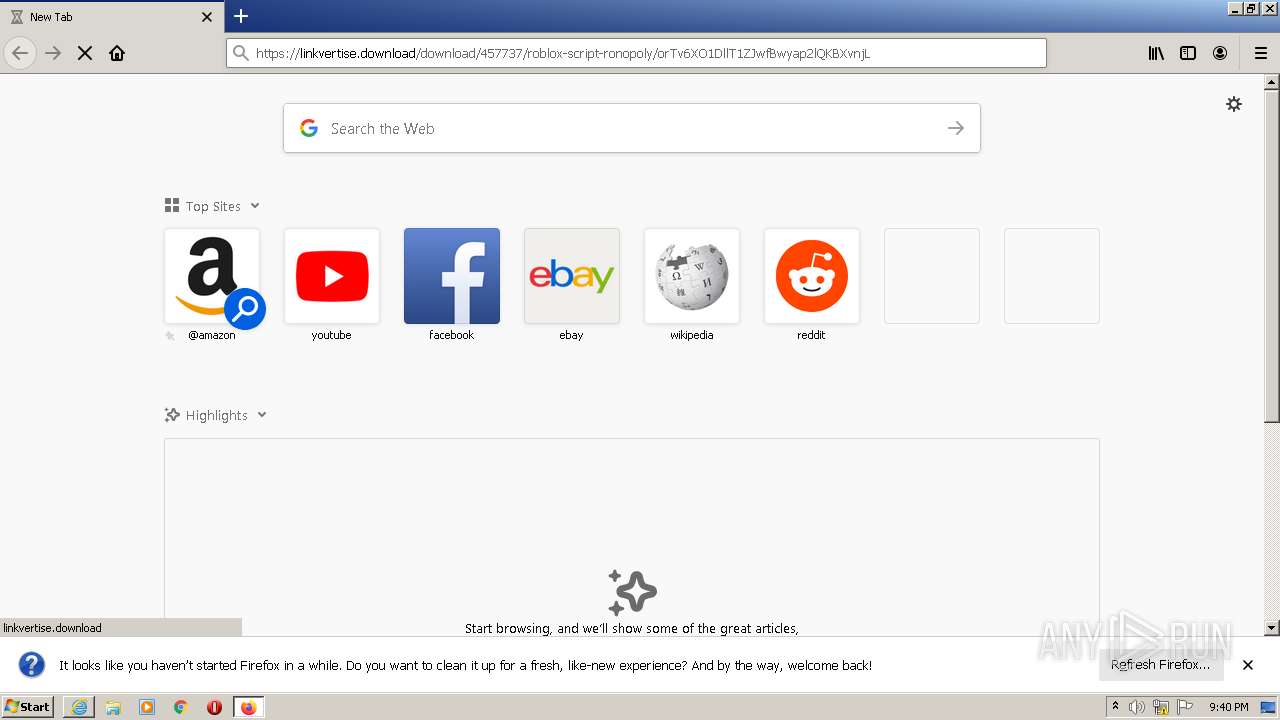
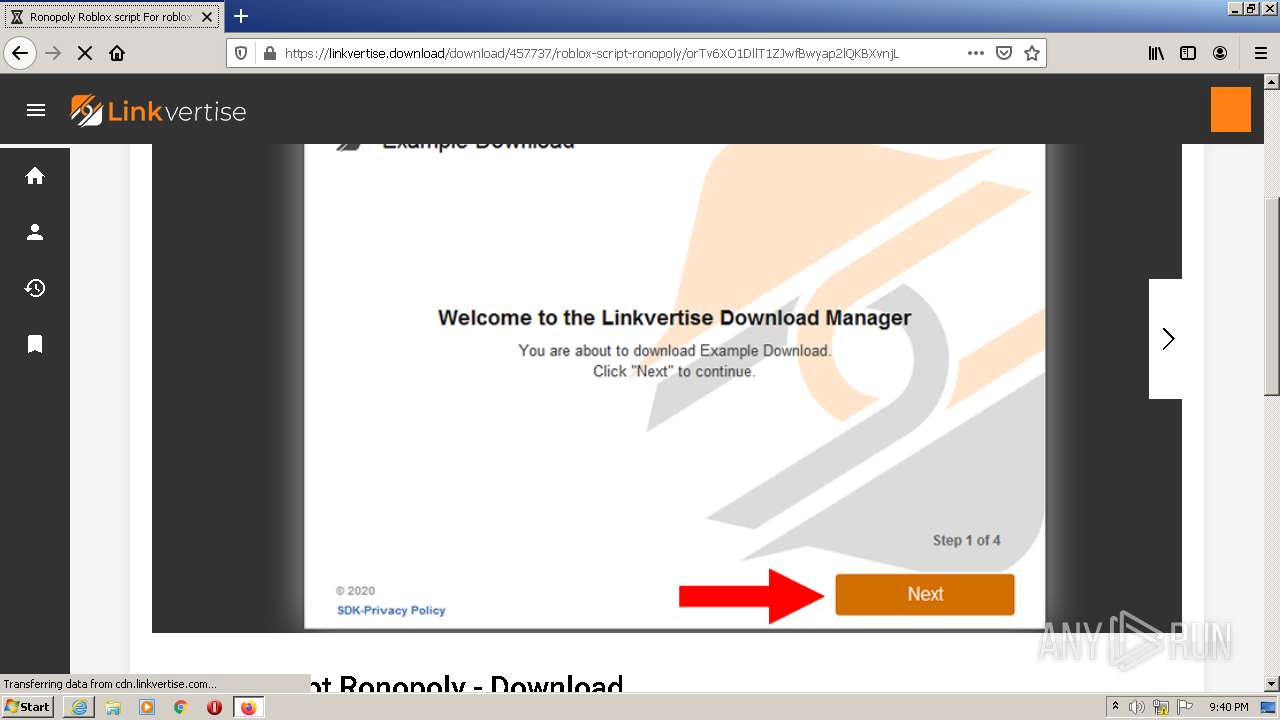
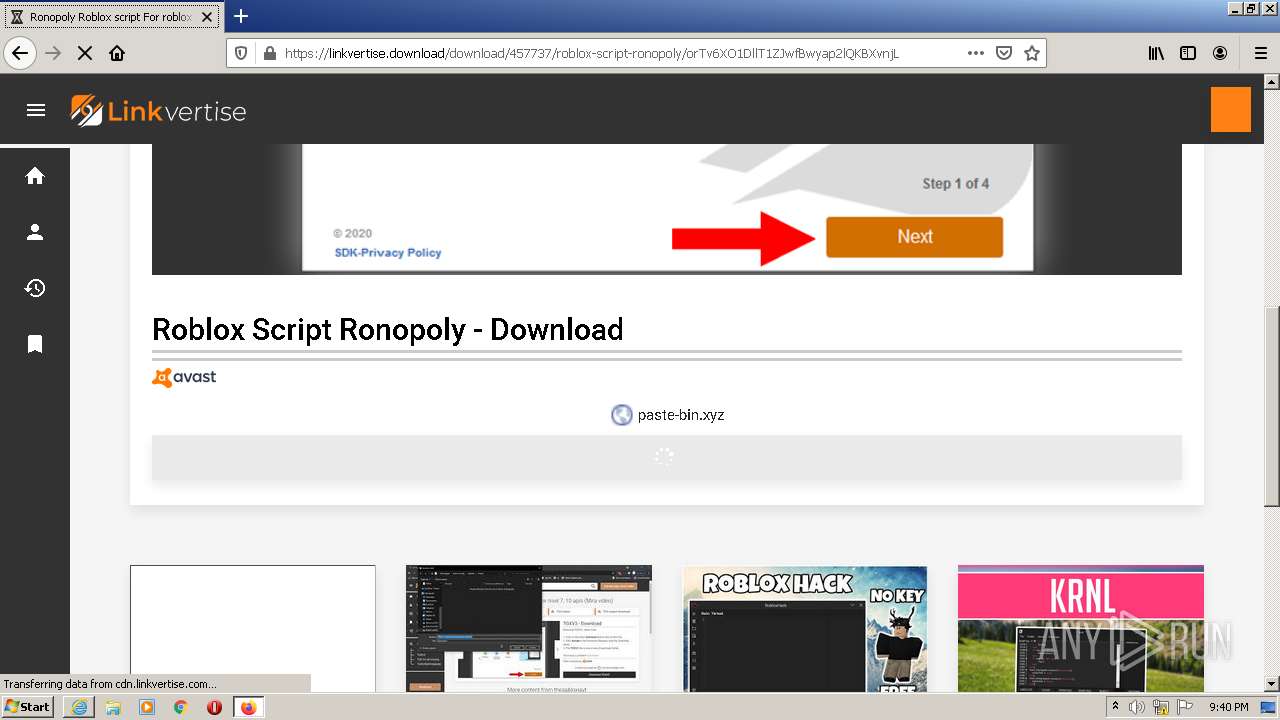
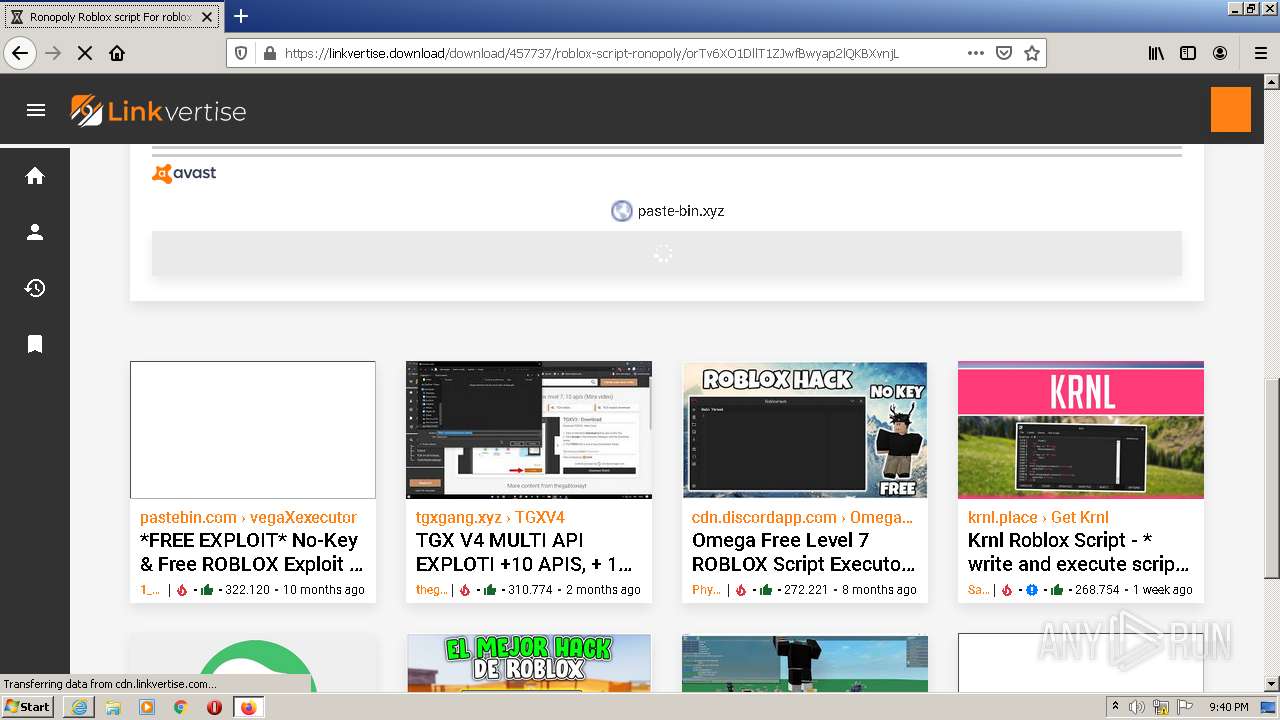
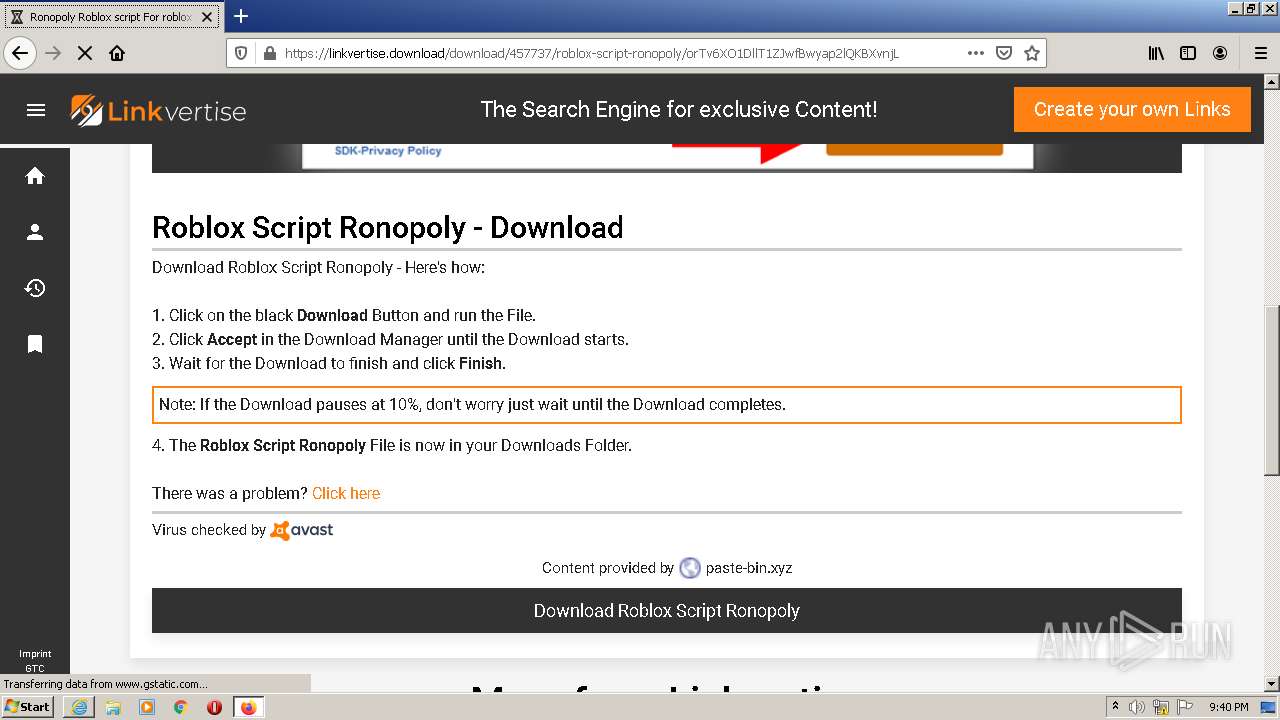
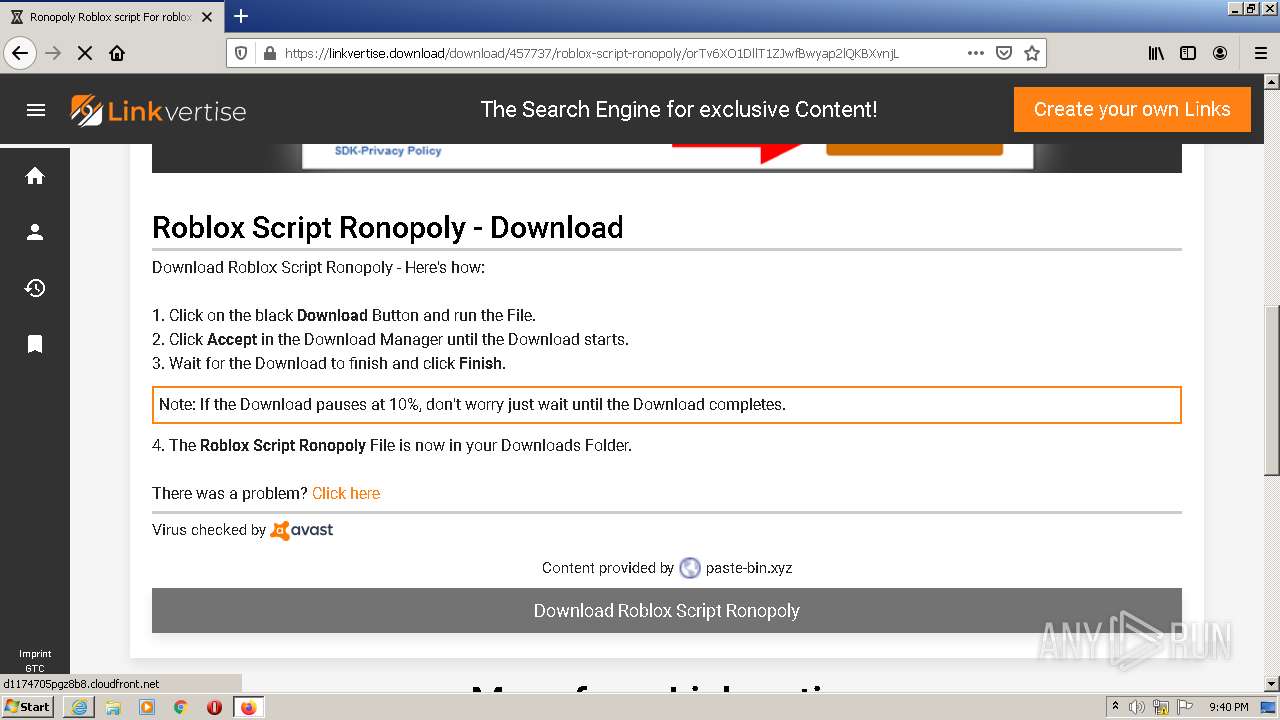
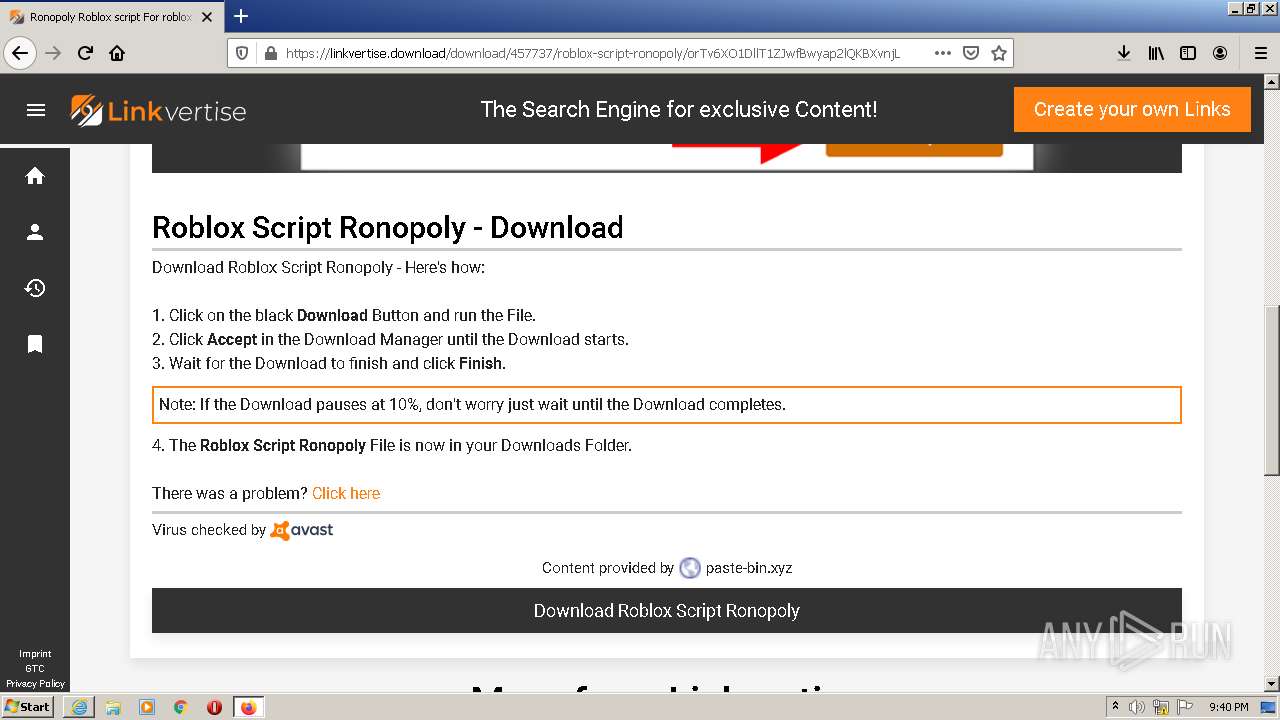
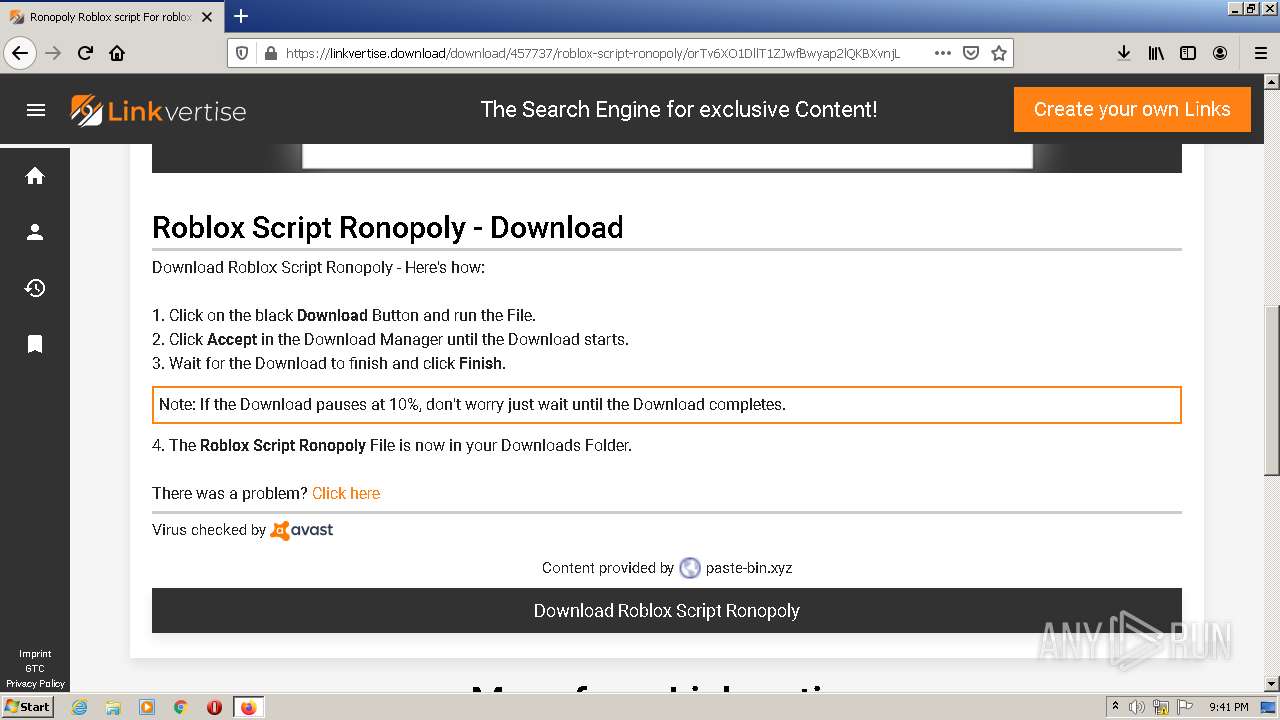
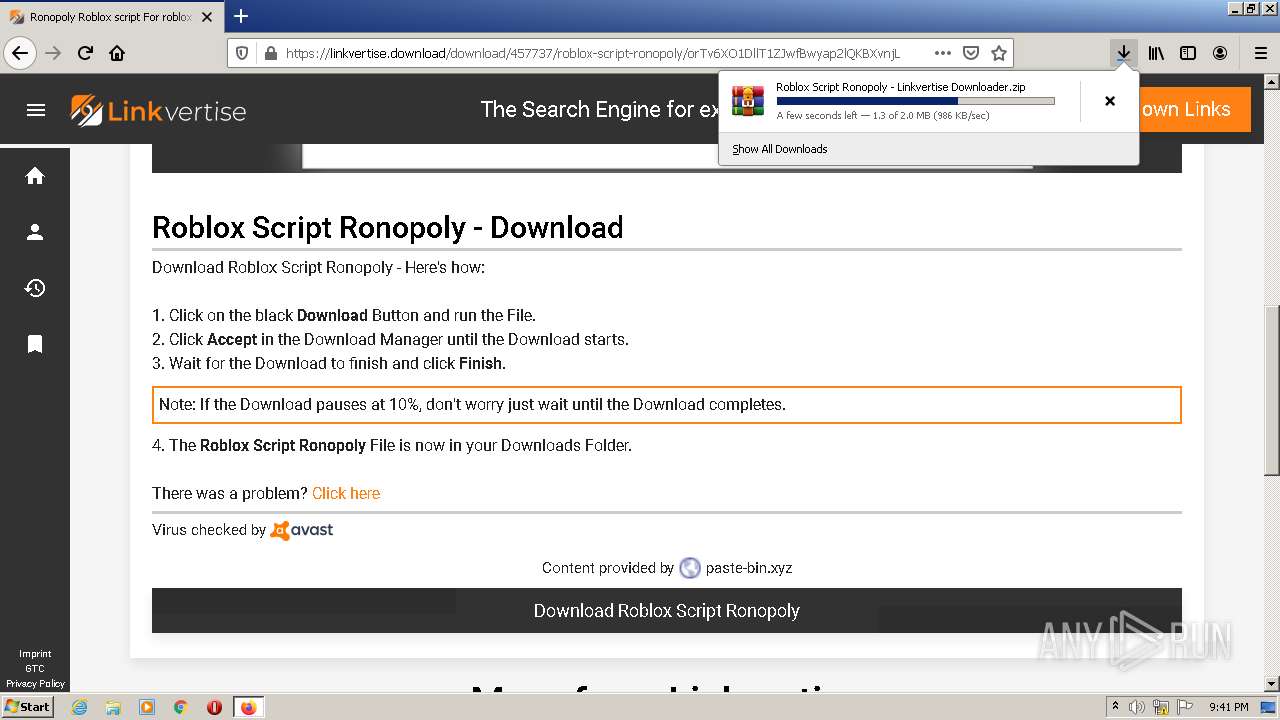
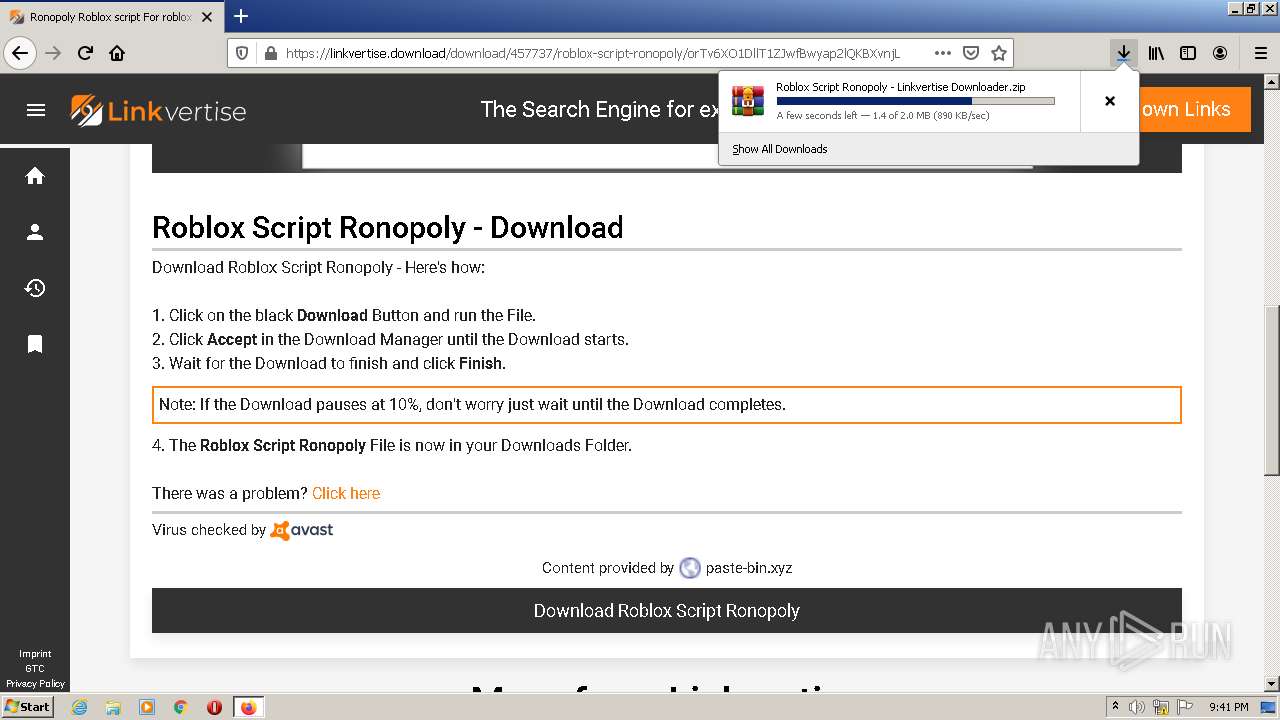
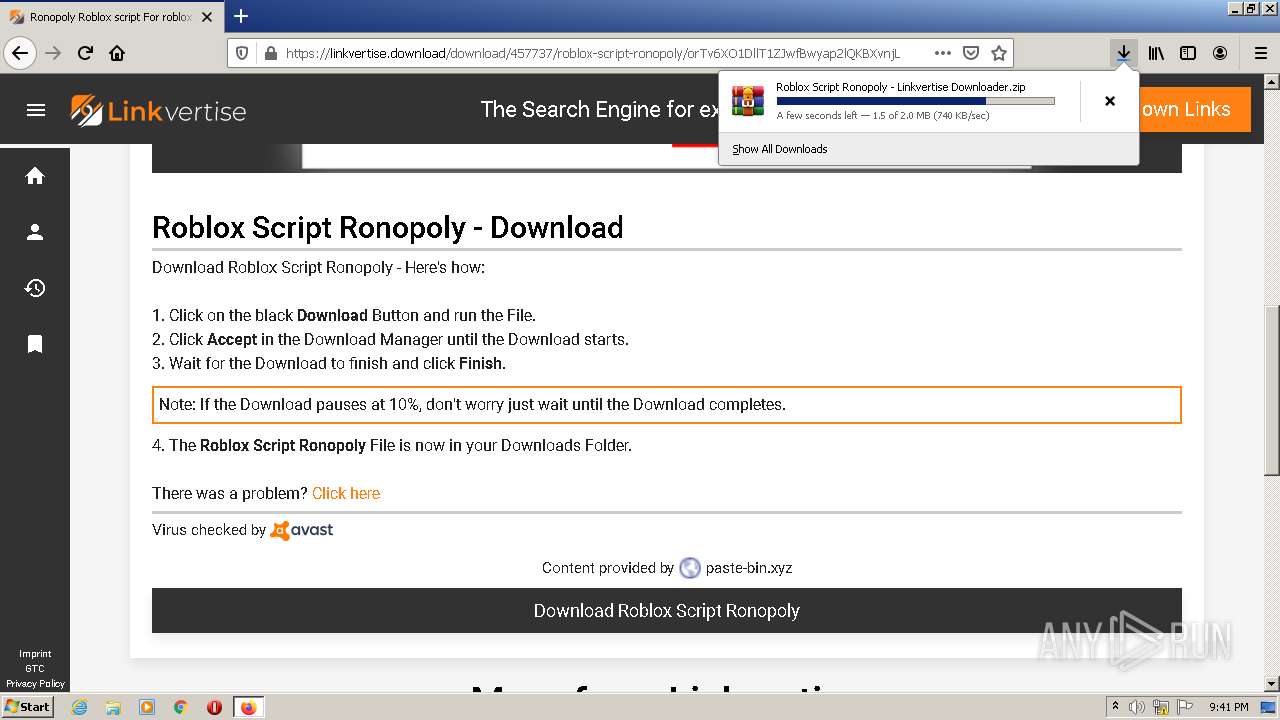
| URL: | https://linkvertise.download/download/457737/roblox-script-ronopoly/orTv6XO1DllT1ZJwfBwyap2lQKBXvnjL |
| Full analysis: | https://app.any.run/tasks/238446d2-1f9e-43b8-8916-e90582743cdf |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2022, 20:40:21 |
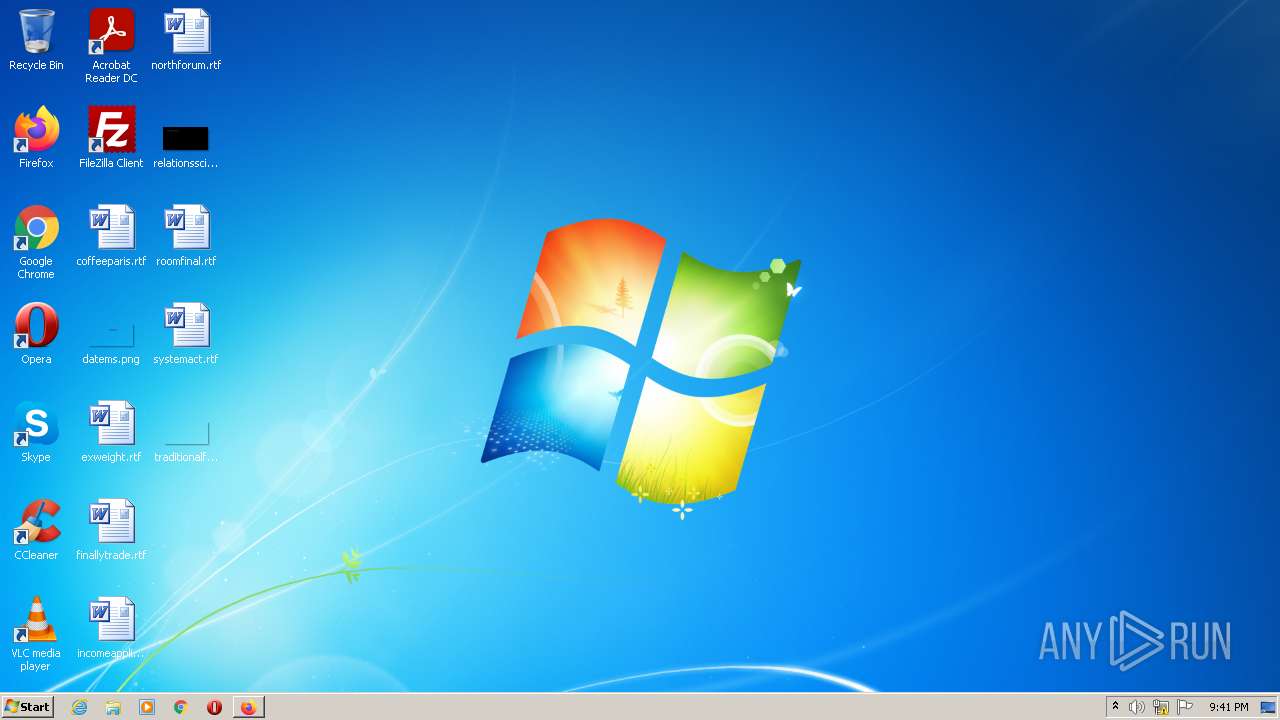
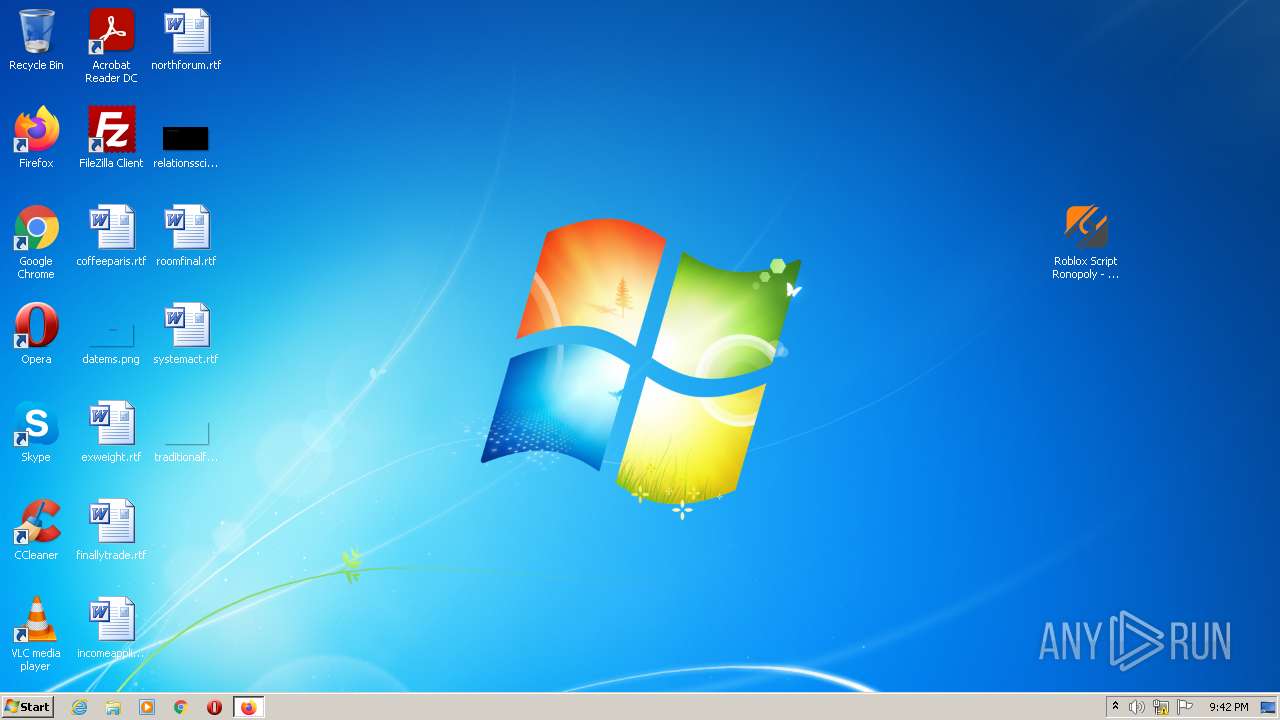
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9359AE7FF817A750411BD5C8C5772407 |
| SHA1: | DA79CCF97F271A883B879668F8519A41AFD5BADE |
| SHA256: | 7F27F083883C1919DD1D5F93324782311E2FEC9F3DEE812AE9373A013197167F |
| SSDEEP: | 3:N8MLRBXA1zKXXJkRygXKpGvPoXybLR:2MNi1zo8KpGvPoXybLR |
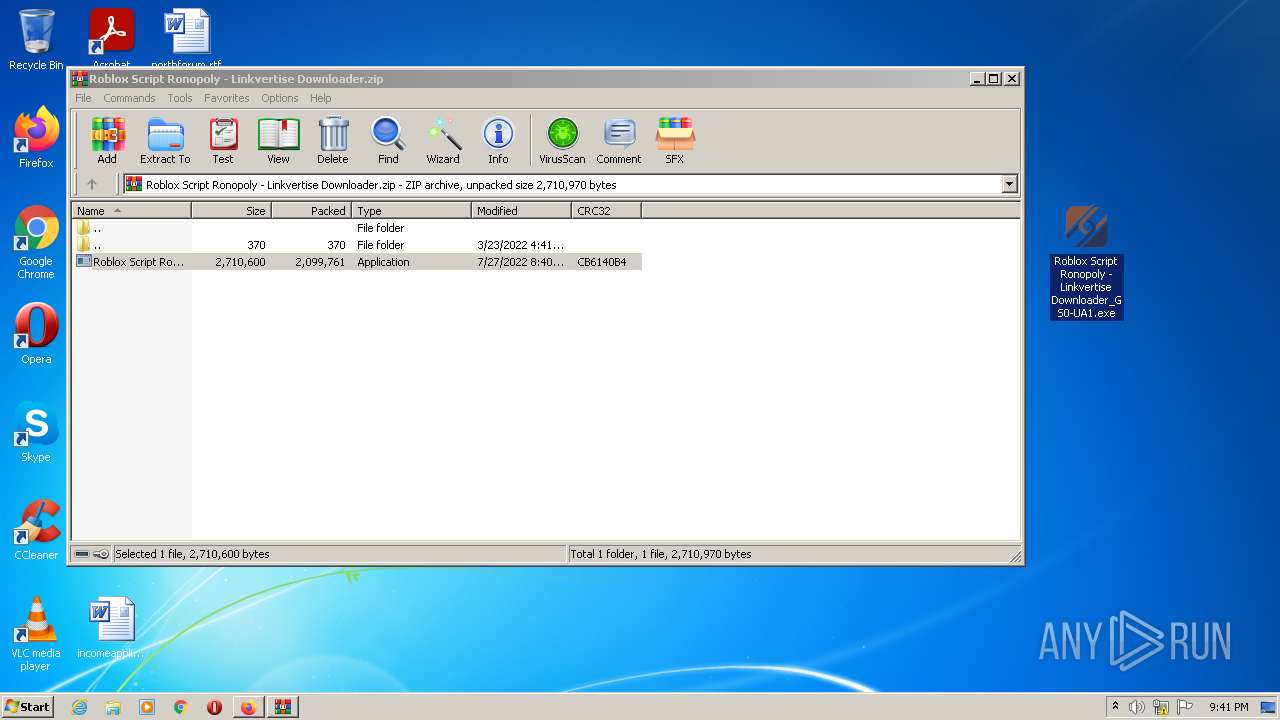
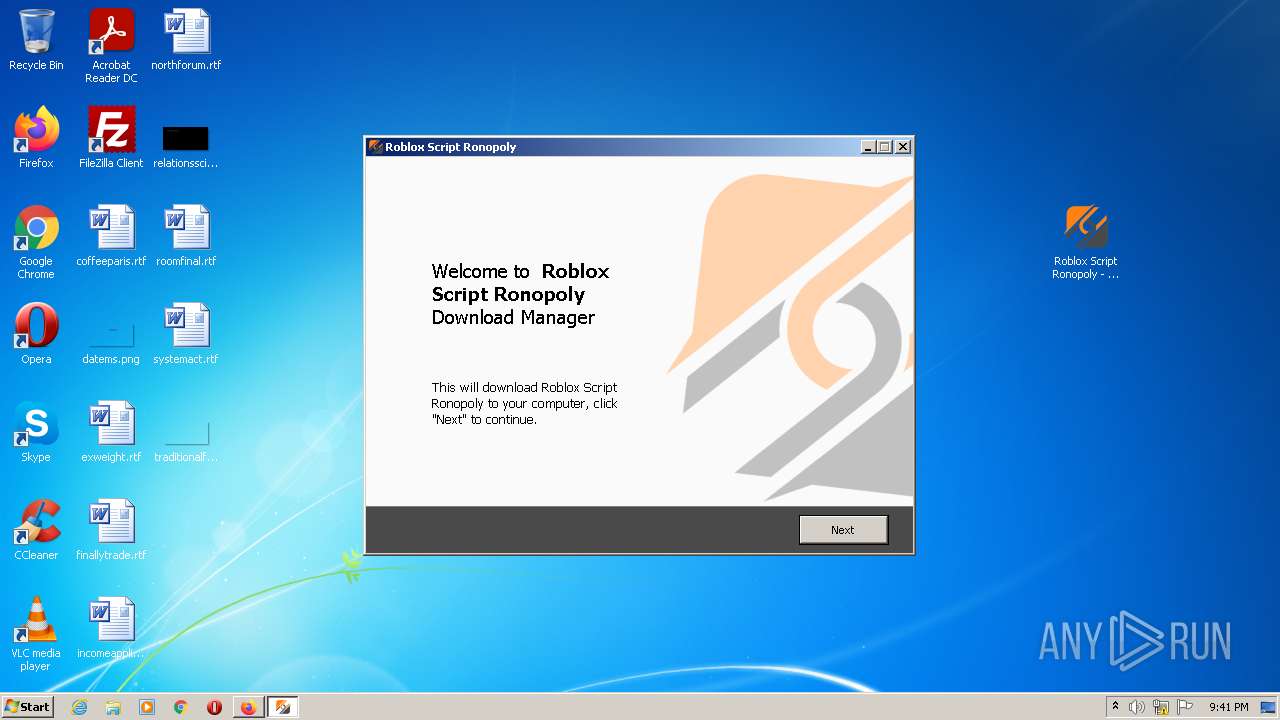
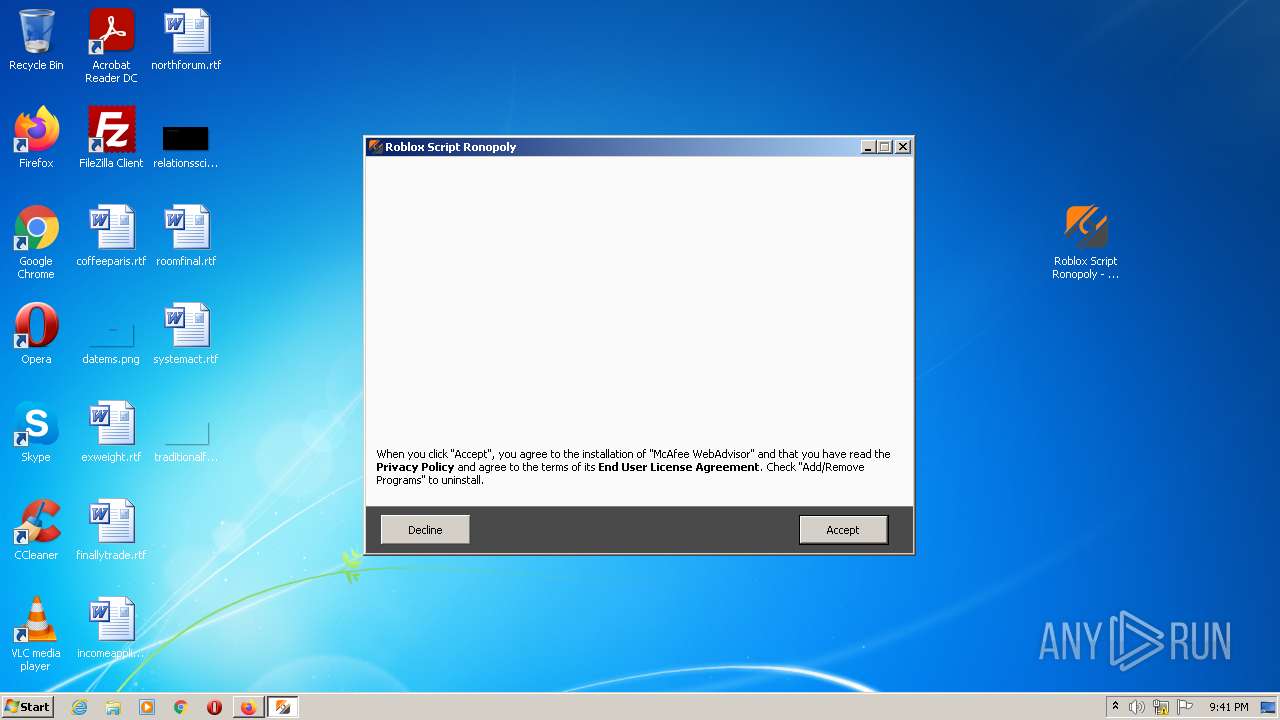
MALICIOUS
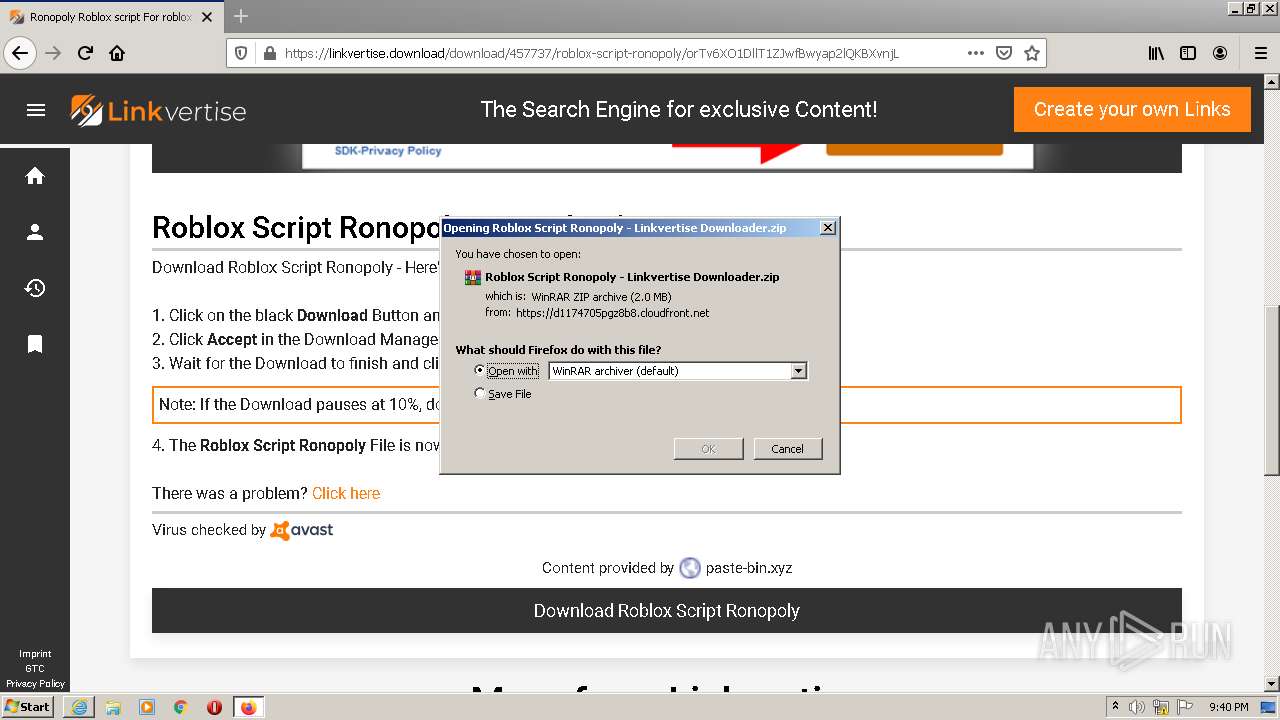
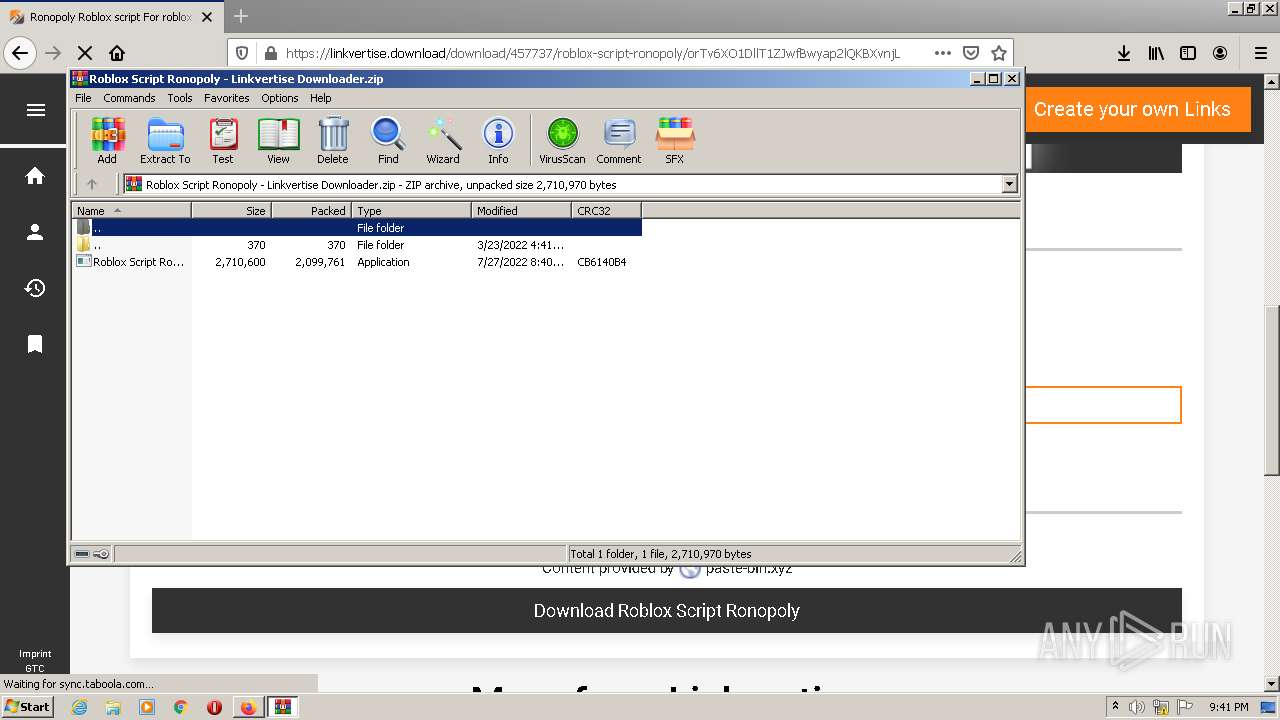
Drops executable file immediately after starts
- WinRAR.exe (PID: 3580)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2584)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2500)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
- firefox.exe (PID: 1856)
Application was dropped or rewritten from another process
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2584)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2500)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 3120)
Reads the computer name
- WinRAR.exe (PID: 3580)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 2372)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
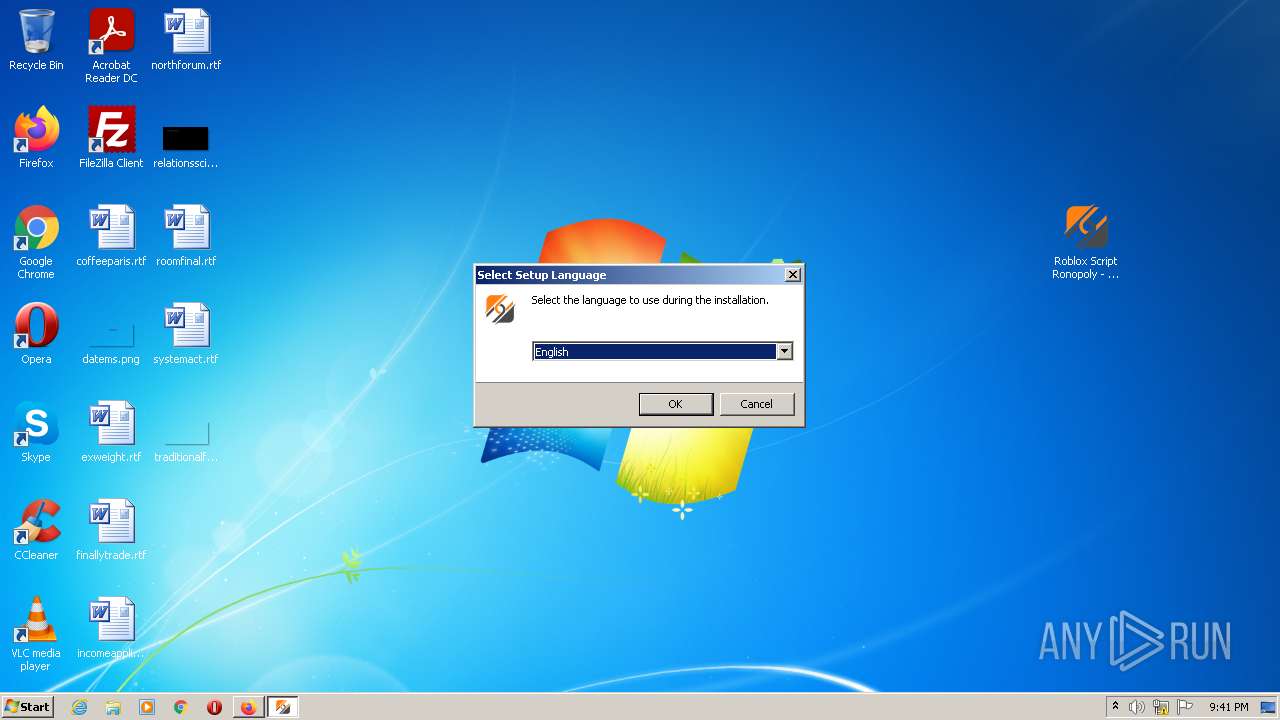
Checks supported languages
- WinRAR.exe (PID: 3580)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 2372)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2500)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2584)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3580)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2584)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2500)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
- firefox.exe (PID: 1856)
Executable content was dropped or overwritten
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2584)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2500)
- WinRAR.exe (PID: 3580)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
- firefox.exe (PID: 1856)
Reads Windows owner or organization settings
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
Reads the Windows organization settings
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
INFO
Reads the computer name
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 3264)
- firefox.exe (PID: 1856)
- firefox.exe (PID: 1824)
- firefox.exe (PID: 280)
- firefox.exe (PID: 1980)
- firefox.exe (PID: 2832)
- firefox.exe (PID: 1860)
- firefox.exe (PID: 2996)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 3120)
Checks supported languages
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2952)
- firefox.exe (PID: 2960)
- firefox.exe (PID: 1856)
- firefox.exe (PID: 1824)
- firefox.exe (PID: 280)
- firefox.exe (PID: 2832)
- firefox.exe (PID: 1980)
- firefox.exe (PID: 2996)
- firefox.exe (PID: 1860)
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 1972)
Checks Windows Trust Settings
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2952)
- firefox.exe (PID: 1856)
- iexplore.exe (PID: 3120)
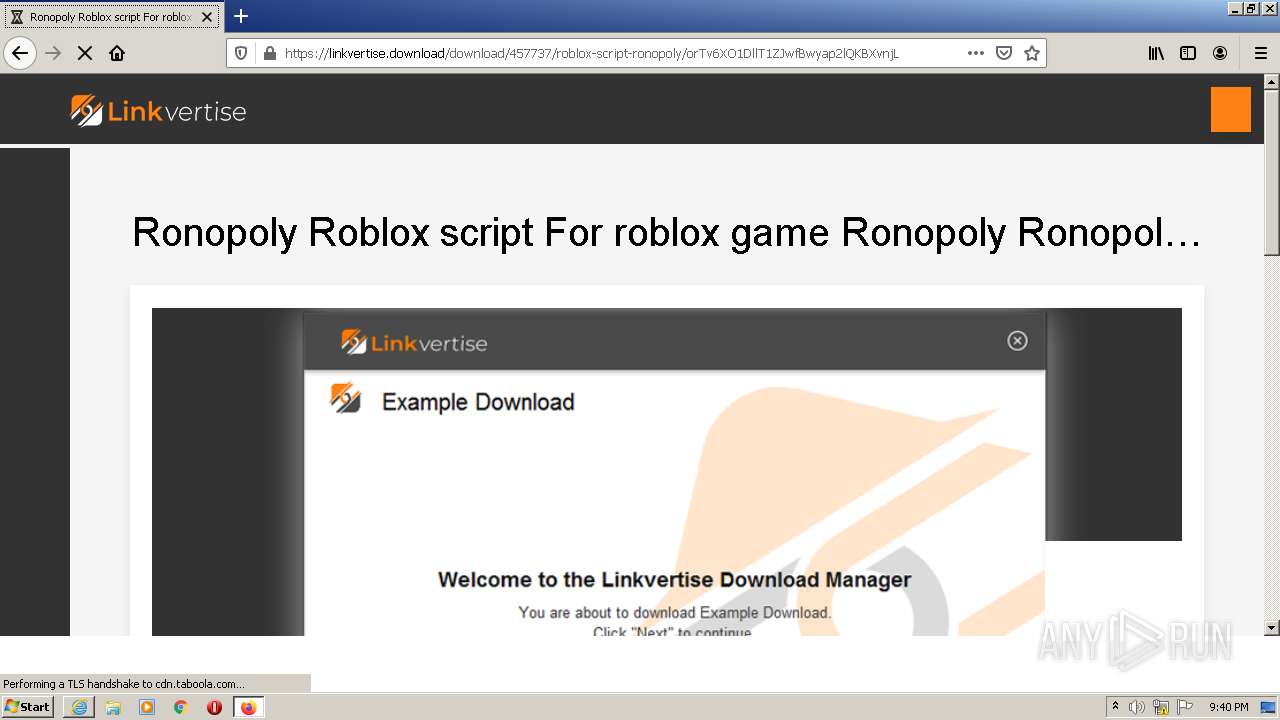
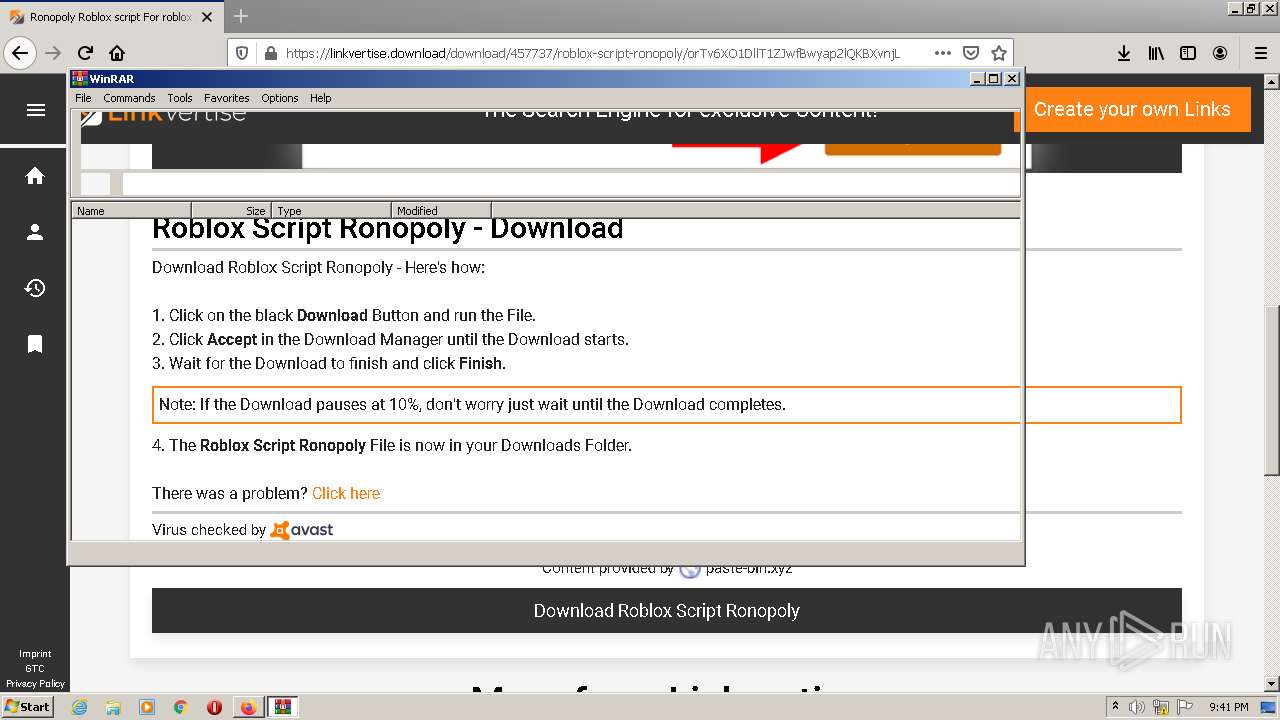
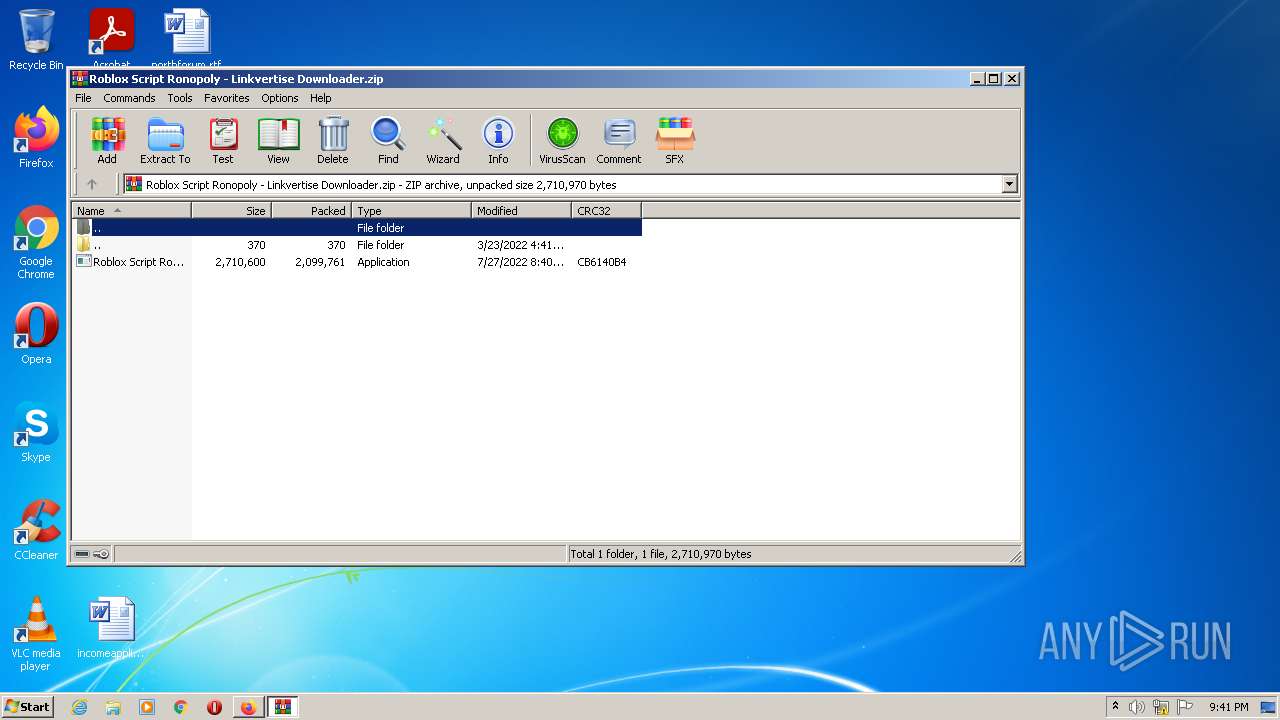
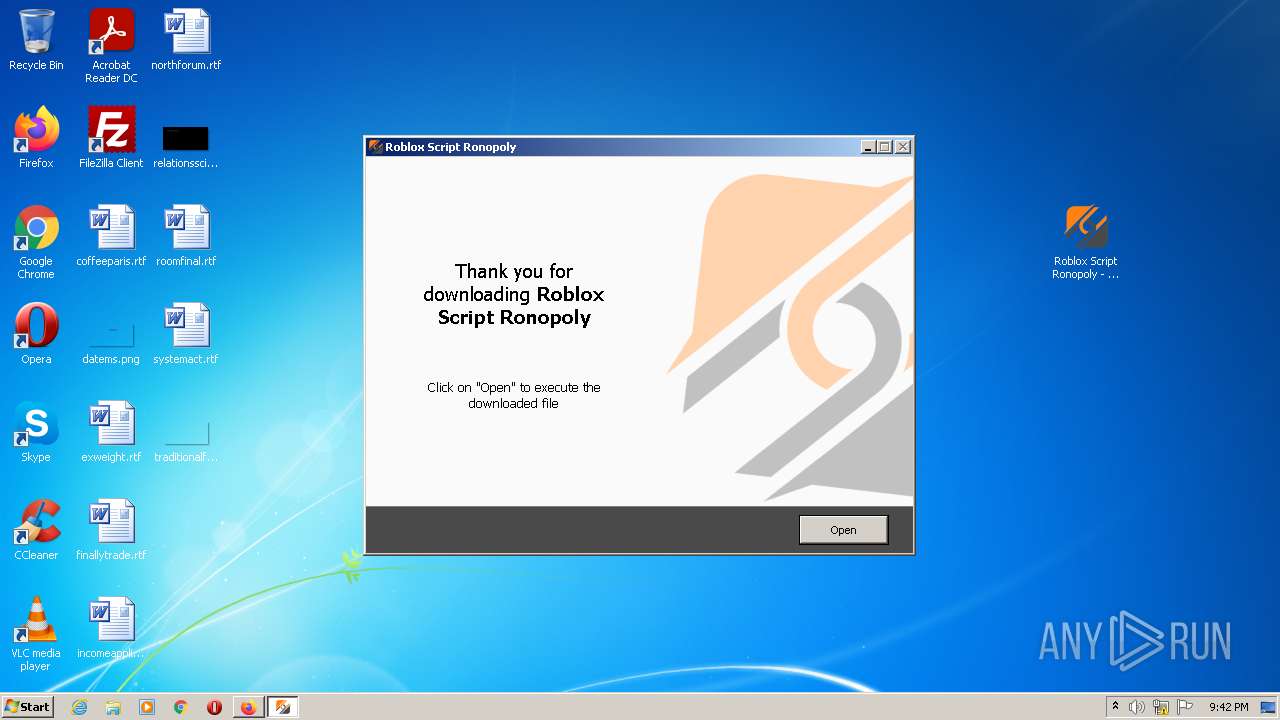
Manual execution by user
- firefox.exe (PID: 2960)
- WinRAR.exe (PID: 3580)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe (PID: 2584)
Application launched itself
- iexplore.exe (PID: 2952)
- firefox.exe (PID: 2960)
- firefox.exe (PID: 1856)
- iexplore.exe (PID: 1972)
Changes internet zones settings
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 1972)
Reads settings of System Certificates
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 2952)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
- iexplore.exe (PID: 3120)
Reads CPU info
- firefox.exe (PID: 1856)
Creates files in the program directory
- firefox.exe (PID: 1856)
Reads internet explorer settings
- iexplore.exe (PID: 3264)
- iexplore.exe (PID: 3120)
Reads the date of Windows installation
- iexplore.exe (PID: 2952)
- firefox.exe (PID: 1856)
- iexplore.exe (PID: 1972)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 1856)
Application was dropped or rewritten from another process
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 2372)
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
Loads dropped or rewritten executable
- Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp (PID: 1560)
Changes settings of System certificates
- iexplore.exe (PID: 3120)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
17
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1856.6.1225688624\704673056" -childID 1 -isForBrowser -prefsHandle 2412 -prefMapHandle 2408 -prefsLen 181 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 1856 "\\.\pipe\gecko-crash-server-pipe.1856" 2424 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Temp\is-3IM3R.tmp\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp" /SL5="$5012C,1785071,899584,C:\Users\admin\Desktop\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe" /SPAWNWND=$30186 /NOTIFYWND=$3015A | C:\Users\admin\AppData\Local\Temp\is-3IM3R.tmp\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp | Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1856.0.1438635720\460748737" -parentBuildID 20201112153044 -prefsHandle 1144 -prefMapHandle 1076 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 1856 "\\.\pipe\gecko-crash-server-pipe.1856" 1256 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1856.13.1229552924\19057936" -childID 2 -isForBrowser -prefsHandle 3132 -prefMapHandle 3124 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 1856 "\\.\pipe\gecko-crash-server-pipe.1856" 3144 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
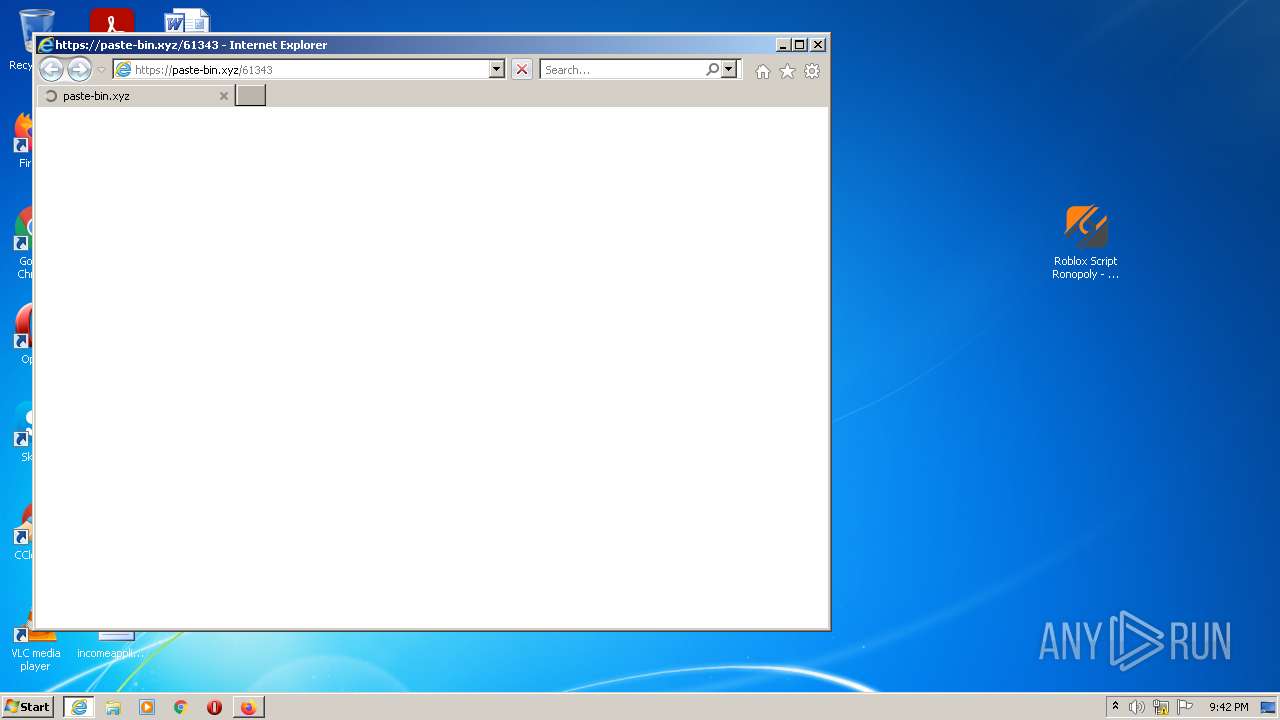
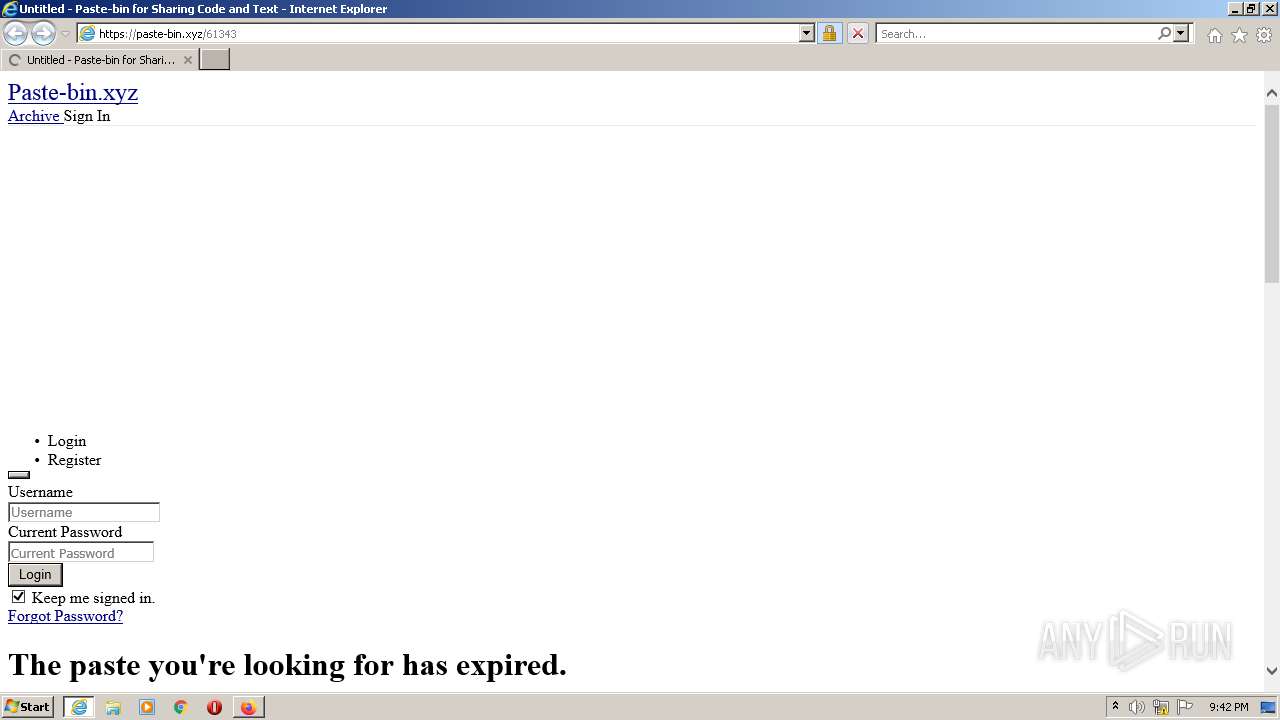
| 1972 | "C:\Program Files\Internet Explorer\iexplore.exe" https://paste-bin.xyz/61343 | C:\Program Files\Internet Explorer\iexplore.exe | — | Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1856.34.91666485\84114564" -childID 5 -isForBrowser -prefsHandle 4144 -prefMapHandle 4140 -prefsLen 7470 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 1856 "\\.\pipe\gecko-crash-server-pipe.1856" 4160 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2372 | "C:\Users\admin\AppData\Local\Temp\is-9ICAU.tmp\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp" /SL5="$3015A,1785071,899584,C:\Users\admin\Desktop\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe" | C:\Users\admin\AppData\Local\Temp\is-9ICAU.tmp\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp | — | Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\Desktop\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe" /SPAWNWND=$30186 /NOTIFYWND=$3015A | C:\Users\admin\Desktop\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe | Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Linkvertise GmbH & Co. KG Exit code: 0 Version: 2.0.0.13 Modules
| |||||||||||||||
| 2584 | "C:\Users\admin\Desktop\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe" | C:\Users\admin\Desktop\Roblox Script Ronopoly - Linkvertise Downloader_GS0-UA1.exe | Explorer.EXE | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Linkvertise GmbH & Co. KG Exit code: 0 Version: 2.0.0.13 Modules
| |||||||||||||||
Total events
41 977
Read events
41 640
Write events
329
Delete events
8
Modification events
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 429701728 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30974457 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 729857978 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30974457 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
9
Suspicious files
222
Text files
132
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1856 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3264 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3264 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 1856 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1856 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_M9DZqriEDKleGrG | binary | |
MD5:— | SHA256:— | |||
| 1856 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_IoKbP0tZwufi3Xl | binary | |
MD5:— | SHA256:— | |||
| 1856 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1856 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
| 3264 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1856 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
208
DNS requests
298
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1856 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
1856 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3264 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
1856 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
1856 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 278 b | whitelisted |
1856 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1856 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
1856 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
1856 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
1856 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | iexplore.exe | 172.67.195.136:443 | linkvertise.download | — | US | suspicious |
3264 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
2952 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2952 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3264 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1856 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
1856 | firefox.exe | 52.222.214.84:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | suspicious |
1856 | firefox.exe | 44.241.228.251:443 | location.services.mozilla.com | University of California, San Diego | US | unknown |
1856 | firefox.exe | 18.66.139.125:443 | content-signature-2.cdn.mozilla.net | Massachusetts Institute of Technology | US | malicious |
1856 | firefox.exe | 142.250.181.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
linkvertise.download |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1856 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1856 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1856 | firefox.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1856 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1856 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |