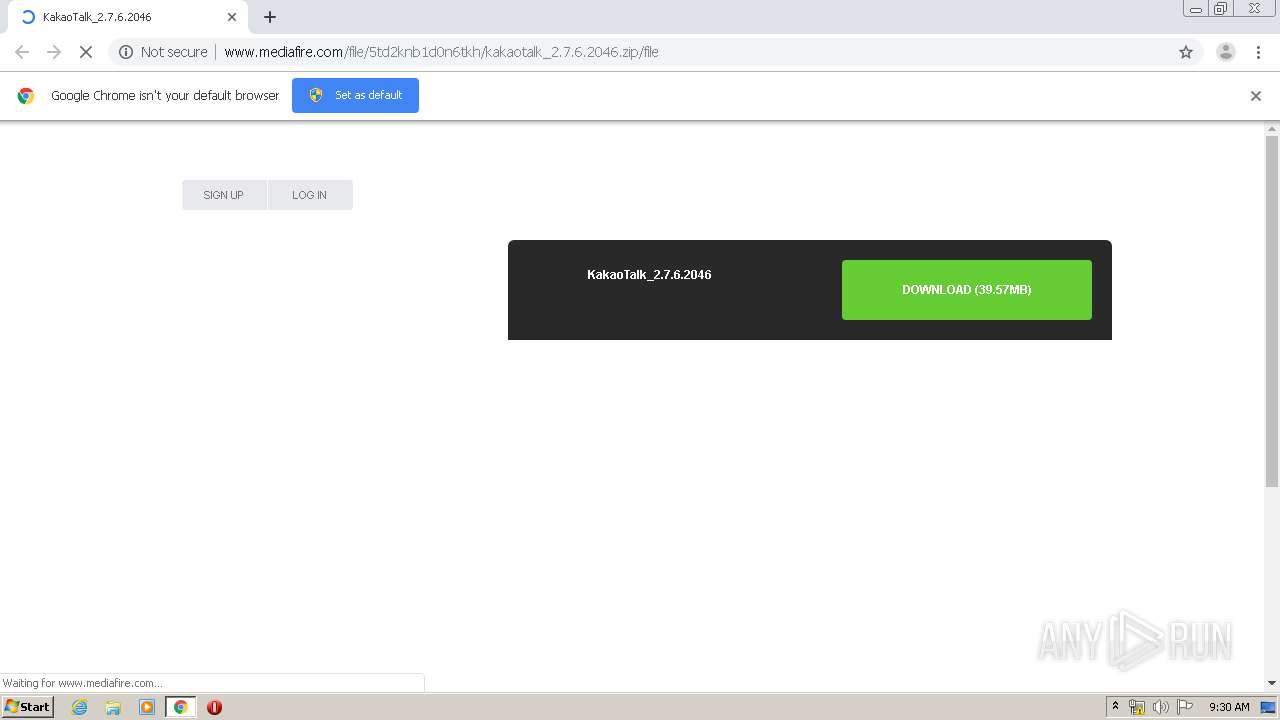
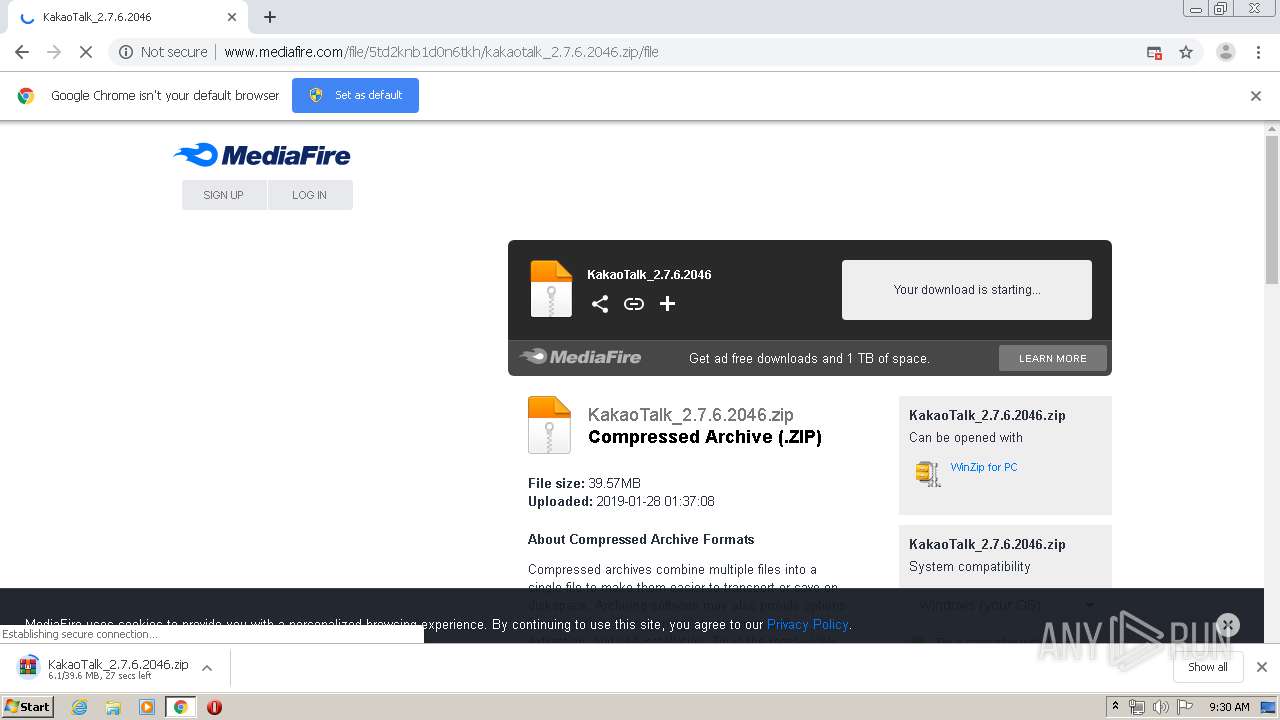
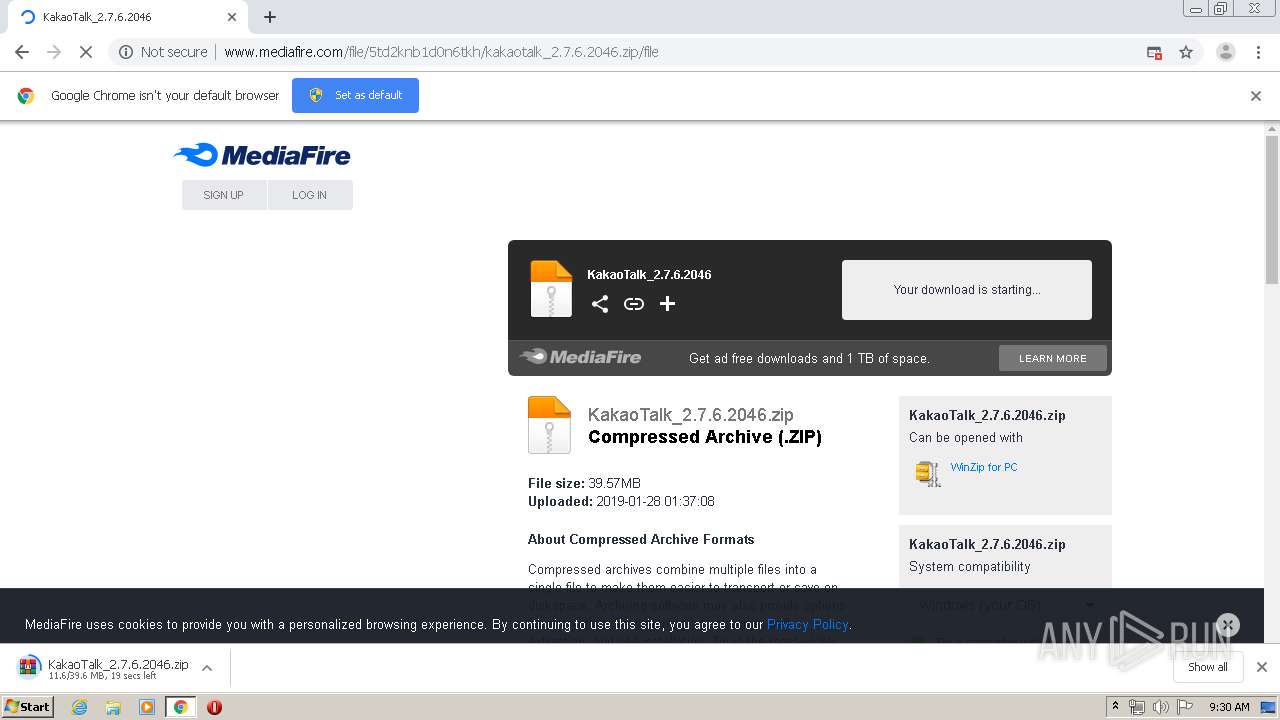
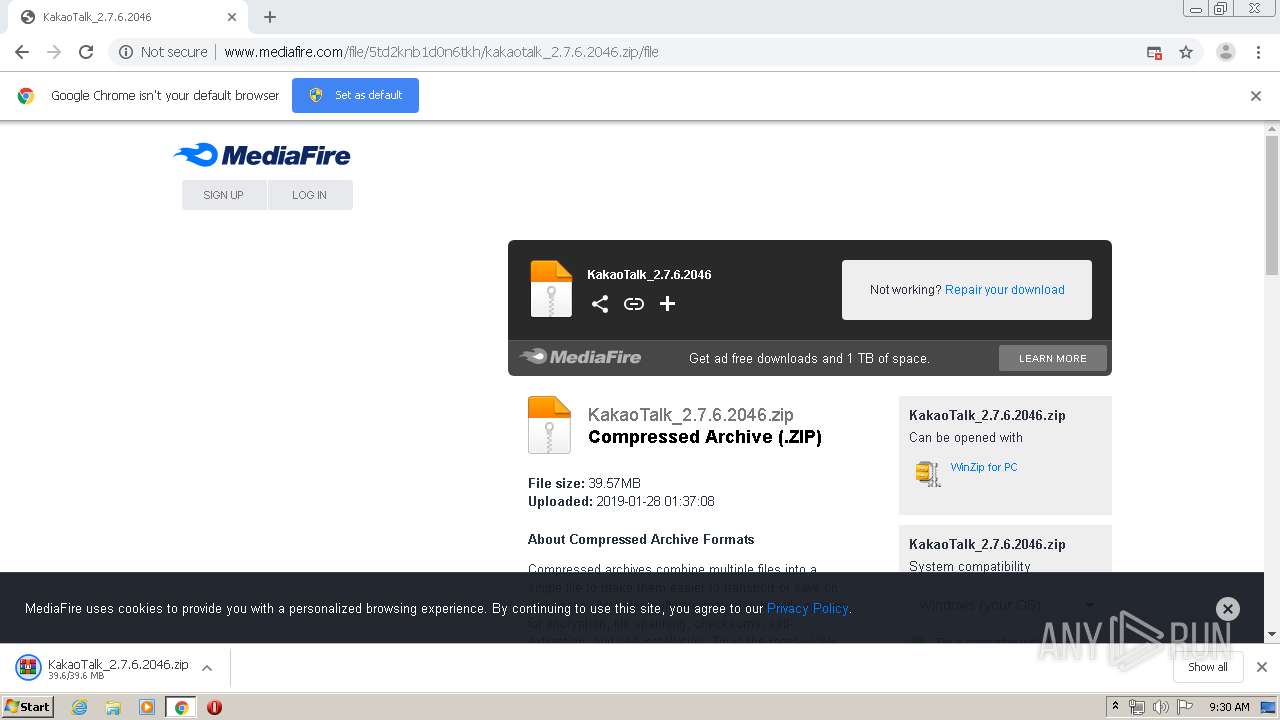
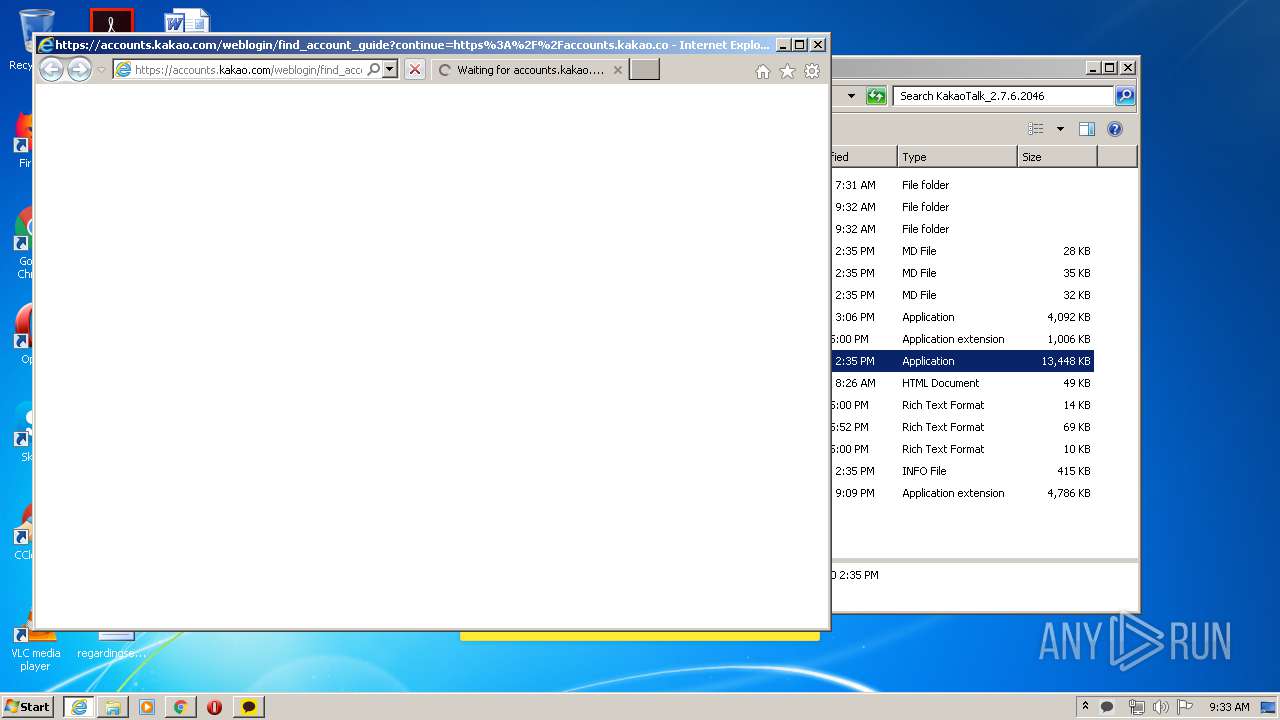
| URL: | http://www.mediafire.com/file/5td2knb1d0n6tkh/kakaotalk_2.7.6.2046.zip/file |
| Full analysis: | https://app.any.run/tasks/3a3a31c1-9924-40f0-a91d-f9e4fddc91d8 |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2020, 08:29:38 |
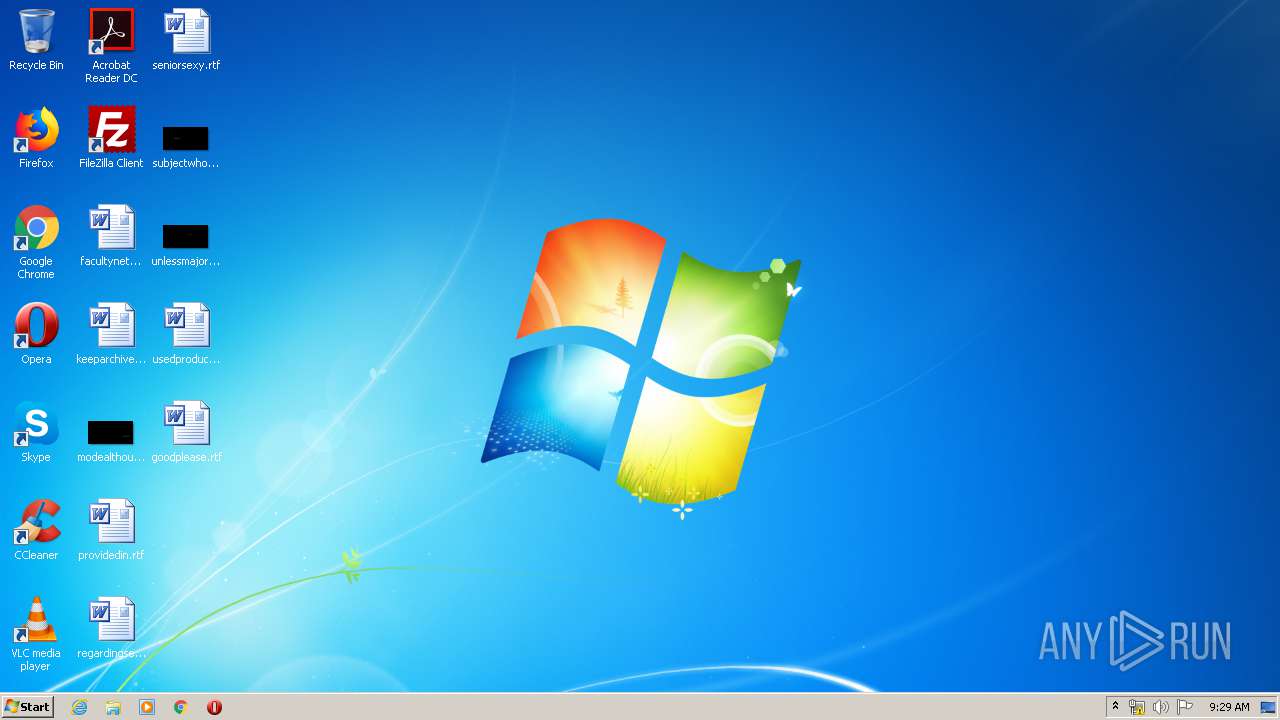
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 03366867F8F3D7630A18F6B3CE0BC55A |
| SHA1: | 79A4B1030AF7BF7612E2359D27A24681865F6853 |
| SHA256: | 7FE9E4577D3C53E305DA13C6F813FA9FB11297A381DDBC4A6637C5A8ED4C5B0C |
| SSDEEP: | 3:N1KJS4w3eGUoQnXkmP6RTj9:Cc4w3eGcjCz |
MALICIOUS
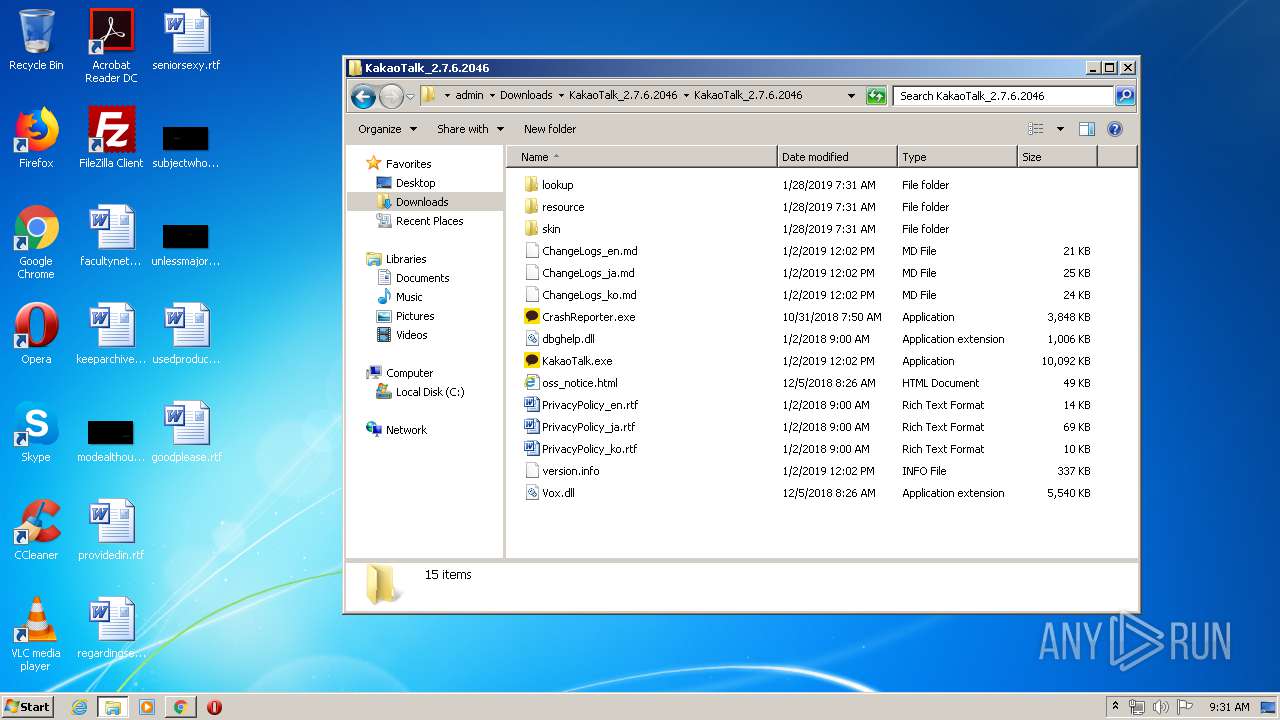
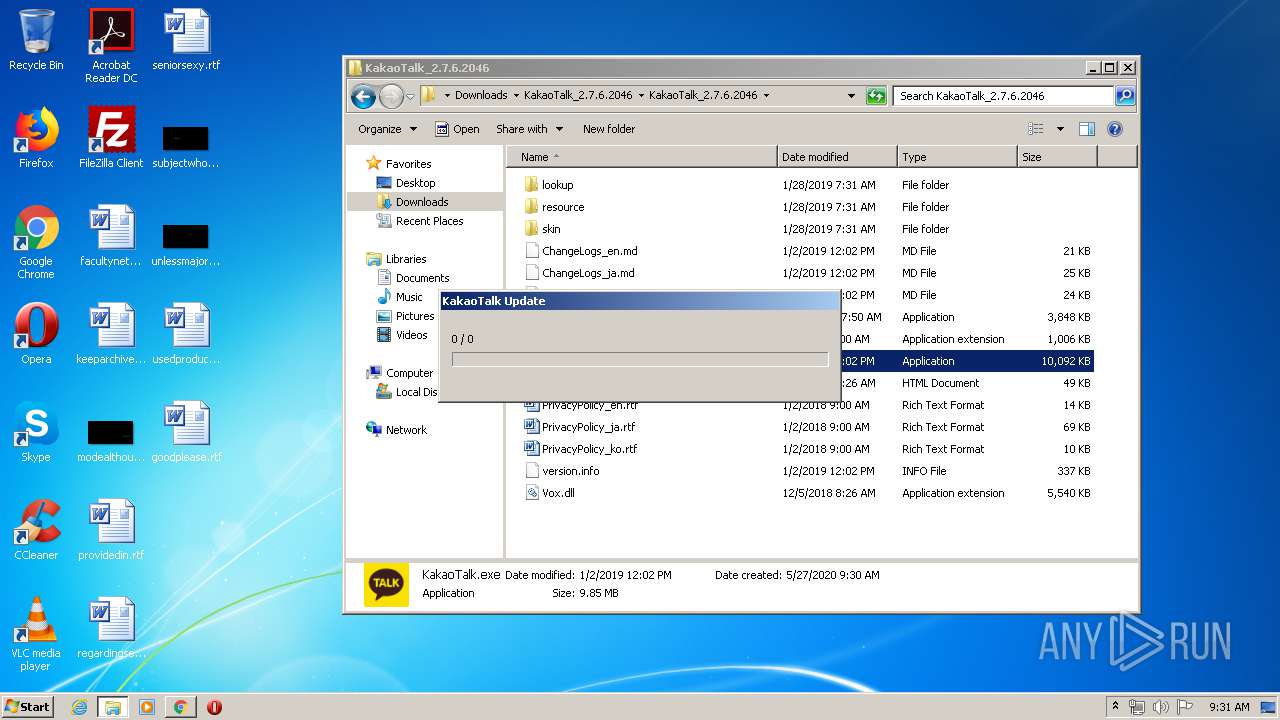
