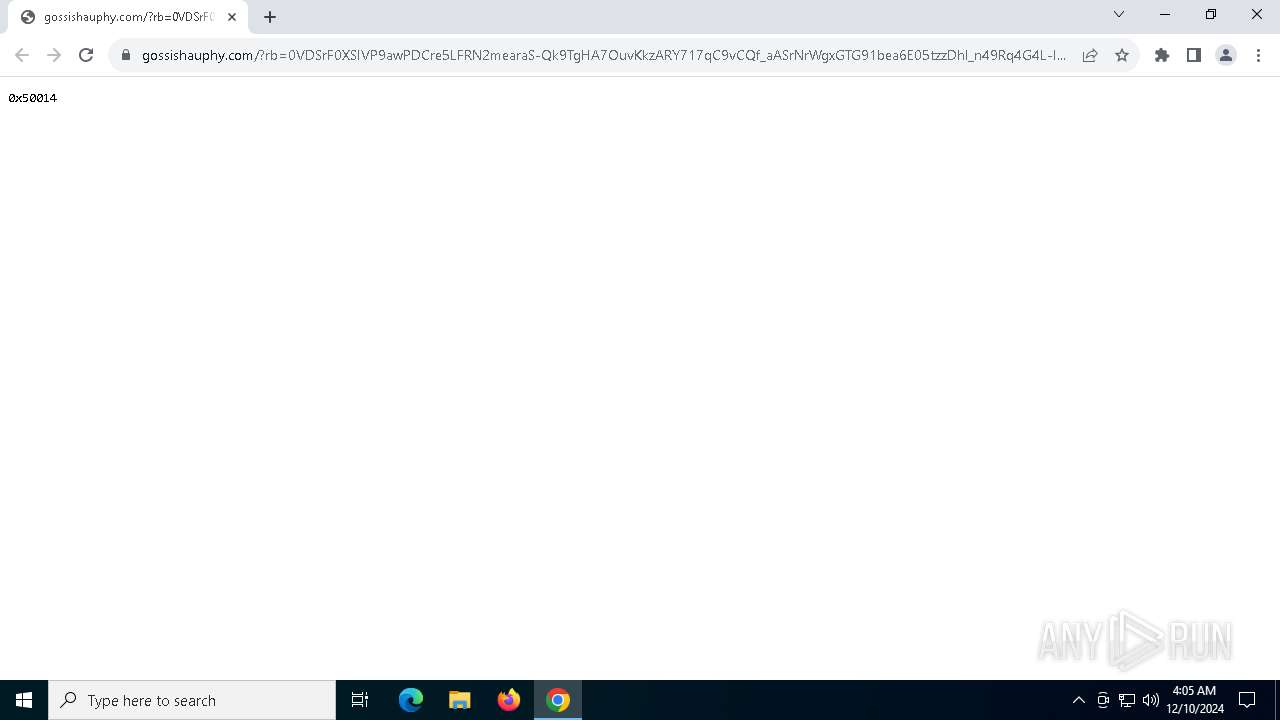
| URL: | https://gossishauphy.com/?rb=0VDSrF0XSIVP9awPDCre5LFRN2mearaS-Qk9TgHA7OuvKkzARY717qC9vCQf_aASrNrWgxGTG91bea6E05tzzDhl_n49Rq4G4L-IN7gXW-znvMrDhSGJ0yytHoNwQBnZjCJJ5qcygy4r_HpUk7rENrHMKupoOBKKtGLlRmeeMVoHg4Ni9VGUMBj3caZt-M0p0y--Svcs0nMY65rpJqG_94Nek9V3O_dzusAmnTBcHy00pqTn1wwaCJ5Zp_6J31yURUPNpAS2Mym2_s4lzcdY1cmHRSglGs5EPefXVHXukgohEXfVDU65-br_zngFbblz2JuwzoYntVjKrIJdEiXlYFPkFcY%3D&request_ab2=0&zoneid=7307286&js_build=iclick-v1.1021.1&jsp=1&fs=0&cf=0&sw=810&sh=1080&wih=771&wiw=1080&ww=1080&wh=810&sah=810&wx=0&wy=0&cw=1080&wfc=1&pl=https%3A%2F%2Ftwstalker.com%2Felonmusk&drf=https%3A%2F%2Ftwstalker.com%2F&np=1&pt=0&nb=1&ng=1&ix=0&nw=1&tb=true&btz=Asia%2FTokyo&bto=-540&tt=3&wgl=Apple%20GPU&js_build=iclick-v1.1021.1&navlng=ja&vsbl=true&pnt=0&pnrc=0&wasm=1&bs=ec6be717-3a90-45fb-98b2-5f9368dc48b8&userId=08012e275083402afaf6efdfa18d65d0&uac=-1&fallback=disabled-by-server |
| Full analysis: | https://app.any.run/tasks/c3341e75-b6b6-401a-adb0-b8af19374e76 |
| Verdict: | Malicious activity |
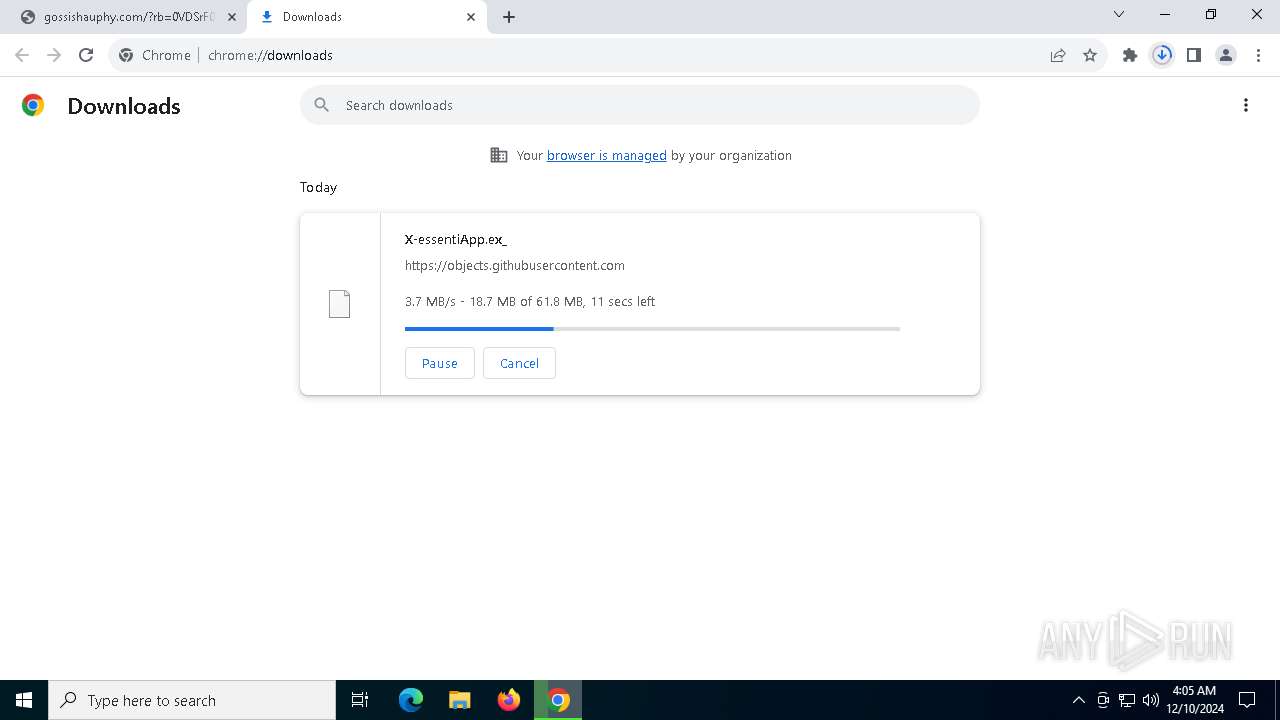
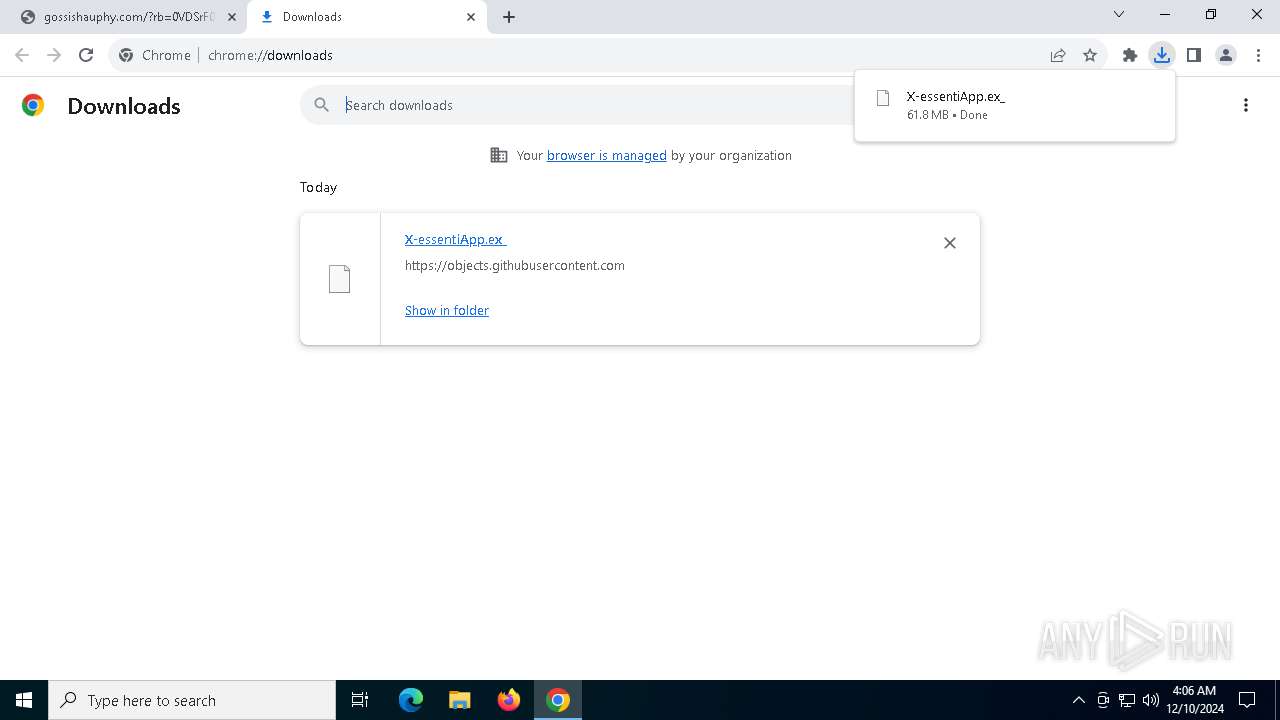
| Analysis date: | December 10, 2024, 04:05:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0743F1DD2BE704882CF26D2FF3914622 |
| SHA1: | 757CDE9E455261408133972C38A4EA3303AFCC12 |
| SHA256: | 7F19D4E473057AC141E513BF268E2AF7C929B21FFA46EB0E8819435A378034E2 |
| SSDEEP: | 24:2a8/ISJtmsFnavxweBSdQ+hpBoTU5x2HCldJGlzdlqCmaCVJ:kTdxGSdQSz2ildJG7lfmaCVJ |
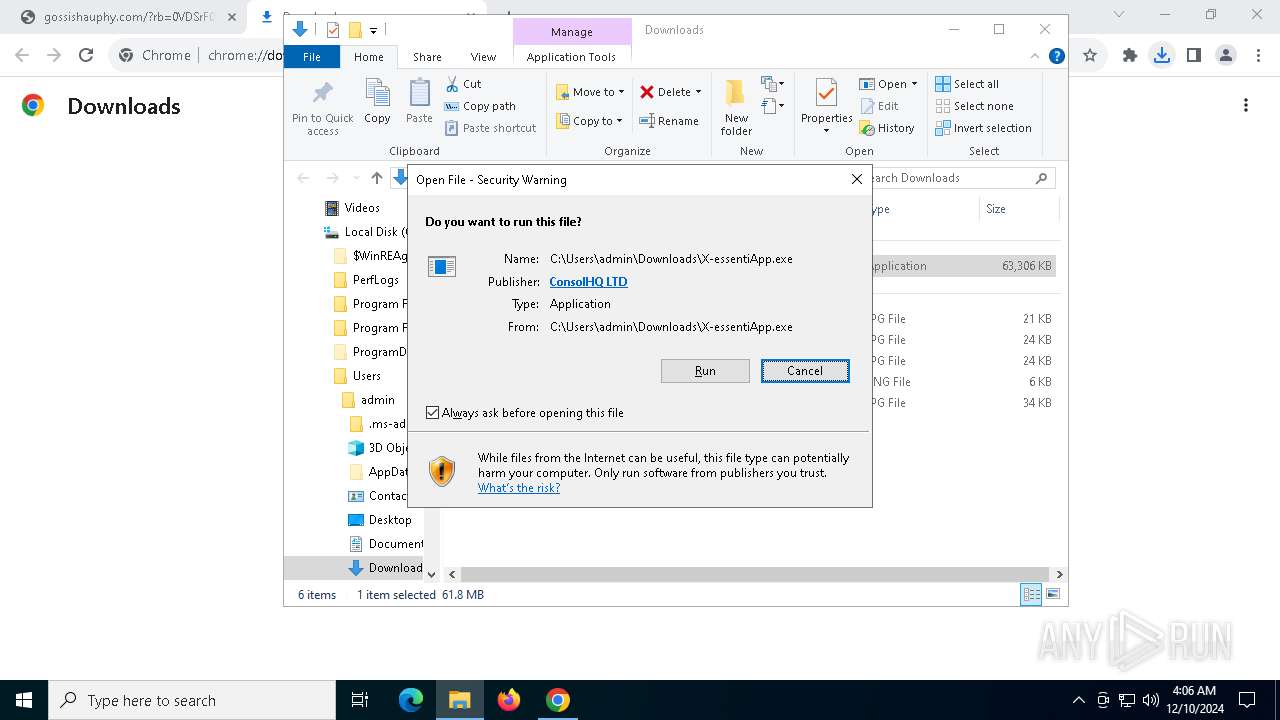
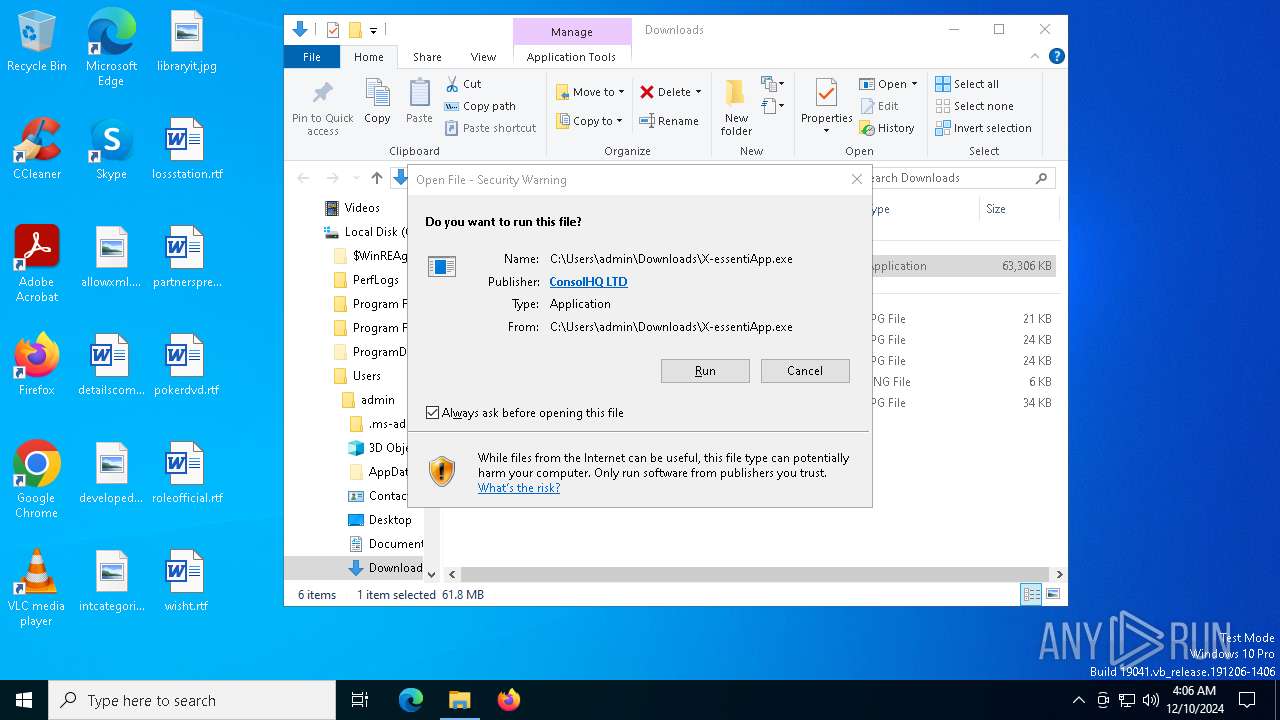
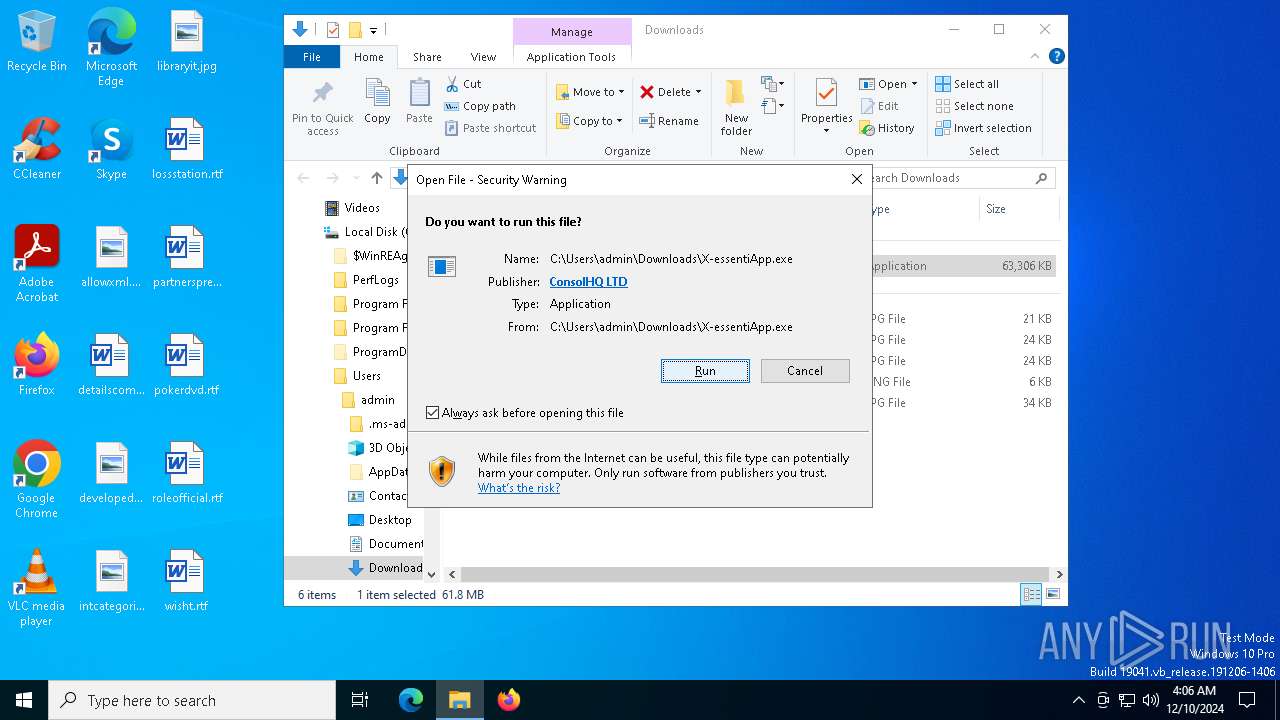
MALICIOUS
Executing a file with an untrusted certificate
- X-essentiApp.exe (PID: 2680)
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 4488)
Malware-specific behavior (creating "System.dll" in Temp)
- X-essentiApp.exe (PID: 2680)
The process creates files with name similar to system file names
- X-essentiApp.exe (PID: 2680)
Executable content was dropped or overwritten
- X-essentiApp.exe (PID: 2680)
Drops 7-zip archiver for unpacking
- X-essentiApp.exe (PID: 2680)
Process drops legitimate windows executable
- X-essentiApp.exe (PID: 2680)
Reads security settings of Internet Explorer
- X-essentiApp.exe (PID: 2680)
Starts CMD.EXE for commands execution
- IoNixNginx.exe (PID: 628)
Application launched itself
- IoNixNginx.exe (PID: 628)
Starts application with an unusual extension
- cmd.exe (PID: 6984)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
- IoNixNginx.exe (PID: 628)
- IoNixNginx.exe (PID: 4548)
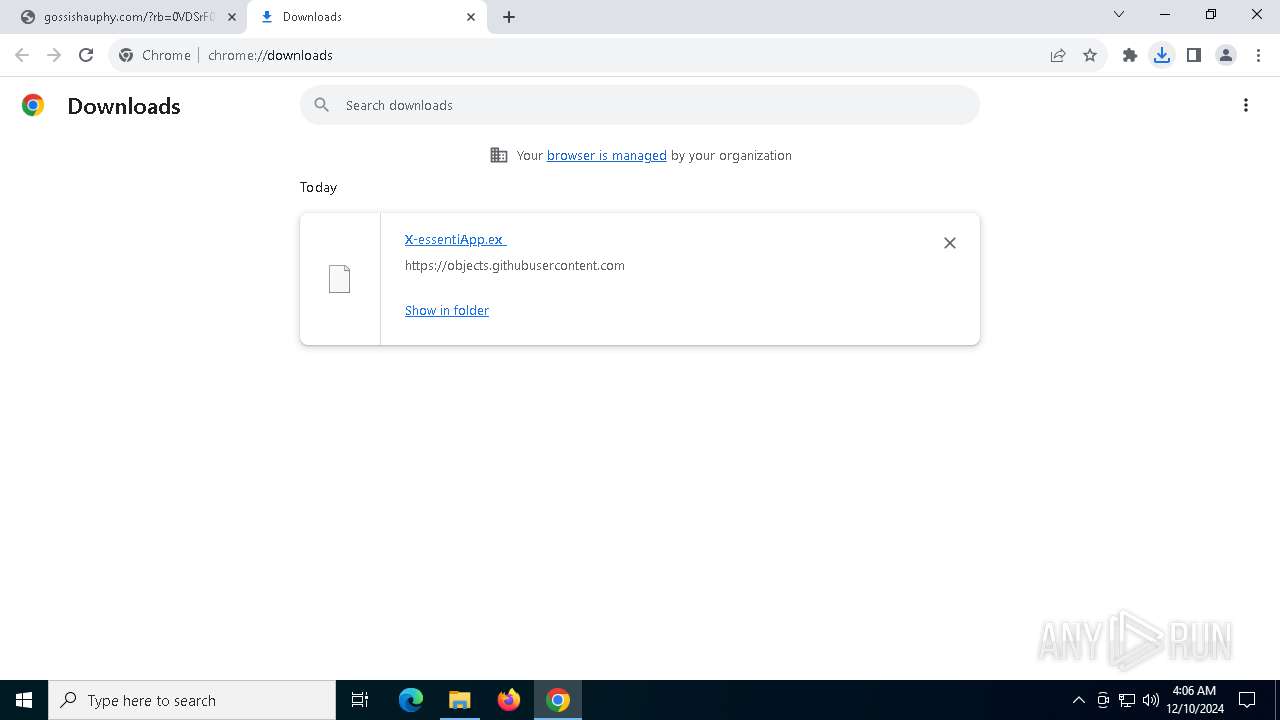
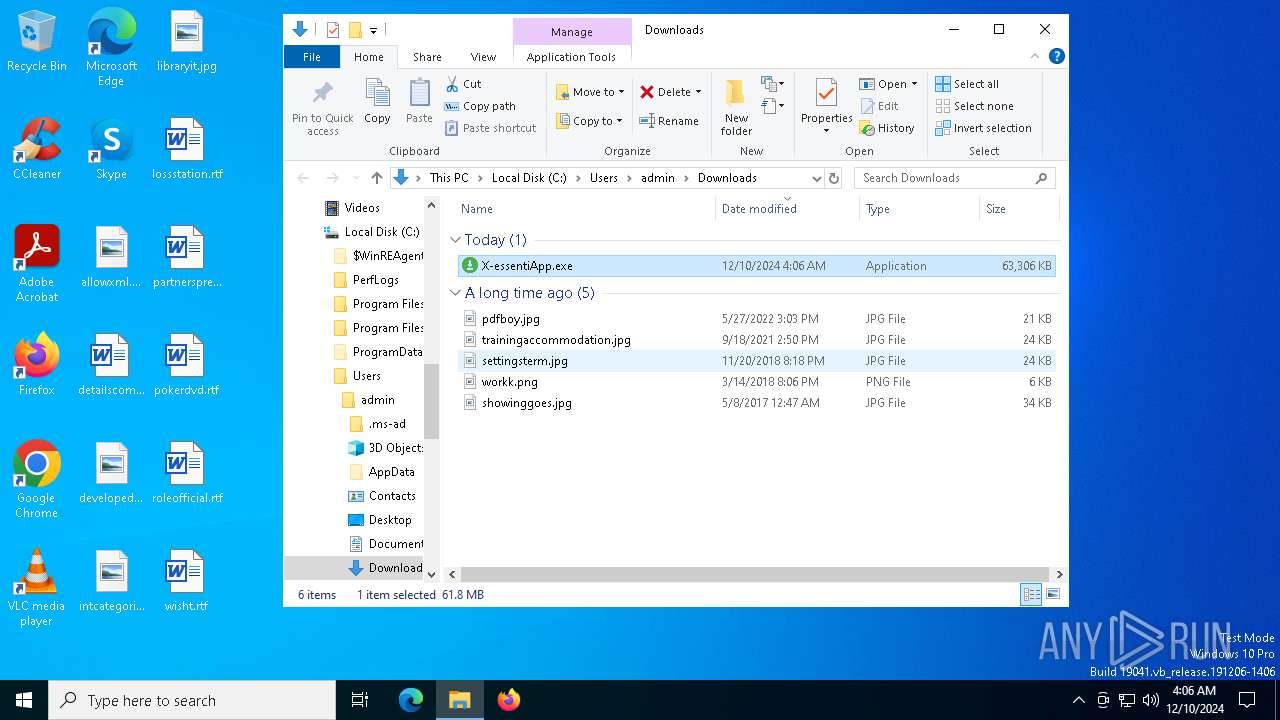
The process uses the downloaded file
- chrome.exe (PID: 4384)
- explorer.exe (PID: 4488)
Executable content was dropped or overwritten
- chrome.exe (PID: 5268)
Checks supported languages
- X-essentiApp.exe (PID: 2680)
- IoNixNginx.exe (PID: 628)
- IoNixNginx.exe (PID: 6868)
- chcp.com (PID: 6772)
- IoNixNginx.exe (PID: 6844)
- IoNixNginx.exe (PID: 4548)
Application launched itself
- chrome.exe (PID: 5268)
Checks proxy server information
- explorer.exe (PID: 4488)
- IoNixNginx.exe (PID: 628)
Reads the software policy settings
- explorer.exe (PID: 4488)
Reads the computer name
- X-essentiApp.exe (PID: 2680)
- IoNixNginx.exe (PID: 628)
- IoNixNginx.exe (PID: 6844)
- IoNixNginx.exe (PID: 6868)
- IoNixNginx.exe (PID: 4548)
Create files in a temporary directory
- X-essentiApp.exe (PID: 2680)
Reads product name
- IoNixNginx.exe (PID: 628)
Node.js compiler has been detected
- IoNixNginx.exe (PID: 628)
- IoNixNginx.exe (PID: 6844)
- IoNixNginx.exe (PID: 6868)
Reads Environment values
- IoNixNginx.exe (PID: 628)
Changes the display of characters in the console
- cmd.exe (PID: 6984)
Reads the machine GUID from the registry
- IoNixNginx.exe (PID: 628)
- IoNixNginx.exe (PID: 4548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
22
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | C:\Users\admin\AppData\Local\Temp\2pvtPES5t7aoV3eXnWrywytFi10\IoNixNginx.exe | C:\Users\admin\AppData\Local\Temp\2pvtPES5t7aoV3eXnWrywytFi10\IoNixNginx.exe | X-essentiApp.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: IoNixNginx Version: 3.5.5 Modules
| |||||||||||||||
| 936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5228 --field-trial-handle=1864,i,14596275810684352600,1446773619924077877,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
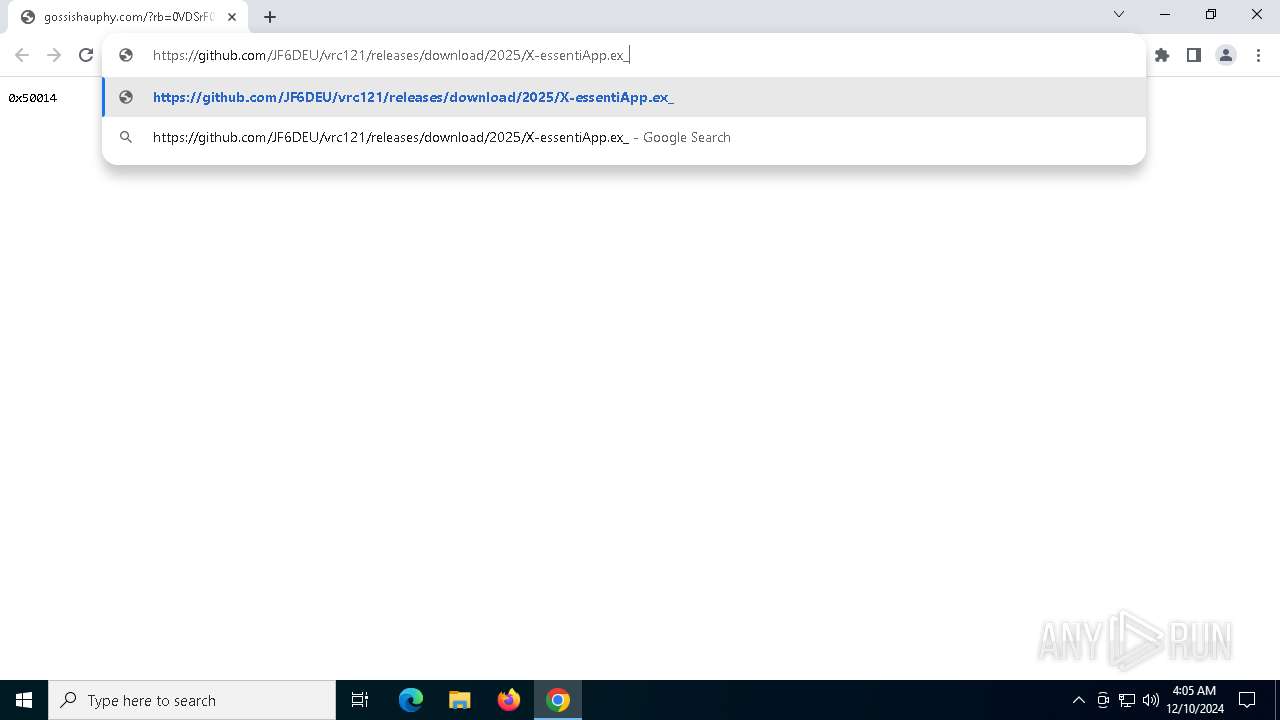
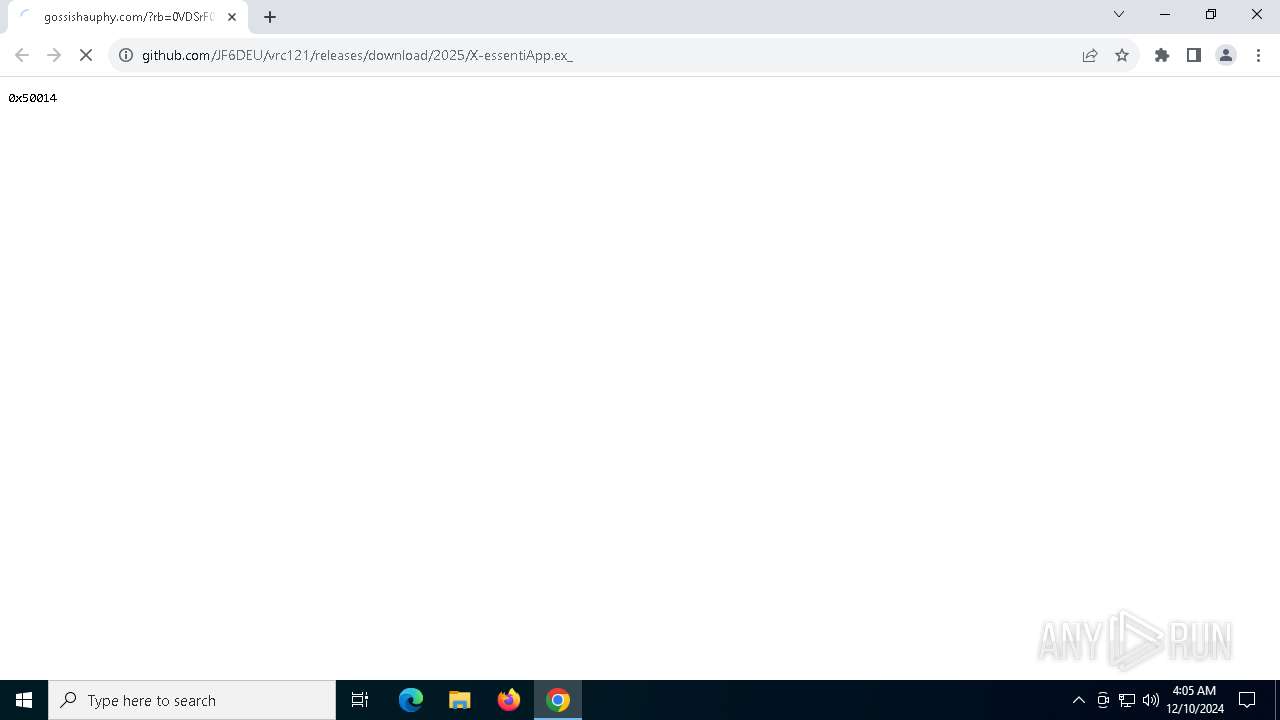
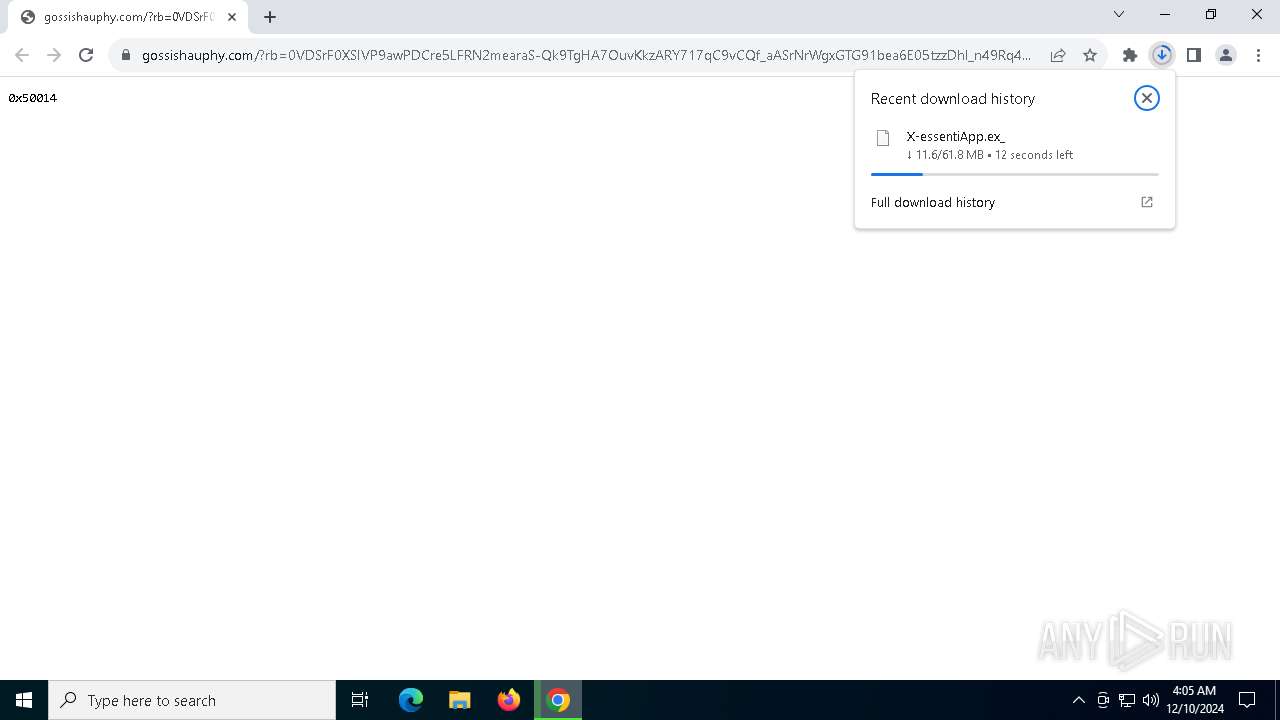
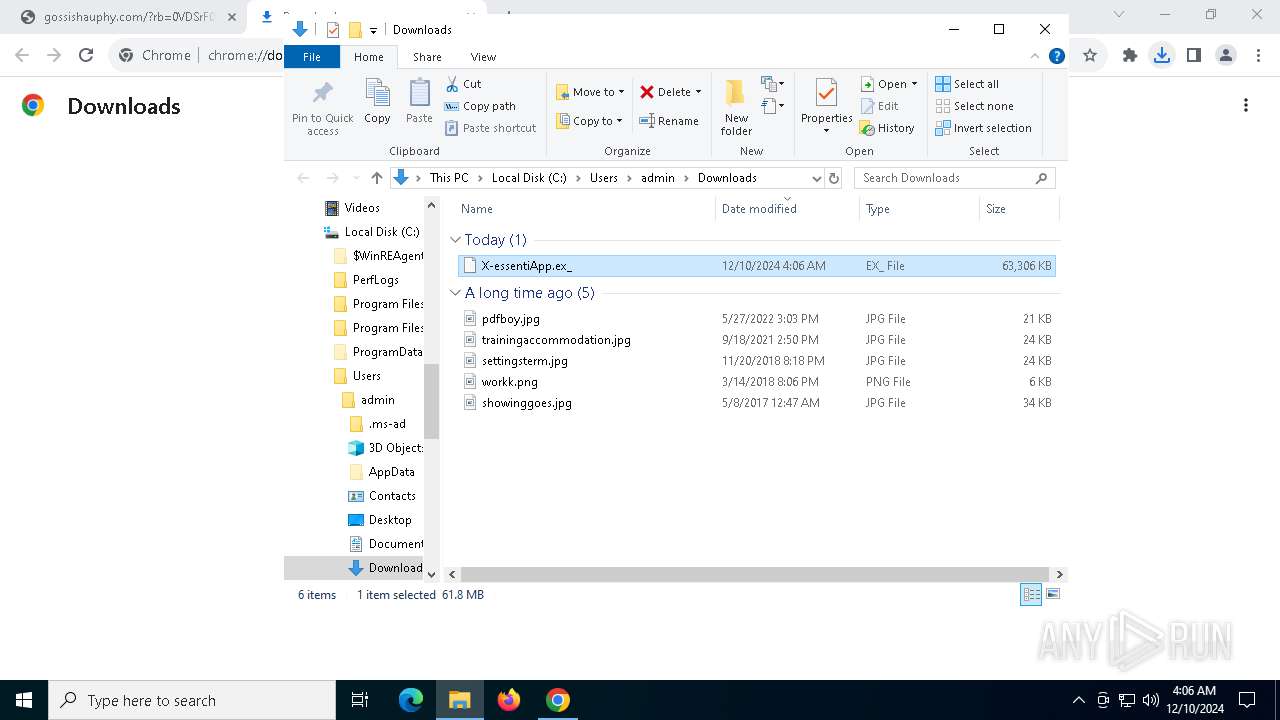
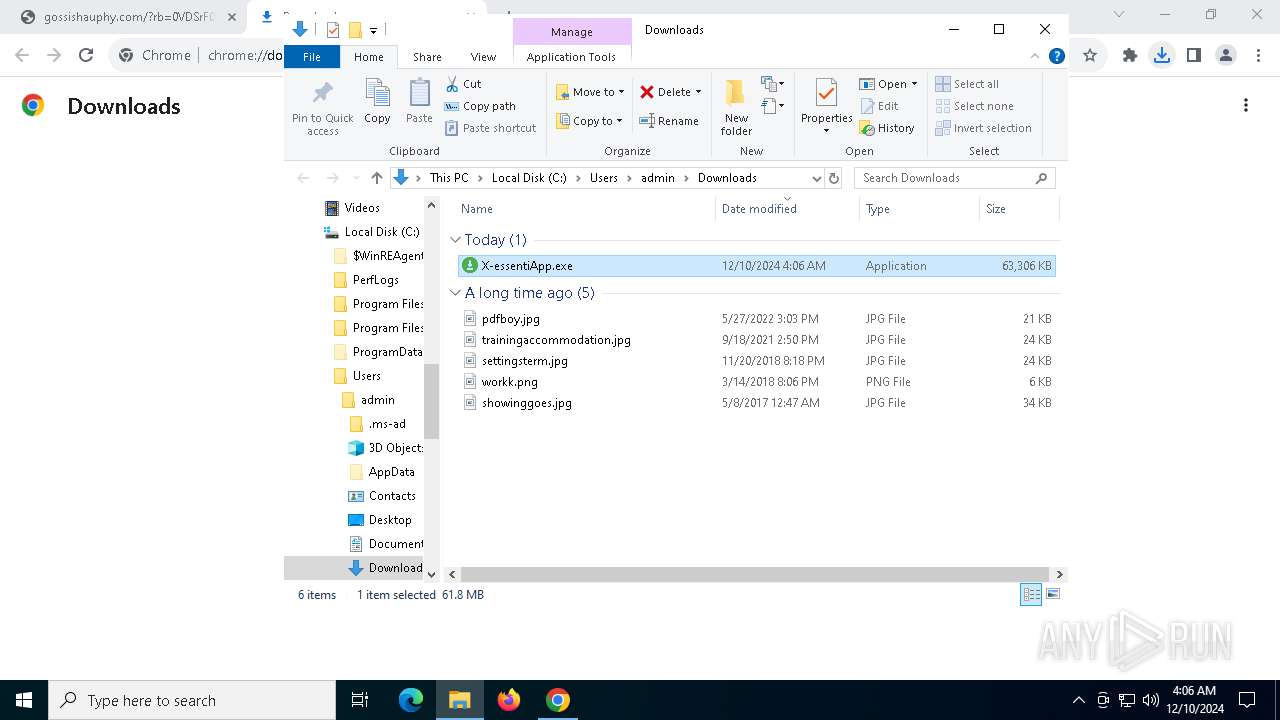
| 2680 | "C:\Users\admin\Downloads\X-essentiApp.exe" | C:\Users\admin\Downloads\X-essentiApp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 3.5.5 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5172 --field-trial-handle=1864,i,14596275810684352600,1446773619924077877,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5560 --field-trial-handle=1864,i,14596275810684352600,1446773619924077877,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4488 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4548 | "C:\Users\admin\AppData\Local\Temp\2pvtPES5t7aoV3eXnWrywytFi10\IoNixNginx.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --user-data-dir="C:\Users\admin\AppData\Roaming\hgekorcpiasneymc" --gpu-preferences=UAAAAAAAAADoAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAACQAAAAAAAAAAAAAAAAAAAAAAAAABgAAAAAAAAAGAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=2580 --field-trial-handle=1932,i,714159736268029785,16553366501463995694,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2pvtPES5t7aoV3eXnWrywytFi10\IoNixNginx.exe | — | IoNixNginx.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: IoNixNginx Exit code: 0 Version: 3.5.5 Modules
| |||||||||||||||
| 4704 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://gossishauphy.com/?rb=0VDSrF0XSIVP9awPDCre5LFRN2mearaS-Qk9TgHA7OuvKkzARY717qC9vCQf_aASrNrWgxGTG91bea6E05tzzDhl_n49Rq4G4L-IN7gXW-znvMrDhSGJ0yytHoNwQBnZjCJJ5qcygy4r_HpUk7rENrHMKupoOBKKtGLlRmeeMVoHg4Ni9VGUMBj3caZt-M0p0y--Svcs0nMY65rpJqG_94Nek9V3O_dzusAmnTBcHy00pqTn1wwaCJ5Zp_6J31yURUPNpAS2Mym2_s4lzcdY1cmHRSglGs5EPefXVHXukgohEXfVDU65-br_zngFbblz2JuwzoYntVjKrIJdEiXlYFPkFcY%3D&request_ab2=0&zoneid=7307286&js_build=iclick-v1.1021.1&jsp=1&fs=0&cf=0&sw=810&sh=1080&wih=771&wiw=1080&ww=1080&wh=810&sah=810&wx=0&wy=0&cw=1080&wfc=1&pl=https%3A%2F%2Ftwstalker.com%2Felonmusk&drf=https%3A%2F%2Ftwstalker.com%2F&np=1&pt=0&nb=1&ng=1&ix=0&nw=1&tb=true&btz=Asia%2FTokyo&bto=-540&tt=3&wgl=Apple%20GPU&js_build=iclick-v1.1021.1&navlng=ja&vsbl=true&pnt=0&pnrc=0&wasm=1&bs=ec6be717-3a90-45fb-98b2-5f9368dc48b8&userId=08012e275083402afaf6efdfa18d65d0&uac=-1&fallback=disabled-by-server" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
26 878
Read events
26 842
Write events
34
Delete events
2
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000402EC |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | Chrome |
Value: 6 | |||
| (PID) Process: | (5268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5268) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (4384) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000427CD1D2B84ADB01 | |||
Executable files
19
Suspicious files
190
Text files
32
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135de2.TMP | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135de2.TMP | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135de2.TMP | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135df2.TMP | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135de2.TMP | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135df2.TMP | — | |
MD5:— | SHA256:— | |||
| 5268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
177
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4536 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7140 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4536 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7140 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 100.24.223.135:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEDDWyDpxW92zLnlW%2FlLWs1I%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5340 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6520 | chrome.exe | 139.45.197.244:443 | gossishauphy.com | RETN Limited | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
gossishauphy.com |
| unknown |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |