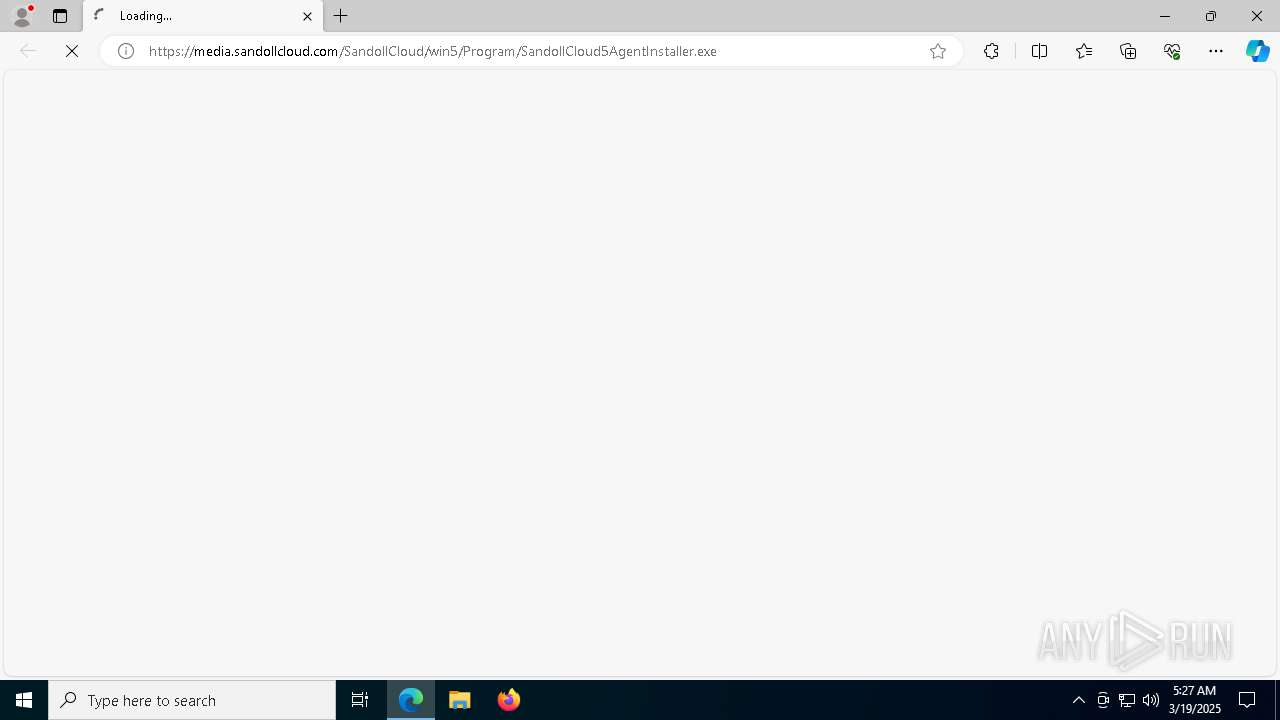
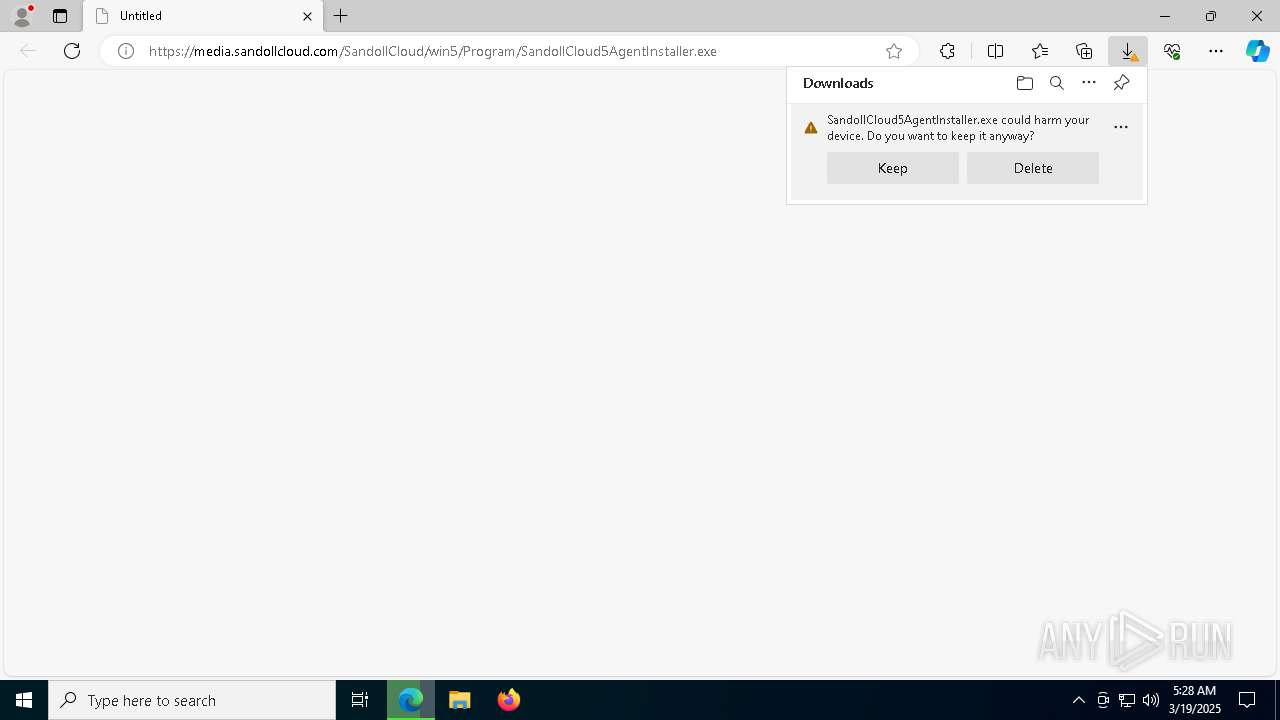
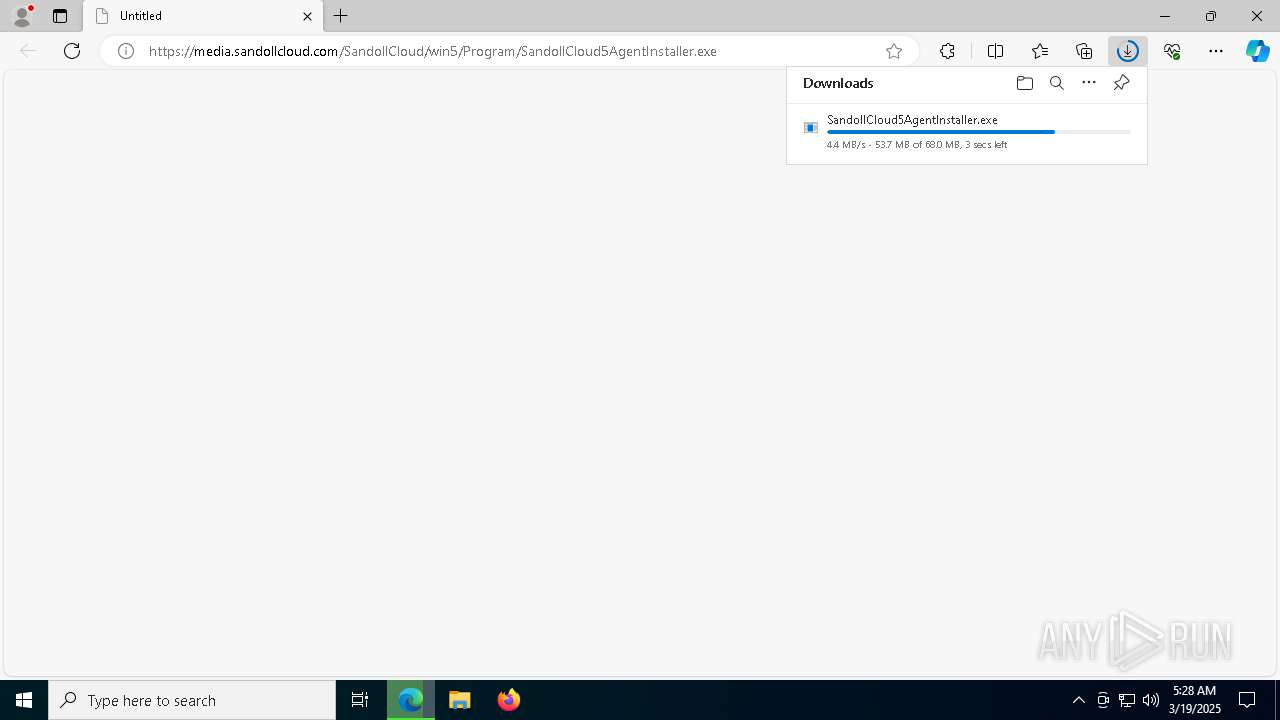
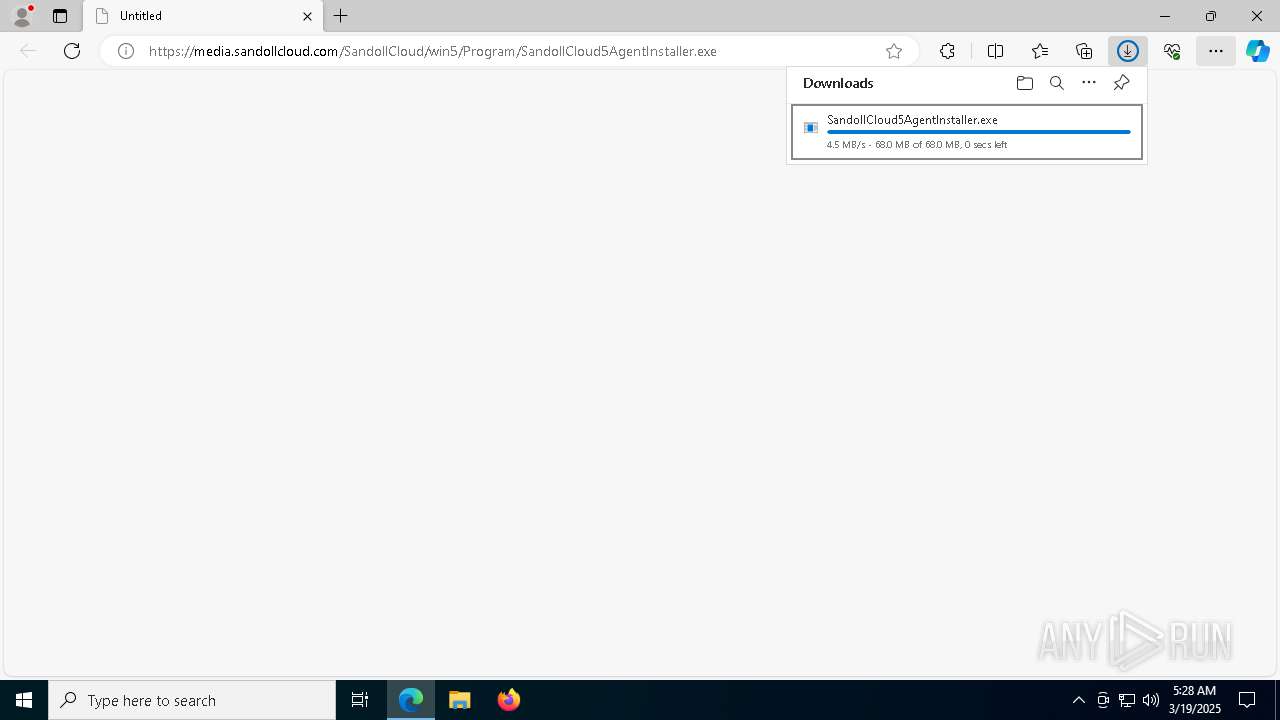
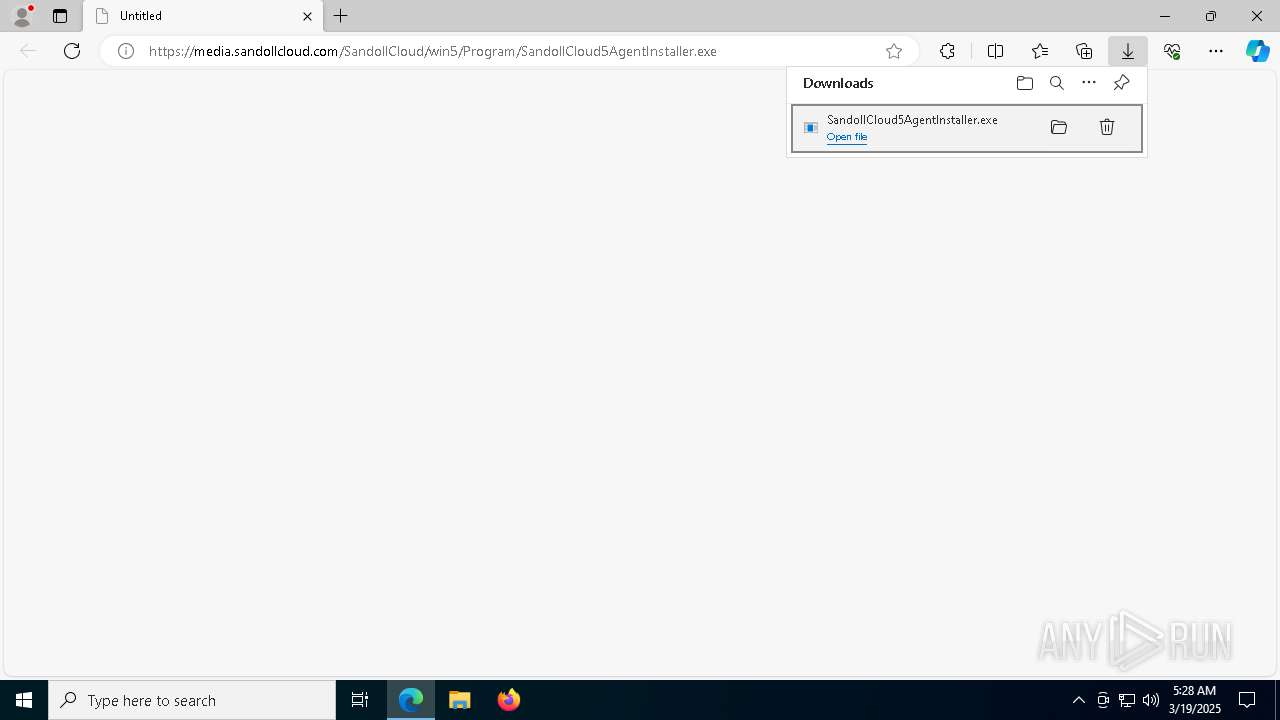
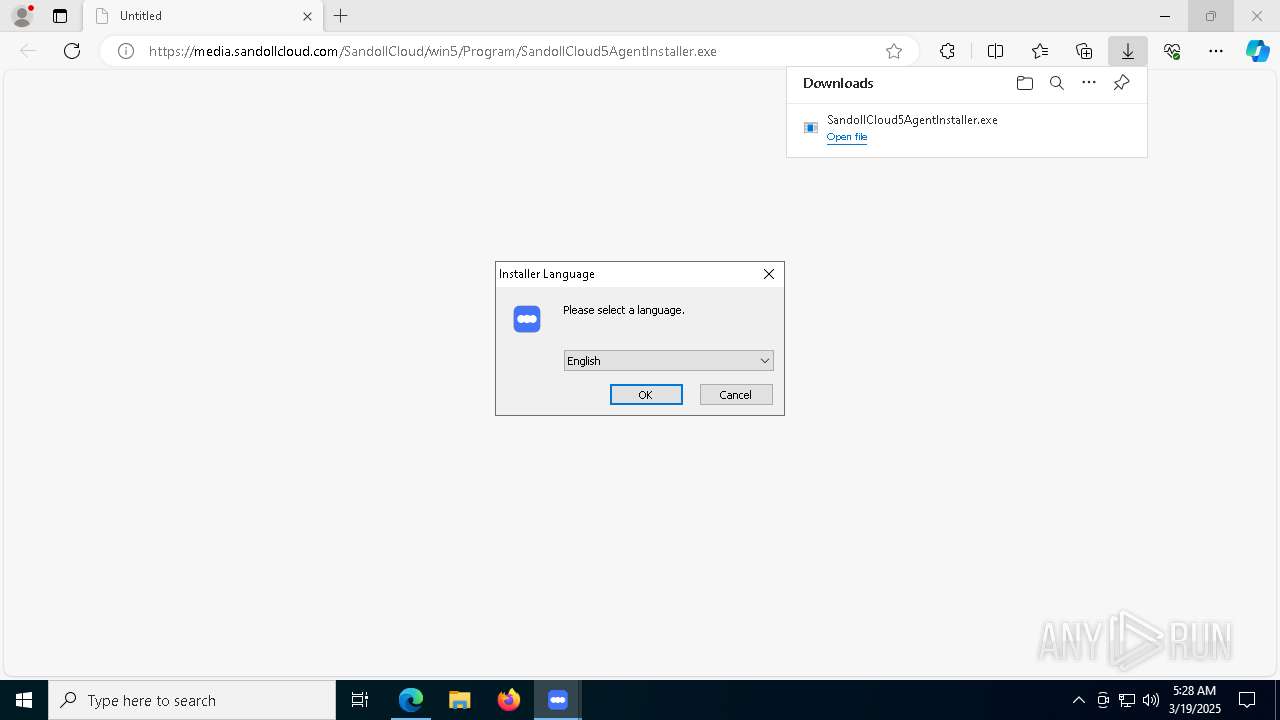
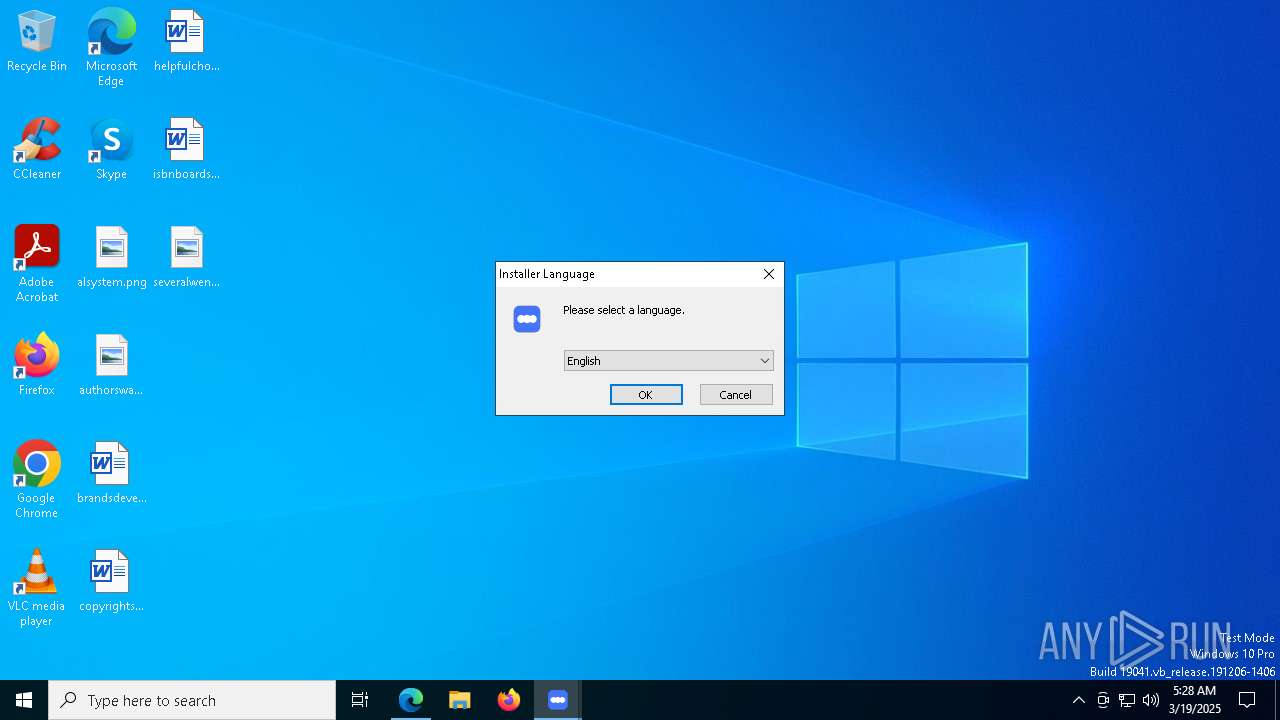
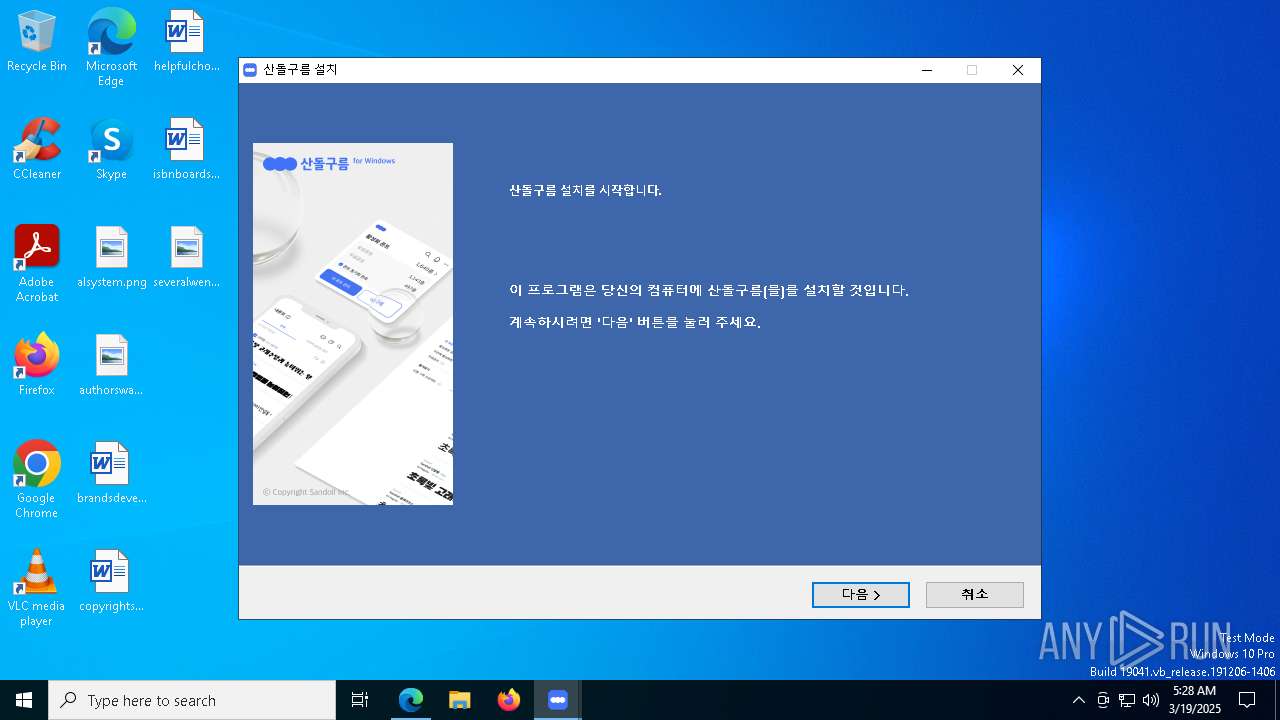
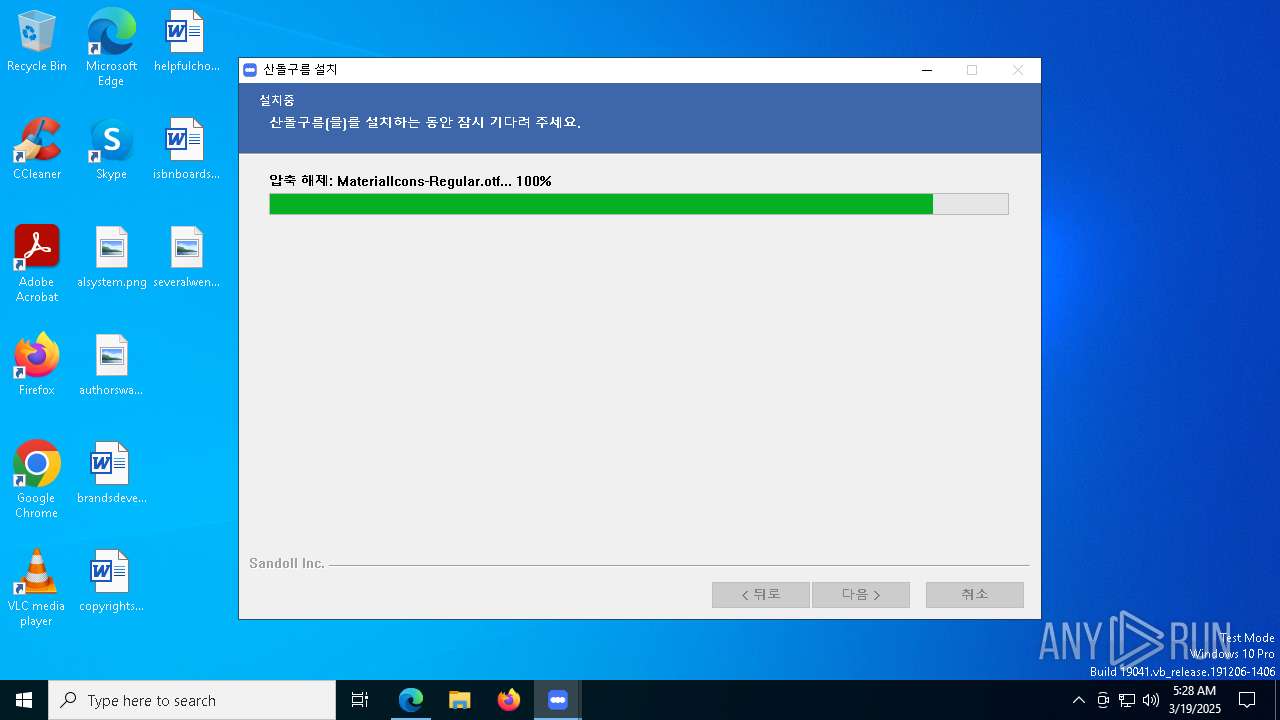
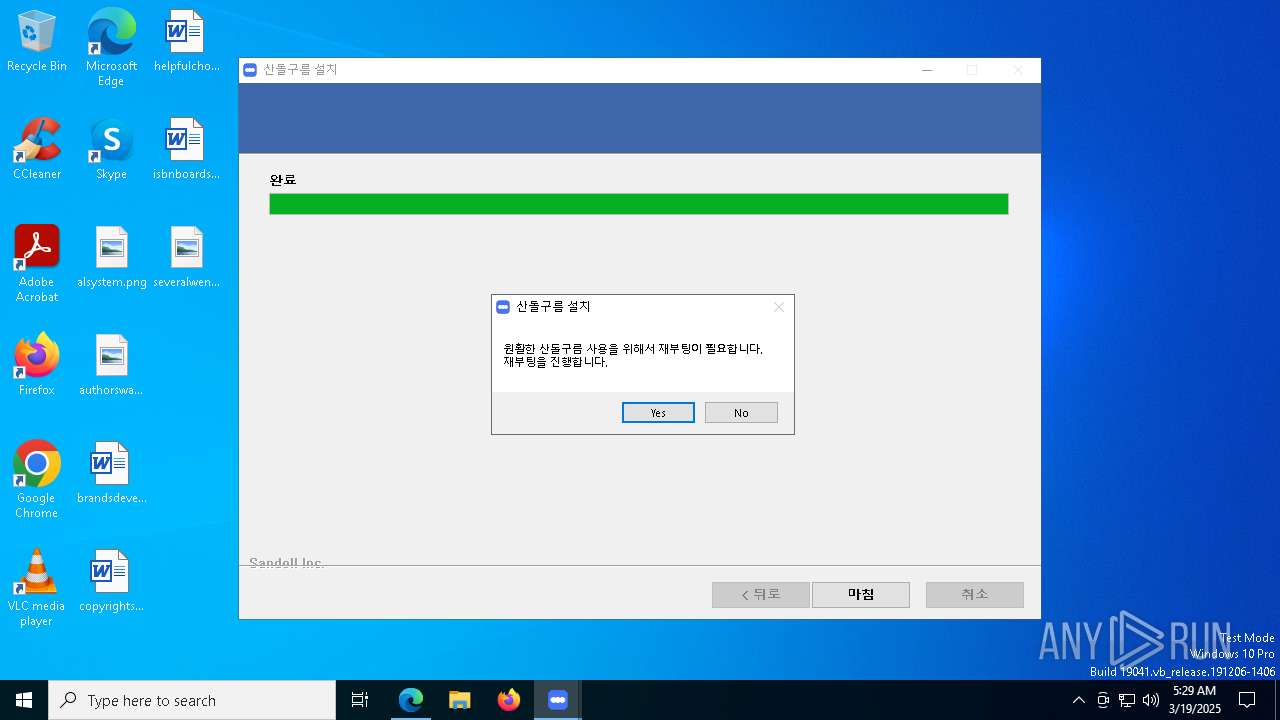
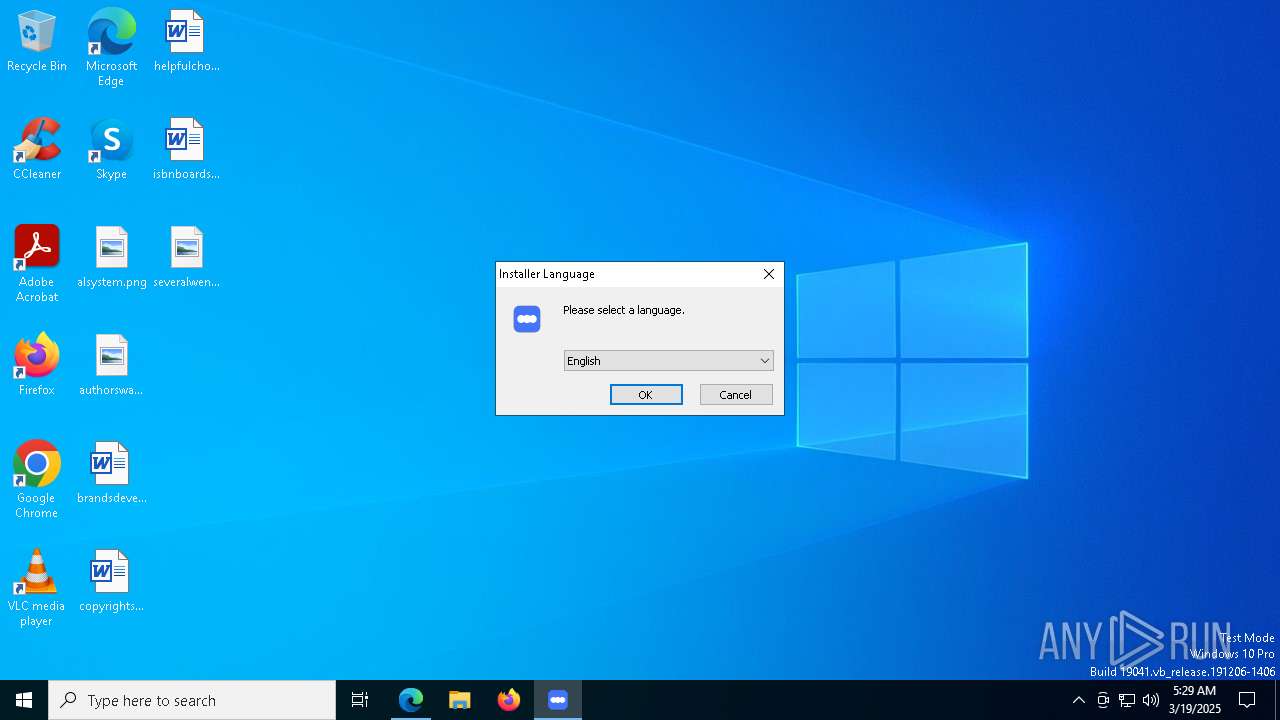
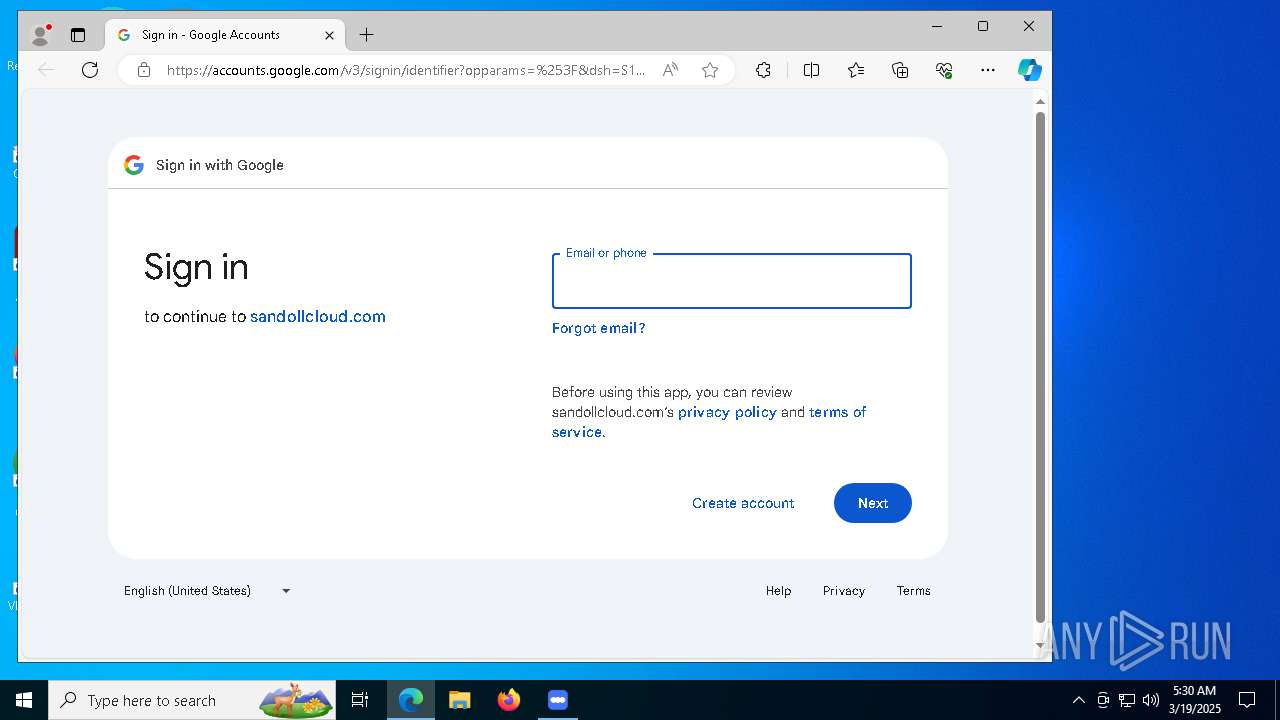
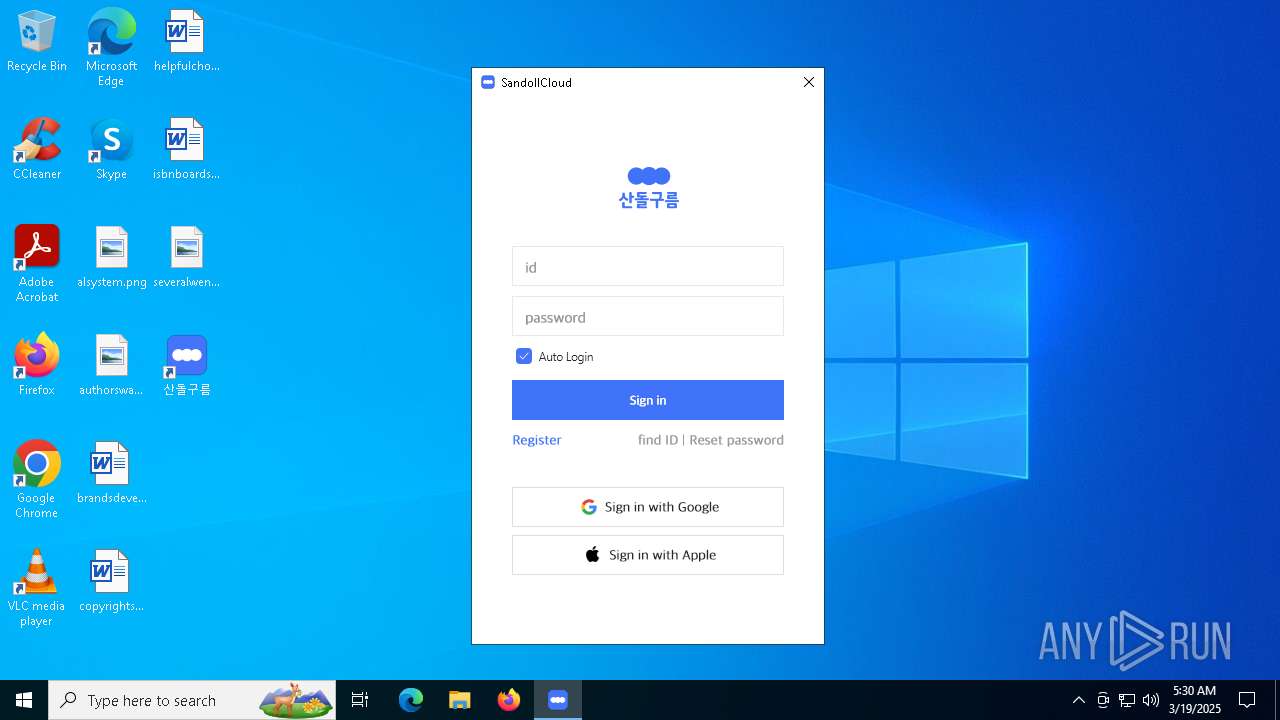
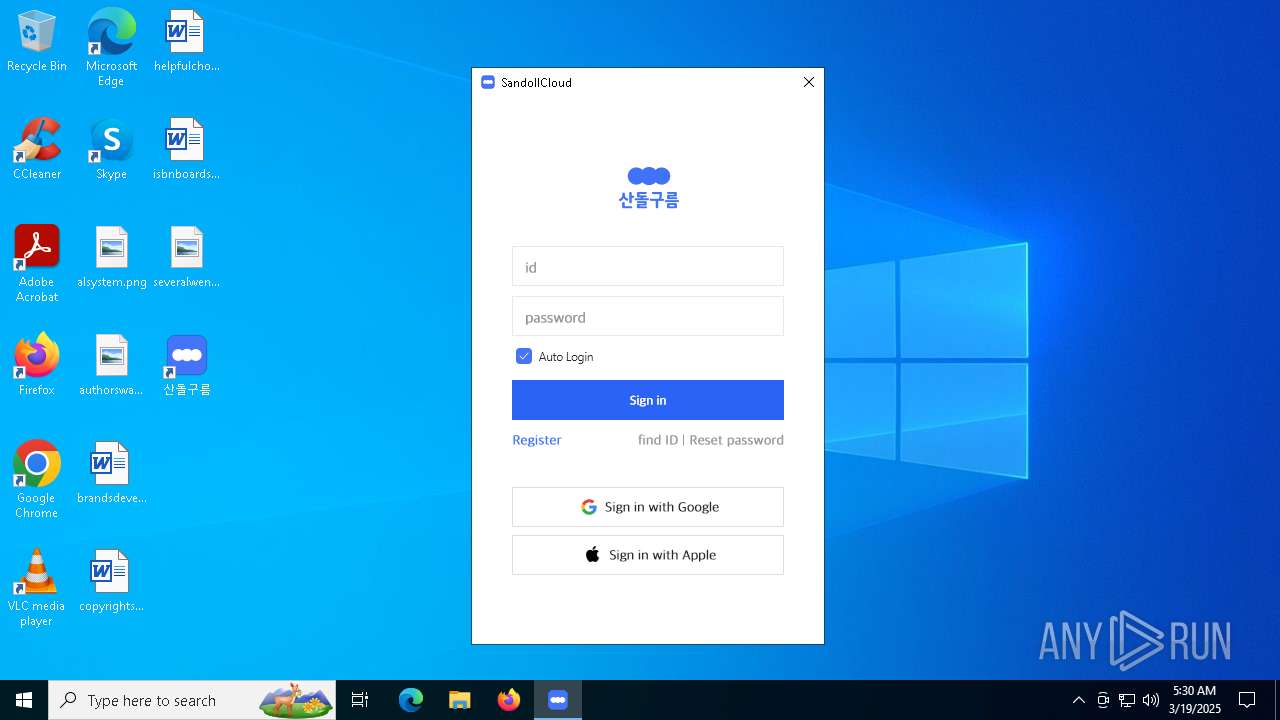
| URL: | https://media.sandollcloud.com/SandollCloud/win5/Program/SandollCloud5AgentInstaller.exe |
| Full analysis: | https://app.any.run/tasks/13948dd7-20fe-4c92-9e40-11efee16aed0 |
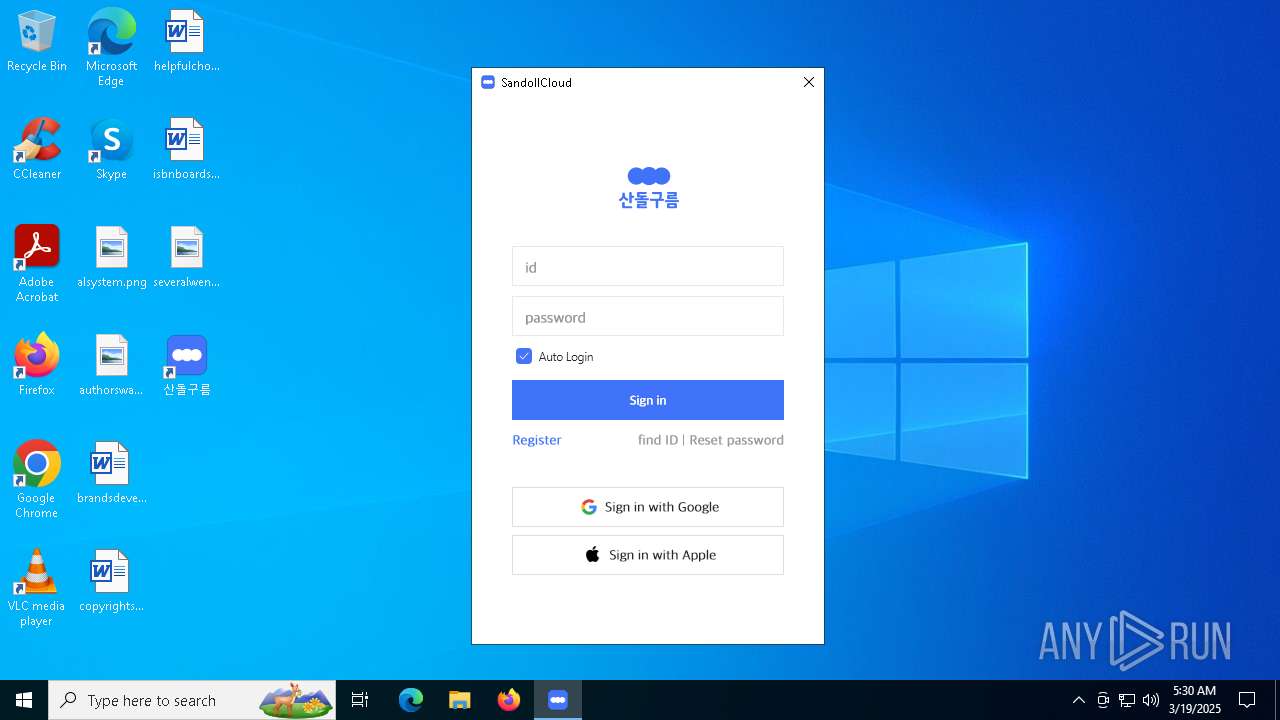
| Verdict: | Malicious activity |
| Analysis date: | March 19, 2025, 05:27:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 88E03810729C5EB96AEB227F4A27B880 |
| SHA1: | 734B0F321B5E6370D5709DF84A29414A86640C8E |
| SHA256: | 7F6B73DF453B818A770C7AE679F1BF2A2F9DB0983878104B7754AC6B2CF4D55A |
| SSDEEP: | 3:N8KiWitEUZGpJoxLnd3MJopA8XLNn:2K1QZGpUlMwnXLN |
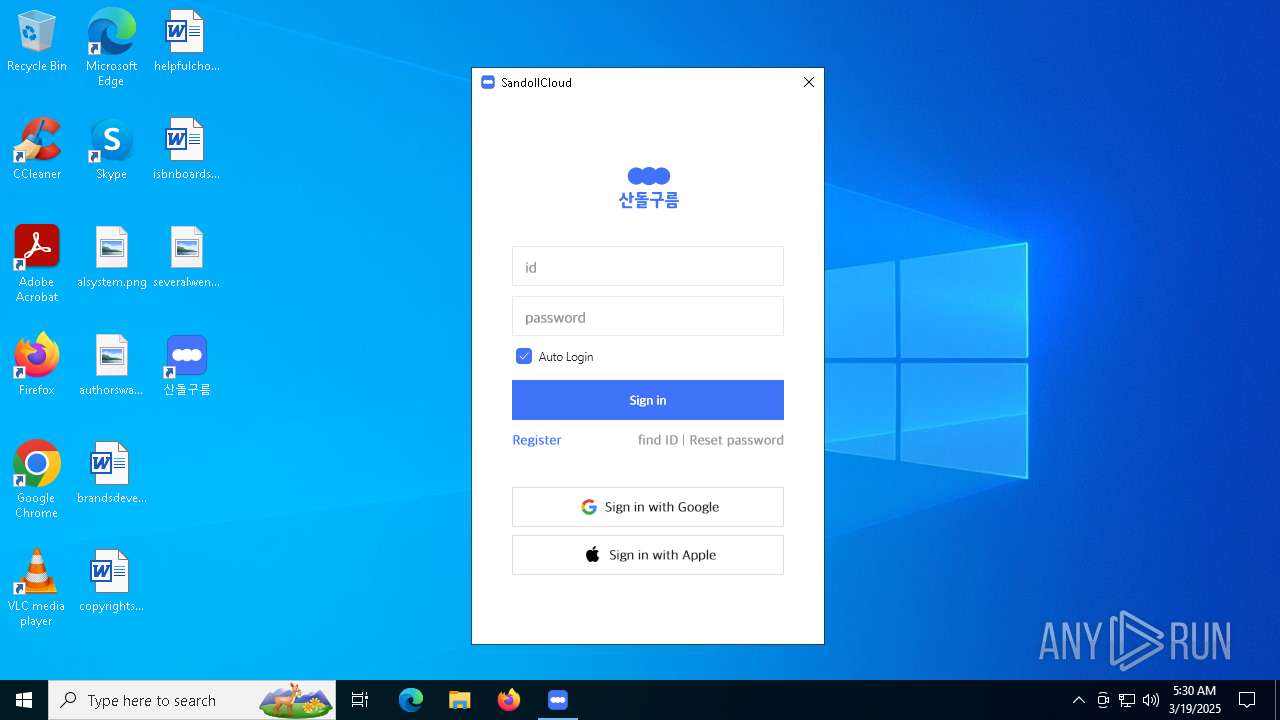
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x64.exe (PID: 516)
SUSPICIOUS
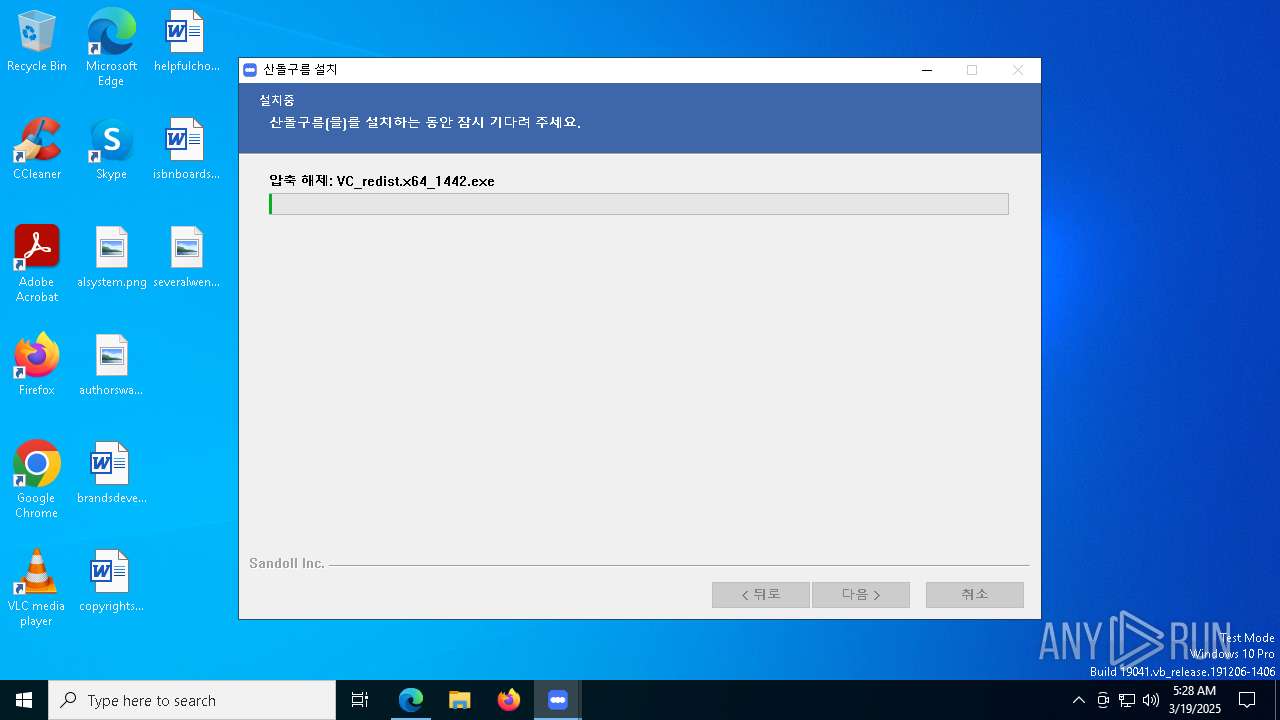
Executable content was dropped or overwritten
- SandollCloud5AgentInstaller.exe (PID: 6668)
- SandollCloud5AgentInstaller.exe (PID: 4400)
- VC_redist.x64_1442.exe (PID: 8104)
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7648)
- VC_redist.x64.exe (PID: 7532)
There is functionality for taking screenshot (YARA)
- SandollCloud5AgentInstaller.exe (PID: 6668)
- SandollCloud5AgentInstaller.exe (PID: 4400)
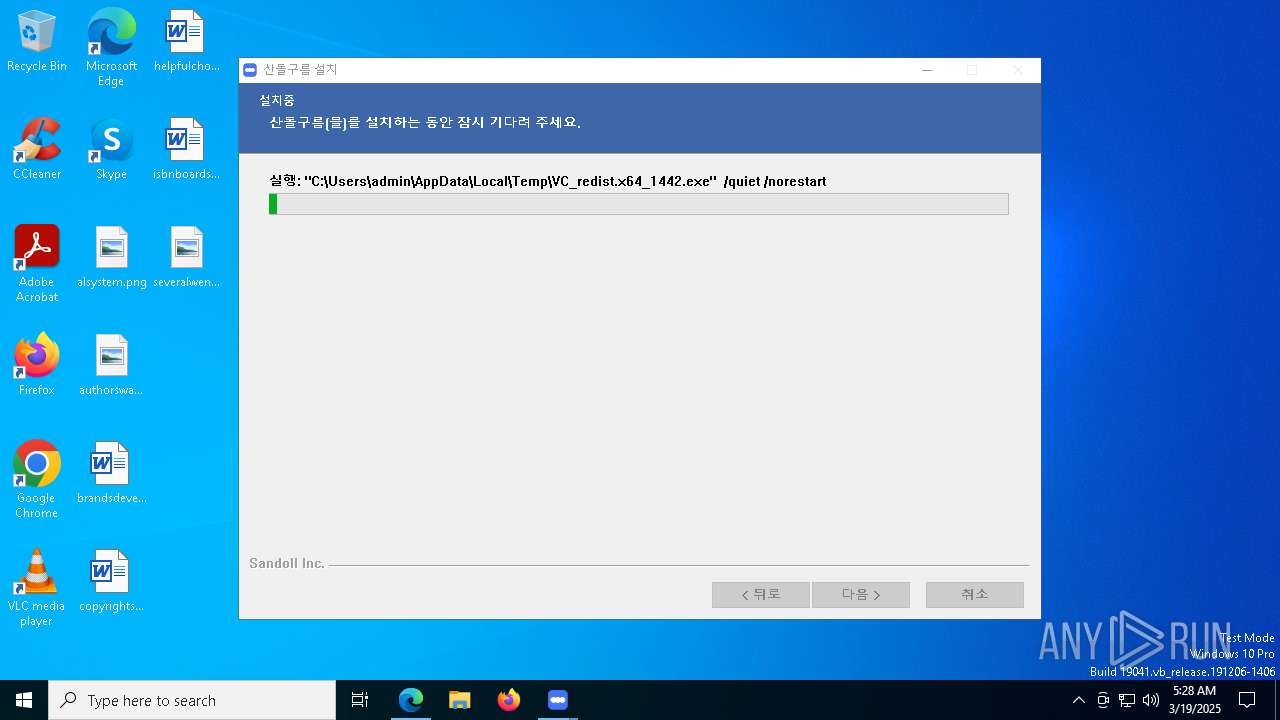
Starts a Microsoft application from unusual location
- VC_redist.x64_1442.exe (PID: 8104)
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 516)
Process drops legitimate windows executable
- SandollCloud5AgentInstaller.exe (PID: 4400)
- VC_redist.x64_1442.exe (PID: 8104)
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 516)
- msiexec.exe (PID: 8184)
- VC_redist.x64.exe (PID: 7532)
Reads security settings of Internet Explorer
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 7648)
- SandollCloud.exe (PID: 6672)
Searches for installed software
- VC_redist.x64_1442.exe (PID: 4488)
- dllhost.exe (PID: 6592)
- VC_redist.x64.exe (PID: 7648)
- VC_redist.x64.exe (PID: 7532)
Executes as Windows Service
- VSSVC.exe (PID: 6324)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8184)
The process drops C-runtime libraries
- msiexec.exe (PID: 8184)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 8184)
- SandollCloud.exe (PID: 6672)
Application launched itself
- VC_redist.x64.exe (PID: 4212)
- VC_redist.x64.exe (PID: 7648)
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 516)
- SandollCloud5AgentInstaller.exe (PID: 4400)
The process creates files with name similar to system file names
- SandollCloud5AgentInstaller.exe (PID: 4400)
Malware-specific behavior (creating "System.dll" in Temp)
- SandollCloud5AgentInstaller.exe (PID: 4400)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4124)
Reads the date of Windows installation
- SandollCloud.exe (PID: 6672)
Starts itself from another location
- VC_redist.x64_1442.exe (PID: 4488)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 4380)
- msiexec.exe (PID: 8184)
Reads the computer name
- identity_helper.exe (PID: 1188)
- SandollCloud5AgentInstaller.exe (PID: 6668)
- SandollCloud5AgentInstaller.exe (PID: 4400)
- VC_redist.x64_1442.exe (PID: 8104)
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 516)
- msiexec.exe (PID: 8184)
- VC_redist.x64.exe (PID: 7648)
- VC_redist.x64.exe (PID: 7532)
- PLUGScheduler.exe (PID: 4124)
- SandollCloud.exe (PID: 6672)
- SandollWinService.exe (PID: 6864)
- identity_helper.exe (PID: 2964)
- identity_helper.exe (PID: 2352)
- identity_helper.exe (PID: 7560)
- identity_helper.exe (PID: 3968)
Checks supported languages
- identity_helper.exe (PID: 1188)
- SandollCloud5AgentInstaller.exe (PID: 6668)
- SandollCloud5AgentInstaller.exe (PID: 4400)
- VC_redist.x64_1442.exe (PID: 8104)
- VC_redist.x64_1442.exe (PID: 4488)
- msiexec.exe (PID: 8184)
- VC_redist.x64.exe (PID: 4212)
- VC_redist.x64.exe (PID: 7648)
- VC_redist.x64.exe (PID: 7532)
- PLUGScheduler.exe (PID: 4124)
- identity_helper.exe (PID: 7560)
- identity_helper.exe (PID: 2352)
- SandollWinService.exe (PID: 6864)
- SandollCloud.exe (PID: 6672)
- identity_helper.exe (PID: 2964)
- identity_helper.exe (PID: 3968)
- VC_redist.x64.exe (PID: 516)
Application launched itself
- msedge.exe (PID: 4380)
- msedge.exe (PID: 7908)
- msedge.exe (PID: 6164)
- msedge.exe (PID: 7680)
- msedge.exe (PID: 7712)
Reads Environment values
- identity_helper.exe (PID: 1188)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1012)
- msiexec.exe (PID: 8184)
- SandollCloud5AgentInstaller.exe (PID: 4400)
- SandollCloud.exe (PID: 6672)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1012)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1012)
- msiexec.exe (PID: 8184)
- slui.exe (PID: 5416)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 3096)
- BackgroundTransferHost.exe (PID: 1128)
- BackgroundTransferHost.exe (PID: 2504)
- BackgroundTransferHost.exe (PID: 1012)
- BackgroundTransferHost.exe (PID: 7988)
Create files in a temporary directory
- SandollCloud5AgentInstaller.exe (PID: 6668)
- SandollCloud5AgentInstaller.exe (PID: 4400)
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7648)
The sample compiled with english language support
- SandollCloud5AgentInstaller.exe (PID: 4400)
- VC_redist.x64_1442.exe (PID: 8104)
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 516)
- msiexec.exe (PID: 8184)
- VC_redist.x64.exe (PID: 7648)
- VC_redist.x64.exe (PID: 7532)
Process checks computer location settings
- VC_redist.x64_1442.exe (PID: 4488)
- VC_redist.x64.exe (PID: 7648)
- SandollCloud.exe (PID: 6672)
Manages system restore points
- SrTasks.exe (PID: 7936)
Autorun file from Registry key
- VC_redist.x64.exe (PID: 516)
Reads the machine GUID from the registry
- VC_redist.x64.exe (PID: 516)
- msiexec.exe (PID: 8184)
Creates files in the program directory
- VC_redist.x64.exe (PID: 516)
- SandollCloud5AgentInstaller.exe (PID: 4400)
- PLUGScheduler.exe (PID: 4124)
Creates a software uninstall entry
- msiexec.exe (PID: 8184)
The sample compiled with korean language support
- SandollCloud5AgentInstaller.exe (PID: 4400)
Manual execution by a user
- SandollCloud.exe (PID: 6672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
451
Monitored processes
157
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5104 --field-trial-handle=2408,i,18024442960041385533,8199828393395817283,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Users\admin\Downloads\SandollCloud5AgentInstaller.exe" | C:\Users\admin\Downloads\SandollCloud5AgentInstaller.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 516 | "C:\WINDOWS\Temp\{E3287026-36F4-442D-ACF5-80C136109493}\.be\VC_redist.x64.exe" -q -burn.elevated BurnPipe.{32F0F1CC-2AC5-435B-8685-7CE4D5754B17} {410EB5BC-6F3E-47E1-B314-6DD521A6AF2A} 4488 | C:\Windows\Temp\{E3287026-36F4-442D-ACF5-80C136109493}\.be\VC_redist.x64.exe | VC_redist.x64_1442.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.42.34438 Exit code: 3010 Version: 14.42.34438.0 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6808 --field-trial-handle=1852,i,4718190832556458686,17174584466616685831,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x2f8,0x7ffc88825fd8,0x7ffc88825fe4,0x7ffc88825ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5468 --field-trial-handle=2348,i,11844744613881805254,15240567913261600076,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6344 --field-trial-handle=1852,i,4718190832556458686,17174584466616685831,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2380 --field-trial-handle=2384,i,13252034565252182774,16600196213241643972,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
37 797
Read events
36 698
Write events
721
Delete events
378
Modification events
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 68B40391418F2F00 | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 67560B91418F2F00 | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197390 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {234A67C5-9167-4A26-BDBC-130B07CF33FA} | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197390 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {909FBB09-897D-4279-AA2B-085FA62337F6} | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 68D94F91418F2F00 | |||
| (PID) Process: | (4380) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197390 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7CE2890A-9B7B-477E-830F-AC1301215652} | |||
Executable files
125
Suspicious files
806
Text files
264
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc2e.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc2e.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc2e.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 4380 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
217
DNS requests
224
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1012 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1324 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8184 | msiexec.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8184 | msiexec.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
1324 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6184 | svchost.exe | HEAD | 200 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742375757&P2=404&P3=2&P4=YeNN6hdFU793RFEDEhYF8Ytg%2fXPg6x%2bz%2f7SDAILI20TgHYoDrpjVYmRBDMjJRMZYovC2XkuZcTaR1SaF0dXUmw%3d%3d | unknown | — | — | whitelisted |
5276 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7284 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4380 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7284 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7284 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7284 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7284 | msedge.exe | 23.48.23.26:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
media.sandollcloud.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7928 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7928 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|