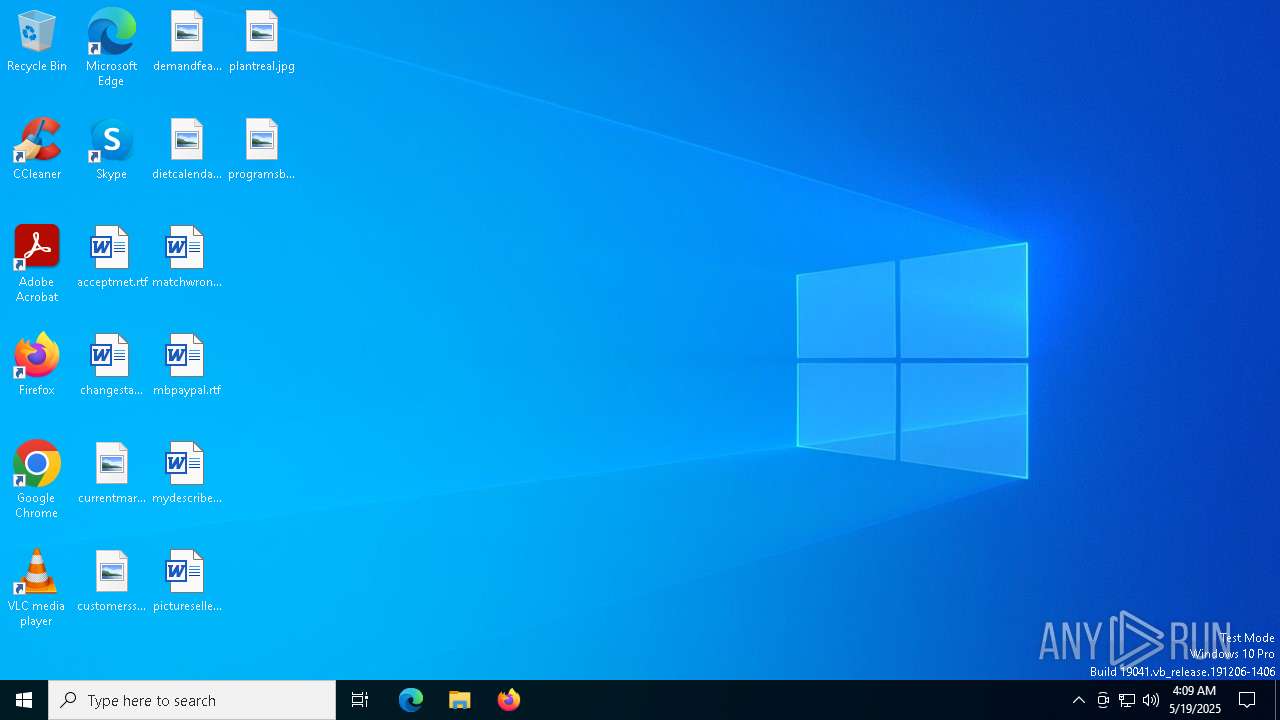
| File name: | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta |
| Full analysis: | https://app.any.run/tasks/8103ced2-6180-4e96-aa4b-a6b679c6fca4 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 04:09:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 968DB9C025884CA2F6F7CA7093CD9745 |
| SHA1: | 5346911B62CAEF4499617FF63BEFC80016806140 |
| SHA256: | 7F6BAC6C5A924CDD9CD1A84CCDE30561F9731A9C7DF71E3BA0E760DA0EFC2787 |
| SSDEEP: | 12288:wK5DHcef6d3EA3+8tNNNRQcssssssssssssssssssssssssssssssssssssssss7:w8D/Cd3Q5BJ8 |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7416)
- FileCoAuth.exe (PID: 7796)
NESHTA mutex has been found
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- FileCoAuth.exe (PID: 7736)
SUSPICIOUS
Starts a Microsoft application from unusual location
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7416)
- FileCoAuth.exe (PID: 7796)
Mutex name with non-standard characters
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- FileCoAuth.exe (PID: 7736)
Reads security settings of Internet Explorer
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- FileCoAuth.exe (PID: 7736)
Executable content was dropped or overwritten
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- FileCoAuth.exe (PID: 7736)
There is functionality for taking screenshot (YARA)
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
Process drops legitimate windows executable
- FileCoAuth.exe (PID: 7736)
INFO
Create files in a temporary directory
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7416)
- FileCoAuth.exe (PID: 7796)
Reads the computer name
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- FileCoAuth.exe (PID: 7796)
Checks supported languages
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7416)
- FileCoAuth.exe (PID: 7796)
Process checks computer location settings
- 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe (PID: 7372)
- FileCoAuth.exe (PID: 7736)
The sample compiled with english language support
- FileCoAuth.exe (PID: 7736)
Reads the machine GUID from the registry
- FileCoAuth.exe (PID: 7796)
Creates files or folders in the user directory
- FileCoAuth.exe (PID: 7796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (89.3) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (4.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.2) |
| .exe | | | Win32 Executable (generic) (1.5) |
| .exe | | | Win16/32 Executable Delphi generic (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8178 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
132
Monitored processes
6
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7372 | "C:\Users\admin\Desktop\2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe" | C:\Users\admin\Desktop\2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7416 | "C:\Users\admin\AppData\Local\Temp\3582-490\2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | — | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Multi-Msi ActiveDirectory Deployment Tool. Exit code: 2 Version: 16.0.4266.1001 Modules
| |||||||||||||||
| 7424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7736 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7796 | "C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe" -Embedding | C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe | — | FileCoAuth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 8136 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 025
Read events
4 025
Write events
0
Delete events
0
Modification events
Executable files
9
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7372 | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:E60370FDAC9779E853E960B9EC930616 | SHA256:08AB8ECA39C472669E2E9103D28EBB8C7784630AB9F1F2493BCA69026D190611 | |||
| 7372 | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | executable | |
MD5:FF256373CE284A43ABECA5E9FCD027D7 | SHA256:3390038959B4D4F558AF67E2DE6493FCA4CE603FDB647E08D09A84F9ED84A0D8 | |||
| 7372 | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe | executable | |
MD5:7F9006F19C0CBB5BB9F40605576A4CE9 | SHA256:D6D33568DF03B731DFB112ABA5B37783BF40C33DB118E8EDA2CE4FCF0BFAB130 | |||
| 7736 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe | executable | |
MD5:394DEEEF3E5FFE6C77A9CDA1832361BB | SHA256:37DCEC7509B0803F2BBA453845ED67FDBAA15771F8A60FC11F9082FD2A64BD23 | |||
| 7372 | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | C:\Users\admin\AppData\Local\Temp\3582-490\2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | executable | |
MD5:87AD1A0BA3F8F55EDBFD974AA767CDD8 | SHA256:3CC7F80D2FA3177B508350AFE4F68AE2FA7D6600D3692EDF25F006AD8246CB7F | |||
| 7372 | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncHelper.exe | executable | |
MD5:87520E22AA036B3F34CD51F3CFABC97B | SHA256:F1AA5E4D81DD63E88908AC3AAE5D40D56FAFF8F52B4ED221256A362C7D841AE2 | |||
| 7372 | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\OneDriveUpdaterService.exe | executable | |
MD5:EC063B6C587473DD9234B3ED966C3500 | SHA256:0EBEE41F9AB8D834123D9A8FC704AA403BD5A3CFA4AC94B81E581E548E77CE7A | |||
| 7416 | 2025-05-19_968db9c025884ca2f6f7ca7093cd9745_black-basta_darkgate_elex_gcleaner_luca-stealer_neshta.exe | C:\Users\admin\AppData\Local\Temp\ODEPLOY(202505190409531CF8).log | text | |
MD5:10453FF64CD30F0EC05D2FD27CA920A6 | SHA256:2B2E591444674B6DF578CCCA69DA53A2F60E4A10040DEBB9ECE59D003CB22BF0 | |||
| 7796 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2025-05-19.0410.7796.1.aodl | binary | |
MD5:28DCA2FF4B34B5A52A2E59DF202A6ED3 | SHA256:33BACCB7296F1ED1F995FC77A23049F261CF391AC0388F9E8DD161F8C17B7F94 | |||
| 7796 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2025-05-19.0410.7796.1.odl | binary | |
MD5:DC1EA7F6280A41DBFF1254ED8C6CA414 | SHA256:D57E0717A2D8C632D978A6D3DB28F772EFCF069200C28072496C2B6580FAA392 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
48
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7852 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7852 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4164 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |