| download: | index.html |
| Full analysis: | https://app.any.run/tasks/e776bab8-ec3f-4593-ae09-e79e0a4c3a8a |
| Verdict: | Malicious activity |
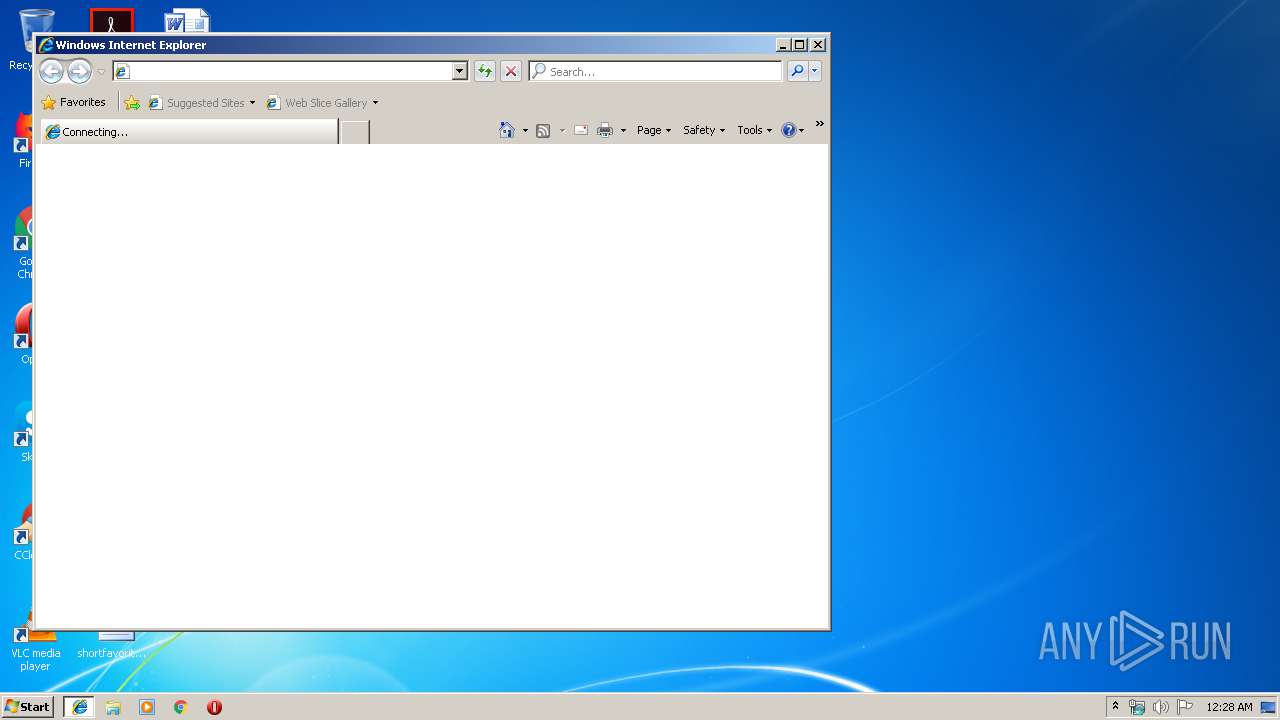
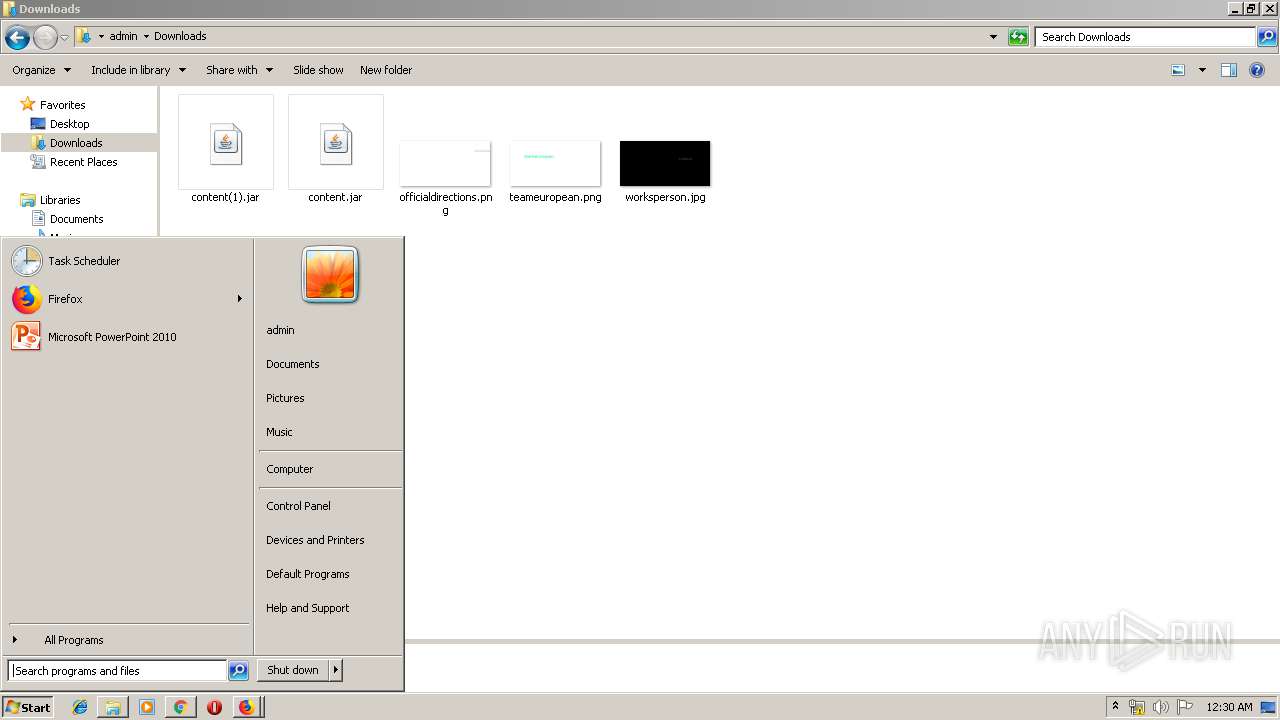
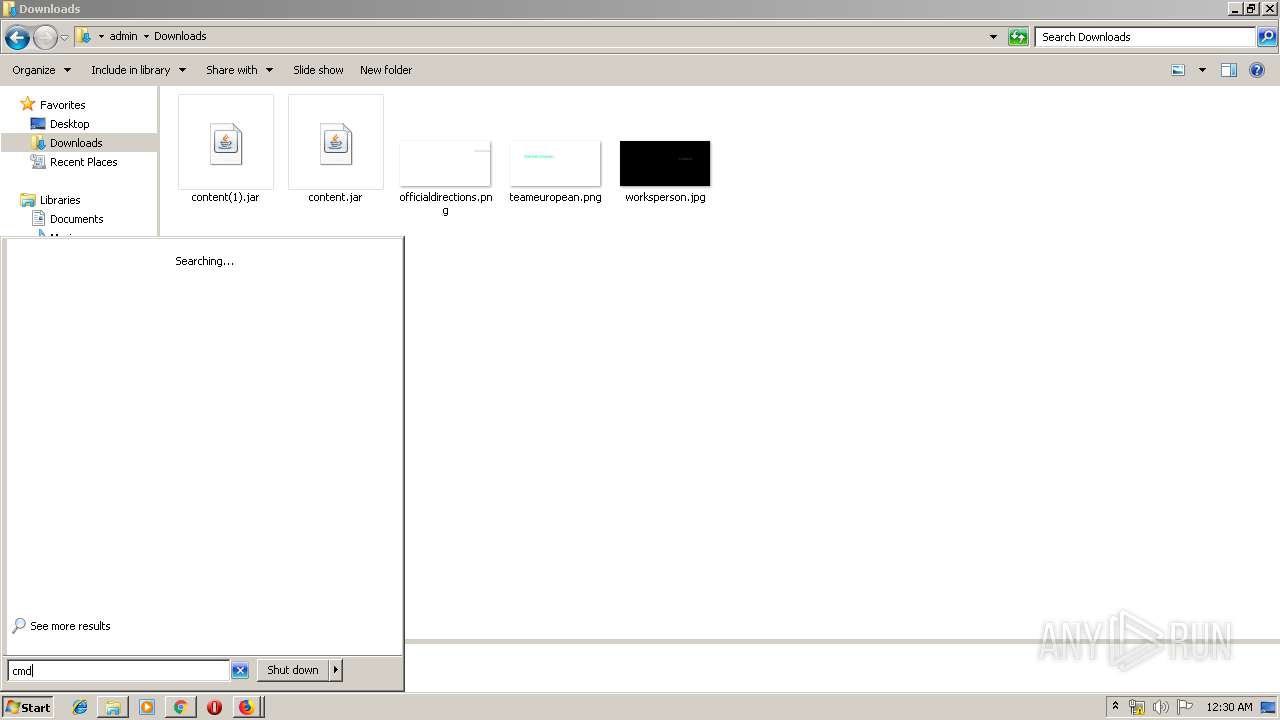
| Analysis date: | May 14, 2019, 23:28:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 04A18D08B0F9589D90398F9AFB30D2C1 |
| SHA1: | 64E7B7BA3F3290F887EE115ADD9626F2FE5B30FA |
| SHA256: | 7F938AD7686F85214A1256BFFE458FC27FC2D483136645EE777AD8331DD0C2C0 |
| SSDEEP: | 6144:yh71ha/iOmxxb7gIZSAED6PU59emYikbVMIKy1NFoM72rdA7yJUpT+Qz9KmlTUtT:yjIIZSpCI+razmrO8zjuJyuobit1ctlo |
MALICIOUS
No malicious indicators.SUSPICIOUS
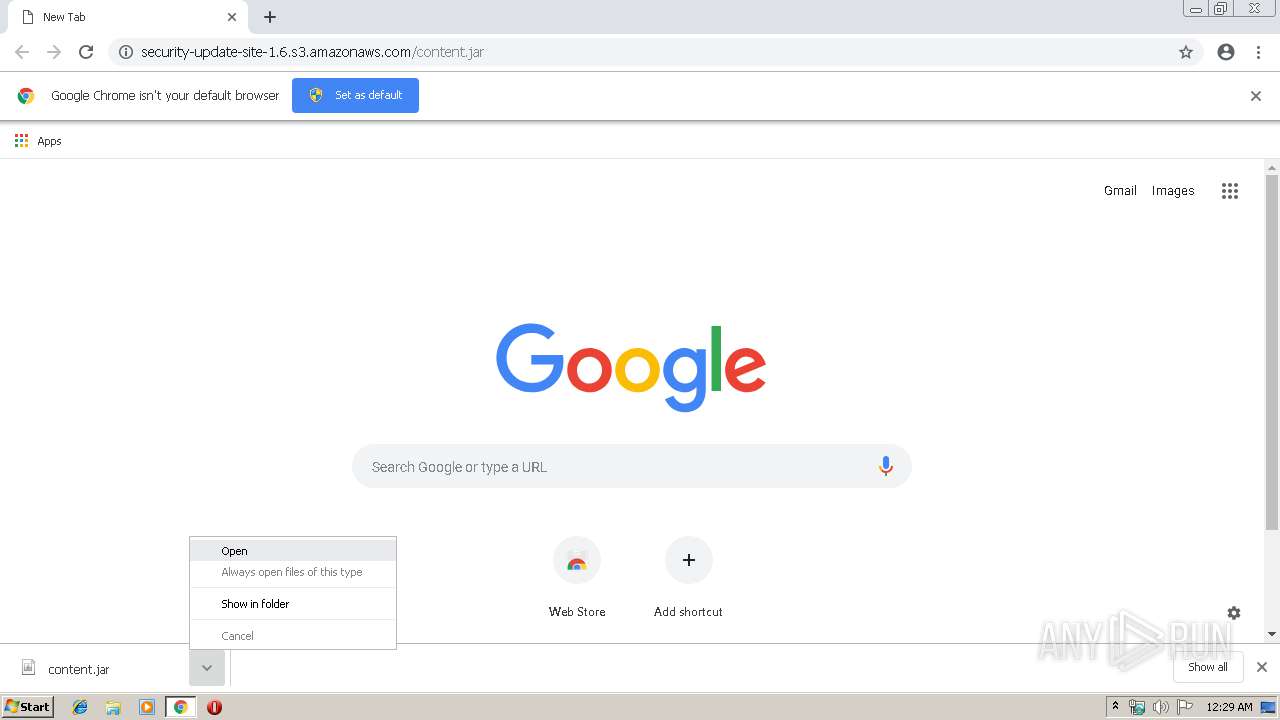
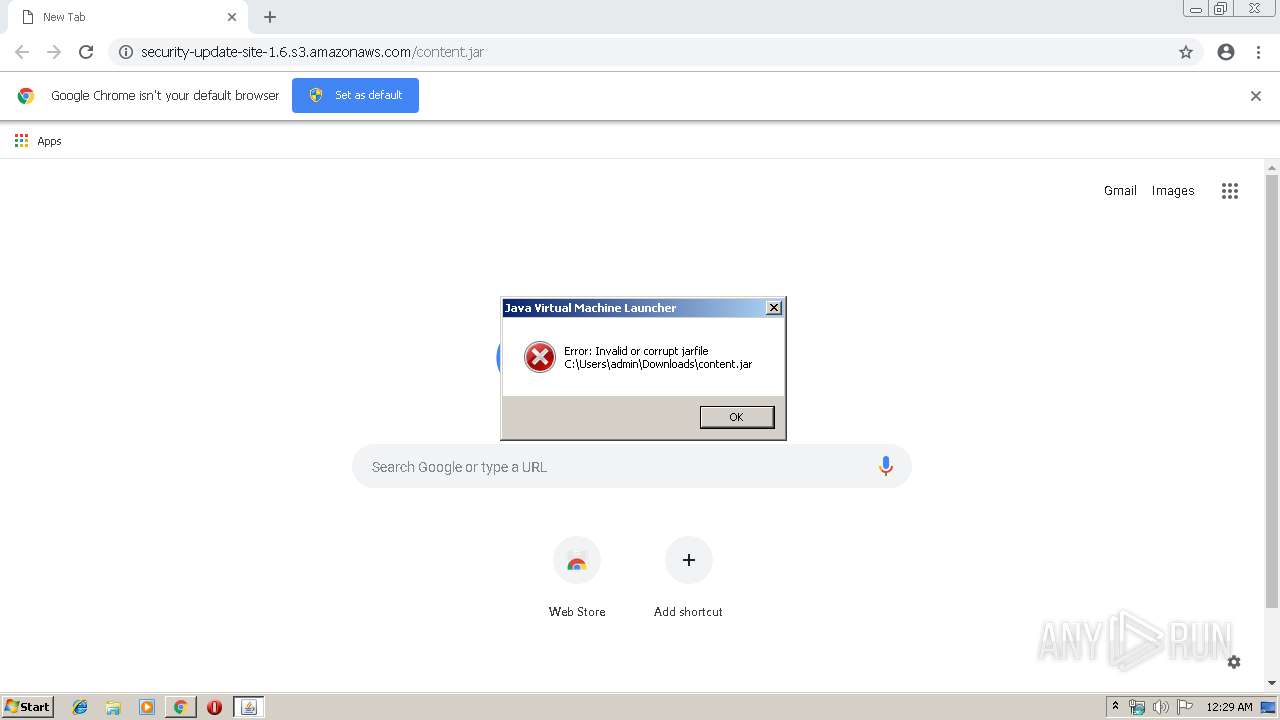
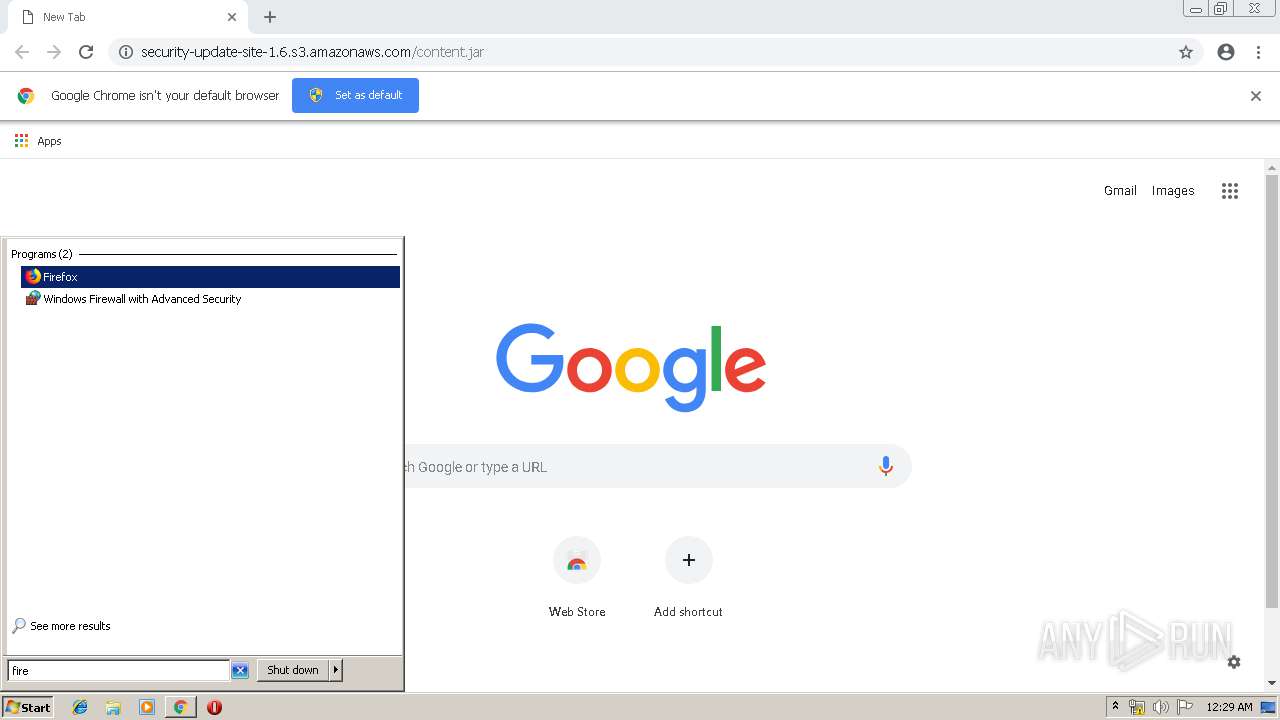
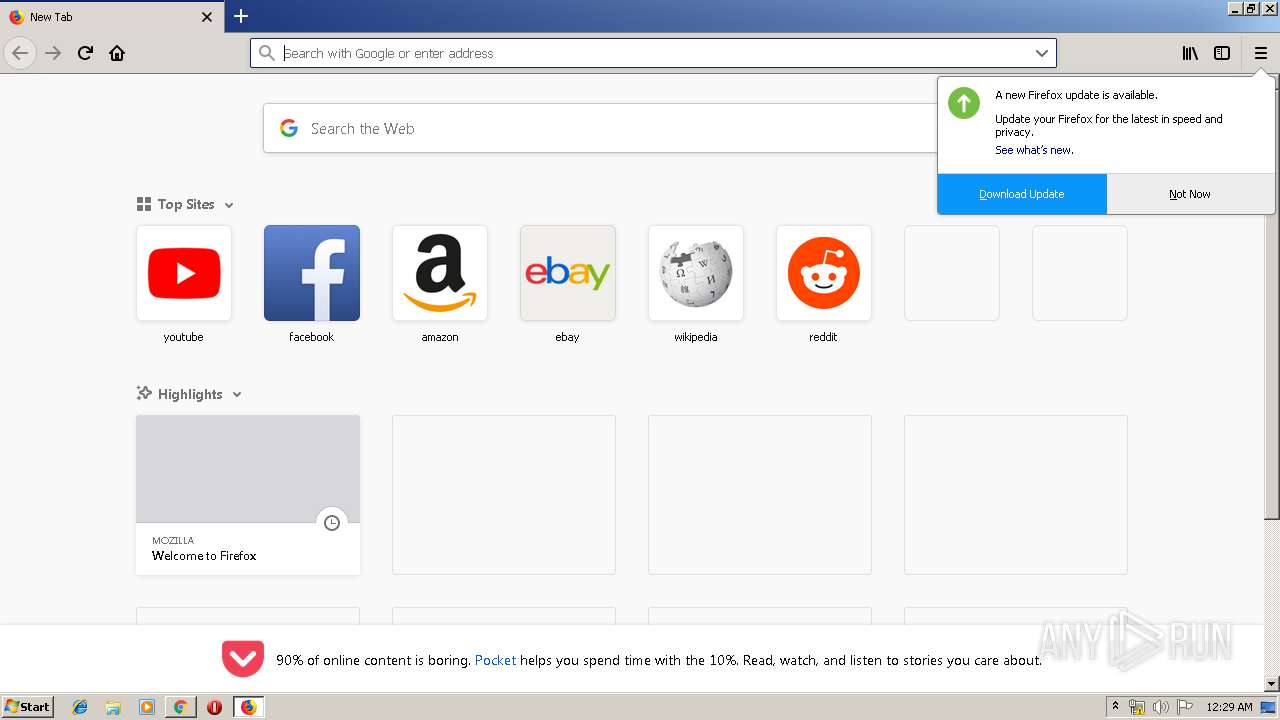
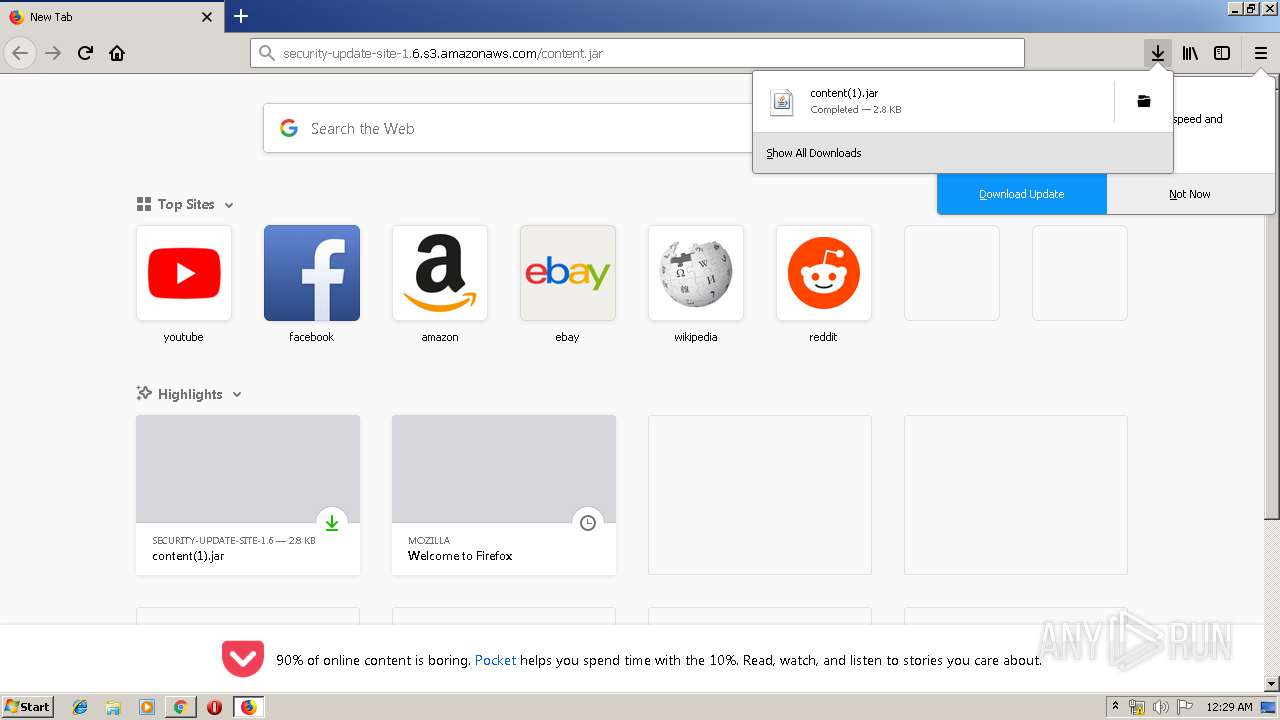
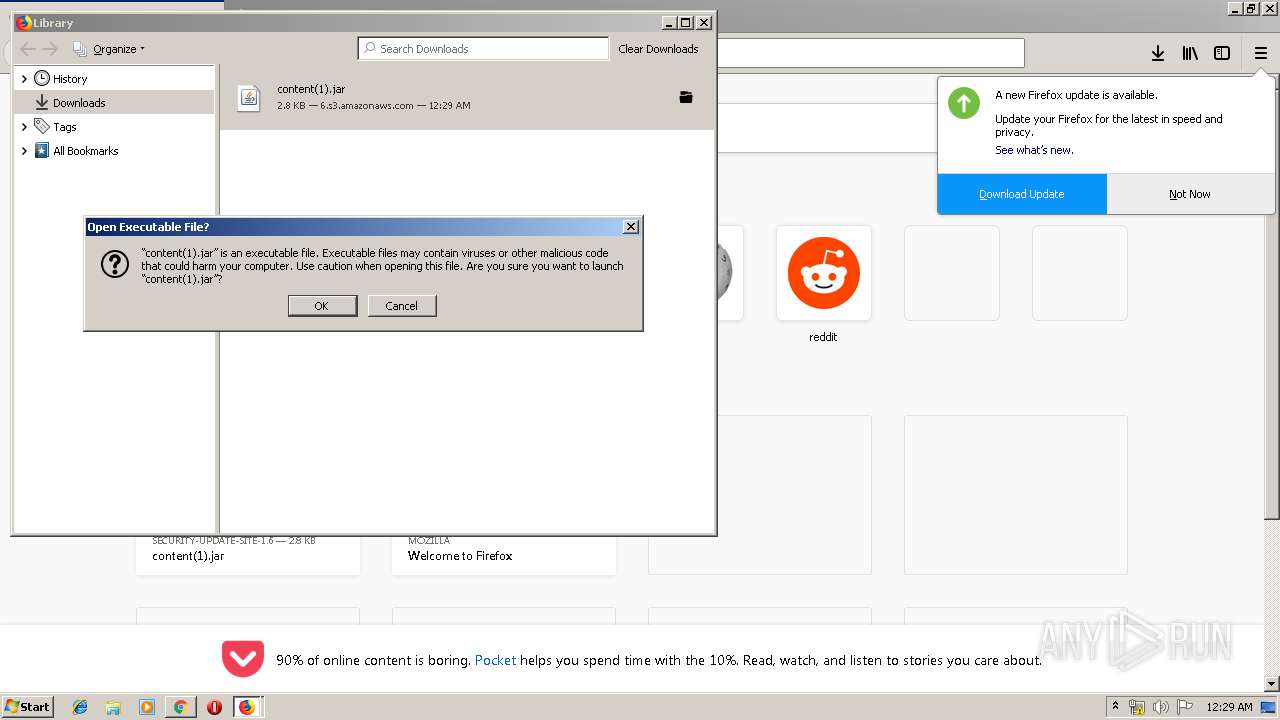
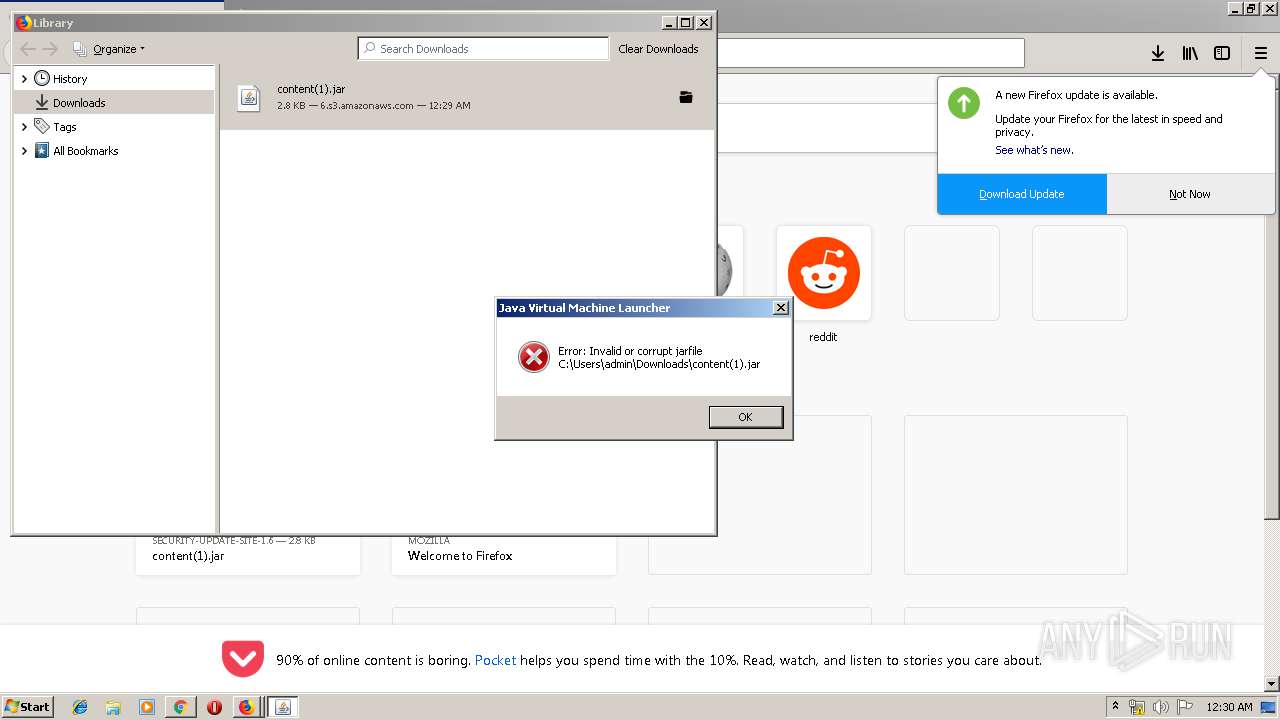
Executes JAVA applets
- chrome.exe (PID: 3764)
- firefox.exe (PID: 2672)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3764)
Creates files in the program directory
- firefox.exe (PID: 2672)
Removes files from Windows directory
- certutil.exe (PID: 600)
Creates files in the Windows directory
- certutil.exe (PID: 600)
INFO
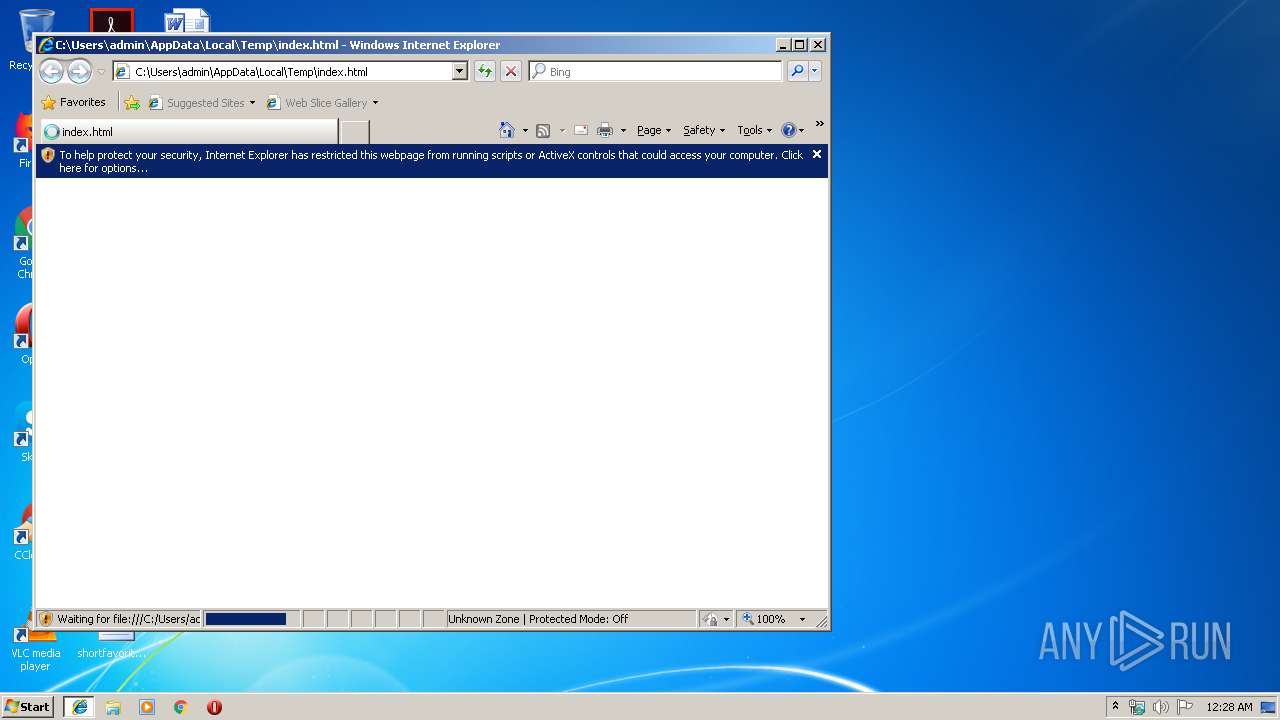
Changes internet zones settings
- iexplore.exe (PID: 2932)
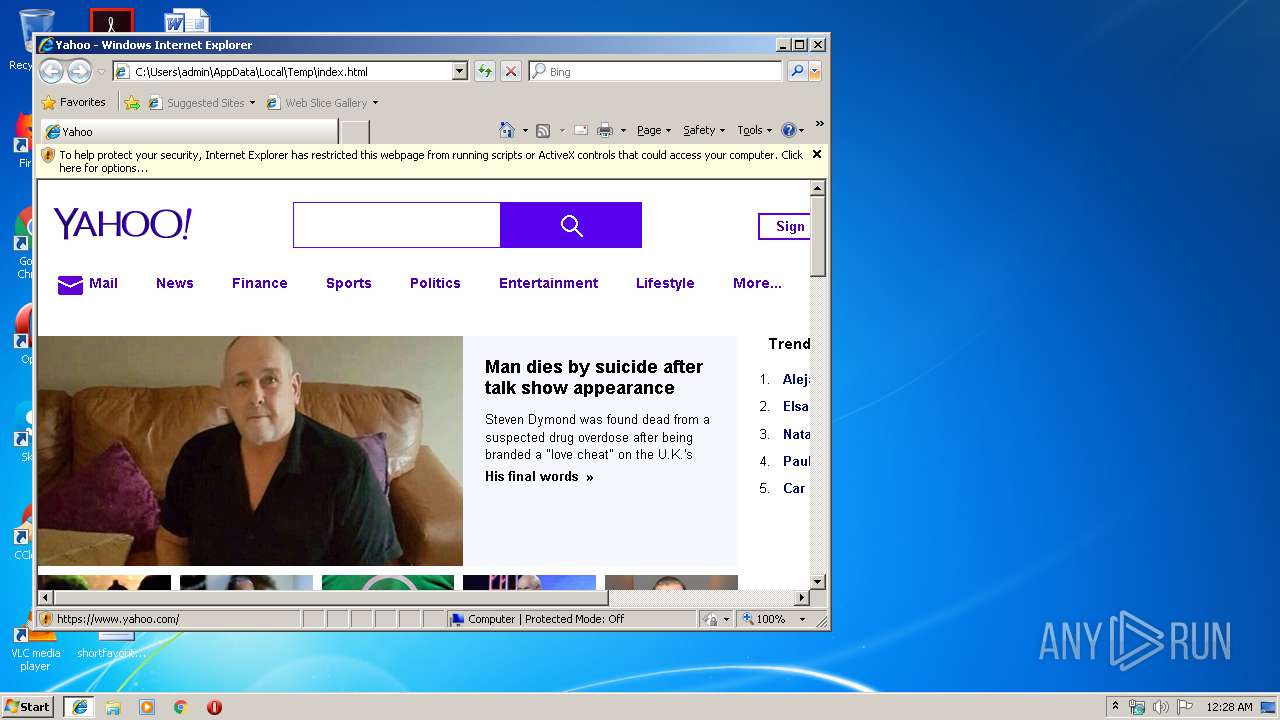
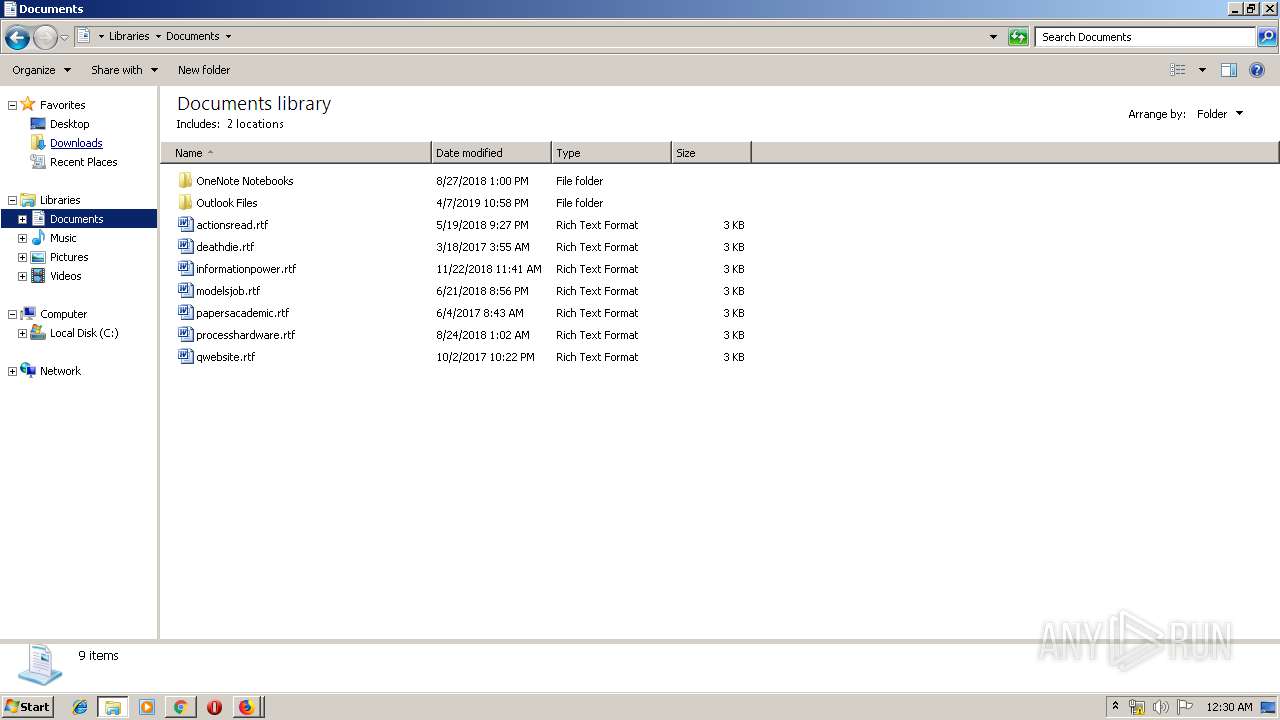
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3332)
- firefox.exe (PID: 2672)
Reads Internet Cache Settings
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 3764)
Creates files in the user directory
- iexplore.exe (PID: 3332)
- firefox.exe (PID: 2672)
- iexplore.exe (PID: 2932)
Changes settings of System certificates
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2932)
Reads internet explorer settings
- iexplore.exe (PID: 3332)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2932)
Application launched itself
- iexplore.exe (PID: 2932)
- firefox.exe (PID: 2672)
- chrome.exe (PID: 3764)
Reads settings of System Certificates
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 3332)
- chrome.exe (PID: 3764)
- firefox.exe (PID: 2672)
Reads CPU info
- firefox.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .aiml | | | Artificial Intelligence Markup Language (48.3) |
|---|---|---|
| .htm/html | | | HyperText Markup Language with DOCTYPE (41.6) |
| .html | | | HyperText Markup Language (9.9) |
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| Title: | Yahoo |
| HTTPEquivXDnsPrefetchControl: | on |
| ContentType: | text/html; charset=utf-8 |
| Description: | News, email and search are just the beginning. Discover more every day. Find your yodel. |
| Keywords: | yahoo, yahoo home page, yahoo homepage, yahoo search, yahoo mail, yahoo messenger, yahoo games, news, finance, sport, entertainment |
| formatDetection: | telephone=no |
| themeColor: | #400090 |
| referrer: | unsafe-url |
| oathGuceConsentHost: | guce.yahoo.com |
Total processes
82
Monitored processes
39
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
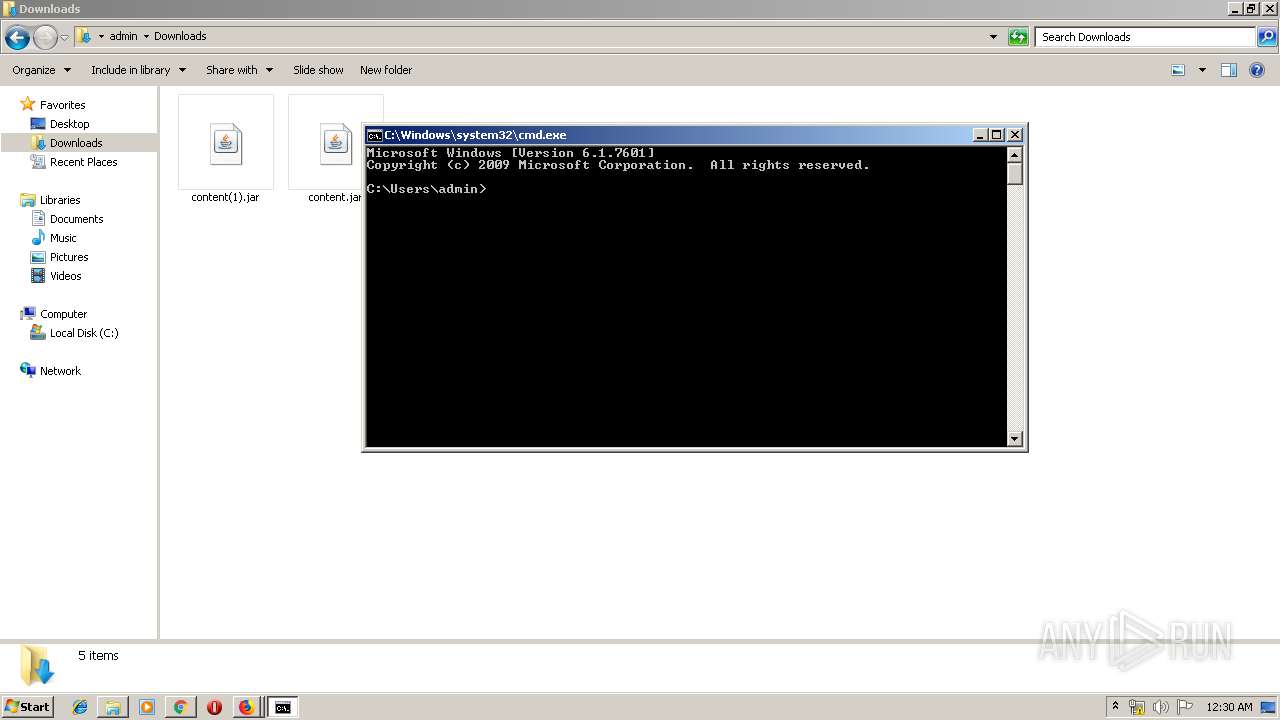
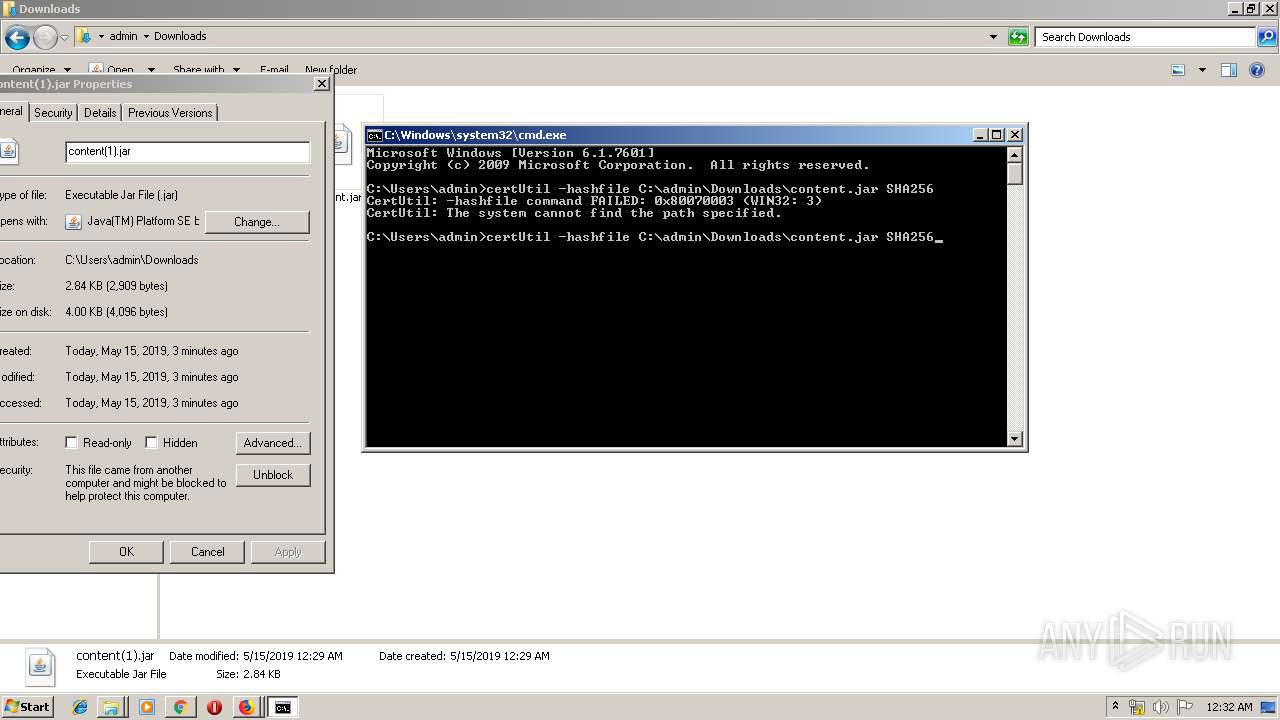
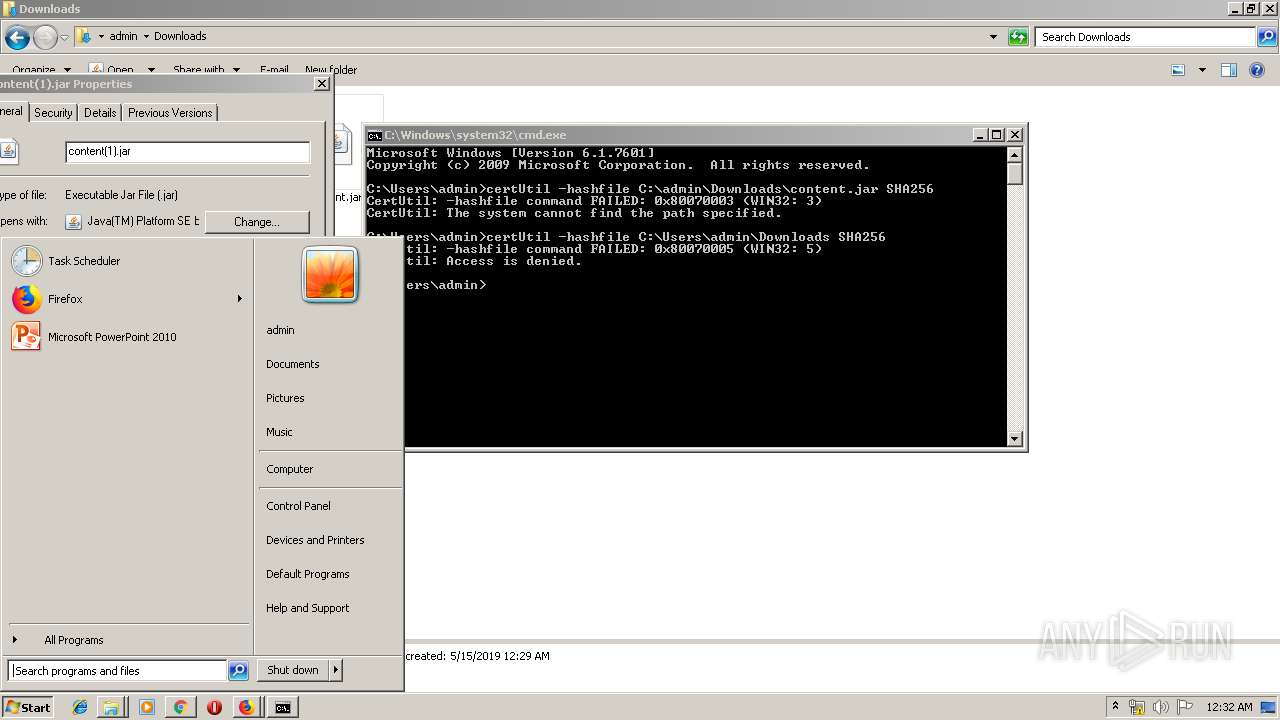
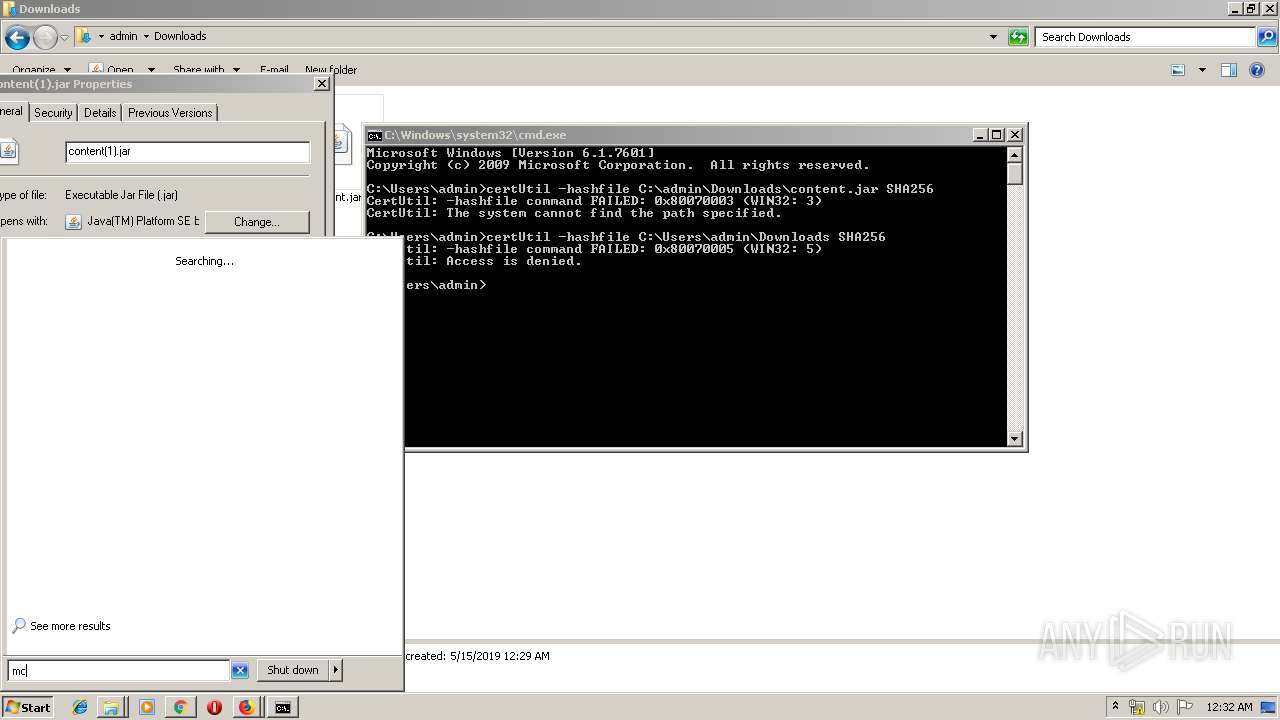
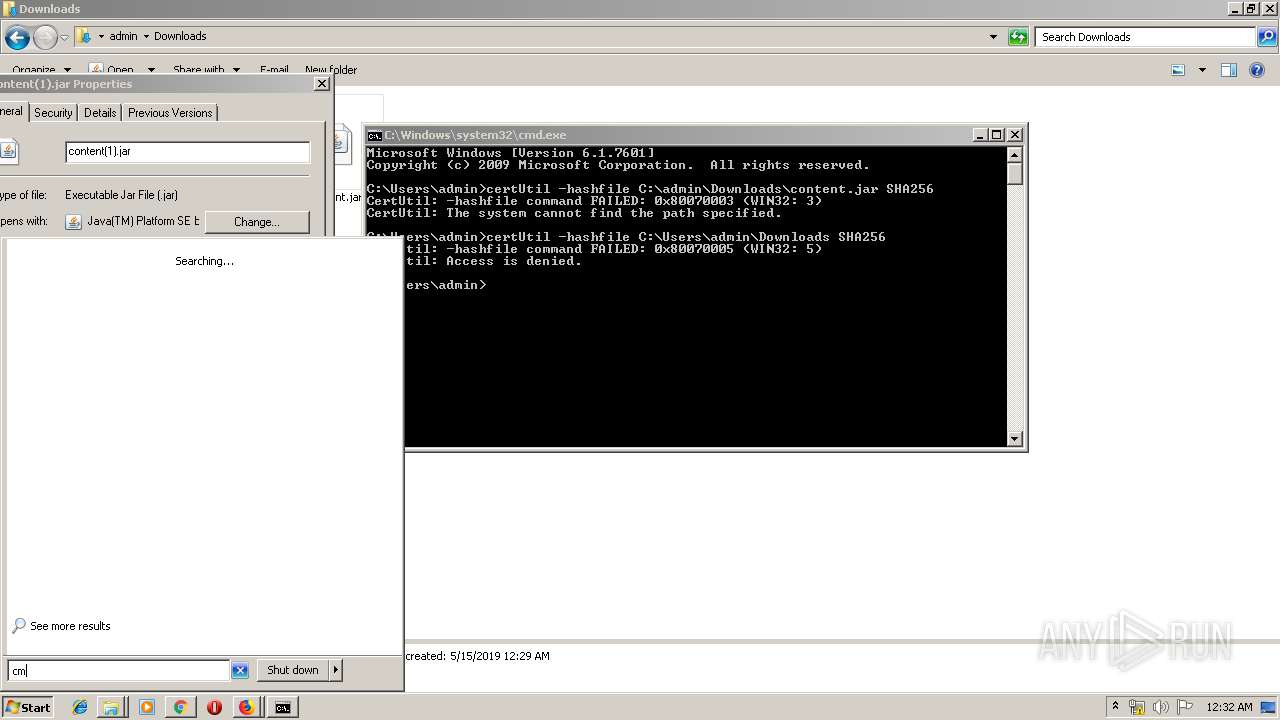
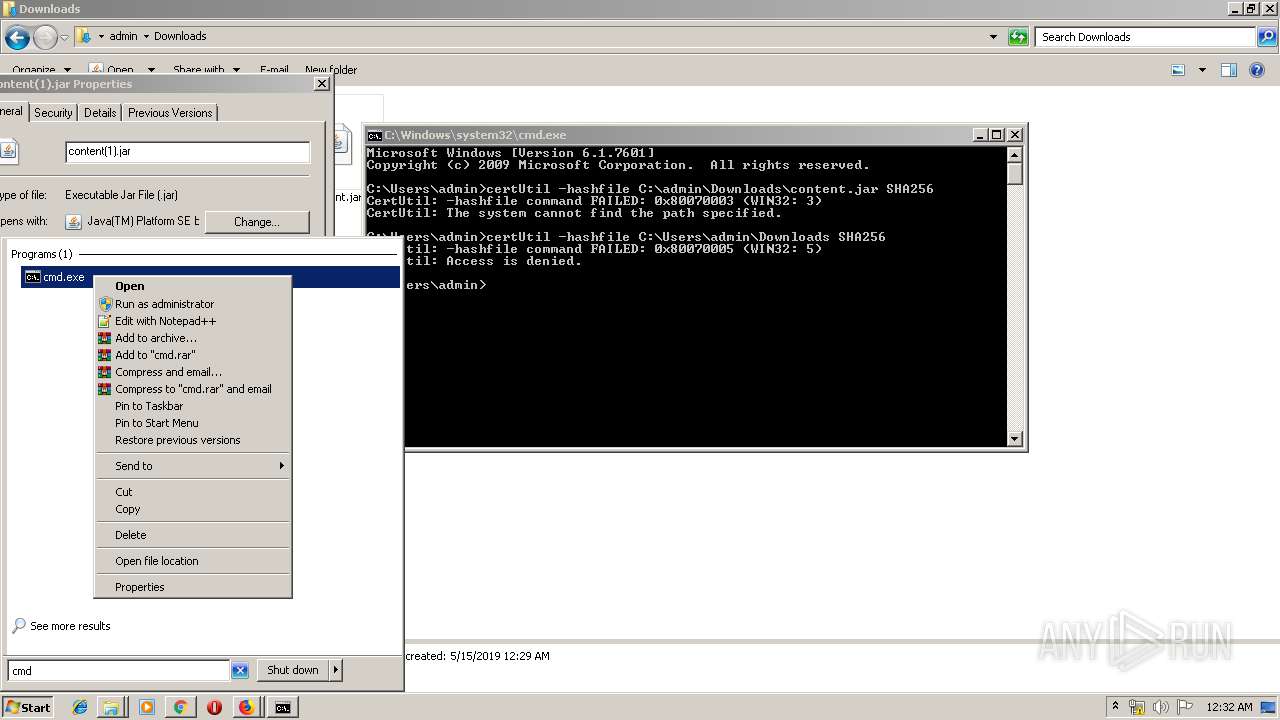
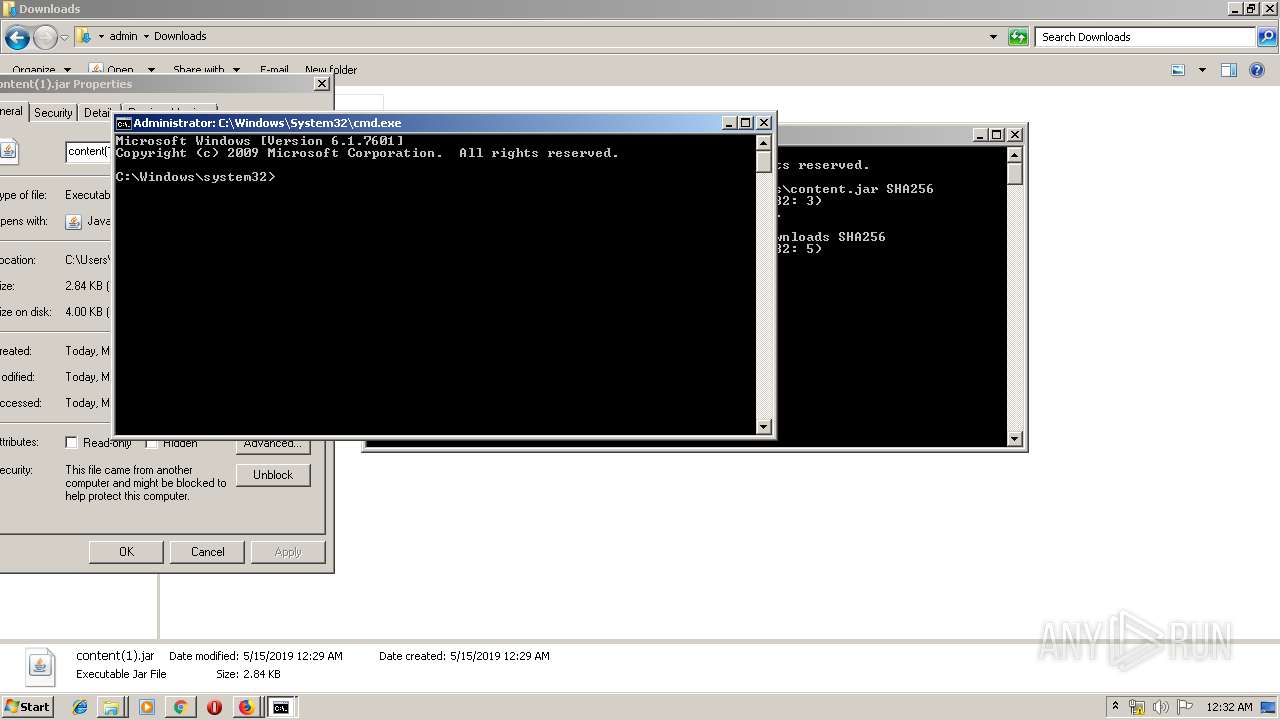
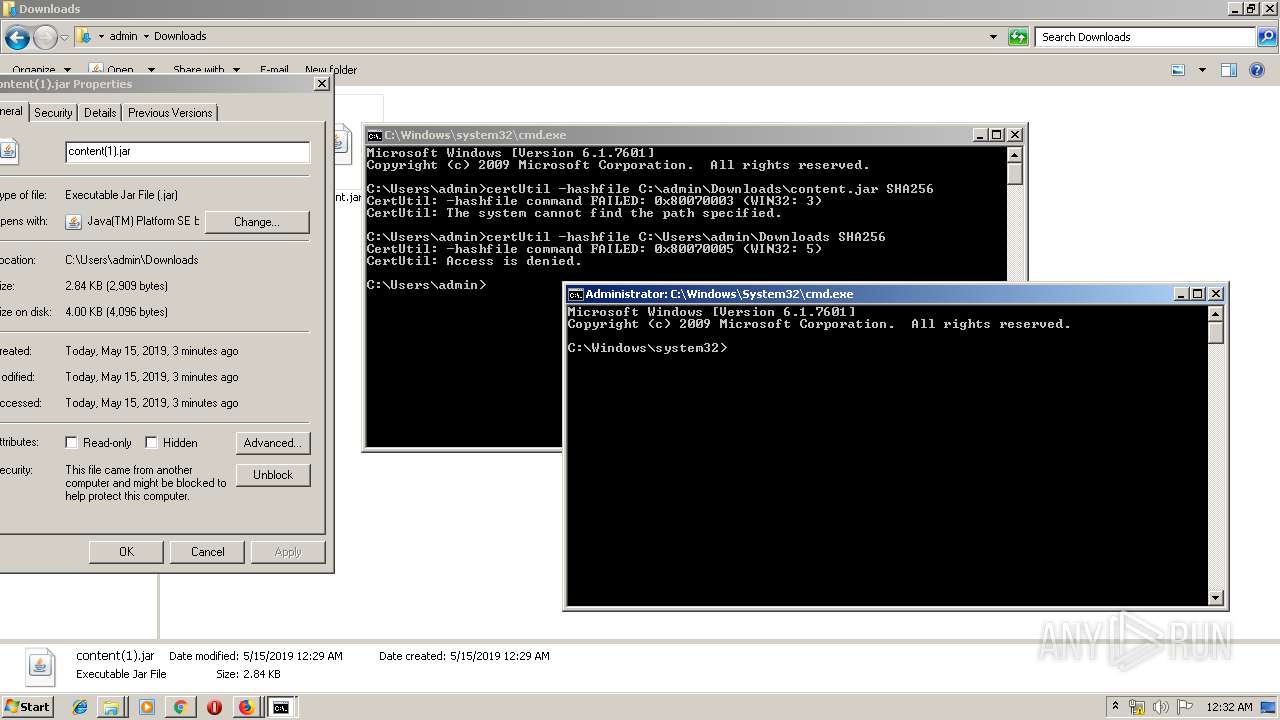
| 236 | certUtil -hashfile C:\Users\admin\Downloads SHA256 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 2147942405 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
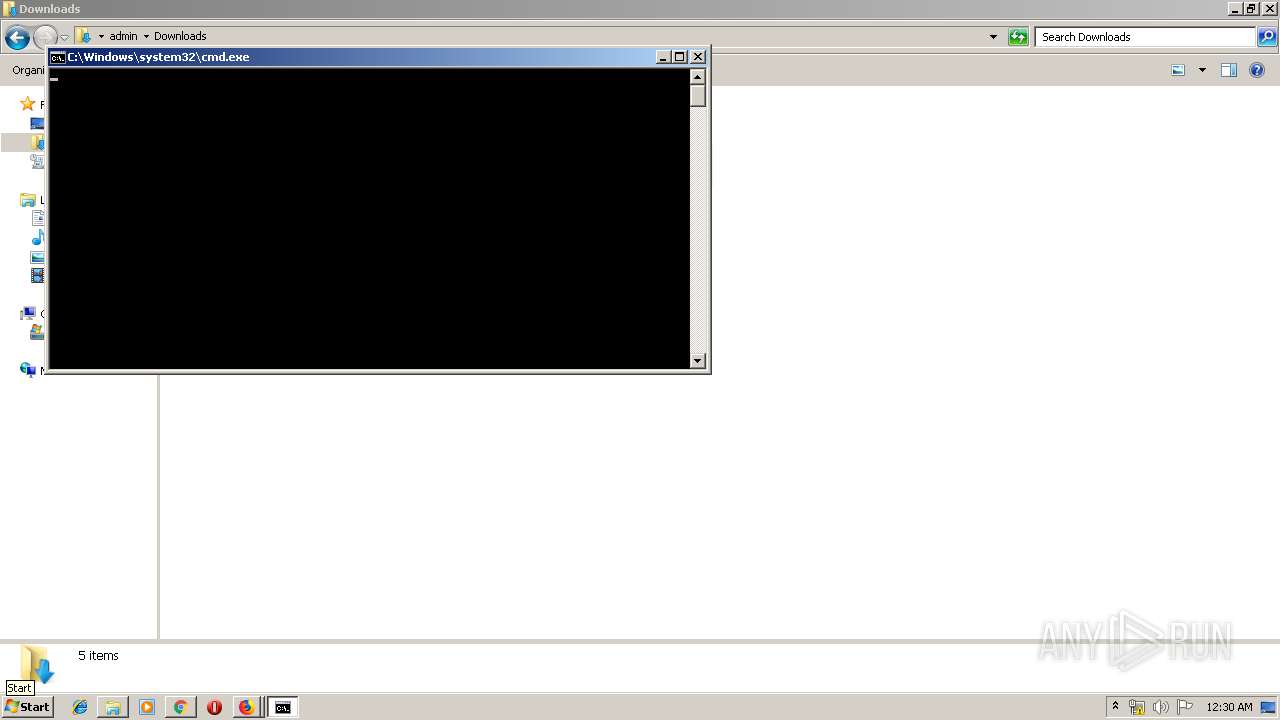
| 304 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 344 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2672.0.70782472\929440999" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 2672 "\\.\pipe\gecko-crash-server-pipe.2672" 1144 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,10304255533118857801,10437070051982360506,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1912094084465933472 --mojo-platform-channel-handle=4732 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 568 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | certUtil -hashfile C;\Users\admin\Downloads SHA256 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 2147942403 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10304255533118857801,10437070051982360506,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2393254684837294489 --mojo-platform-channel-handle=2820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10304255533118857801,10437070051982360506,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7421356483865110472 --mojo-platform-channel-handle=4220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
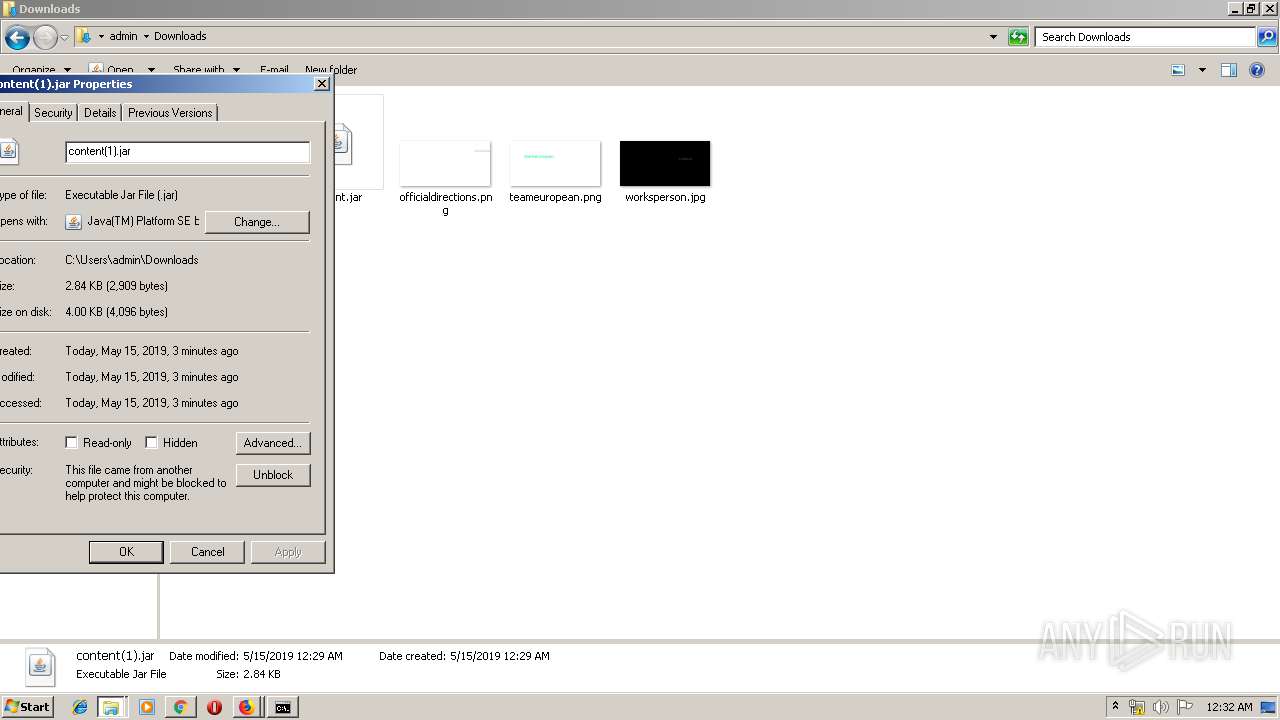
| 2132 | certUtil -hashfile C:\admin\Downloads\content.jar SHA256 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 2147942403 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10304255533118857801,10437070051982360506,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13414679331511033752 --mojo-platform-channel-handle=4828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 369
Read events
2 136
Write events
217
Delete events
16
Modification events
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {F8D8BE67-769F-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050002000E0017001C001B009602 | |||
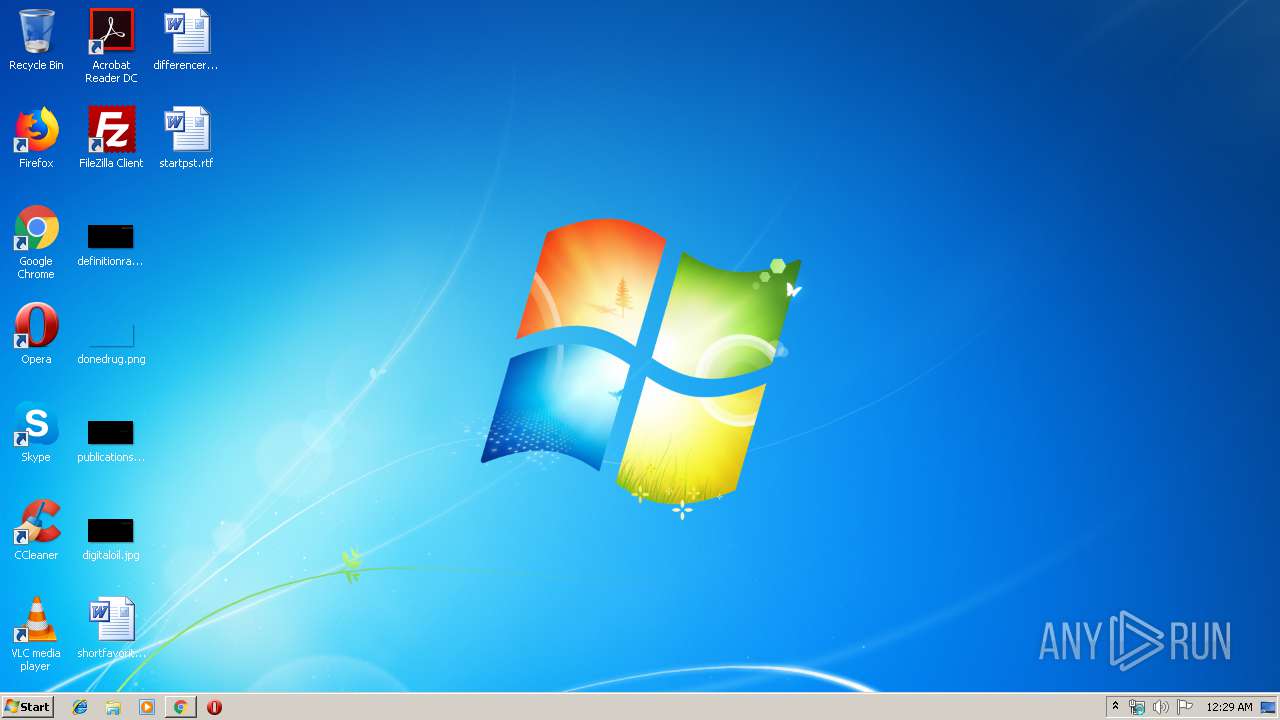
Executable files
5
Suspicious files
97
Text files
273
Unknown types
44
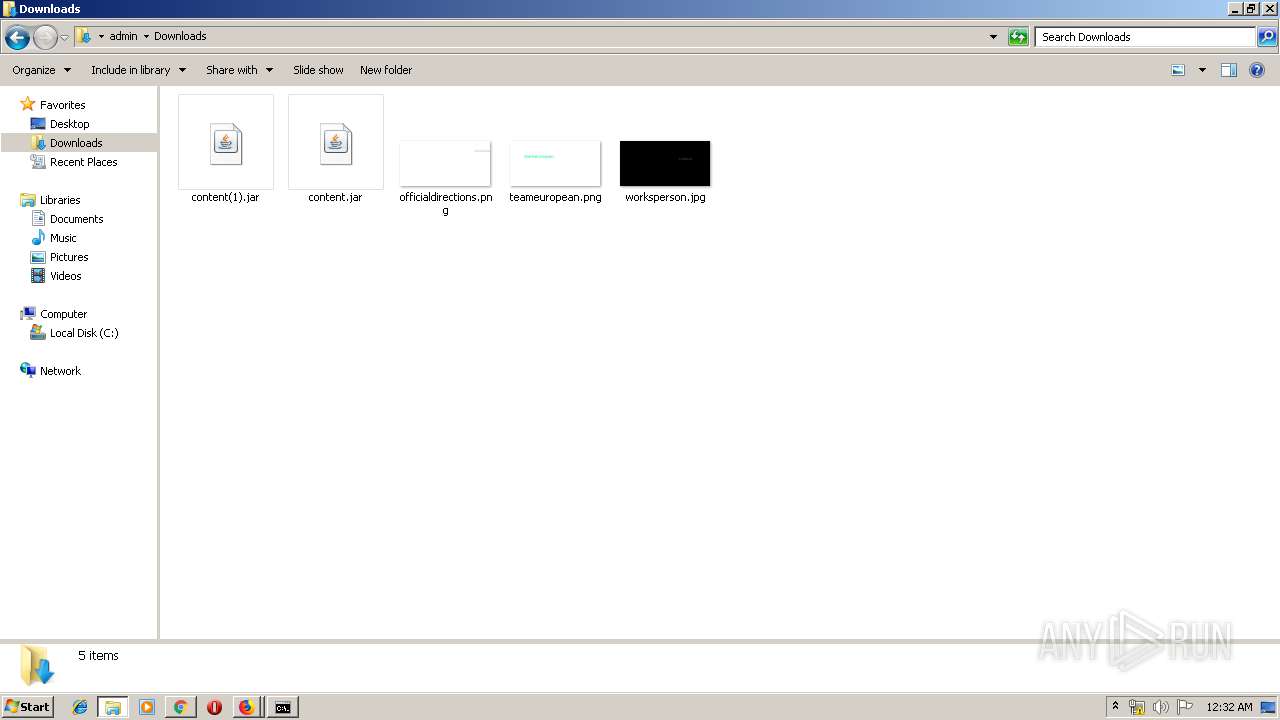
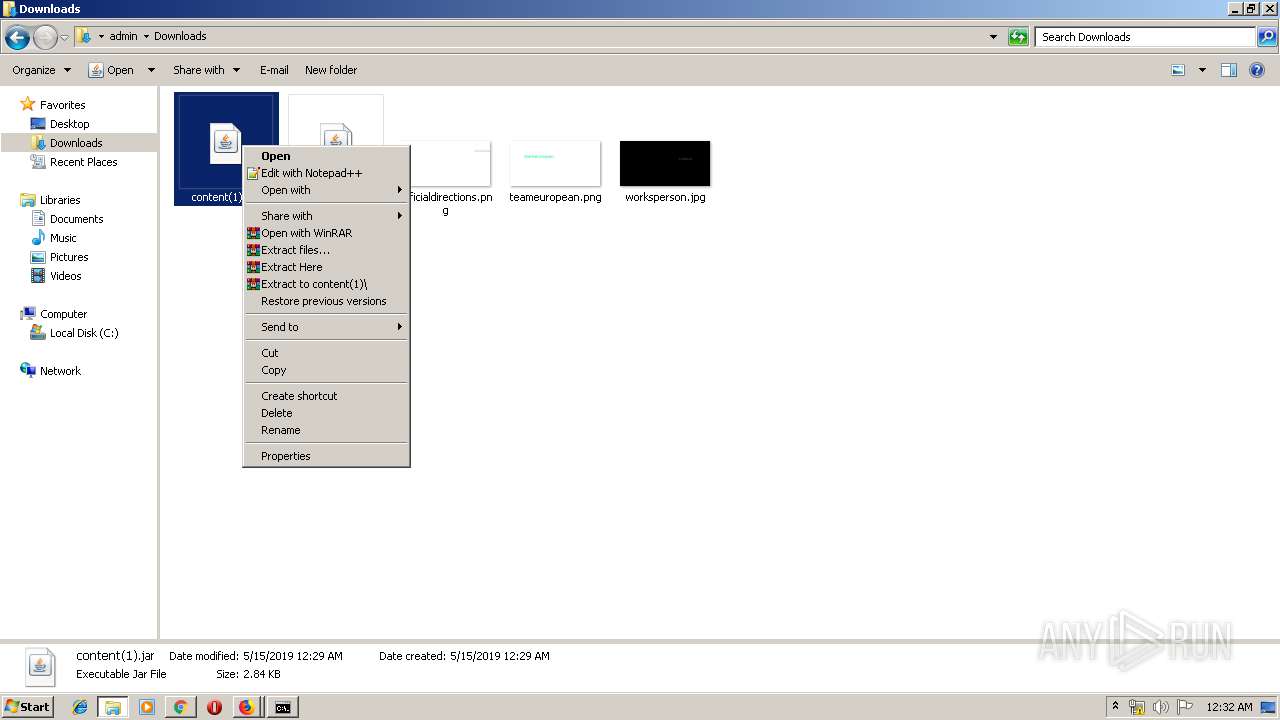
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\custom.desktop.c5483352[1].css | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\atomic.desktop.ltr.2eb82ff5[1].css | text | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\font_rc4_0.0.91[1].css | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\fp_sda_0.0.30[1].css | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\advance_color_0.0.31[1].css | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\atomic-css.ebf87f46[1].css | text | |
MD5:— | SHA256:— | |||
| 3332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\yahoo20_fixed_grid_0.0.33[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
62
DNS requests
95
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
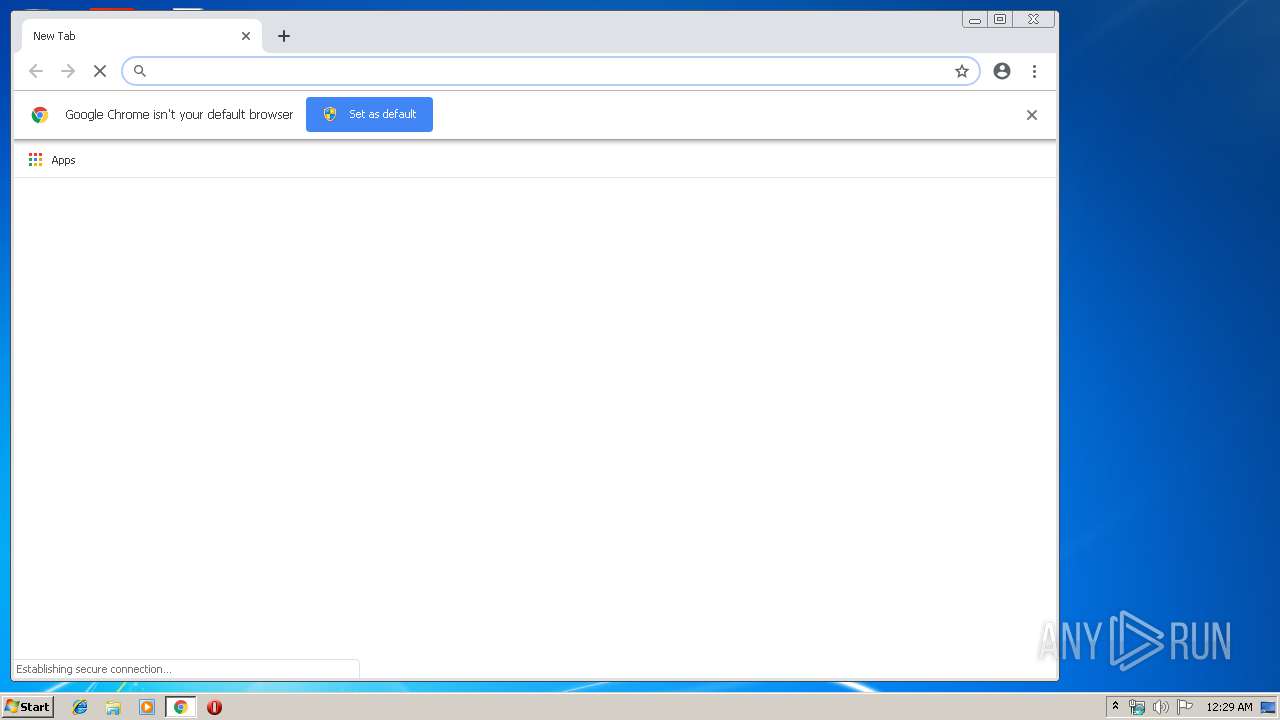
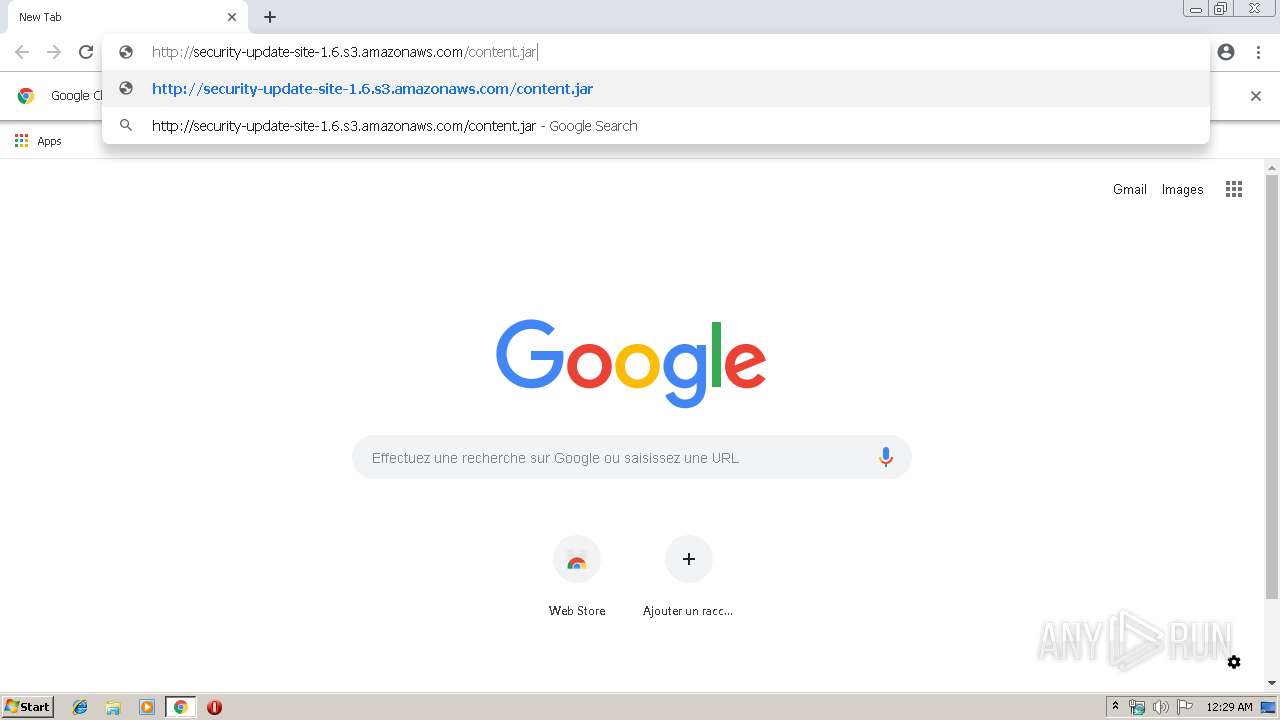
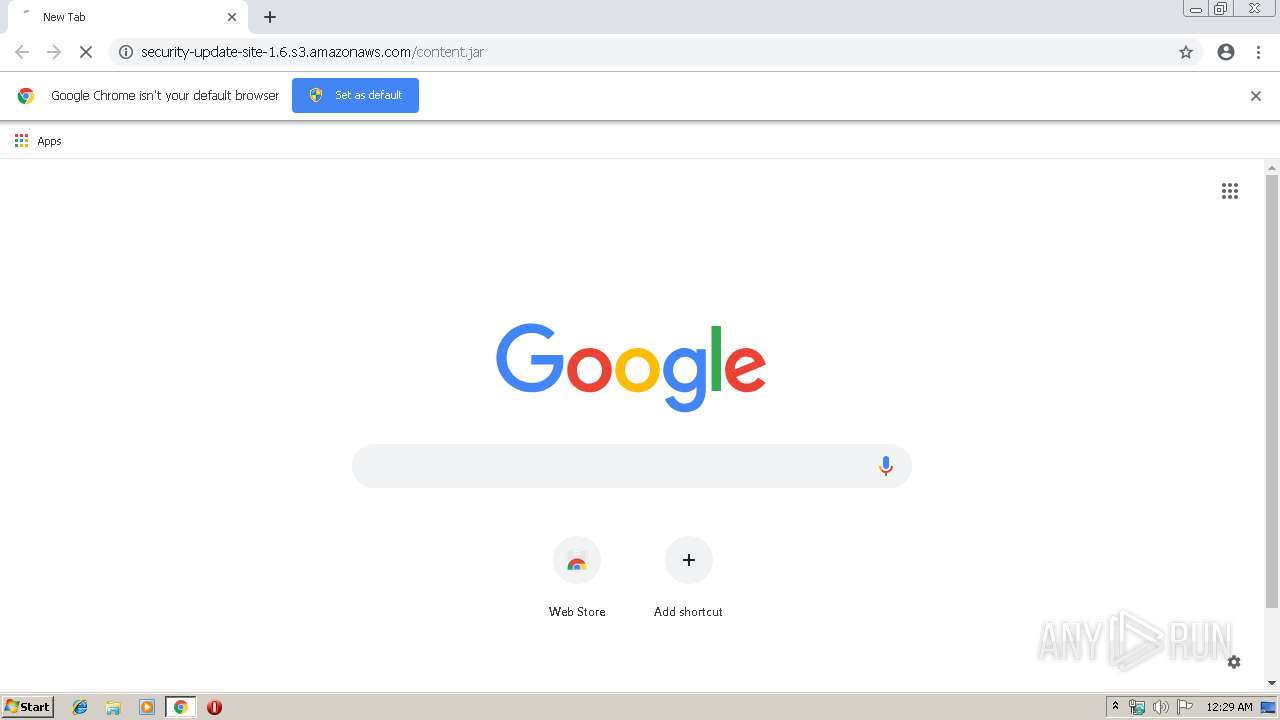
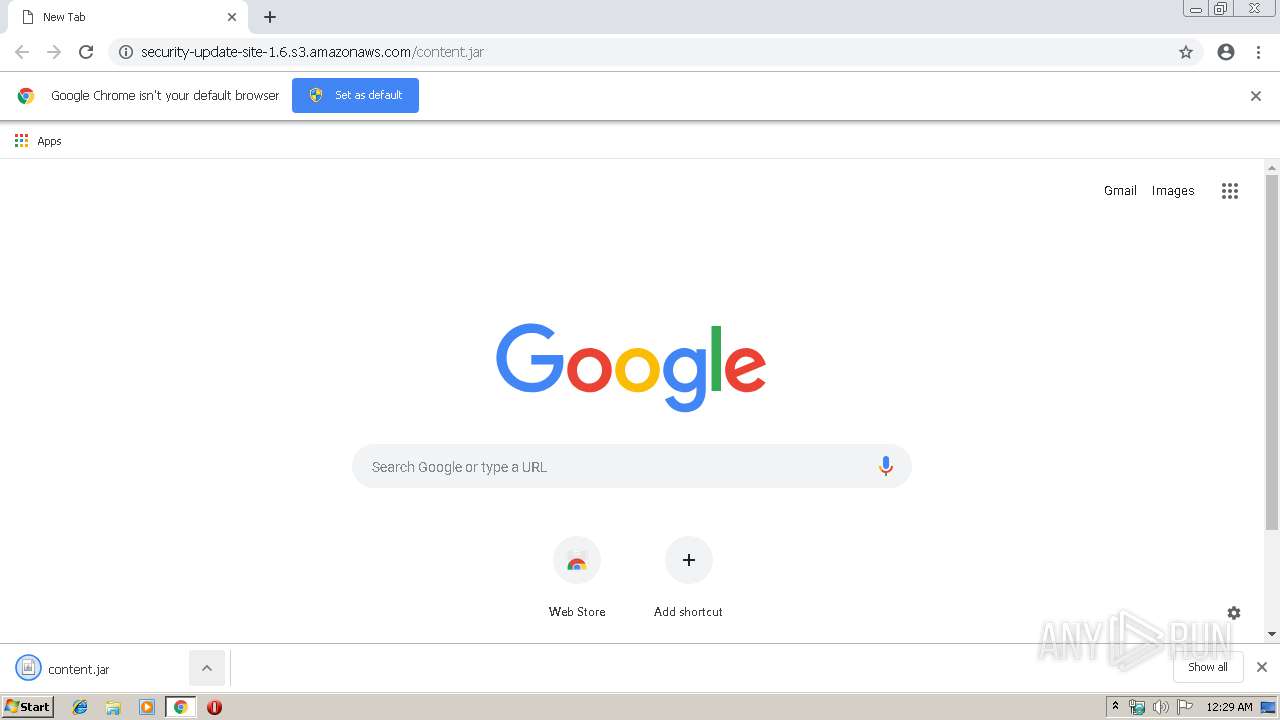
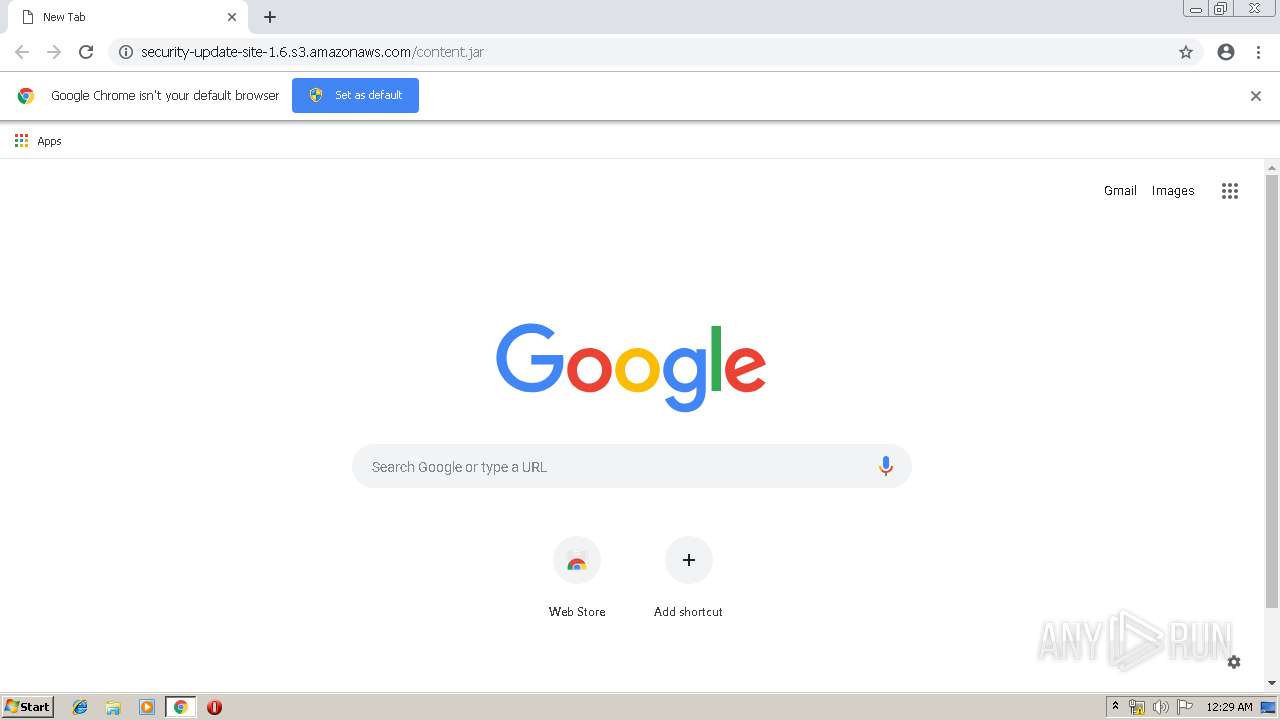
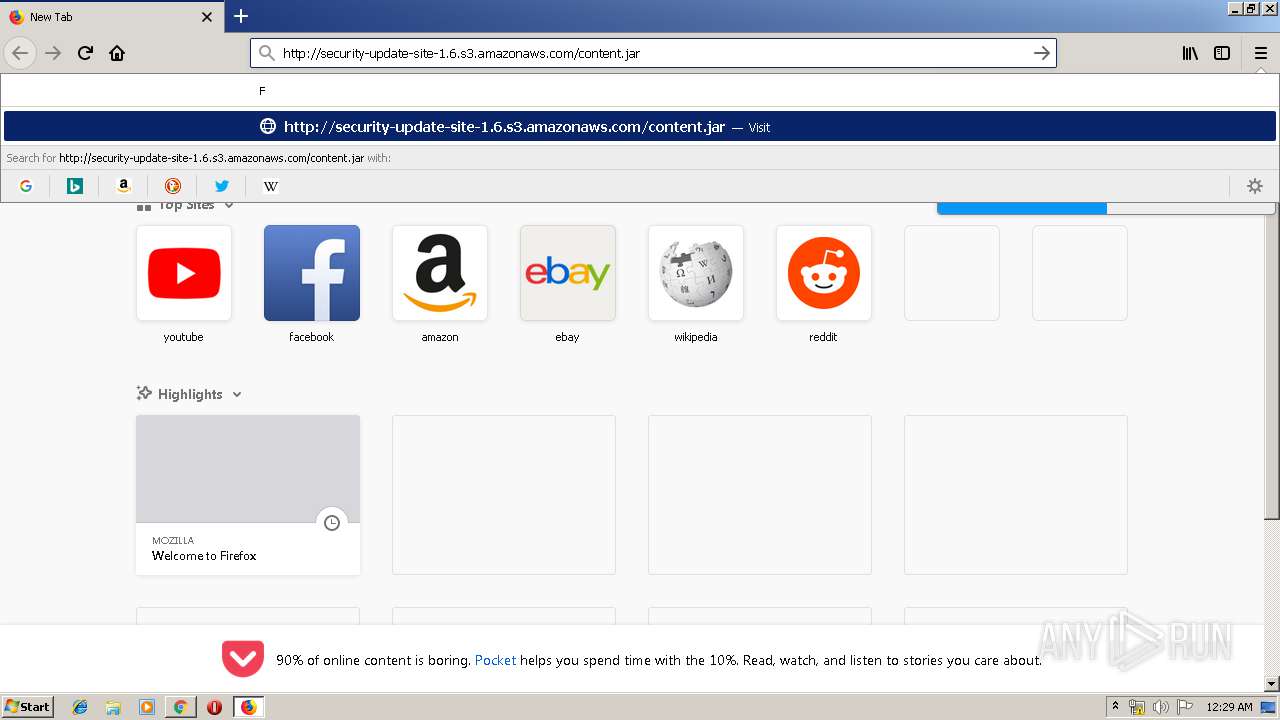
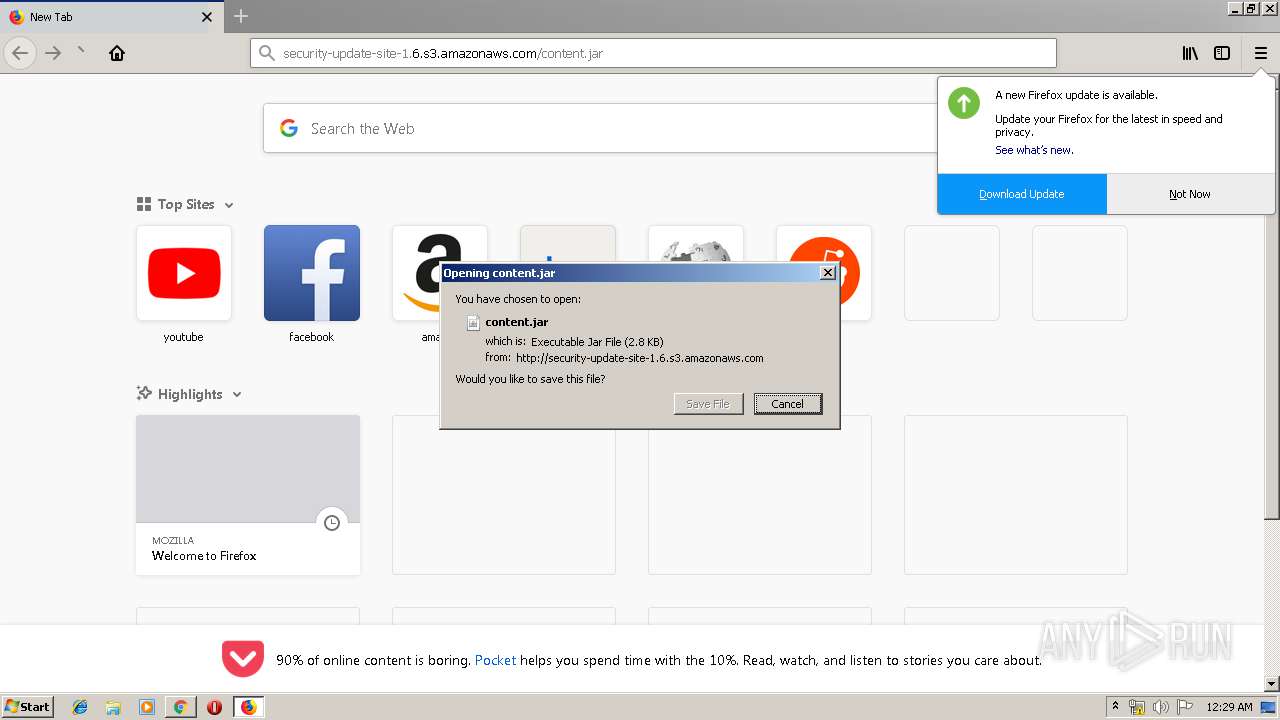
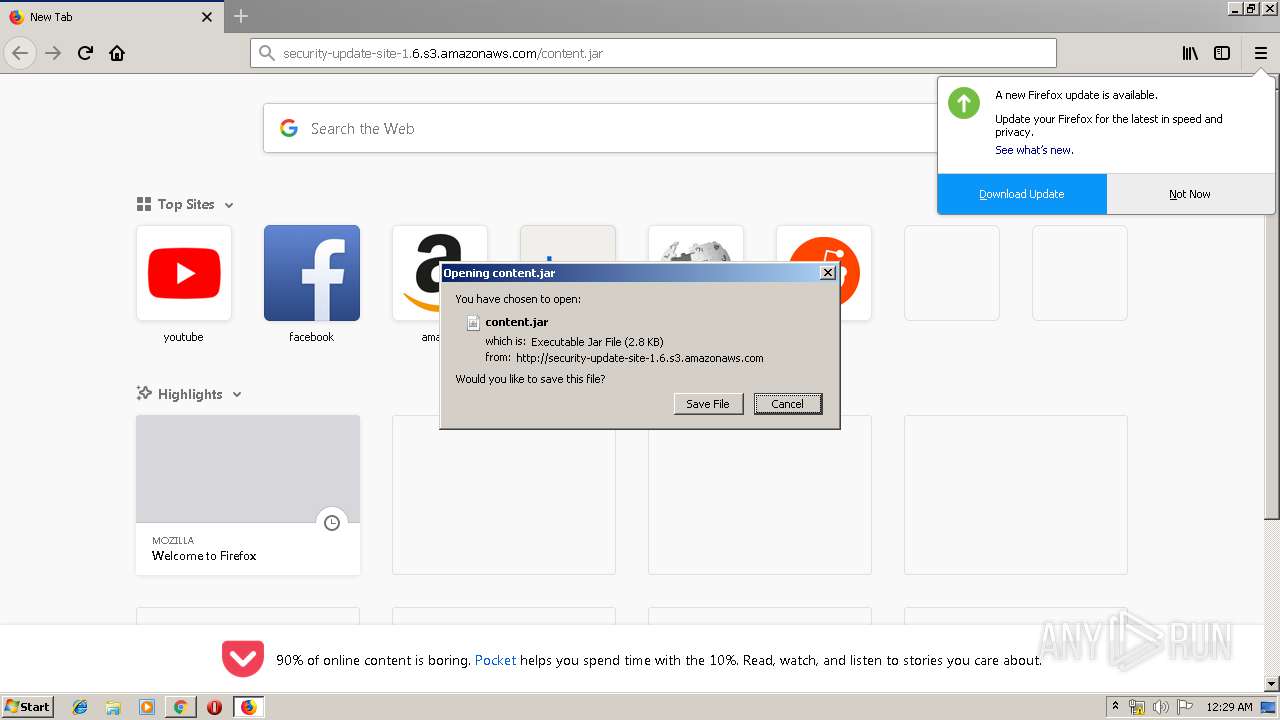
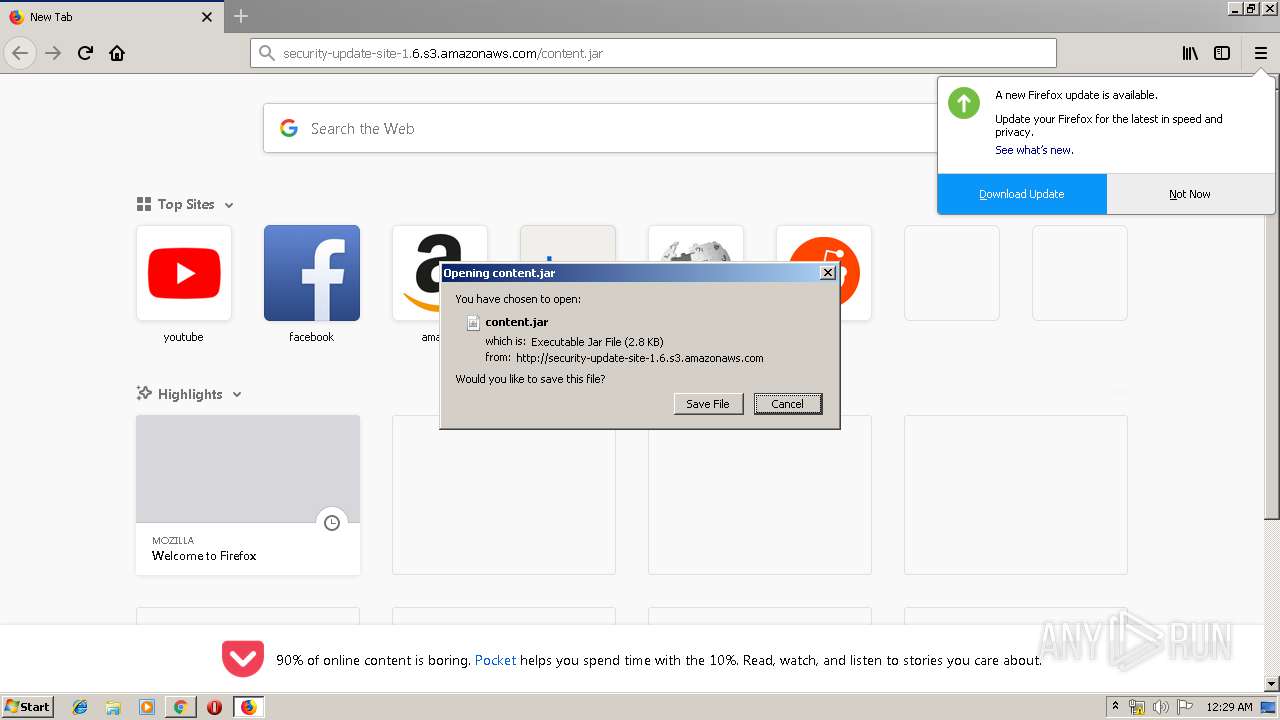
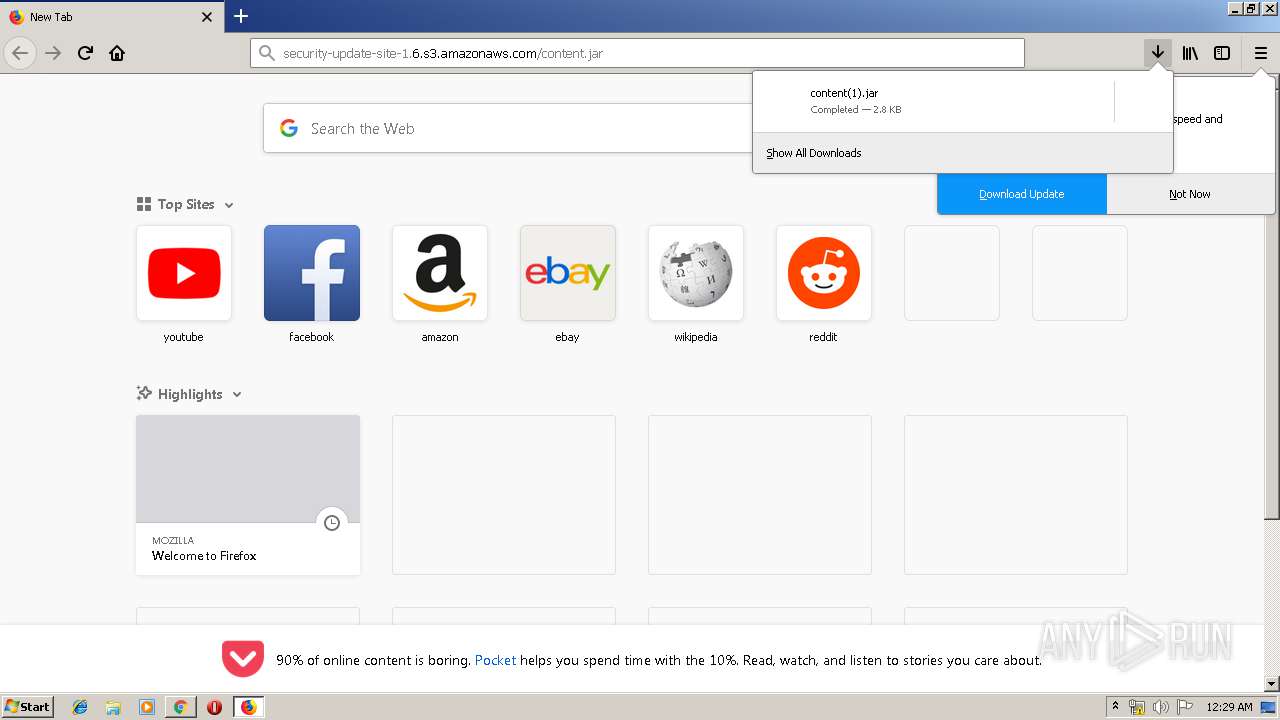
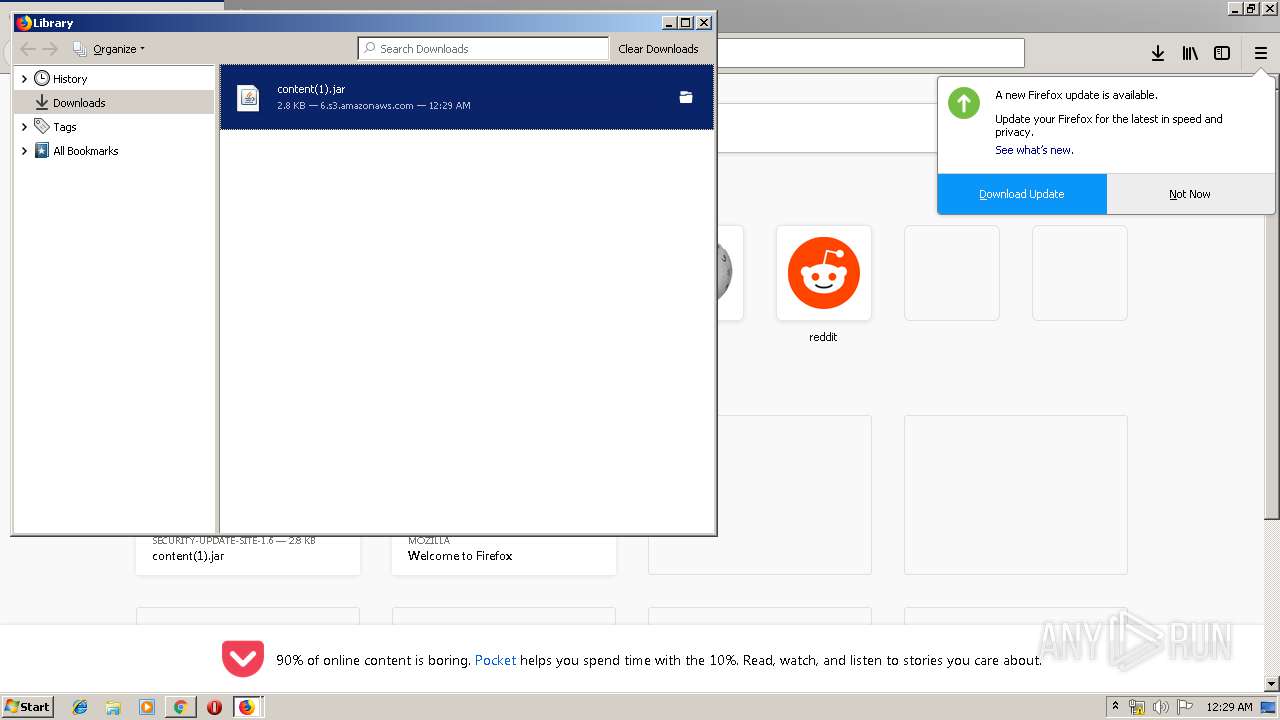
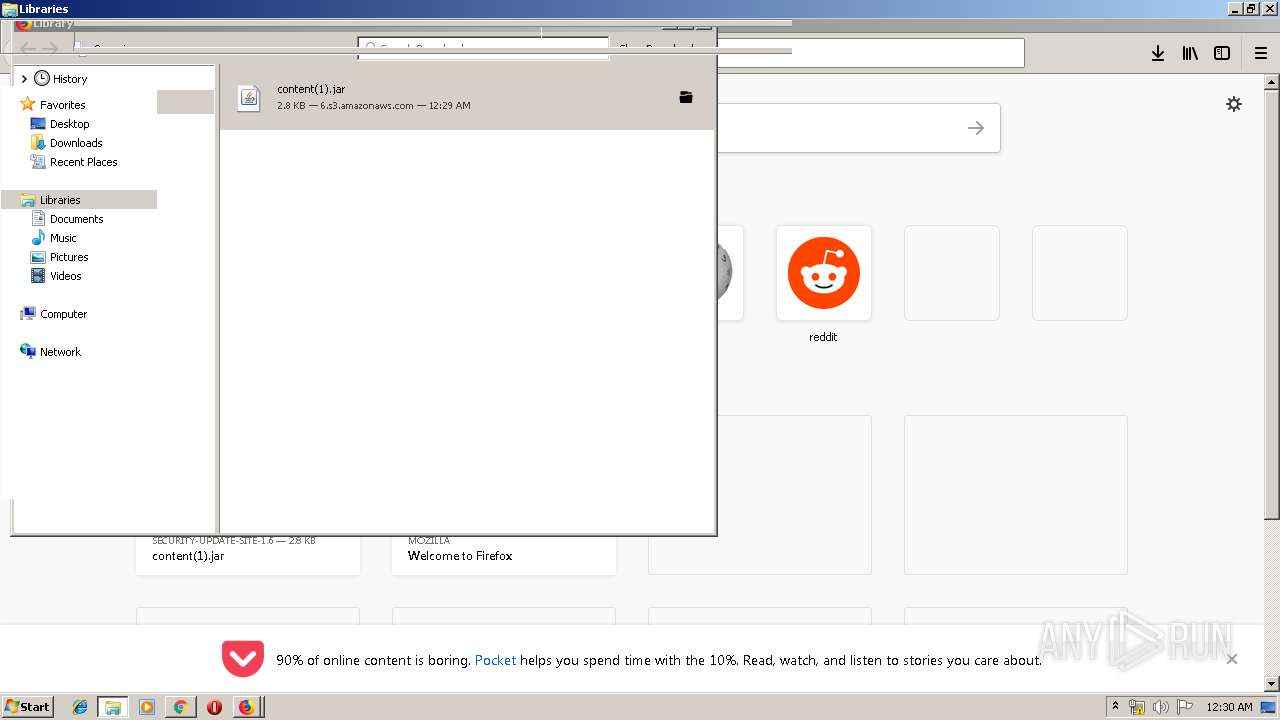
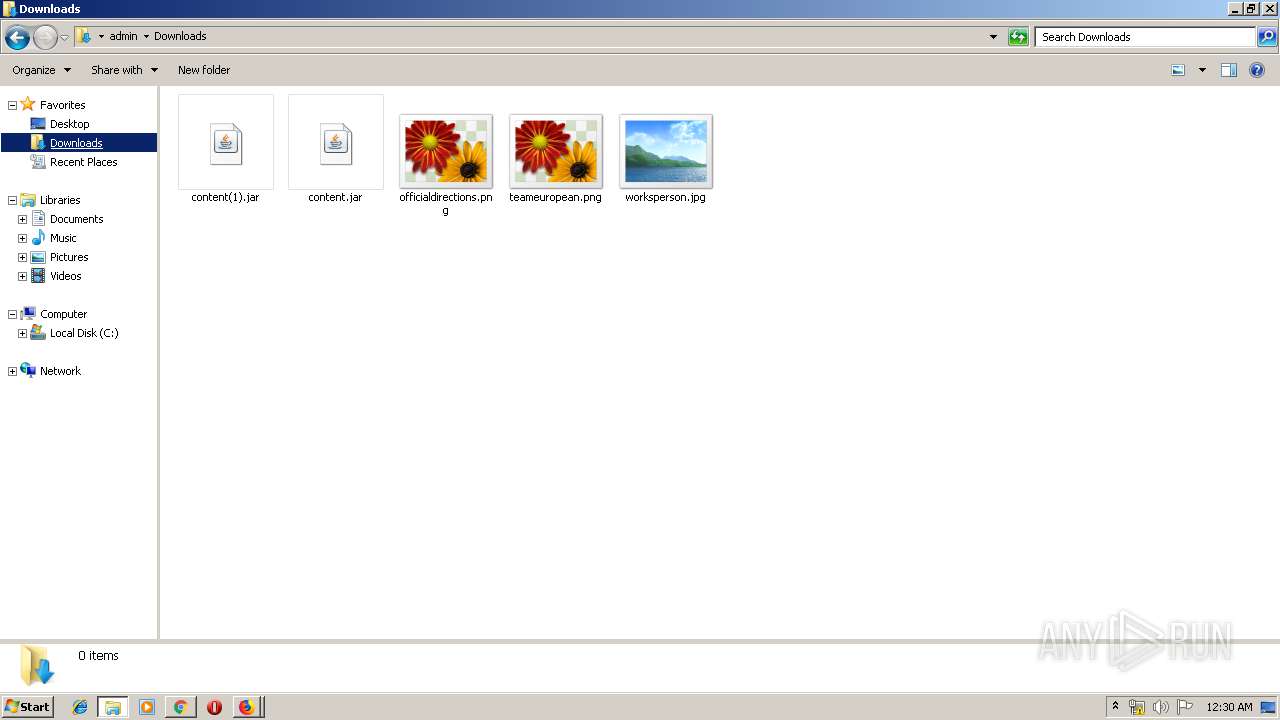
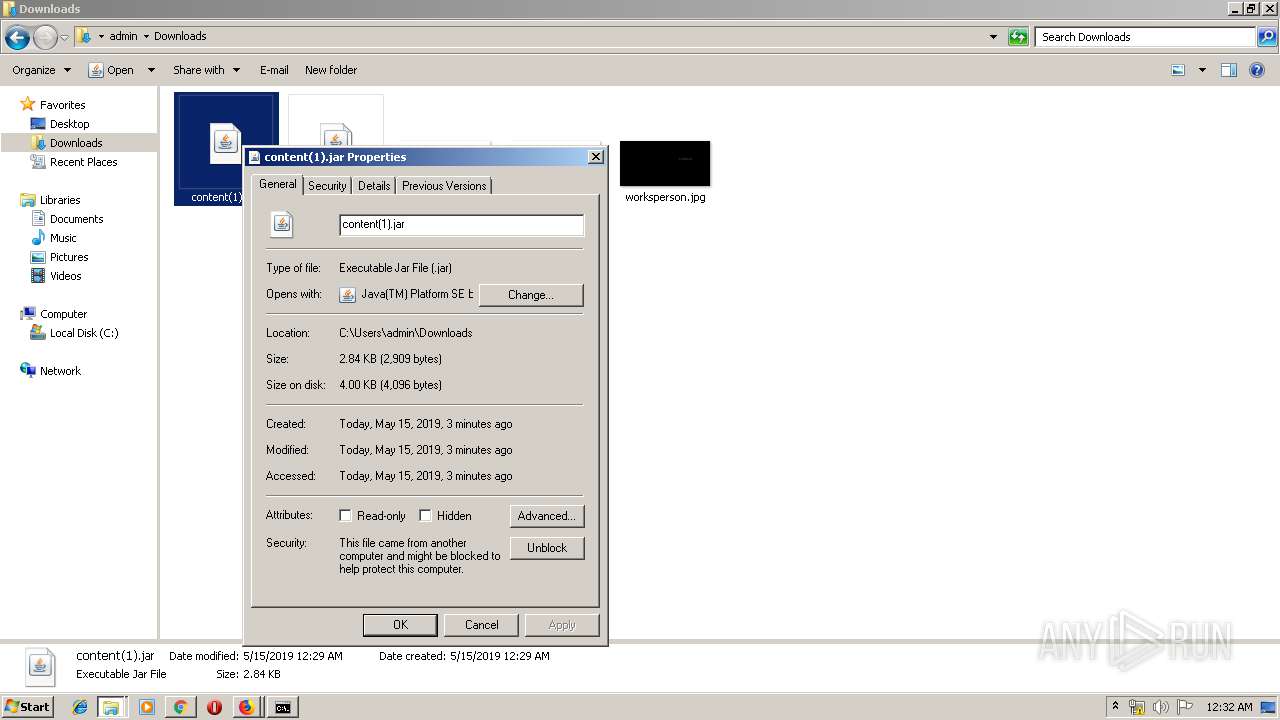
3764 | chrome.exe | GET | 200 | 52.216.1.128:80 | http://security-update-site-1.6.s3.amazonaws.com/content.jar | US | java | 2.84 Kb | shared |
3764 | chrome.exe | GET | 200 | 74.125.173.138:80 | http://r5---sn-4g5ednsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.8&mm=28&mn=sn-4g5ednsy&ms=nvh&mt=1557876398&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2672 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2672 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3764 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2672 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2672 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2672 | firefox.exe | GET | 200 | 2.16.186.112:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2672 | firefox.exe | GET | 200 | 52.216.169.147:80 | http://security-update-site-1.6.s3.amazonaws.com/content.jar | US | java | 2.84 Kb | shared |
2672 | firefox.exe | POST | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | iexplore.exe | 87.248.114.11:443 | s.yimg.com | Yahoo! UK Services Limited | GB | shared |
2932 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3332 | iexplore.exe | 152.195.39.122:443 | us.y.atwola.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3764 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.23.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
3332 | iexplore.exe | 172.227.85.103:443 | sb.scorecardresearch.com | Akamai Technologies, Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2932 | iexplore.exe | 212.82.100.137:443 | search.yahoo.com | Yahoo! UK Services Limited | CH | shared |
3764 | chrome.exe | 216.58.210.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s.yimg.com |
| shared |
www.bing.com |
| whitelisted |
us.y.atwola.com |
| whitelisted |
sb.scorecardresearch.com |
| shared |
search.yahoo.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
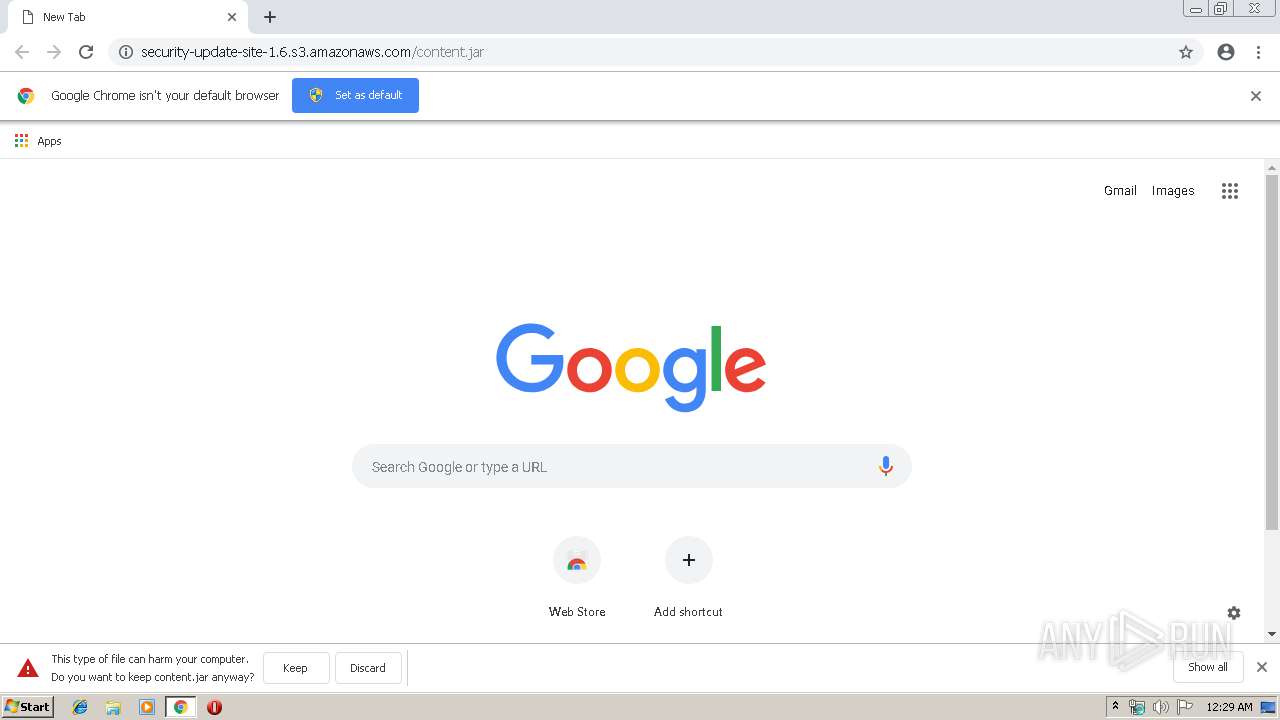
3764 | chrome.exe | Potentially Bad Traffic | ET INFO JAR Size Under 30K Size - Potentially Hostile |
2672 | firefox.exe | Potentially Bad Traffic | ET INFO JAR Size Under 30K Size - Potentially Hostile |