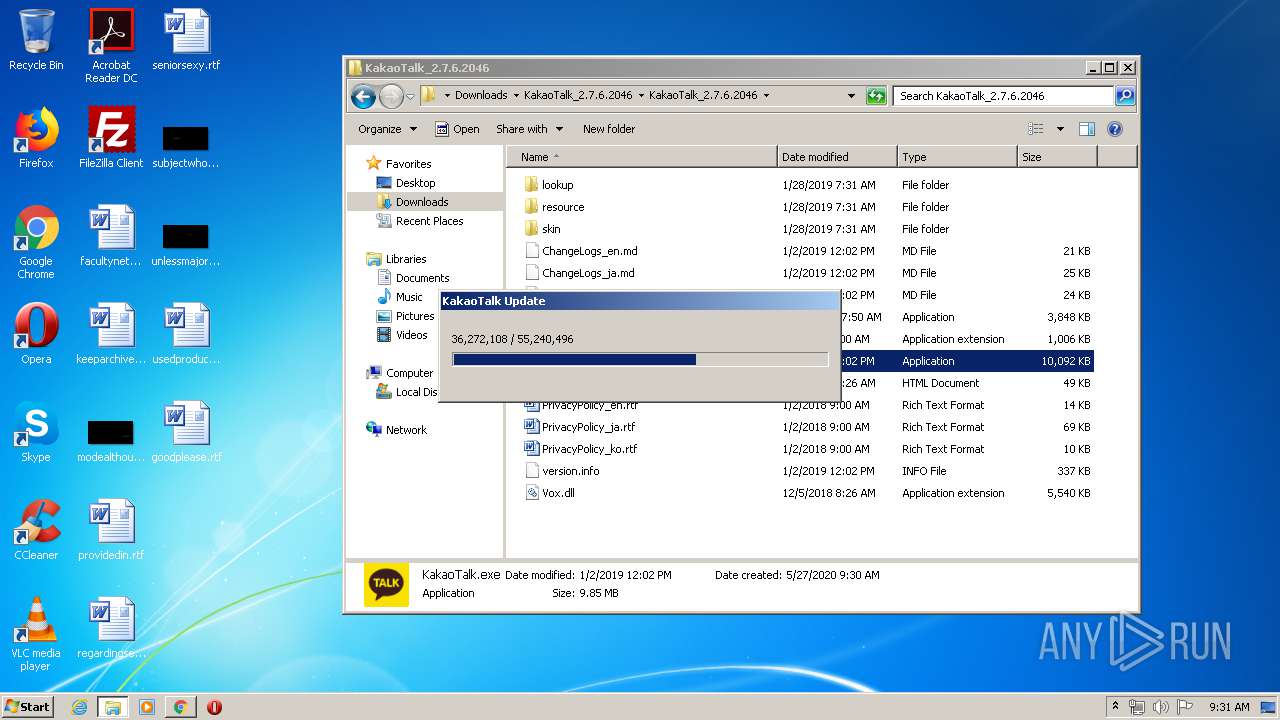
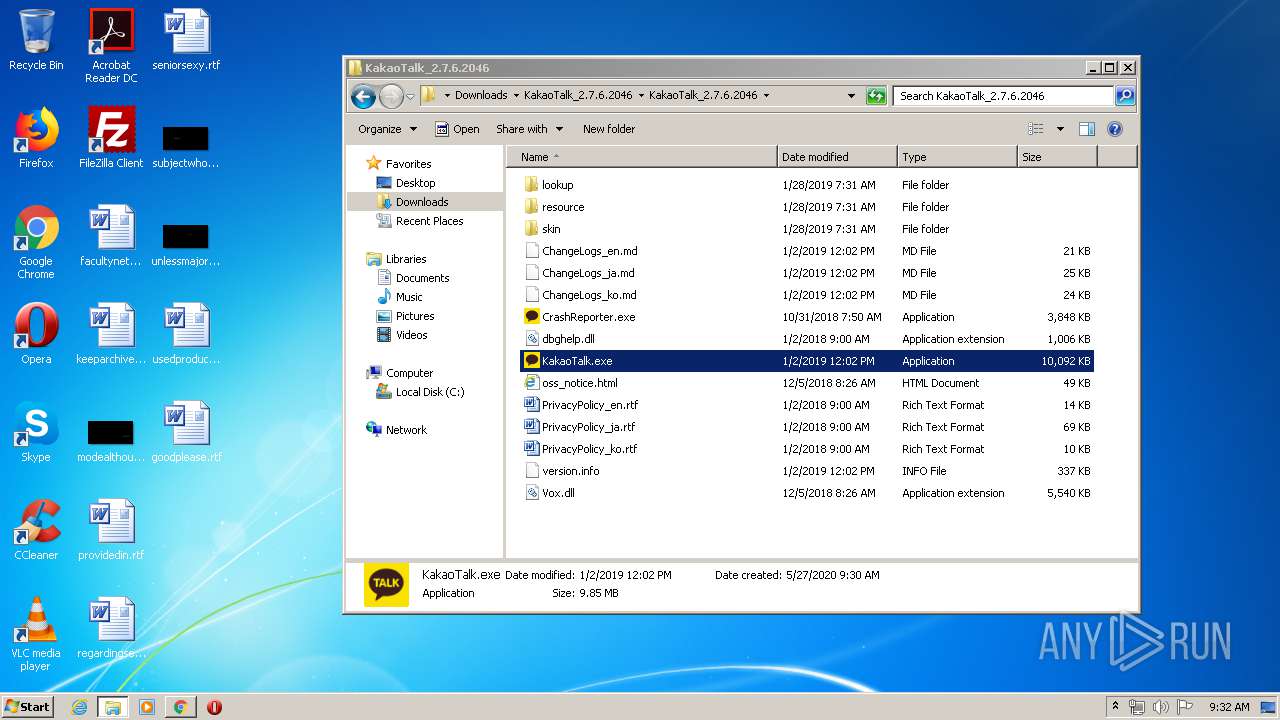
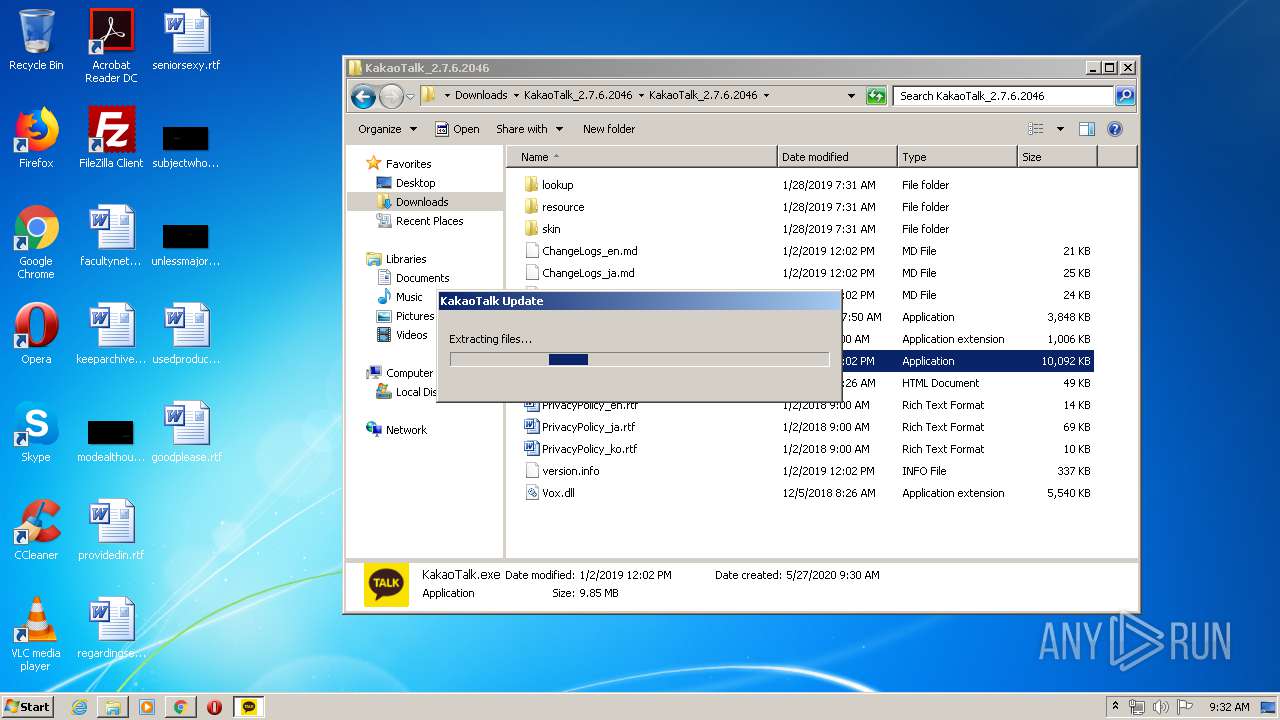
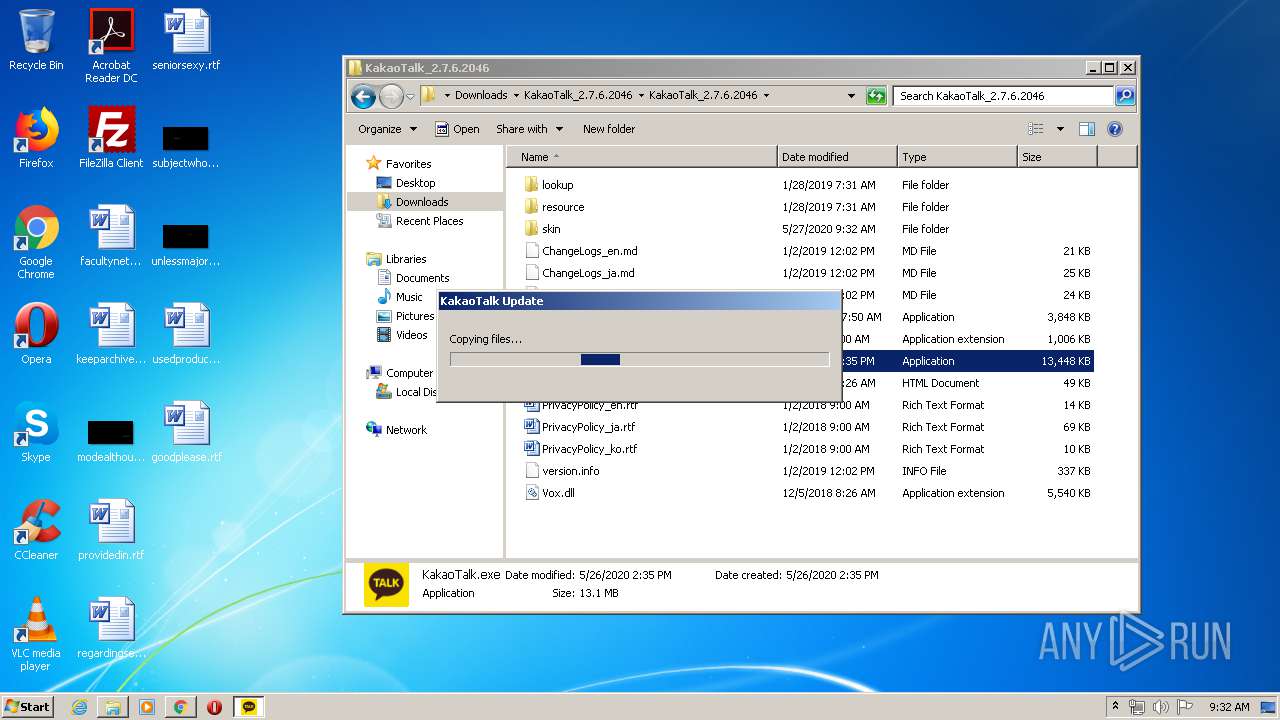
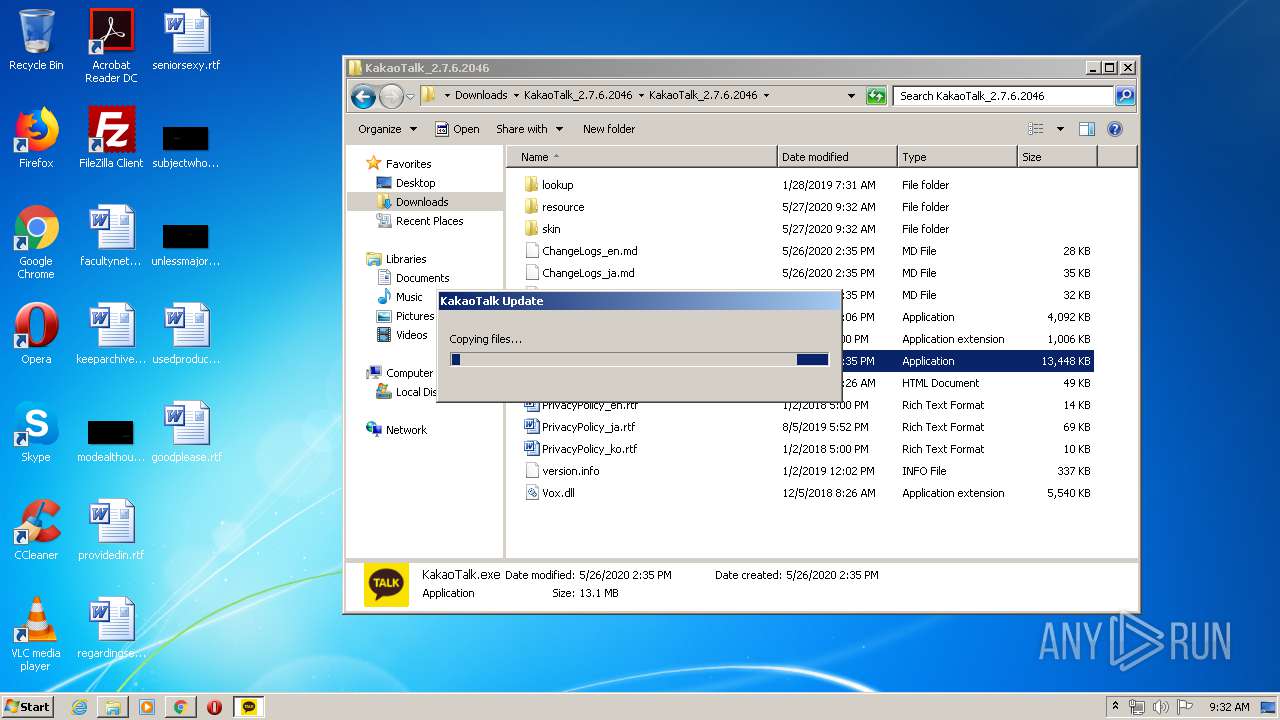
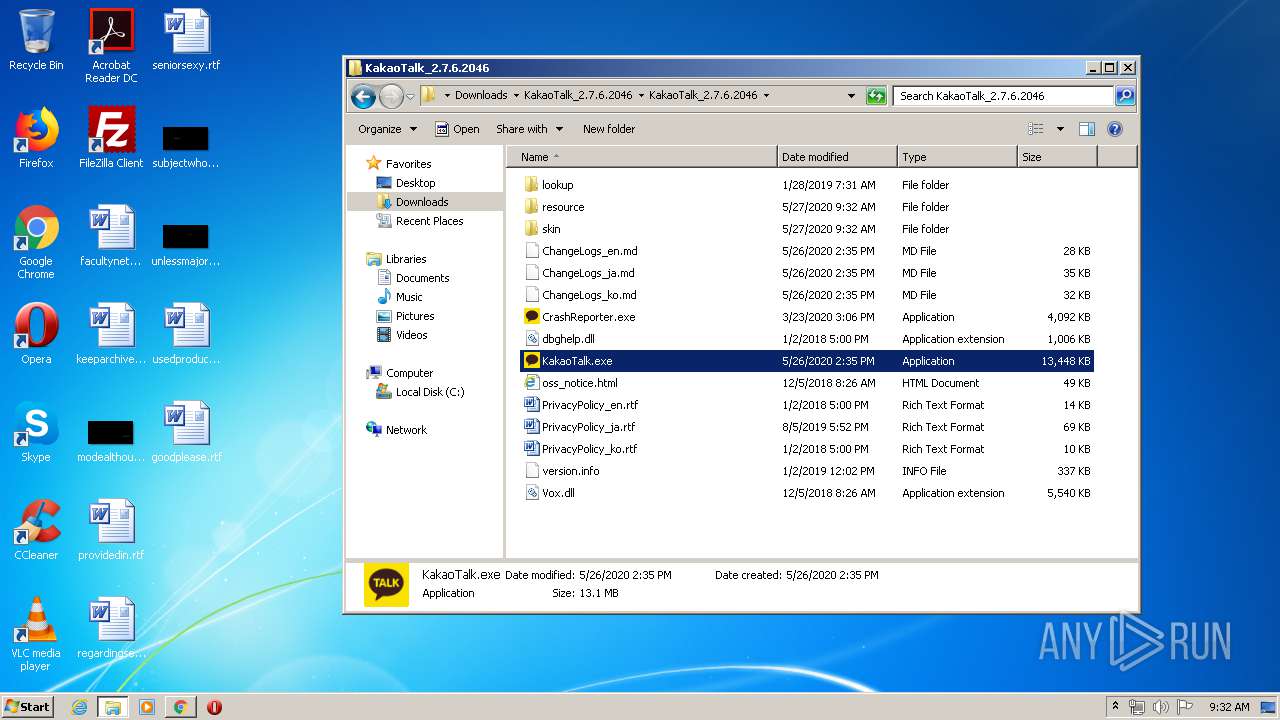
Application was dropped or rewritten from another process
- KakaoTalk.exe (PID: 3116)
- KakaoUpdate.exe (PID: 2992)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3436)
- KakaoTalk.exe (PID: 3116)
Changes the autorun value in the registry
- KakaoTalk.exe (PID: 3116)
Downloads executable files from the Internet
- KakaoTalk.exe (PID: 3116)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1728)
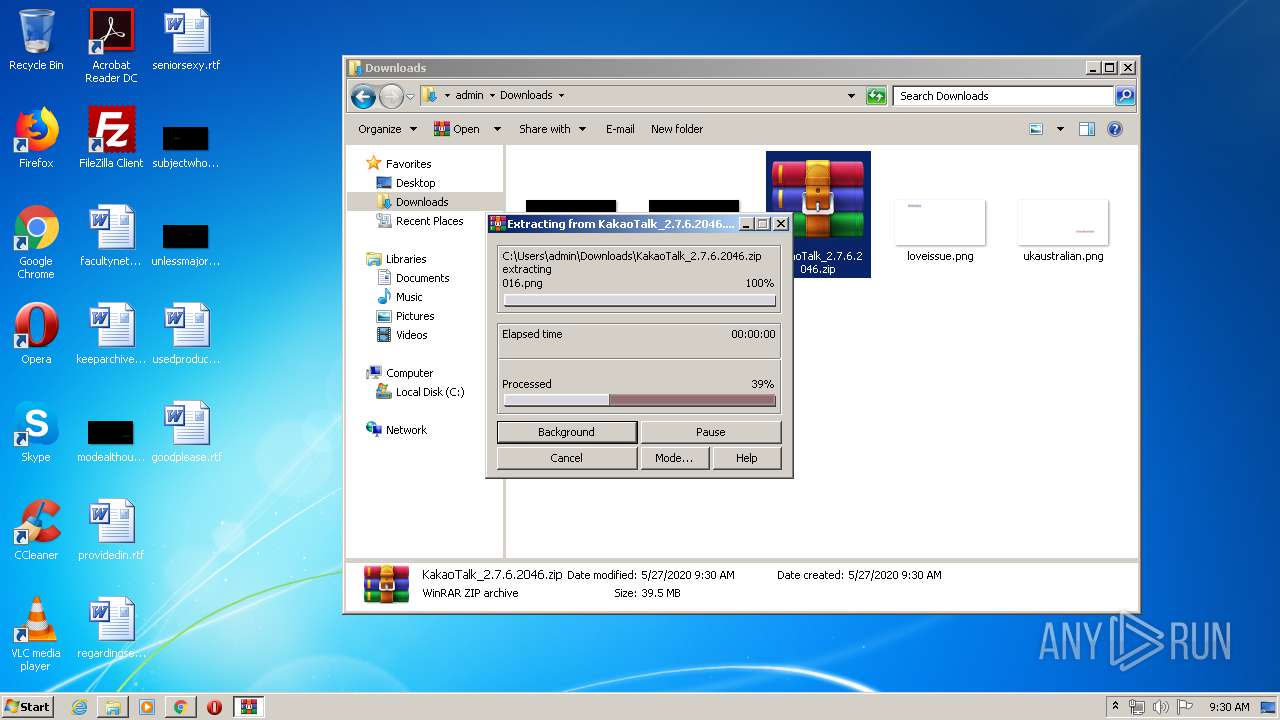
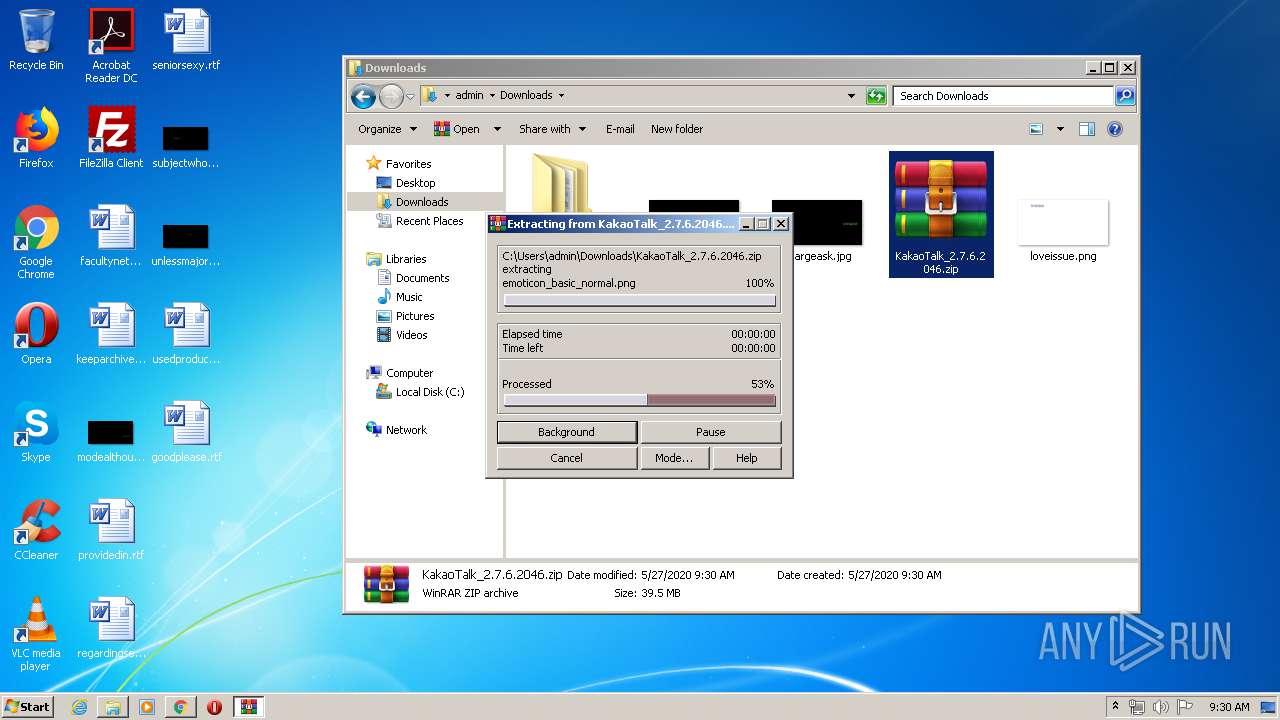
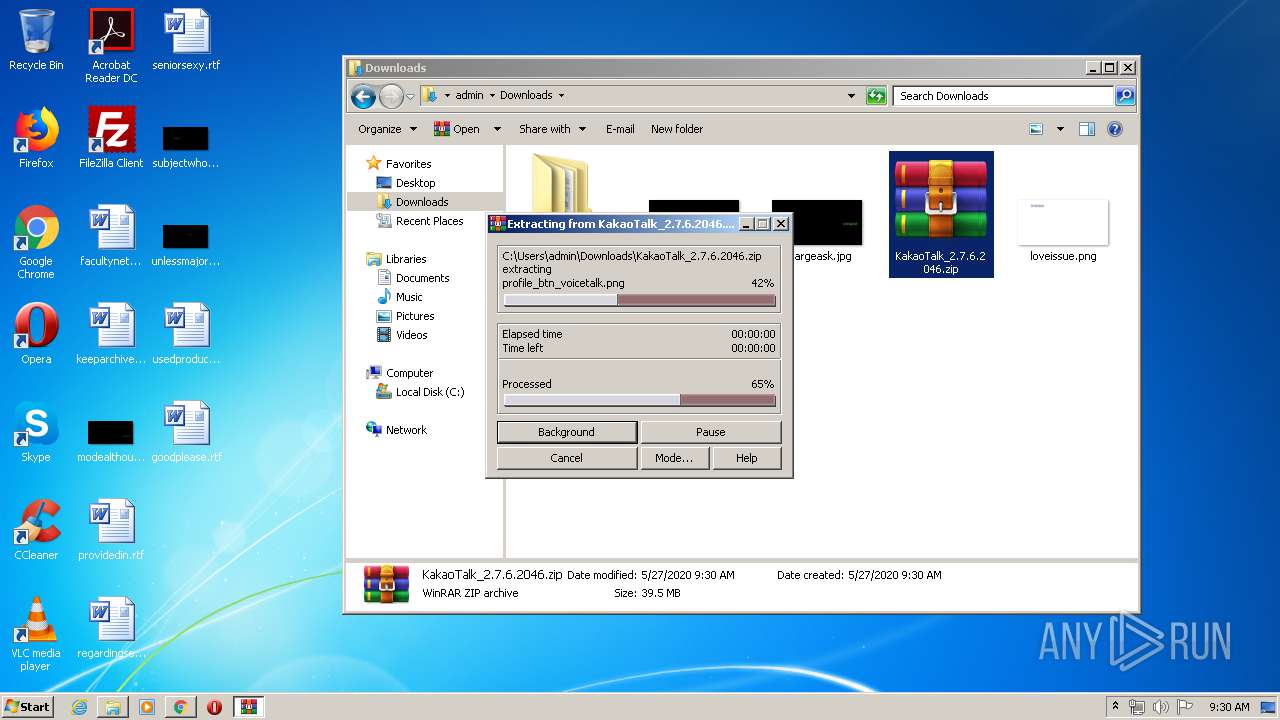
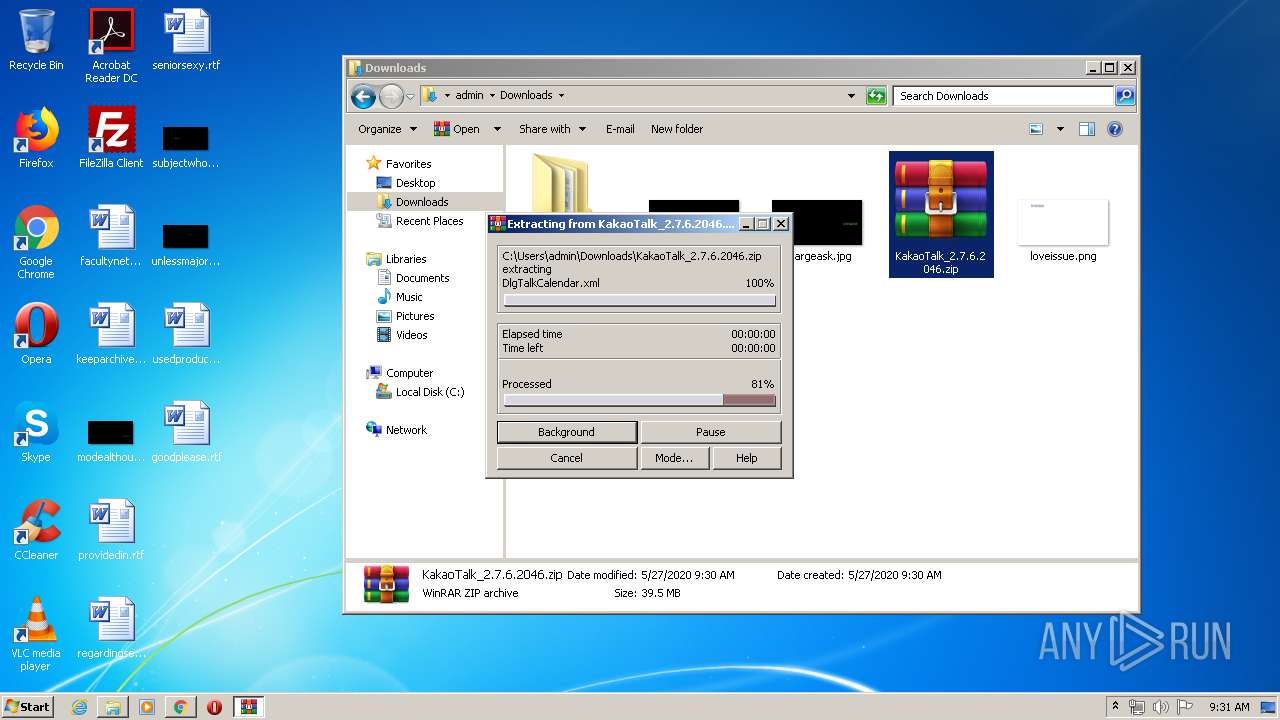
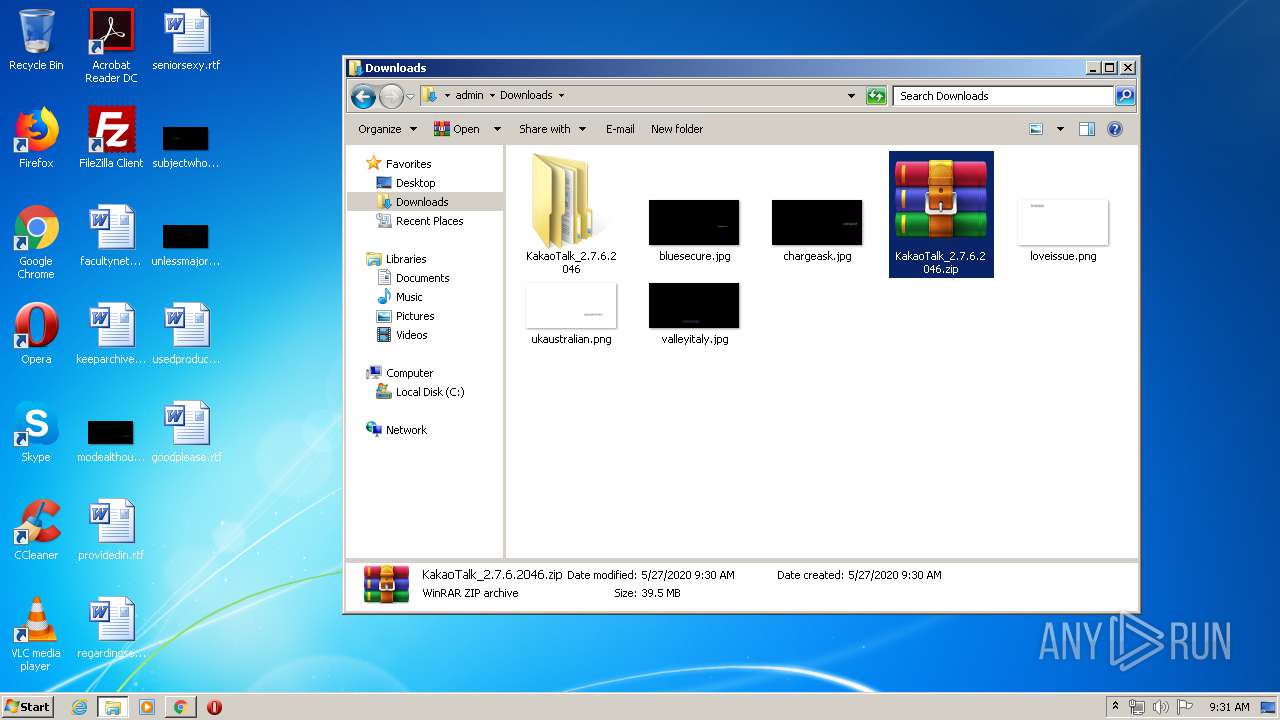
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2496)
- KakaoTalk.exe (PID: 3116)
- KakaoUpdate.exe (PID: 2992)
Modifies the open verb of a shell class
- KakaoUpdate.exe (PID: 2992)
INFO
Application launched itself
- chrome.exe (PID: 1728)
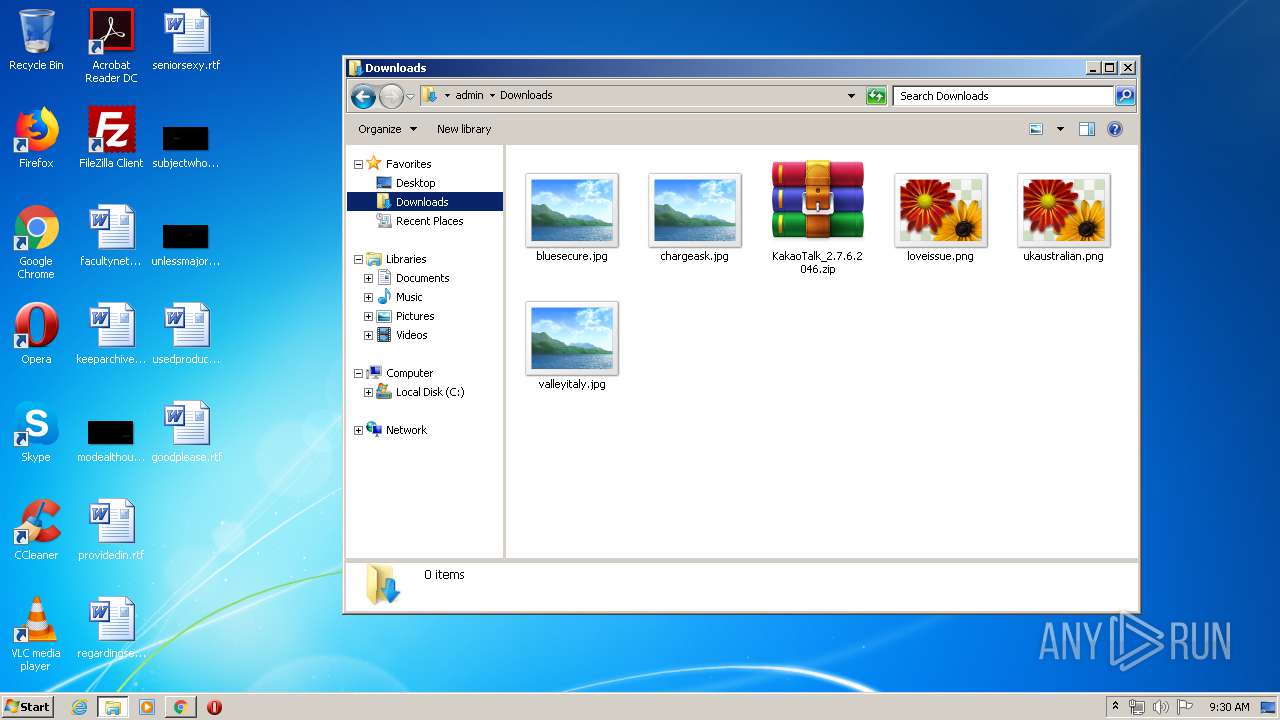
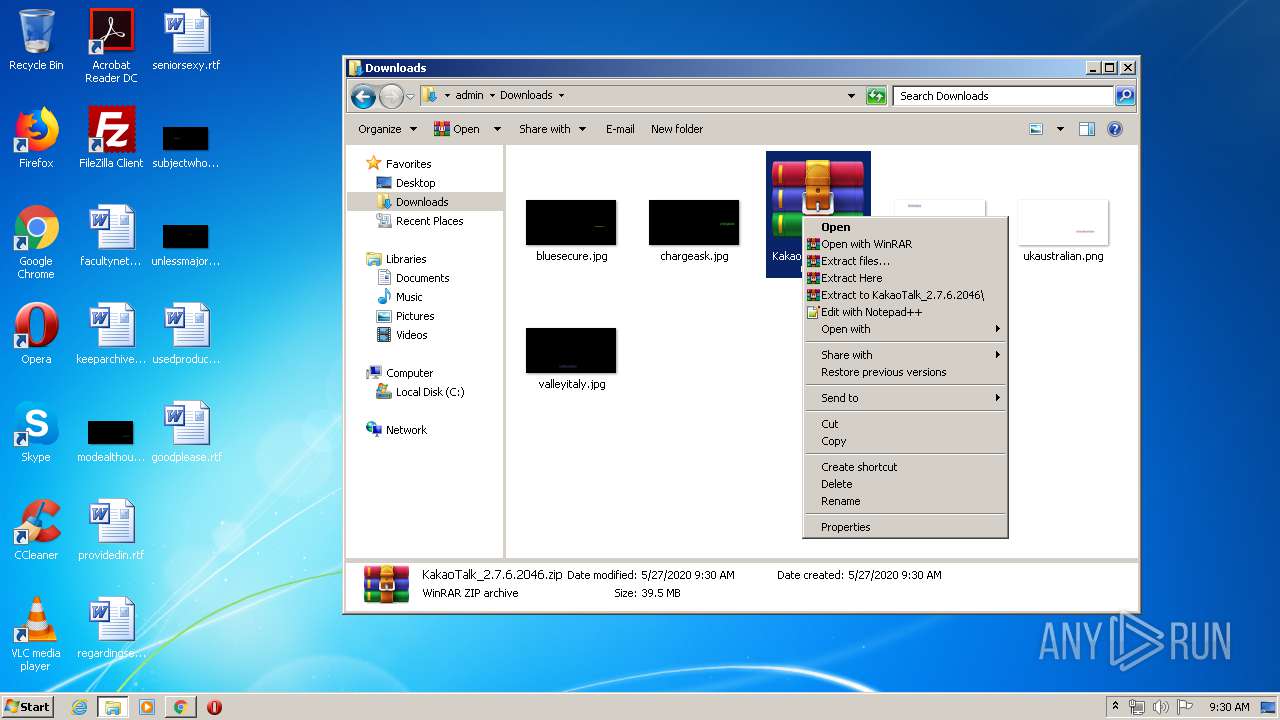
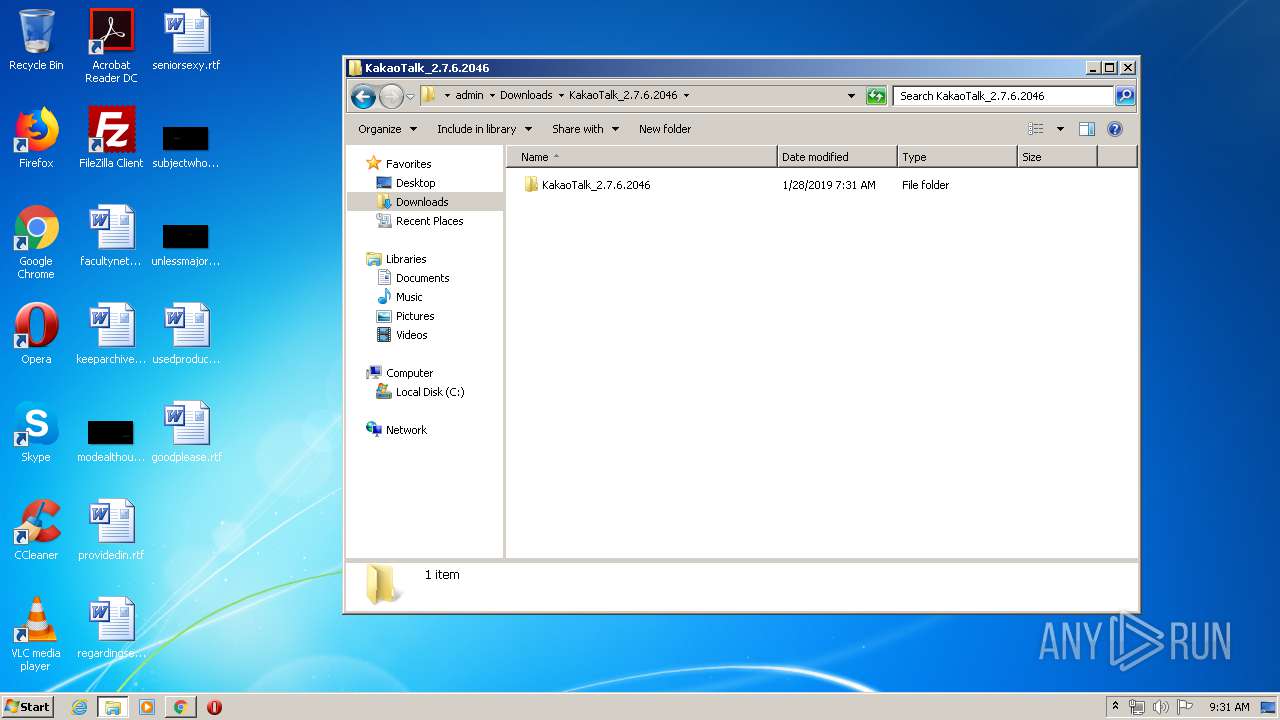
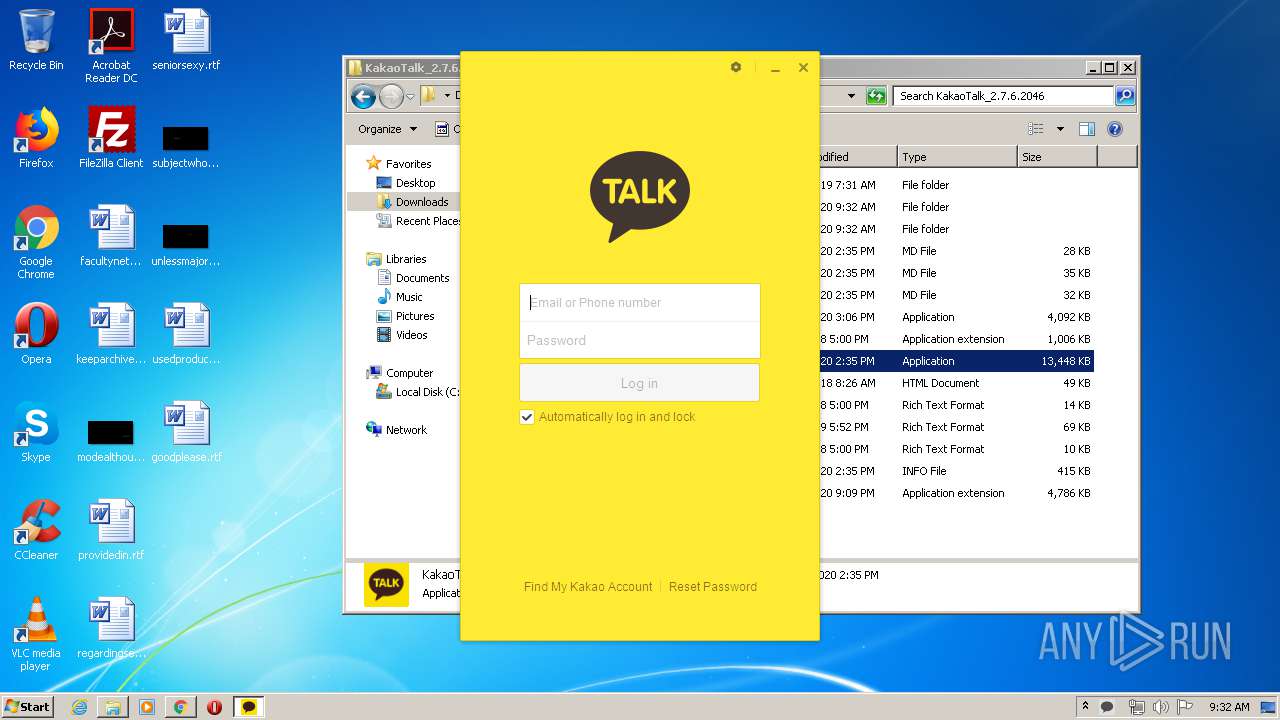
Manual execution by user
- WinRAR.exe (PID: 2496)
- explorer.exe (PID: 2568)
- KakaoTalk.exe (PID: 3116)
Reads the hosts file
- chrome.exe (PID: 3924)
- chrome.exe (PID: 1728)
Reads Internet Cache Settings
- chrome.exe (PID: 1728)
Changes settings of System certificates
- chrome.exe (PID: 3924)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2496)
- KakaoUpdate.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
64
Malicious processes
3
Suspicious processes
0
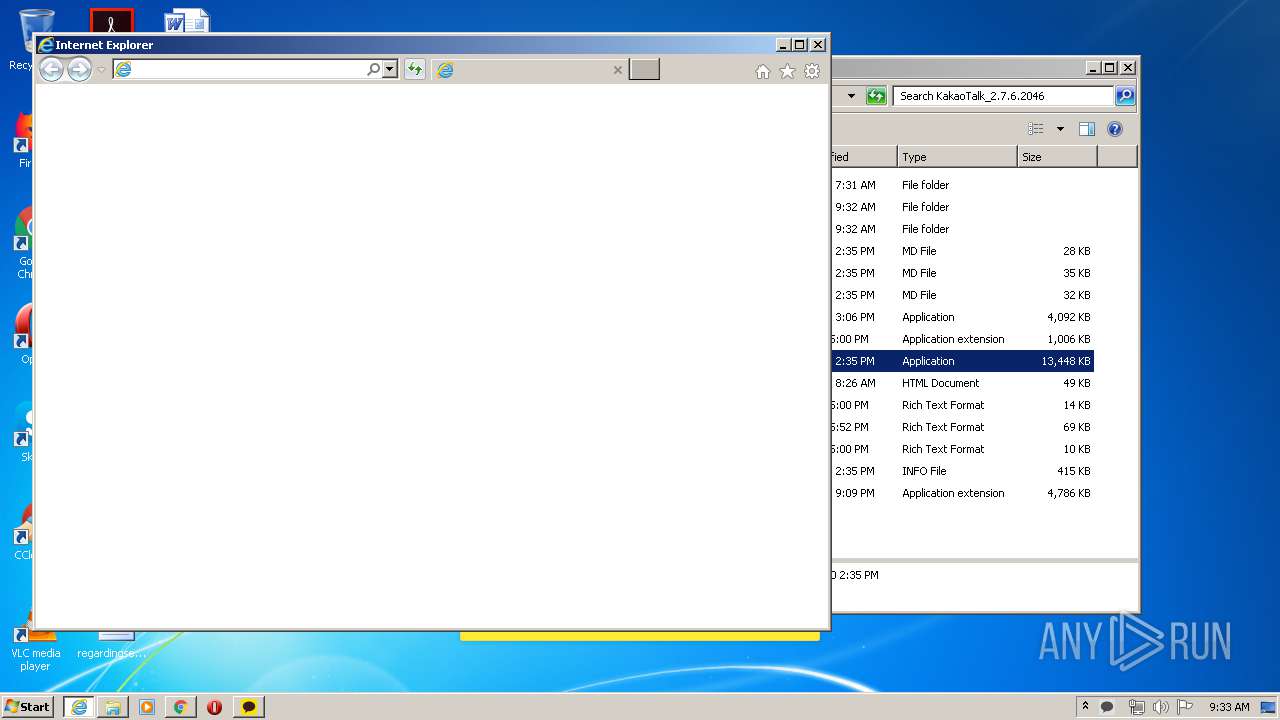
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8047055267680910153 --mojo-platform-channel-handle=5800 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2977767202626598563 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14469322650584210820 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18331483151818237907 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15884762155439239616 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3811853711370015958 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1680 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15949386988592424615 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,10195414826940631520,10000966325232185224,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8877314615552732006 --renderer-client-id=54 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.mediafire.com/file/5td2knb1d0n6tkh/kakaotalk_2.7.6.2046.zip/file" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 837
Read events
1 679
Write events
153
Delete events
5
Modification events
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1112) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1728-13235041794525000 |
Value: 259 | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1728) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
12
Suspicious files
856
Text files
10 703
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ECE2503-6C0.pma | — | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b6483b41-163b-4bda-9b90-bd8a80a30207.tmp | — | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF106469.TMP | text | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF106469.TMP | text | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1066ab.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
158
DNS requests
109
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3924 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
3924 | chrome.exe | GET | — | 199.91.153.86:80 | http://download1839.mediafire.com/yum13nw2q4hg/5td2knb1d0n6tkh/KakaoTalk_2.7.6.2046.zip | US | — | — | suspicious |
3924 | chrome.exe | GET | — | 162.252.214.5:80 | http://adsco.re/p | US | — | — | whitelisted |
3924 | chrome.exe | GET | 200 | 216.58.206.14:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 797 b | whitelisted |
3924 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
3924 | chrome.exe | POST | 200 | 162.252.214.5:80 | http://adsco.re/p | US | text | 132 b | whitelisted |
3924 | chrome.exe | GET | 200 | 104.17.167.186:80 | http://c.adsco.re/ | US | html | 12.6 Kb | whitelisted |
3924 | chrome.exe | GET | 304 | 104.17.167.186:80 | http://c.adsco.re/ | US | compressed | 12.6 Kb | whitelisted |
3924 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/icons/svg_dark/check_circle_green.svg | US | image | 300 b | shared |
3924 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/images/icons/svg_dark/arrow_dropdown.svg | US | image | 250 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3924 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3924 | chrome.exe | 2.20.168.110:443 | c.aaxads.com | Akamai Technologies, Inc. | — | unknown |
3924 | chrome.exe | 216.58.206.14:80 | translate.google.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 172.217.23.162:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
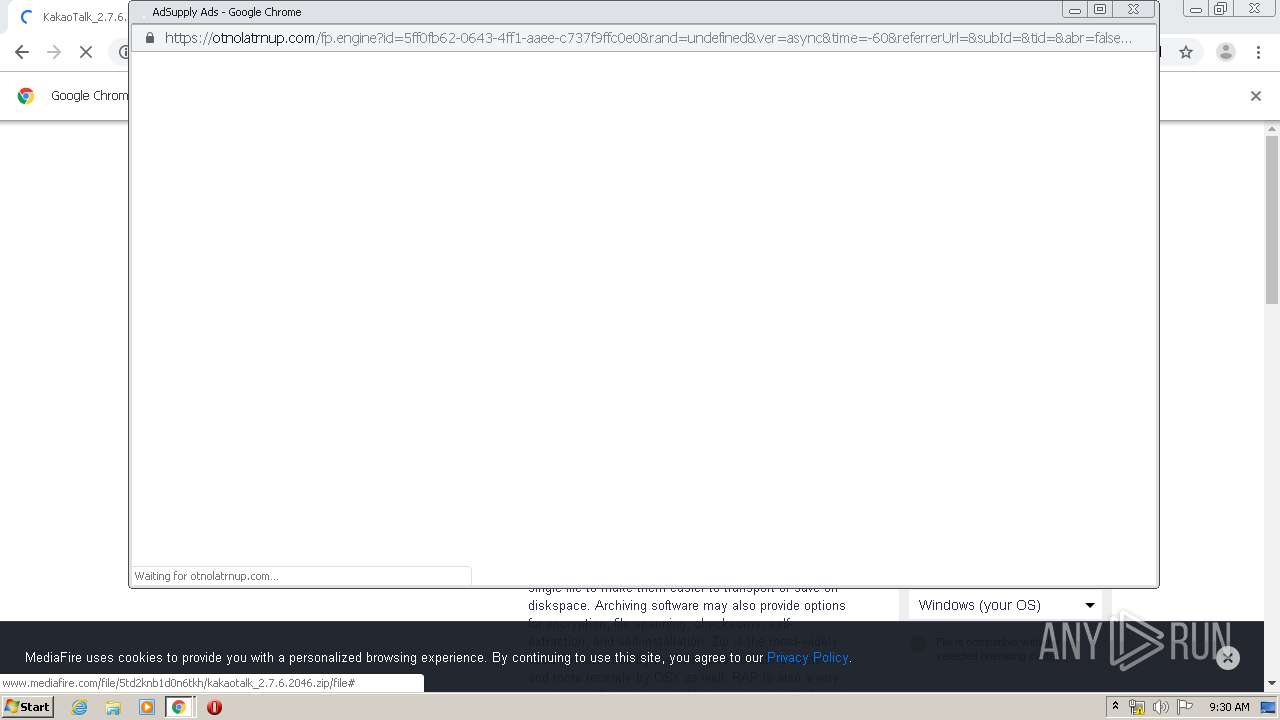
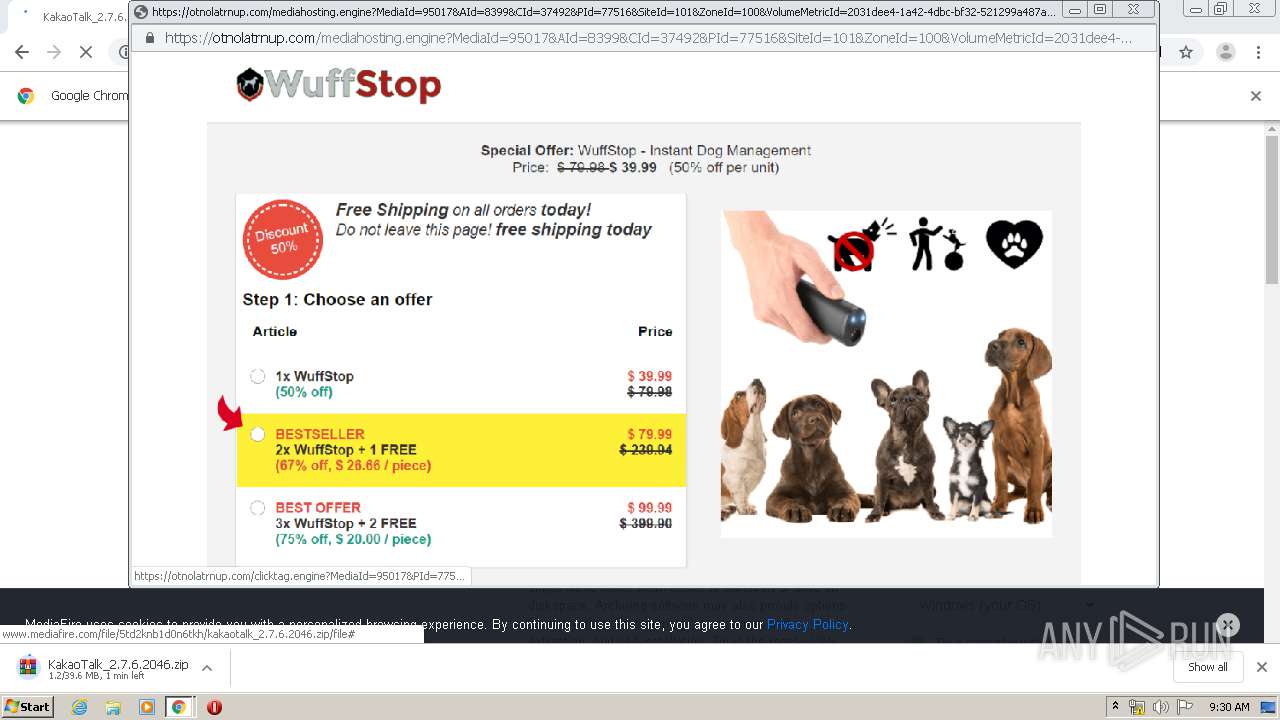
3924 | chrome.exe | 104.19.214.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
3924 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 172.217.22.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.mediafire.com |
| shared |
facebook.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3924 | chrome.exe | Misc Attack | ET DROP Dshield Block Listed Source group 1 |
3924 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3924 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3924 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3116 | KakaoTalk.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |