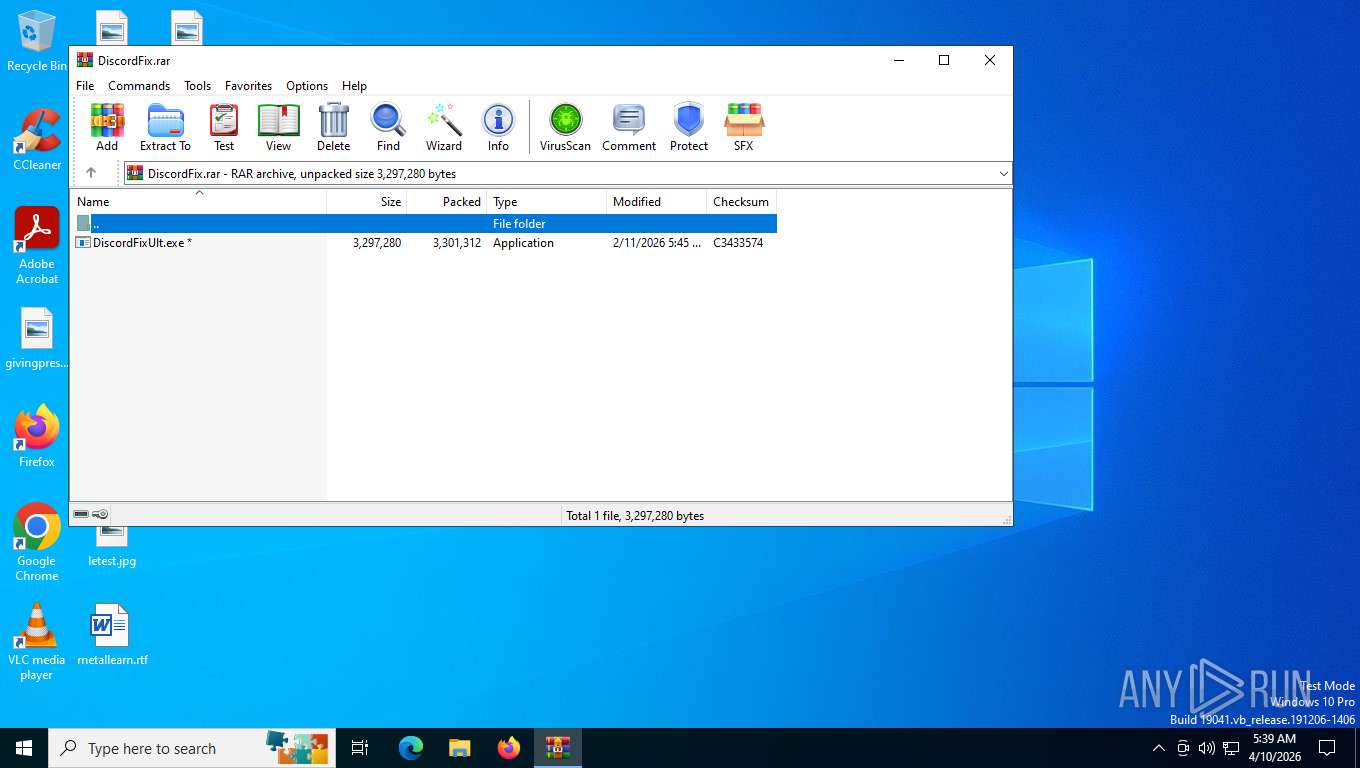
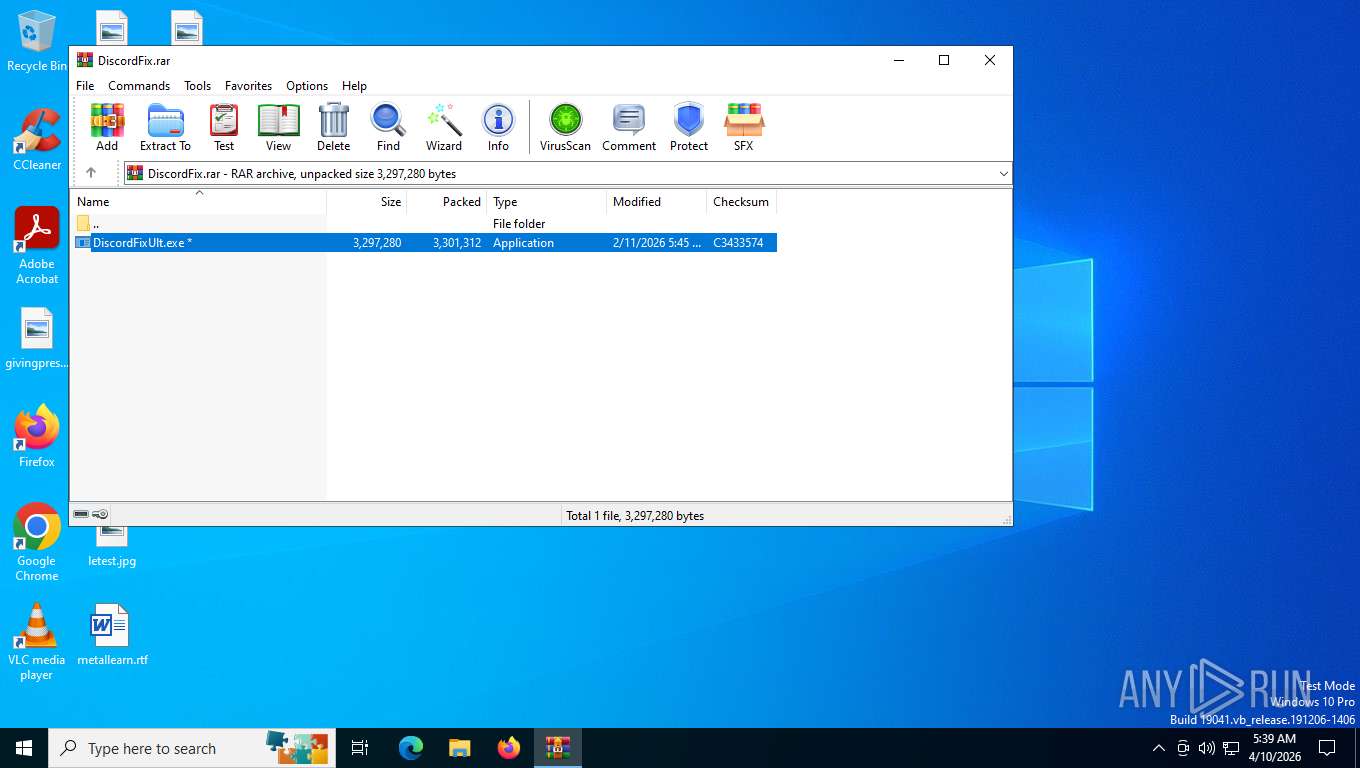
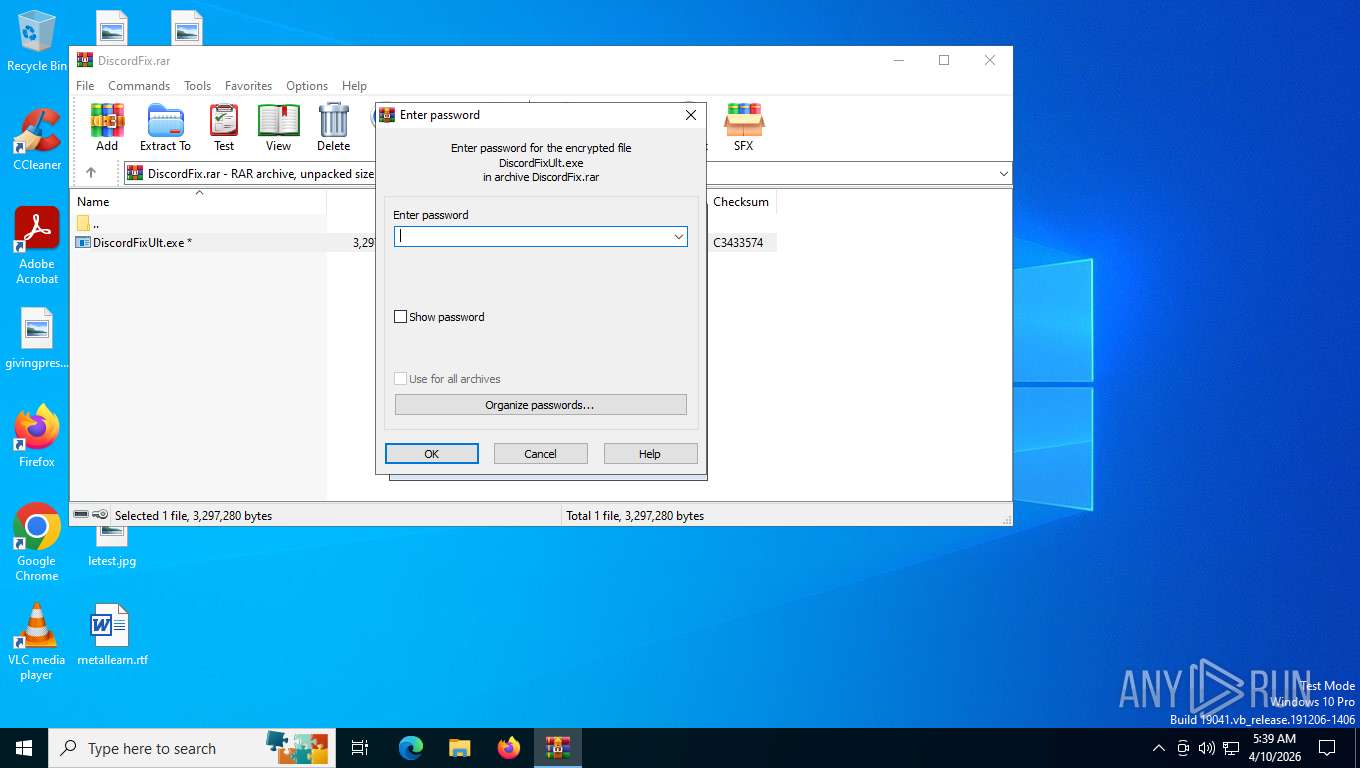
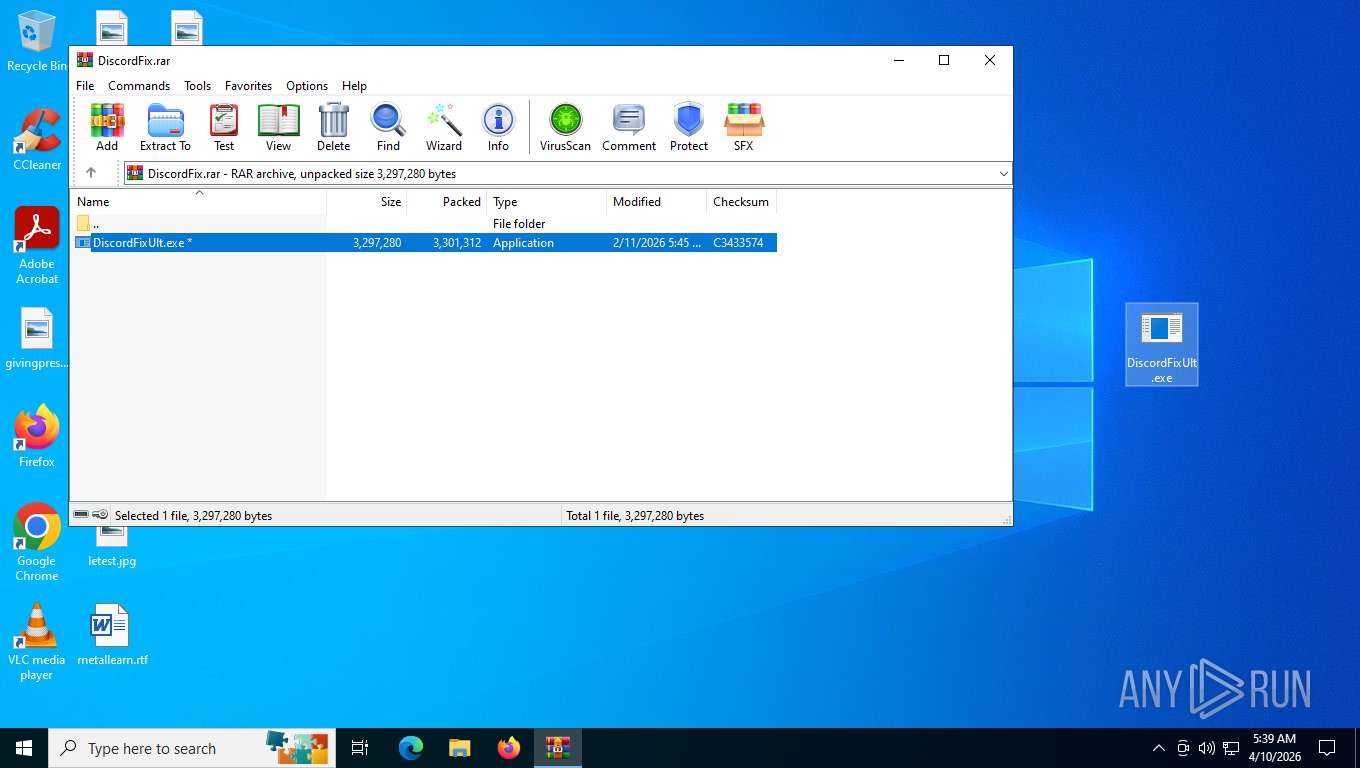
| File name: | DiscordFix.rar |
| Full analysis: | https://app.any.run/tasks/e6cf87a2-eb88-44c6-8212-c77025b79dfe |
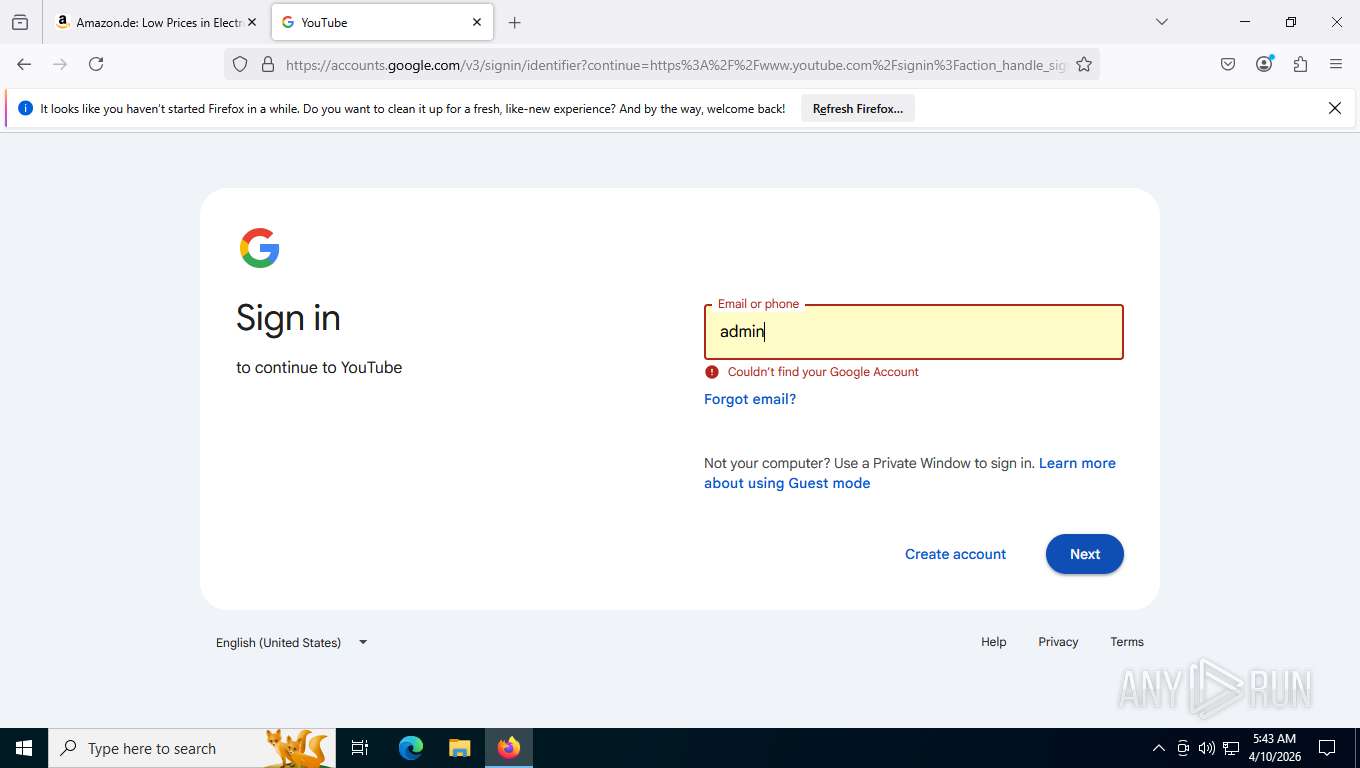
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 10, 2026, 09:39:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F090688A6DED0F4537E00D970D363F36 |
| SHA1: | 7857E58C993CFF8993D80D0C3F92E282C57D137D |
| SHA256: | 7F40F9A9C15AC1D3226DEECDE864596351579F6D5BD9D970BFA47187086C9AF6 |
| SSDEEP: | 98304:bAhUK7IcVtA9opDZyQY3lxKVzl18UltmZpMQkAetD+60/rChUv53rdjDz6W9hYhr:CWK5836 |
MALICIOUS
SALATSTEALER mutex has been found
- DiscordFixUlt.exe (PID: 6864)
SALATSTEALER has been detected (SURICATA)
- DiscordFixUlt.exe (PID: 6864)
SALATSTEALER has been detected (YARA)
- DiscordFixUlt.exe (PID: 6864)
SUSPICIOUS
Application launched itself
- DiscordFixUlt.exe (PID: 1164)
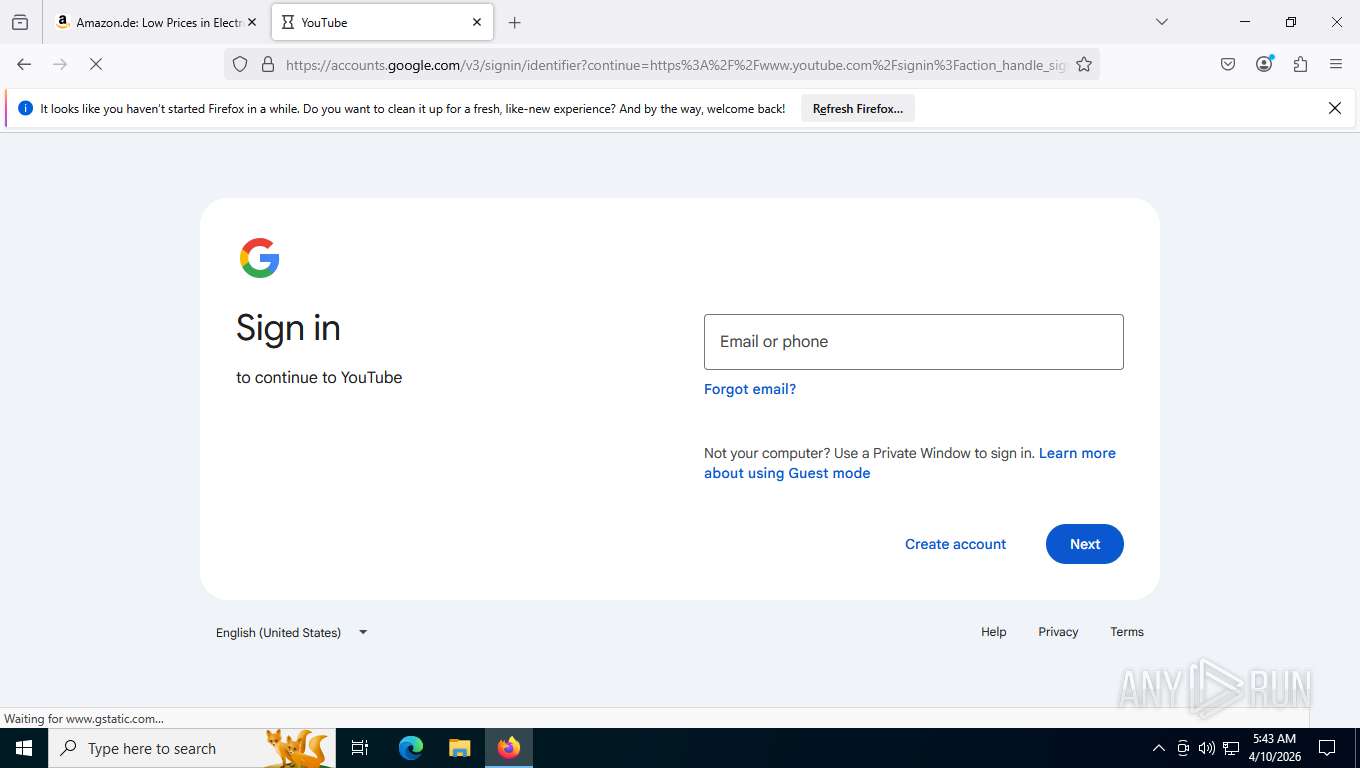
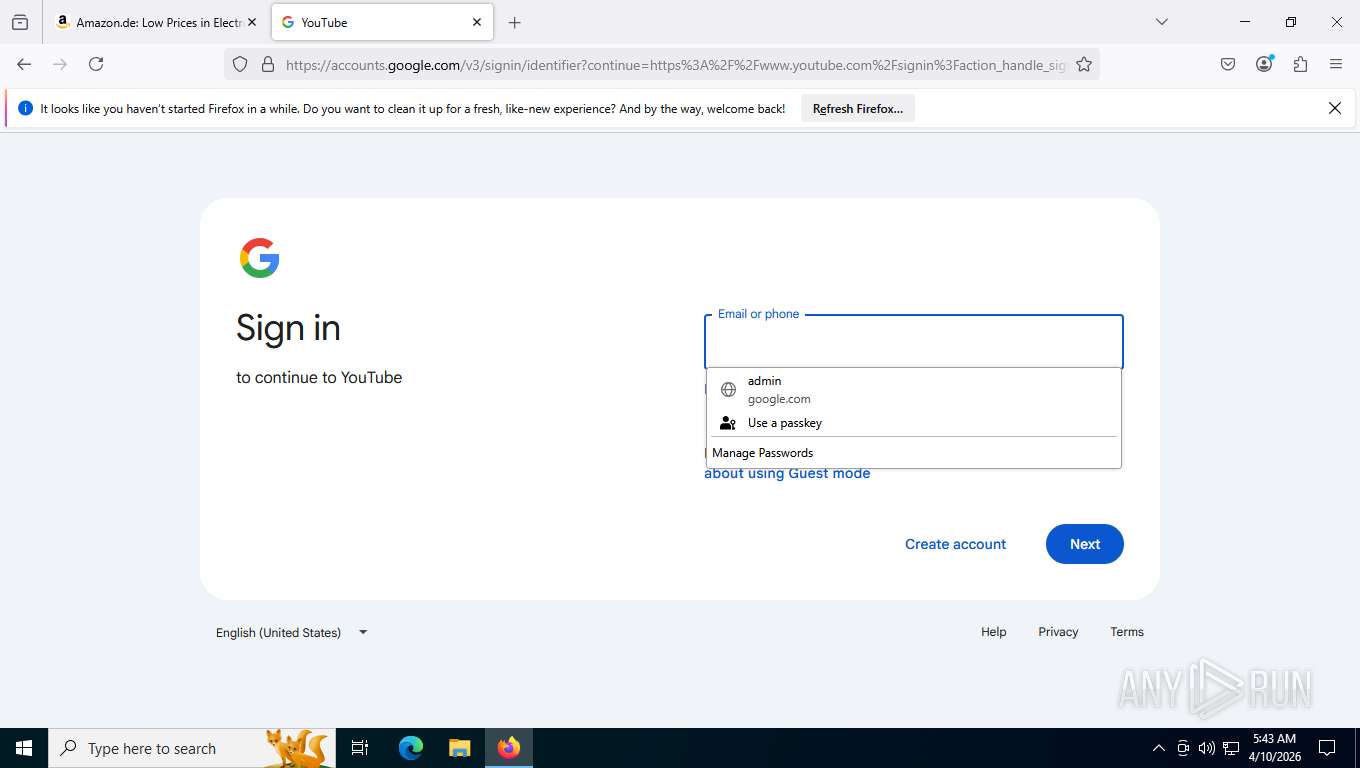
Multiple wallet extension IDs have been found
- DiscordFixUlt.exe (PID: 6864)
INFO
Checks supported languages
- DiscordFixUlt.exe (PID: 1164)
- DiscordFixUlt.exe (PID: 6864)
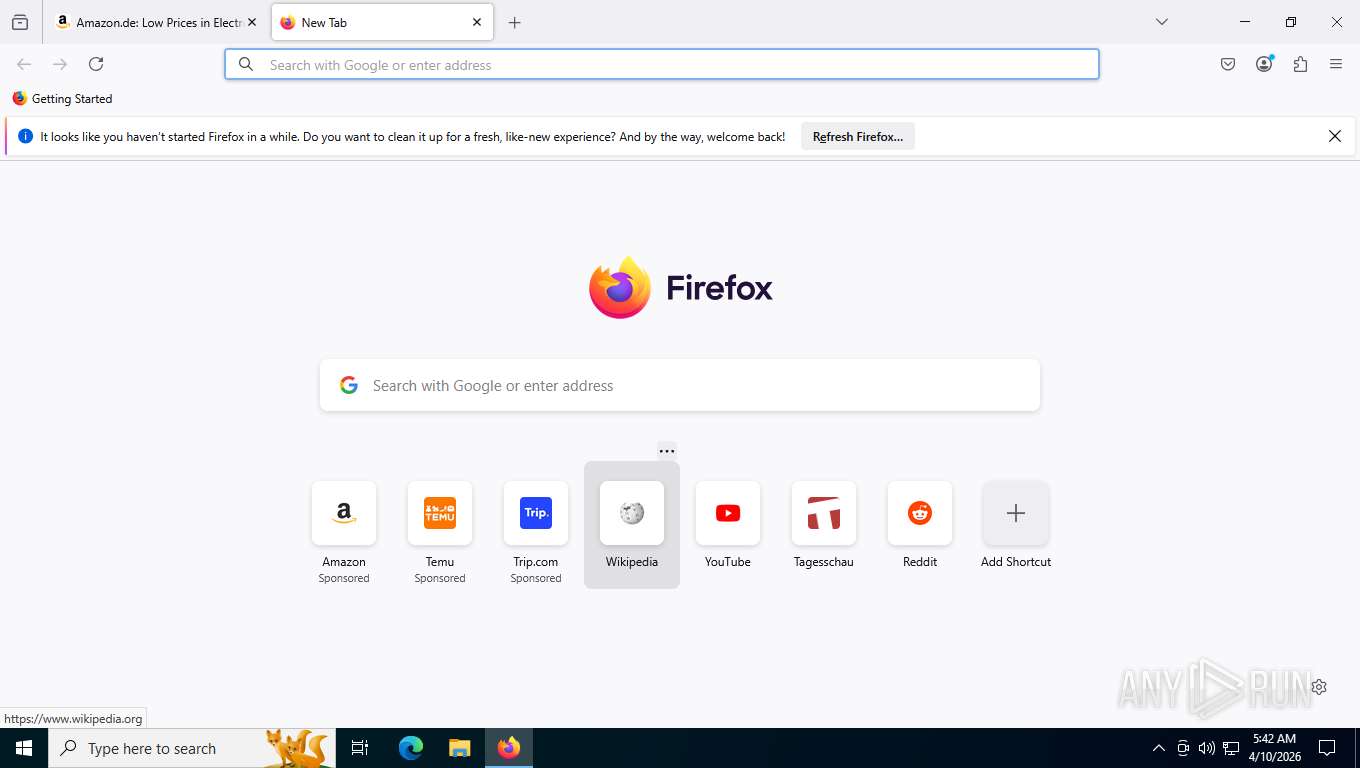
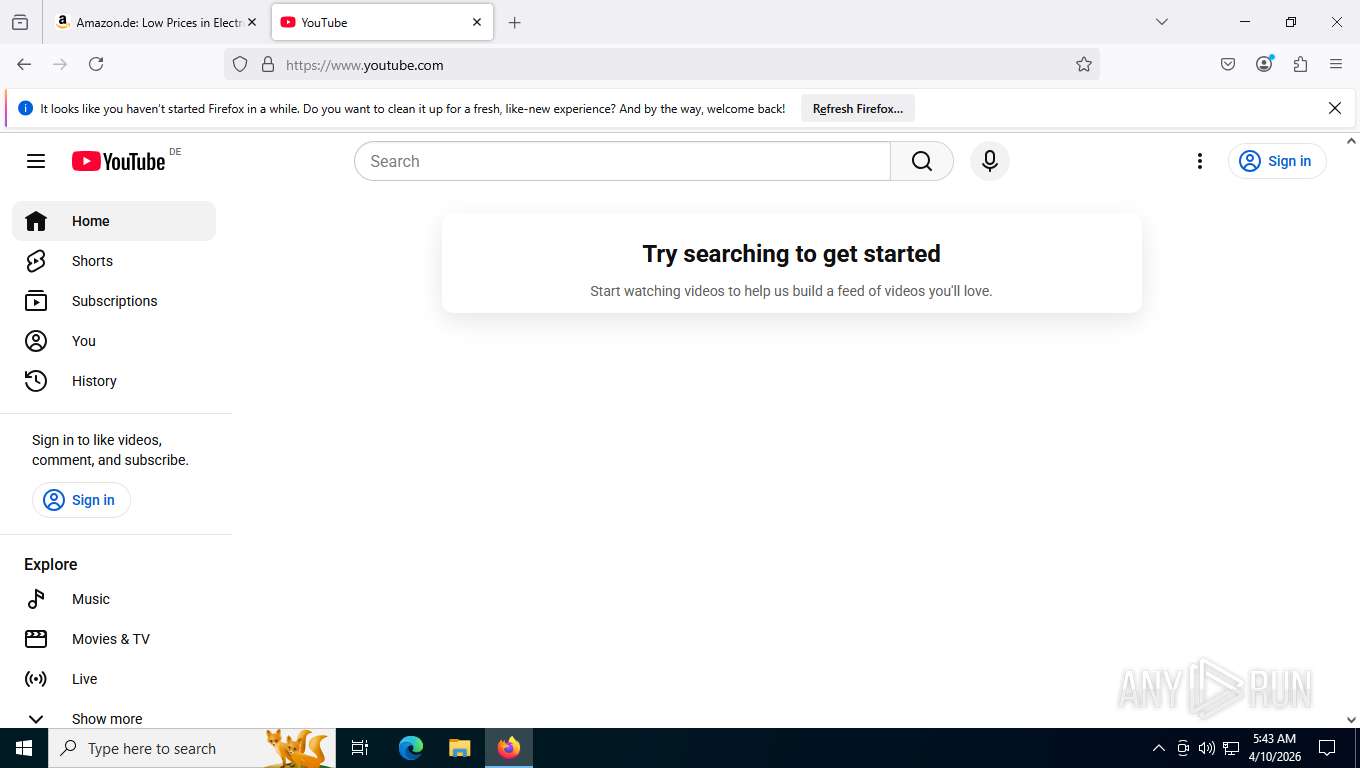
Manual execution by a user
- DiscordFixUlt.exe (PID: 1164)
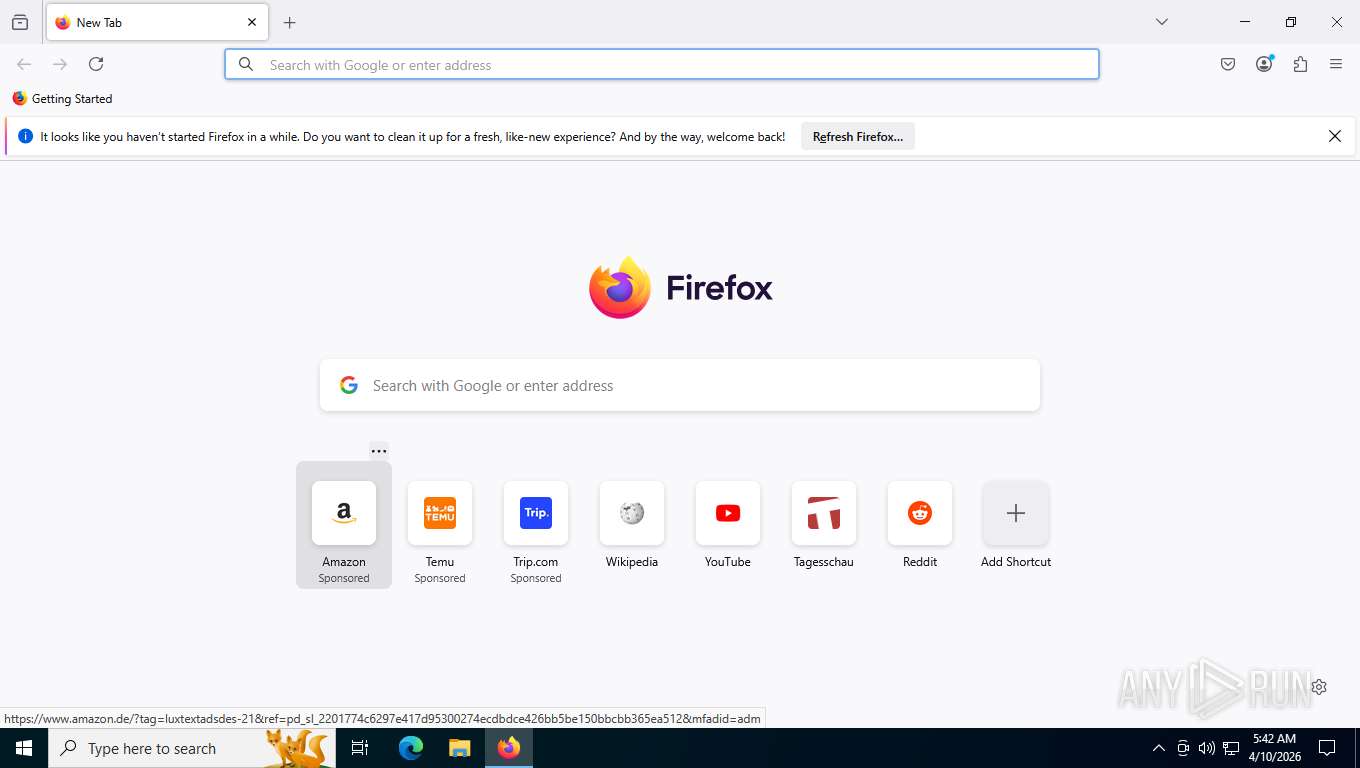
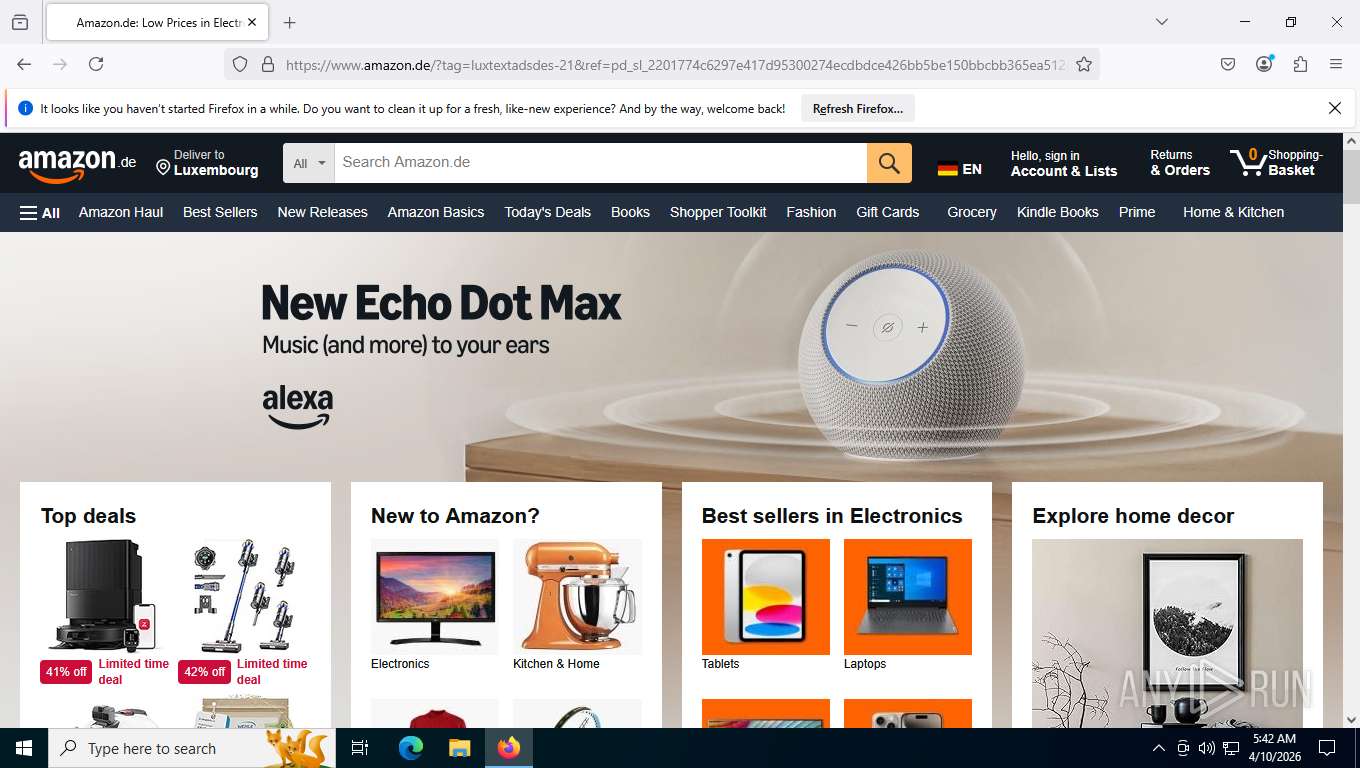
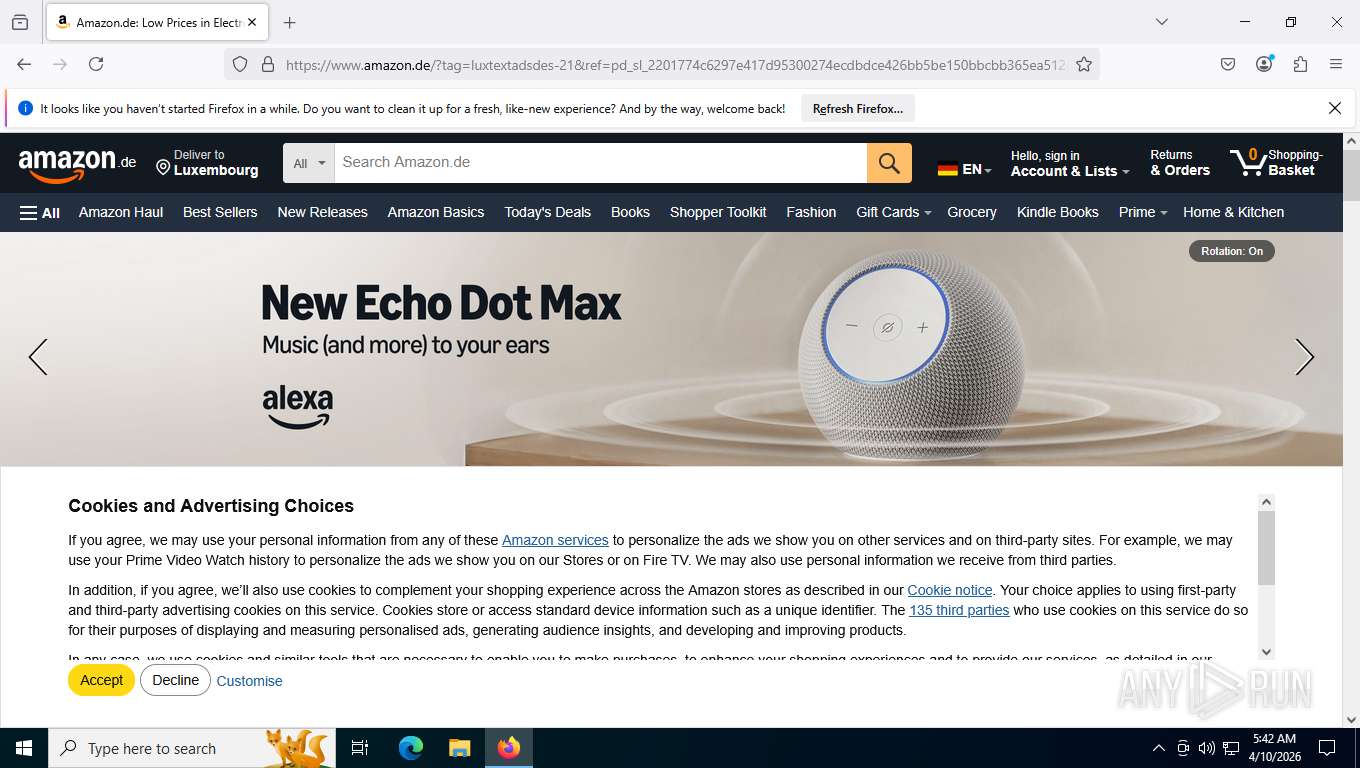
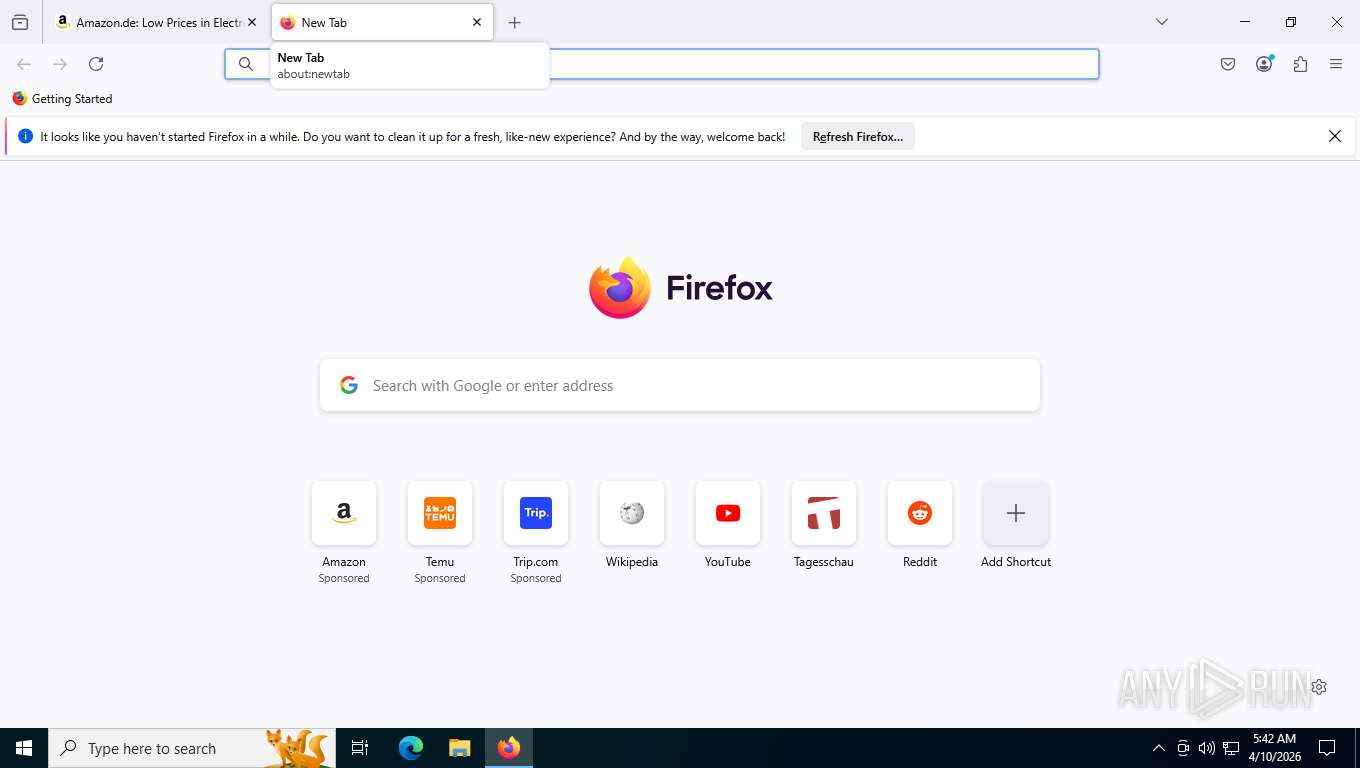
- firefox.exe (PID: 2308)
Reads the machine GUID from the registry
- DiscordFixUlt.exe (PID: 1164)
- DiscordFixUlt.exe (PID: 6864)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3748)
- firefox.exe (PID: 6472)
Process checks computer location settings
- DiscordFixUlt.exe (PID: 1164)
Reads security settings of Internet Explorer
- DiscordFixUlt.exe (PID: 1164)
Reads the computer name
- DiscordFixUlt.exe (PID: 6864)
- DiscordFixUlt.exe (PID: 1164)
There is functionality for taking screenshot (YARA)
- DiscordFixUlt.exe (PID: 6864)
Detects GO elliptic curve encryption (YARA)
- DiscordFixUlt.exe (PID: 6864)
Application based on Golang
- DiscordFixUlt.exe (PID: 6864)
UPX packer has been detected
- DiscordFixUlt.exe (PID: 6864)
Found Base64 encoded access to environment variables via PowerShell (YARA)
- DiscordFixUlt.exe (PID: 6864)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- DiscordFixUlt.exe (PID: 6864)
Application launched itself
- firefox.exe (PID: 6472)
- firefox.exe (PID: 2308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 3301312 |
| UncompressedSize: | 3297280 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | DiscordFixUlt.exe |
Total processes
162
Monitored processes
24
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 2240 -prefsLen 36580 -prefMapHandle 2244 -prefMapSize 273045 -ipcHandle 2252 -initialChannelId {f6659cbf-52fa-47c2-adad-911196f1dc1a} -parentPid 6472 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6472" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 2 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
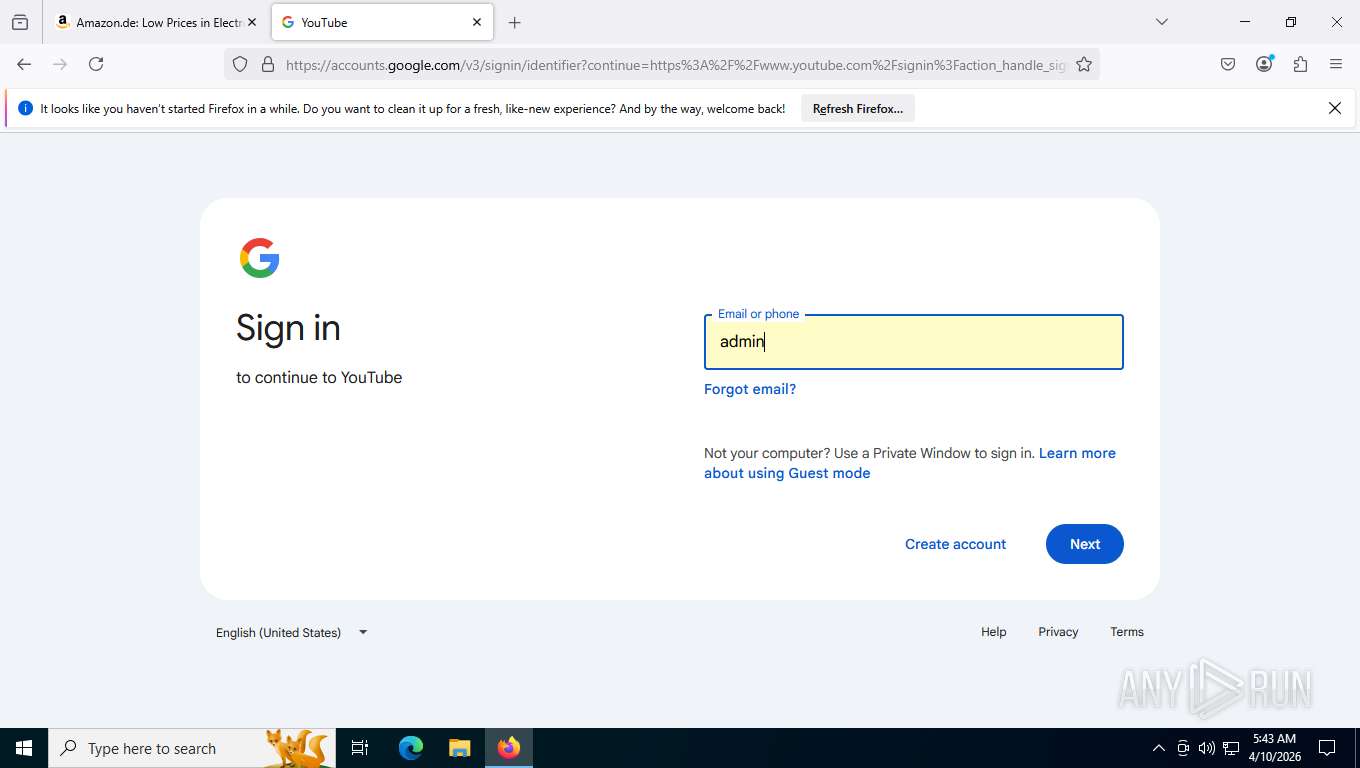
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\Desktop\DiscordFixUlt.exe" | C:\Users\admin\Desktop\DiscordFixUlt.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5048 -prefsLen 39429 -prefMapHandle 5012 -prefMapSize 273045 -jsInitHandle 5020 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5080 -initialChannelId {948fe8b8-ad80-4ded-bbe3-570b93a42936} -parentPid 6472 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6472" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 2032 -prefsLen 36580 -prefMapHandle 2036 -prefMapSize 273045 -ipcHandle 2096 -initialChannelId {07dab540-87ca-4306-bac0-aceb9a441f9c} -parentPid 6472 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6472" -appDir "C:\Program Files\Mozilla Firefox\browser" - 1 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3532 -prefsLen 37375 -prefMapHandle 3776 -prefMapSize 273045 -jsInitHandle 3780 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3788 -initialChannelId {648d6858-13e3-4111-982b-6b01179658e5} -parentPid 6472 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6472" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 3748 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Downloads\DiscordFix.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5296 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5340 -prefsLen 39510 -prefMapHandle 5636 -prefMapSize 273045 -jsInitHandle 5640 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5648 -initialChannelId {97d9486d-7042-4fae-888e-216f3289302d} -parentPid 6472 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6472" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 5444 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3868 -prefsLen 39510 -prefMapHandle 2812 -prefMapSize 273045 -jsInitHandle 3836 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5904 -initialChannelId {e3a087dc-6a9e-44aa-97ae-53a51507e459} -parentPid 6472 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6472" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 11 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
Total events
3 274
Read events
3 253
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\DiscordFix.rar | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
515
Text files
68
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:73A2E89AF4D3D52D0167E7B3805E20E5 | SHA256:AB2871B600E4E7A13DF4552B1172DA5EEA32C9BA8E3D2153F1987FE2B124CFC4 | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json | text | |
MD5:815E2F92EDD10007D321EF76CD698377 | SHA256:A6A87313301298FFB6F58106862ADDC88C9647B7972EB19FDE66A412041A011B | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.contile.json.tmp | text | |
MD5:815E2F92EDD10007D321EF76CD698377 | SHA256:A6A87313301298FFB6F58106862ADDC88C9647B7972EB19FDE66A412041A011B | |||
| 3748 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3748.12952\DiscordFixUlt.exe | executable | |
MD5:AFB3973F8389C562A5824924138A60BB | SHA256:BF8C3CE6BB07689E2F01B2D206D1CA028EE8B40C635EFAFCA6BD8C83B147BE98 | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.discovery_stream.json.tmp | text | |
MD5:3AFFBD6CBFC074B3025F8EB603F24041 | SHA256:C8A6EE446789CDF02A7FD8547085C78D3F1266BC9EB5920B5FC66294E3250662 | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | text | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
793
TCP/UDP connections
173
DNS requests
172
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 74.179.77.164:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 20.165.94.63:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
7452 | svchost.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 312 b | whitelisted |
7452 | svchost.exe | GET | 200 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.74 Kb | whitelisted |
7452 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
7452 | svchost.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7452 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 2.16.204.149:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7452 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7452 | svchost.exe | 23.216.77.20:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
dns.google |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7452 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2232 | svchost.exe | Misc activity | INFO [ANY.RUN] Google DNS-over-HTTPS service requested (dns. google) |
6864 | DiscordFixUlt.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Salatstealer JA3 hash observed |
6864 | DiscordFixUlt.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Salatstealer JA3 hash observed |
2232 | svchost.exe | Misc activity | INFO [ANY.RUN] Cloudflare DNS-over-HTTPS service requested (cloudflare-dns .com) |
6864 | DiscordFixUlt.exe | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |
6864 | DiscordFixUlt.exe | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
2232 | svchost.exe | A Network Trojan was detected | ET MALWARE Observed DNS Query to Salat Stealer Domain (salat .cn) |
6864 | DiscordFixUlt.exe | A Network Trojan was detected | ET MALWARE Observed Salat Stealer Domain (salat .cn in TLS SNI) |
6864 | DiscordFixUlt.exe | A Network Trojan was detected | ET MALWARE Observed Salat Stealer Domain (salat .cn in TLS SNI) |