| URL: | http://vip.qajacefo.xyz/tracker?s_id=7&aff_id=149 |
| Full analysis: | https://app.any.run/tasks/6ca1d4ff-30c4-4954-a9ab-af0d4ea53b91 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 13:56:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C3668128E56B6C0FED6A48B7A72E429E |
| SHA1: | 5E290301E09419FCDE3C24863DEFD95175B97C22 |
| SHA256: | 7F090891121364CBE50F8C5898379D788FDEFBDCF46427A0E391878476641C0D |
| SSDEEP: | 3:N1KISUEPF4GESMbRc:CISURTS26 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2300)
Reads the hosts file
- chrome.exe (PID: 2300)
- chrome.exe (PID: 2080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14818139863567342976 --mojo-platform-channel-handle=3924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4009362107702827806 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9919485428916322212 --mojo-platform-channel-handle=3260 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9681914343454275059 --mojo-platform-channel-handle=3300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15570854594584470620 --mojo-platform-channel-handle=3320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10916542236007394098 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4699422116491045540 --mojo-platform-channel-handle=2100 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2432410636566206129 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13288707651889753091 --mojo-platform-channel-handle=3988 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,2362764329789182552,18086670521994703777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17862389816084662398 --mojo-platform-channel-handle=3912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
624
Read events
514
Write events
104
Delete events
6
Modification events
| (PID) Process: | (2452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2300-13217695031791750 |
Value: 259 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2300) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
17
Text files
147
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\799d63a3-a486-4c03-8518-65cf2e2abe79.tmp | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a998.TMP | text | |
MD5:— | SHA256:— | |||
| 2300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
23
DNS requests
13
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
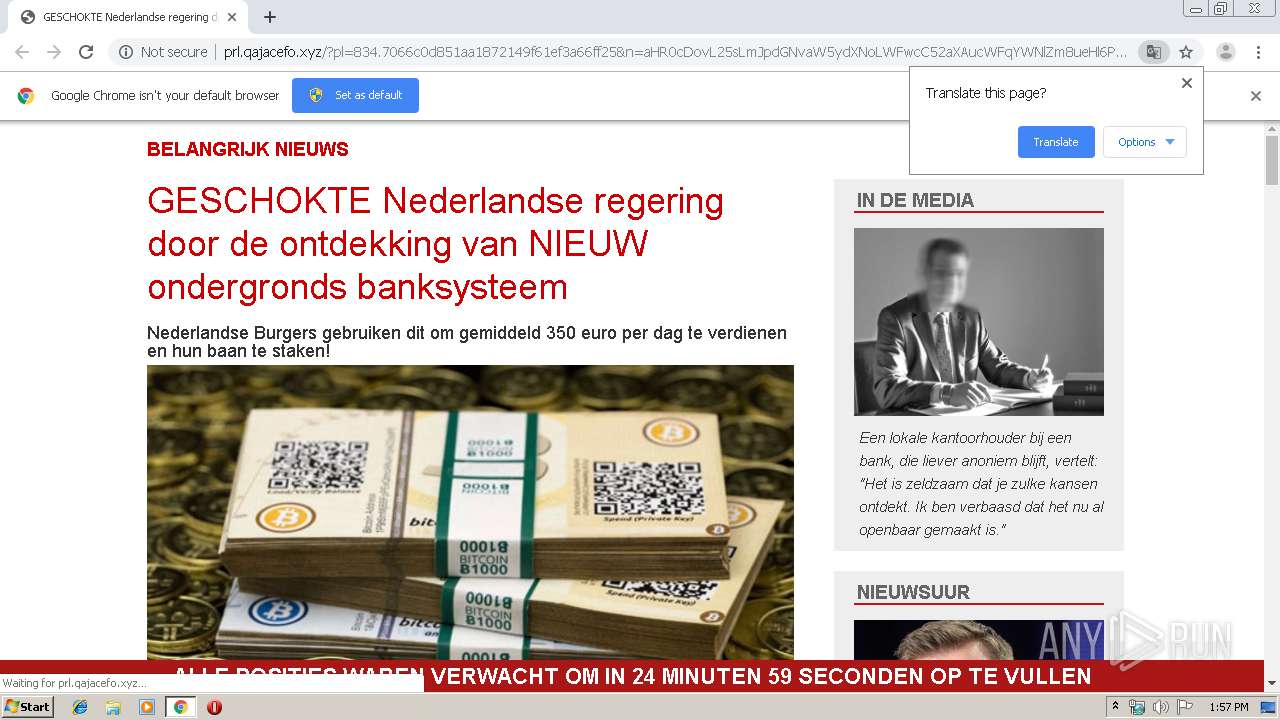
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/images/check-nl.jpg | US | image | 96.5 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/images/aufam_nl.jpg | US | image | 458 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/css/stylef2ad.css | US | text | 4.30 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/css/bootstrap.min.css | US | text | 18.8 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/images/sidenews3b.jpg | US | image | 40.8 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/images/sidenews2.jpg | US | image | 324 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/images/news_deborah1.jpg | US | image | 97.5 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/css/reset.css | US | text | 543 b | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/images/ian.jpg | US | image | 1.24 Kb | suspicious |
2080 | chrome.exe | GET | 200 | 104.31.79.119:80 | http://prl.qajacefo.xyz/prelands/834/images/sidenews10.jpg | US | image | 29.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2080 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2080 | chrome.exe | 104.31.78.119:80 | vip.qajacefo.xyz | Cloudflare Inc | US | suspicious |
2080 | chrome.exe | 104.31.79.119:80 | vip.qajacefo.xyz | Cloudflare Inc | US | suspicious |
2080 | chrome.exe | 216.58.210.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.42:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2080 | chrome.exe | 172.217.18.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2080 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2080 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2080 | chrome.exe | 74.125.8.167:80 | r1---sn-5hne6nlk.gvt1.com | Google Inc. | US | whitelisted |
2080 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vip.qajacefo.xyz |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
prl.qajacefo.xyz |
| suspicious |
clients2.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
nl.bitcoinrush-app.vip.qajacefo.xyz |
| suspicious |
redirector.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2080 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |