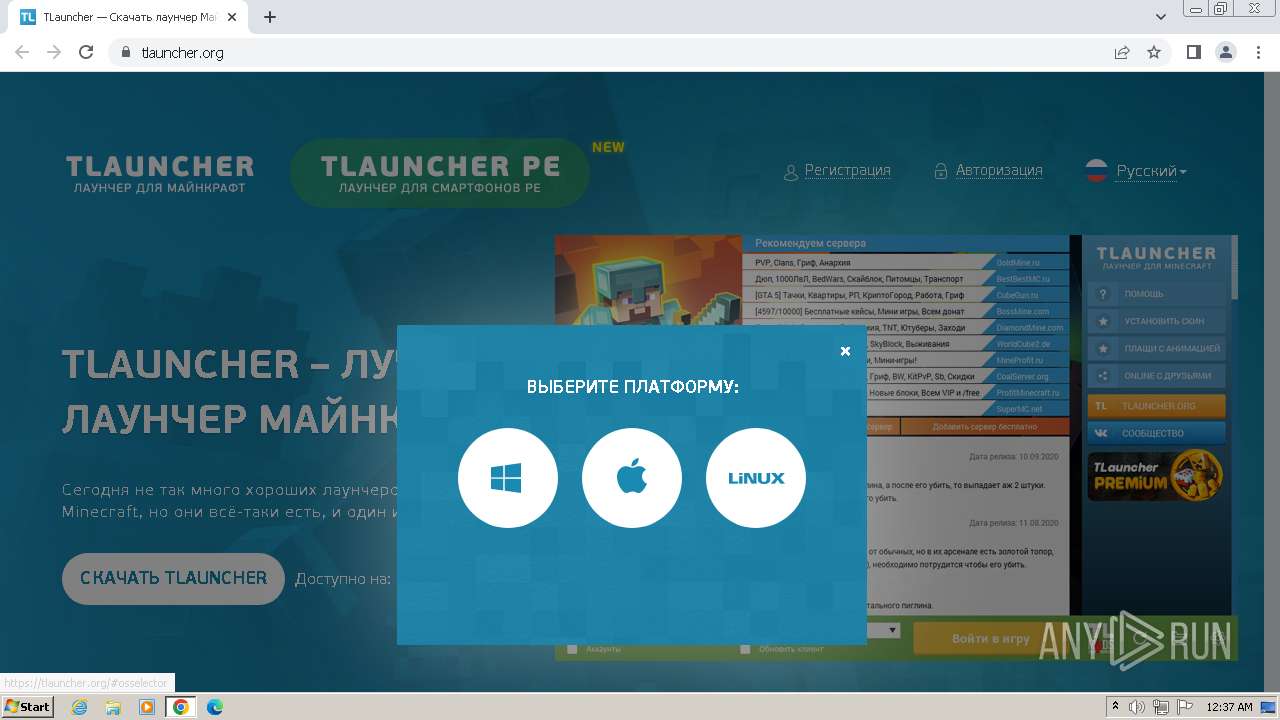
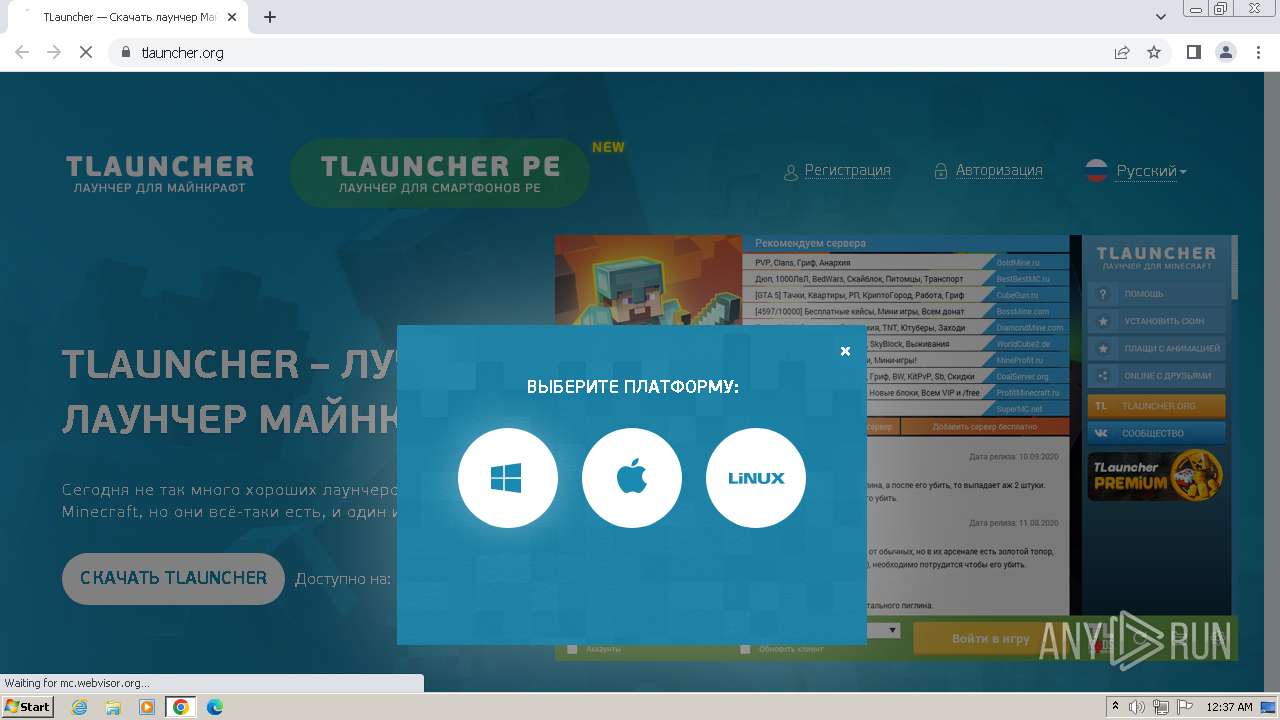
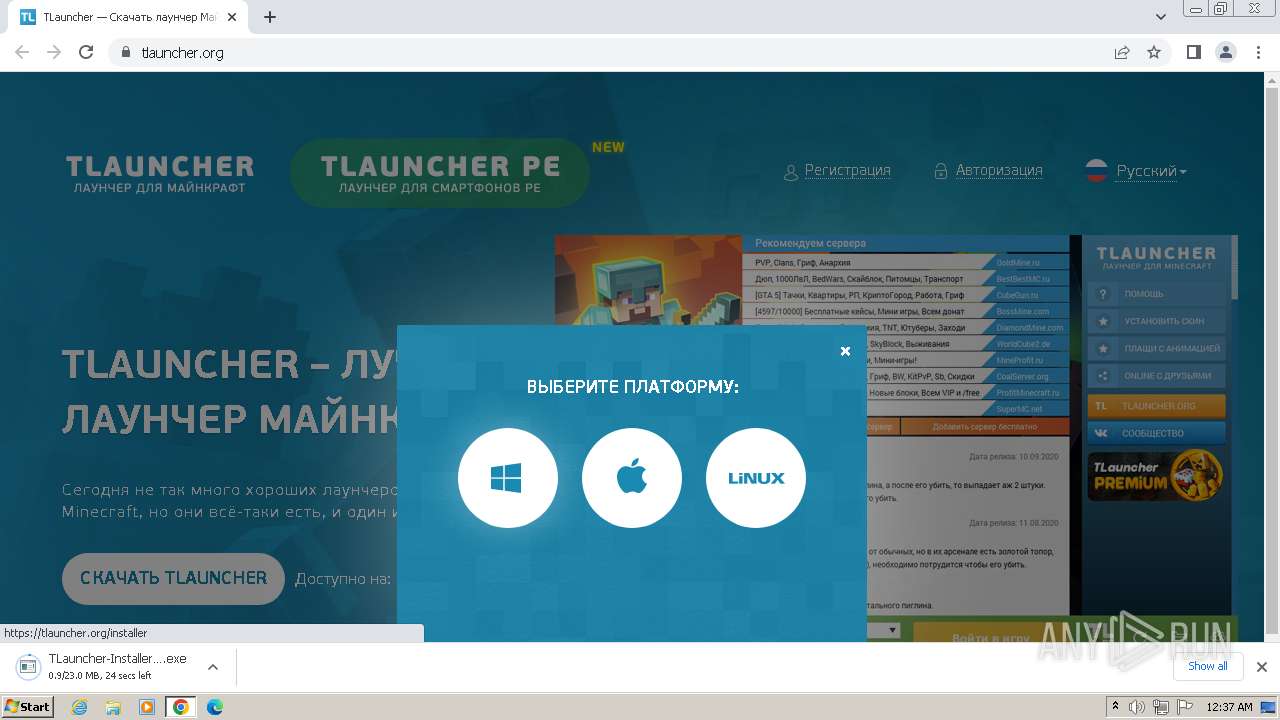
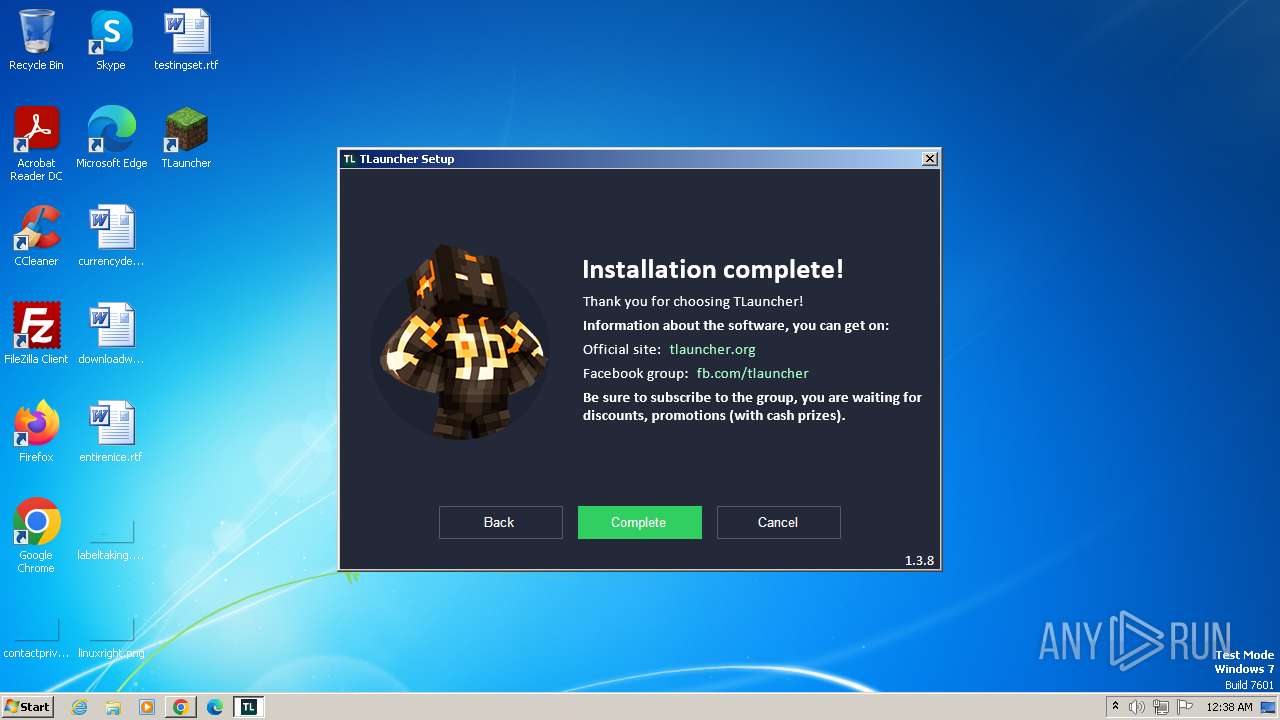
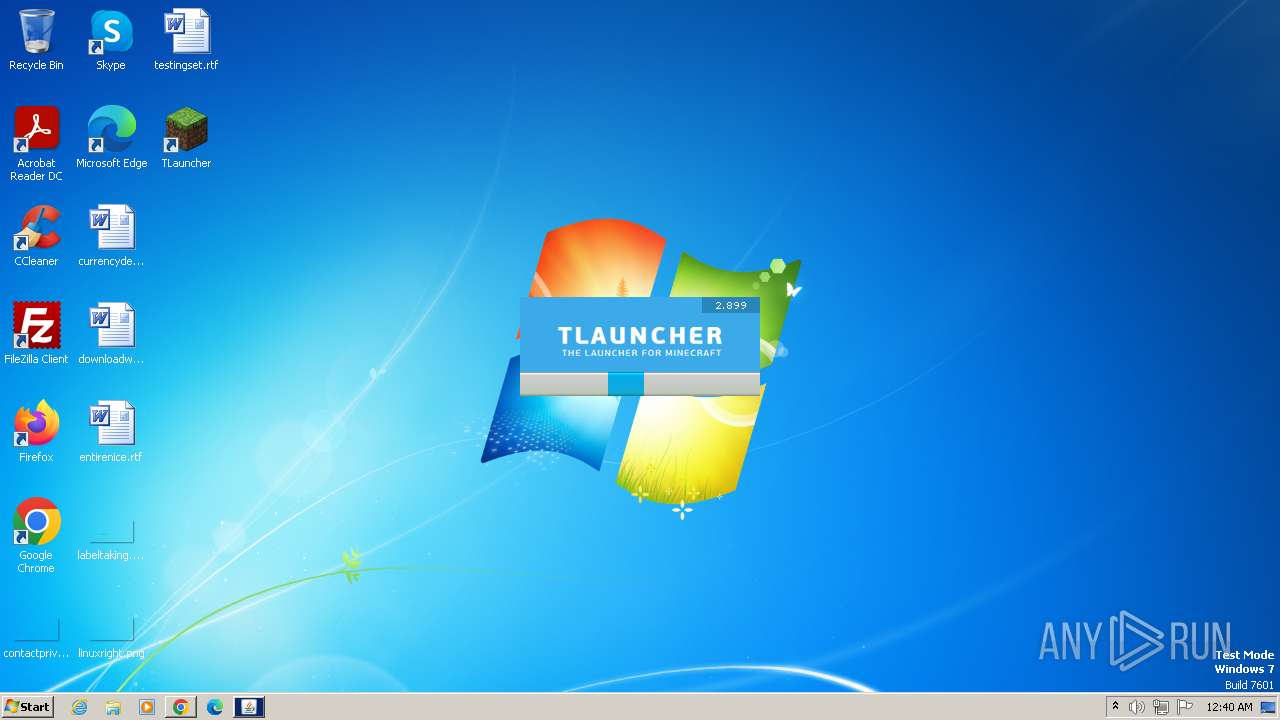
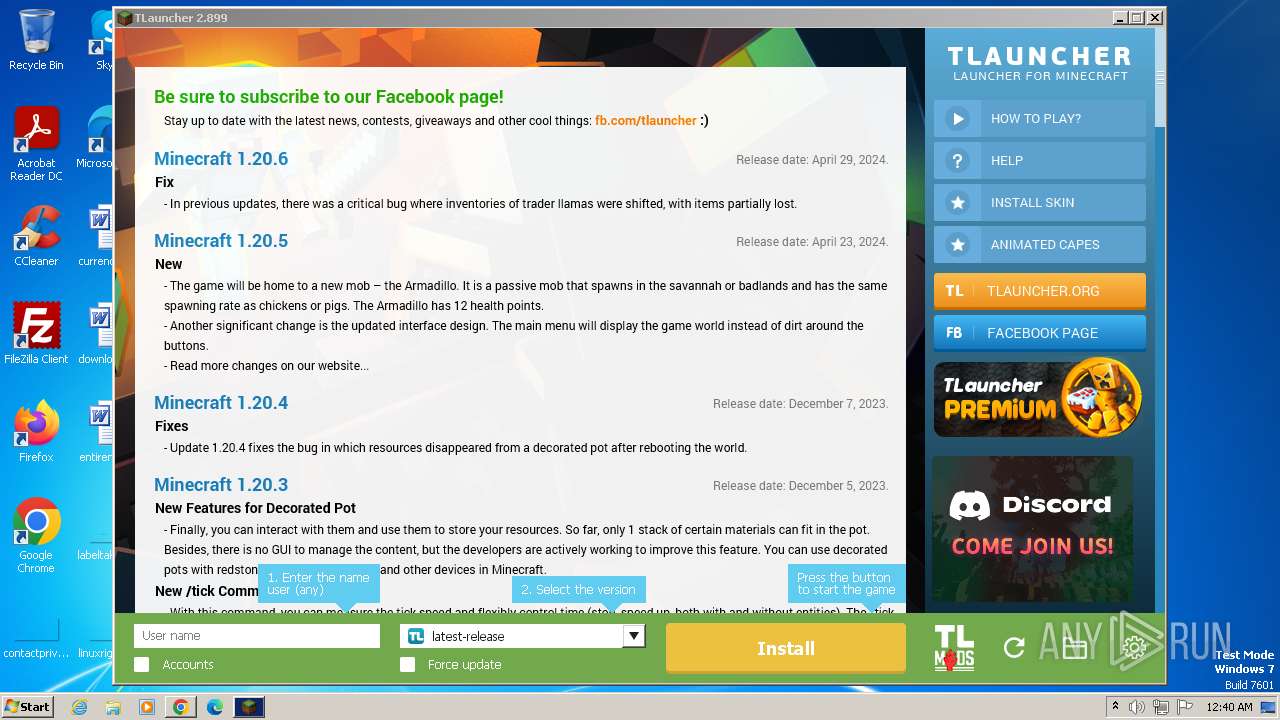
| URL: | https://tlauncher.org |
| Full analysis: | https://app.any.run/tasks/95013655-c4ba-470d-8ccf-f44115538f92 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2024, 23:36:52 |
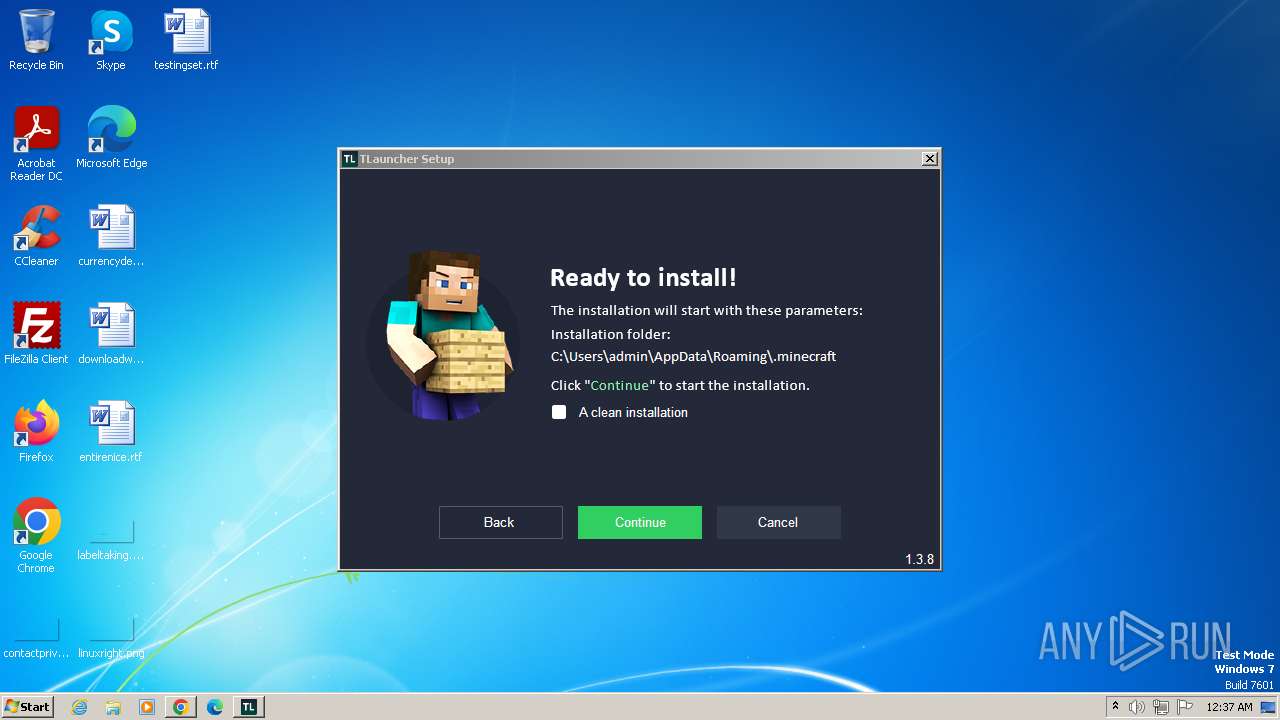
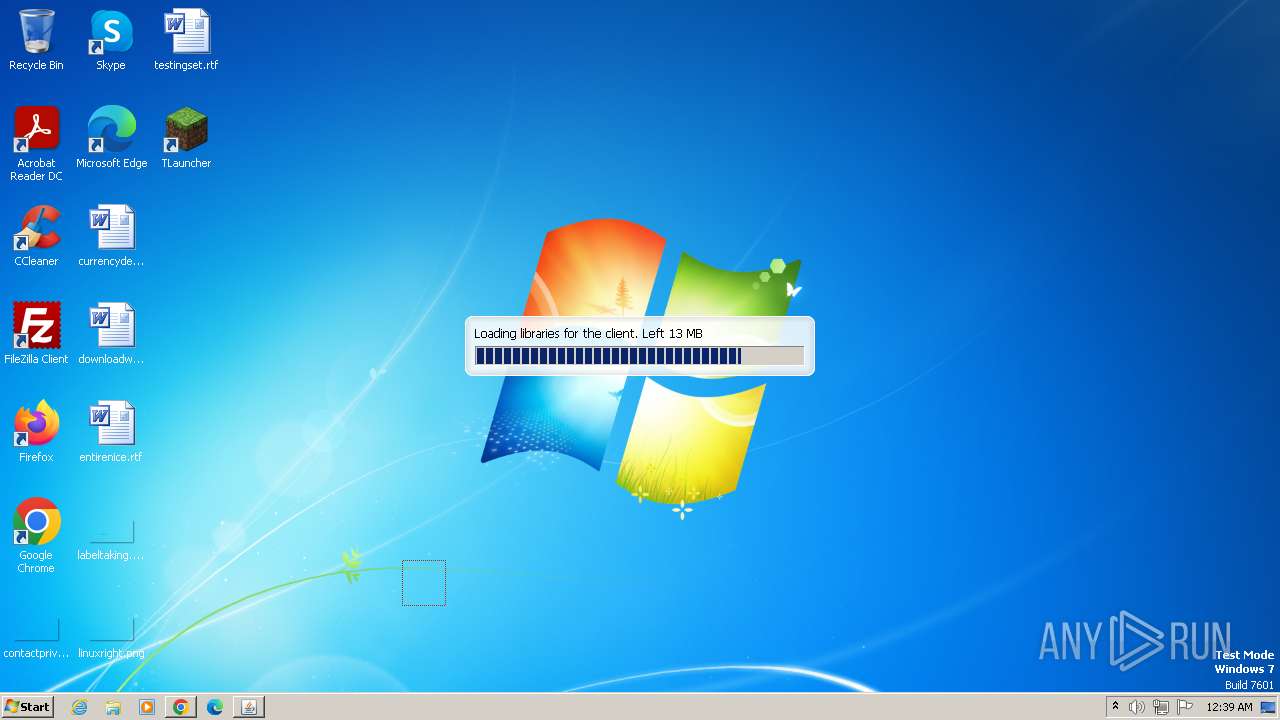
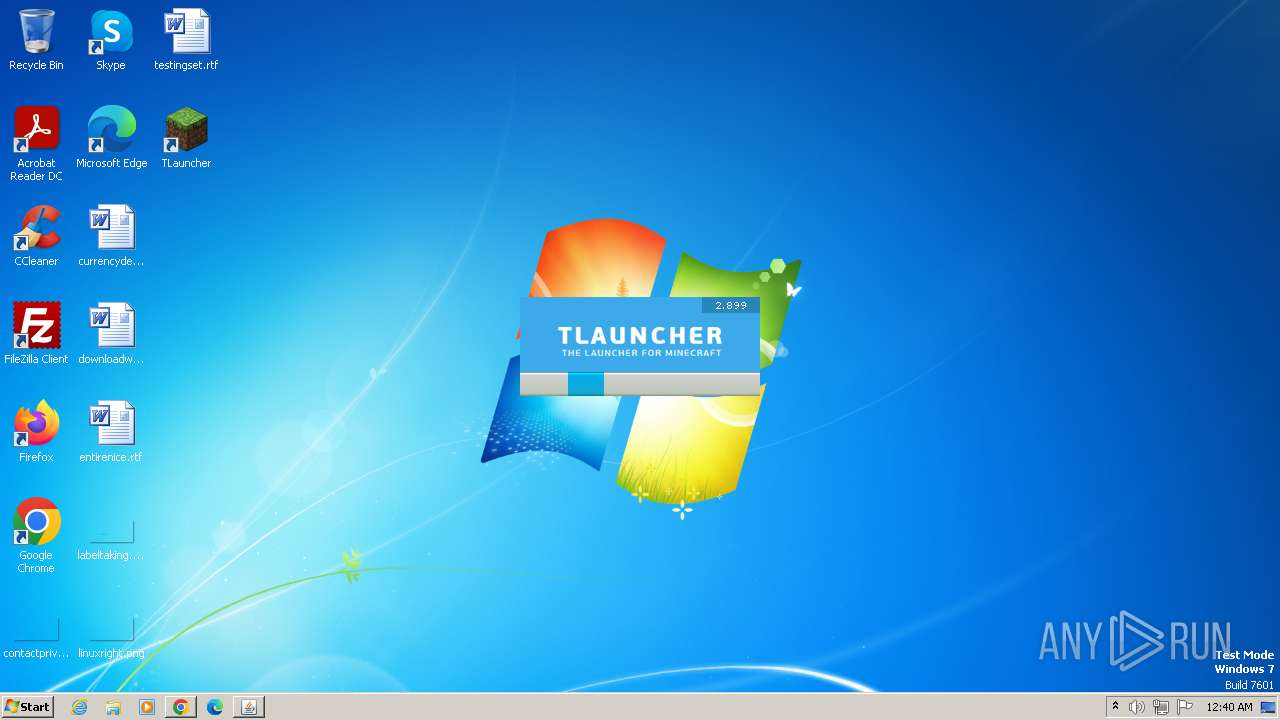
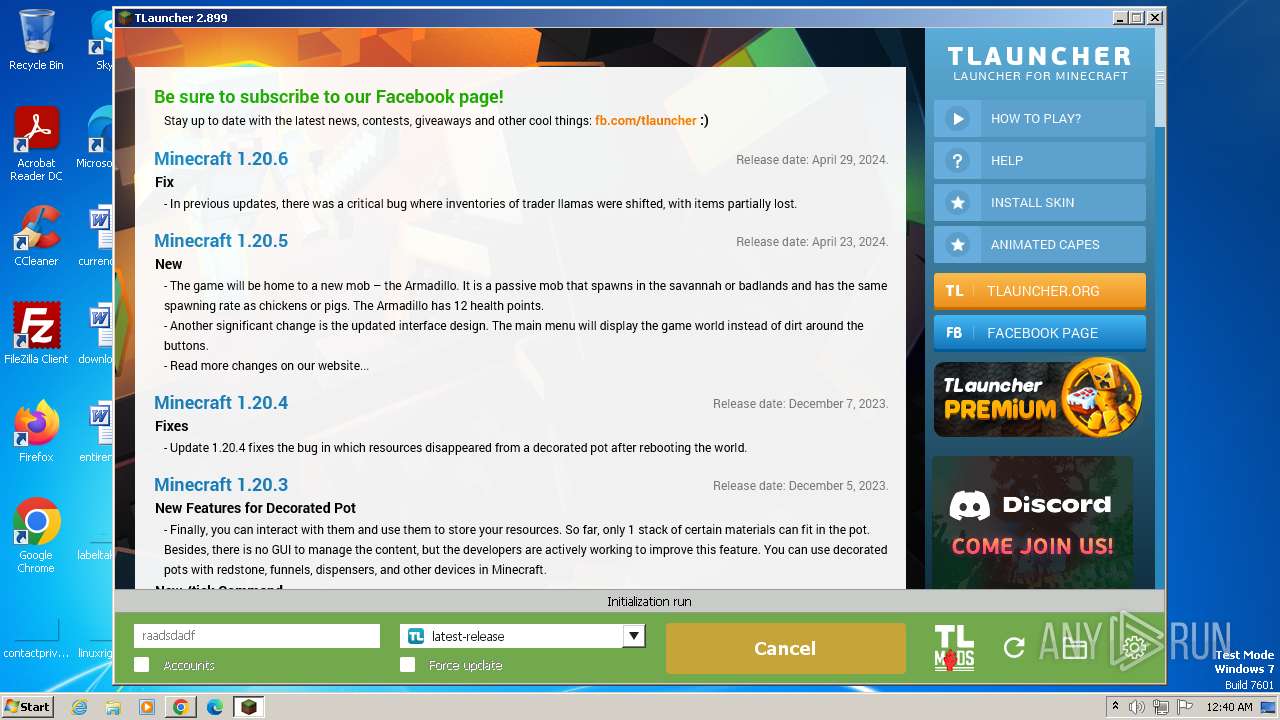
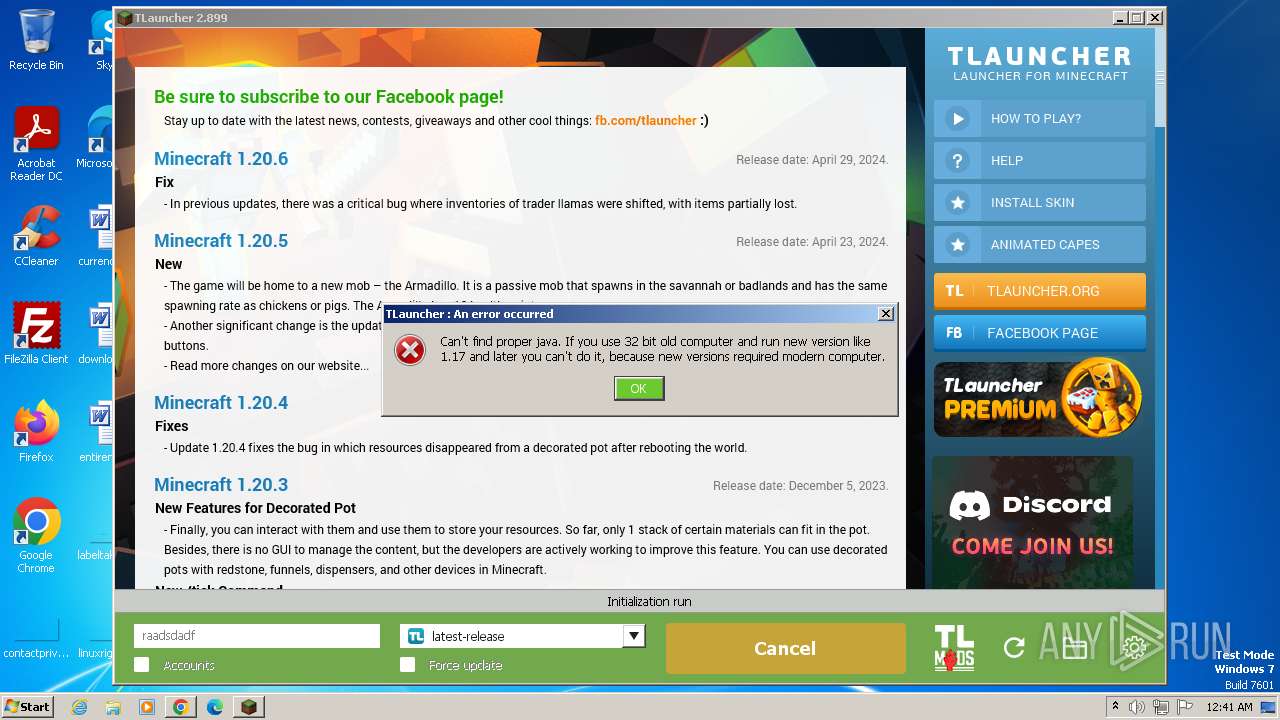
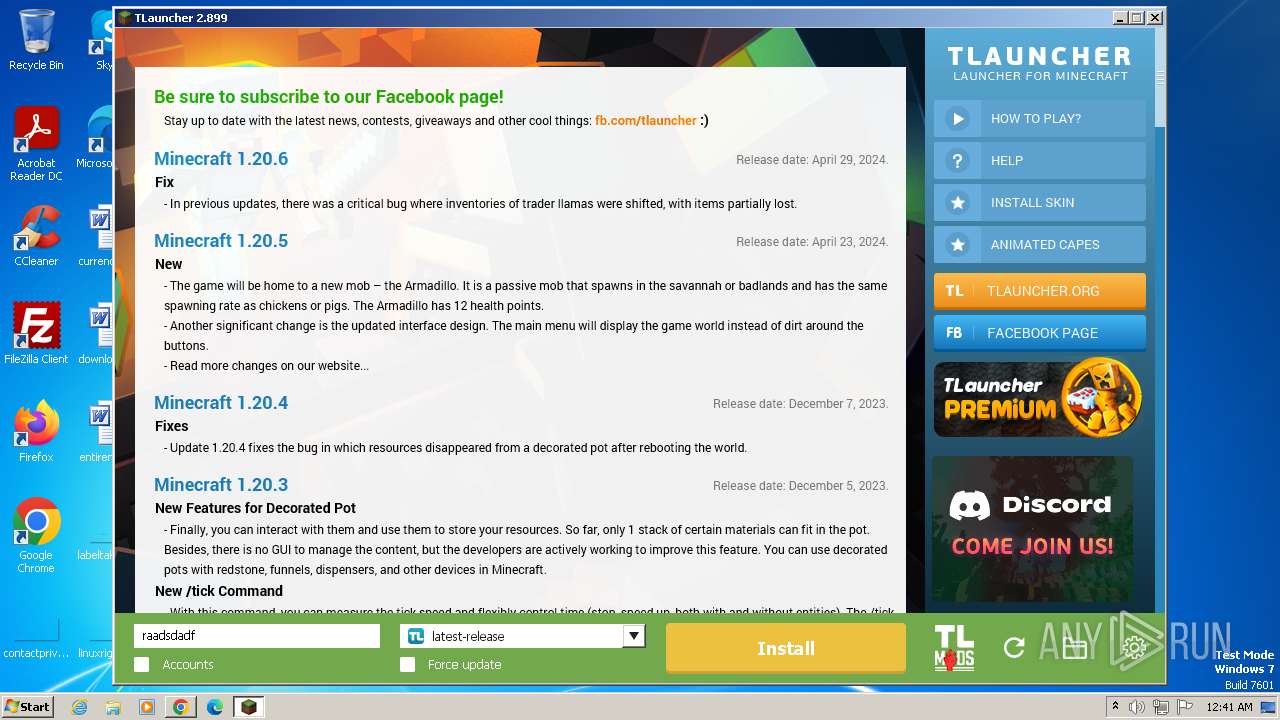
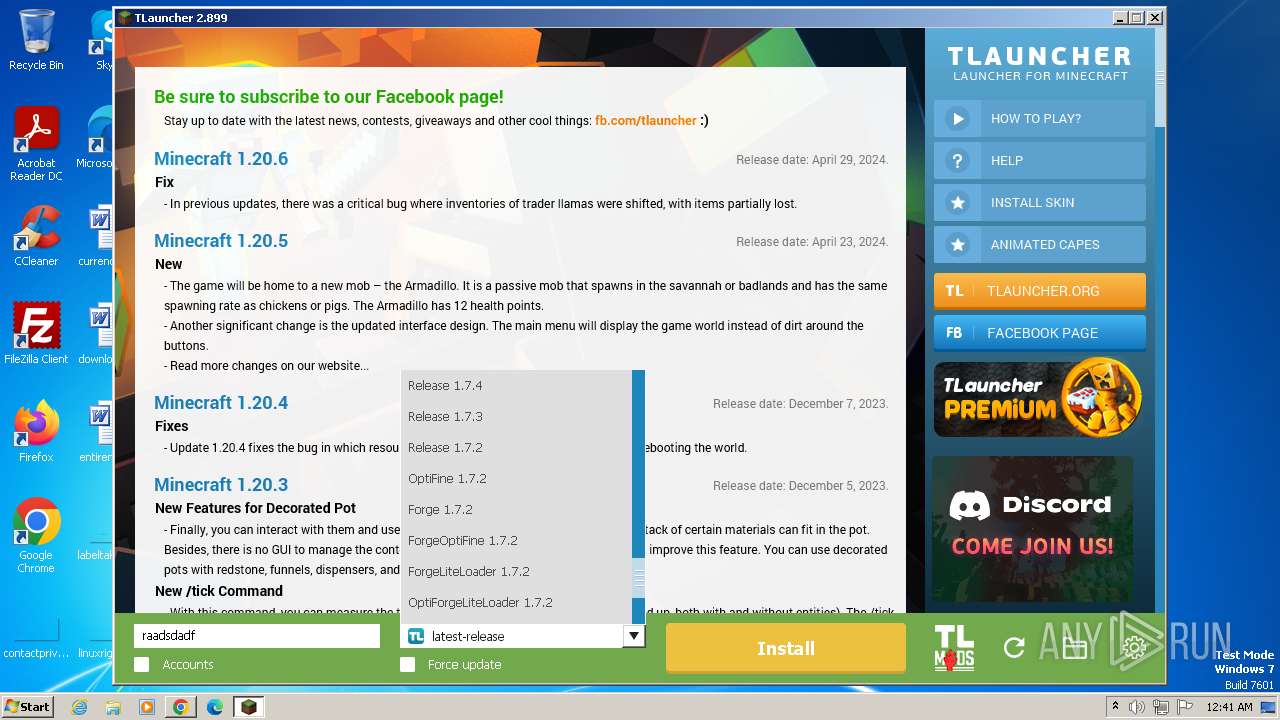
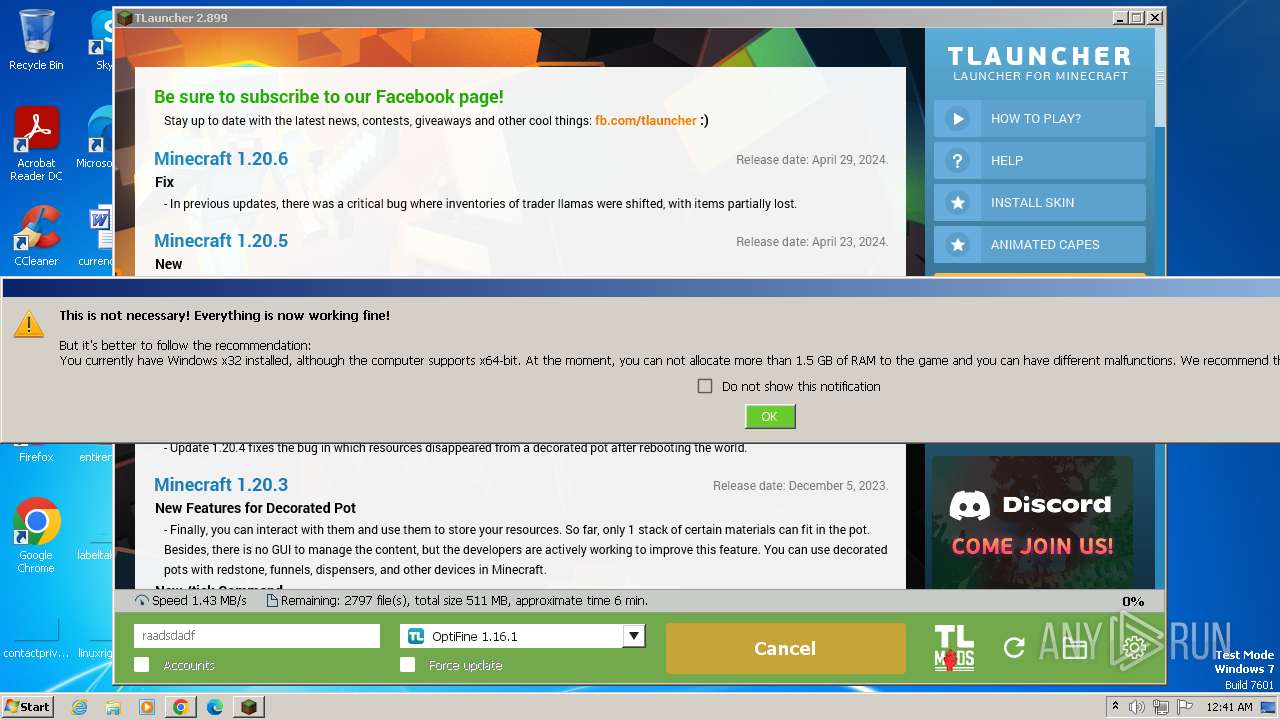
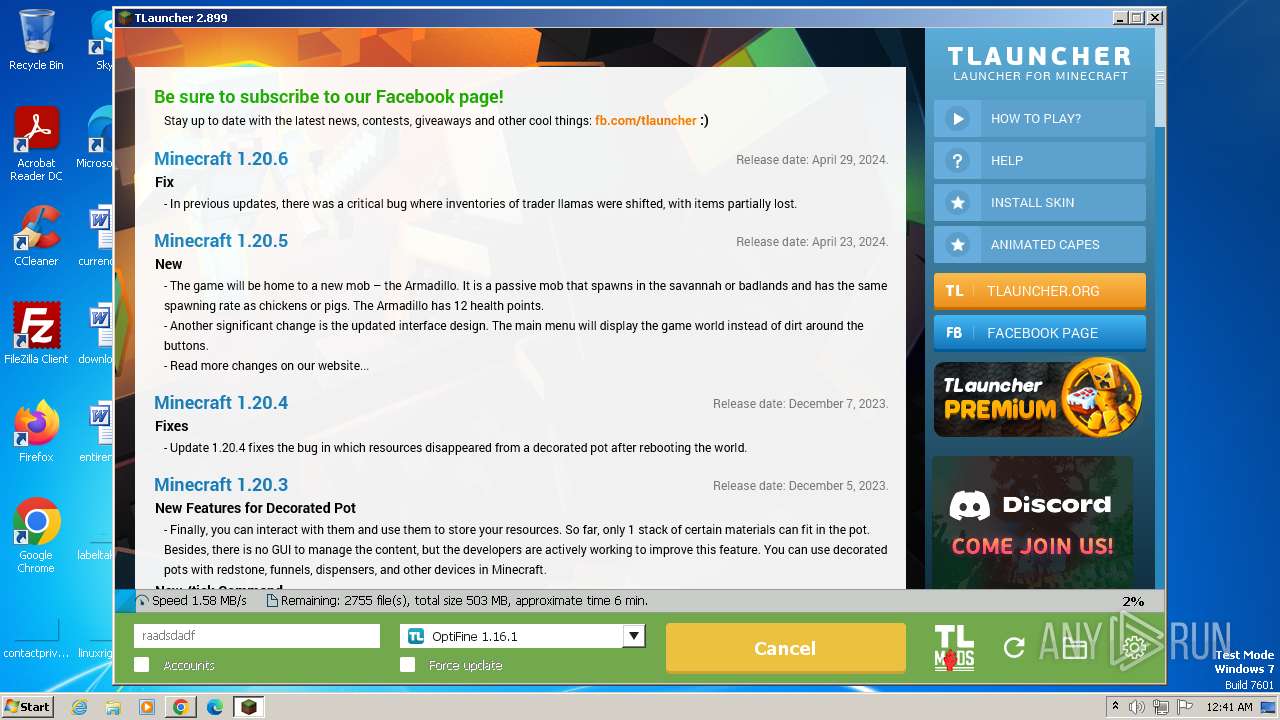
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A8BC9AD6485D9C7D084A3393AE1E9C89 |
| SHA1: | 5761101D5EC08DC25FB46DCD9377A3B084AF13E8 |
| SHA256: | 7F9725F4AE9A5E9D6EBFC2B1A9BC3A7A4F0623A372909DE2F0033402C2034F24 |
| SSDEEP: | 3:N8BEeLuS:2KS |
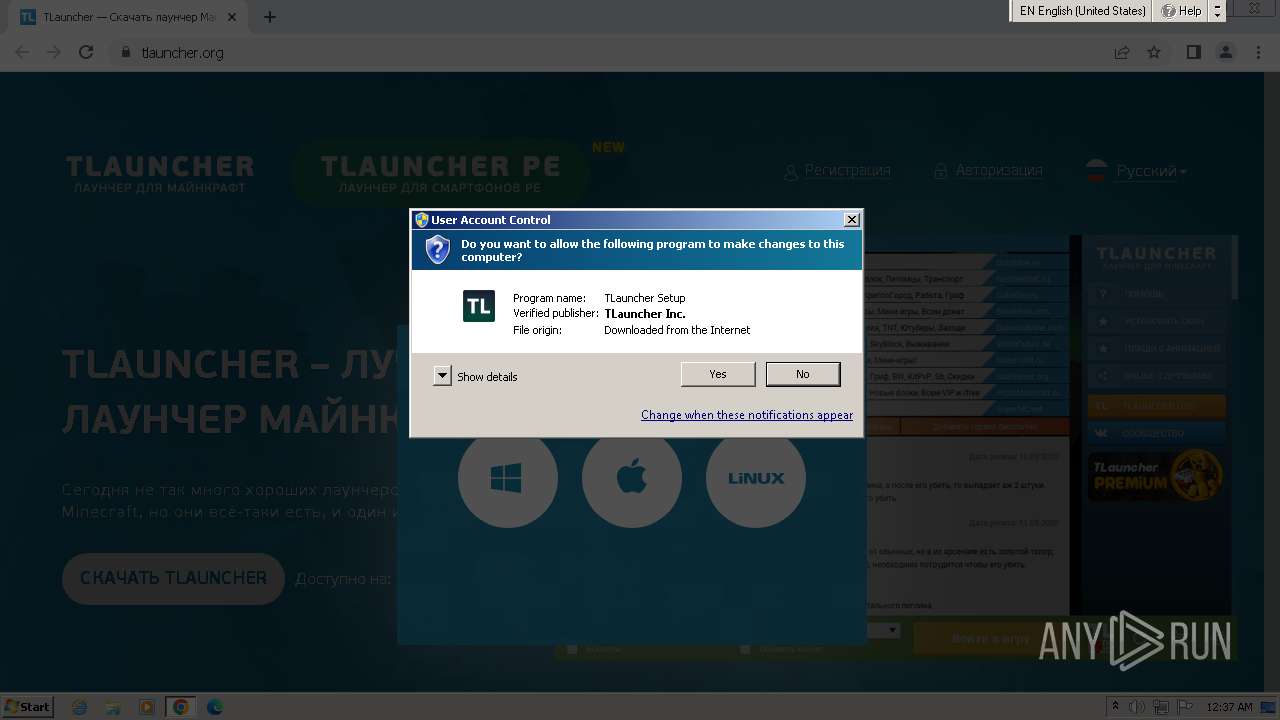
MALICIOUS
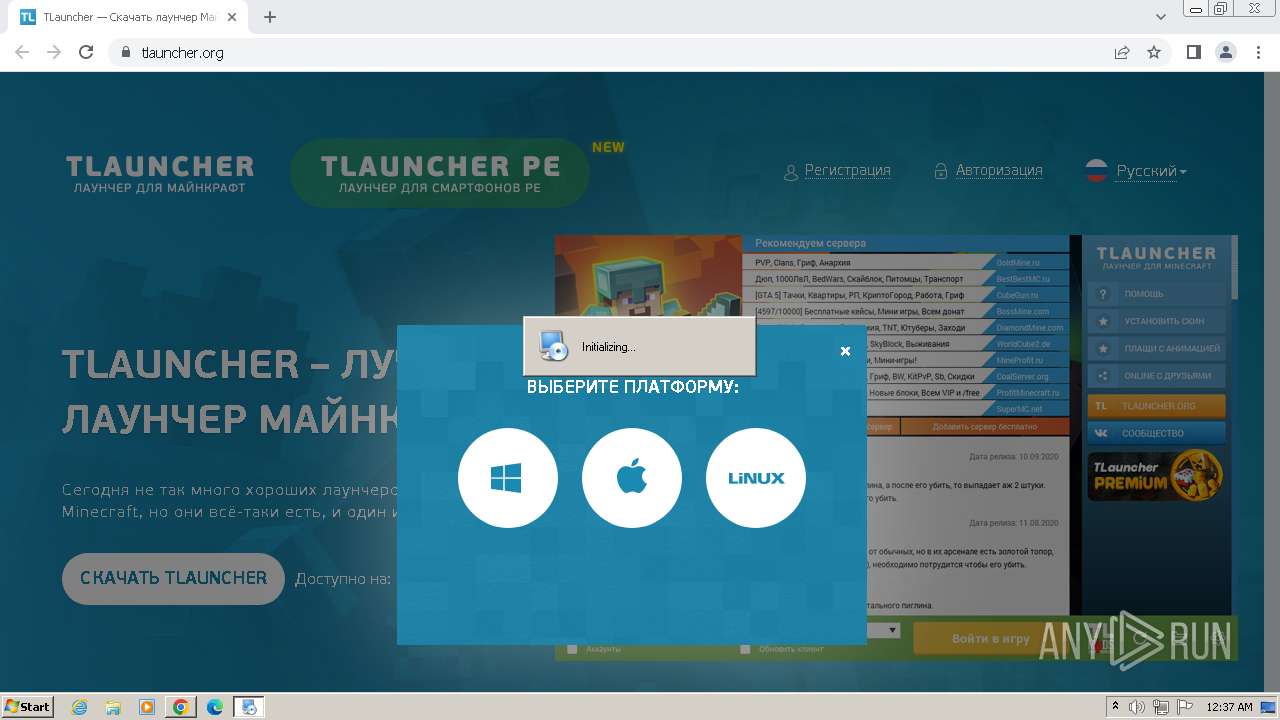
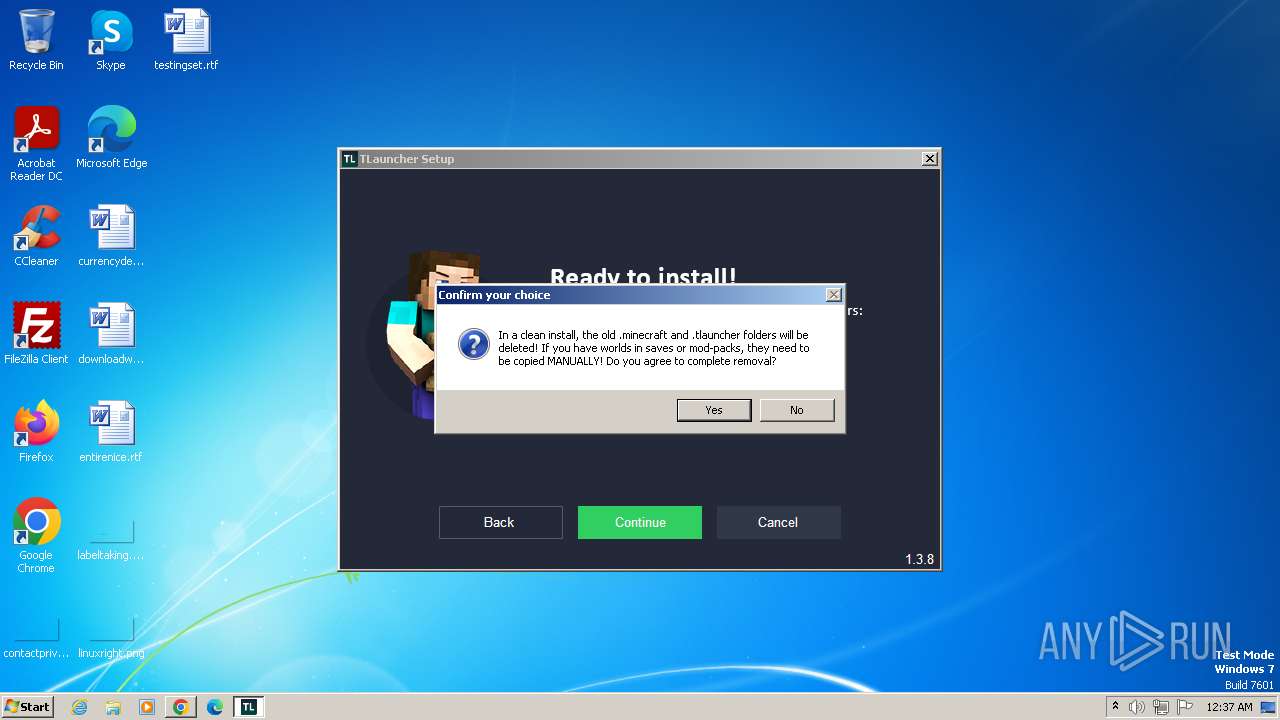
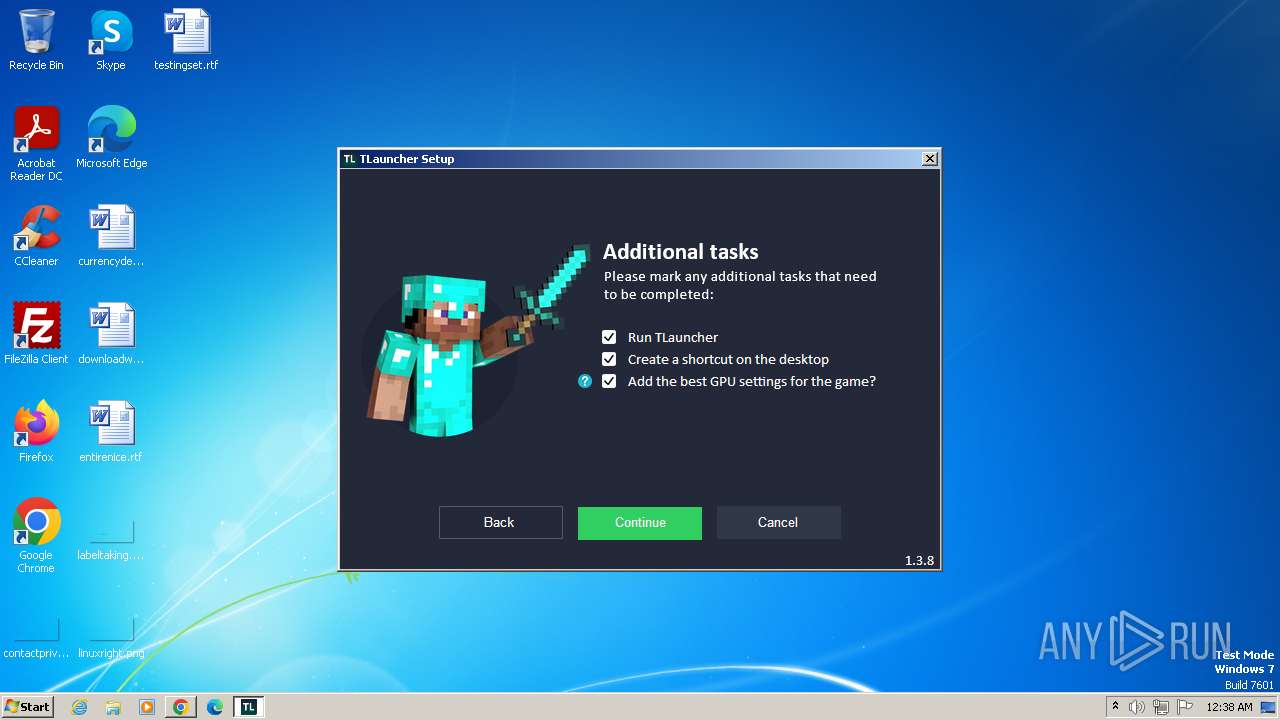
Drops the executable file immediately after the start
- TLauncher-Installer-1.3.8.exe (PID: 1312)
- irsetup.exe (PID: 2832)
- BrowserInstaller.exe (PID: 3136)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Actions looks like stealing of personal data
- irsetup.exe (PID: 2832)
SUSPICIOUS
Executable content was dropped or overwritten
- TLauncher-Installer-1.3.8.exe (PID: 1312)
- irsetup.exe (PID: 2832)
- BrowserInstaller.exe (PID: 3136)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Reads security settings of Internet Explorer
- TLauncher-Installer-1.3.8.exe (PID: 1312)
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
- BrowserInstaller.exe (PID: 3136)
Reads the Internet Settings
- TLauncher-Installer-1.3.8.exe (PID: 1312)
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
- BrowserInstaller.exe (PID: 3136)
- WMIC.exe (PID: 1884)
- WMIC.exe (PID: 1928)
- WMIC.exe (PID: 3572)
- WMIC.exe (PID: 3704)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
Adds/modifies Windows certificates
- irsetup.exe (PID: 2832)
Checks for Java to be installed
- irsetup.exe (PID: 2832)
- TLauncher.exe (PID: 3944)
Checks Windows Trust Settings
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
Reads settings of System Certificates
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
- dxdiag.exe (PID: 1652)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 2832)
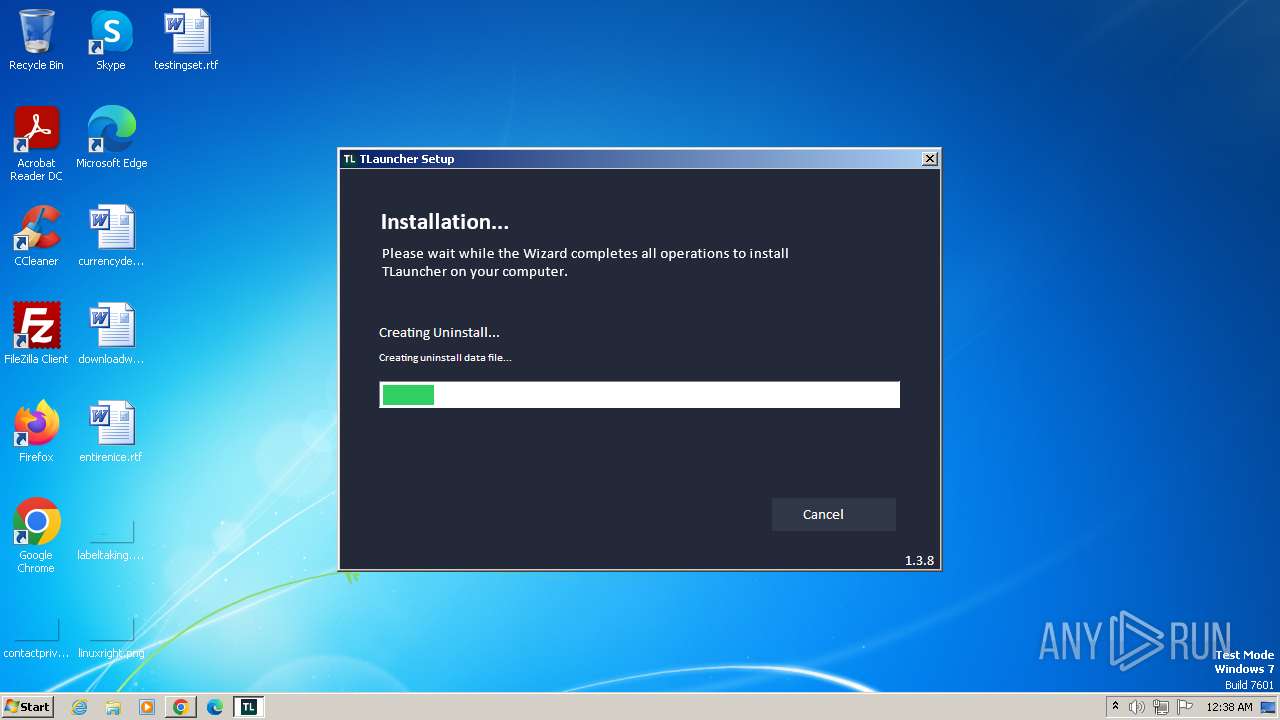
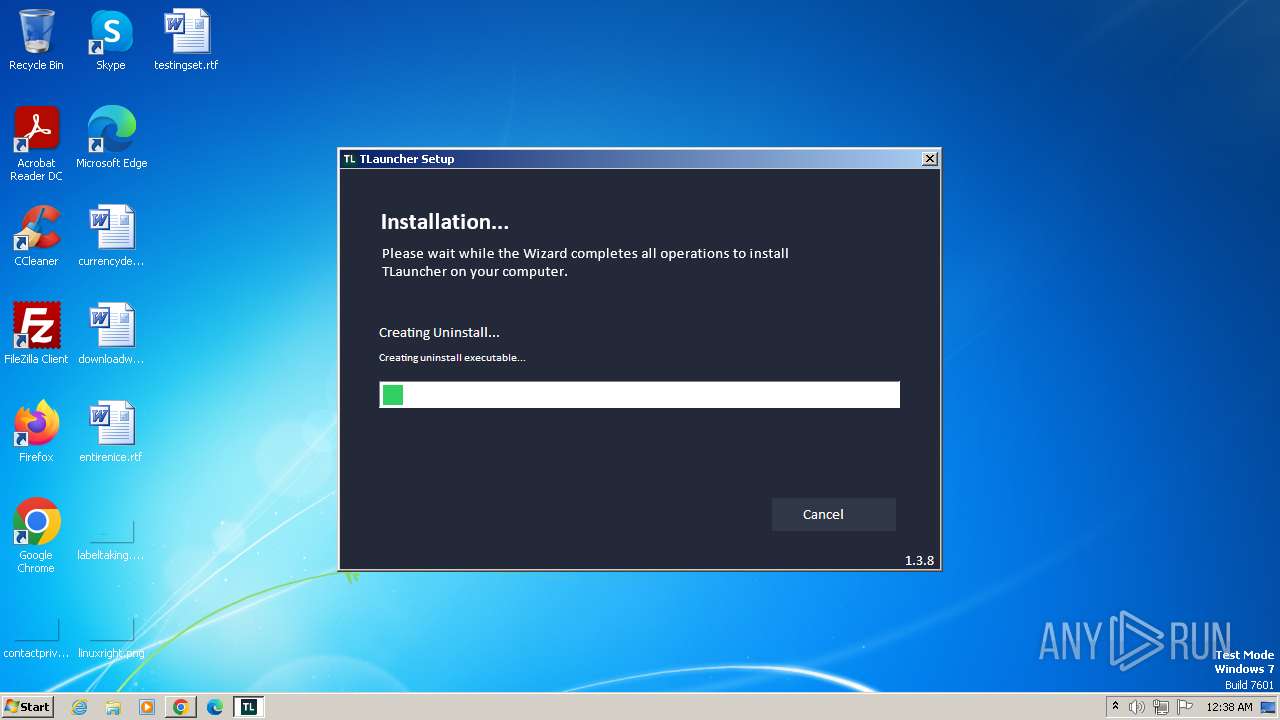
Creates a software uninstall entry
- irsetup.exe (PID: 2832)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Process requests binary or script from the Internet
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Starts application with an unusual extension
- cmd.exe (PID: 1824)
- cmd.exe (PID: 1820)
- cmd.exe (PID: 3380)
- cmd.exe (PID: 1472)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 2944)
- cmd.exe (PID: 2672)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 1824)
- cmd.exe (PID: 1820)
The process drops C-runtime libraries
- javaw.exe (PID: 3832)
Process drops legitimate windows executable
- javaw.exe (PID: 3832)
Uses ICACLS.EXE to modify access control lists
- javaw.exe (PID: 2544)
Reads Internet Explorer settings
- irsetup.exe (PID: 2832)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 3380)
Creates/Modifies COM task schedule object
- dxdiag.exe (PID: 1652)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 2672)
INFO
Application launched itself
- chrome.exe (PID: 3988)
Checks supported languages
- wmpnscfg.exe (PID: 1944)
- TLauncher-Installer-1.3.8.exe (PID: 1312)
- irsetup.exe (PID: 2832)
- BrowserInstaller.exe (PID: 3136)
- irsetup.exe (PID: 2652)
- TLauncher.exe (PID: 3944)
- chcp.com (PID: 2092)
- chcp.com (PID: 860)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
- chcp.com (PID: 3644)
- chcp.com (PID: 3580)
- chcp.com (PID: 2980)
- chcp.com (PID: 2796)
- chcp.com (PID: 3612)
Manual execution by a user
- wmpnscfg.exe (PID: 1944)
Reads the computer name
- wmpnscfg.exe (PID: 1944)
- TLauncher-Installer-1.3.8.exe (PID: 1312)
- irsetup.exe (PID: 2832)
- BrowserInstaller.exe (PID: 3136)
- irsetup.exe (PID: 2652)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Executable content was dropped or overwritten
- chrome.exe (PID: 3988)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 2508)
The process uses the downloaded file
- chrome.exe (PID: 3988)
- chrome.exe (PID: 1012)
Drops the executable file immediately after the start
- chrome.exe (PID: 3988)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 2508)
Create files in a temporary directory
- TLauncher-Installer-1.3.8.exe (PID: 1312)
- irsetup.exe (PID: 2832)
- BrowserInstaller.exe (PID: 3136)
- irsetup.exe (PID: 2652)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Reads the software policy settings
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
- dxdiag.exe (PID: 1652)
Reads the machine GUID from the registry
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Checks proxy server information
- irsetup.exe (PID: 2832)
- irsetup.exe (PID: 2652)
Creates files or folders in the user directory
- irsetup.exe (PID: 2652)
- irsetup.exe (PID: 2832)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Creates files in the program directory
- irsetup.exe (PID: 2832)
- javaw.exe (PID: 3832)
- javaw.exe (PID: 2544)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 1652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
56
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1512 --field-trial-handle=1160,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2016 --field-trial-handle=1160,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2036 --field-trial-handle=1160,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 316 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1272 --field-trial-handle=1160,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 860 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
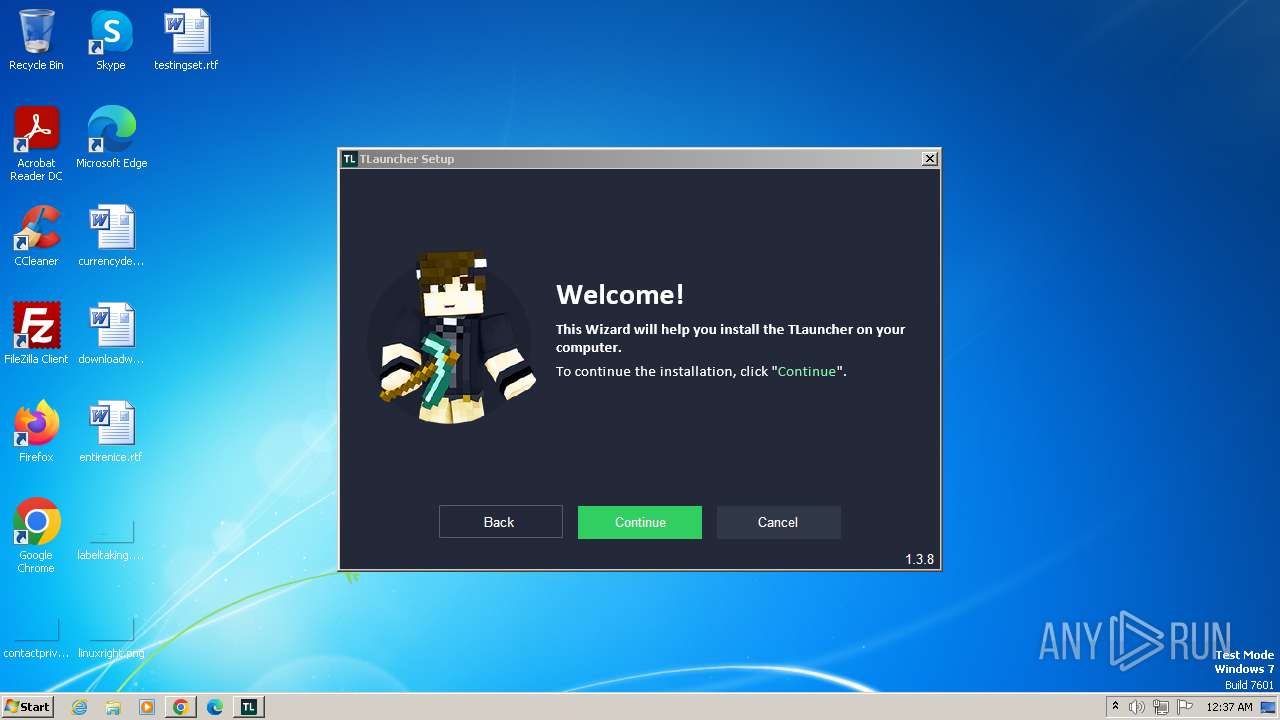
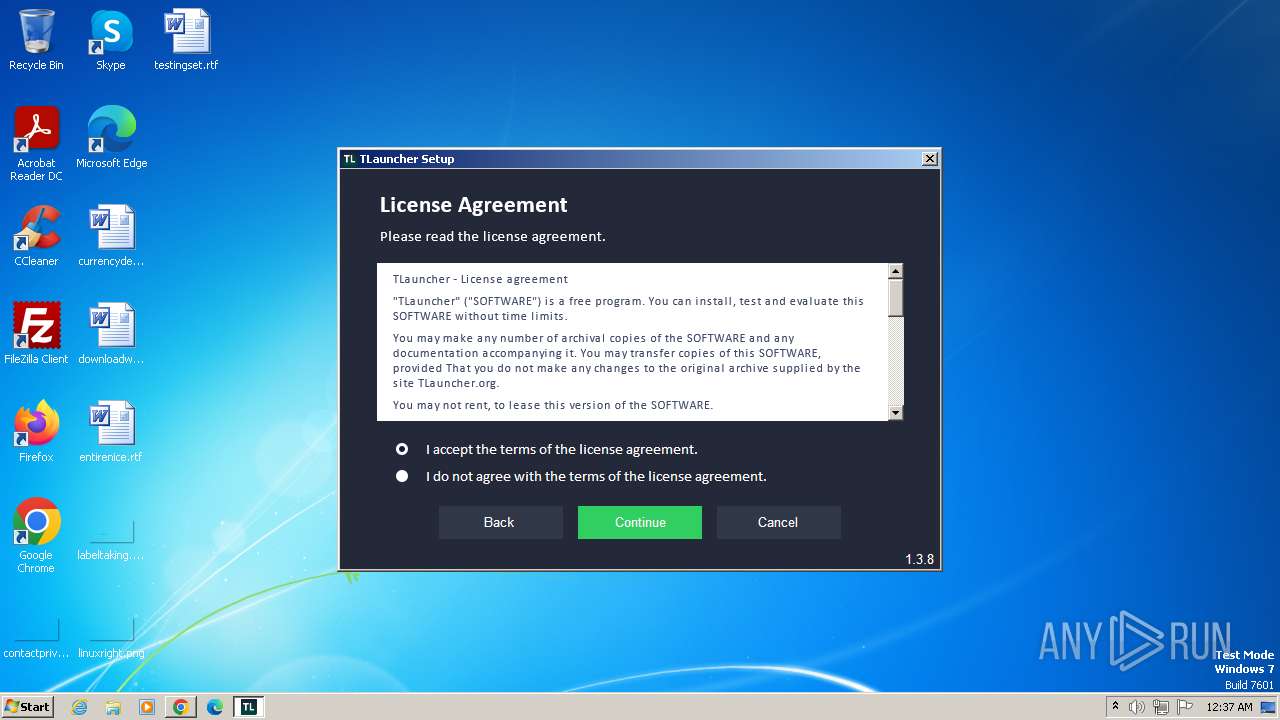
| 936 | "C:\Users\admin\Downloads\TLauncher-Installer-1.3.8.exe" | C:\Users\admin\Downloads\TLauncher-Installer-1.3.8.exe | — | chrome.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 3221226540 Version: 1.3.8.0 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3864 --field-trial-handle=1160,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1092 --field-trial-handle=1160,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3988 --field-trial-handle=1160,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
44 773
Read events
44 287
Write events
432
Delete events
54
Modification events
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
230
Suspicious files
940
Text files
877
Unknown types
217
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF103867.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF103a1d.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF104325.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF103b65.TMP | text | |
MD5:65239F35CB63C76EA1F59EF64F7AAFF4 | SHA256:252EF82CC03FDE4BEF13CF81CD1AC5CE45854212D1A7359035E7A5D6BEDBE229 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\94748721-3b54-4624-8faa-c4db78281366.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
78
DNS requests
59
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2652 | irsetup.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ccff43c03525aec8 | unknown | — | — | unknown |
2652 | irsetup.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3988 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
748 | chrome.exe | 104.20.37.13:443 | tlauncher.org | CLOUDFLARENET | — | unknown |
748 | chrome.exe | 172.217.218.84:443 | accounts.google.com | GOOGLE | US | unknown |
748 | chrome.exe | 142.250.185.234:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
748 | chrome.exe | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
748 | chrome.exe | 104.19.229.21:443 | hcaptcha.com | CLOUDFLARENET | — | unknown |
748 | chrome.exe | 104.16.79.73:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tlauncher.org |
| unknown |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
hcaptcha.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.gstatic.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
748 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
— | — | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
— | — | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3832 | javaw.exe | A Network Trojan was detected | ET HUNTING suspicious - gzipped file via JAVA - could be pack200-ed JAR |