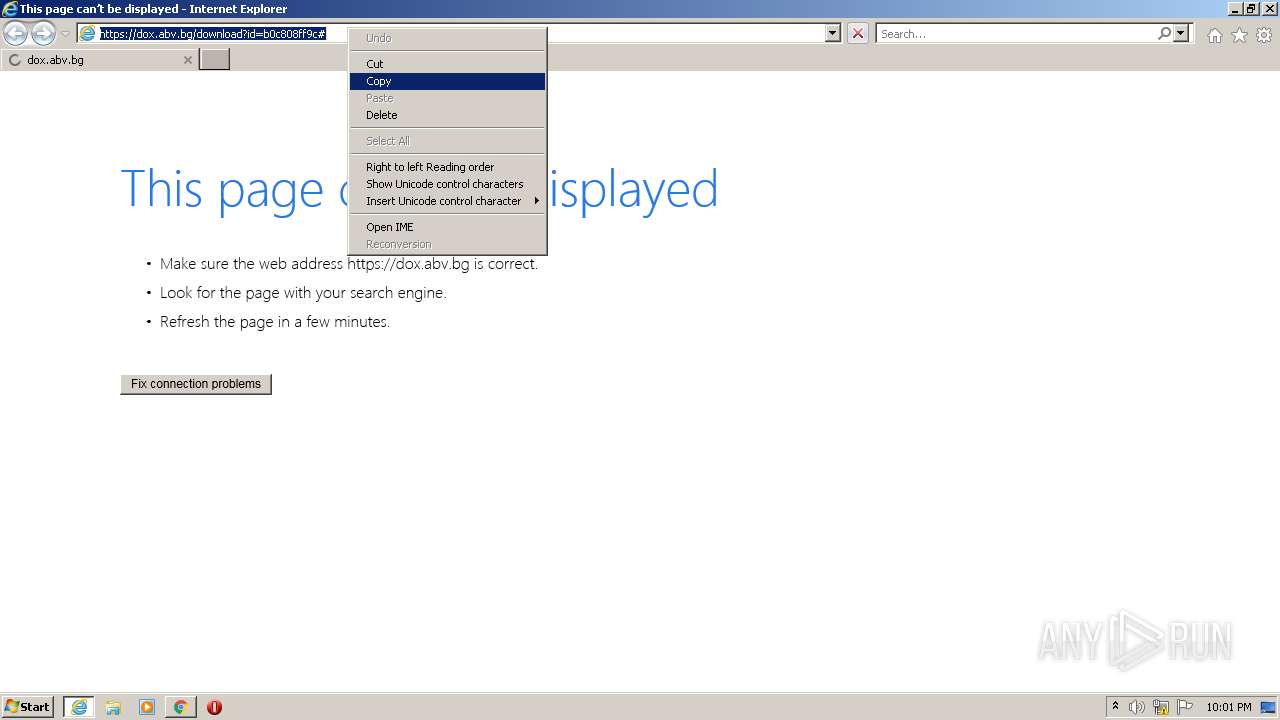
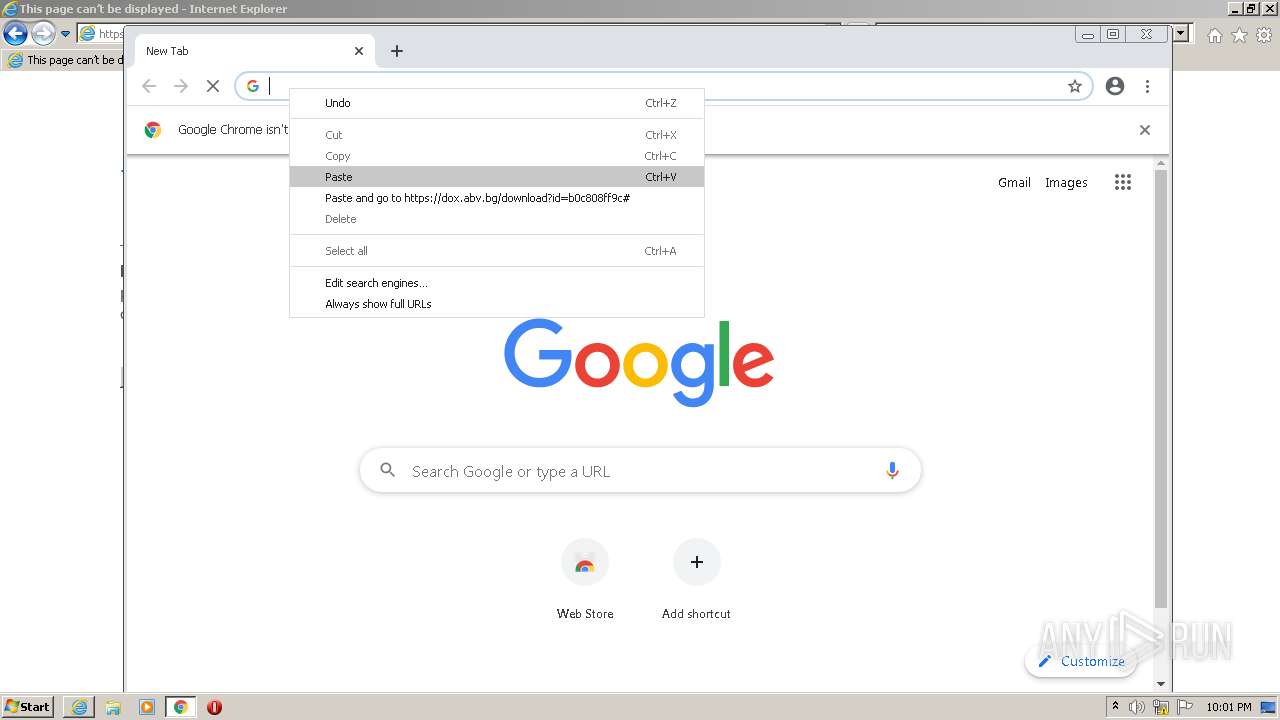
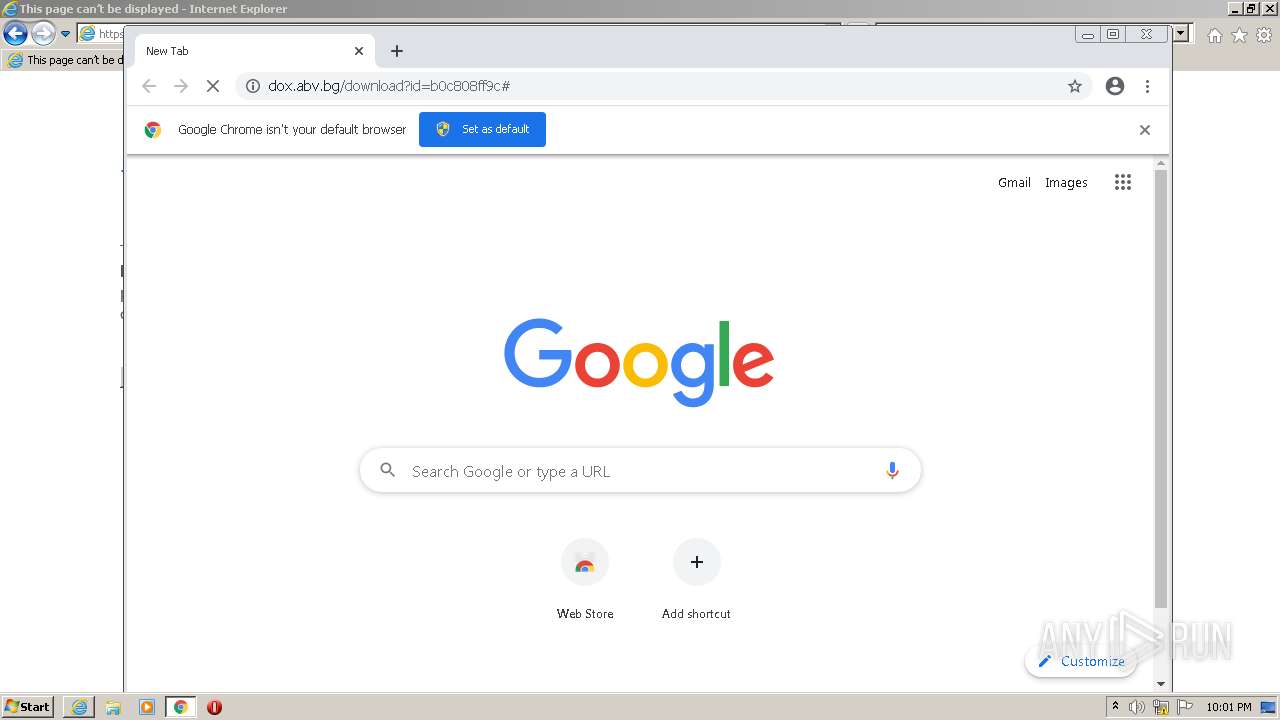
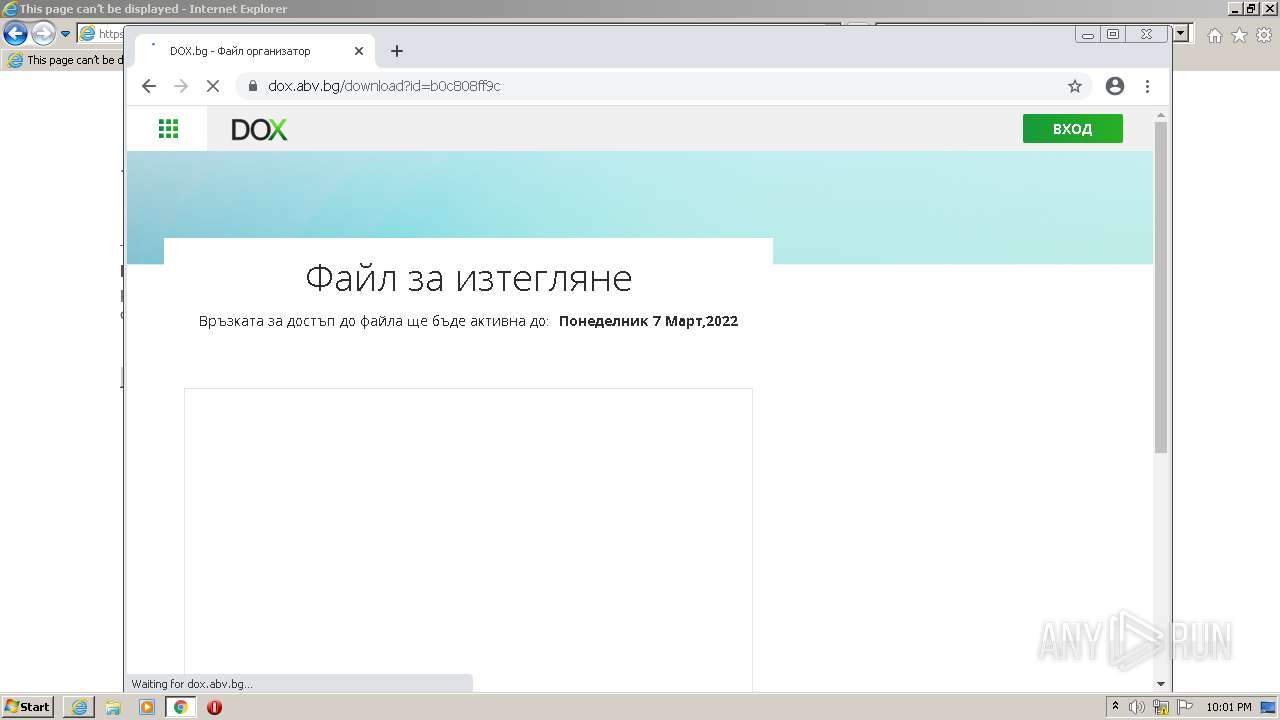
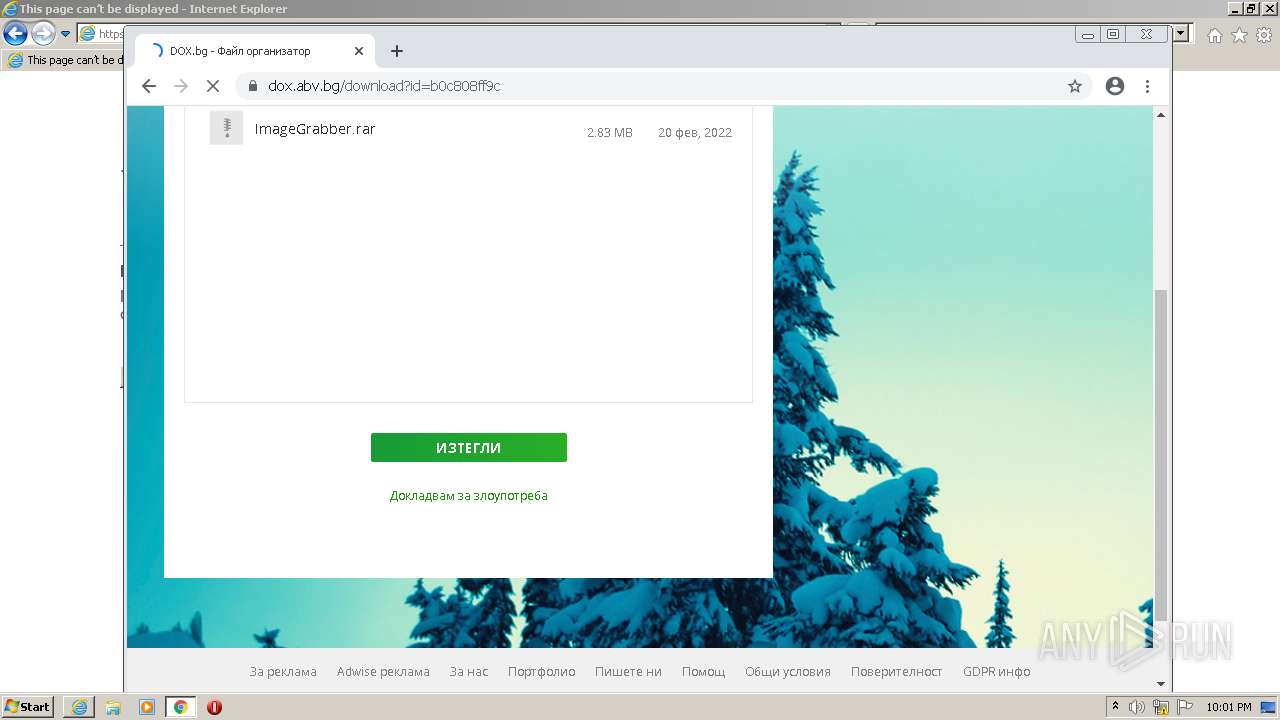
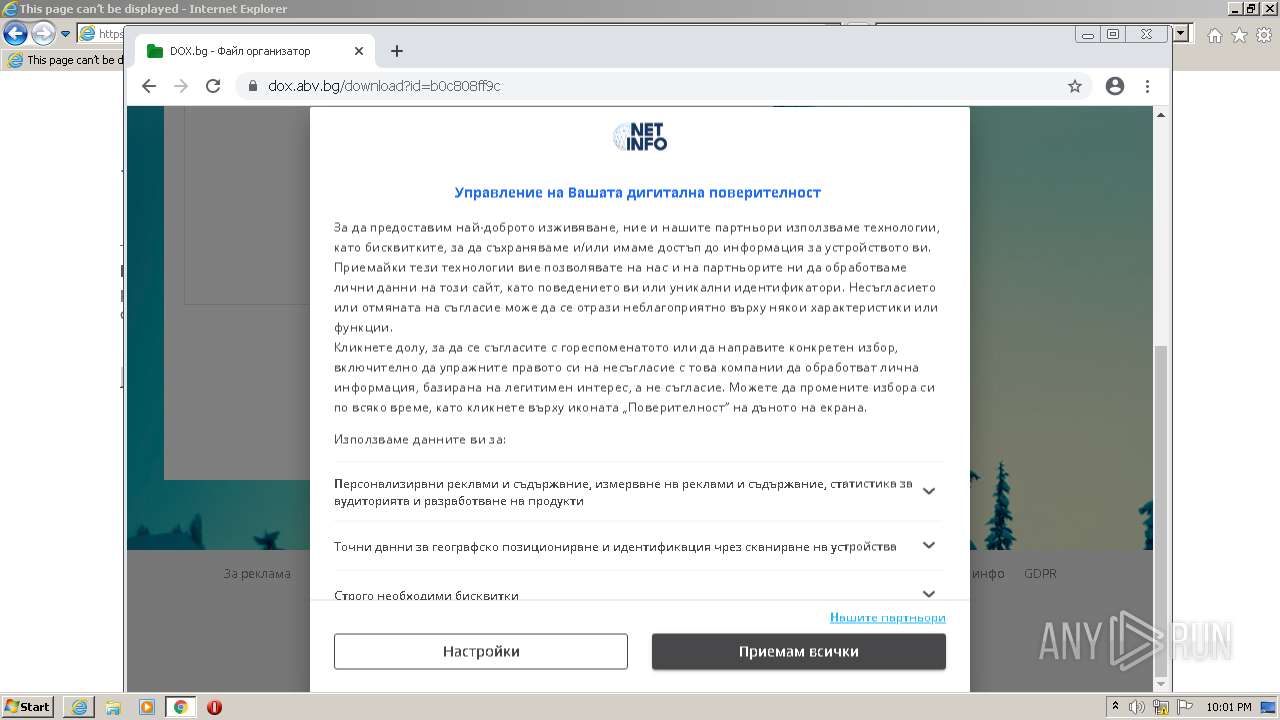
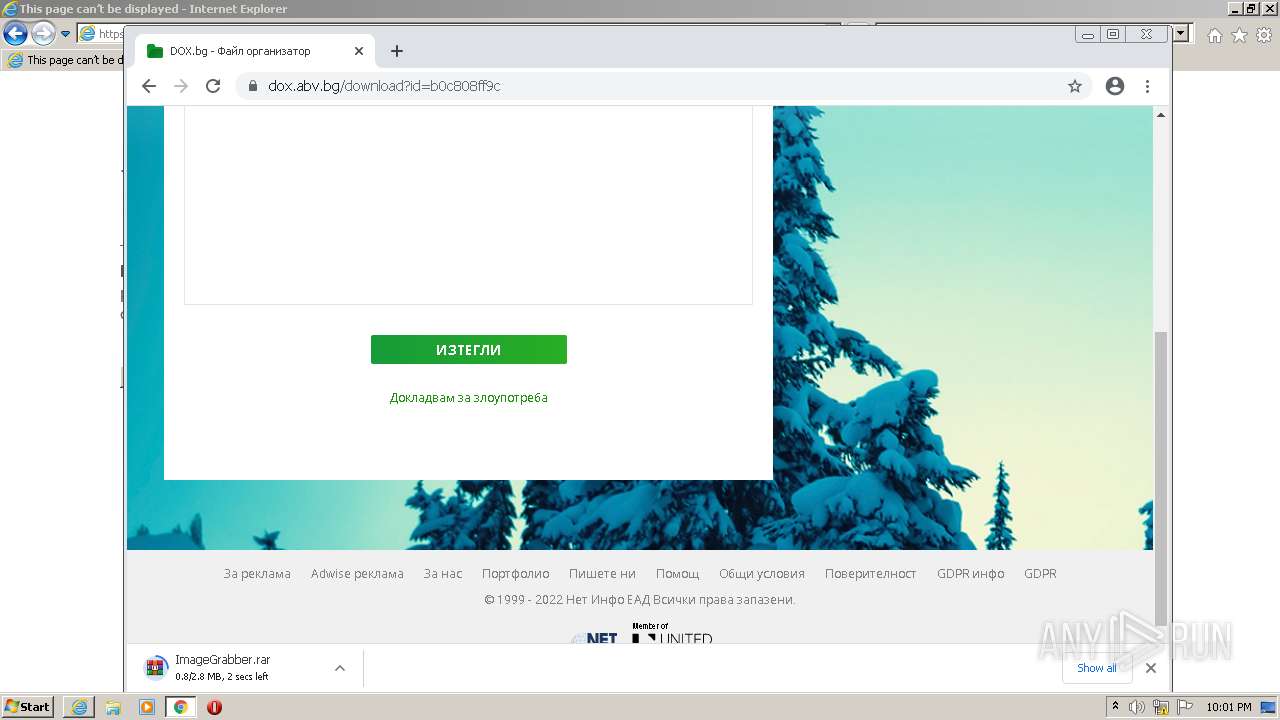
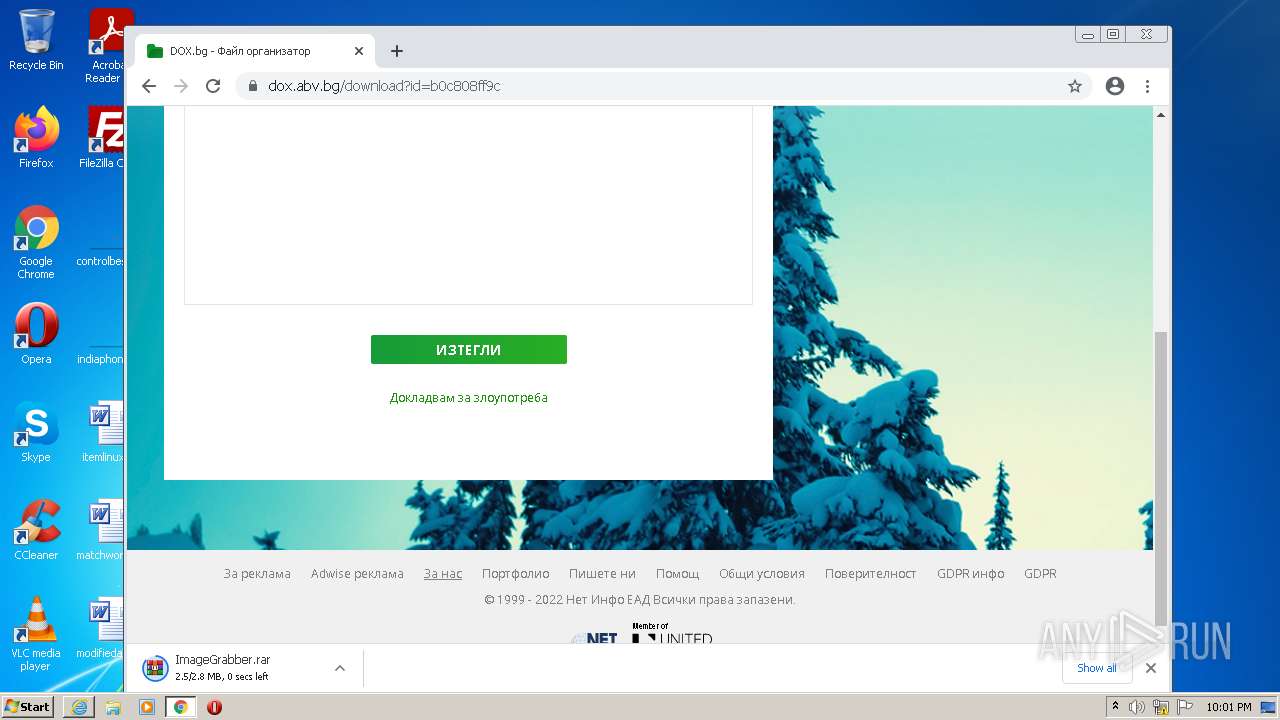
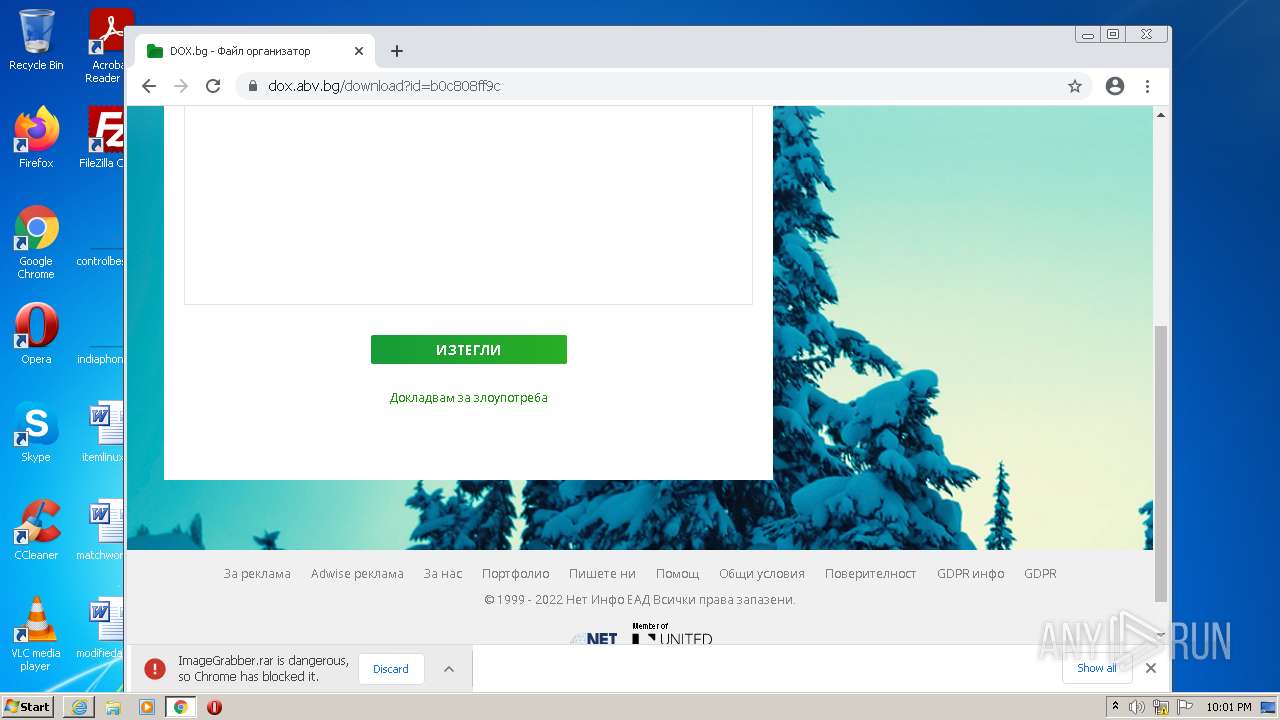
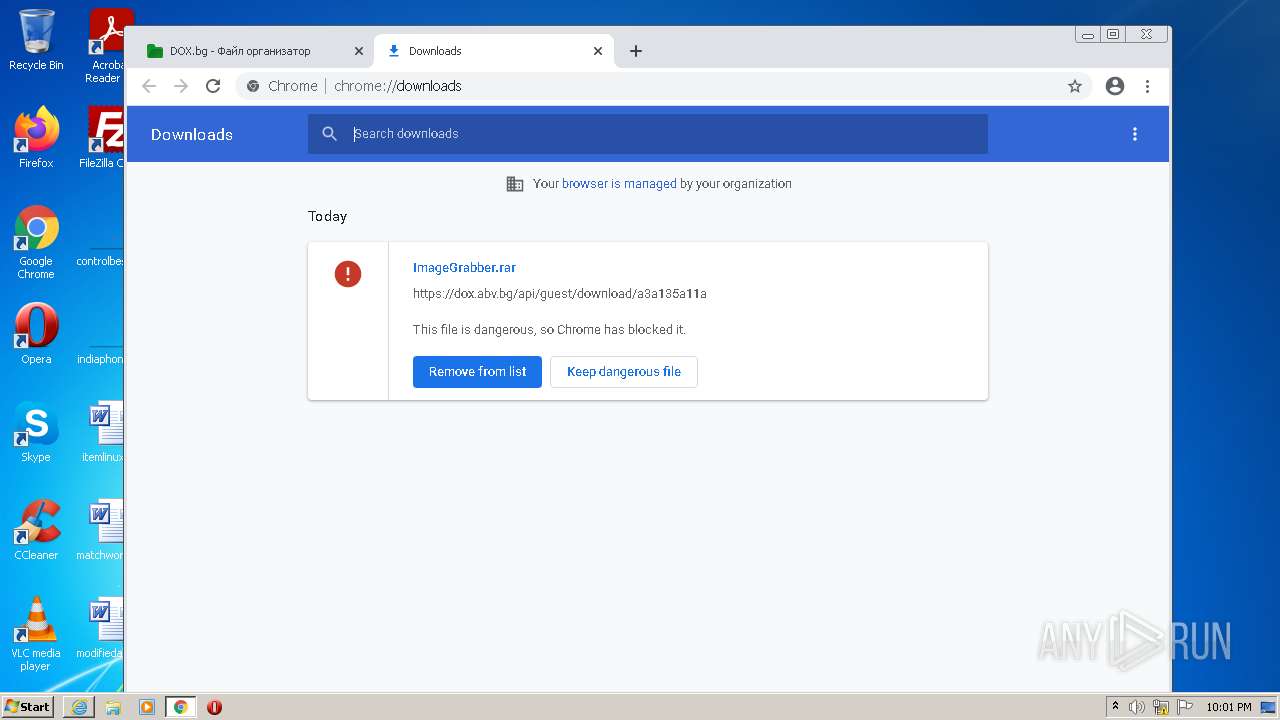
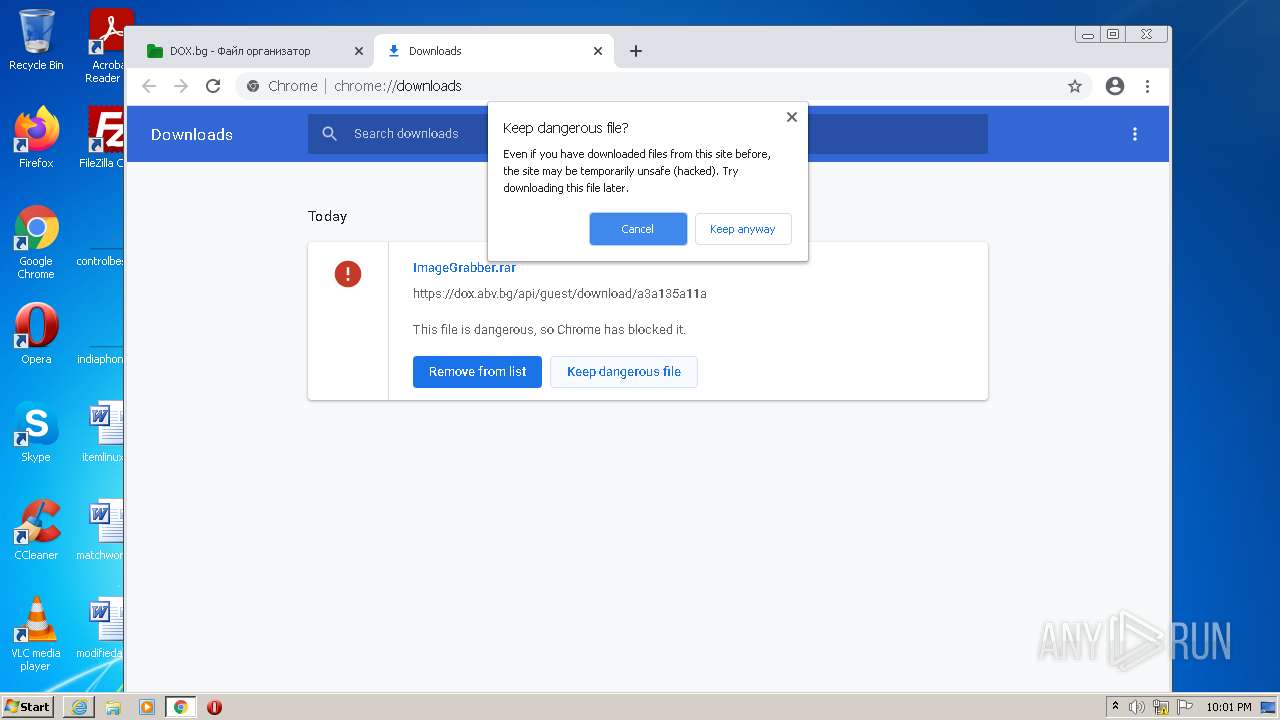
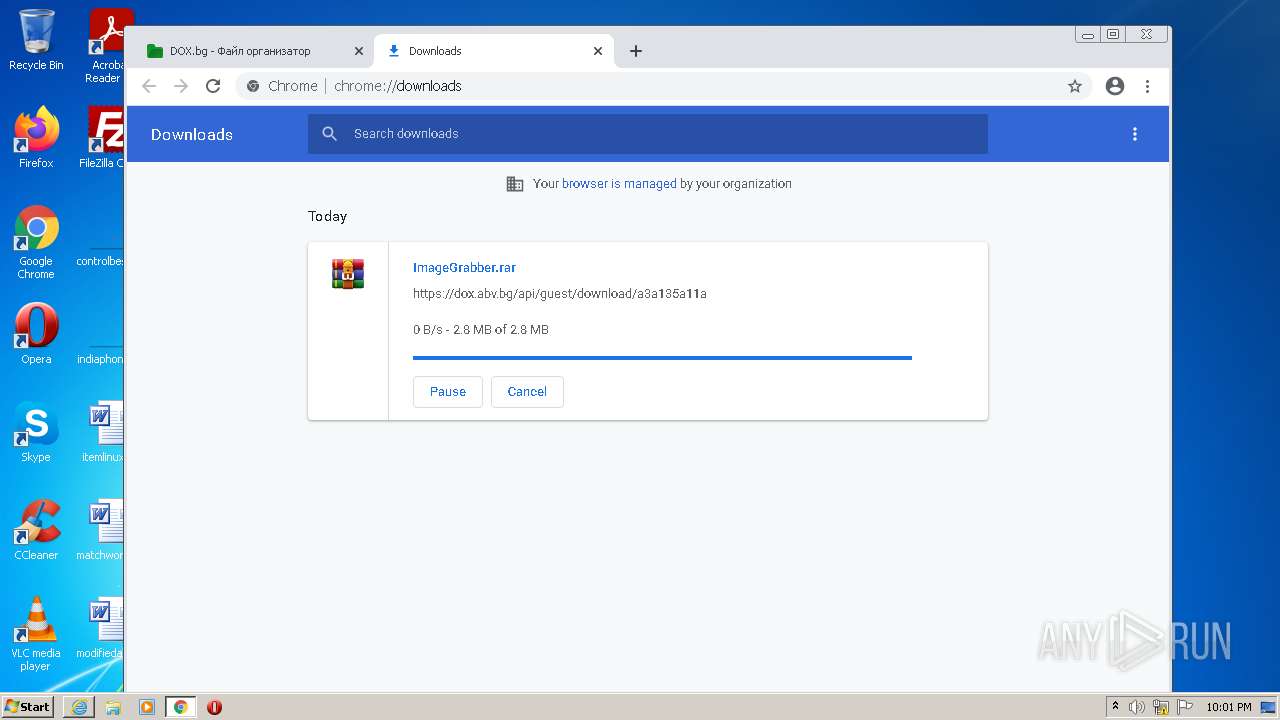
| URL: | https://dox.abv.bg/download?id=b0c808ff9c# |
| Full analysis: | https://app.any.run/tasks/7df11888-b57a-429d-afde-0345b2d2584f |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2022, 22:01:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3ECE9758BE83D63C1E6120406DFD90F6 |
| SHA1: | 7AA0F6966B9D93B549EDD126B985A97F2292527A |
| SHA256: | 7F763FC28257550BCDC9B47FB18D6B25F65EA772581FEC337F36FDC55C266BF0 |
