| URL: | https://www.rocknet.com |
| Full analysis: | https://app.any.run/tasks/a7fc50a4-5835-41c1-91bb-d7ff24ce074d |
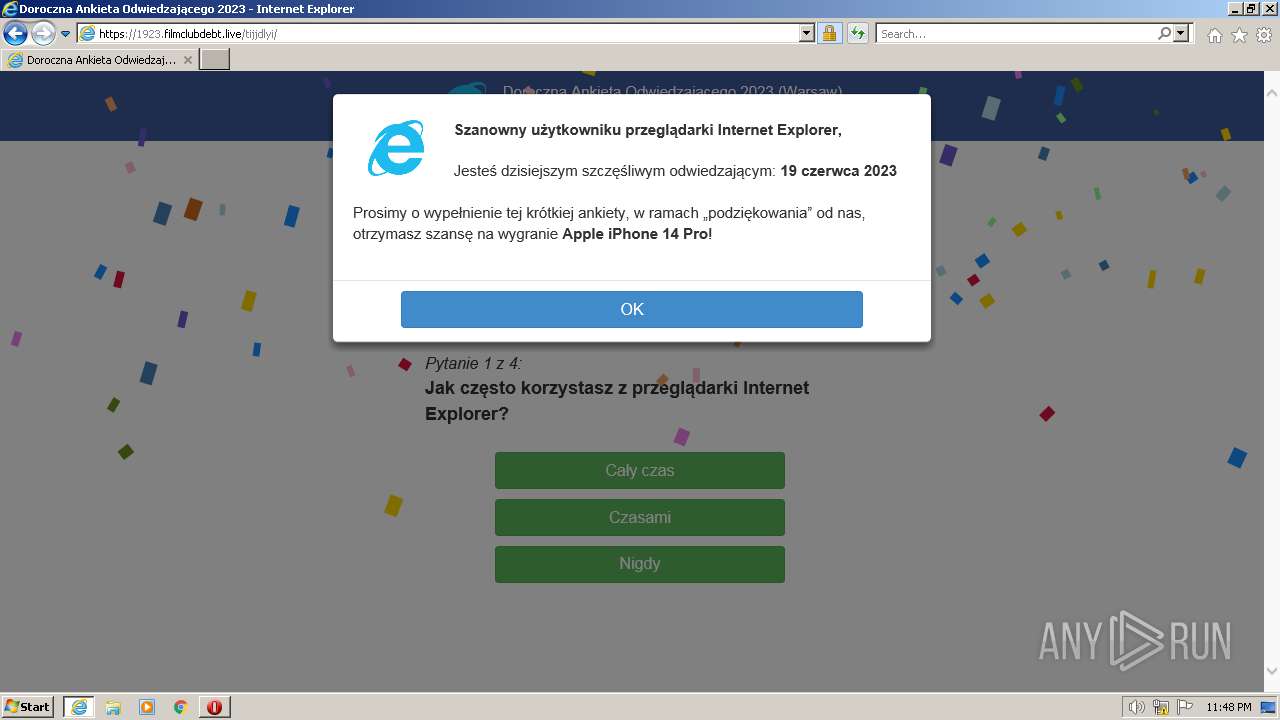
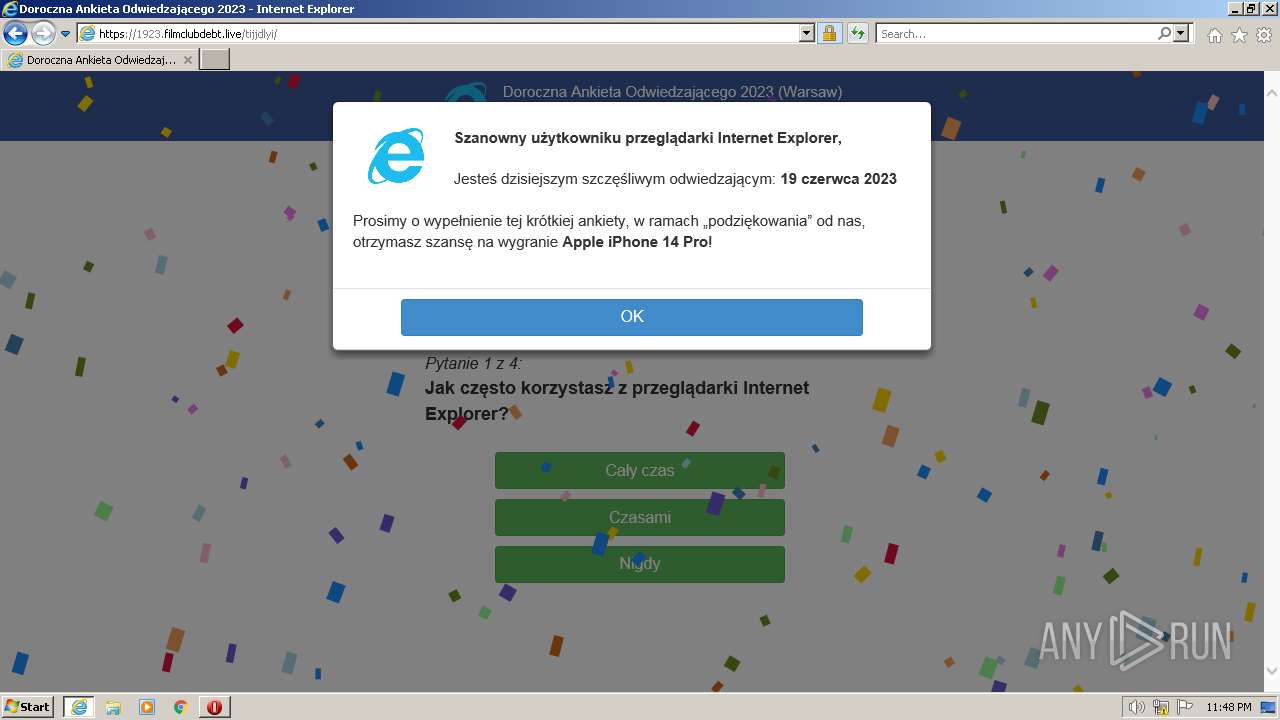
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2023, 22:47:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 52D827D560E9A1B1D806A366CB238429 |
| SHA1: | A59CE1C2D7C73523E1FF5A37D7928F9B04DF3348 |
| SHA256: | 7F5349225200FE38F15944E7F98E3A14B063B44504F8D89C8950700EE5D4AE9B |
| SSDEEP: | 3:N8DSLaG6Tn:2OLaG6Tn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2524 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.rocknet.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2524 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
17 845
Read events
17 553
Write events
288
Delete events
4
Modification events
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
49
Text files
76
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bootstrap.min[1].css | text | |
MD5:EED22D79DA03A754316E13356749FDFD | SHA256:9695448E6108222EC72E5ECAC5A8E930AD76A2E8904914237C52EA857D9C3785 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style.min[1].css | text | |
MD5:47CDB0E81EA341AD27A1A0B0BA6B02D8 | SHA256:ACA566587618E75FA291A419C7C430BE02E03FC72F6105658C1BC8E7D59A65E4 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:09E7D9840110AC6ADCFFEF39848F784B | SHA256:76AB81E3F7024EB43DF7445F7F1D1CBC44E086C9CCF960D504DF047F01C5D475 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\HH64F3SD.htm | html | |
MD5:D854F4F14DCC9FCDCA4FD9CBD5AB00EC | SHA256:40B1846C73B43CFA64A91C47B42AC7ACE19CAA7B693B89F1CE75F9972C346526 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\template.min[1].css | text | |
MD5:5CE60088908E2C10627505AE759032C5 | SHA256:4660618A88D707B64D40EC3D359525ADF84C0D5750C0C0DD7E60B18ECC6B6644 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\mediaelementplayer-legacy.min[1].css | text | |
MD5:2B0DD7EECEA03B4BDEDB94BA622FDB03 | SHA256:B7908A015A567EC2363011DF2475368DBFF34360E9DA3FDFF50604D6395FB646 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\animate.min[1].css | text | |
MD5:66ABB9FA0C1A1124E707A68459E3E2A3 | SHA256:BB12D5816613C889ED6F31328230C60E1D007711F49D8E441458E8BF8ECDB4E4 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\290-layout[1].css | text | |
MD5:628BC1FEBEBF4A3E6CEECAAFAA25B526 | SHA256:ED8E4FECC6F5A5A8C738DE1809ABCA8554BF91996443F7EDD53479A6C9E7DEA2 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\print[1].css | text | |
MD5:F59A9DAC512B3967205A6B372504B49F | SHA256:D0DBC4AB9E7712C361D0FEB03A454CC079677849DA32E959D4BE3CEE6CFC84F3 | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
130
DNS requests
39
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2616 | iexplore.exe | GET | — | 95.101.54.114:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTF45uulfpH2Id%2F6XGuV5z57g%3D%3D | DE | — | — | shared |
2616 | iexplore.exe | GET | — | 184.24.77.77:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgOisGHP95EkipcUj%2BYLmMWAYg%3D%3D | US | — | — | shared |
2616 | iexplore.exe | GET | 200 | 67.27.158.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6cf9e2792163bd41 | US | compressed | 4.70 Kb | whitelisted |
2616 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c94711078477d7ef | US | compressed | 62.3 Kb | whitelisted |
2616 | iexplore.exe | GET | 200 | 184.24.77.77:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTF45uulfpH2Id%2F6XGuV5z57g%3D%3D | US | binary | 503 b | shared |
2616 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2616 | iexplore.exe | GET | 200 | 67.27.158.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9d6d31a1c30b261e | US | compressed | 62.3 Kb | whitelisted |
2524 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
2616 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2616 | iexplore.exe | GET | 200 | 184.24.77.77:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPIlLedMCoANj4BUchXbk%2B60A%3D%3D | US | binary | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2616 | iexplore.exe | 67.27.158.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | malicious |
2524 | iexplore.exe | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | malicious |
2616 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
568 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2616 | iexplore.exe | 192.0.76.3:443 | stats.wp.com | AUTOMATTIC | US | suspicious |
2616 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2616 | iexplore.exe | 188.114.96.3:443 | www.rocknet.com | CLOUDFLARENET | NL | malicious |
2524 | iexplore.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | suspicious |
2616 | iexplore.exe | 142.250.186.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.rocknet.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
code.jquery.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
toolkit.mobileautorepairmechanic.com |
| unknown |
www.staging.rocknet.com |
| unknown |
stats.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
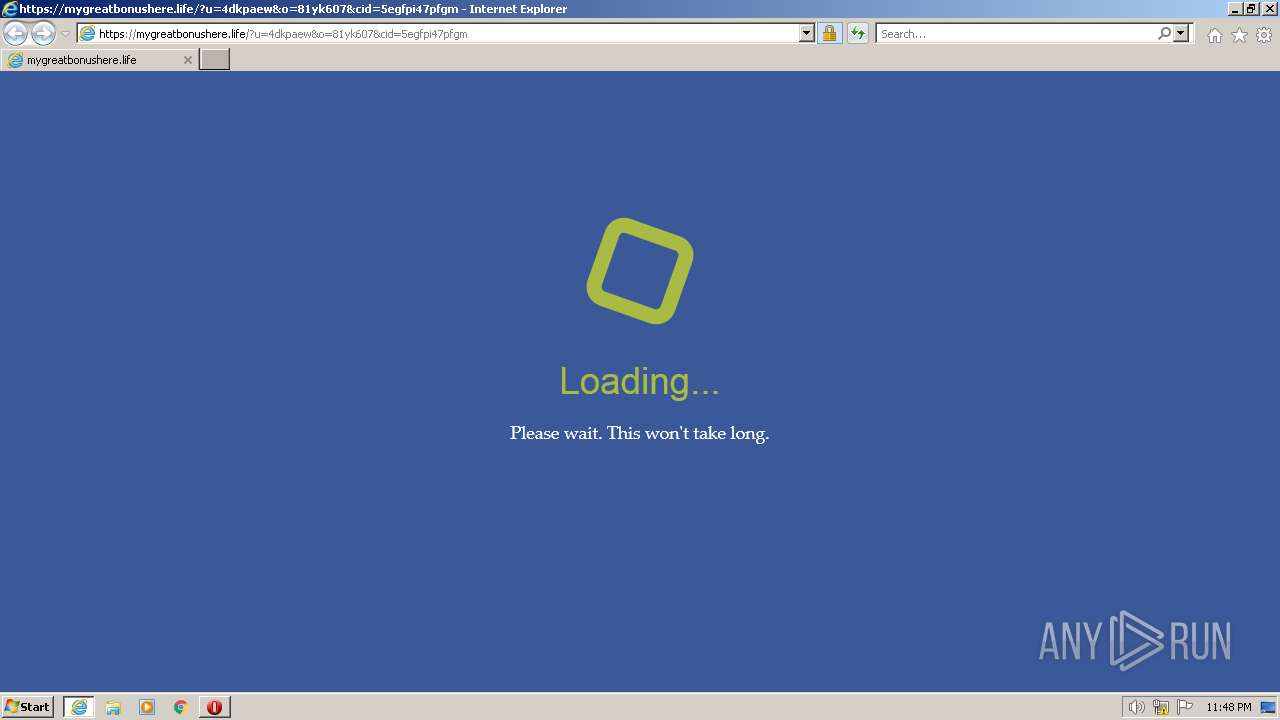
1076 | svchost.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (toolkit .mobileautorepairmechanic .com) |
1076 | svchost.exe | A Network Trojan was detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (jqscr .com) |
1076 | svchost.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (libertader .org) |
1076 | svchost.exe | access to a potentially vulnerable web application | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (getquery .org) |
1076 | svchost.exe | A Network Trojan was detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (jqueryns .com) |
1076 | svchost.exe | A Network Trojan was detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (jqueryh .org) |
1076 | svchost.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (dailytickyclock .org) |
1076 | svchost.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (lemonicecold .org) |
1076 | svchost.exe | A Network Trojan was detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (jsqur .com) |
1076 | svchost.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (neworderspath .org) |