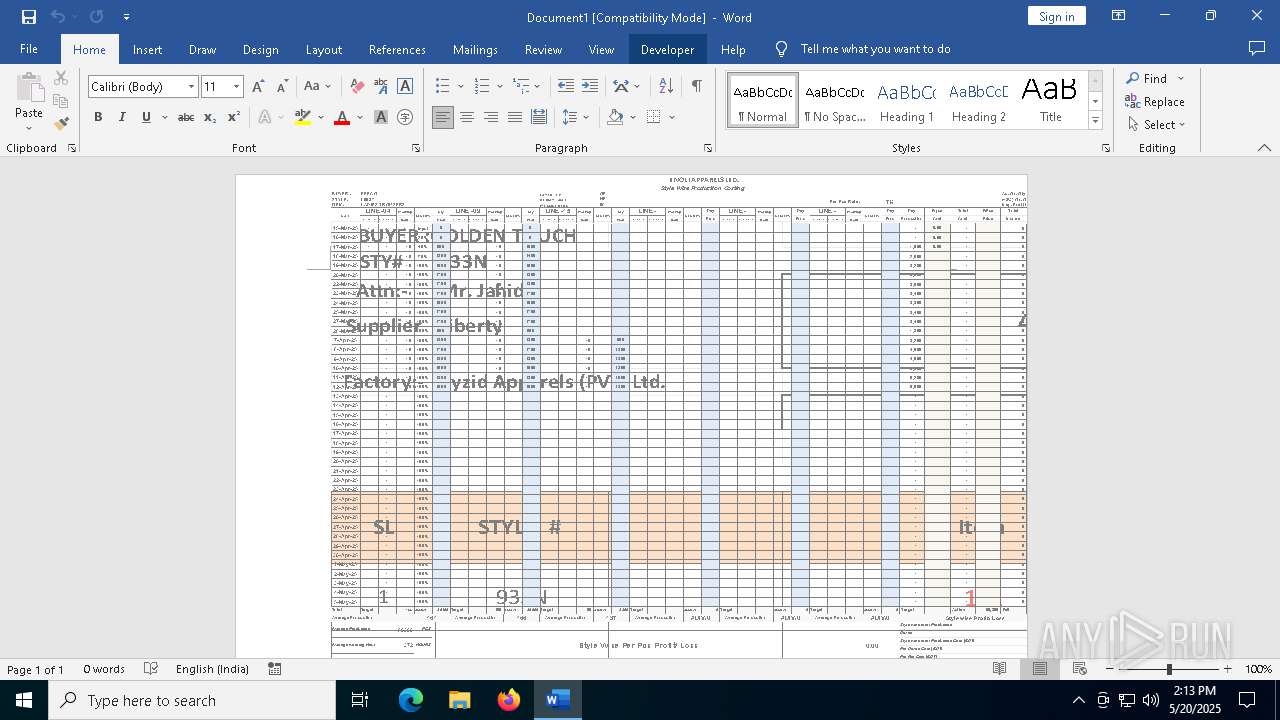
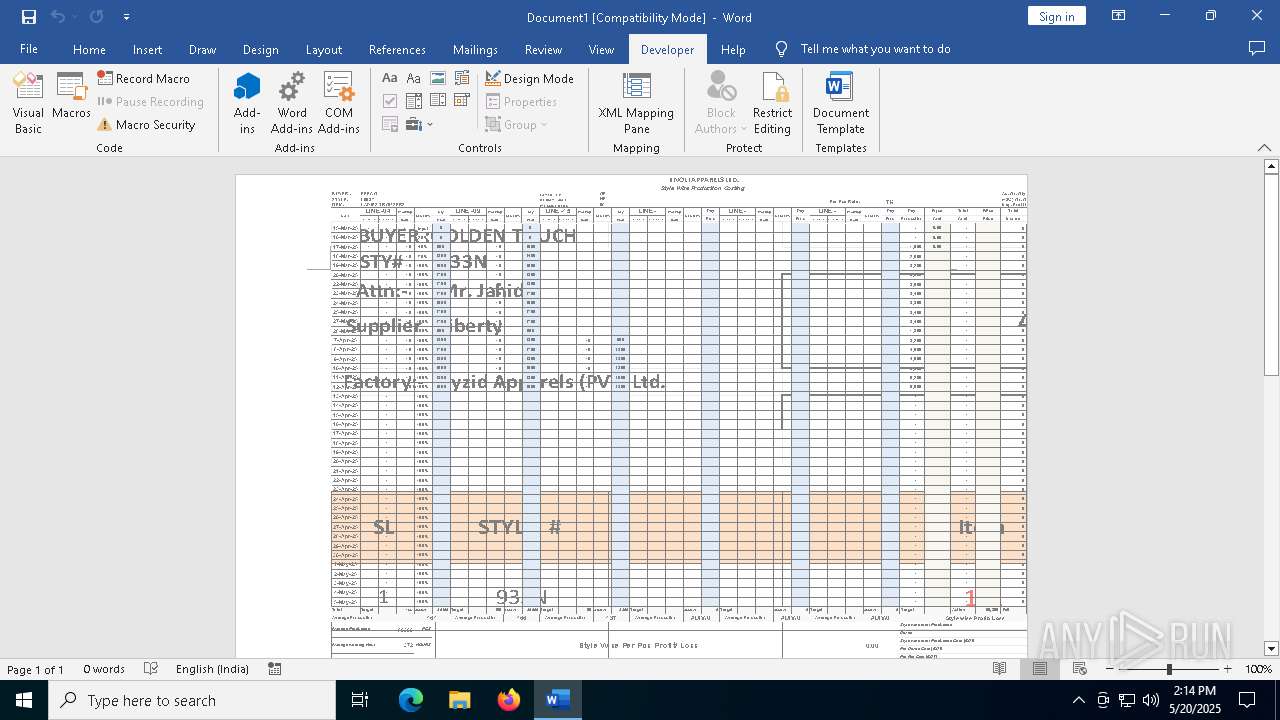
| File name: | payment.docx |
| Full analysis: | https://app.any.run/tasks/97715643-5acc-421a-a117-5ab64536c931 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2025, 14:09:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 8DC91825C4AEAA3814ABFF5060ECAF78 |
| SHA1: | 4ADC9AA0ED9C13316AB44B77C1593C2594AEF029 |
| SHA256: | 7F7D42510E2926B93BAAABB65036834D4898244A2EF237CA1527461150116763 |
| SSDEEP: | 3072:LP6rqRX369Om79R6jDh+b0AKWGMjPsjexxv05GKeUQyloI6876R:cqRn1jDh1AShj/eUlM8mR |
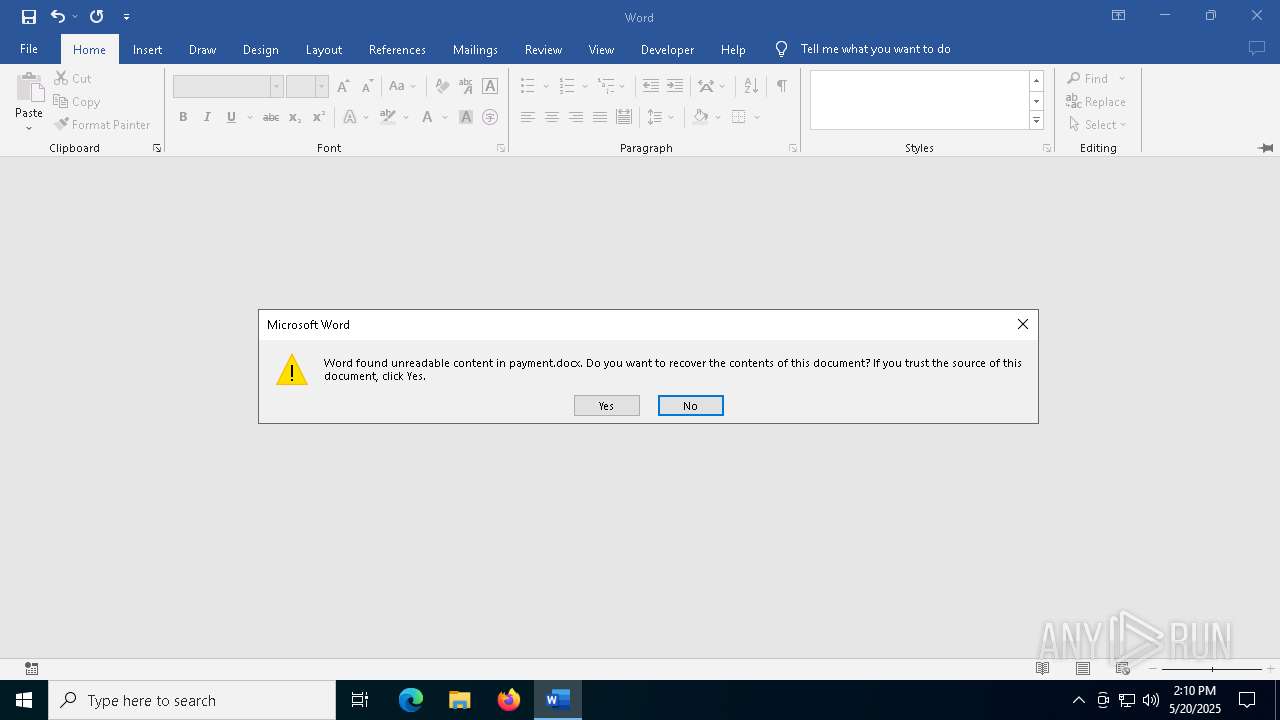
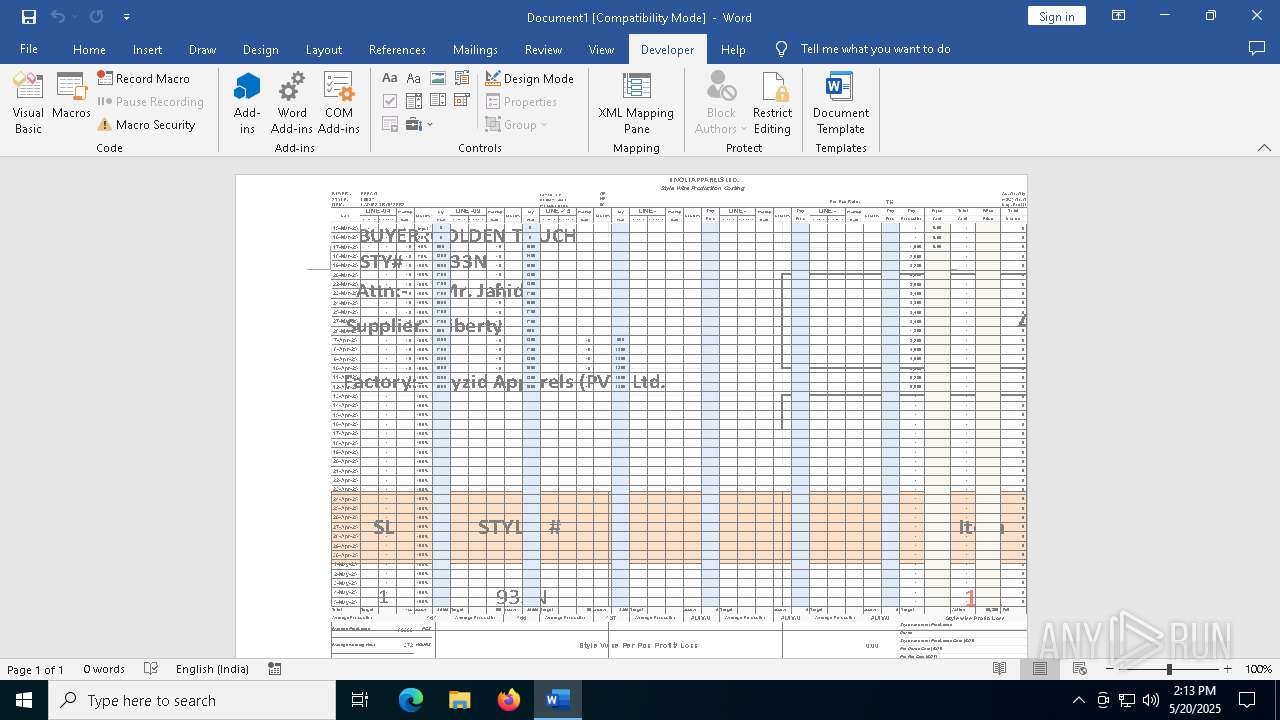
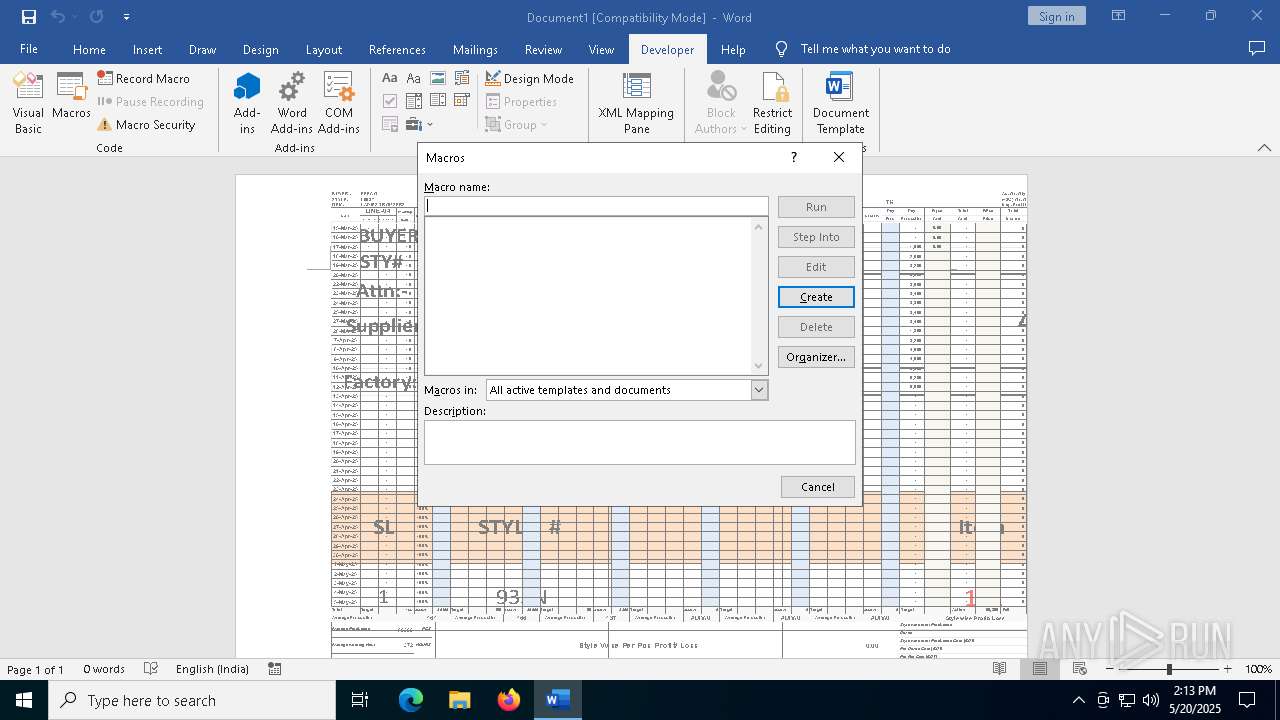
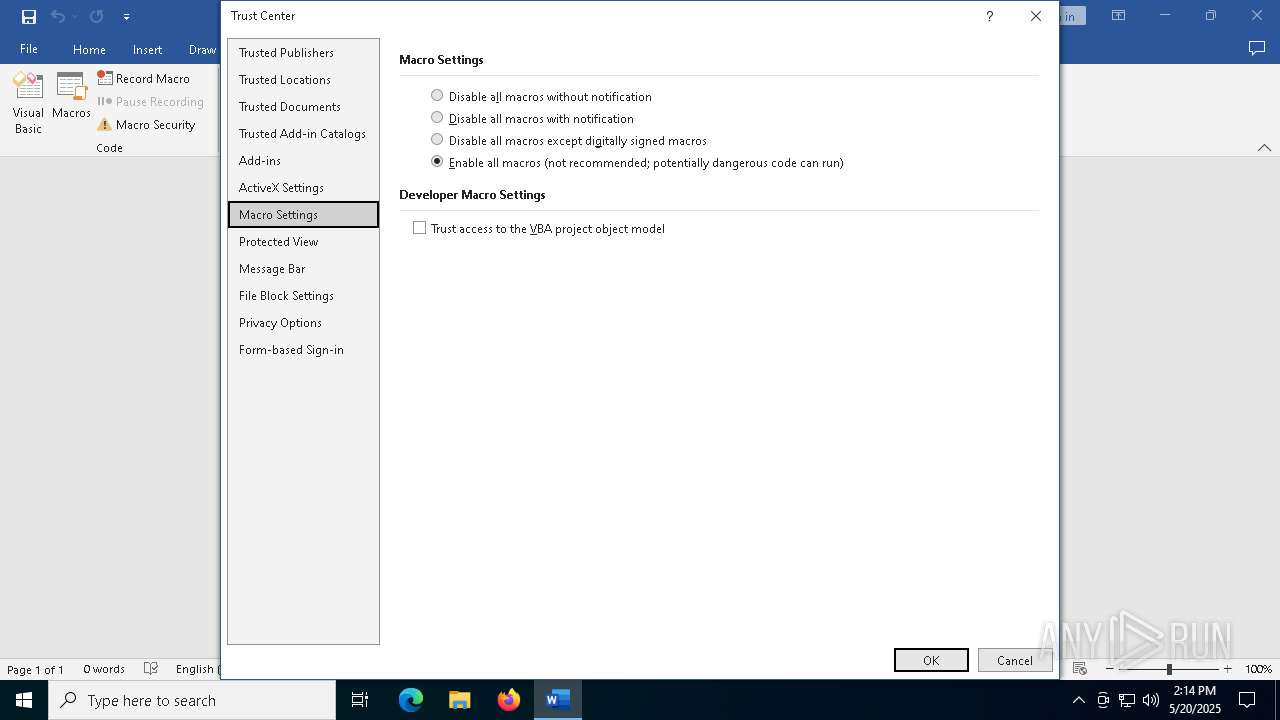
MALICIOUS
EXPLOIT has been detected (SURICATA)
- WINWORD.EXE (PID: 7532)
SUSPICIOUS
Connects to the server without a host name
- WINWORD.EXE (PID: 7532)
INFO
Checks proxy server information
- slui.exe (PID: 8032)
Reads the software policy settings
