| download: | EternalBlues.exe |
| Full analysis: | https://app.any.run/tasks/37ebcd51-ac2b-4cf7-818e-d72eb13b2dfe |
| Verdict: | Suspicious activity |
| Analysis date: | June 24, 2020, 14:59:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 981AAAC4782BB076AA737901910F2556 |
| SHA1: | A552A4DAC03B584CBB7D461FD48B01DDAA85AF5D |
| SHA256: | 7F5F447FE870449A8245E7ABC19B9F4071095E02813D5F42C622ADD56DA15B8B |
| SSDEEP: | 12288:96fny4wDTzvE/XICULcJ48j406qbgg6RaAD9bSoGGHgm3Ihr6k:96fny4wbkHJ4I40vggPWSoGWv3c |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- EternalBlues.exe (PID: 2144)
Reads Internet Cache Settings
- EternalBlues.exe (PID: 2144)
Creates files in the user directory
- EternalBlues.exe (PID: 2144)
INFO
Reads settings of System Certificates
- EternalBlues.exe (PID: 2144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:26 04:42:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 859648 |
| InitializedDataSize: | 47616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd3ac6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
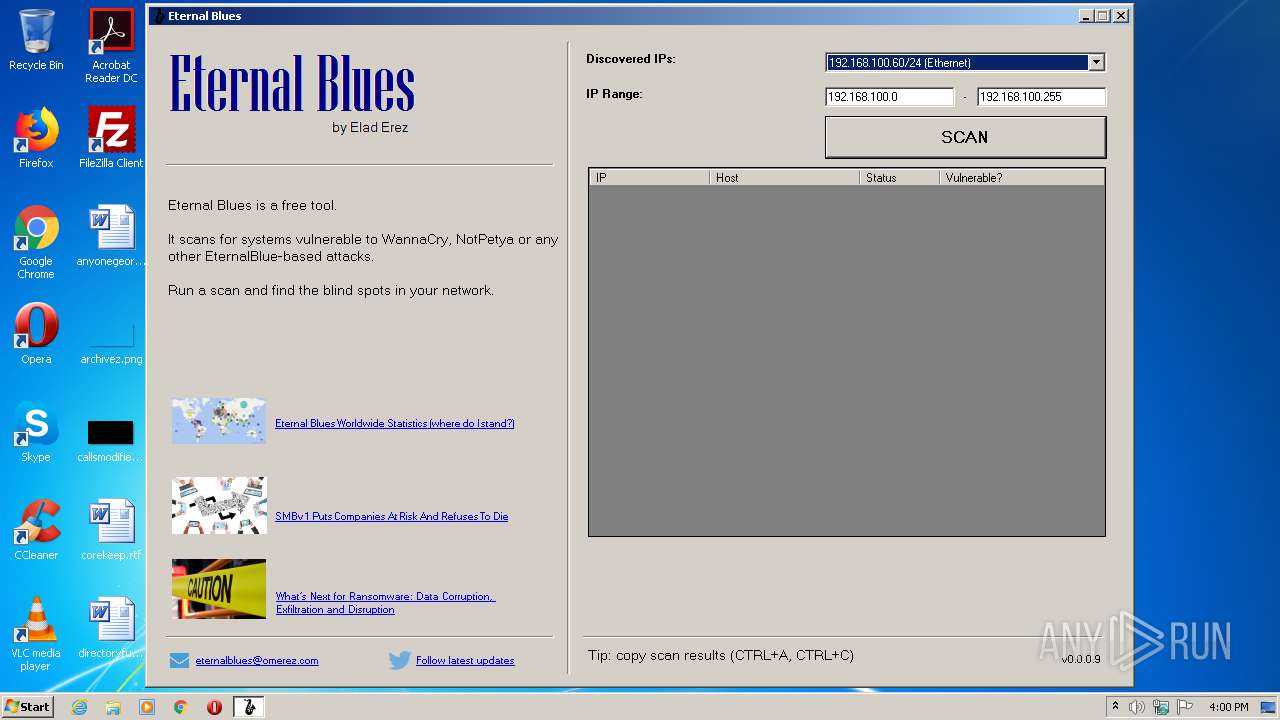
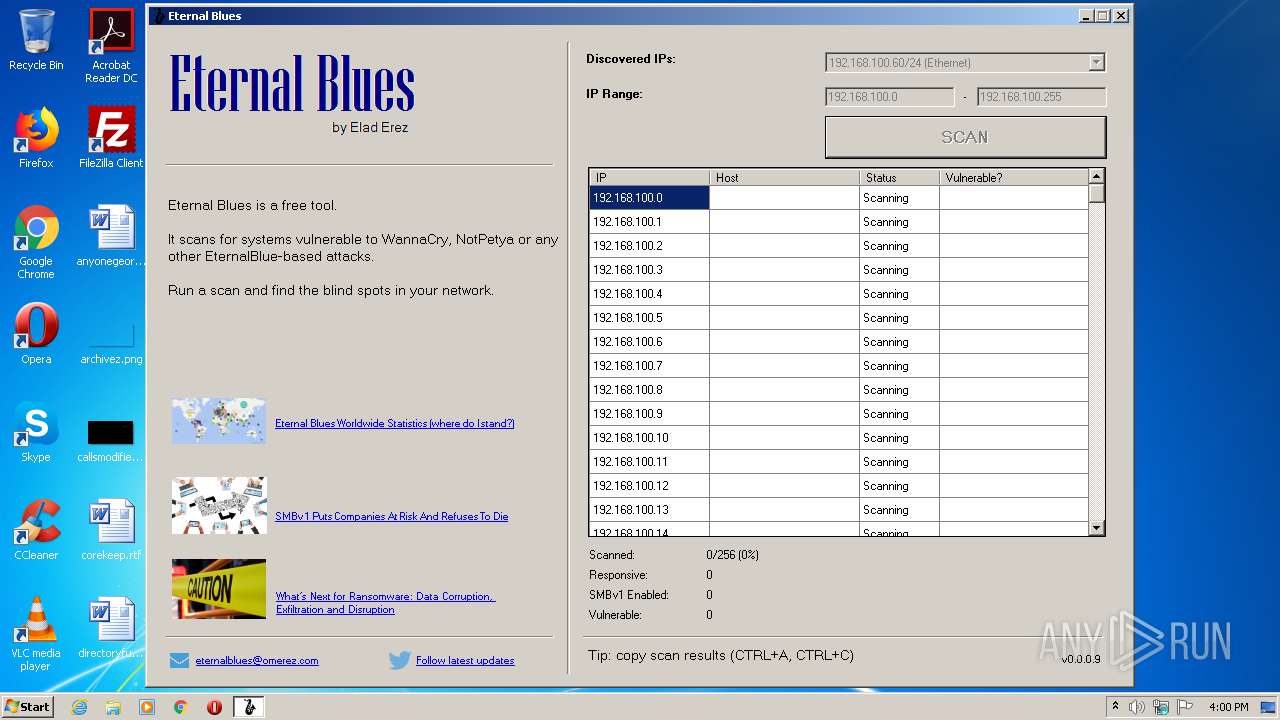
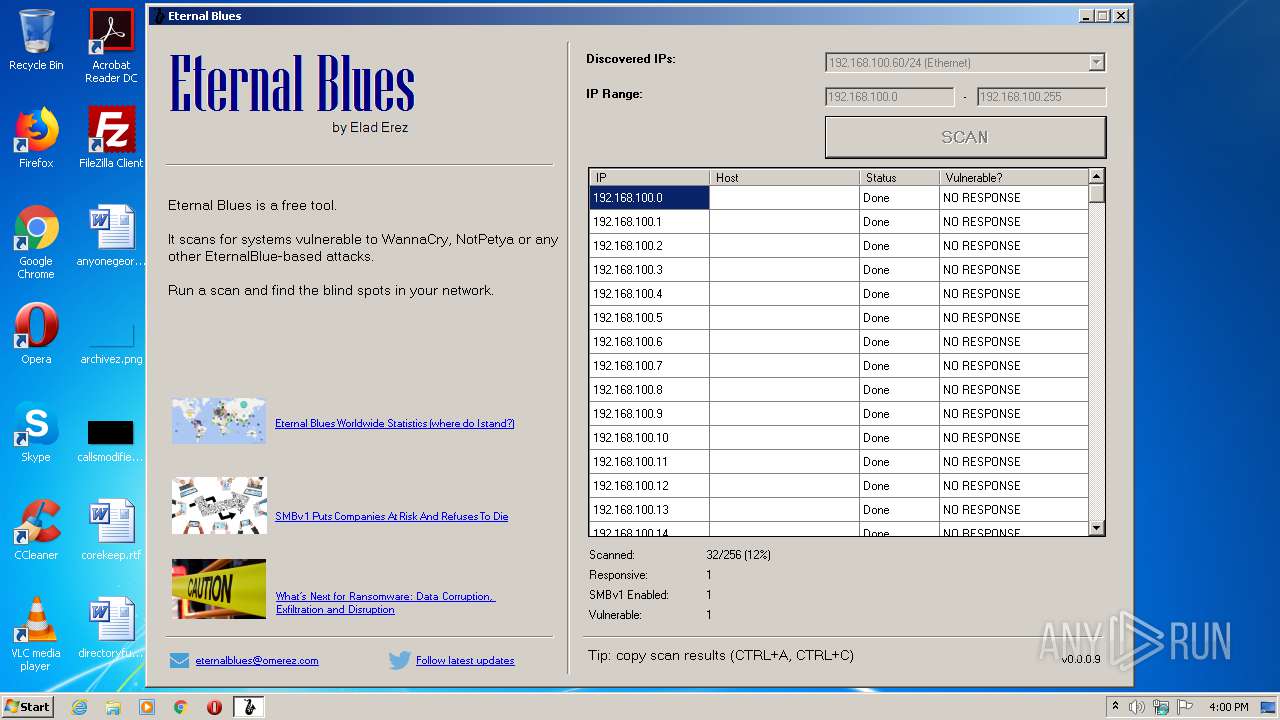
| FileVersionNumber: | 0.0.0.9 |
| ProductVersionNumber: | 0.0.0.9 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Elad Erez |
| FileDescription: | EternalBlues |
| FileVersion: | 0.0.0.9 |
| InternalName: | EternalBlues.exe |
| LegalCopyright: | Copyright © Elad Erez |
| LegalTrademarks: | - |
| OriginalFileName: | EternalBlues.exe |
| ProductName: | Eternal Blues |
| ProductVersion: | 0.0.0.9 |
| AssemblyVersion: | 0.0.0.9 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jul-2017 02:42:28 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | Elad Erez |
| FileDescription: | EternalBlues |
| FileVersion: | 0.0.0.9 |
| InternalName: | EternalBlues.exe |
| LegalCopyright: | Copyright © Elad Erez |
| LegalTrademarks: | - |
| OriginalFilename: | EternalBlues.exe |
| ProductName: | Eternal Blues |
| ProductVersion: | 0.0.0.9 |
| Assembly Version: | 0.0.0.9 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Jul-2017 02:42:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000D1C0C | 0x000D1E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.80315 |
.rsrc | 0x000D4000 | 0x0000B630 | 0x0000B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.95701 |
.reloc | 0x000E0000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Users\admin\AppData\Local\Temp\EternalBlues.exe" | C:\Users\admin\AppData\Local\Temp\EternalBlues.exe | explorer.exe | ||||||||||||
User: admin Company: Elad Erez Integrity Level: MEDIUM Description: EternalBlues Exit code: 0 Version: 0.0.0.9 Modules
| |||||||||||||||
Total events
185
Read events
149
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2144) EternalBlues.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EternalBlues_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
4
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\Local\Temp\CabE5C6.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\Local\Temp\TarE5C7.tmp | — | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\H9X3FL1B.txt | — | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\MY3SHU1X.txt | — | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CC197601BE0898B7B0FCC91FA15D8A69_D47F2BA53F1E3056E83DA06100B54E7B | der | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\FQWHTM4T.txt | text | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CC197601BE0898B7B0FCC91FA15D8A69_D47F2BA53F1E3056E83DA06100B54E7B | binary | |
MD5:— | SHA256:— | |||
| 2144 | EternalBlues.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\eternalblues-report[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2144 | EternalBlues.exe | GET | 200 | 182.50.132.48:80 | http://omerez.com/repository/pages/eternalblues-report.html?id=528478706&startScan=256&version=0.0.0.9 | SG | html | 520 b | suspicious |
2144 | EternalBlues.exe | GET | 200 | 182.50.132.48:80 | http://omerez.com/repository/eternalblues-version.txt | SG | text | 7 b | suspicious |
2144 | EternalBlues.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2144 | EternalBlues.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEH37YvsUovAmAgAAAABrIG0%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2144 | EternalBlues.exe | 182.50.132.48:80 | omerez.com | GoDaddy.com, LLC | SG | suspicious |
2144 | EternalBlues.exe | 172.217.23.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2144 | EternalBlues.exe | 216.58.210.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
omerez.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
1 ETPRO signatures available at the full report