| File name: | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb |
| Full analysis: | https://app.any.run/tasks/3a3221a0-21e8-48a3-a9e2-0b6e1aae02bb |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2019, 08:20:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | 02BA1C44B6392F013A7AA0B91314F45A |
| SHA1: | 724C1977101ECAE88E4F104A8422B64BFEC01A98 |
| SHA256: | 7FBE59195F5F6F45C8B38B12488A169FDCB3A272004DBAF44C9D92A60A3690CB |
| SSDEEP: | 24576:4AmTUWOc8w79cO634s6zyG2fzjTrqVHqOx:4B/OBVloswV2LjHzOx |
MALICIOUS
Application was dropped or rewritten from another process
- detect_x86.exe (PID: 2156)
- curl_x86.exe (PID: 3088)
- detect_x86.exe (PID: 2276)
- detect_x86.exe (PID: 2748)
- detect_x86.exe (PID: 2492)
- detect_x86.exe (PID: 2980)
- curl_x86.exe (PID: 2996)
- aes_x86.exe (PID: 3736)
SUSPICIOUS
Starts SC.EXE for service management
- 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe (PID: 3424)
Executable content was dropped or overwritten
- 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe (PID: 3424)
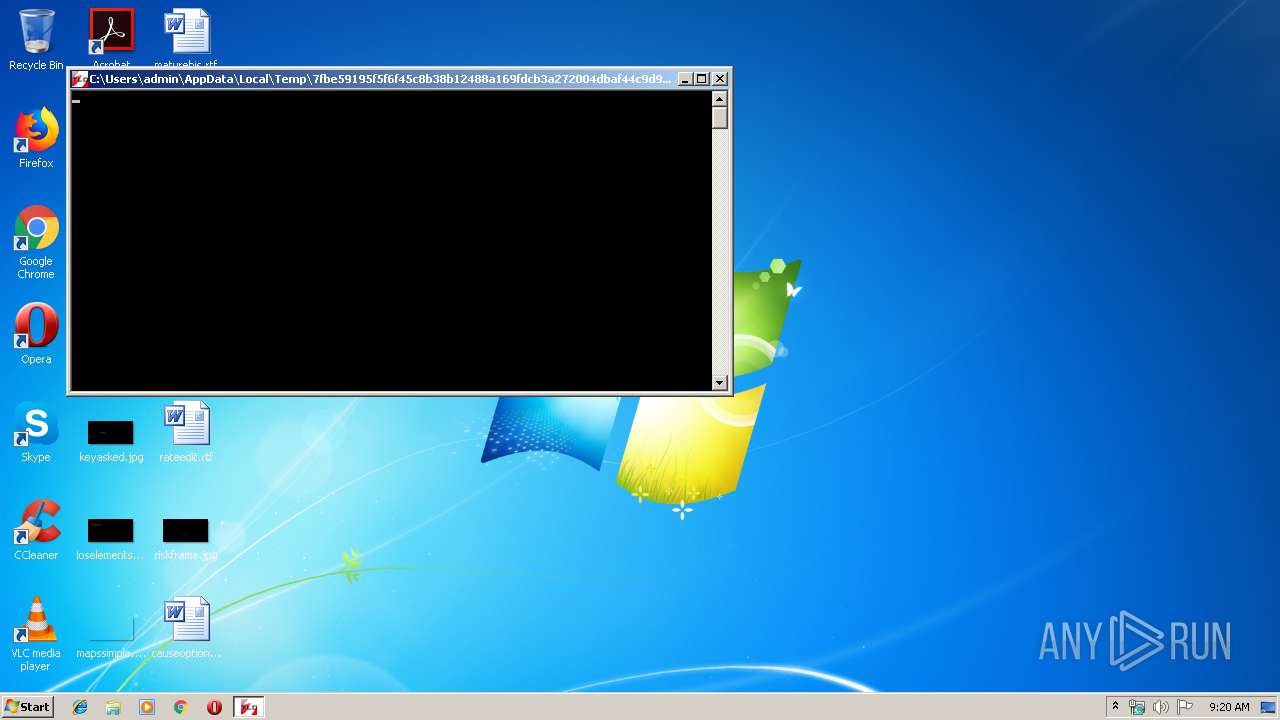
Starts CMD.EXE for commands execution
- 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe (PID: 3424)
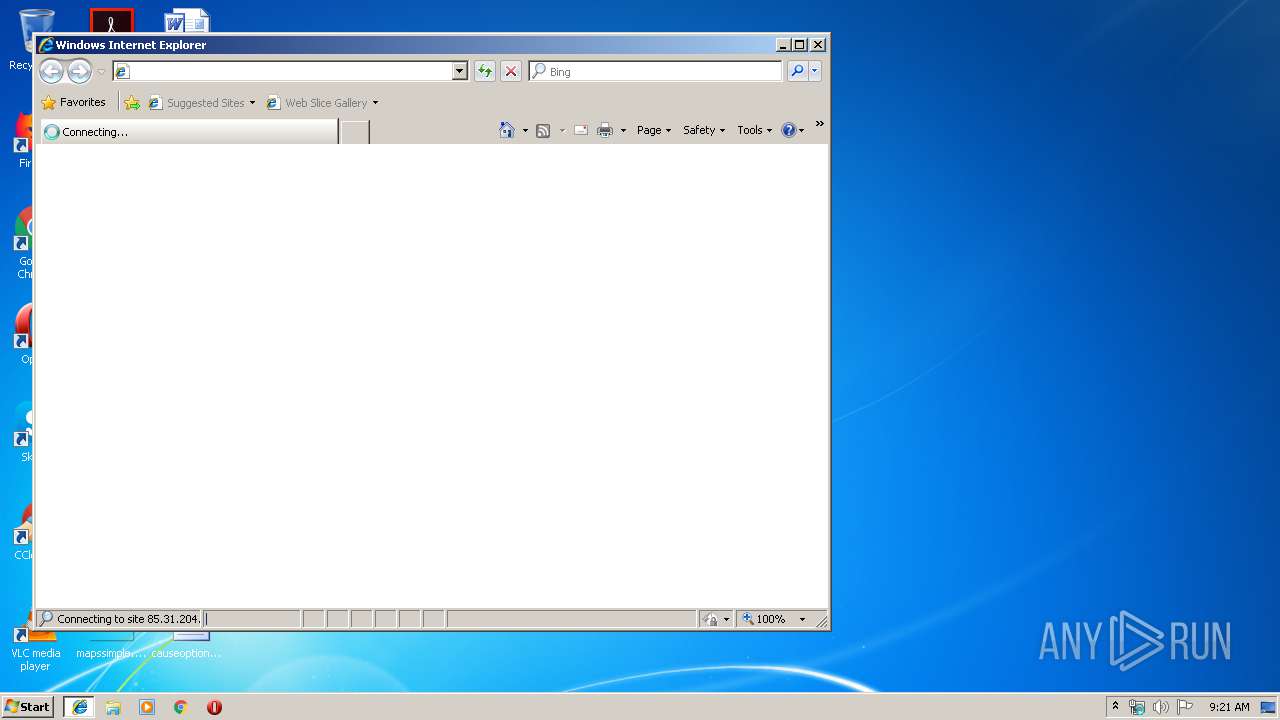
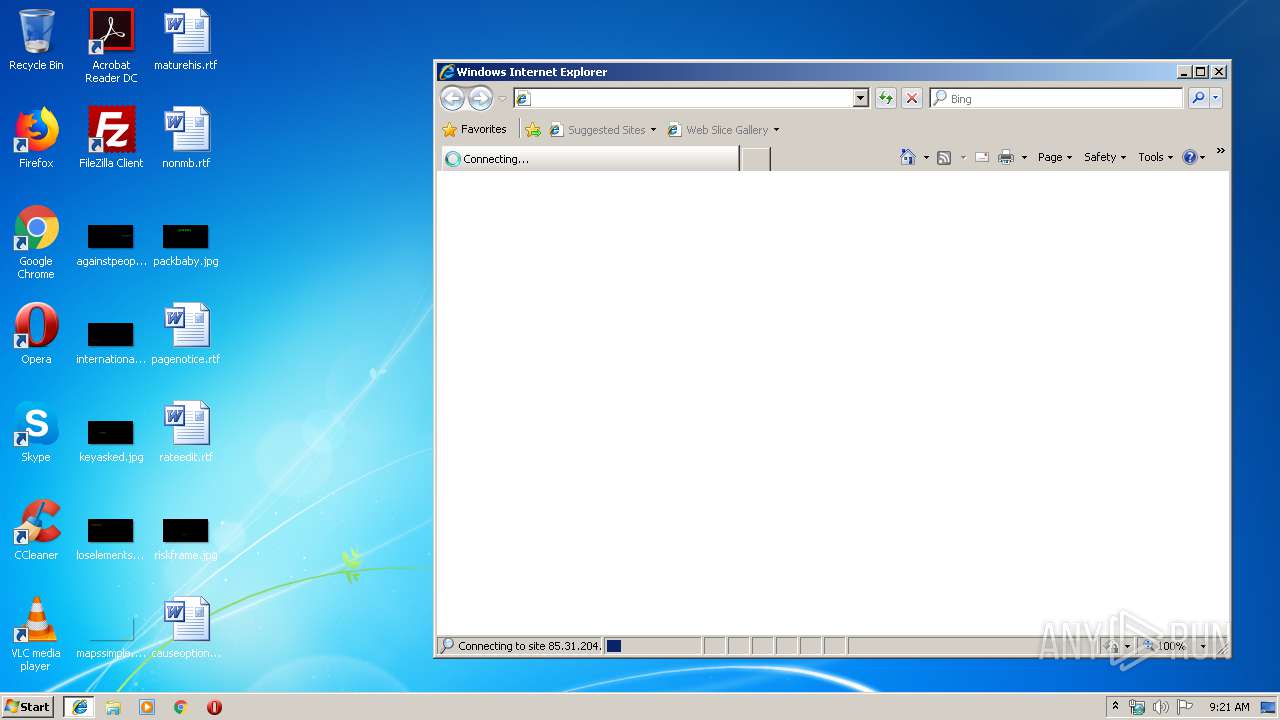
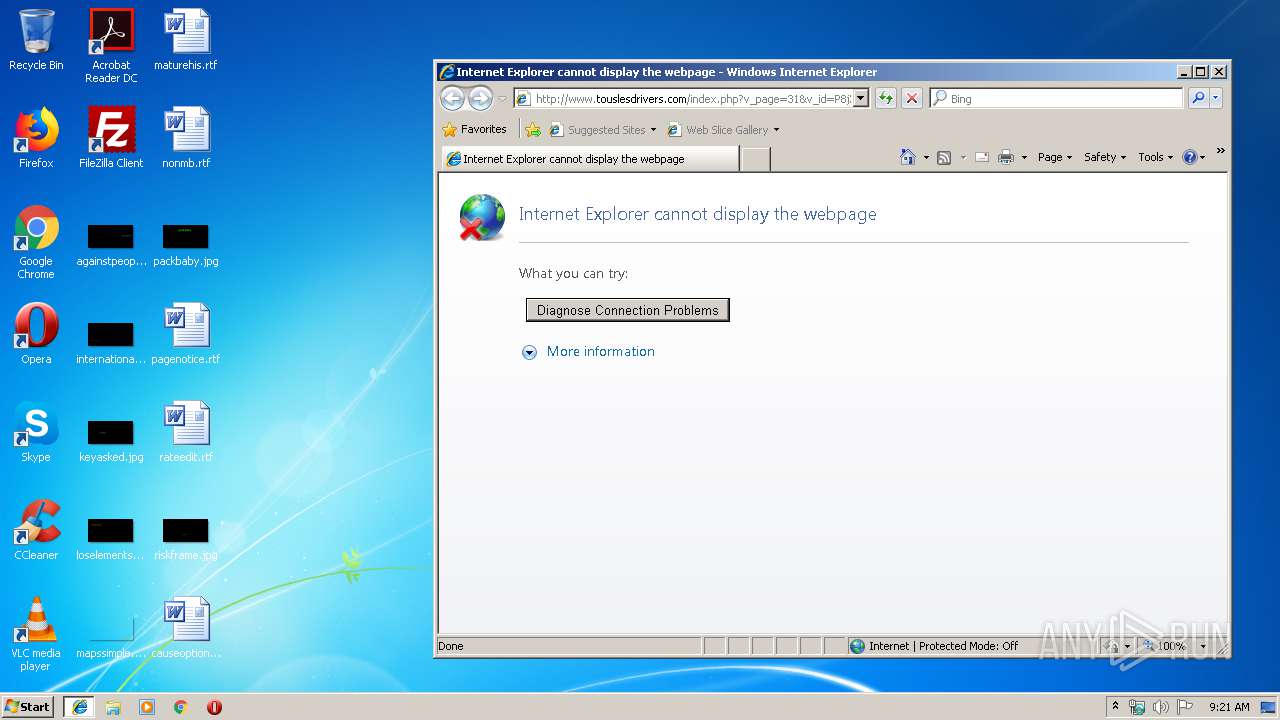
Starts Internet Explorer
- cmd.exe (PID: 4040)
INFO
Application launched itself
- iexplore.exe (PID: 3488)
Changes internet zones settings
- iexplore.exe (PID: 3488)
Creates files in the user directory
- iexplore.exe (PID: 3968)
Reads Internet Cache Settings
- iexplore.exe (PID: 3968)
Reads internet explorer settings
- iexplore.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:09 23:38:59+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 353280 |
| InitializedDataSize: | 2237440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x28e2c5 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 3.0.4.0 |
| ProductVersionNumber: | 3.0.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Tous Les Drivers |
| FileDescription: | Mes Drivers |
| FileVersion: | 3. 0. 4. 0 |
| InternalName: | - |
| LegalCopyright: | Copyright © 2016 Tous Les Drivers - Tous droits réservés |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Mes Drivers |
| ProductVersion: | 3. 0. 4. 0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Sep-2016 21:38:59 |
| Detected languages: |
|
| CompanyName: | Tous Les Drivers |
| FileDescription: | Mes Drivers |
| FileVersion: | 3. 0. 4. 0 |
| InternalName: | - |
| LegalCopyright: | Copyright © 2016 Tous Les Drivers - Tous droits réservés |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Mes Drivers |
| ProductVersion: | 3. 0. 4. 0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0040 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0002 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0xB400 |
| OEM information: | 0xCD09 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-Sep-2016 21:38:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.MPRESS1 | 0x00001000 | 0x0028D000 | 0x00117E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99983 |
.MPRESS2X\x0e | 0x0028E000 | 0x00000E58 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.12106 |
.rsrc | 0x0028F000 | 0x0000366C | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.60344 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07702 | 517 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4086 | 5.62878 | 56 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 7.88841 | 1784 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 7.75269 | 812 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 7.77778 | 904 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 7.77755 | 932 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 7.37266 | 328 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 6.99077 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 7.62605 | 516 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 7.77954 | 924 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
URLMON.DLL |
advapi32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
54
Monitored processes
18
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | WAITFOR /S USER-PC /SI unlock | C:\Windows\system32\WAITFOR.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: waitfor - wait/send a signal over a network Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1428 | WAITFOR /S USER-PC /SI unlock | C:\Windows\system32\WAITFOR.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: waitfor - wait/send a signal over a network Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\Temp\detect_x86.exe" driverfiles 1394\* DISPLAY\* HDAUDIO\* HID\* MONITOR\* PCI\* PCMCIA\* SBP2\* SD\* USB\* | C:\Users\admin\AppData\Local\Temp\detect_x86.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Detect Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\AppData\Local\Temp\detect_x86.exe" drivernodes 1394\* DISPLAY\* HDAUDIO\* HID\* MONITOR\* PCI\* PCMCIA\* SBP2\* SD\* USB\* | C:\Users\admin\AppData\Local\Temp\detect_x86.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Detect Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2492 | "C:\Users\admin\AppData\Local\Temp\detect_x86.exe" hwids 1394\* DISPLAY\* HDAUDIO\* HID\* MONITOR\* PCI\* PCMCIA\* SBP2\* SD\* USB\* | C:\Users\admin\AppData\Local\Temp\detect_x86.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Detect Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2660 | WAITFOR /S USER-PC /SI unlock | C:\Windows\system32\WAITFOR.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: waitfor - wait/send a signal over a network Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Local\Temp\detect_x86.exe" stack 1394\* DISPLAY\* HDAUDIO\* HID\* MONITOR\* PCI\* PCMCIA\* SBP2\* SD\* USB\* | C:\Users\admin\AppData\Local\Temp\detect_x86.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Detect Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\AppData\Local\Temp\detect_x86.exe" status 1394\* DISPLAY\* HDAUDIO\* HID\* MONITOR\* PCI\* PCMCIA\* SBP2\* SD\* USB\* | C:\Users\admin\AppData\Local\Temp\detect_x86.exe | — | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Detect Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Temp\curl_x86.exe" --connect-timeout 5 --max-time 20 --fail --silent --request POST --form "v_configuration=<C:\Users\admin\AppData\Local\Temp\P8jXfHzIDLW5iJkc\P8jXfHzIDLW5iJkc" "https://www.touslesdrivers.com/php/mes_drivers/envoi.php?v_id=P8jXfHzIDLW5iJkc&v_version=3.0.4" | C:\Users\admin\AppData\Local\Temp\curl_x86.exe | 7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: HIGH Description: The curl executable Exit code: 23 Version: 7.51.0 Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\AppData\Local\Temp\7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe" | C:\Users\admin\AppData\Local\Temp\7fbe59195f5f6f45c8b38b12488a169fdcb3a272004dbaf44c9d92a60a3690cb.exe | — | explorer.exe | |||||||||||
User: admin Company: Tous Les Drivers Integrity Level: MEDIUM Description: Mes Drivers Exit code: 3221226540 Version: 3. 0. 4. 0 Modules
| |||||||||||||||
Total events
435
Read events
361
Write events
74
Delete events
0
Modification events
| (PID) Process: | (2156) detect_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (2156) detect_x86.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2276) detect_x86.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\AdminActive |
| Operation: | write | Name: | {2250D66F-AEB5-11E9-B506-5254004A04AF} |
Value: 0 | |||
Executable files
8
Suspicious files
0
Text files
259
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\CabF83D.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\TarF83E.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\CabF83F.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\TarF840.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\CabF850.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\TarF851.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\CabF862.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\TarF863.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\CabF873.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | detect_x86.exe | C:\Users\admin\AppData\Local\Temp\TarF874.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3488 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
— | — | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQCX%2BefD9f1Iq1caTv8hQqls | US | der | 728 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3088 | curl_x86.exe | 85.31.204.81:443 | www.touslesdrivers.com | Jaguar Network SAS | FR | unknown |
3968 | iexplore.exe | 85.31.204.81:80 | www.touslesdrivers.com | Jaguar Network SAS | FR | unknown |
3488 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2996 | curl_x86.exe | 85.31.204.81:443 | www.touslesdrivers.com | Jaguar Network SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.touslesdrivers.com |
| unknown |
ocsp.usertrust.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |