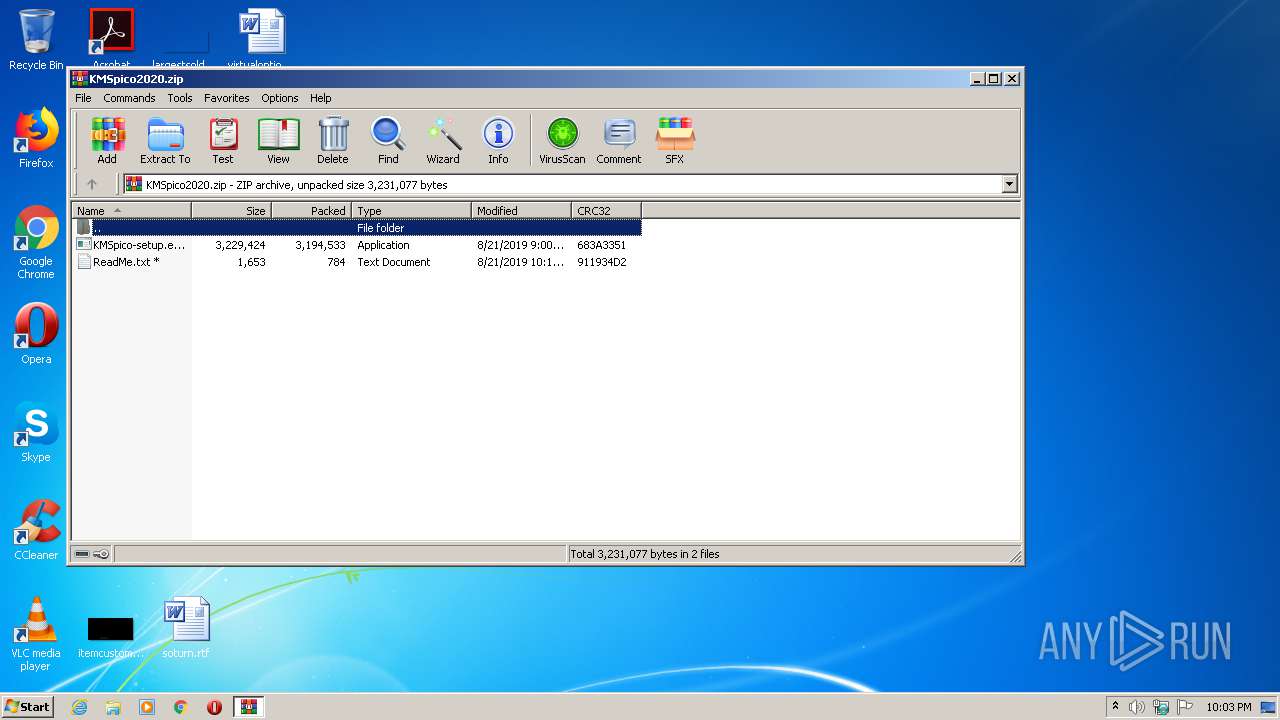
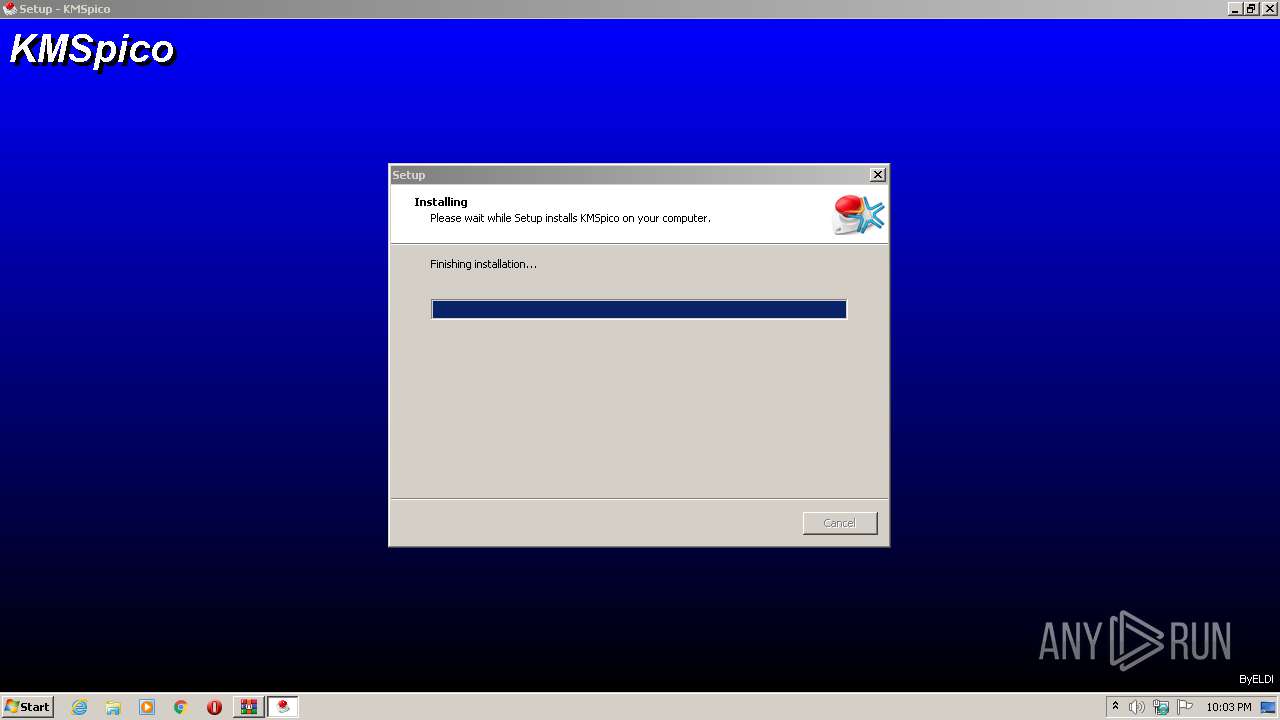
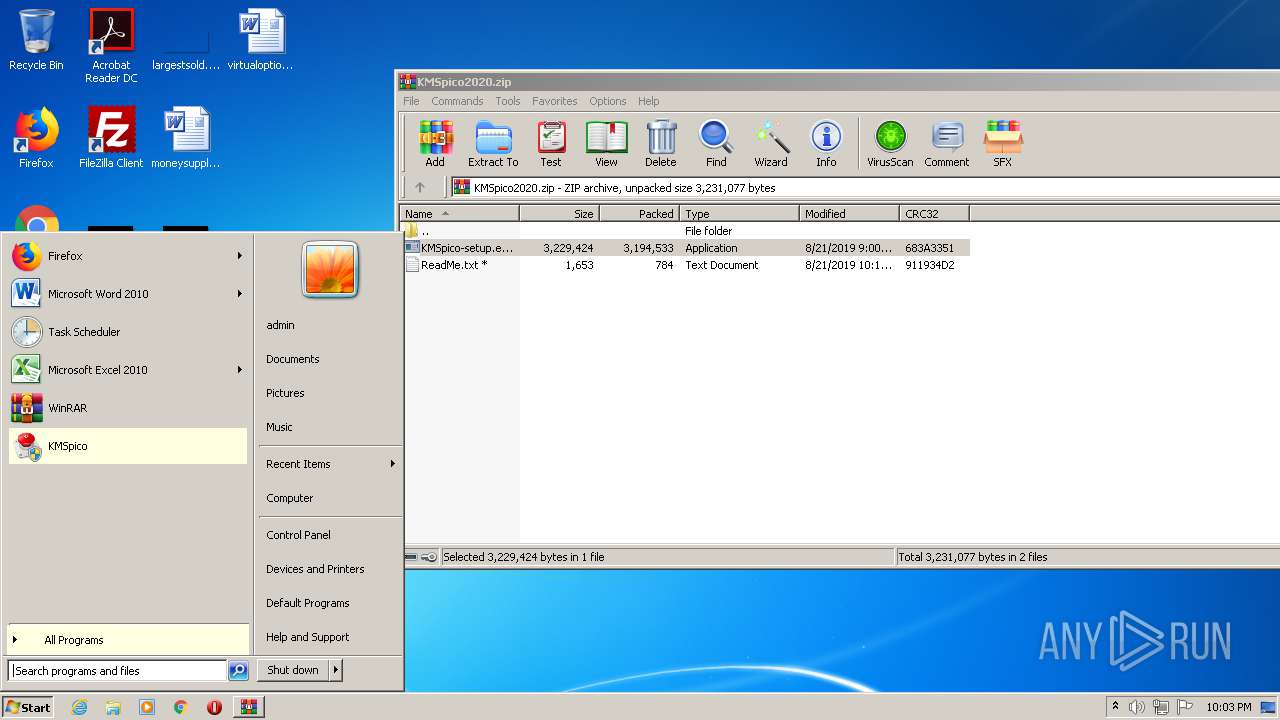
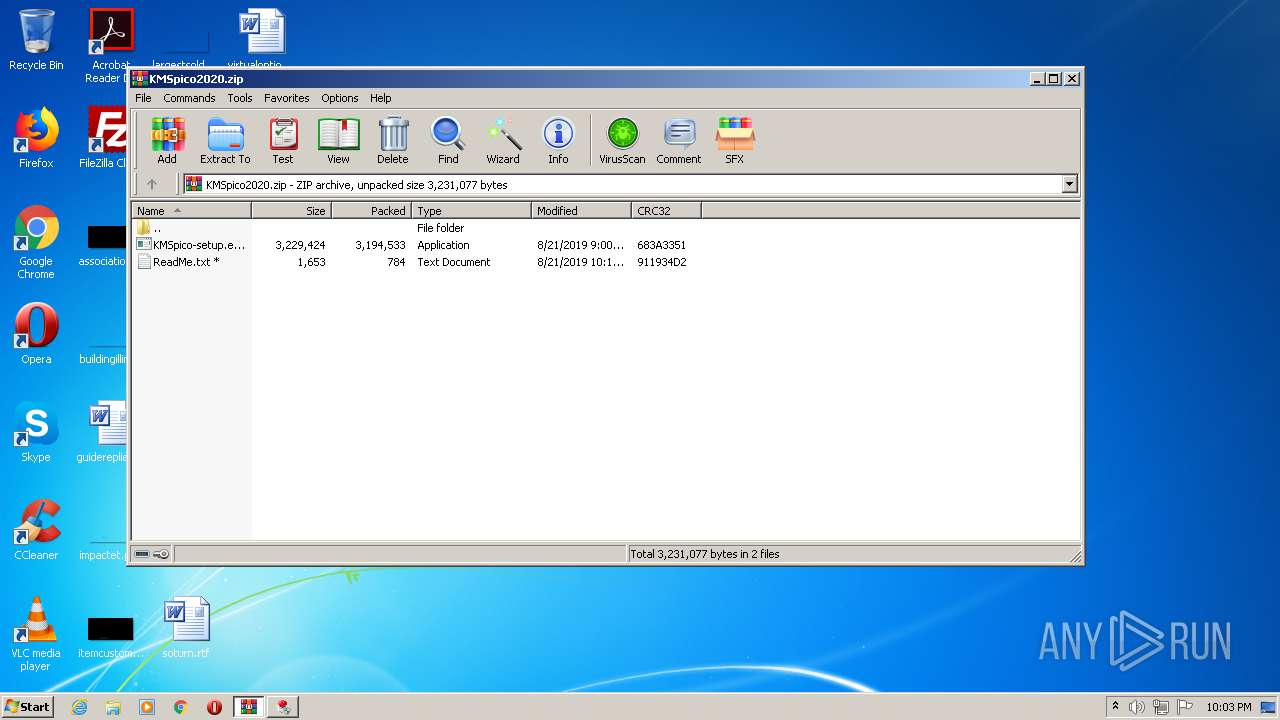
| File name: | KMSpico2020.zip |
| Full analysis: | https://app.any.run/tasks/d503d926-a94b-49d8-b935-1a1620f5653e |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 21:02:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 71A6C4016565E0062F34D1EA1636BC1A |
| SHA1: | A9A12381AF15D29C35E5BE968550292C1B1D2D7C |
| SHA256: | 7F83D0B47BCCDEF4983920967B4E1EEB0ED247960C43F9B29E83C0A540B0B483 |
| SSDEEP: | 98304:fgIk3pAy/+tYY3cLt0O+9y3BtuzsnaB4Alpd:e3pAywYBiouzsnsRpd |
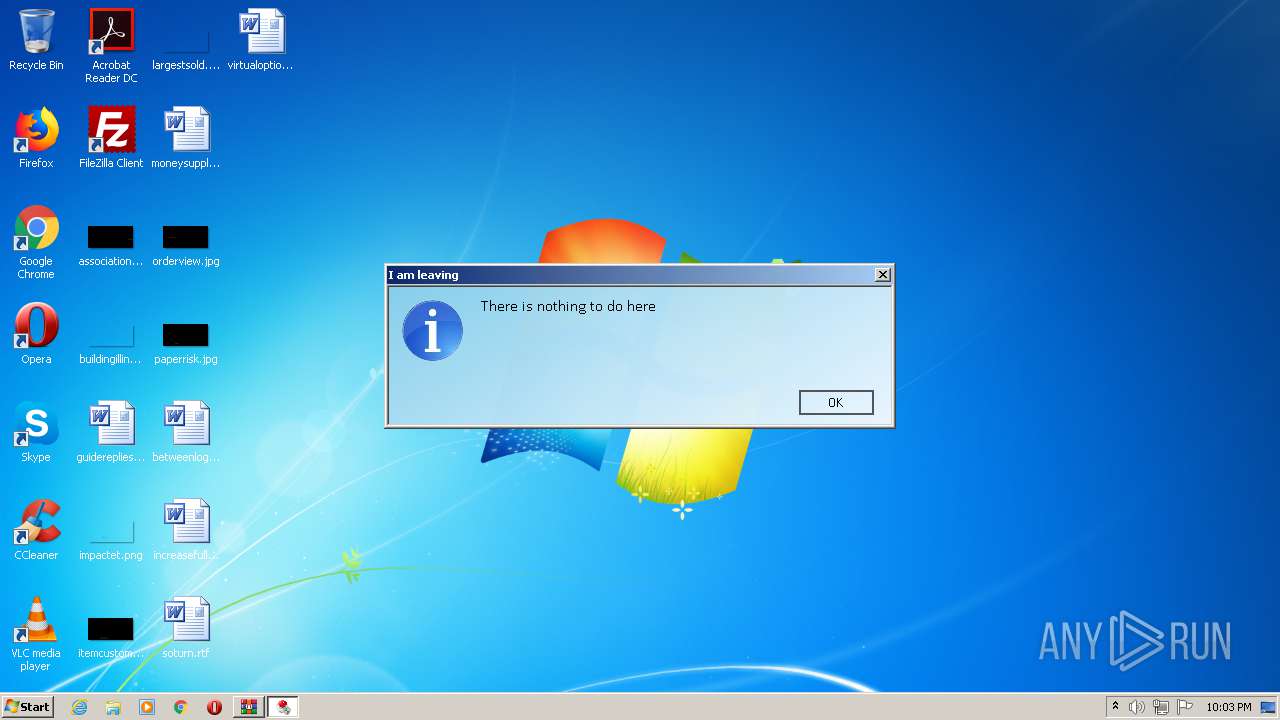
MALICIOUS
Application was dropped or rewritten from another process
- KMSpico-setup.exe (PID: 3144)
- KMSpico-setup.exe (PID: 3512)
- KMSELDI.exe (PID: 1124)
- UninsHs.exe (PID: 3372)
- KMSELDI.exe (PID: 3800)
- AutoPico.exe (PID: 2488)
- KMSELDI.exe (PID: 2864)
- KMSELDI.exe (PID: 3408)
- KMSELDI.exe (PID: 3448)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2832)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2916)
Loads dropped or rewritten executable
- KMSELDI.exe (PID: 1124)
- KMSELDI.exe (PID: 2864)
- KMSELDI.exe (PID: 3448)
SUSPICIOUS
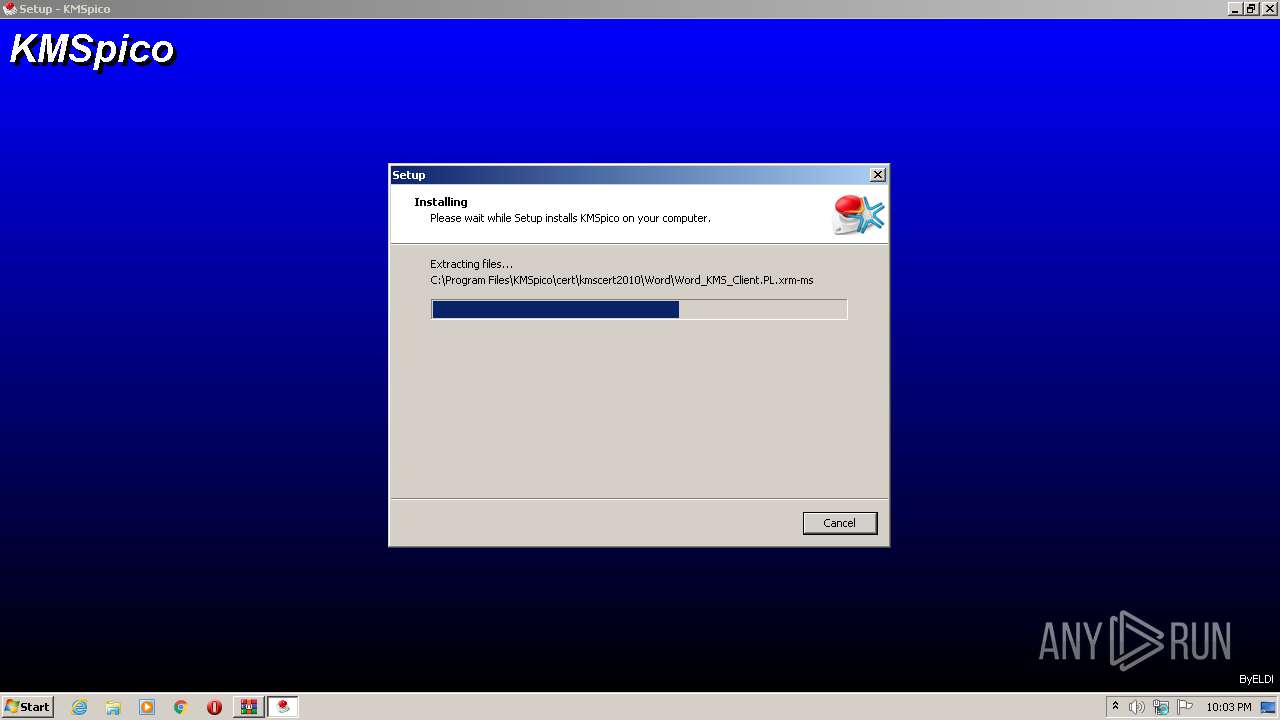
Executable content was dropped or overwritten
- KMSpico-setup.exe (PID: 3144)
- KMSpico-setup.exe (PID: 3512)
- KMSpico-setup.tmp (PID: 3888)
- WinRAR.exe (PID: 3116)
Creates files in the Windows directory
- KMSpico-setup.tmp (PID: 3888)
Modifies the phishing filter of IE
- KMSpico-setup.tmp (PID: 3888)
Starts SC.EXE for service management
- cmd.exe (PID: 2752)
Starts CMD.EXE for commands execution
- KMSpico-setup.tmp (PID: 3888)
Reads Environment values
- KMSELDI.exe (PID: 1124)
- AutoPico.exe (PID: 2488)
- KMSELDI.exe (PID: 2864)
- KMSELDI.exe (PID: 3448)
Creates or modifies windows services
- KMSELDI.exe (PID: 1124)
Creates files in the program directory
- KMSELDI.exe (PID: 1124)
- AutoPico.exe (PID: 2488)
- KMSELDI.exe (PID: 2864)
- KMSELDI.exe (PID: 3448)
INFO
Application was dropped or rewritten from another process
- KMSpico-setup.tmp (PID: 3528)
- KMSpico-setup.tmp (PID: 3888)
Loads dropped or rewritten executable
- KMSpico-setup.tmp (PID: 3888)
Creates a software uninstall entry
- KMSpico-setup.tmp (PID: 3888)
Reads Microsoft Office registry keys
- AutoPico.exe (PID: 2488)
- KMSELDI.exe (PID: 1124)
- KMSELDI.exe (PID: 2864)
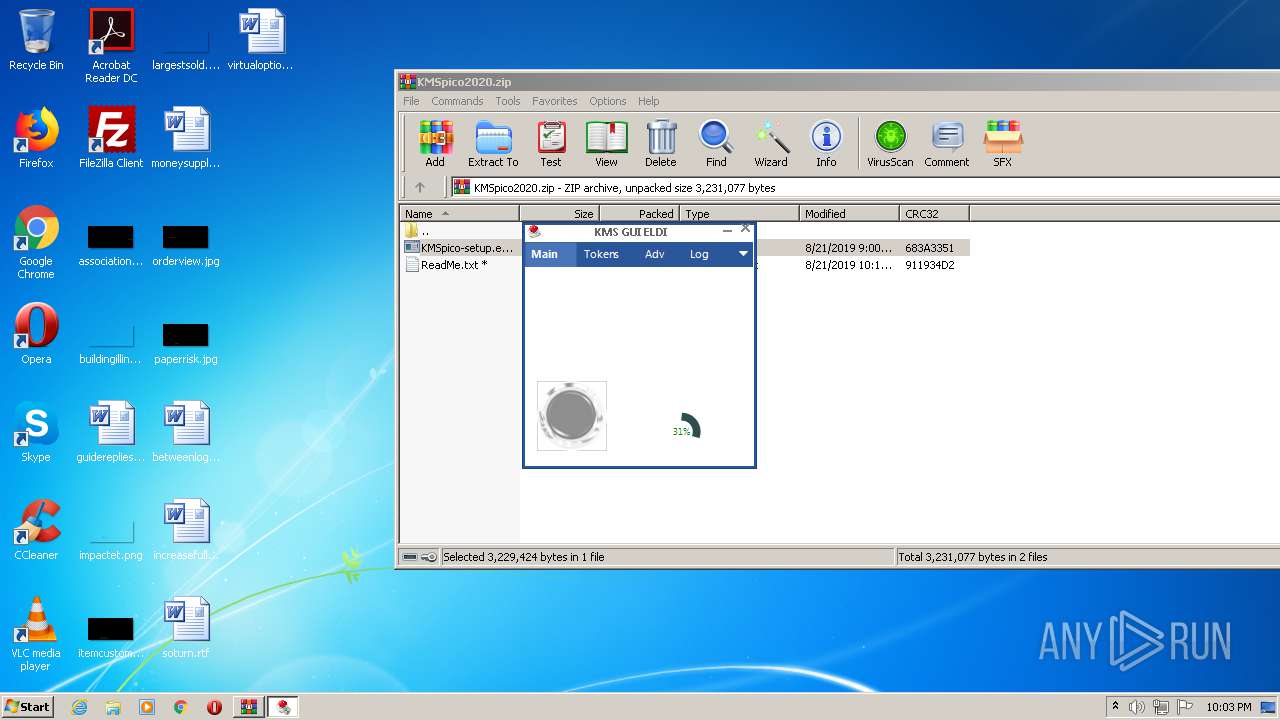
Manual execution by user
- KMSELDI.exe (PID: 3800)
- KMSELDI.exe (PID: 2864)
- KMSELDI.exe (PID: 3408)
- KMSELDI.exe (PID: 3448)
Creates files in the program directory
- KMSpico-setup.tmp (PID: 3888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
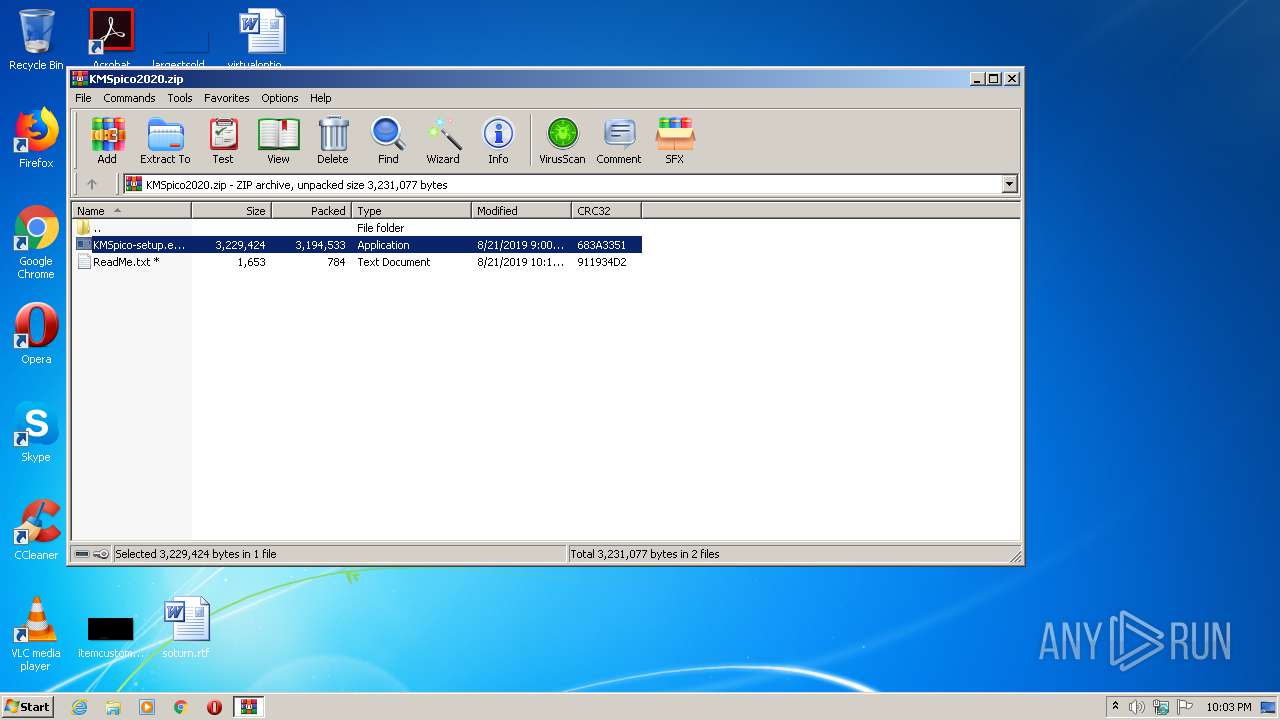
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2019:08:21 10:00:28 |
| ZipCRC: | 0x683a3351 |
| ZipCompressedSize: | 3194533 |
| ZipUncompressedSize: | 3229424 |
| ZipFileName: | KMSpico-setup.exe |
Total processes
65
Monitored processes
16
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1124 | "C:\Program Files\KMSpico\KMSELDI.exe" /silent /backup | C:\Program Files\KMSpico\KMSELDI.exe | KMSpico-setup.tmp | ||||||||||||
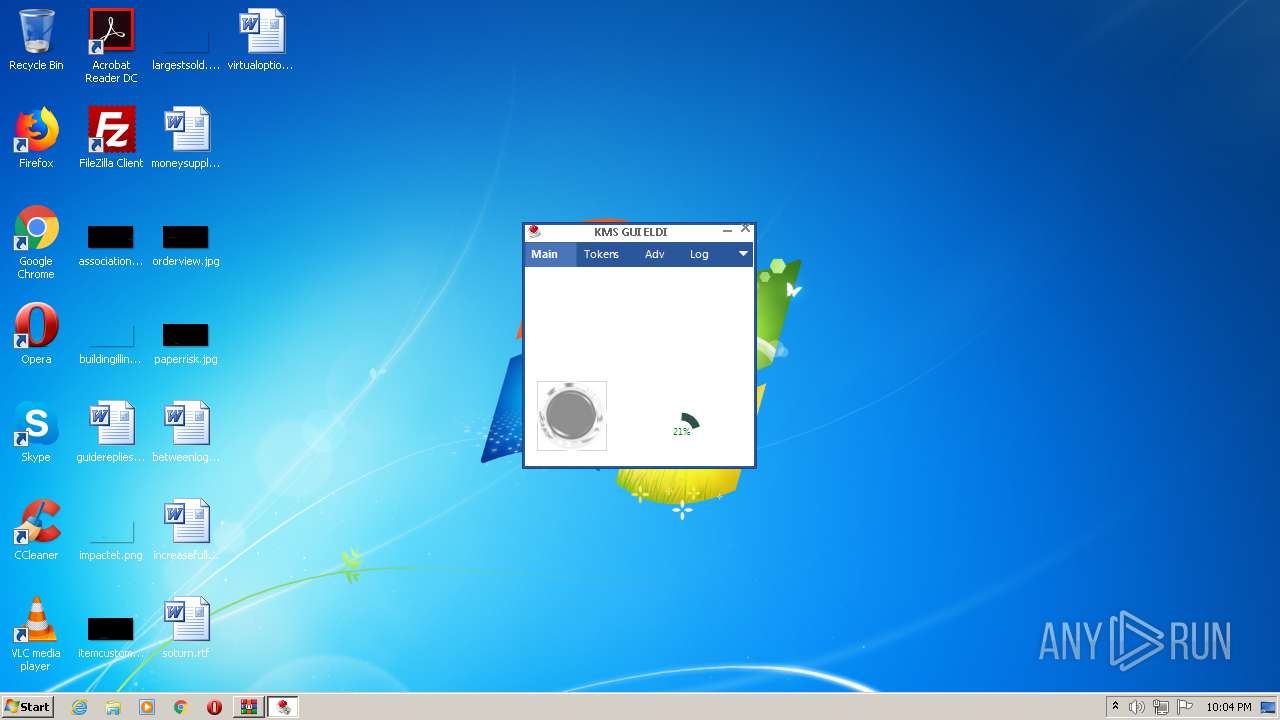
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 4294967295 Version: 37.1.0.0 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | KMSpico-setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 16.1.0.0 Modules
| |||||||||||||||
| 2752 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Service.cmd"" | C:\Windows\system32\cmd.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2832 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\KMSpico\KMSELDI.exe" | C:\Program Files\KMSpico\KMSELDI.exe | explorer.exe | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 3221225547 Version: 37.1.0.0 Modules
| |||||||||||||||
| 2872 | sc create "Service KMSELDI" binPath= "C:\Program Files\KMSpico\Service_KMS.exe" type= own error= normal start= auto DisplayName= "Service KMSELDI" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Task.cmd"" | C:\Windows\system32\cmd.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
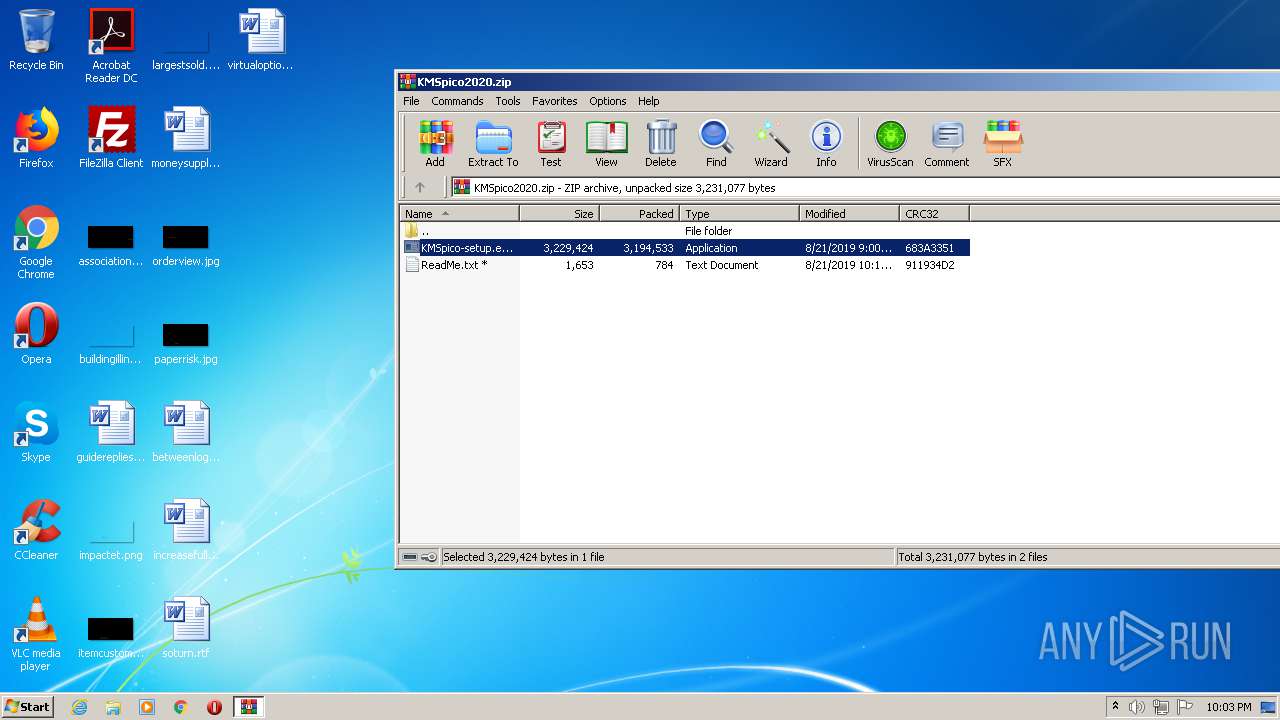
| 3116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\KMSpico2020.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
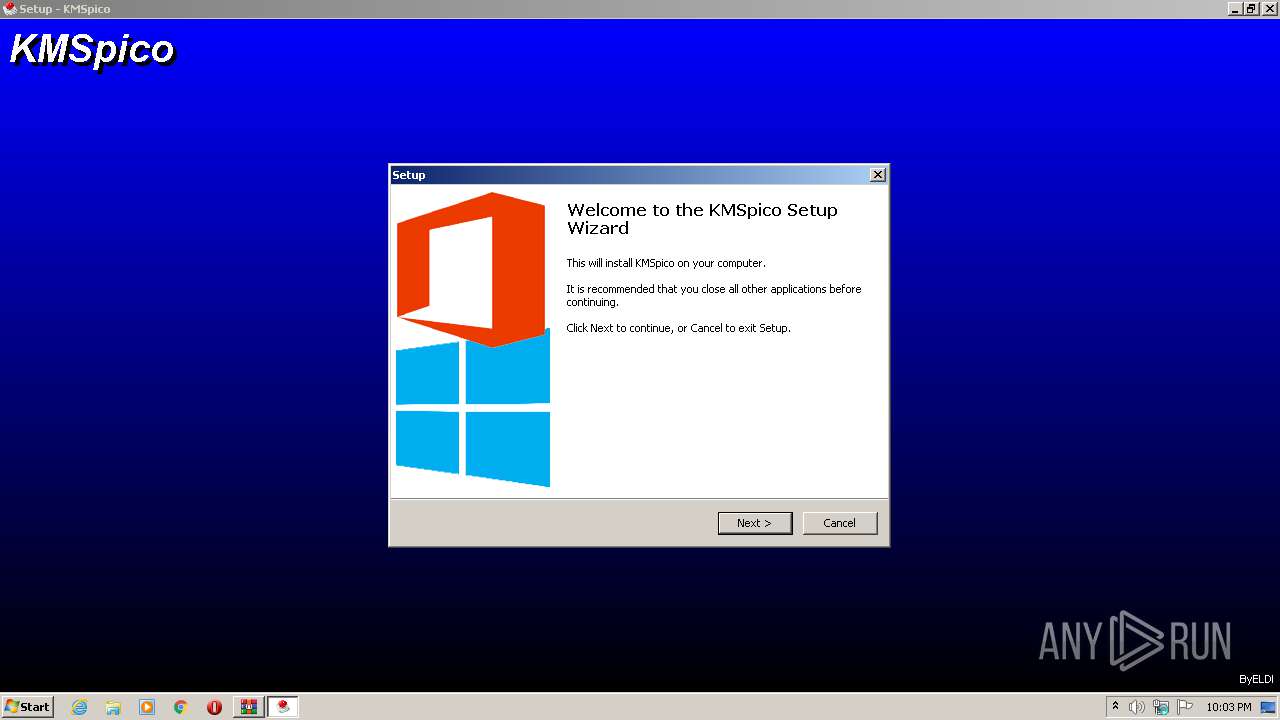
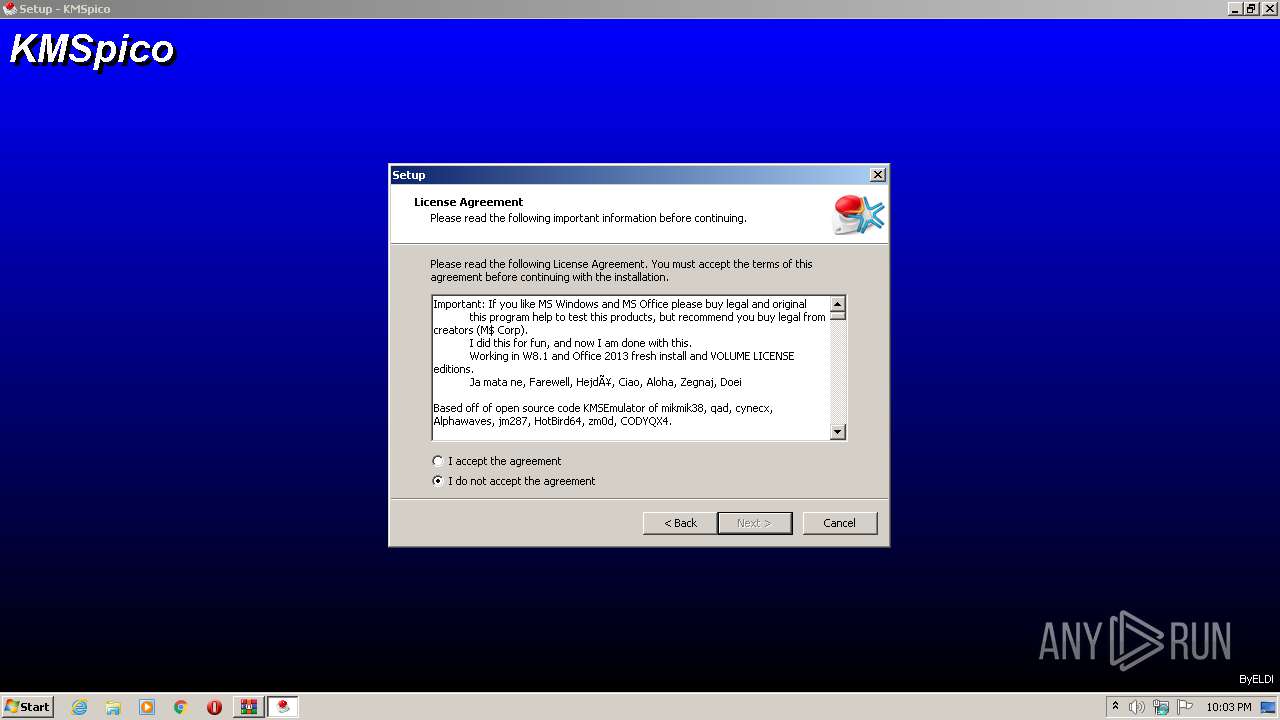
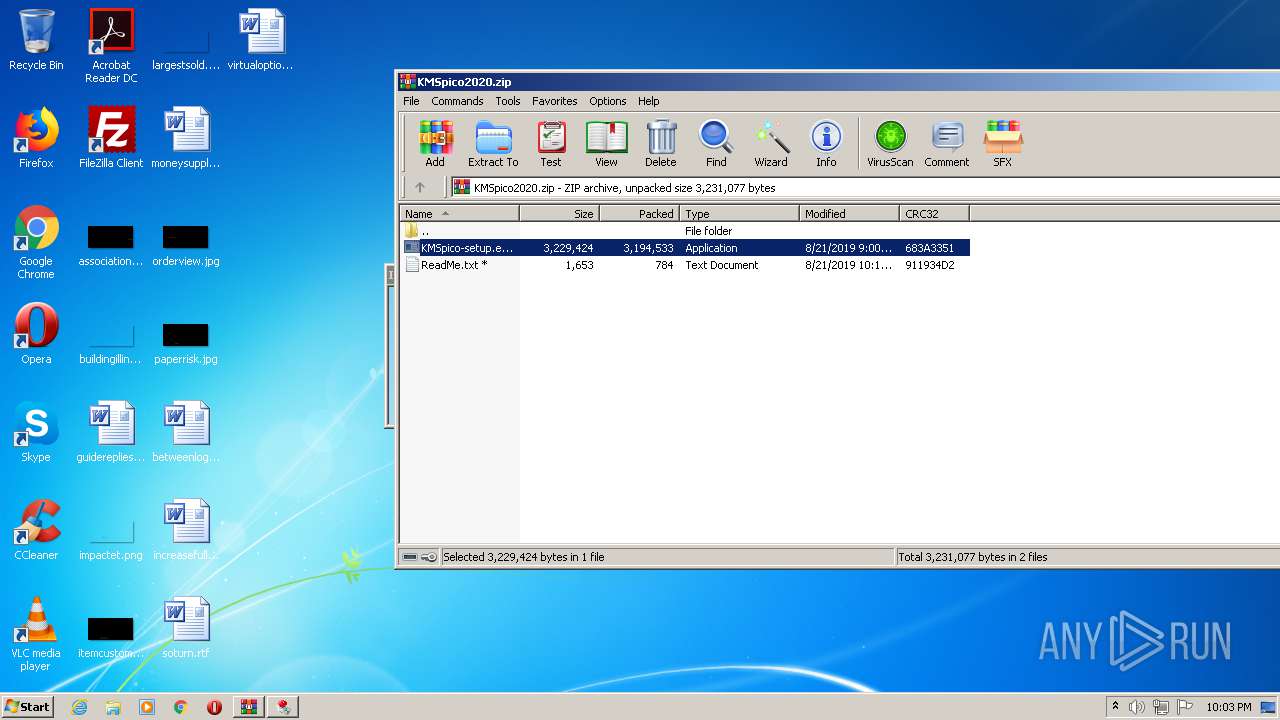
| 3144 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3116.21893\KMSpico-setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3116.21893\KMSpico-setup.exe | WinRAR.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
| 3372 | "C:\Program Files\KMSpico\UninsHs.exe" /r0=KMSpico,default,C:\Users\admin\AppData\Local\Temp\Rar$EXb3116.21893\KMSpico-setup.exe | C:\Program Files\KMSpico\UninsHs.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Han-soft Integrity Level: HIGH Description: Uninstall for InnoSetup by Han-soft Exit code: 0 Version: 2.1.0.283 Modules
| |||||||||||||||
Total events
1 649
Read events
1 522
Write events
121
Delete events
6
Modification events
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMSpico2020.zip | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
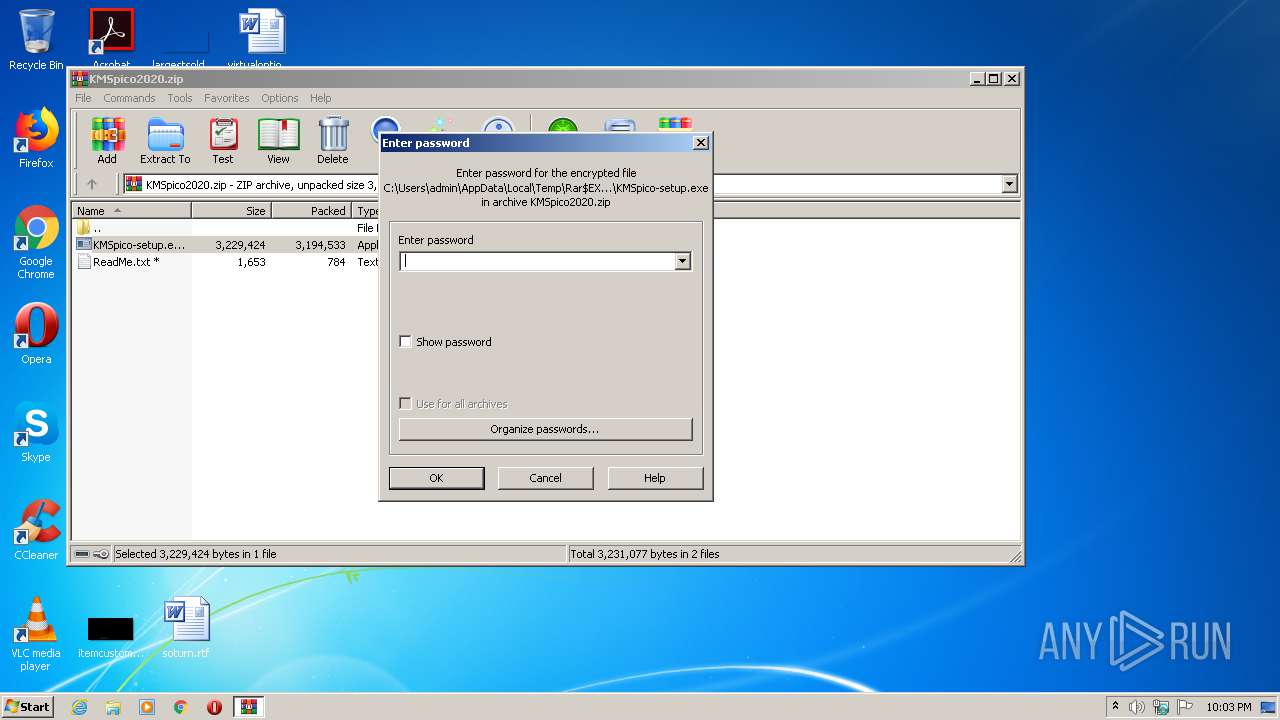
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
13
Suspicious files
2
Text files
460
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\is-4BCP1.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\is-AUKCS.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\is-1T8NB.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\is-BTTFU.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Windows\system32\is-9IP02.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\is-KGCQU.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\is-L1BKK.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\is-C1NL8.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\cert\kmscert2010\Access\is-R5LPO.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | KMSpico-setup.tmp | C:\Program Files\KMSpico\cert\kmscert2010\Access\is-ACUMG.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1124 | KMSELDI.exe | 173.212.222.171:123 | 2.pool.ntp.org | Contabo GmbH | DE | unknown |
2488 | AutoPico.exe | 193.158.22.13:123 | 3.pool.ntp.org | Deutsche Telekom AG | DE | unknown |
2864 | KMSELDI.exe | 37.120.184.82:123 | 0.pool.ntp.org | netcup GmbH | DE | suspicious |
— | — | 193.30.120.245:123 | 3.pool.ntp.org | — | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
2.pool.ntp.org |
| whitelisted |
3.pool.ntp.org |
| whitelisted |
0.pool.ntp.org |
| whitelisted |