- slui.exe (PID: 8032)
- slui.exe (PID: 7764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:20 07:45:04 |
| ZipCRC: | 0x8d4b0b97 |
| ZipCompressedSize: | 424 |
| ZipUncompressedSize: | 2461 |
| ZipFileName: | [Content_Types].xml |
Total processes
141
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
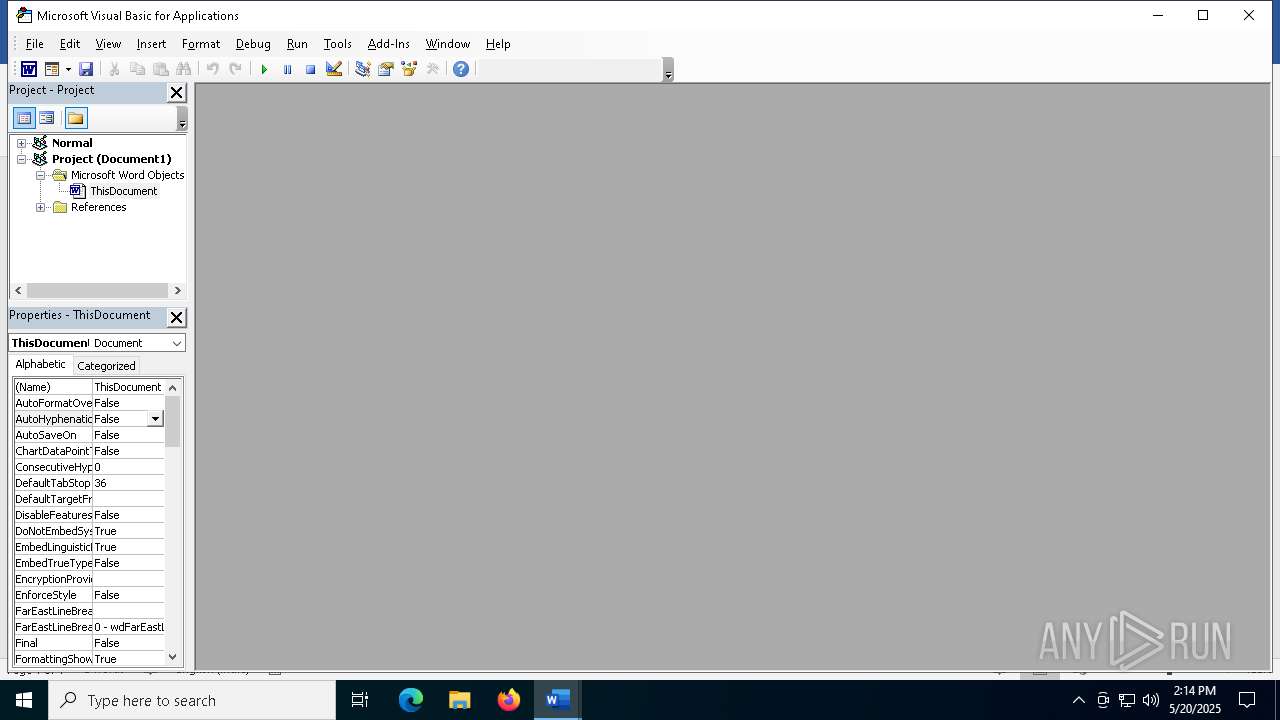
| 2108 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "6F2EDE92-B51D-473E-85E1-DB70A145D274" "5A62EBA6-CEAB-492E-BE5D-FFB5E2E7A86C" "7532" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7532 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\payment.docx /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7700 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7764 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8032 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
53 543
Read events
33 792
Write events
19 658
Delete events
93
Modification events
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\7532 |
| Operation: | write | Name: | 0 |
Value: 0B0E106CBA6DFC643E66479C2AC8B89F08E2EB230046CC93C6AC8EB2F2ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511EC3AD2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (7532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
33
Suspicious files
141
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:FAC04C46E6E58973D6D6E3509A702C53 | SHA256:E288DAF32B72AF24AF52950972DF90565621546EB437C5274E8CD50FCBF0B0E7 | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:DCDB8A2328C8F79589B318B6A8100BBE | SHA256:AC2A15BA22BEA731C449618786895A6FEC601F6D3B96CDCA29B9EB82B0452908 | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:9FCD10FBEA9120DC637CD0205505CB94 | SHA256:25A0300B2661E9A5B2020F25F72663F19124D10EBAE1EF22BA16DD47236B47BB | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\866CF4C7-6271-467C-AADD-16D03C7B2190 | xml | |
MD5:3F94B673465C5251349C8C91C9FA9C6D | SHA256:89399E24CF26A264300052741E9FFC15415D976E4AC5E335B44C896D307E8BDB | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\ResourceInfoCache\data.json | binary | |
MD5:A749D8FEE2FE7DA8960DAD52078BE0C9 | SHA256:18CB193E093B7C9A0E2EE13551AFAD45DD01440C06631CB256D46F71F63EDD7B | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:2E06FC71162E5219FEF0FF8181B041D0 | SHA256:3F0EC80472C4FA046766E1BDC3CD0BBDF6084C86A9E1020BC20DB142CAF0EC09 | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ayment.docx | binary | |
MD5:F2D89AEE92A68B3818D53045D552E369 | SHA256:3A92EFE36A2F16FB7BE3134778AEF62DC8B3319CD7E4D75072CE91DD7C0423E3 | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:D7F11D8F4F0254E2CCA8B9DE6DF0A289 | SHA256:4E4F1714E26E1FF03609C6CD5548CE6D2FFDFA663A93A0D484C11DEC62456E83 | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\ResourceInfoCache\07fc2a8c43a1d1f16572d21e959a4847e306edae.temp | binary | |
MD5:A749D8FEE2FE7DA8960DAD52078BE0C9 | SHA256:18CB193E093B7C9A0E2EE13551AFAD45DD01440C06631CB256D46F71F63EDD7B | |||
| 7532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\msoED8E.tmp | document | |
MD5:A891589D2F4028AC9A074A1FF4C5EEB0 | SHA256:9A4558E5C7D76BB173E823126666D396A1FFB7091B524F854E860BFACE9ECB6D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
72
DNS requests
33
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7532 | WINWORD.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7532 | WINWORD.EXE | HEAD | 200 | 107.175.246.32:80 | http://107.175.246.32/xampp/rgb/nic/nicetoseeyoubesttingstodobetterwaysgivebetter________nicetoseeyoubesttingstodobetterwaysgivebetter_________nicetoseeyoubesttingstodobetterwaysgivebetter.doc | unknown | — | — | unknown |
7532 | WINWORD.EXE | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7532 | WINWORD.EXE | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
7532 | WINWORD.EXE | GET | 200 | 107.175.246.32:80 | http://107.175.246.32/xampp/rgb/nic/nicetoseeyoubesttingstodobetterwaysgivebetter________nicetoseeyoubesttingstodobetterwaysgivebetter_________nicetoseeyoubesttingstodobetterwaysgivebetter.doc | unknown | — | — | unknown |
680 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
680 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7532 | WINWORD.EXE | HEAD | 200 | 107.175.246.32:80 | http://107.175.246.32/xampp/rgb/nic/nicetoseeyoubesttingstodobetterwaysgivebetter________nicetoseeyoubesttingstodobetterwaysgivebetter_________nicetoseeyoubesttingstodobetterwaysgivebetter.doc | unknown | — | — | unknown |
7532 | WINWORD.EXE | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7532 | WINWORD.EXE | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7532 | WINWORD.EXE | 52.109.28.47:443 | roaming.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
7532 | WINWORD.EXE | 52.123.130.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7532 | WINWORD.EXE | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7532 | WINWORD.EXE | 2.16.168.101:443 | omex.cdn.office.net | Akamai International B.V. | RU | whitelisted |
6544 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
ecs.office.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
login.live.com |
| whitelisted |
smollq.cc |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
c.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
7532 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
7532 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
7532 | WINWORD.EXE | Potentially Bad Traffic | ET HUNTING Microsoft Office User-Agent Requesting A Doc File |
7532 | WINWORD.EXE | Misc Attack | EXPLOIT [ANY.RUN] Obfuscated RTF document including the CLSID of the Equation Editor (CVE-2017-11882) |
7532 | WINWORD.EXE | Potentially Bad Traffic | ET INFO Dotted Quad Host DOC Request |
7532 | WINWORD.EXE | Misc activity | ET USER_AGENTS Microsoft Office Existence Discovery User-Agent |