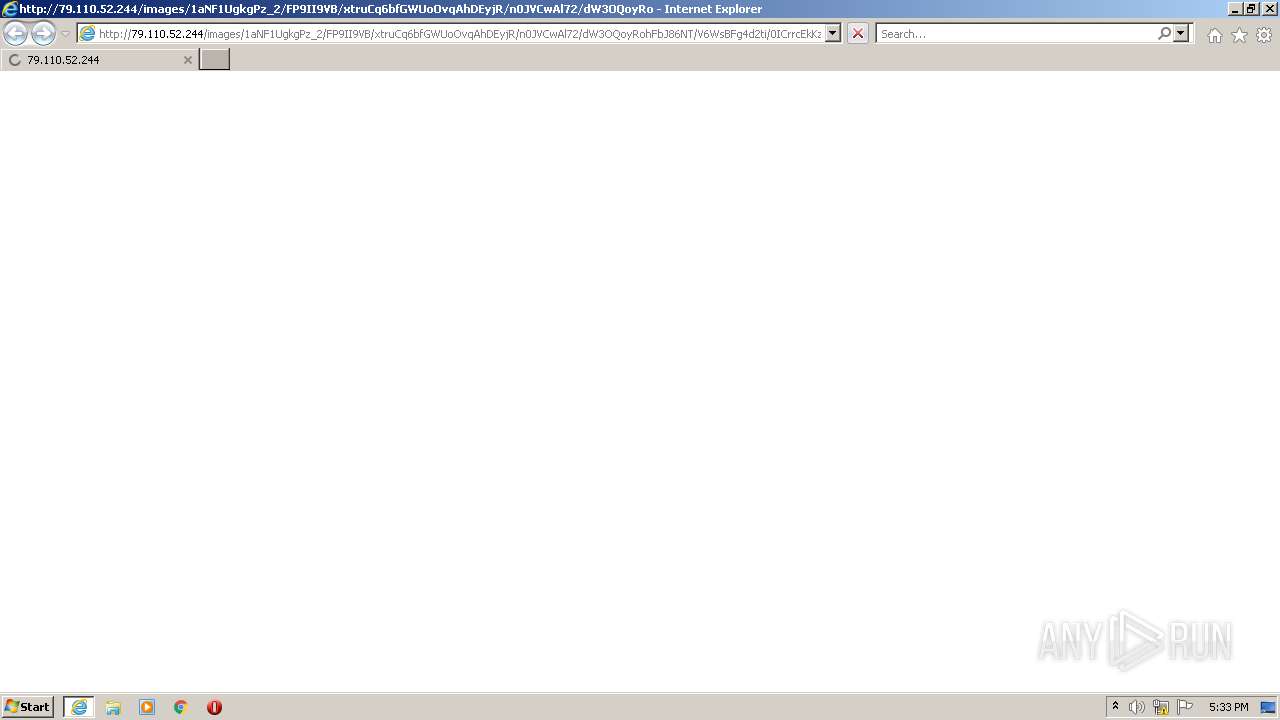
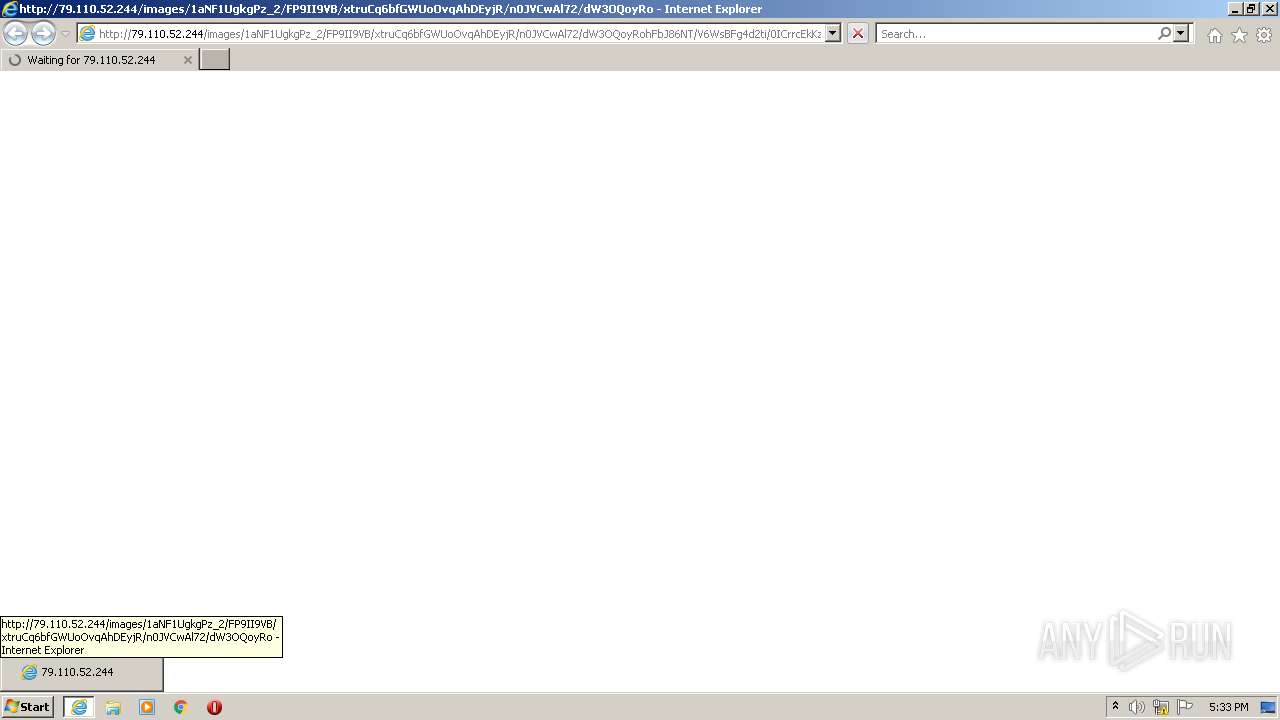
| URL: | http://79.110.52.244/images/1aNF1UgkgPz_2/FP9II9VB/xtruCq6bfGWUoOvqAhDEyjR/n0JVCwAl72/dW3OQoyRohFbJ86NT/V6WsBFg4d2ti/0ICrrcEkKz7/bUZG0UaPeVDWGB/n6ohu7yhPDvwJKQUr53O_/2Bthm8DSgsv_2FRS/xb82u9MSPBwZNEv/cA6XaJR0SufDvijHcc/SJOPNH_2B/BkeSq0TpomjvNyGH7qRC/fOEVoD_2FHoieqVfJaF/Z38DVgTyYhQTQJeRMrw8Vc/_2FJ_2BDjUgg6/j3uONksg/ji_2F78cjLCIItceGgiw4Rq/FLn2OK2xLI/hlDZUkwJDk2FCSJja/L3Qzy85x4gI_2Bh81M/E.jpeg |
| Full analysis: | https://app.any.run/tasks/3221976a-378a-4ea2-a6dc-07451fcf3377 |
| Verdict: | Malicious activity |
| Threats: | Trojans are a group of malicious programs distinguished by their ability to masquerade as benign software. Depending on their type, trojans possess a variety of capabilities, ranging from maintaining full remote control over the victim’s machine to stealing data and files, as well as dropping other malware. At the same time, the main functionality of each trojan family can differ significantly depending on its type. The most common trojan infection chain starts with a phishing email. |
| Analysis date: | July 15, 2022, 16:32:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C16D854689A966E0961DB5102ABEB635 |
| SHA1: | E04362D25C34644E0328A9679B5212A19F3360FF |
| SHA256: | 7F6EBDE37BA8D58DD5FD69586957BE9F62A42D7B5C47128D71B1848AB7B8C981 |
| SSDEEP: | 6:CSqsmTXvFKOqXB1ANtHkFciqrkGpxe3Dh/PrFoiwB3Q+We5Pqukb3J1n:teT9iitEnq4Gp03DBiiwBg+V5ydb3f |
MALICIOUS
URSNIF was detected
- iexplore.exe (PID: 3140)
Connects to CnC server
- iexplore.exe (PID: 3140)
SUSPICIOUS
Checks supported languages
- notepad++.exe (PID: 2852)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3140)
INFO
Checks supported languages
- iexplore.exe (PID: 1332)
- rundll32.exe (PID: 1384)
- iexplore.exe (PID: 3140)
Reads the computer name
- iexplore.exe (PID: 1332)
- iexplore.exe (PID: 3140)
Application launched itself
- iexplore.exe (PID: 1332)
Reads the date of Windows installation
- iexplore.exe (PID: 1332)
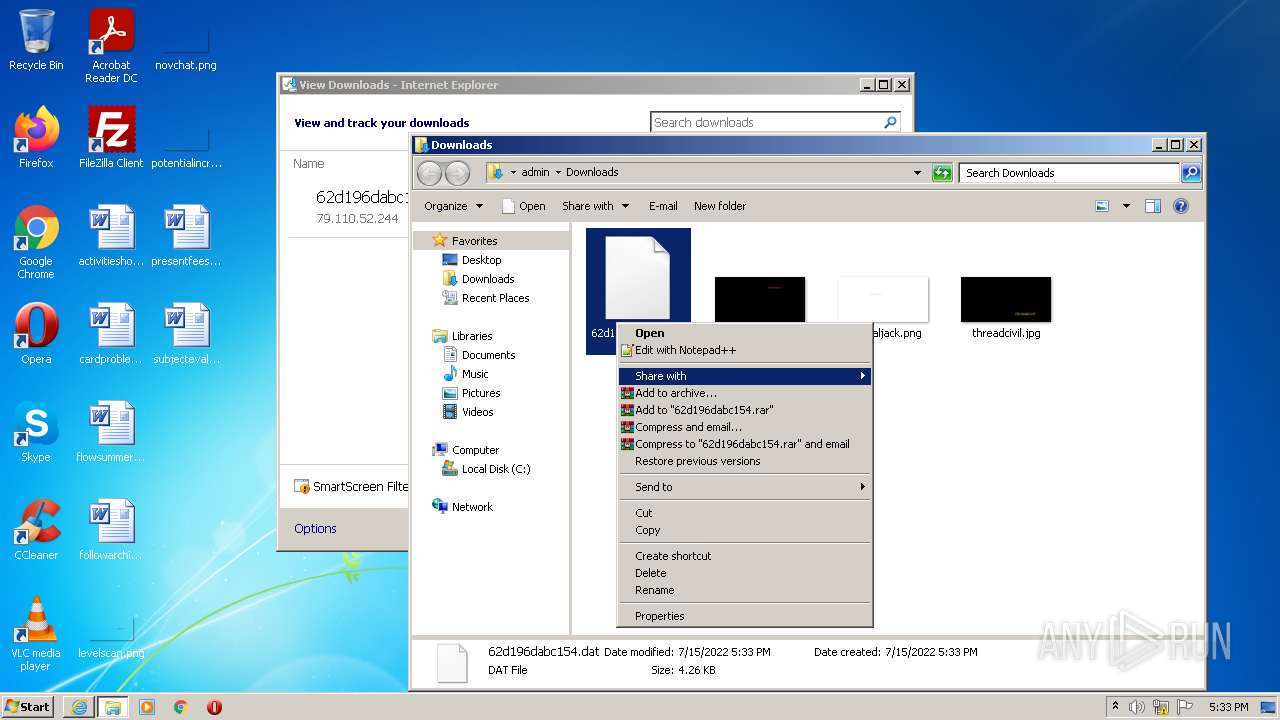
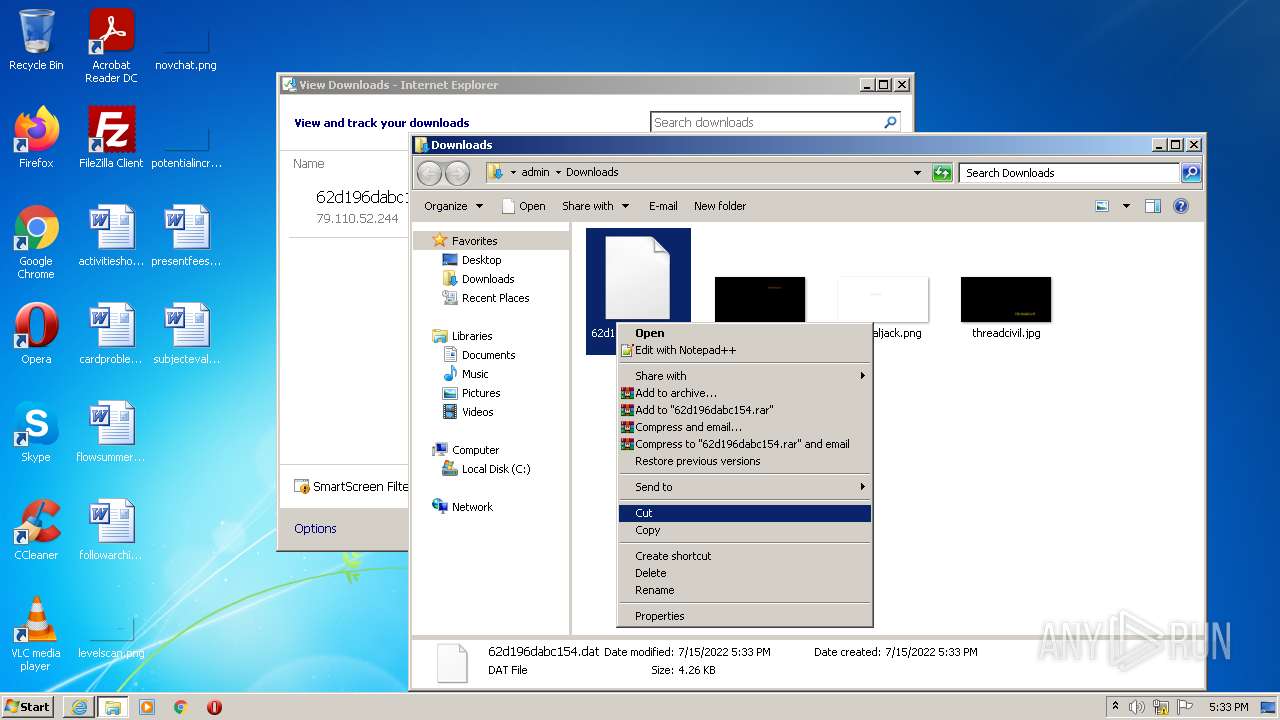
Manual execution by user
- rundll32.exe (PID: 1384)
- notepad++.exe (PID: 2852)
Reads settings of System Certificates
- iexplore.exe (PID: 1332)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1332)
Checks Windows Trust Settings
- iexplore.exe (PID: 1332)
Reads internet explorer settings
- iexplore.exe (PID: 3140)
Changes internet zones settings
- iexplore.exe (PID: 1332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1332 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://79.110.52.244/images/1aNF1UgkgPz_2/FP9II9VB/xtruCq6bfGWUoOvqAhDEyjR/n0JVCwAl72/dW3OQoyRohFbJ86NT/V6WsBFg4d2ti/0ICrrcEkKz7/bUZG0UaPeVDWGB/n6ohu7yhPDvwJKQUr53O_/2Bthm8DSgsv_2FRS/xb82u9MSPBwZNEv/cA6XaJR0SufDvijHcc/SJOPNH_2B/BkeSq0TpomjvNyGH7qRC/fOEVoD_2FHoieqVfJaF/Z38DVgTyYhQTQJeRMrw8Vc/_2FJ_2BDjUgg6/j3uONksg/ji_2F78cjLCIItceGgiw4Rq/FLn2OK2xLI/hlDZUkwJDk2FCSJja/L3Qzy85x4gI_2Bh81M/E.jpeg" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
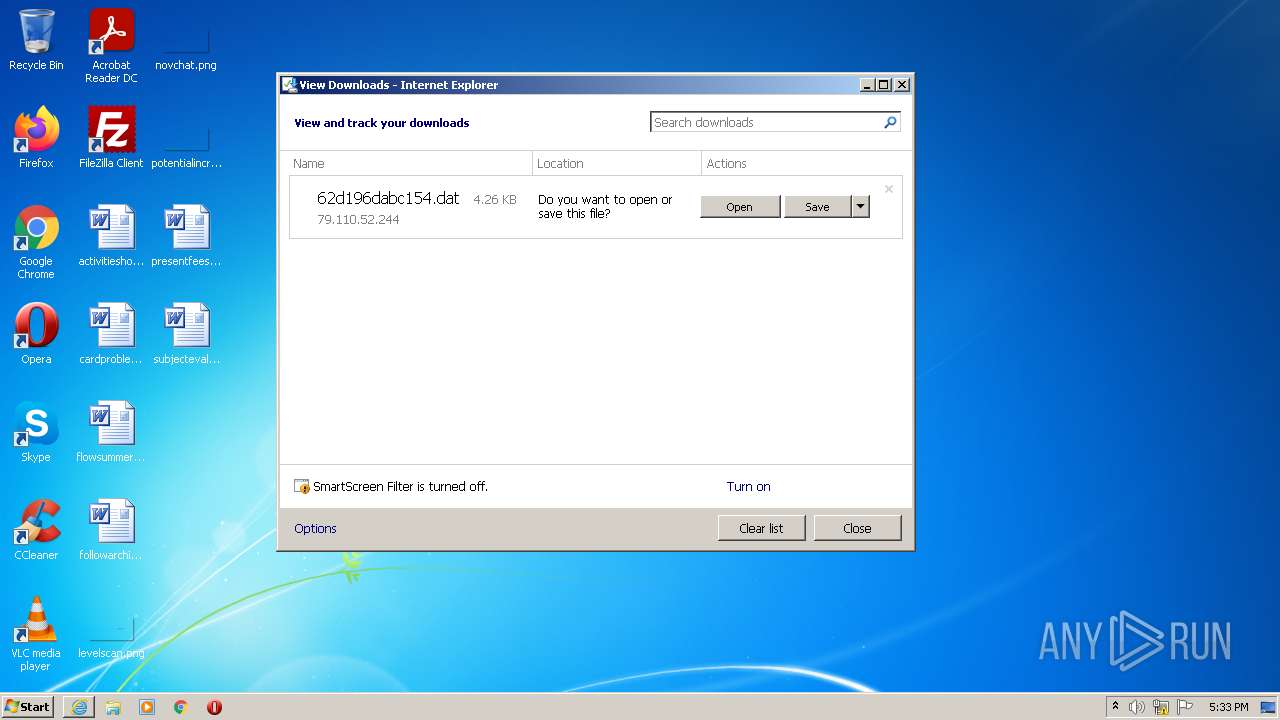
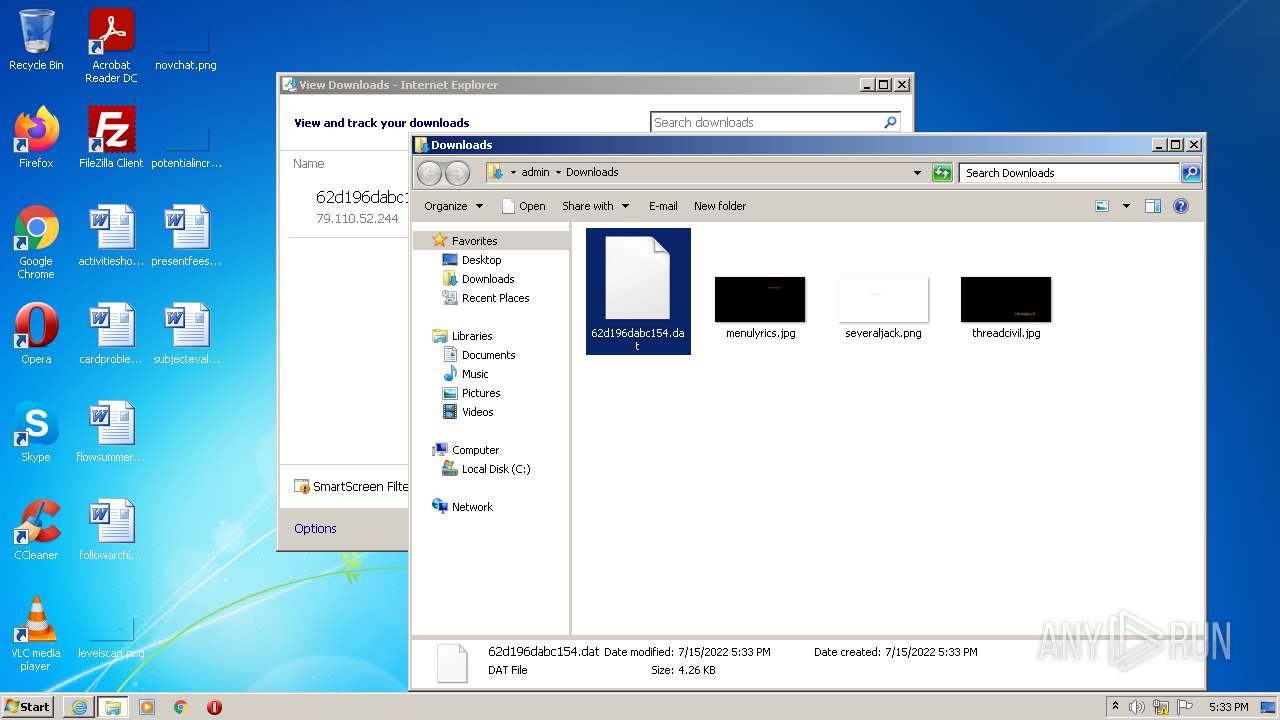
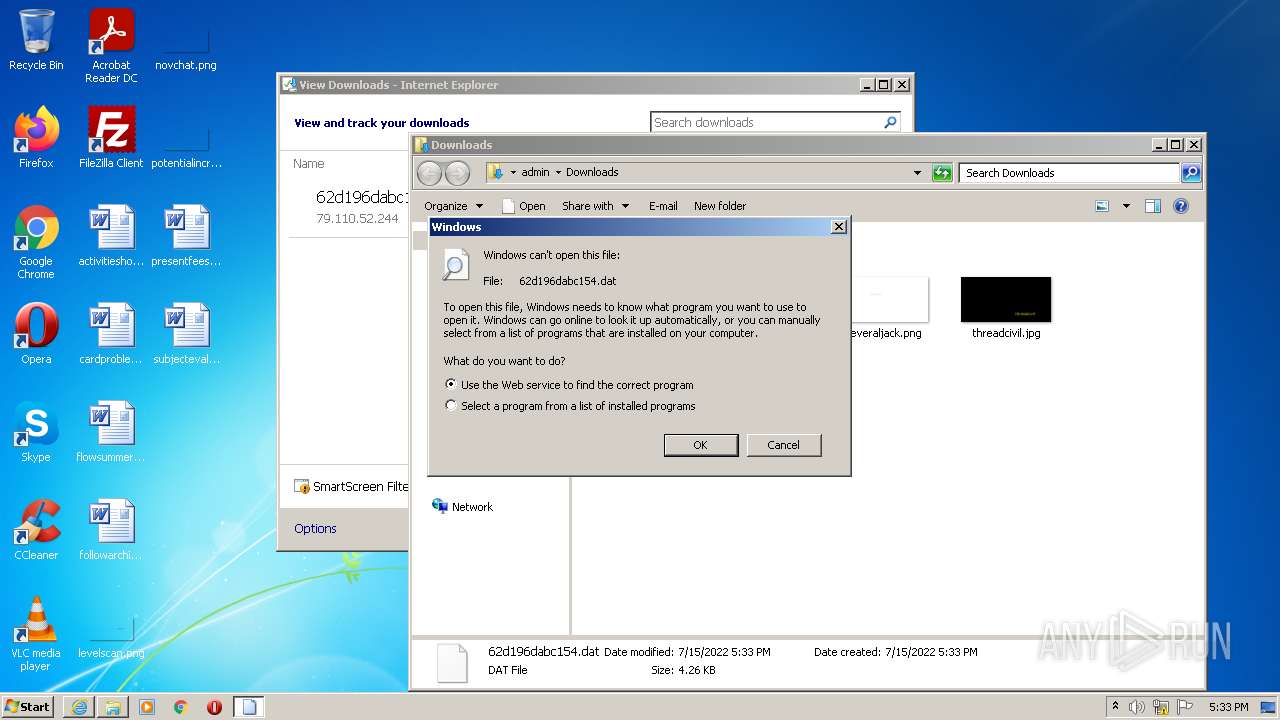
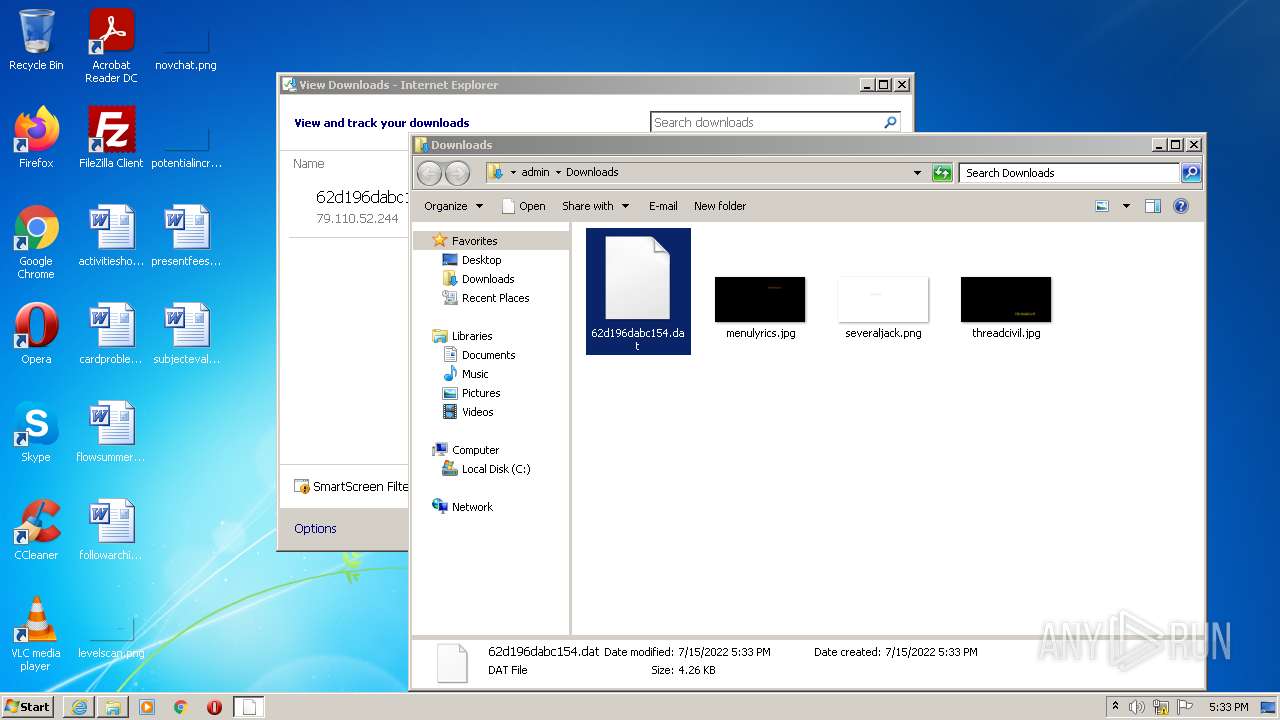
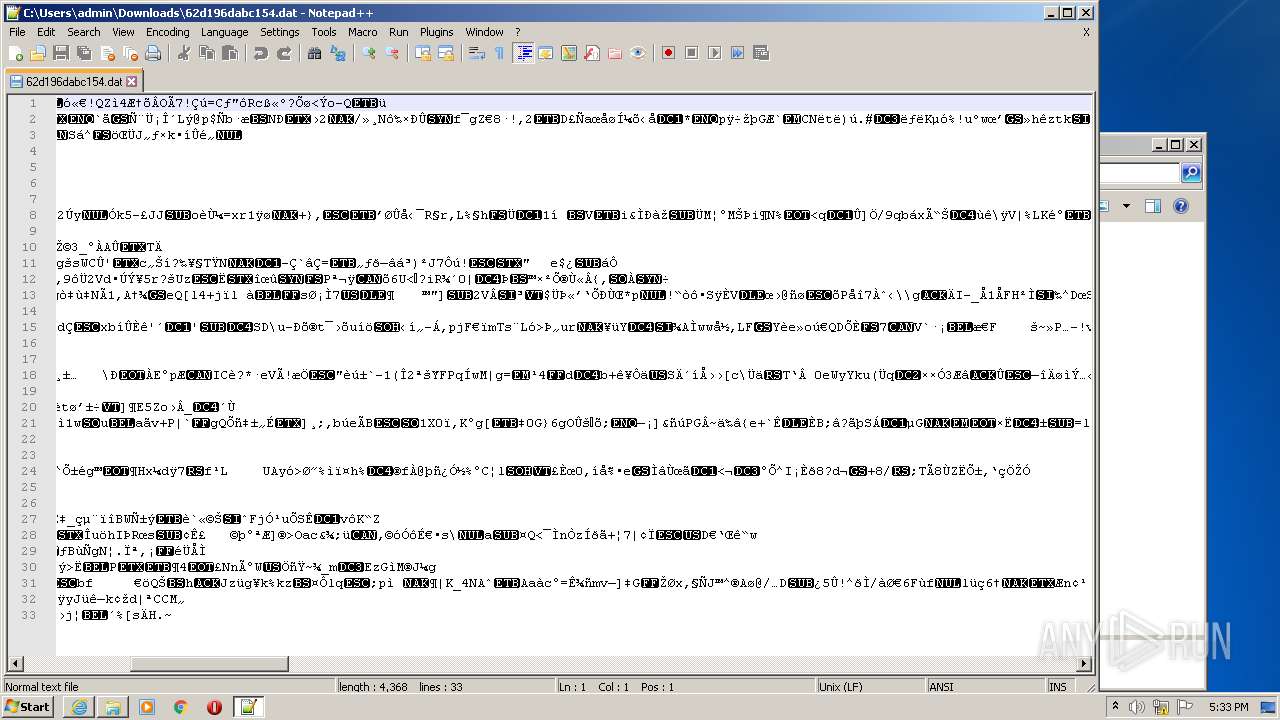
| 1384 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\62d196dabc154.dat | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
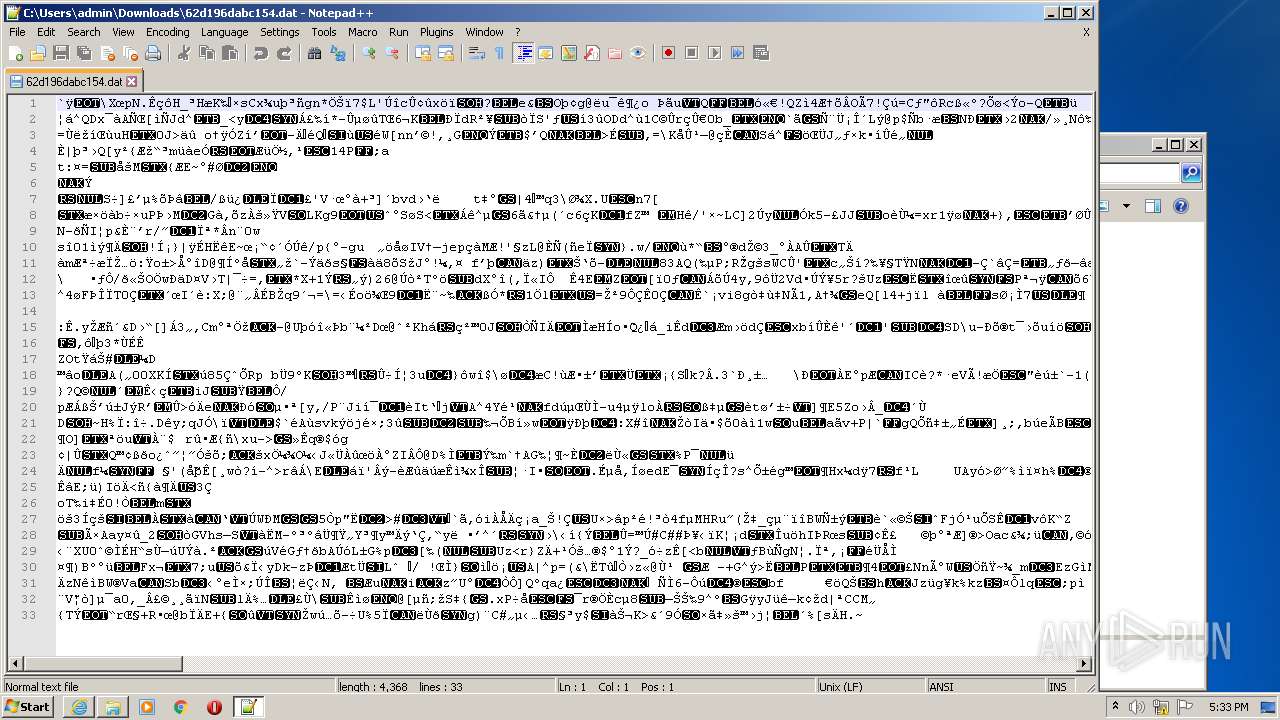
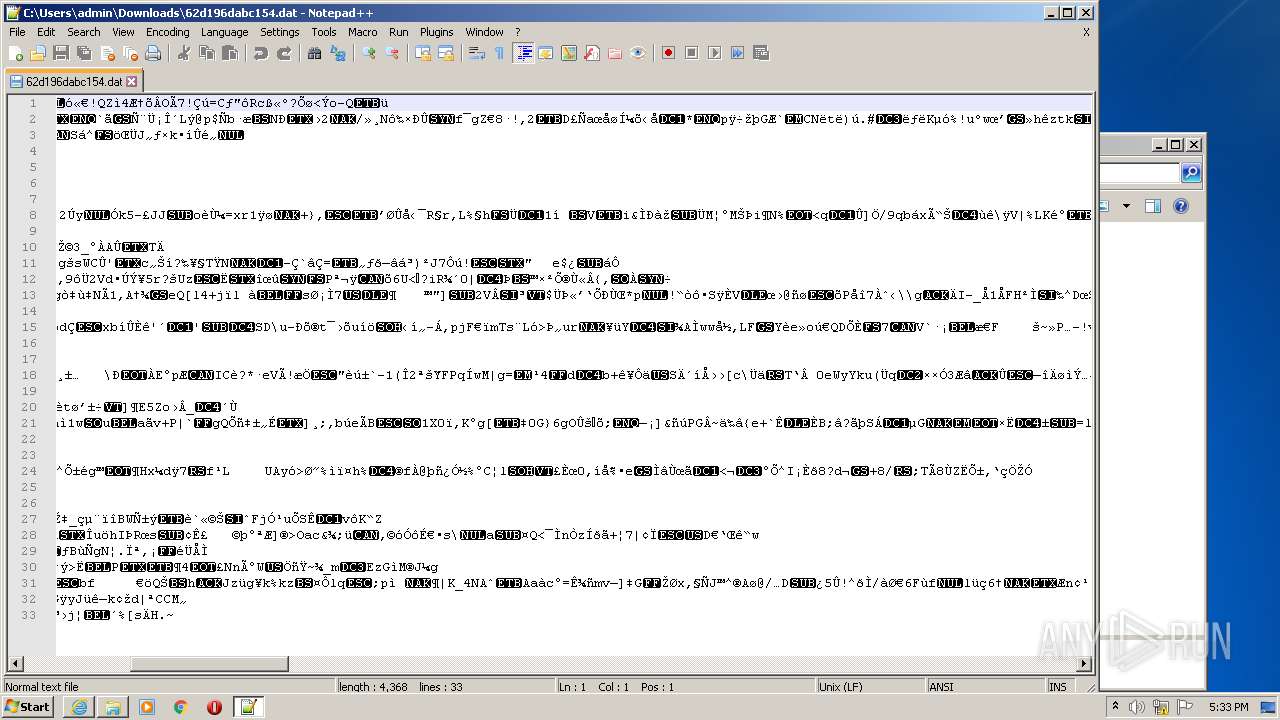
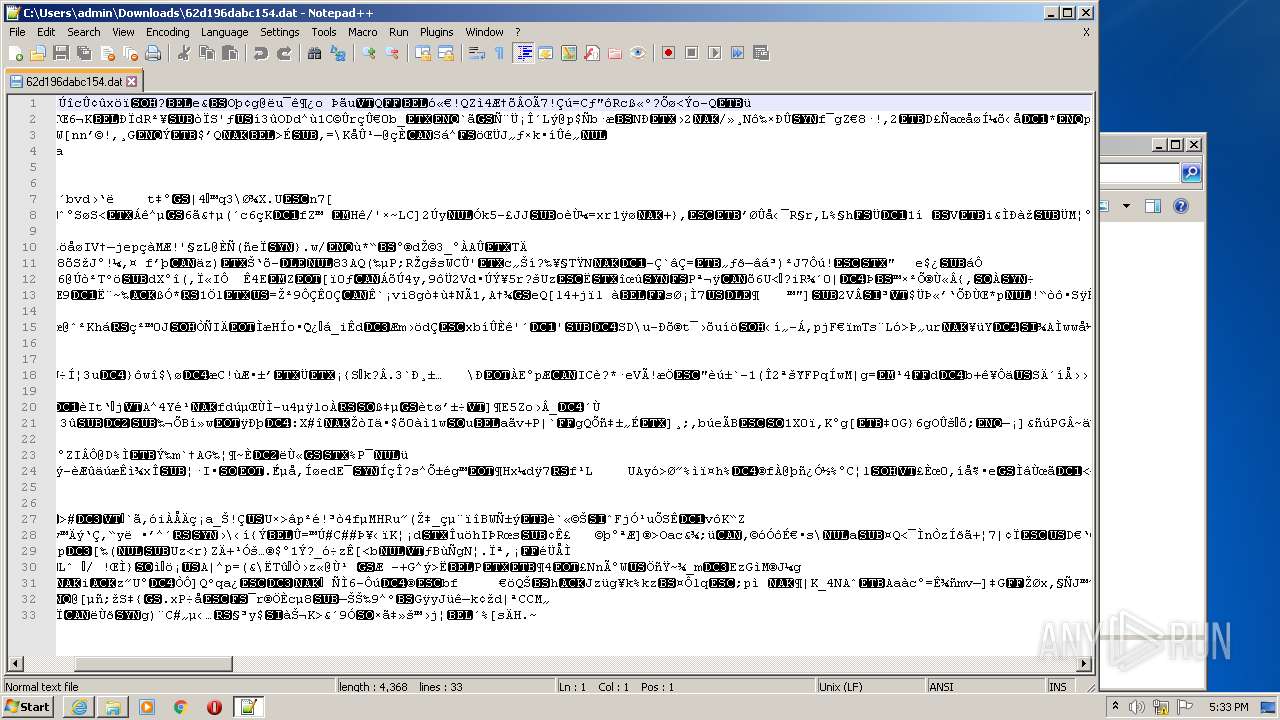
| 2852 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\62d196dabc154.dat" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1332 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 263
Read events
7 140
Write events
123
Delete events
0
Modification events
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30972008 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30972008 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
9
Text files
6
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
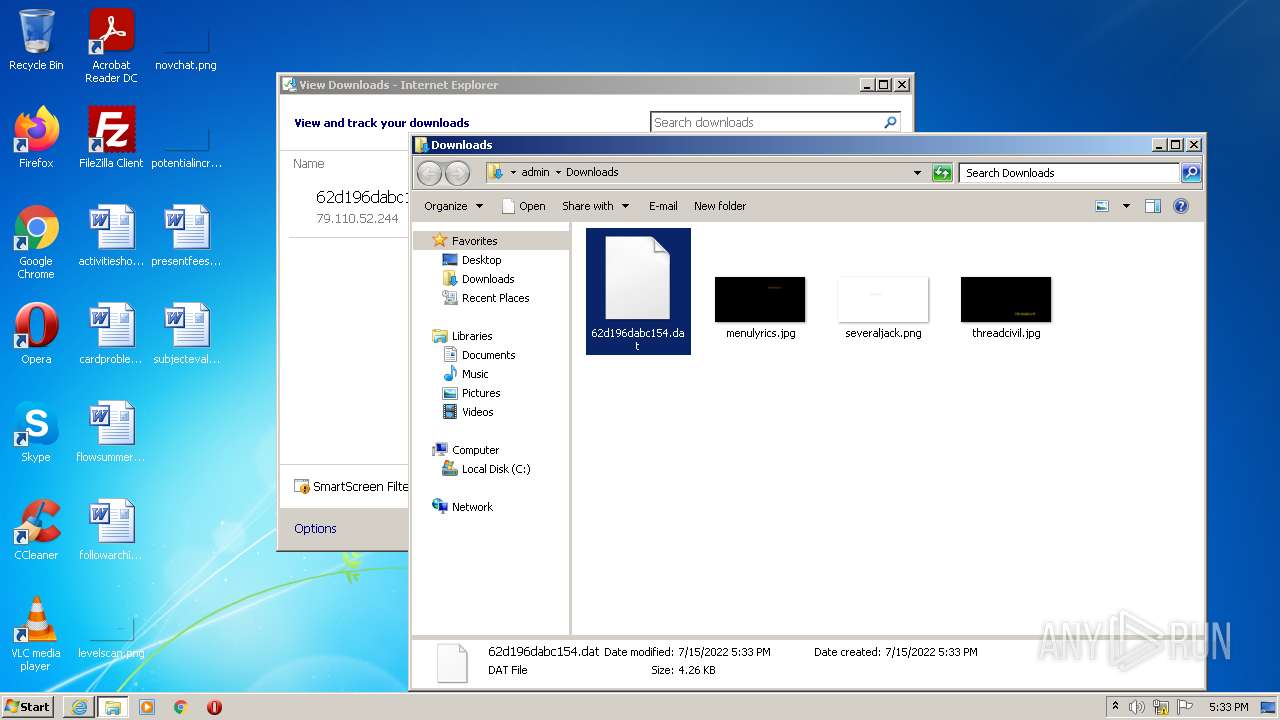
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\62d196dabc154[1].dat | binary | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{C985C2BB-045B-11ED-8C9F-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1210F6E0B64E4431.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\Downloads\62d196dabc154.dat | binary | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{D30803AA-045B-11ED-8C9F-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 1332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF96F71315FA3F891A.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
22
DNS requests
12
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3140 | iexplore.exe | GET | 200 | 79.110.52.244:80 | http://79.110.52.244/images/1aNF1UgkgPz_2/FP9II9VB/xtruCq6bfGWUoOvqAhDEyjR/n0JVCwAl72/dW3OQoyRohFbJ86NT/V6WsBFg4d2ti/0ICrrcEkKz7/bUZG0UaPeVDWGB/n6ohu7yhPDvwJKQUr53O_/2Bthm8DSgsv_2FRS/xb82u9MSPBwZNEv/cA6XaJR0SufDvijHcc/SJOPNH_2B/BkeSq0TpomjvNyGH7qRC/fOEVoD_2FHoieqVfJaF/Z38DVgTyYhQTQJeRMrw8Vc/_2FJ_2BDjUgg6/j3uONksg/ji_2F78cjLCIItceGgiw4Rq/FLn2OK2xLI/hlDZUkwJDk2FCSJja/L3Qzy85x4gI_2Bh81M/E.jpeg | unknown | binary | 4.27 Kb | malicious |
1332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1332 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9cb9948fc2784e09 | US | compressed | 4.70 Kb | whitelisted |
1332 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?175633d0d9a3ce48 | US | compressed | 4.70 Kb | whitelisted |
1332 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?558300e65715dc53 | US | compressed | 4.70 Kb | whitelisted |
1332 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d37f9224ece94a8d | US | compressed | 4.70 Kb | whitelisted |
1332 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?13a7ef4b2ab263f9 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | iexplore.exe | 79.110.52.244:80 | — | — | — | malicious |
1332 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1332 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1332 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1332 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1332 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3140 | iexplore.exe | A Network Trojan was detected | ET TROJAN Ursnif Variant CnC Beacon - URI Struct M1 (_2B) |
3140 | iexplore.exe | A Network Trojan was detected | ET TROJAN Ursnif Variant CnC Beacon - URI Struct M2 (_2F) |
3140 | iexplore.exe | A Network Trojan was detected | AV TROJAN Ursnif Variant CnC Beacon 2019-09-18 |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|