| SSDEEP: | 3:N8ScHHBL2l8VBG:2ScHhxVw |
MALICIOUS
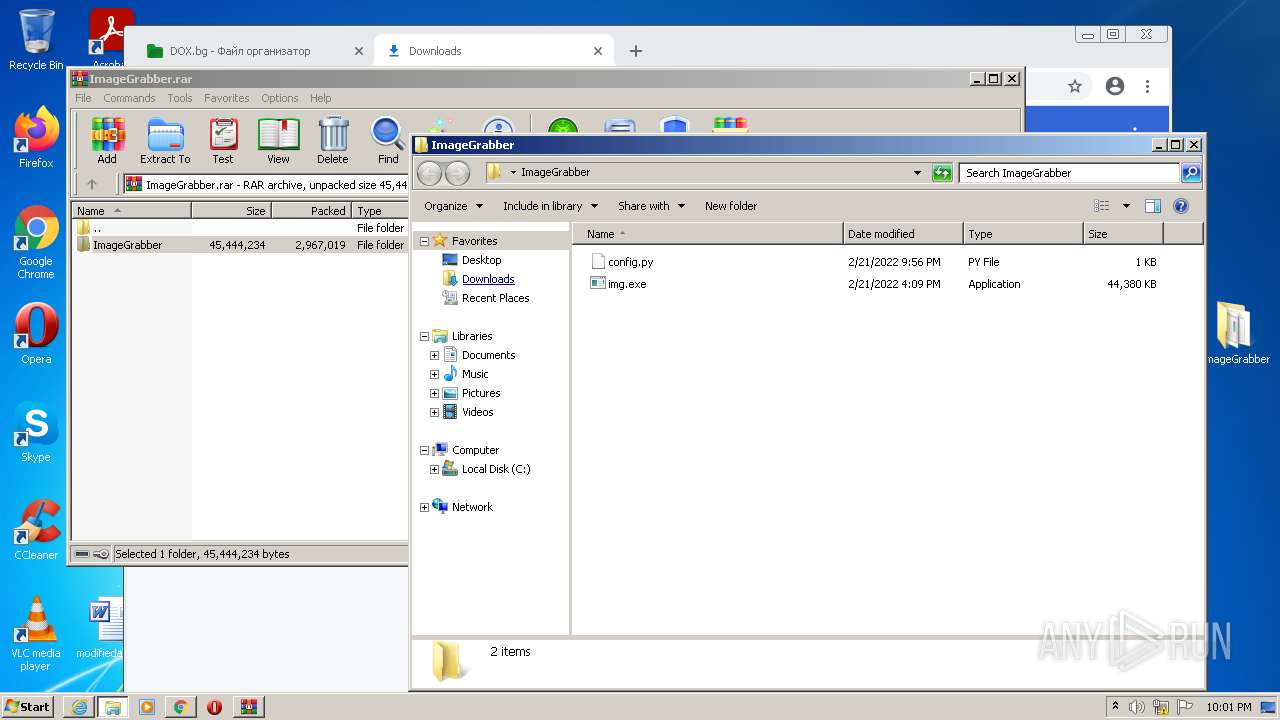
Drops executable file immediately after starts
- msdt.exe (PID: 2992)
- img.exe (PID: 3184)
Application was dropped or rewritten from another process
- RtkBtManServ.exe (PID: 2992)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 268)
Executable content was dropped or overwritten
- msdt.exe (PID: 2992)
- img.exe (PID: 3184)
- RtkBtManServ.exe (PID: 2992)
Drops a file with too old compile date
- msdt.exe (PID: 2992)
Executed via COM
- sdiagnhost.exe (PID: 2768)
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 2768)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1100)
Reads the computer name
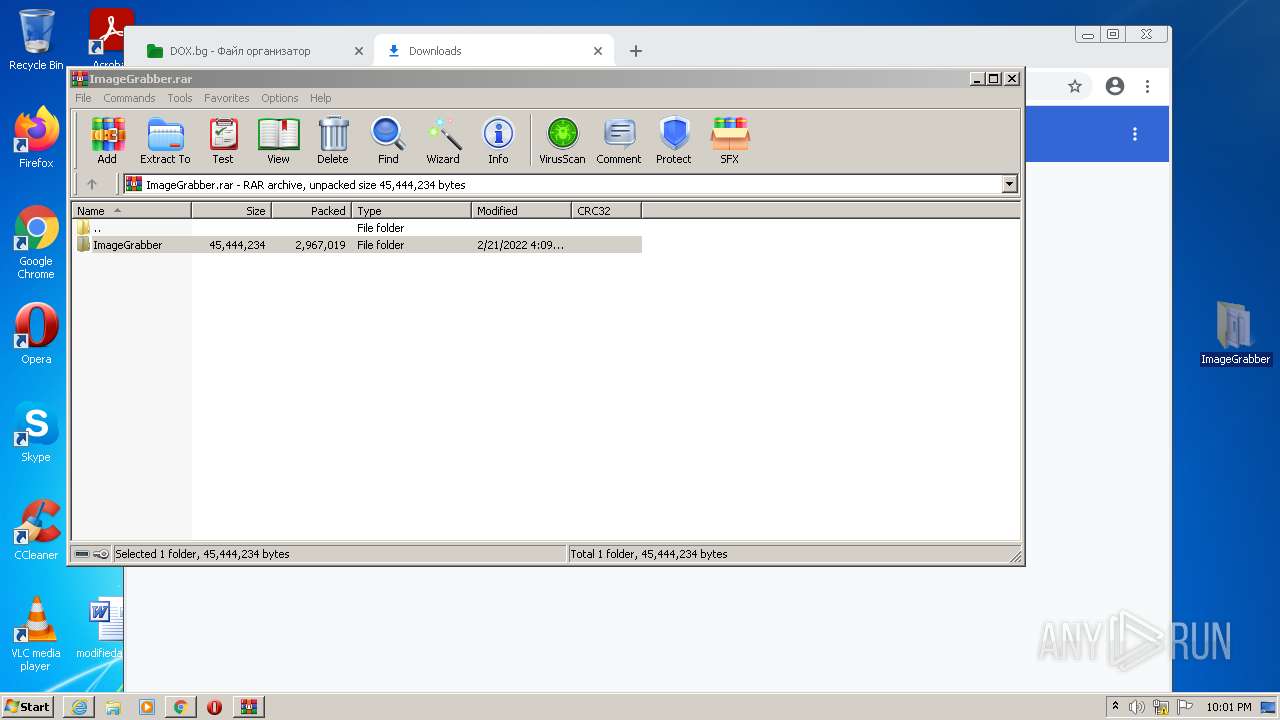
- WinRAR.exe (PID: 3792)
- img.exe (PID: 3184)
- RtkBtManServ.exe (PID: 2992)
Checks supported languages
- img.exe (PID: 3184)
- WinRAR.exe (PID: 3792)
- RtkBtManServ.exe (PID: 2992)
Drops a file that was compiled in debug mode
- RtkBtManServ.exe (PID: 2992)
INFO
Application launched itself
- iexplore.exe (PID: 3416)
- chrome.exe (PID: 1100)
Reads the computer name
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 268)
- msdt.exe (PID: 2992)
- sdiagnhost.exe (PID: 2768)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 2844)
- ipconfig.exe (PID: 2240)
- ROUTE.EXE (PID: 2792)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 3504)
Checks supported languages
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 268)
- msdt.exe (PID: 2992)
- sdiagnhost.exe (PID: 2768)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 1104)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 3868)
- ipconfig.exe (PID: 2240)
- makecab.exe (PID: 2452)
- ROUTE.EXE (PID: 2792)
- chrome.exe (PID: 556)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 1300)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 1520)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 3504)
Changes internet zones settings
- iexplore.exe (PID: 3416)
Reads internet explorer settings
- iexplore.exe (PID: 268)
Checks Windows Trust Settings
- msdt.exe (PID: 2992)
- iexplore.exe (PID: 3416)
- sdiagnhost.exe (PID: 2768)
Reads settings of System Certificates
- msdt.exe (PID: 2992)
- iexplore.exe (PID: 3416)
- chrome.exe (PID: 2924)
Manual execution by user
- chrome.exe (PID: 1100)
- img.exe (PID: 3184)
Reads the hosts file
- chrome.exe (PID: 1100)
- chrome.exe (PID: 2924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
33
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3416 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2860 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3180 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1044,3810682463057650756,5350462265437001074,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
