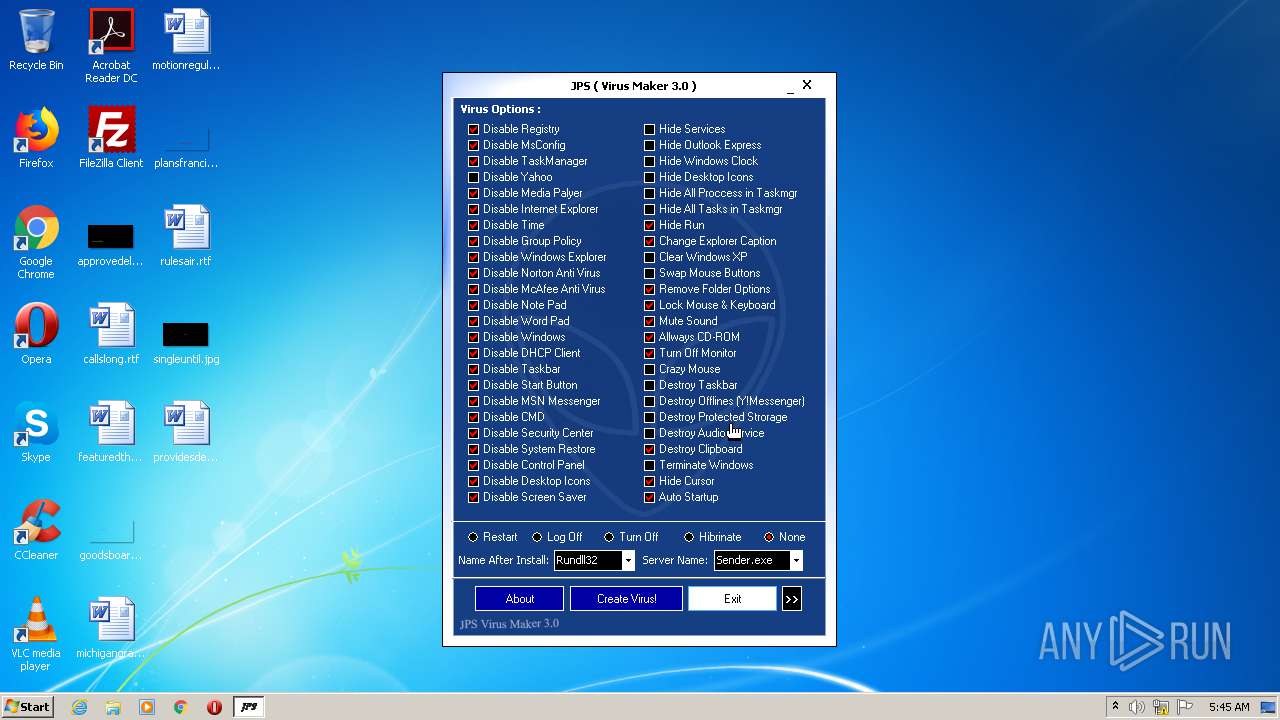
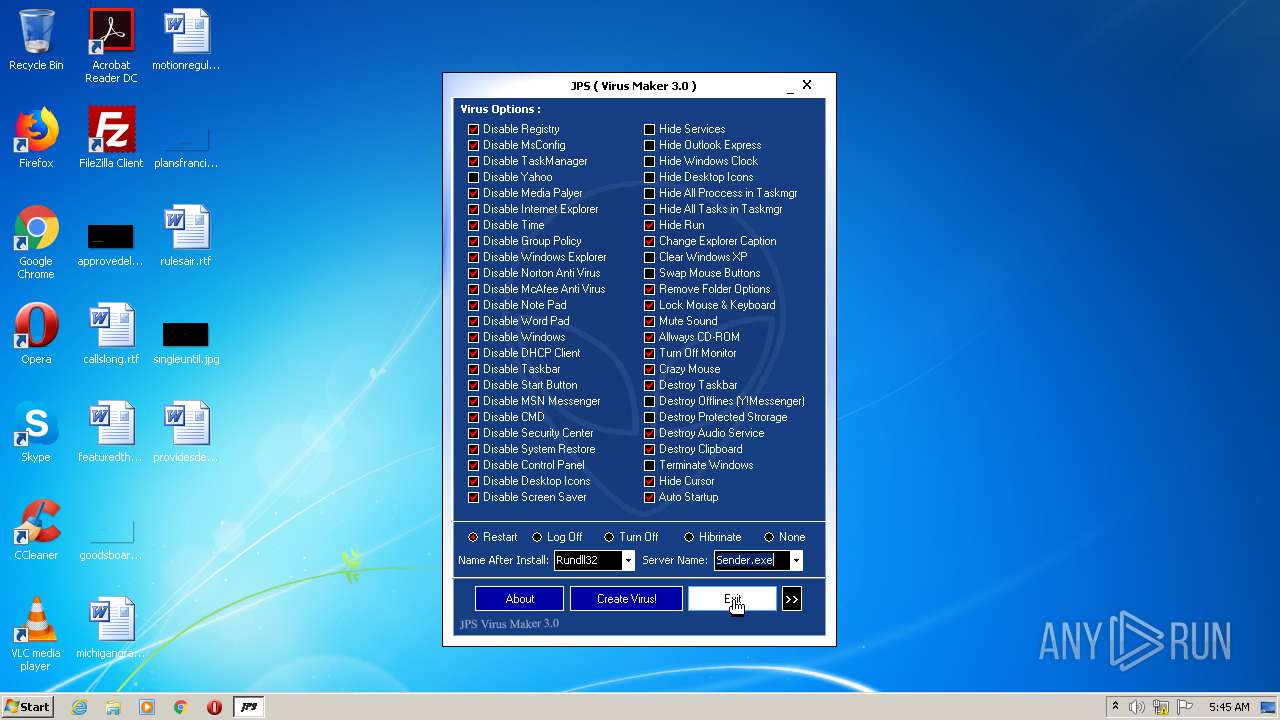
| LegalTrademarks: | JPS (Virus Maker 3.0) |
| OriginalFilename: | VirusMaker.exe |
| ProductName: | JPS (Virus Maker 3.0) |
| ProductVersion: | 3.0 |
| Comments: | Coded By Arash Veyskarami ( in Delphi ) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x2020 |
| Relocations: | 0x2020 |
| Size of header: | 0x2020 |
| Min extra paragraphs: | 0x2020 |
| Max extra paragraphs: | 0x2020 |
| Initial SS value: | 0x2020 |
| Initial SP value: | 0x2020 |
| Checksum: | 0x2020 |
| Initial IP value: | 0x2020 |
| Initial CS value: | 0x2020 |
| Overlay number: | 0x2020 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x000BD000 | 0x00049000 | 0x00048A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91754 | |
0x00106000 | 0x00002000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.5703 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41556 | 956 | UNKNOWN | Farsi - Iran | RT_VERSION |
50 | 7.28193 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
32761 | 4.12193 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_CURSOR |
ICO | 7.90842 | 24064 | UNKNOWN | Farsi - Iran | ICONS9 |
FLATDOWN | 6.48827 | 124 | UNKNOWN | UNKNOWN | RT_BITMAP |
FLATUP | 6.28174 | 124 | UNKNOWN | UNKNOWN | RT_BITMAP |
DLGTEMPLATE | 6.10444 | 82 | UNKNOWN | UNKNOWN | RT_DIALOG |
DVCLAL | 3.875 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 7.66259 | 824 | UNKNOWN | UNKNOWN | RT_RCDATA |
TFORM1 | 7.88398 | 86189 | UNKNOWN | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
43
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1216 | "C:\Users\admin\AppData\Local\Temp\JPS virus maker.exe" | C:\Users\admin\AppData\Local\Temp\JPS virus maker.exe | explorer.exe | ||||||||||||
User: admin Company: www.jeyjey.blogfa.com Integrity Level: MEDIUM Description: Arash Veyskarami Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2436 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30
Read events
29
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3260) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
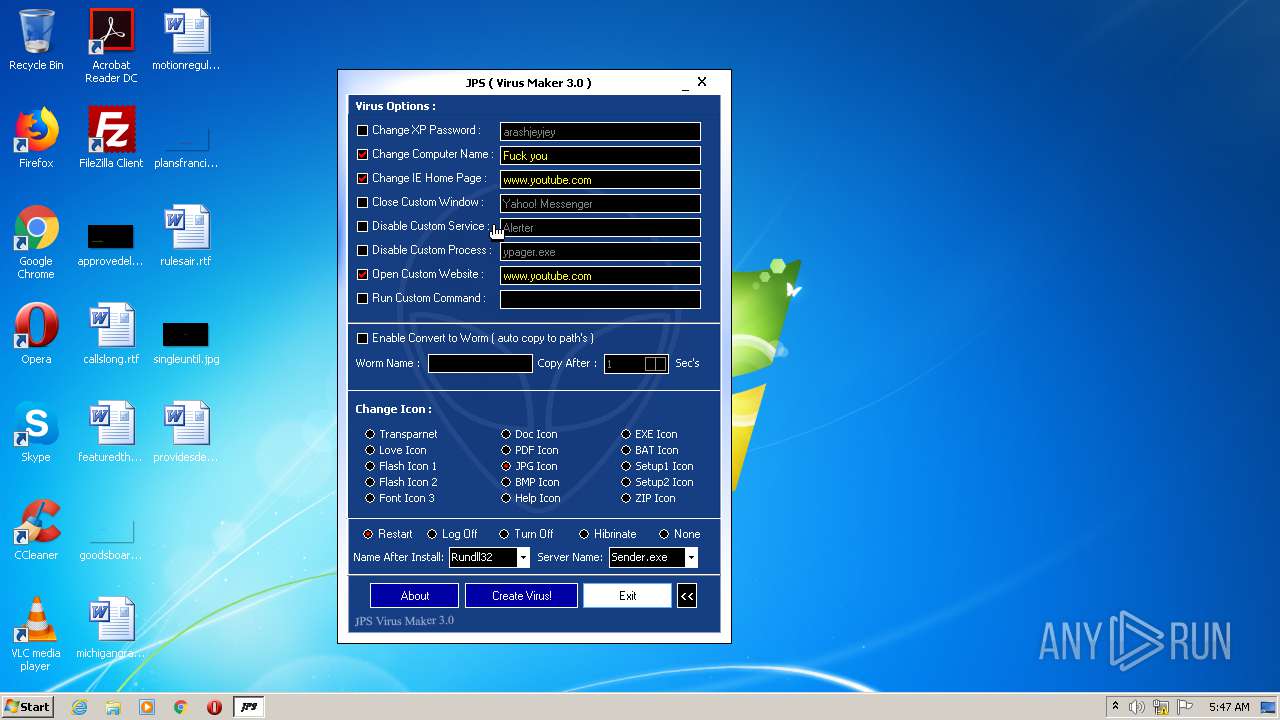
| 1216 | JPS virus maker.exe | C:\Users\admin\AppData\Local\Temp\Sender.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report