| File name: | H-Worm Plus.exe |
| Full analysis: | https://app.any.run/tasks/4f2b468b-bcd3-4fdc-b27d-b9b56dac89dc |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 08:12:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A660222D479A76724321E2F01FFBE1A3 |
| SHA1: | FC5A3932CA773D6E970CB2F046F4E079C63FCAD0 |
| SHA256: | 7F3DDE47AD84F07F0833A760D69F7B020A06D8A4FE52D9CA435500047CF185D8 |
| SSDEEP: | 98304:rTX1fQ4wQt5A52PlSPIKm/E27K6OIuGeJp3CcBDDZHG7v9wmGsaFGwTjhE:GW5PLU |
MALICIOUS
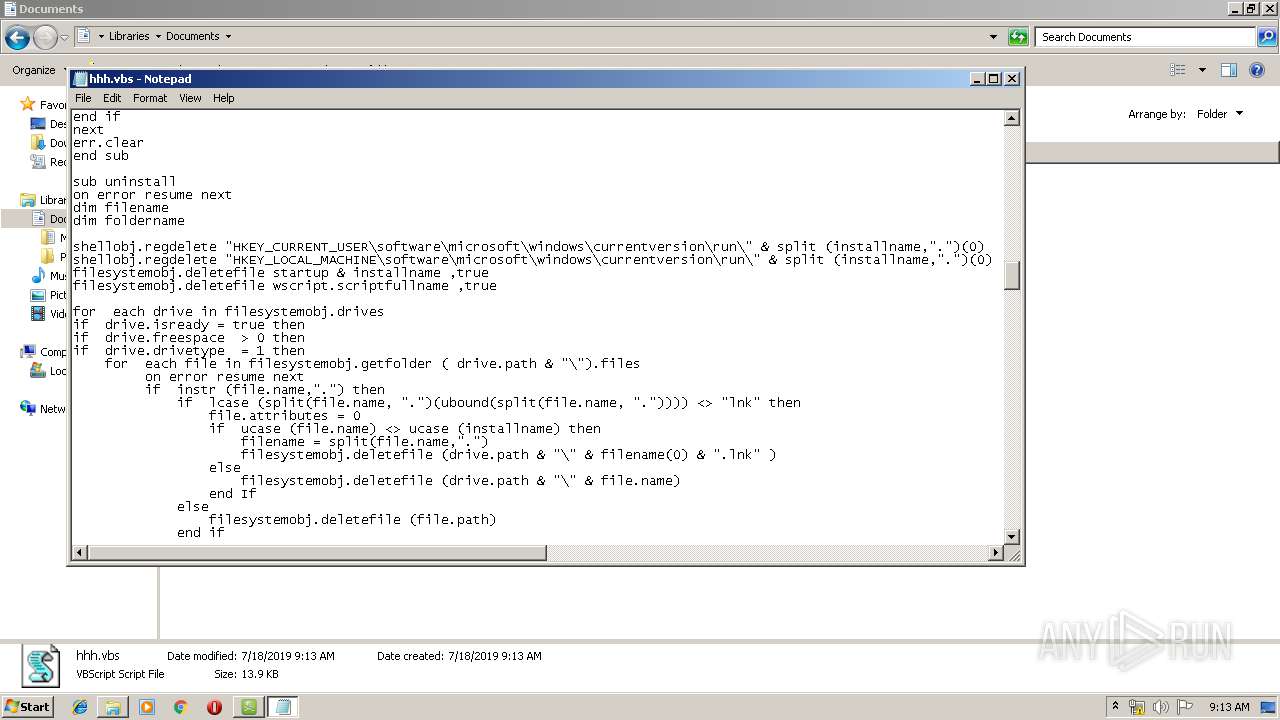
Changes the autorun value in the registry
- WScript.exe (PID: 3864)
- wscript.exe (PID: 4036)
Writes to a start menu file
- WScript.exe (PID: 3864)
- wscript.exe (PID: 4036)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 3864)
- wscript.exe (PID: 4036)
Reads Internet Cache Settings
- H-Worm Plus.exe (PID: 3600)
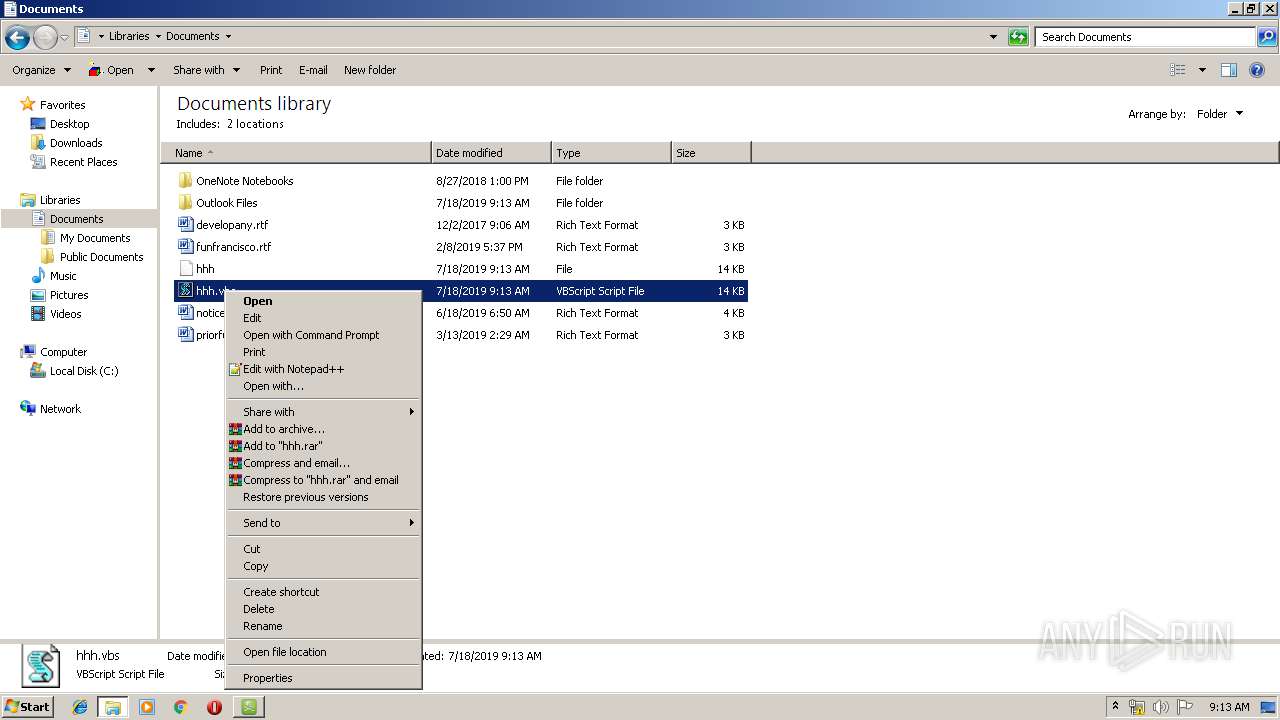
Executes scripts
- WScript.exe (PID: 3864)
INFO
Manual execution by user
- WScript.exe (PID: 3864)
- explorer.exe (PID: 2884)
- Notepad.exe (PID: 2144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (56.2) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (38.1) |
| .exe | | | Win32 EXE PECompact compressed (generic) (3.5) |
| .exe | | | Win32 Executable Delphi generic (1.1) |
| .exe | | | Win32 Executable (generic) (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1370624 |
| InitializedDataSize: | 2120192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14f8dc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | French |
| CharacterSet: | Windows, Latin1 |
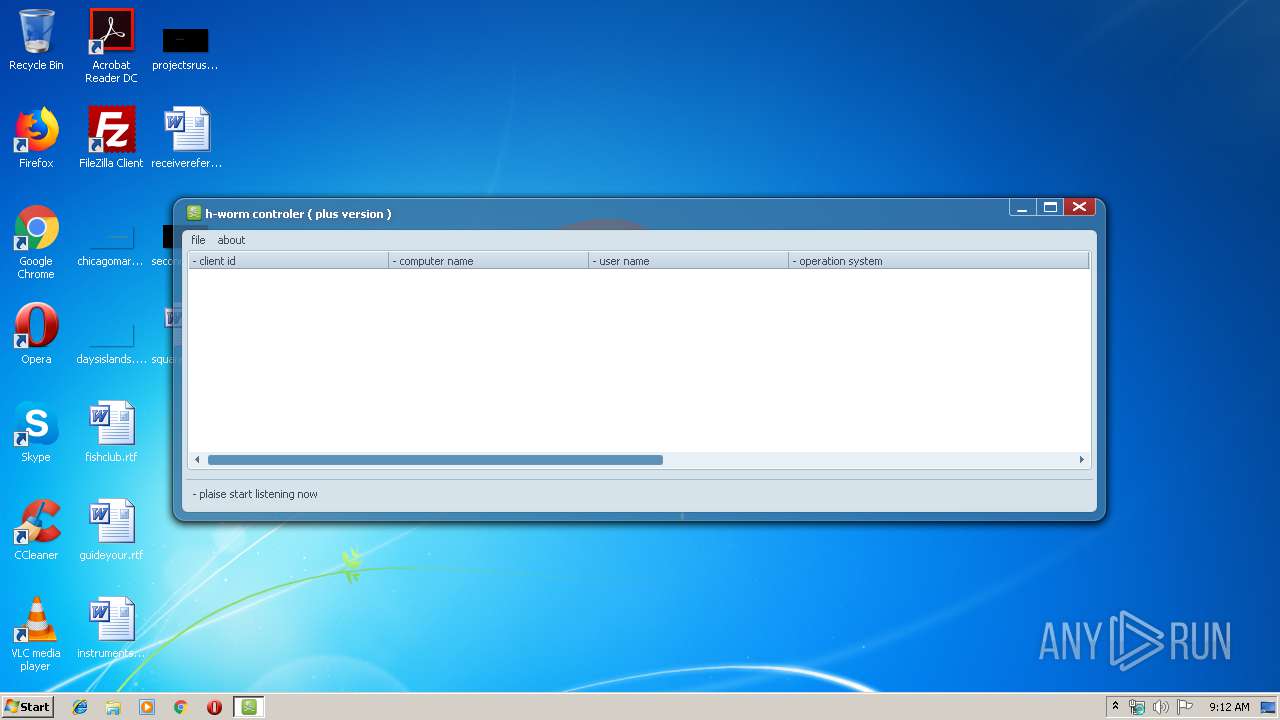
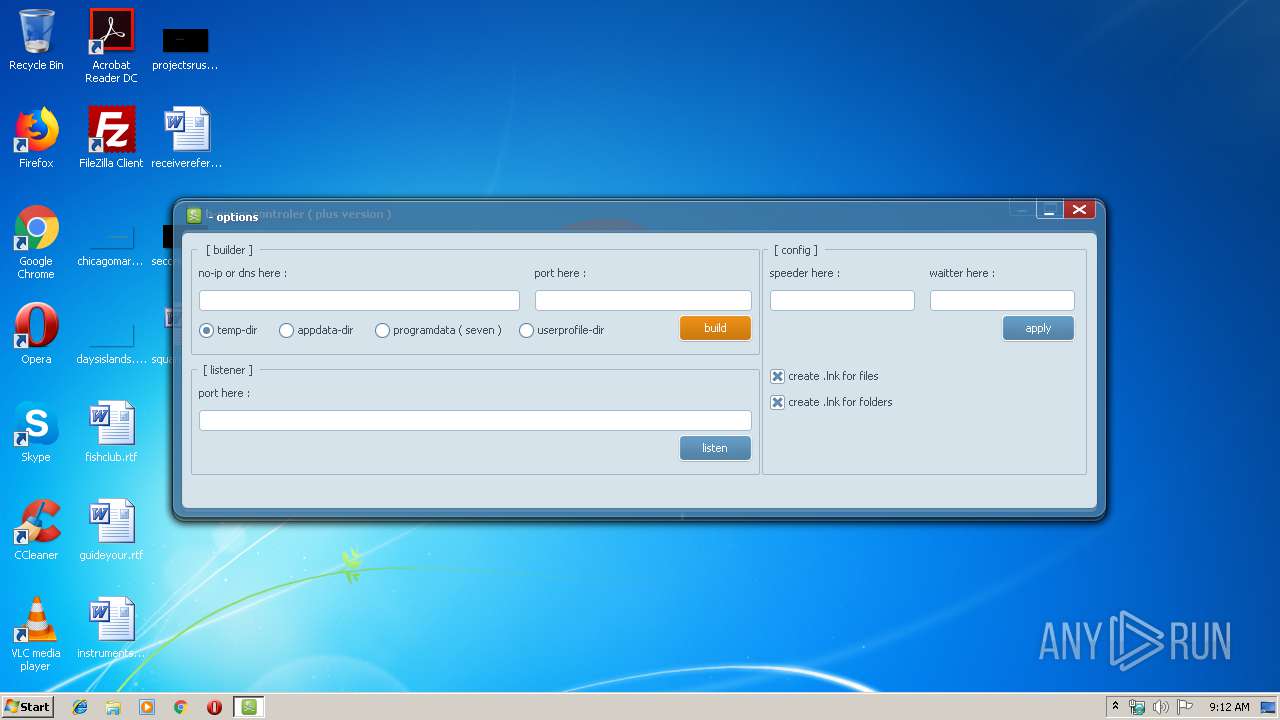
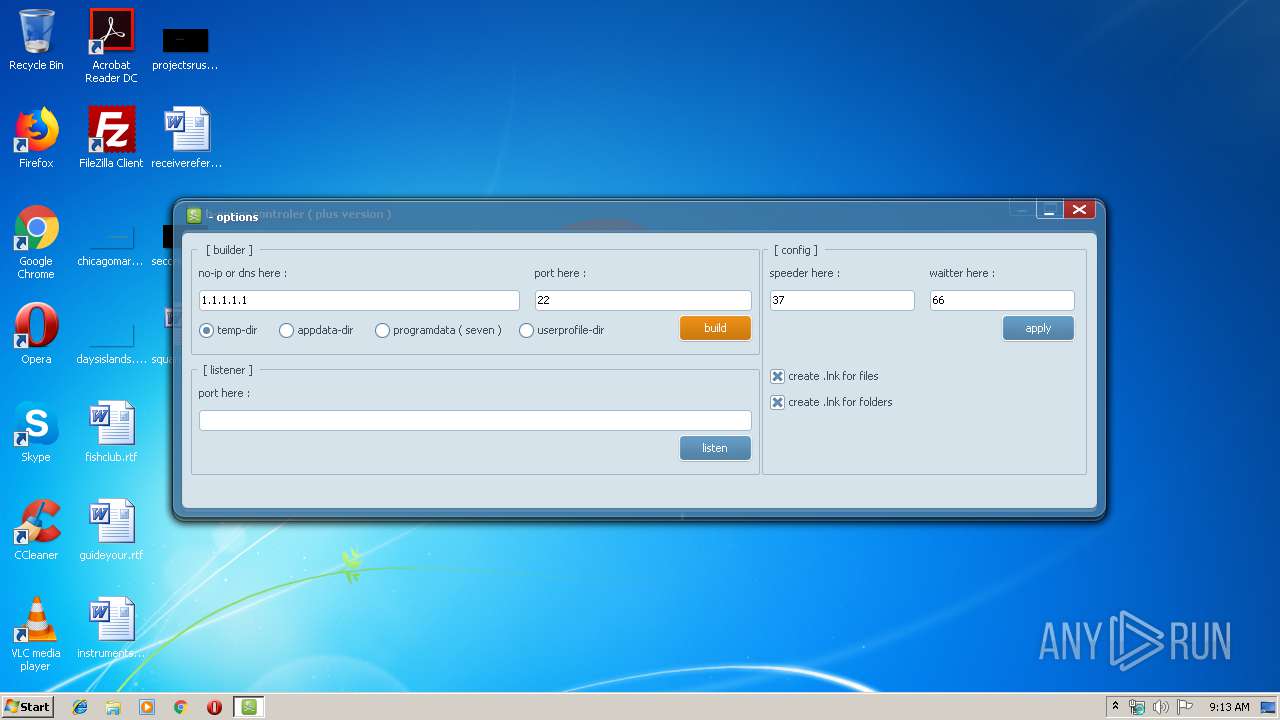
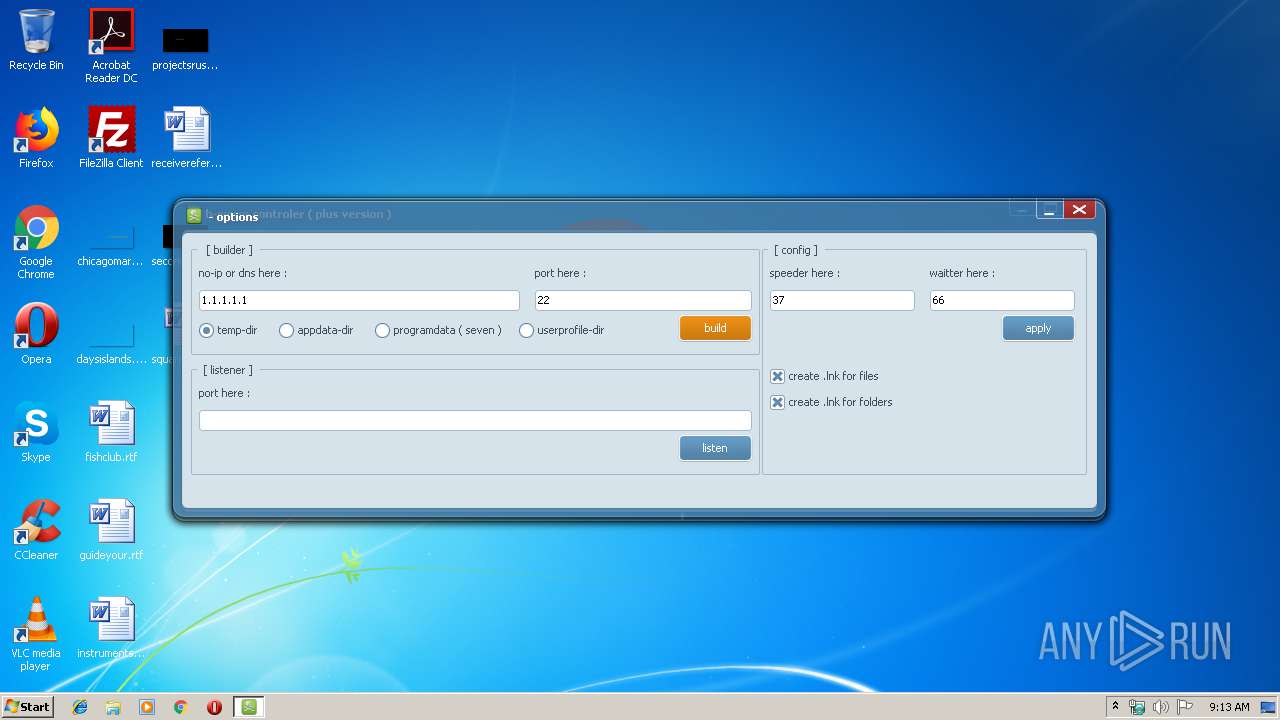
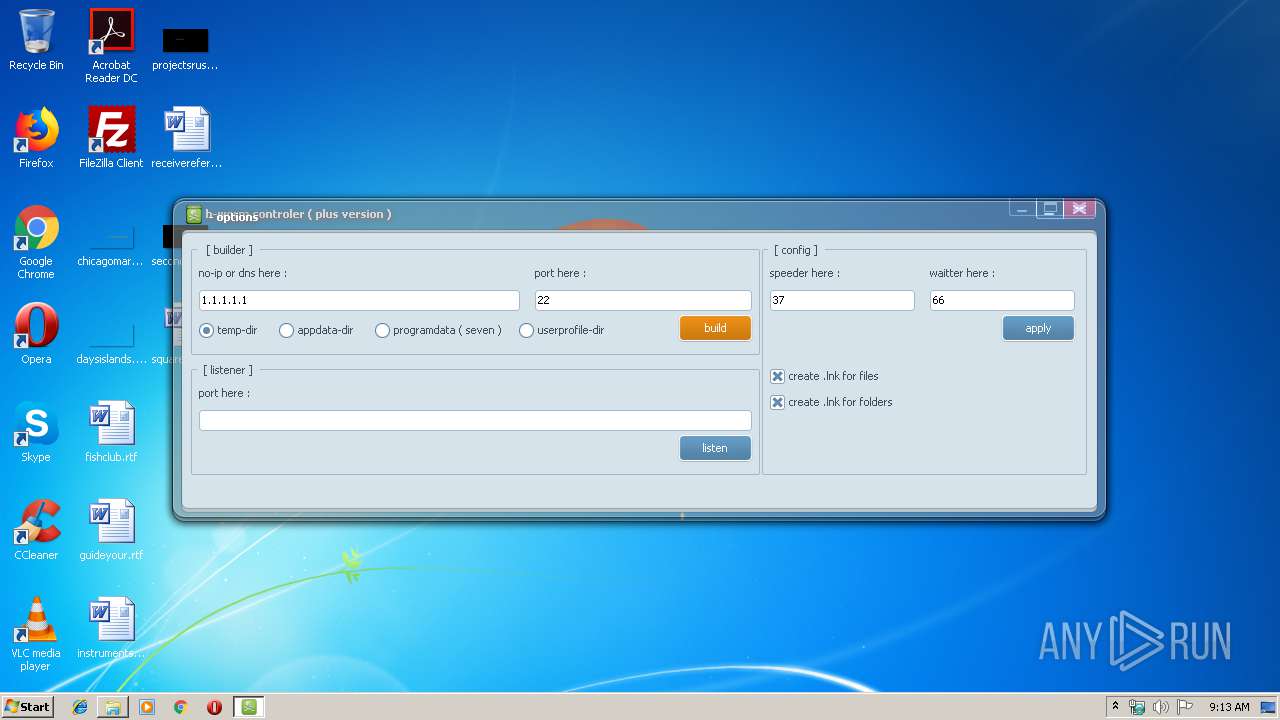
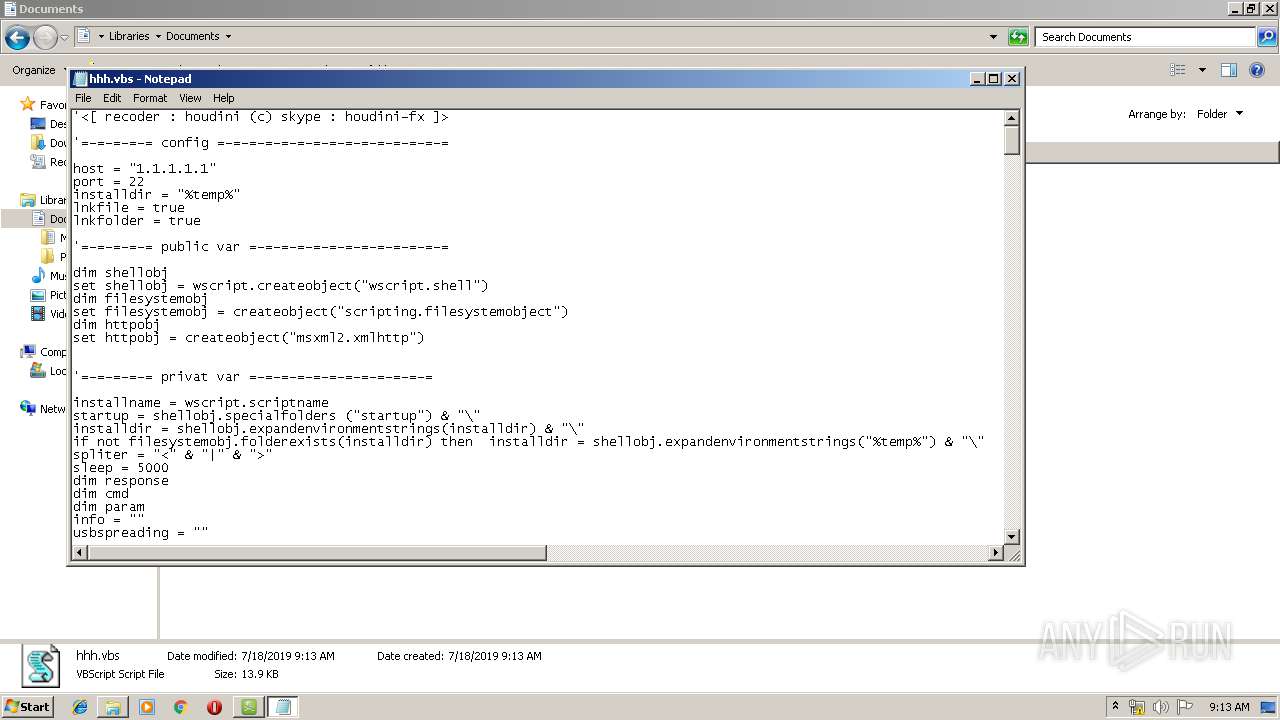
| CompanyName: | skype : houdini-fx |
| FileDescription: | worm of houdini (c) controler |
| FileVersion: | 4.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | skype : houdini-fx |
| FileDescription: | worm of houdini (c) controler |
| FileVersion: | 4.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0014E970 | 0x0014EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51348 |
DATA | 0x00150000 | 0x00006160 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.38717 |
BSS | 0x00157000 | 0x00001381 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00159000 | 0x0000280A | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.92467 |
.tls | 0x0015C000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0015D000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.180244 |
.reloc | 0x0015E000 | 0x00011BAC | 0x00011C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.66162 |
.rsrc | 0x00170000 | 0x001EB000 | 0x001EB000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.02492 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.95218 | 581 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.43985 | 4264 | UNKNOWN | French - France | RT_ICON |
3 | 6.42678 | 1128 | UNKNOWN | French - France | RT_ICON |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
3683 | 2.92331 | 170 | UNKNOWN | UNKNOWN | RT_STRING |
3684 | 3.47221 | 390 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
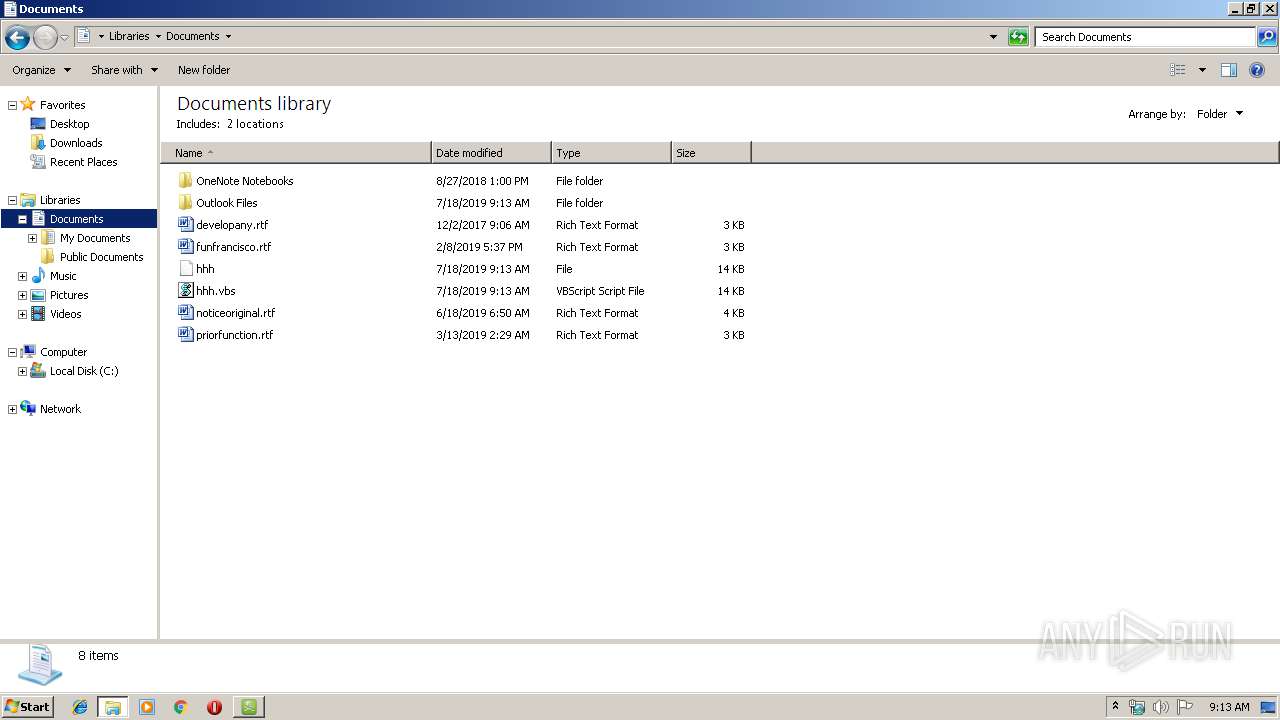
| 2144 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Documents\hhh.vbs | C:\Windows\System32\Notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2884 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\AppData\Local\Temp\H-Worm Plus.exe" | C:\Users\admin\AppData\Local\Temp\H-Worm Plus.exe | — | explorer.exe | |||||||||||
User: admin Company: skype : houdini-fx Integrity Level: MEDIUM Description: worm of houdini (c) controler Exit code: 0 Version: 4.0.0.0 Modules
| |||||||||||||||
| 3864 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Documents\hhh.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4036 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Local\Temp\hhh.vbs" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
885
Read events
773
Write events
108
Delete events
4
Modification events
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | 0 |
Value: 48002D0057006F0072006D00200050006C00750073002E00650078006500000014001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC20000000 | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3600) H-Worm Plus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | 1 |
Value: 14001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC20001C030000160381191410EC02200000004840000000000000000000000000000000000000000000000000000000005B0000003153505330F125B7EF471A10A5F102608C9EEBAC190000000A000000001F000000040000006800680068000000150000000C00000000150000000000000000000000110000000D000000001300000080000000000000002402000031535053A66A63283D95D211B5D600C04FD918D01100000019000000001300000077014840C9010000200000000011100000B501000014001F50E04FD020EA3A6910A2D808002B30309D19002F433A5C000000000000000000000000000000000000007400310000000000454B314E1100557365727300600008000400EFBEEE3AA314454B314E2A0000005A01000000000100000000000000000036000000000055007300650072007300000040007300680065006C006C00330032002E0064006C006C002C002D0032003100380031003300000014004C003100000000001C4D9960100061646D696E00380008000400EFBE454B804A1C4D99602A0000002D000000000004000000000000000000000000000000610064006D0069006E00000014008000310000000000F24E93411100444F43554D457E310000680008000400EFBE454B814AF24E93412A0000007A0100000000020000000000000000003E000000000044006F00630075006D0065006E0074007300000040007300680065006C006C00330032002E0064006C006C002C002D003200310037003700300000001800460032000000000000000000800068686800340008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000006800680068000000120000000000001900000018000000001F000000040000006800680068000000150000000B000000001F000000020000002E00000000000000690000003153505340E83E1E2BBC6C4782372ACD1A839B224D00000008000000001F0000001D00000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F00630075006D0065006E00740073005C0068006800680000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
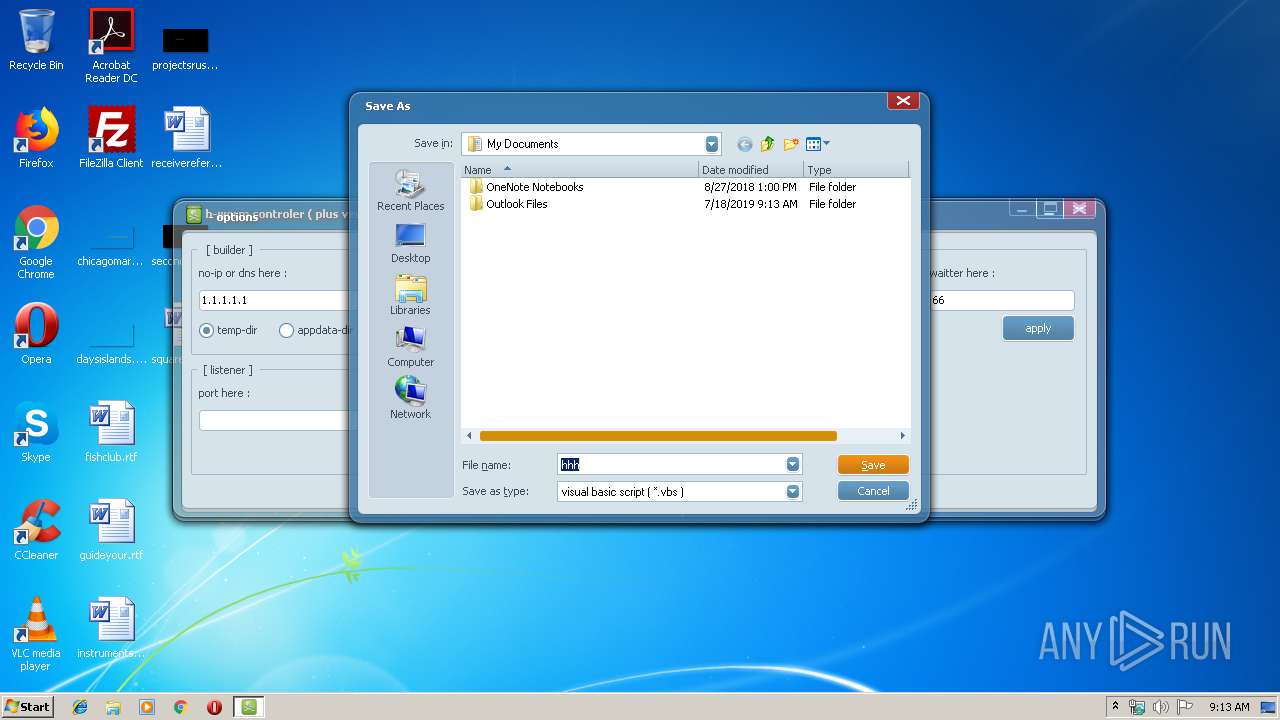
| 4036 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\hhh.vbs | text | |
MD5:— | SHA256:— | |||
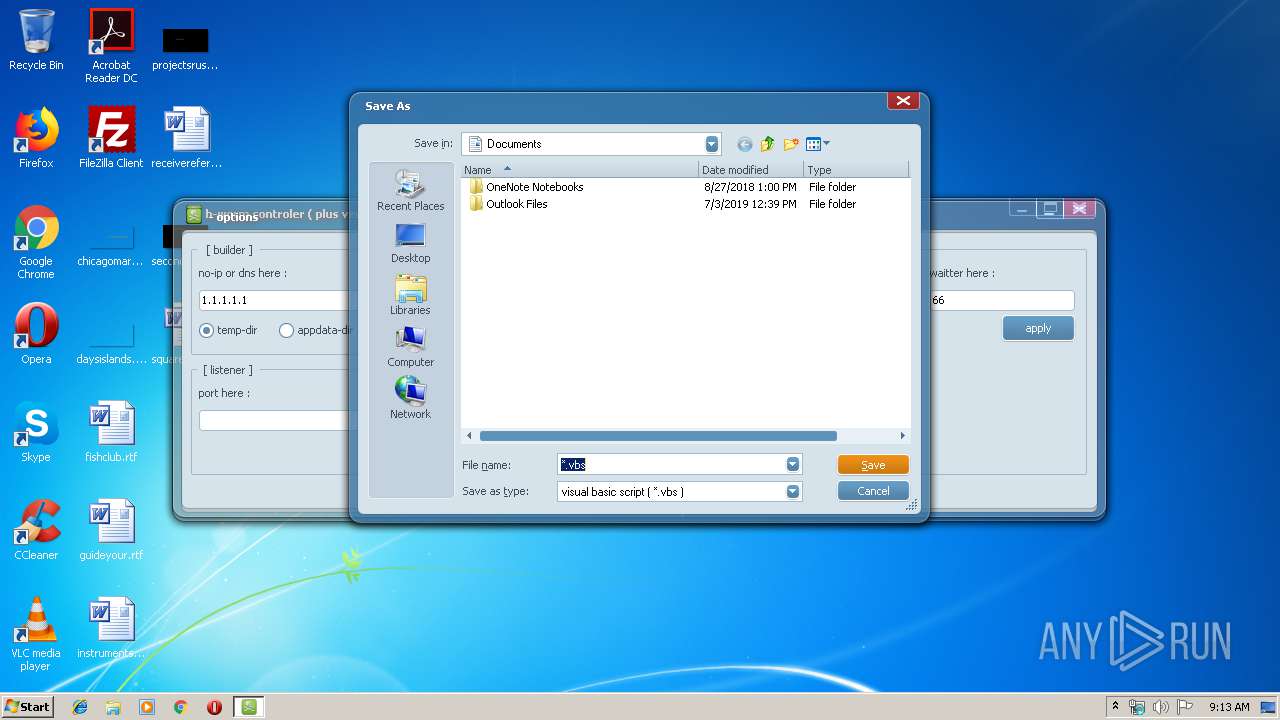
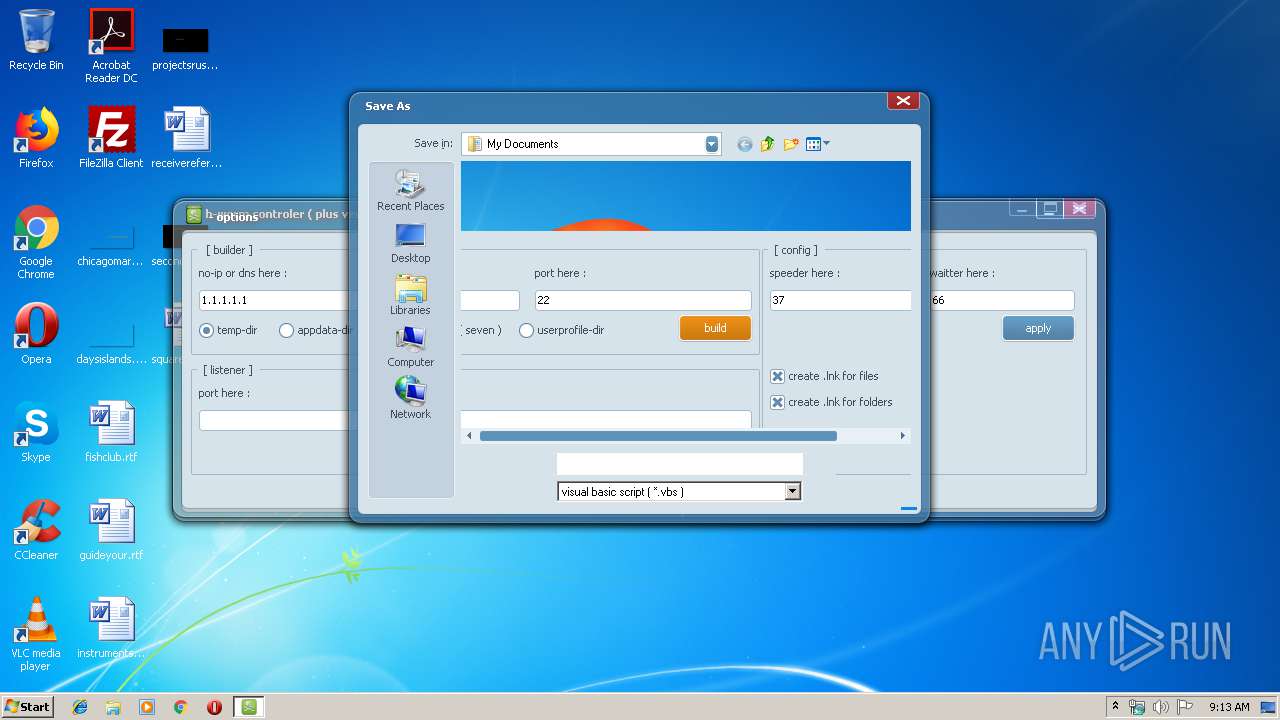
| 3600 | H-Worm Plus.exe | C:\Users\admin\Documents\hhh.vbs | text | |
MD5:— | SHA256:— | |||
| 3600 | H-Worm Plus.exe | C:\Users\admin\AppData\Local\Temp\geoip.dat | binary | |
MD5:CBF00B75A45AAE54CD797CA4C07DBF1E | SHA256:58FCDEAAC15E222A744B27333A776A2B91DC493D212ACBE971BA6B987265A73C | |||
| 3864 | WScript.exe | C:\Users\admin\AppData\Local\Temp\hhh.vbs | text | |
MD5:— | SHA256:— | |||
| 3600 | H-Worm Plus.exe | C:\Users\admin\Documents\hhh | text | |
MD5:— | SHA256:— | |||
| 3864 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\hhh.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report