36 791
Read events
36 523
Write events
266
Delete events
2
Modification events
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30943086 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30943086 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
9
Suspicious files
215
Text files
141
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62140BAA-44C.pma | — | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\NDF3B5F.tmp | binary | |
MD5:— | SHA256:— | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\NetworkDiagnosticsTroubleshoot.ps1 | text | |
MD5:1D192CE36953DBB7DC7EE0D04C57AD8D | SHA256:935A231924AE5D4A017B0C99D4A5F3904EF280CEA4B3F727D365283E26E8A756 | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\HTInteractiveRes.ps1 | text | |
MD5:C25ED2111C6EE9299E6D9BF51012F2F5 | SHA256:8E326EE0475208D4C943D885035058FAD7146BBA02B66305F7C9F31F6A57E81B | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\InteractiveRes.ps1 | text | |
MD5:25B8543DBF571F040118423BC3C7A75E | SHA256:D78E6291D6F27AC6FEBDCF0A4D5A34521E7F033AF8875E026DF21BA7513AB64A | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\DiagPackage.diagpkg | xml | |
MD5:C9FB87FA3460FAE6D5D599236CFD77E2 | SHA256:CDE728C08A4E50A02FCFF35C90EE2B3B33AB24C8B858F180B6A67BFA94DEF35F | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\result\results.xsl | xml | |
MD5:310E1DA2344BA6CA96666FB639840EA9 | SHA256:67401342192BABC27E62D4C1E0940409CC3F2BD28F77399E71D245EAE8D3F63C | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\StartDPSService.ps1 | text | |
MD5:A660422059D953C6D681B53A6977100E | SHA256:D19677234127C38A52AEC23686775A8EB3F4E3A406F4A11804D97602D6C31813 | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\NetworkDiagnosticsVerify.ps1 | text | |
MD5:C0BB6343BD0F6F9B46B33E4B66106953 | SHA256:EB9BC61668A93759D0127A11CDFC03E924100D69C7E6457FEAA89330474C90C3 | |||
| 2992 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_4ab3f8ef-9e14-4ac8-9235-75c404bb6772\NetworkDiagnosticsResolve.ps1 | text | |
MD5:A7B957F221C643580184665BE57E6AC8 | SHA256:8582EF50174CB74233F196F193E04C0CCBBEE2AED5CE50964CBB95822C218E7F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
86
DNS requests
51
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3416 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3416 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2924 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
3416 | iexplore.exe | GET | 200 | 2.16.106.186:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70fbc2ab68232dfb | unknown | compressed | 4.70 Kb | whitelisted |
3416 | iexplore.exe | GET | 200 | 2.16.106.186:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d5a6dd4f3e8c7a9c | unknown | compressed | 4.70 Kb | whitelisted |
2924 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?dc543dbd5a3e837a | US | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
268 | iexplore.exe | 194.153.145.119:443 | dox.abv.bg | Telepoint Ltd | BG | suspicious |
3416 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3416 | iexplore.exe | 2.16.106.186:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2924 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2924 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 142.250.186.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 142.250.185.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 142.250.186.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dox.abv.bg |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
268 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
268 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
268 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |