| download: | index.html |
| Full analysis: | https://app.any.run/tasks/36ae9fde-8348-4612-b9bd-10405cec31a7 |
| Verdict: | Malicious activity |
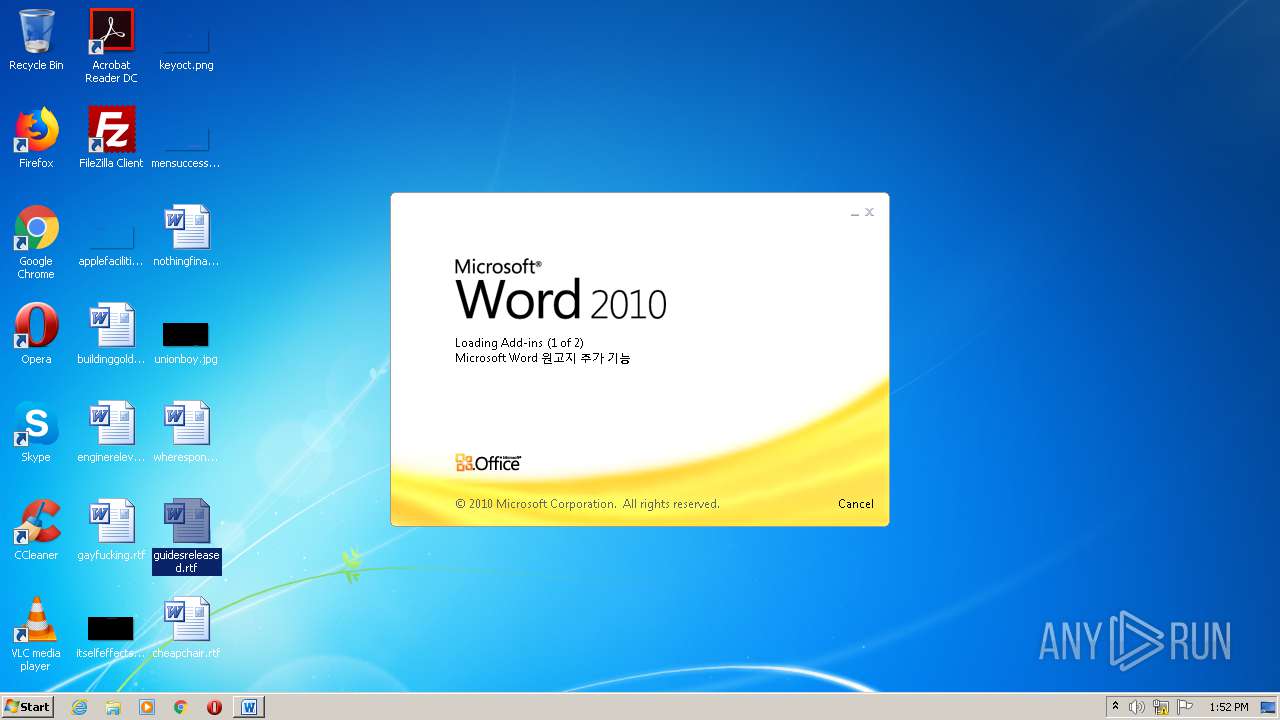
| Analysis date: | October 20, 2020, 12:52:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with no line terminators |
| MD5: | D0AD6CAE60756CA042D86D1C5F45AACD |
| SHA1: | F989D370116DF3BAC08D196DF9C18CC07B35E48A |
| SHA256: | 7F0AE41514116F6EC6F0FE975E620A0E948239360C0D436F30598478BAEDC19A |
| SSDEEP: | 24:haHkJ0HPatnvSi9uts/8RWJrSu1+BlRWUICgqzH4JEuYqY5S0I/fNHS0IZyMeFHq:WP6vJIwJrDywUIGzx5SP/FHSPXeFHq |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2452)
- iexplore.exe (PID: 2908)
Application launched itself
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 2452)
Reads settings of System Certificates
- iexplore.exe (PID: 2452)
Reads internet explorer settings
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 2908)
Changes settings of System certificates
- iexplore.exe (PID: 2452)
Creates files in the user directory
- iexplore.exe (PID: 2452)
- WINWORD.EXE (PID: 2168)
Manual execution by user
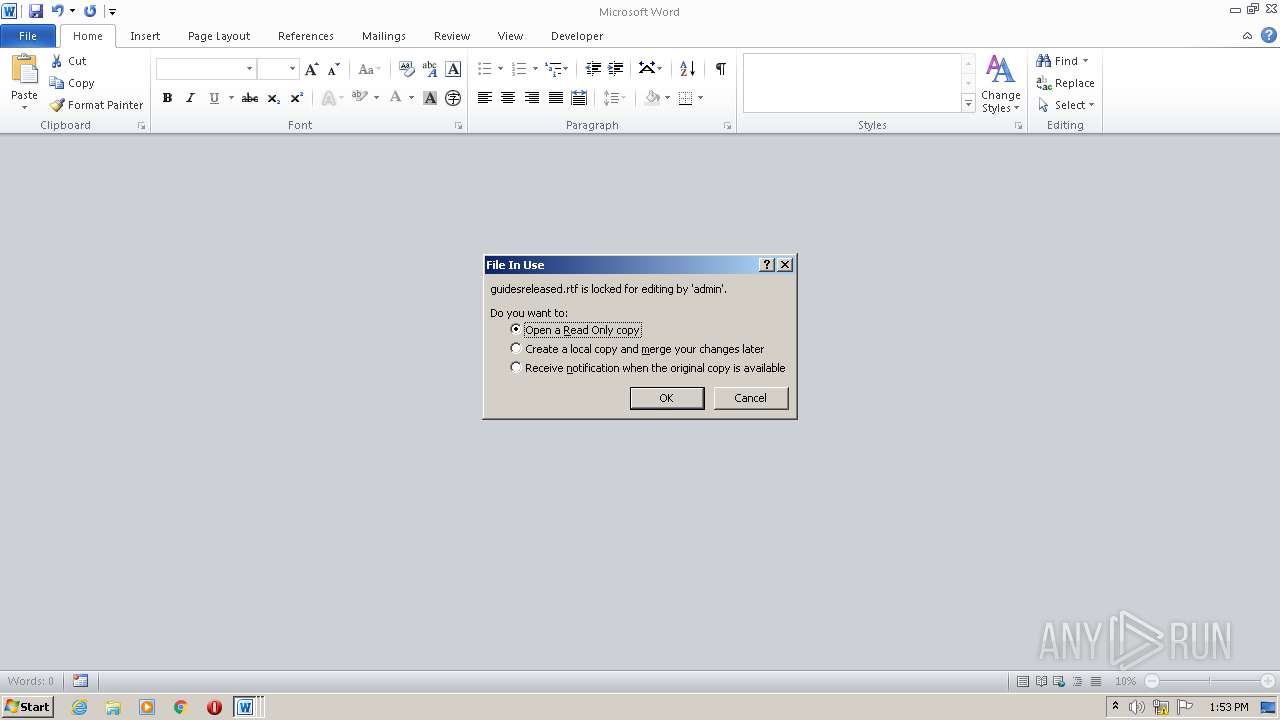
- WINWORD.EXE (PID: 3176)
- WINWORD.EXE (PID: 2292)
- WINWORD.EXE (PID: 2168)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3176)
- WINWORD.EXE (PID: 2168)
- WINWORD.EXE (PID: 2292)
Changes internet zones settings
- iexplore.exe (PID: 2452)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
43
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2452 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
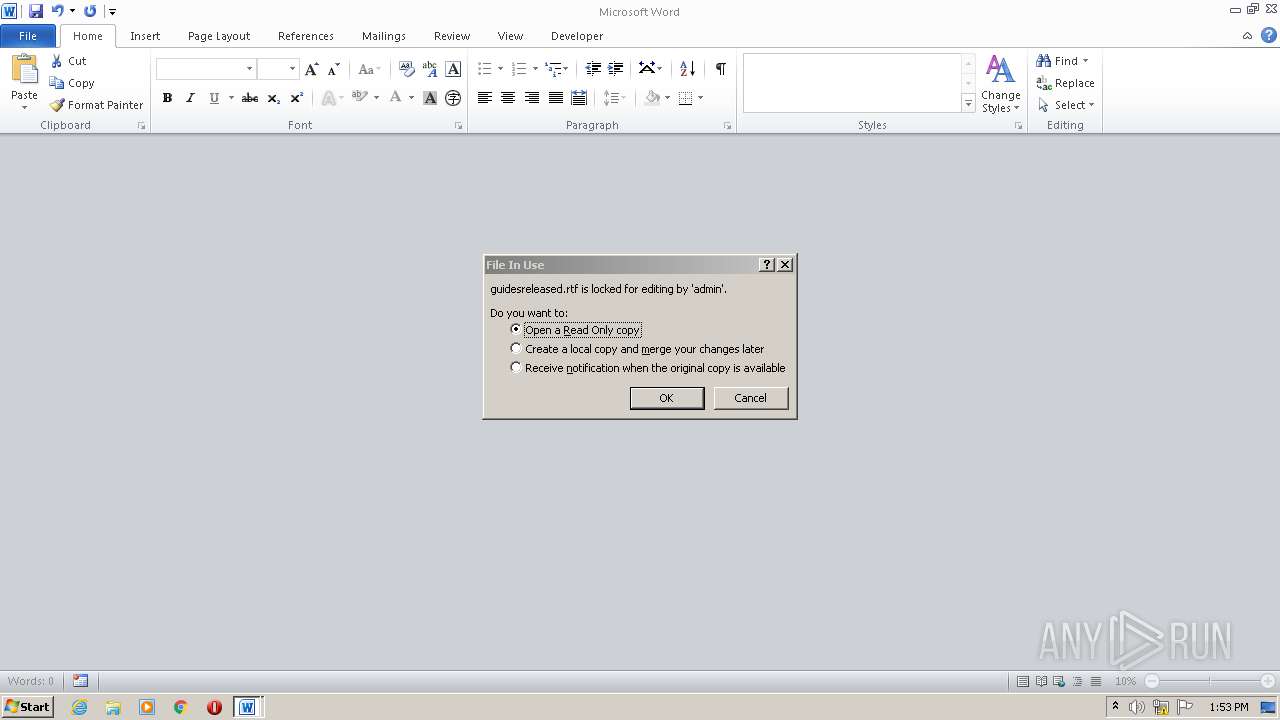
| 2168 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\guidesreleased.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\guidesreleased.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2452 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\guidesreleased.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 065
Read events
2 263
Write events
709
Delete events
93
Modification events
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3926240106 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844639 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2452) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
12
Text files
19
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2452 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC1DE.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC1DF.tmp | — | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\SOSHOYO2.htm | html | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verC21E.tmp | — | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\min[1].js | text | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\px[1].js | text | |
MD5:F84F931C0DD37448E03F0DABF4E4CA9F | SHA256:5C1D5FD46A88611C31ECBB8FFC1142A7E74EC7FB7D72BD3891131C880EF3F584 | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | binary | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | der | |
MD5:— | SHA256:— | |||
| 2452 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0D82BDA9CEA1540A.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
28
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2452 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 2.16.186.106:80 | http://i2.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
2452 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2452 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://i4.cdn-image.com/__media__/pics/12471/bodybg.png | unknown | image | 94.9 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://i4.cdn-image.com/__media__/pics/12471/search-icon.png | unknown | image | 1.16 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://i1.cdn-image.com/__media__/pics/12471/libg.png | unknown | image | 1.07 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://i1.cdn-image.com/__media__/pics/12471/kwbg.jpg | unknown | image | 36.3 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://i1.cdn-image.com/__media__/pics/12471/arrow.png | unknown | image | 1.04 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 2.16.186.106:80 | http://i2.cdn-image.com/__media__/pics/12471/libgh.png | unknown | image | 1.06 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
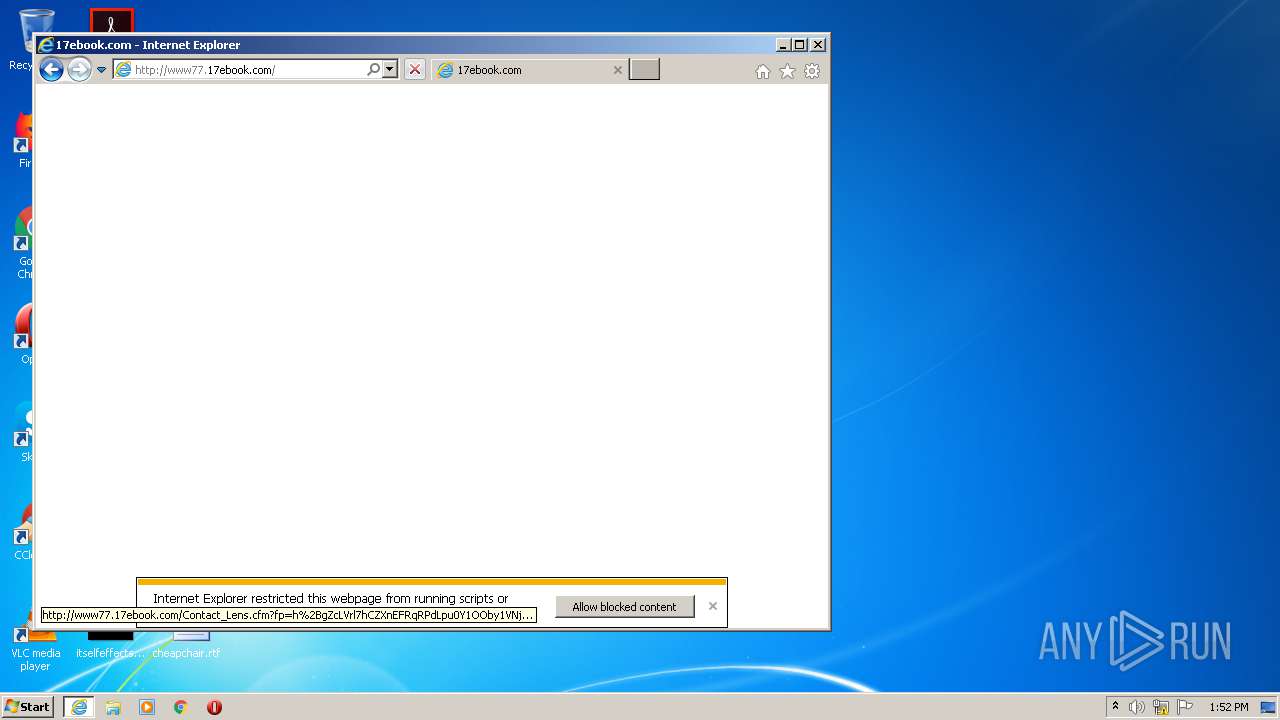
2908 | iexplore.exe | 45.56.79.23:80 | www.17ebook.com | Linode, LLC | US | malicious |
2908 | iexplore.exe | 2.16.186.64:80 | i4.cdn-image.com | Akamai International B.V. | — | whitelisted |
2908 | iexplore.exe | 2.16.186.106:80 | i4.cdn-image.com | Akamai International B.V. | — | whitelisted |
2452 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2908 | iexplore.exe | 199.191.50.39:80 | www77.17ebook.com | Confluence Networks Inc | VG | malicious |
2452 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2452 | iexplore.exe | 199.191.50.39:80 | www77.17ebook.com | Confluence Networks Inc | VG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.17ebook.com |
| malicious |
www77.17ebook.com |
| malicious |
i4.cdn-image.com |
| whitelisted |
i3.cdn-image.com |
| whitelisted |
i1.cdn-image.com |
| whitelisted |
i2.cdn-image.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |