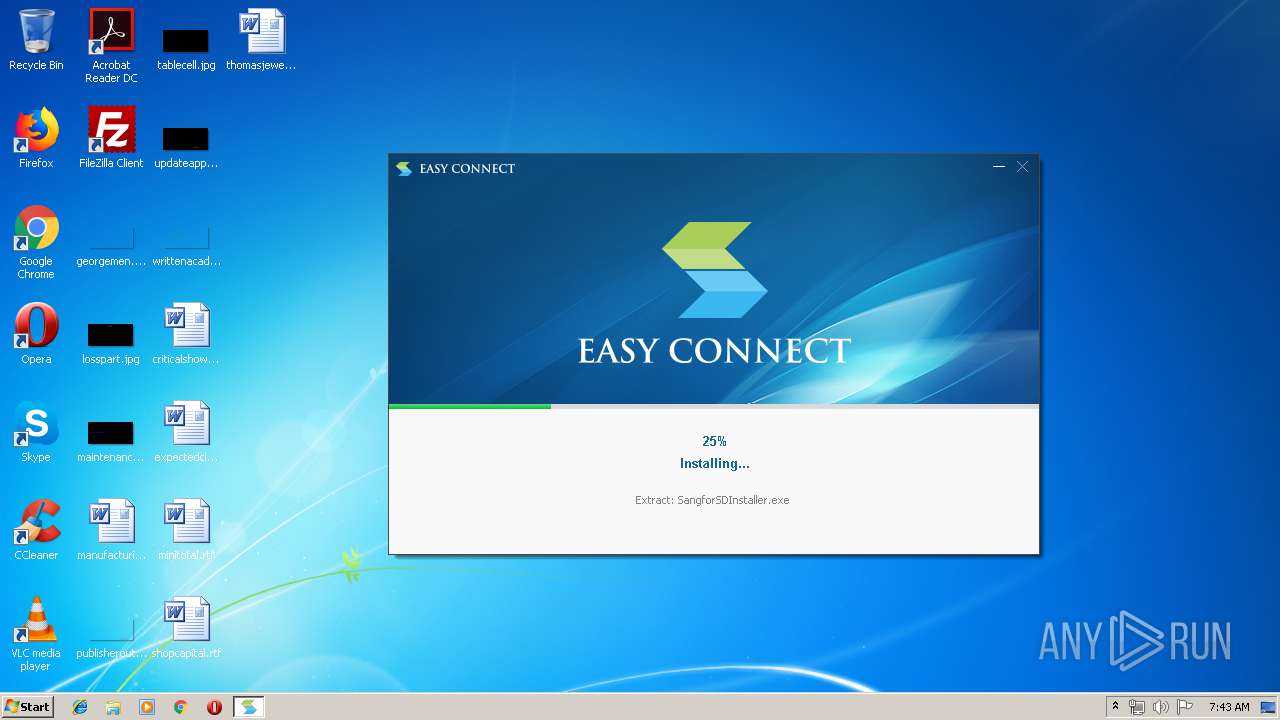
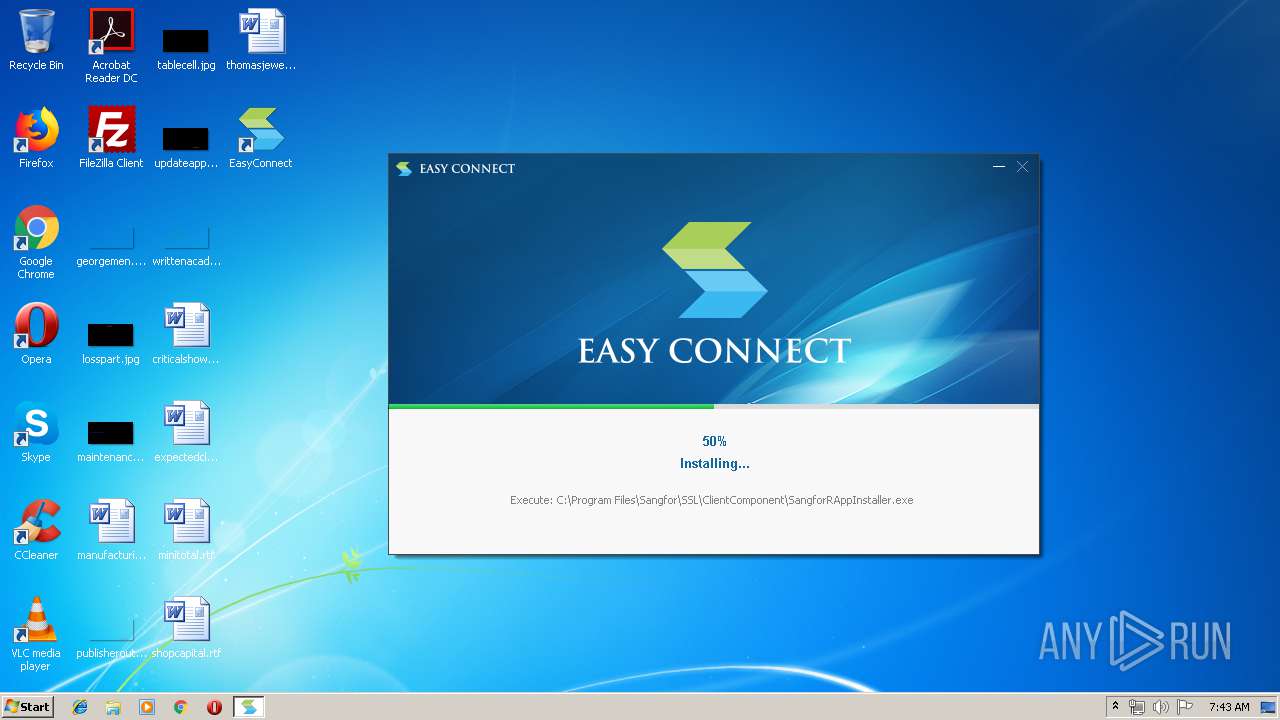
| download: | EasyConnectInstaller.exe |
| Full analysis: | https://app.any.run/tasks/db4c0dbb-1268-4b8a-82f3-fde44411d078 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2019, 06:42:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 7444855D7B0A8747A02F55D72F30D7E4 |
| SHA1: | A0F7EE7F271667C25902ED3B9C7E9B76636F3FDB |
| SHA256: | 7FF56B5367A33EF70FC999BD2F25B9242DB63A4866F12F67912331C78BBA2B5C |
| SSDEEP: | 393216:t78Uwc6LCV4U+xKLGorIbu9yVckNAnS0hJfaZU9nc:RDwc6xU2Nor1yLNAS0baZn |
MALICIOUS
Application was dropped or rewritten from another process
- Uninstall.exe (PID: 3648)
- TcpDriverInstaller.exe (PID: 2512)
- SangforCSClientInstaller.exe (PID: 3288)
- Remove.exe (PID: 2488)
- Install.exe (PID: 3080)
- DnsDriverInstaller.exe (PID: 2776)
- SuperExeInstaller.exe (PID: 2140)
- Remove.exe (PID: 3796)
- Install.exe (PID: 4088)
- SangforServiceClientInstaller.exe (PID: 3864)
- HTPInstaller.exe (PID: 2212)
- SJobberInstaller.exe (PID: 2524)
- SangforUpdateInstaller.exe (PID: 404)
- SangforRAppInstaller.exe (PID: 2216)
- VC2010RedistX86UInstaller.exe (PID: 2144)
- InstallControl.exe (PID: 2416)
- SangforSDInstaller.exe (PID: 2476)
- VNICInstaller.exe (PID: 3016)
- ndiscleanup.x86.exe (PID: 2812)
- SdDriverInstaller.exe (PID: 2720)
- InstallGSDDrvhelper.exe (PID: 2804)
- ns5422.tmp (PID: 4068)
- RestartSpooler.exe (PID: 2648)
- ns55AA.tmp (PID: 2668)
- vacon.exe (PID: 692)
- Install.exe (PID: 3000)
- Remove.exe (PID: 3788)
- SangforECPluginInstaller.exe (PID: 3952)
- nsAA53.tmp (PID: 3068)
- SetIPTime.exe (PID: 360)
- SsdtDriverInstaller.exe (PID: 1344)
- ECBaseInstaller.exe (PID: 3812)
- Install.exe (PID: 2092)
- ECAgentInstaller.exe (PID: 3140)
- SuperServiceInstaller.exe (PID: 2400)
- ECAgent.exe (PID: 3308)
- SangforPromoteService.exe (PID: 3704)
- ECAgent.exe (PID: 2912)
- ECAgent.exe (PID: 3572)
- ECAgent.exe (PID: 4028)
- SangforCSClient.exe (PID: 4016)
- SangforPromote.exe (PID: 3108)
- SangforCSClient.exe (PID: 2320)
- SangforCSClient.exe (PID: 1520)
- ECAgent.exe (PID: 2996)
Loads dropped or rewritten executable
- SangforECPluginInstaller.exe (PID: 3952)
- EasyConnectInstaller.exe (PID: 2612)
- rundll32.exe (PID: 2768)
- TcpDriverInstaller.exe (PID: 2512)
- DnsDriverInstaller.exe (PID: 2776)
- SangforServiceClientInstaller.exe (PID: 3864)
- SuperExeInstaller.exe (PID: 2140)
- SdDriverInstaller.exe (PID: 2720)
- VNICInstaller.exe (PID: 3016)
- InstallControl.exe (PID: 2416)
- SangforCSClientInstaller.exe (PID: 3288)
- svchost.exe (PID: 852)
- svchost.exe (PID: 1232)
- svchost.exe (PID: 980)
- ECAgent.exe (PID: 3308)
- SangforPromoteService.exe (PID: 3704)
- SuperServiceInstaller.exe (PID: 2400)
- ECAgent.exe (PID: 3572)
- ECAgent.exe (PID: 2912)
- ECBaseInstaller.exe (PID: 3812)
- SangforCSClient.exe (PID: 4016)
- SangforPromote.exe (PID: 3108)
- SangforCSClient.exe (PID: 1520)
- SangforCSClient.exe (PID: 2320)
- ECAgent.exe (PID: 4028)
- ECAgent.exe (PID: 2996)
Changes settings of System certificates
- vacon.exe (PID: 692)
- ECAgent.exe (PID: 3308)
- ECAgent.exe (PID: 3572)
- SangforPromoteService.exe (PID: 3704)
- ECAgent.exe (PID: 2996)
SUSPICIOUS
Creates COM task schedule object
- EasyConnectInstaller.exe (PID: 2612)
- InstallControl.exe (PID: 2416)
Executable content was dropped or overwritten
- EasyConnectInstaller.exe (PID: 2612)
- SangforCSClientInstaller.exe (PID: 3288)
- TcpDriverInstaller.exe (PID: 2512)
- SuperExeInstaller.exe (PID: 2140)
- DnsDriverInstaller.exe (PID: 2776)
- expand.exe (PID: 3900)
- expand.exe (PID: 1868)
- SangforServiceClientInstaller.exe (PID: 3864)
- HTPInstaller.exe (PID: 2212)
- SJobberInstaller.exe (PID: 2524)
- VC2010RedistX86UInstaller.exe (PID: 2144)
- SangforUpdateInstaller.exe (PID: 404)
- InstallControl.exe (PID: 2416)
- SdDriverInstaller.exe (PID: 2720)
- SangforRAppInstaller.exe (PID: 2216)
- SangforSDInstaller.exe (PID: 2476)
- VNICInstaller.exe (PID: 3016)
- vacon.exe (PID: 692)
- DrvInst.exe (PID: 2272)
- SangforECPluginInstaller.exe (PID: 3952)
- DrvInst.exe (PID: 3708)
- SsdtDriverInstaller.exe (PID: 1344)
- ECBaseInstaller.exe (PID: 3812)
- SuperServiceInstaller.exe (PID: 2400)
- ECAgentInstaller.exe (PID: 3140)
Creates files in the program directory
- EasyConnectInstaller.exe (PID: 2612)
- SangforCSClientInstaller.exe (PID: 3288)
- TcpDriverInstaller.exe (PID: 2512)
- expand.exe (PID: 3900)
- DnsDriverInstaller.exe (PID: 2776)
- expand.exe (PID: 1868)
- SangforServiceClientInstaller.exe (PID: 3864)
- SuperExeInstaller.exe (PID: 2140)
- HTPInstaller.exe (PID: 2212)
- SJobberInstaller.exe (PID: 2524)
- SangforUpdateInstaller.exe (PID: 404)
- SangforRAppInstaller.exe (PID: 2216)
- InstallControl.exe (PID: 2416)
- SangforSDInstaller.exe (PID: 2476)
- SdDriverInstaller.exe (PID: 2720)
- VNICInstaller.exe (PID: 3016)
- SangforECPluginInstaller.exe (PID: 3952)
- SsdtDriverInstaller.exe (PID: 1344)
- ECAgentInstaller.exe (PID: 3140)
- ECBaseInstaller.exe (PID: 3812)
- SuperServiceInstaller.exe (PID: 2400)
Executed as Windows Service
- spoolsv.exe (PID: 1976)
- spoolsv.exe (PID: 2536)
- vssvc.exe (PID: 456)
- rundll32.exe (PID: 2768)
- SangforPromoteService.exe (PID: 3704)
Creates files in the Windows directory
- SangforCSClientInstaller.exe (PID: 3288)
- expand.exe (PID: 3900)
- DrvInst.exe (PID: 2272)
- DrvInst.exe (PID: 3708)
- ECAgent.exe (PID: 3572)
- ECAgent.exe (PID: 2996)
Creates a software uninstall entry
- SangforCSClientInstaller.exe (PID: 3288)
- HTPInstaller.exe (PID: 2212)
- VNICInstaller.exe (PID: 3016)
Modifies the open verb of a shell class
- SangforCSClientInstaller.exe (PID: 3288)
Starts application with an unusual extension
- SuperExeInstaller.exe (PID: 2140)
- SangforServiceClientInstaller.exe (PID: 3864)
- VNICInstaller.exe (PID: 3016)
Adds / modifies Windows certificates
- vacon.exe (PID: 692)
Executed via COM
- DrvInst.exe (PID: 2272)
- DrvInst.exe (PID: 2764)
- DrvInst.exe (PID: 3708)
Creates files in the driver directory
- DrvInst.exe (PID: 2272)
- DrvInst.exe (PID: 3708)
Removes files from Windows directory
- DrvInst.exe (PID: 2272)
- DrvInst.exe (PID: 3708)
- ECAgent.exe (PID: 3572)
- ECAgent.exe (PID: 2996)
Uses NETSH.EXE for network configuration
- SetIPTime.exe (PID: 360)
Creates files in the user directory
- ECAgent.exe (PID: 3308)
- ECAgent.exe (PID: 2912)
INFO
Dropped object may contain Bitcoin addresses
- SangforSDInstaller.exe (PID: 2476)
Searches for installed software
- DrvInst.exe (PID: 2272)
Low-level read access rights to disk partition
- vssvc.exe (PID: 456)
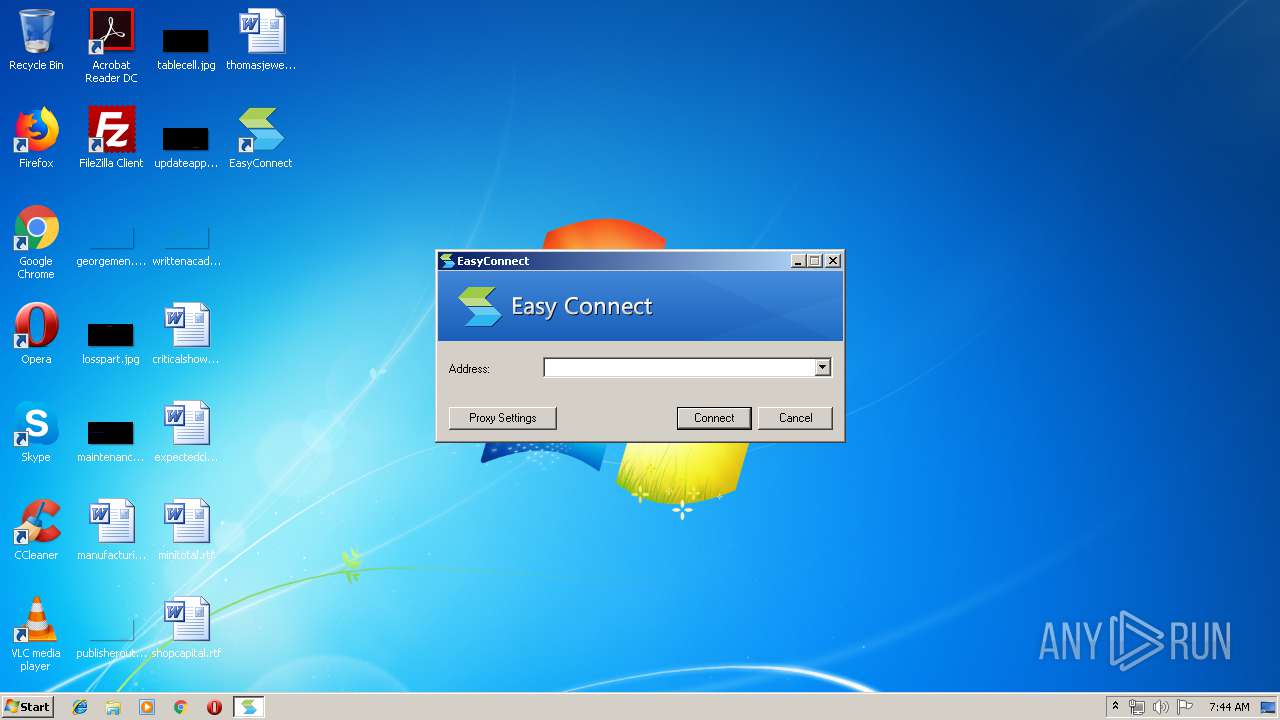
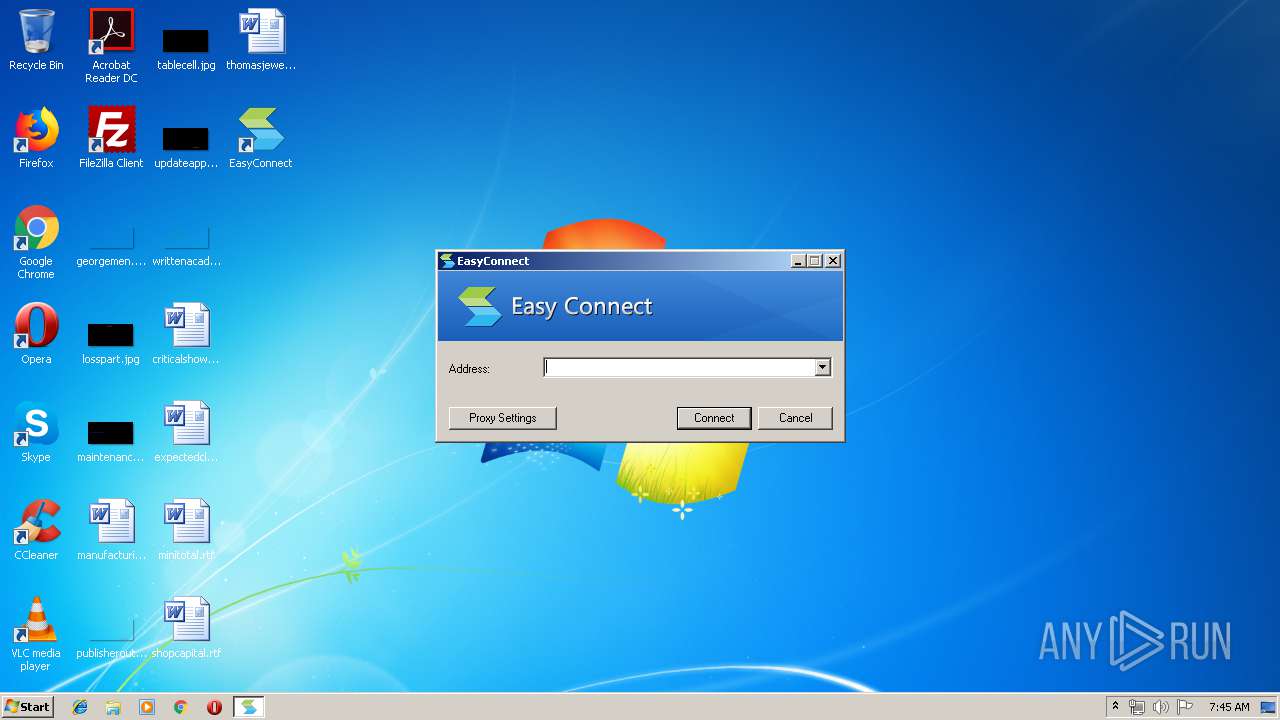
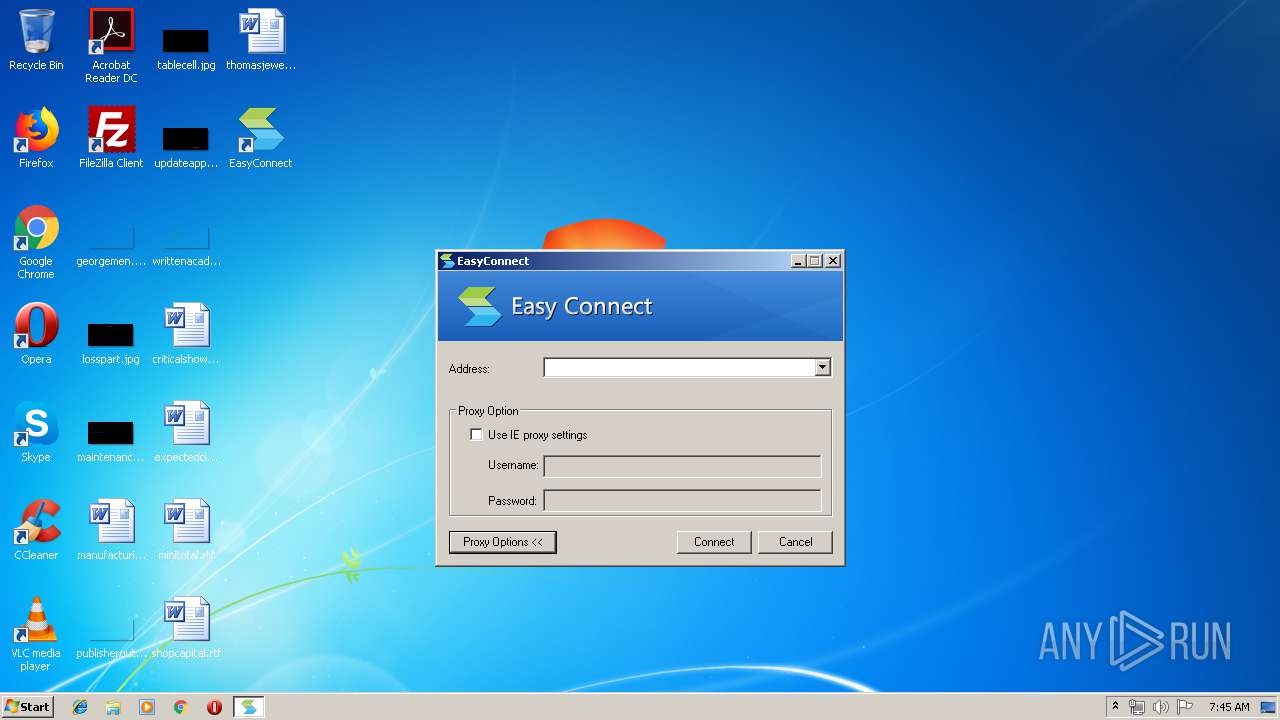
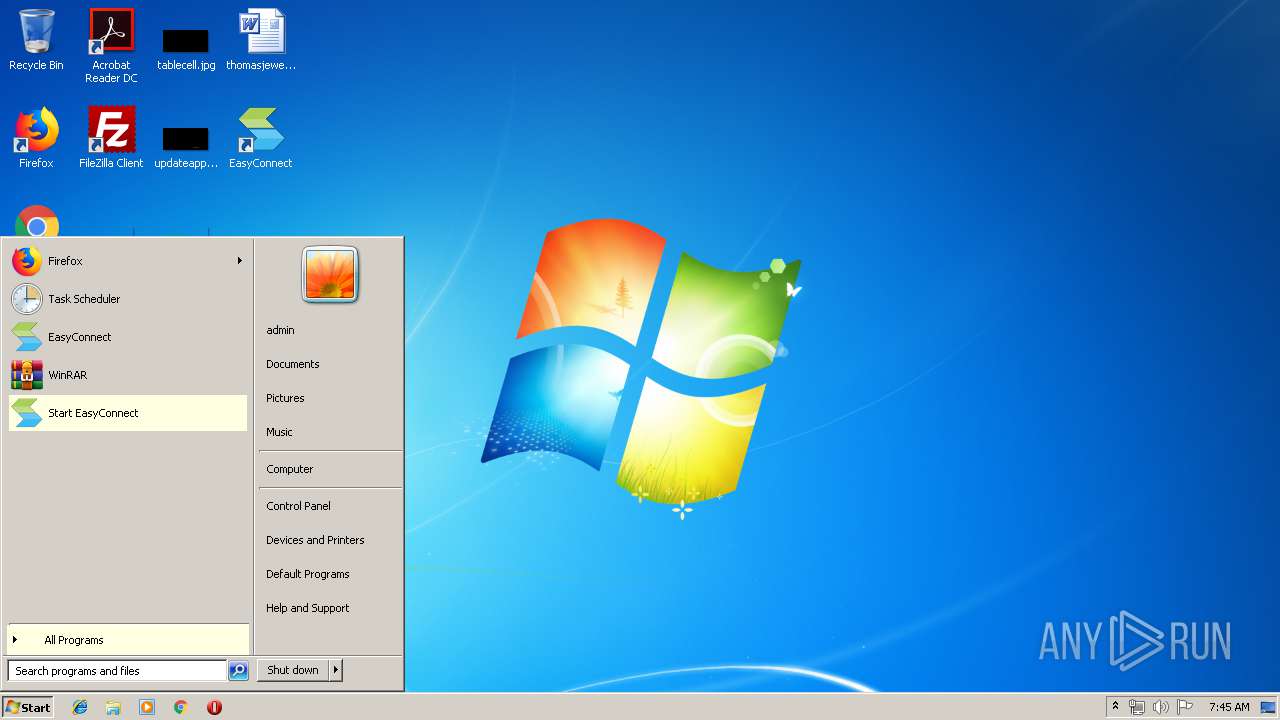
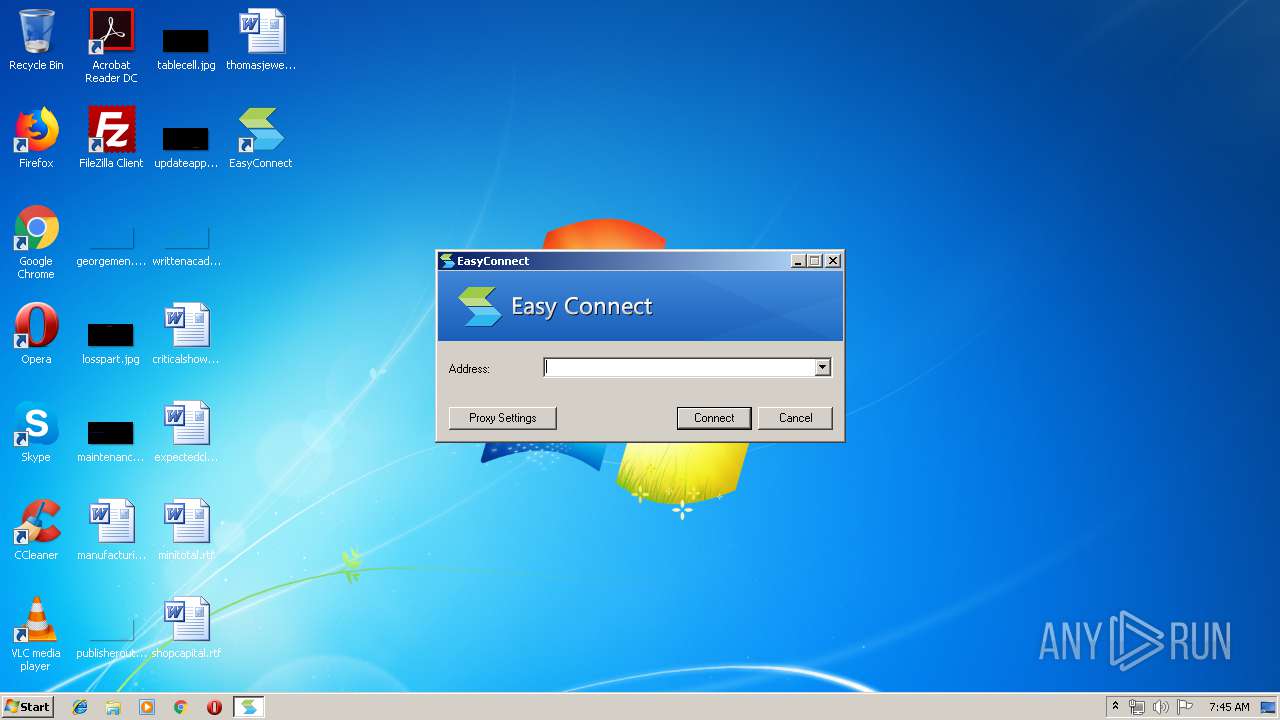
Manual execution by user
- SangforCSClient.exe (PID: 4016)
- SangforCSClient.exe (PID: 1520)
- SangforCSClient.exe (PID: 2320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:53:18+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 124928 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x36a0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:53:18 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:53:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000061A4 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44297 |
.rdata | 0x00008000 | 0x000011E0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.3067 |
.data | 0x0000A000 | 0x0001C3F8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1303 |
.ndata | 0x00027000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00035000 | 0x0001A1F0 | 0x0001A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.89431 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.87125 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 4.32403 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.57732 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 4.76878 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 5.09933 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.93166 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73119 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.74597 | 408 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
102
Monitored processes
62
Malicious processes
27
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Sangfor\SSL\CSClient\VNIC\SetIPTime.exe" | C:\Program Files\Sangfor\SSL\CSClient\VNIC\SetIPTime.exe | — | nsAA53.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Sangfor\SSL\ClientComponent\SangforUpdateInstaller.exe" | C:\Program Files\Sangfor\SSL\ClientComponent\SangforUpdateInstaller.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 456 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Program Files\Sangfor\SSL\CSClient\VNIC\vacon.exe" install "C:\Program Files\Sangfor\SSL\CSClient\VNIC\SangforCertificate.cer" "C:\Program Files\Sangfor\SSL\CSClient\VNIC\SangforVNIC.inf" SangforVNIC | C:\Program Files\Sangfor\SSL\CSClient\VNIC\vacon.exe | ns55AA.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | C:\Windows\system32\svchost.exe -k LocalService | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | C:\Windows\system32\svchost.exe -k LocalServiceNoNetwork | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Sangfor\SSL\ClientComponent\SsdtDriverInstaller.exe" | C:\Program Files\Sangfor\SSL\ClientComponent\SsdtDriverInstaller.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1436 | "C:\Users\admin\AppData\Local\Temp\EasyConnectInstaller.exe" | C:\Users\admin\AppData\Local\Temp\EasyConnectInstaller.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Sangfor\SSL\SangforCSClient\SangforCSClient.exe" /ShortCutAutoLogin | C:\Program Files\Sangfor\SSL\SangforCSClient\SangforCSClient.exe | explorer.exe | ||||||||||||
User: admin Company: Sangfor Technologies Co.,Ltd Integrity Level: MEDIUM Description: EasyConnect Exit code: 0 Version: 7, 1, 0, 4 Modules
| |||||||||||||||
Total events
3 504
Read events
1 463
Write events
1 762
Delete events
279
Modification events
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum |
| Operation: | write | Name: | _ObjectId_ |
Value: D600000000000000 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceClasses |
| Operation: | write | Name: | ObjectId |
Value: D600000000000000 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceClasses |
| Operation: | write | Name: | ObjectLru |
Value: BA03000000000000 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum |
| Operation: | write | Name: | _ObjectLru_ |
Value: BA03000000000000 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum |
| Operation: | write | Name: | _FileId_ |
Value: 94CA000000000B00 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum |
| Operation: | write | Name: | _Usn_ |
Value: 00873E0300000000 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum |
| Operation: | write | Name: | _UsnJournalId_ |
Value: CAF752A8FD3DD301 | |||
| (PID) Process: | (852) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class |
| Operation: | write | Name: | B00000000CA94 |
Value: 94CA000000000B00 | |||
| (PID) Process: | (2612) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CSClientManagerPrj.CSClientManager.1 |
| Operation: | write | Name: | |
Value: CSClientManager Class | |||
| (PID) Process: | (2612) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CSClientManagerPrj.CSClientManager.1\CLSID |
| Operation: | write | Name: | |
Value: {F257CF85-8E97-4C9B-8407-459B28007109} | |||
Executable files
152
Suspicious files
26
Text files
261
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2612 | EasyConnectInstaller.exe | C:\Program Files\Sangfor\SSL\ClientComponent\nd_dkey_v2.CAB | compressed | |
MD5:— | SHA256:— | |||
| 2612 | EasyConnectInstaller.exe | C:\Program Files\Sangfor\SSL\ClientComponent\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 2612 | EasyConnectInstaller.exe | C:\Program Files\Sangfor\SSL\ClientComponent\nd_dkey_v2_win8.CAB | compressed | |
MD5:— | SHA256:— | |||
| 2612 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsuB12.tmp\SkinBtn.dll | executable | |
MD5:E4EC95271FF1BCEBAB49BDFED6817A22 | SHA256:EE1C06692A757473737B0EBDEF16F77B63AFAC864D0890022D905E4873737DD6 | |||
| 2612 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsuB12.tmp\progress_b.bmp | image | |
MD5:CE4078C76F01007446659836BE211AE8 | SHA256:DB95A500F6971AA753F670DD5779F1E92F89AE471DDF8061E9A0D06FE0D7987A | |||
| 2612 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsuB12.tmp\btn_mini.bmp | image | |
MD5:89F661E7046201913DCA29B752148B70 | SHA256:08A09B319267BB46BCD9A25D9F154A9F4285CFF781D196D88CC77609E685B554 | |||
| 2612 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsuB12.tmp\btn_finish_cn.bmp | image | |
MD5:71607B1DD8E735196DBED039BDBAEAF5 | SHA256:5E36F3A5686695A302F2B1066069119C0374DE7D31093153F716DD40EE18BD48 | |||
| 2612 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsuB12.tmp\SkinProgress.dll | executable | |
MD5:CC037C4703D3EC257EFEEF2CE0A1A20E | SHA256:888B32ECBC37CE67D4EDC28D894CBA0A4F4E2488CFC2212D1AF011BD0BFE97FF | |||
| 2612 | EasyConnectInstaller.exe | C:\Program Files\Sangfor\SSL\ClientComponent\InstallControl.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
EasyConnectInstaller.exe | [SangforNsp] [GetCurOsVersion] Ver = 6.1
|
EasyConnectInstaller.exe | [SangforNsp] [LoadSangforPrinterDll] Enter |
EasyConnectInstaller.exe | [SangforNsp] InstallNspIn2000 NspNum=8 |
EasyConnectInstaller.exe | [SangforNsp] [RestartSpooler] RestartSpoolerThread begin! |
EasyConnectInstaller.exe | [SangforNsp] [RestartSpooler] begin to stop spoolsv service! |
EasyConnectInstaller.exe | [SangforNsp] [RestartSpoolerThread] waitting service stop , current state = 3 |
EasyConnectInstaller.exe | [SangforNsp] [RestartSpoolerThread] service has stopped! |
EasyConnectInstaller.exe | [SangforNsp] [RestartSpooler] stop spoolsv service success! |
EasyConnectInstaller.exe | [SangforNsp] [RestartSpooler] start spoolsv service success! |
EasyConnectInstaller.exe | CSProxy refcount 1
|