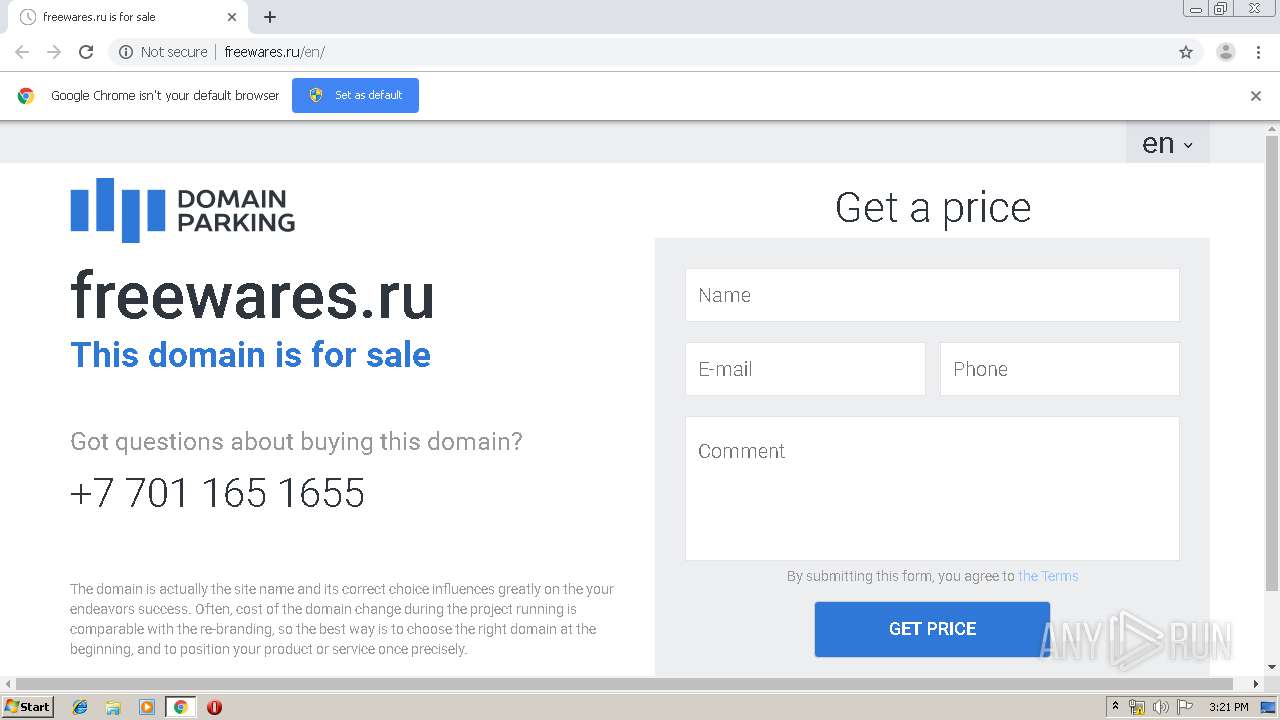
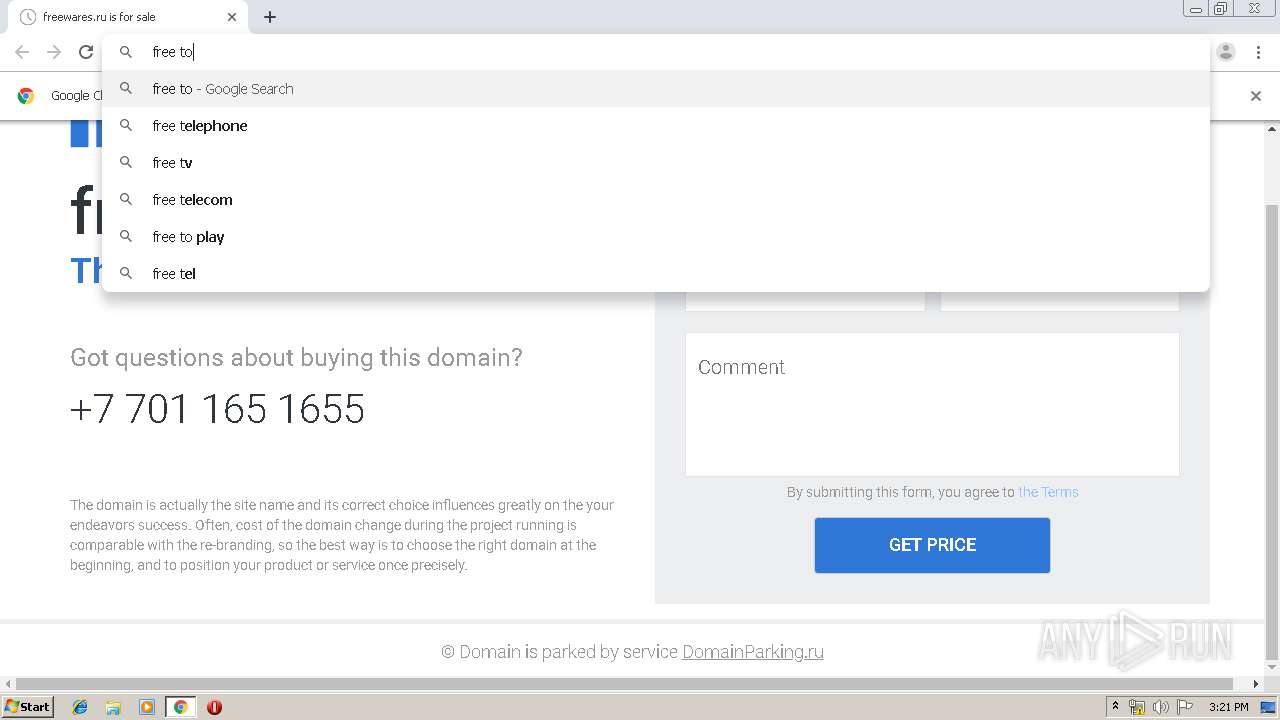
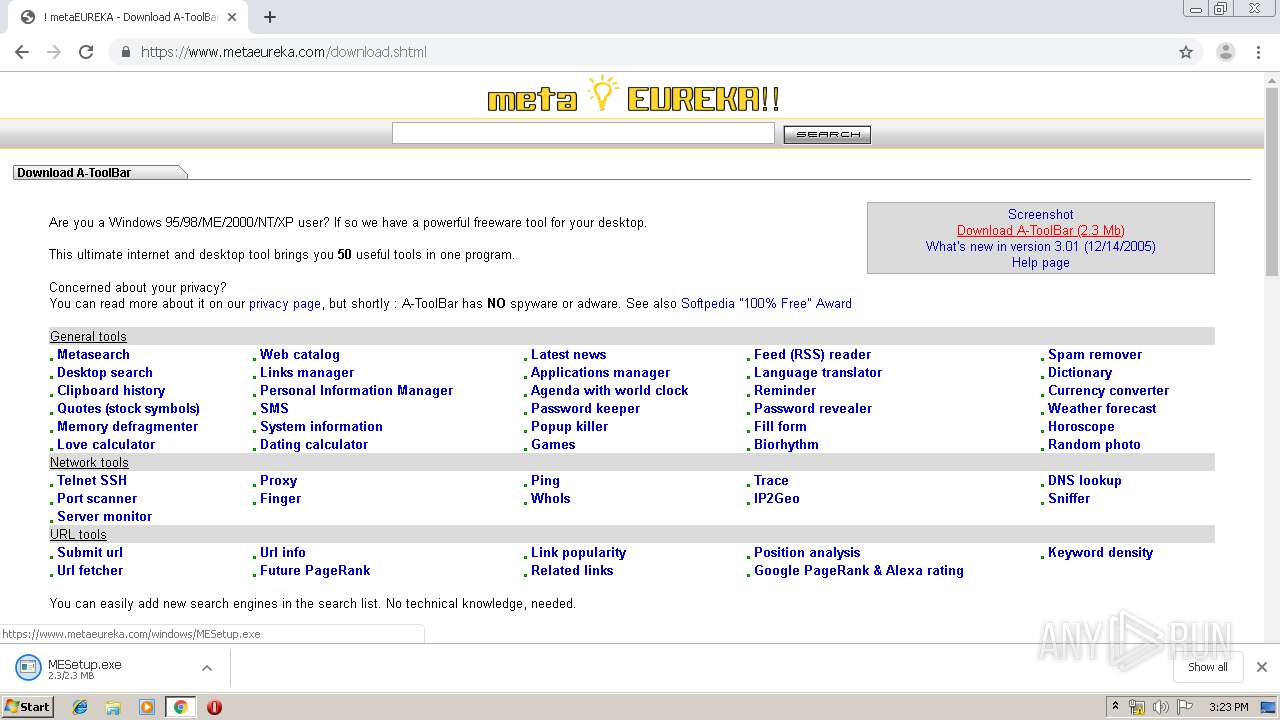
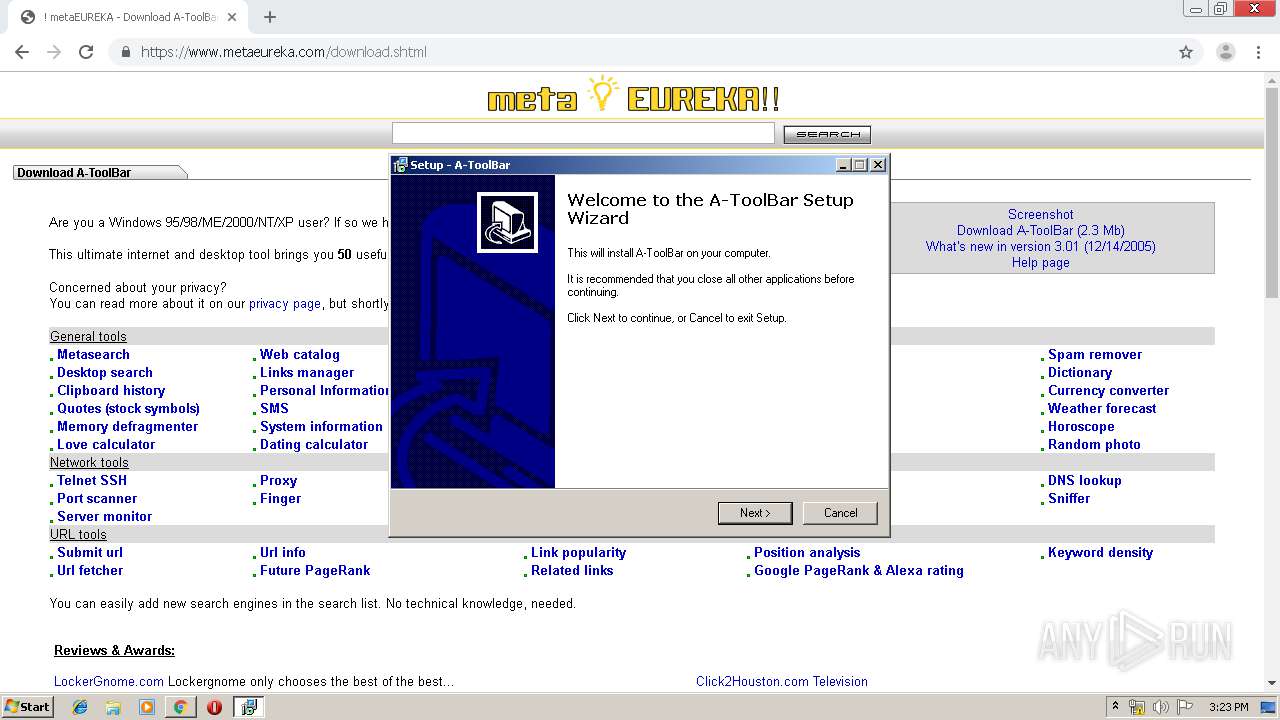
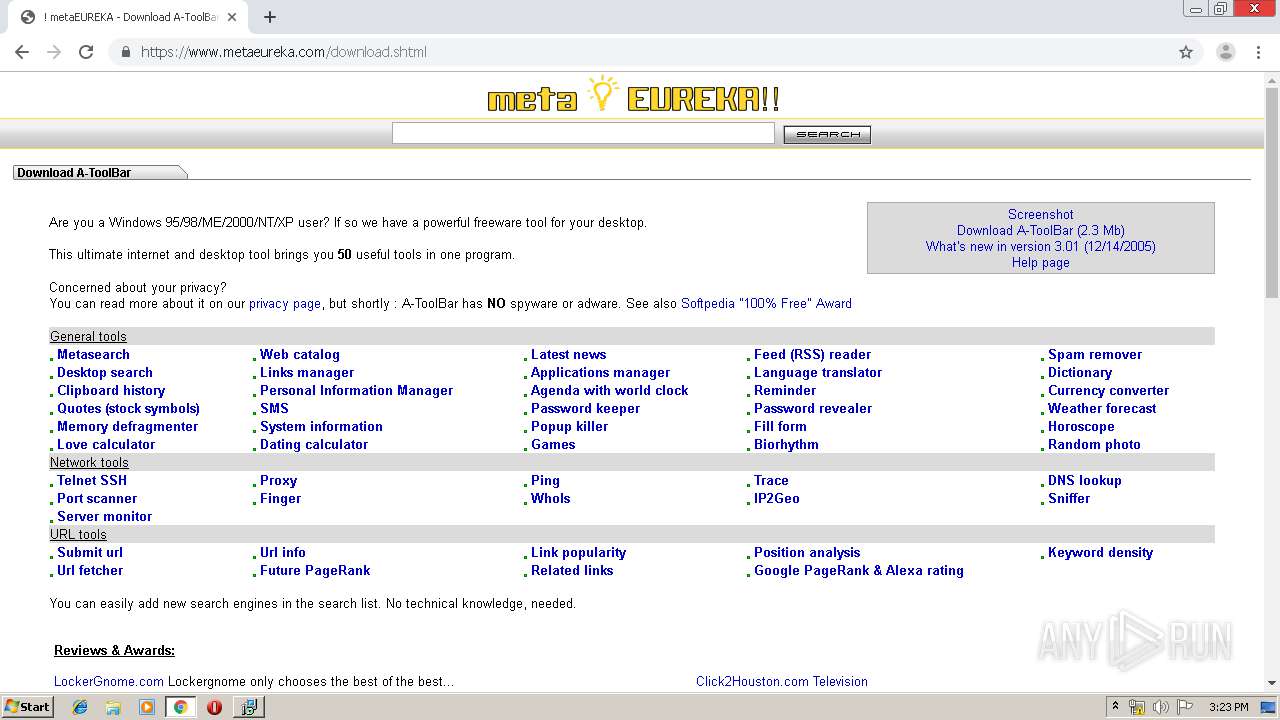
| URL: | http://freewares.ru |
| Full analysis: | https://app.any.run/tasks/f7bca8e6-ad8d-4853-a27b-016f33fd7faa |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 14:21:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3CD08972AED76B6D528B9354A74CAB79 |
| SHA1: | D0E4FE60712EB52F5599DE23DE90E5AAD9C96464 |
| SHA256: | 7F051ED45B2B4611EA37EB94CFEE9C3C67786FF91264FFD83ACEDE663EEE9556 |
| SSDEEP: | 3:N1KYQ3EQWjQn:CY4EQX |
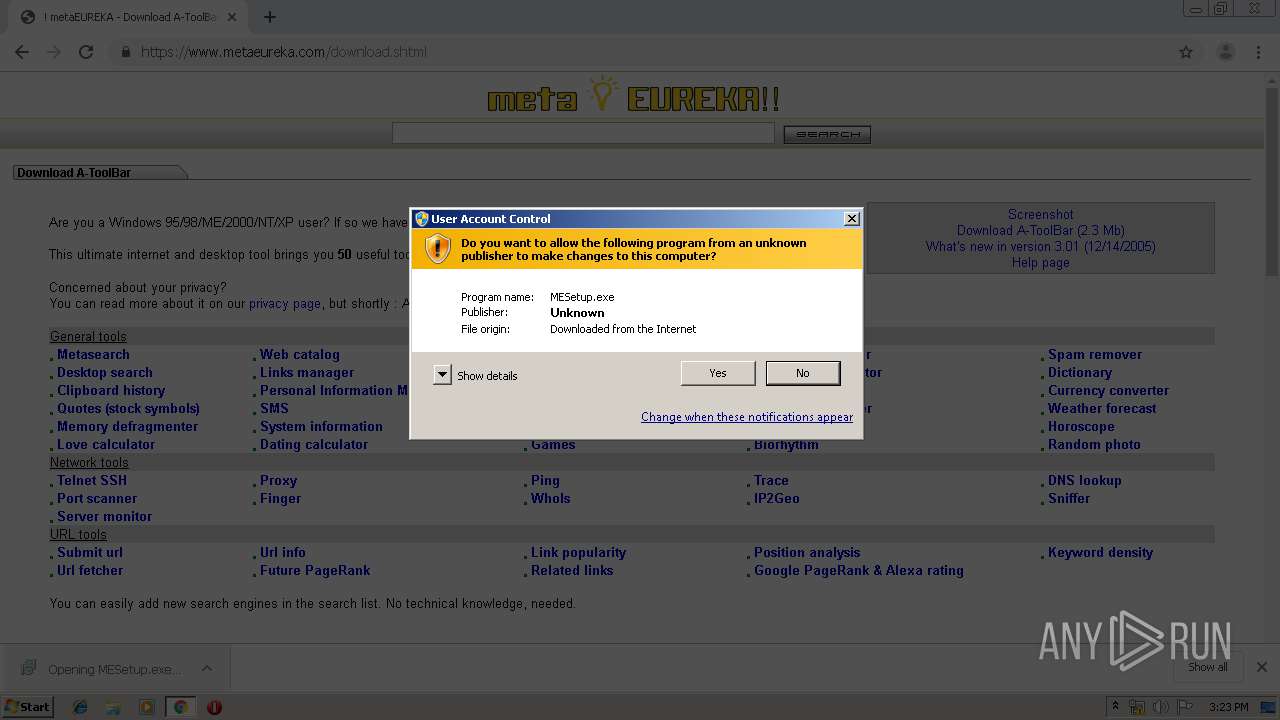
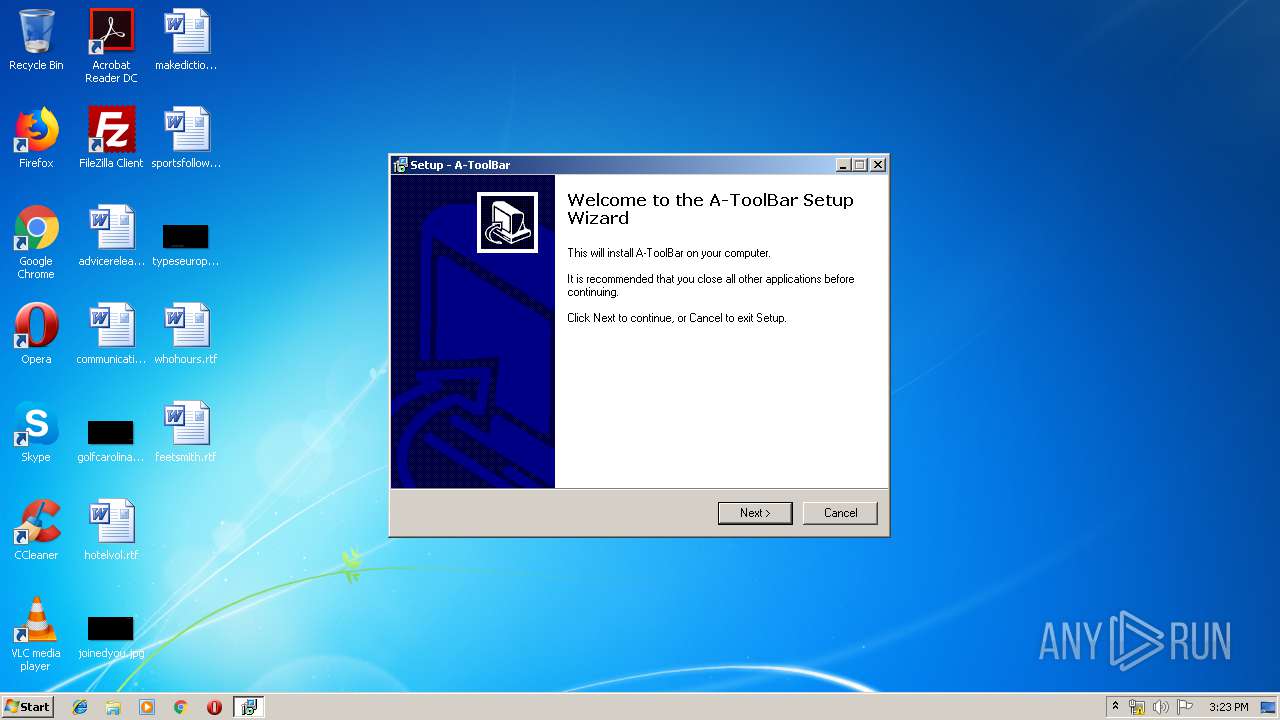
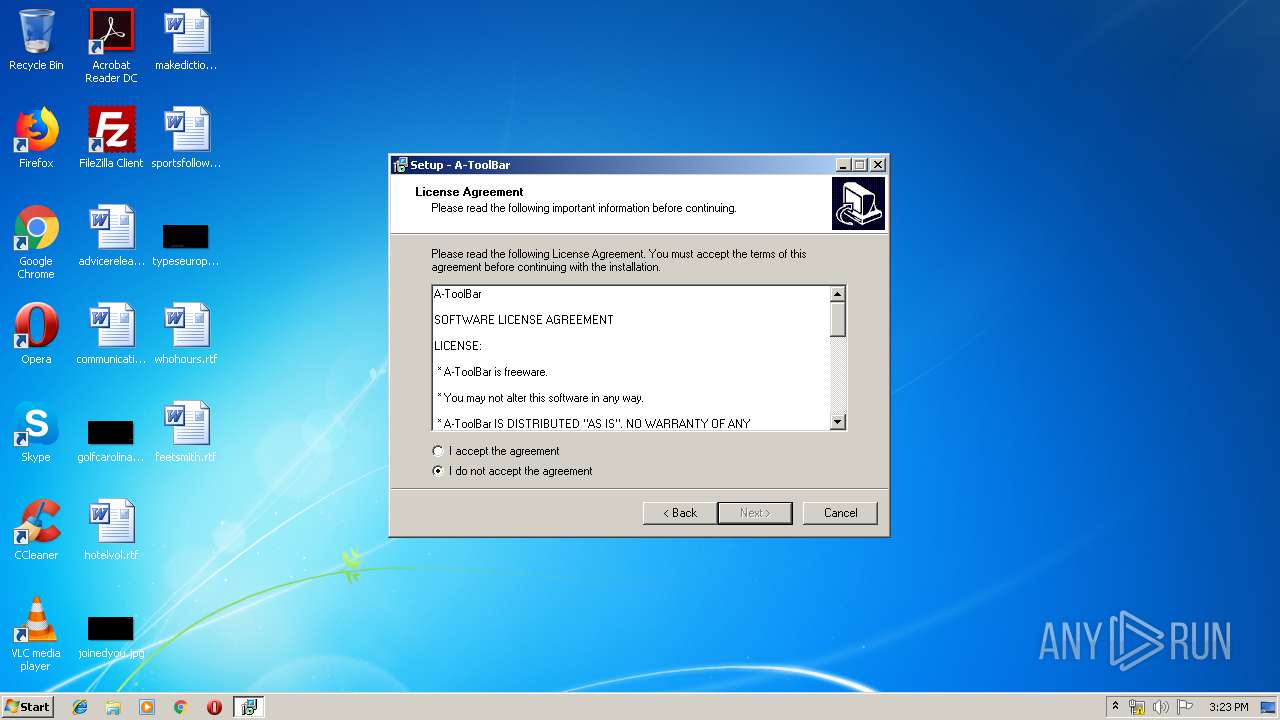
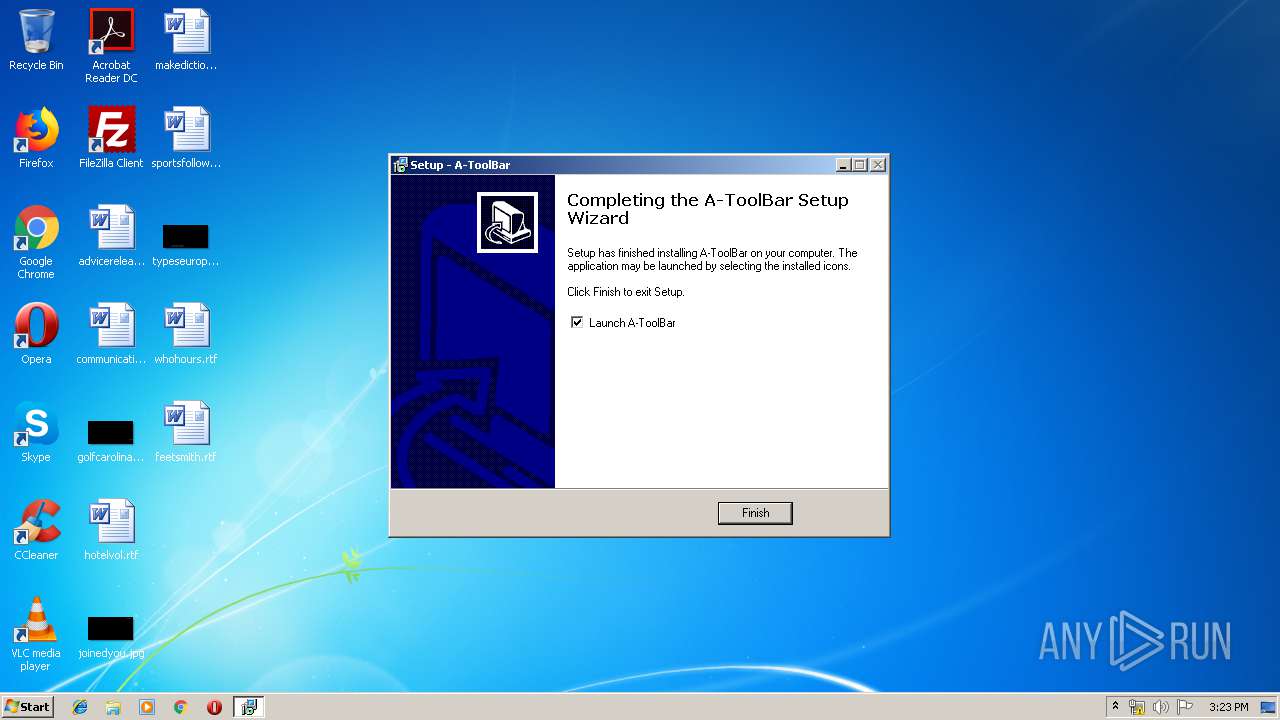
MALICIOUS
Application was dropped or rewritten from another process
- MESetup.exe (PID: 884)
- MESetup.exe (PID: 116)
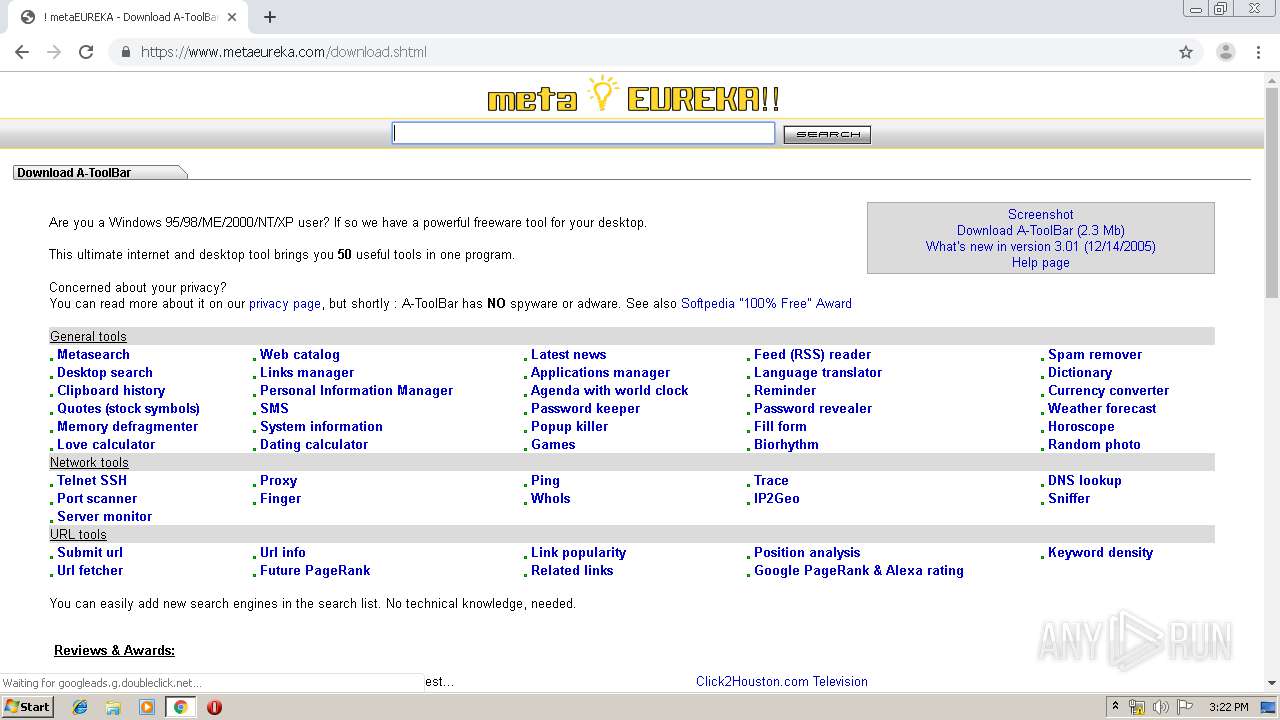
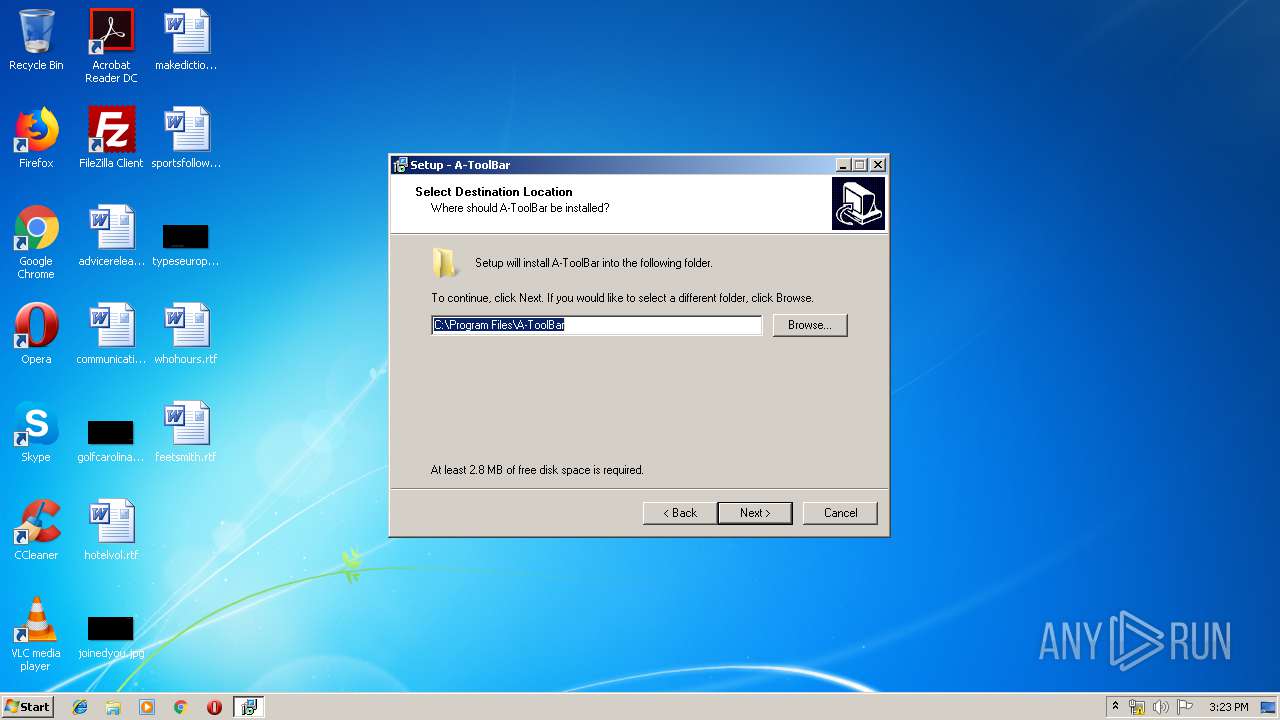
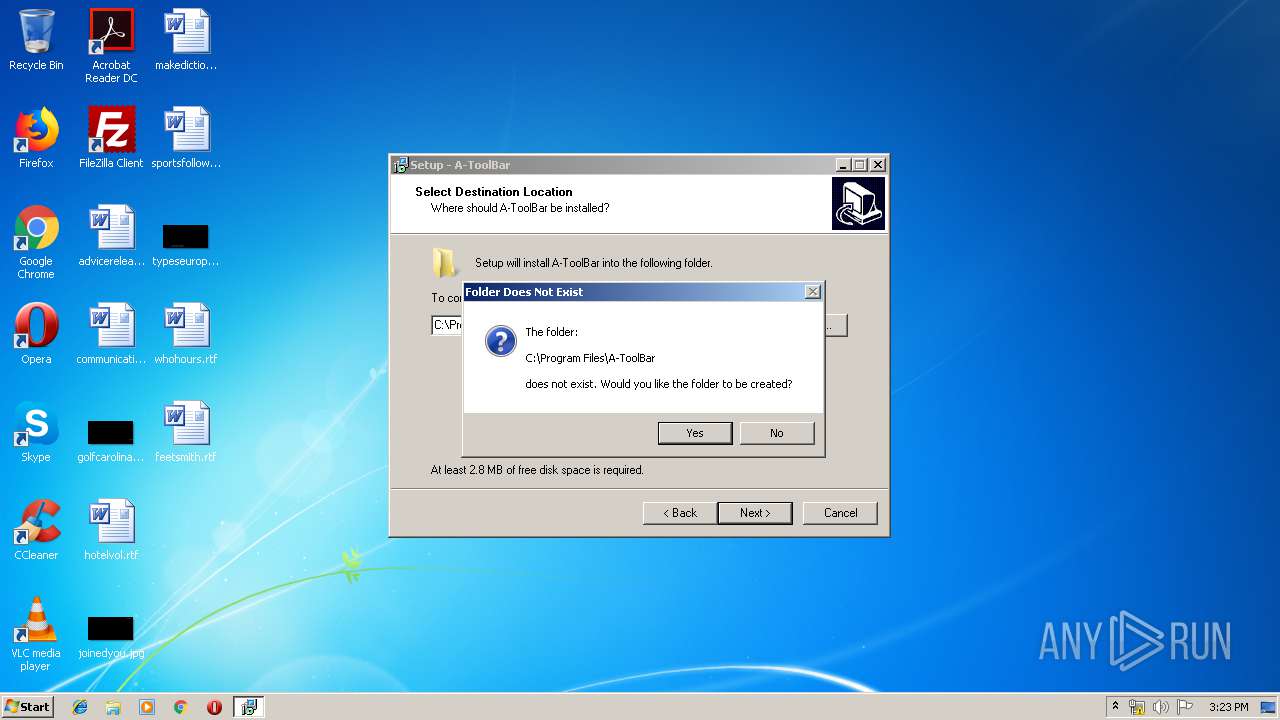
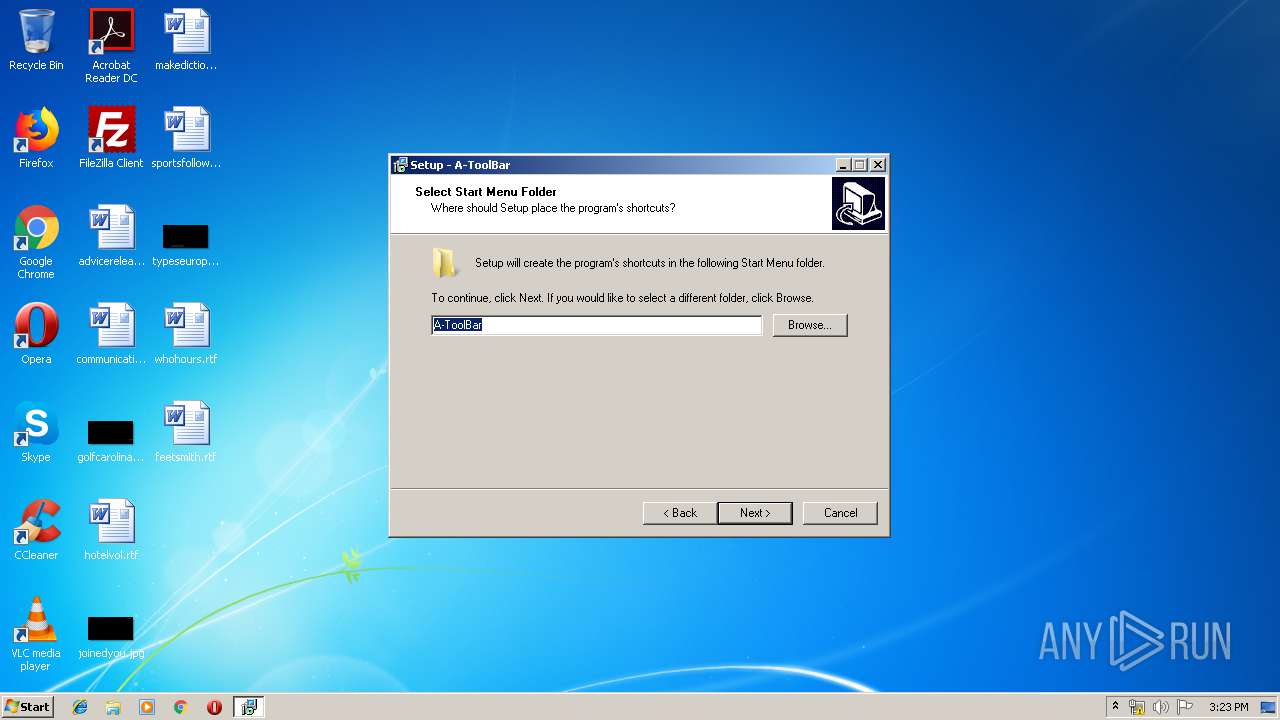
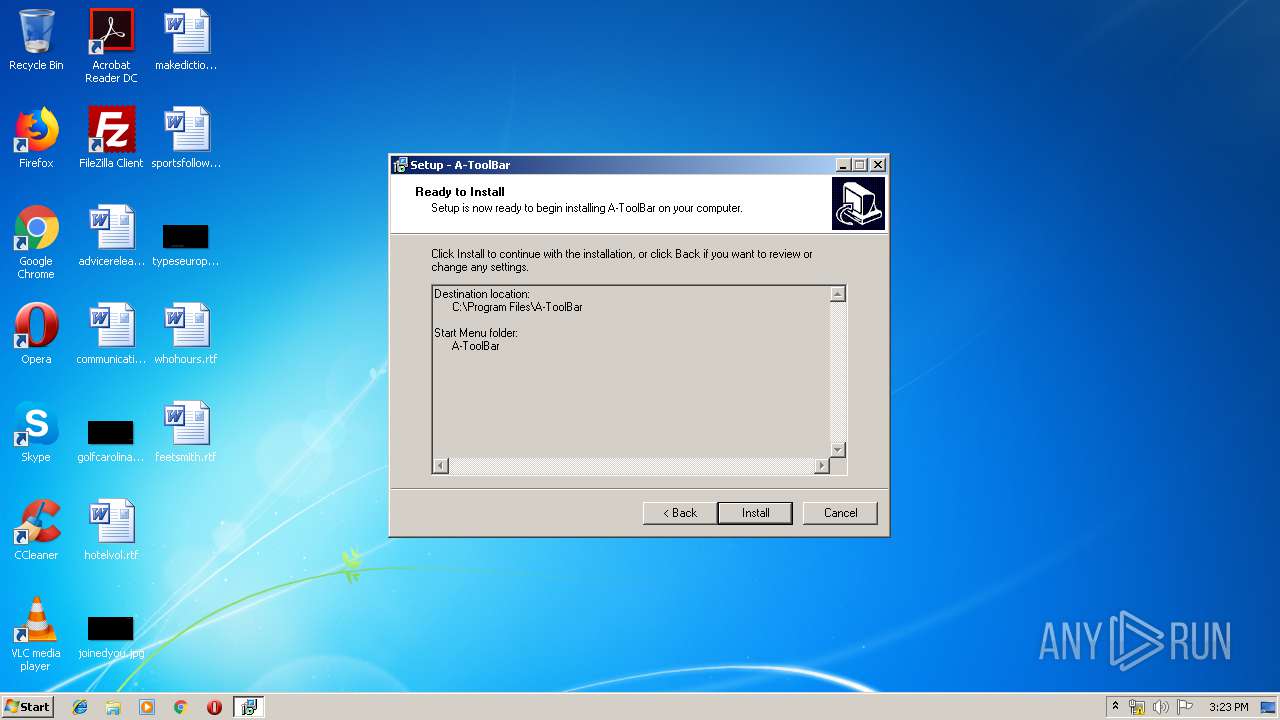
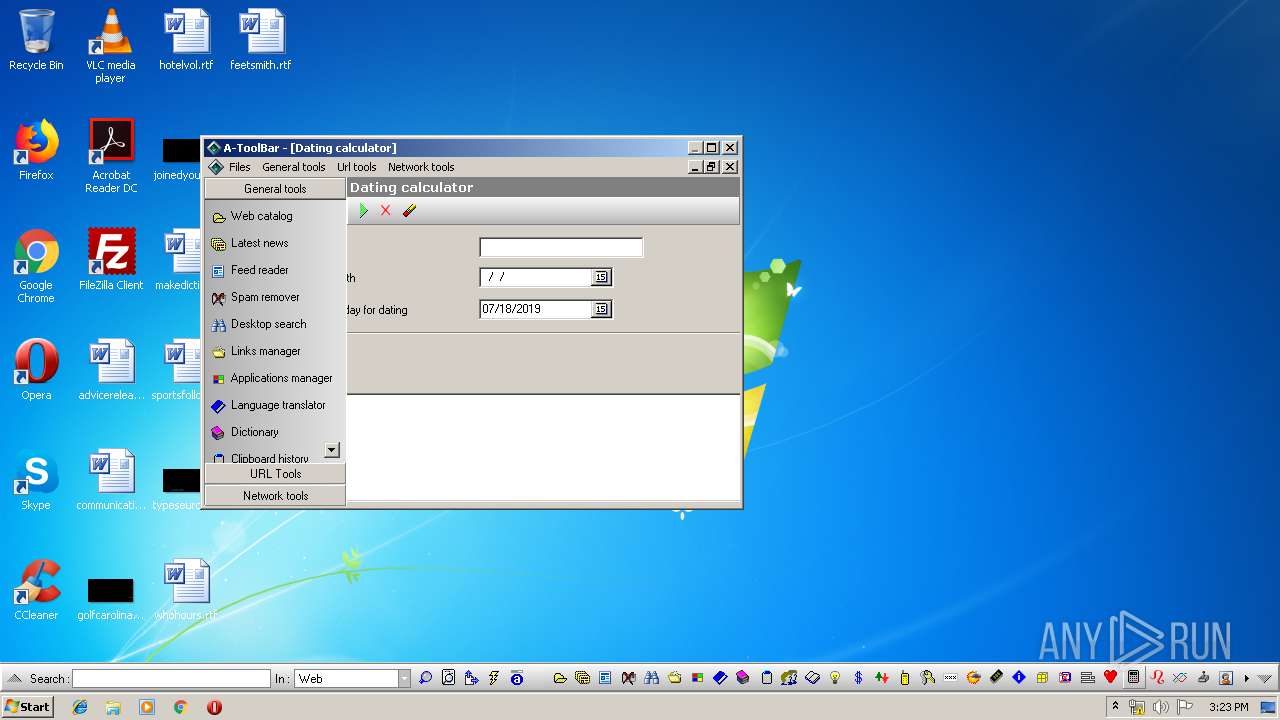
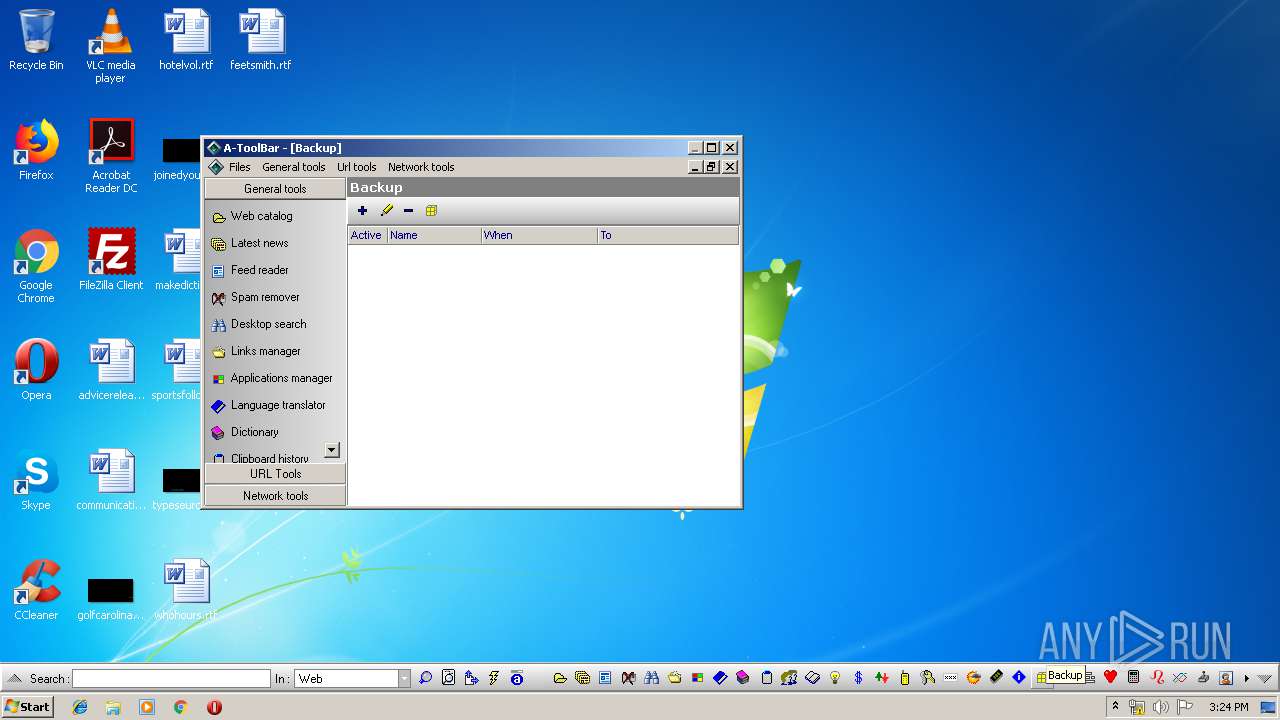
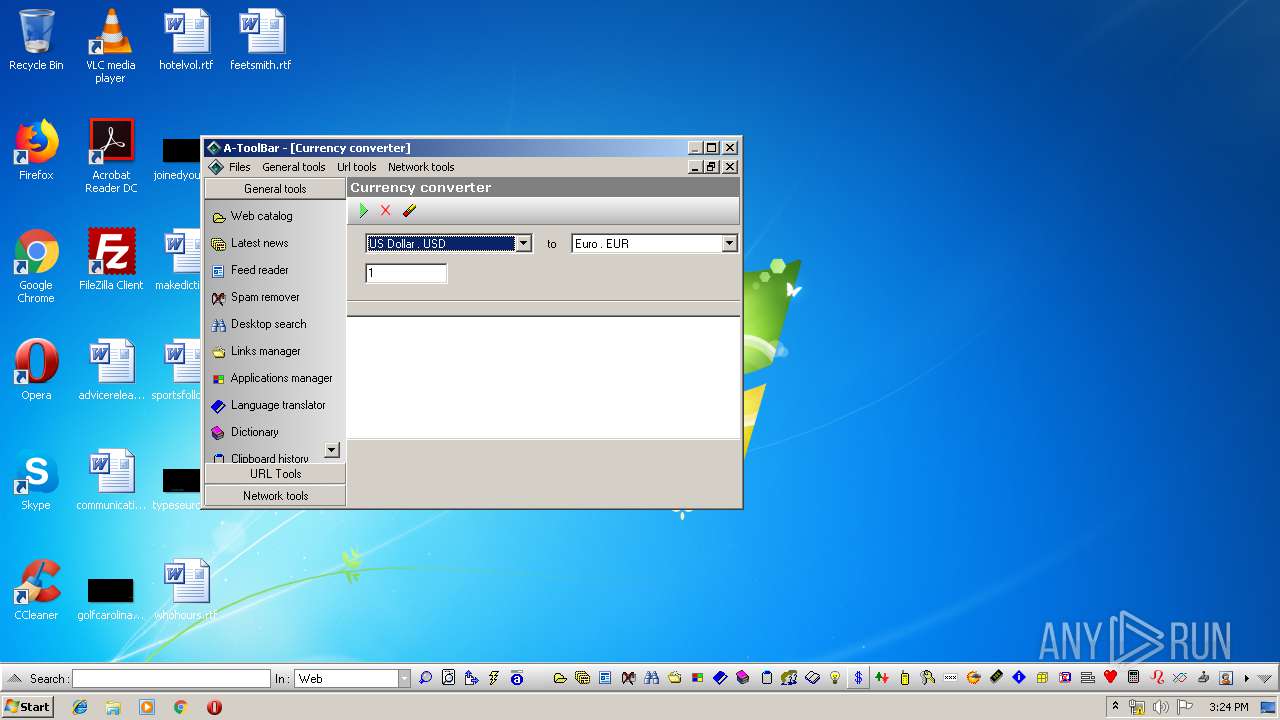
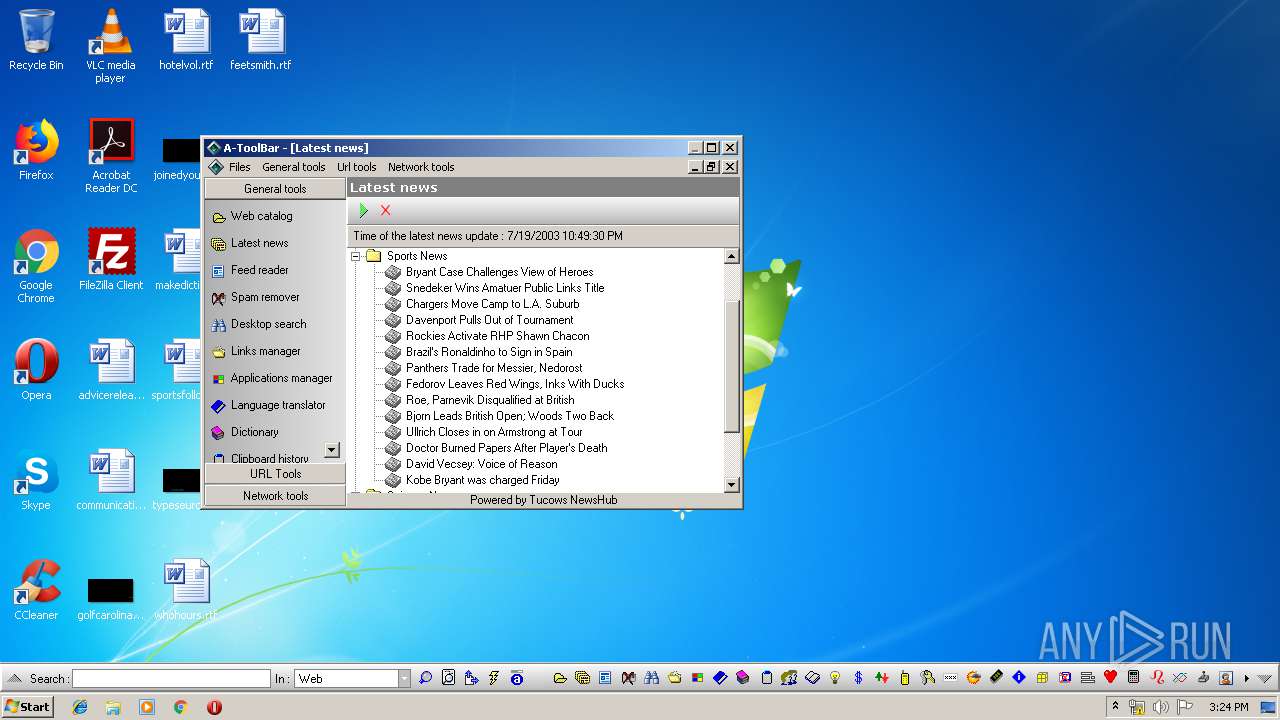
- AToolBar.exe (PID: 3360)
Changes the autorun value in the registry
- AToolBar.exe (PID: 3360)
- is-7V2BK.tmp (PID: 3324)
Loads dropped or rewritten executable
- AToolBar.exe (PID: 3360)
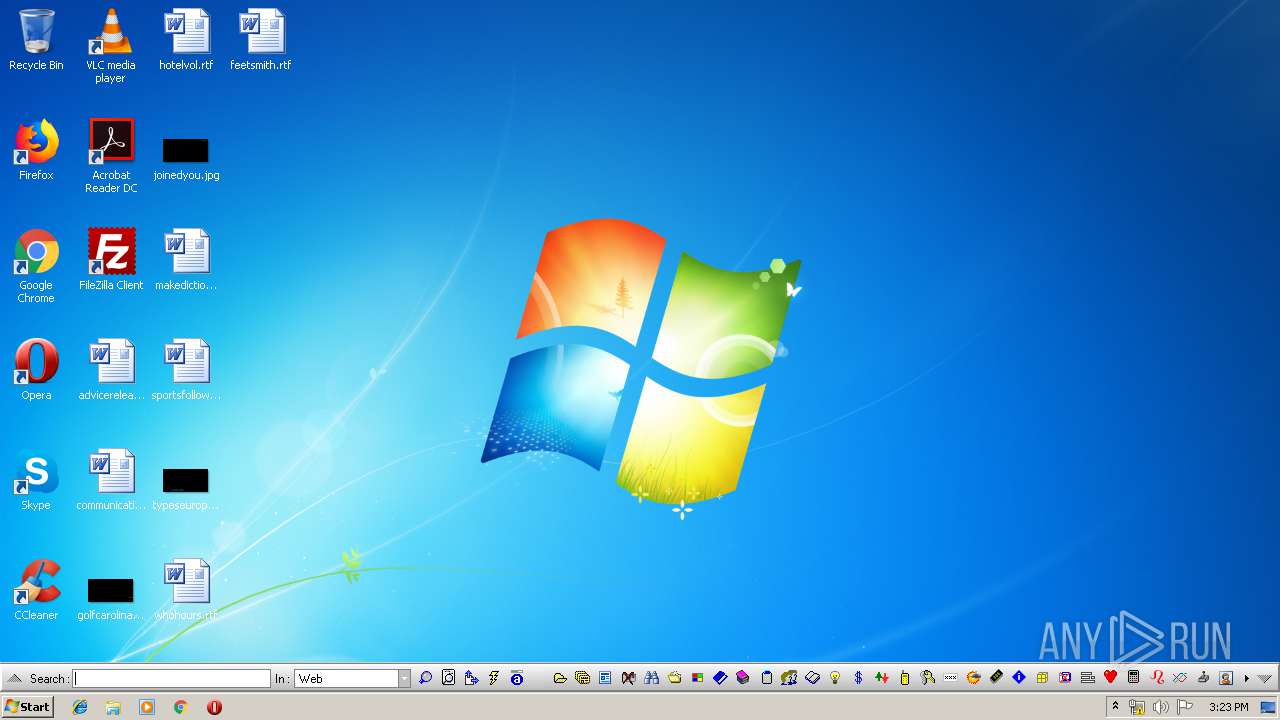
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3868)
- chrome.exe (PID: 2032)
- is-7V2BK.tmp (PID: 3324)
- MESetup.exe (PID: 116)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3868)
Creates files in the program directory
- AToolBar.exe (PID: 3360)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3868)
Application launched itself
- chrome.exe (PID: 3868)
Application was dropped or rewritten from another process
- is-7V2BK.tmp (PID: 3324)
Creates a software uninstall entry
- is-7V2BK.tmp (PID: 3324)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2032)
Creates files in the program directory
- is-7V2BK.tmp (PID: 3324)
Loads dropped or rewritten executable
- is-7V2BK.tmp (PID: 3324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
31
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\Downloads\MESetup.exe" | C:\Users\admin\Downloads\MESetup.exe | chrome.exe | ||||||||||||
User: admin Company: 4C Software Integrity Level: HIGH Description: A-ToolBar Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,3900562215960436406,10585639139836360748,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=295624635609869481 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Users\admin\Downloads\MESetup.exe" | C:\Users\admin\Downloads\MESetup.exe | — | chrome.exe | |||||||||||
User: admin Company: 4C Software Integrity Level: MEDIUM Description: A-ToolBar Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,3900562215960436406,10585639139836360748,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17418762530046878263 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,3900562215960436406,10585639139836360748,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9539757882606237801 --mojo-platform-channel-handle=3540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,3900562215960436406,10585639139836360748,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10750093882172073896 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,3900562215960436406,10585639139836360748,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8040161347264367339 --mojo-platform-channel-handle=2676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,3900562215960436406,10585639139836360748,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13816689986399248352 --mojo-platform-channel-handle=1580 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,3900562215960436406,10585639139836360748,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13444331310206658044 --mojo-platform-channel-handle=2620 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f96a9d0,0x6f96a9e0,0x6f96a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 404
Read events
1 273
Write events
126
Delete events
5
Modification events
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3868-13207933279652125 |
Value: 259 | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3868) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
12
Suspicious files
78
Text files
285
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7ae39fc5-8fb2-47ff-bd06-859d2e781627.tmp | — | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFdfa3f.TMP | text | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdf9f1.TMP | text | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFdf9e1.TMP | text | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
48
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
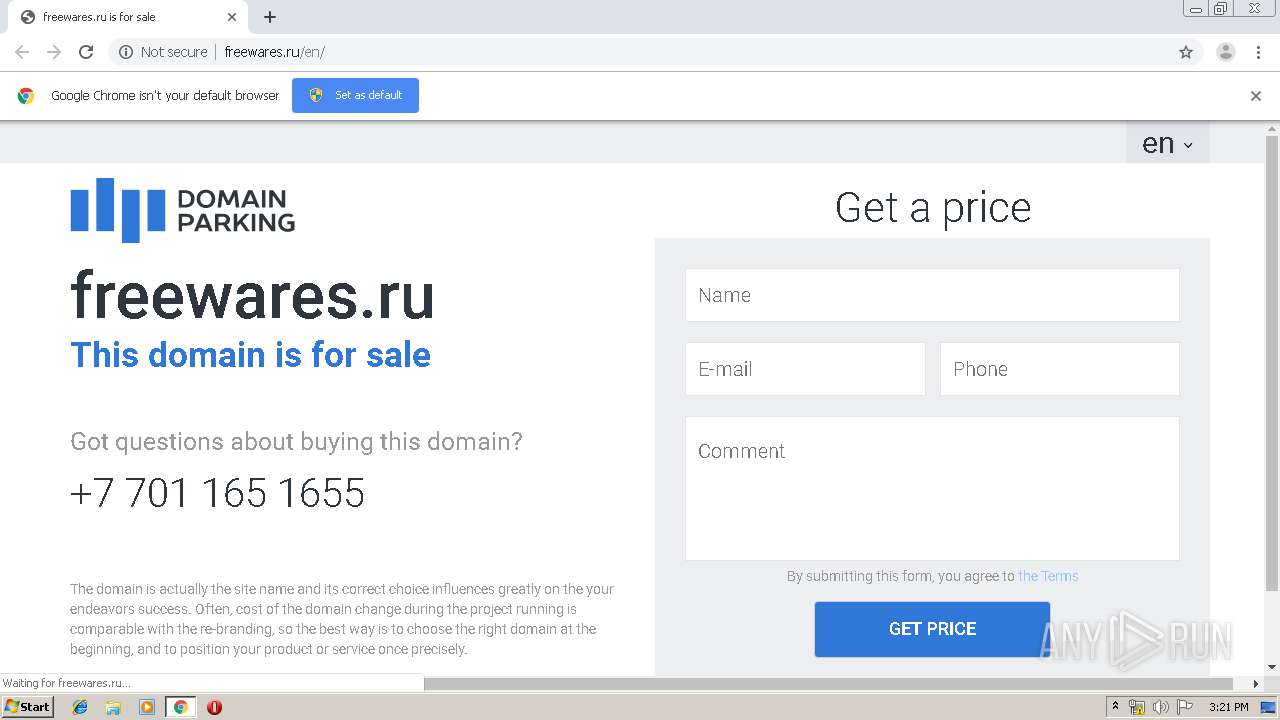
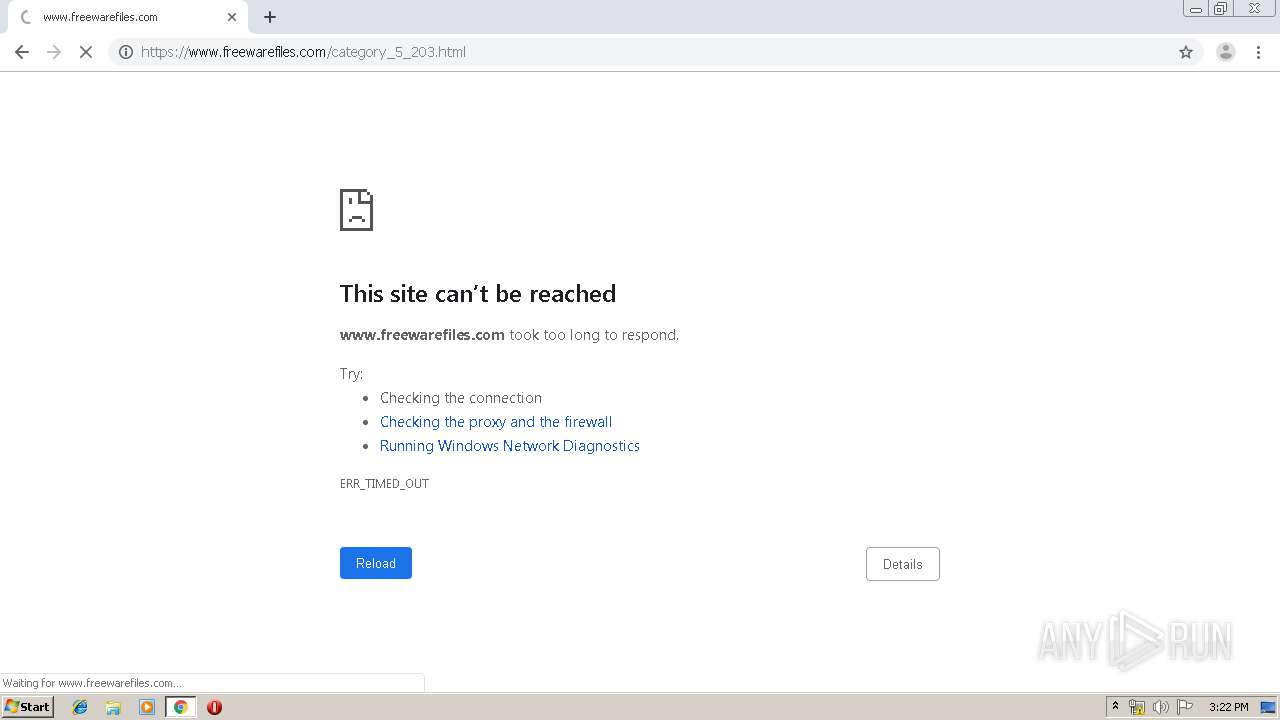
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/css/feedback.css?77 | RU | text | 1.27 Kb | malicious |
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/js/callback/user.php?callback=parking&key=65b12e55261f8466a33791f62210e5e4 | RU | text | 181 b | malicious |
2032 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2032 | chrome.exe | GET | 302 | 31.31.205.163:80 | http://freewares.ru/ | RU | — | — | malicious |
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/js/callback/check.php? | RU | compressed | 264 b | malicious |
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/css/vnd/normilize.css | RU | text | 2.54 Kb | malicious |
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/js/langVars.js | RU | text | 264 b | malicious |
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/css/general.css?3 | RU | text | 1.54 Kb | malicious |
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/css/pnotify.css?2 | RU | text | 1.73 Kb | malicious |
2032 | chrome.exe | GET | 200 | 31.31.205.163:80 | http://freewares.ru/06-18/css/bootstrap.min.css | RU | text | 19.2 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2032 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2032 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2032 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2032 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
2032 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2032 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
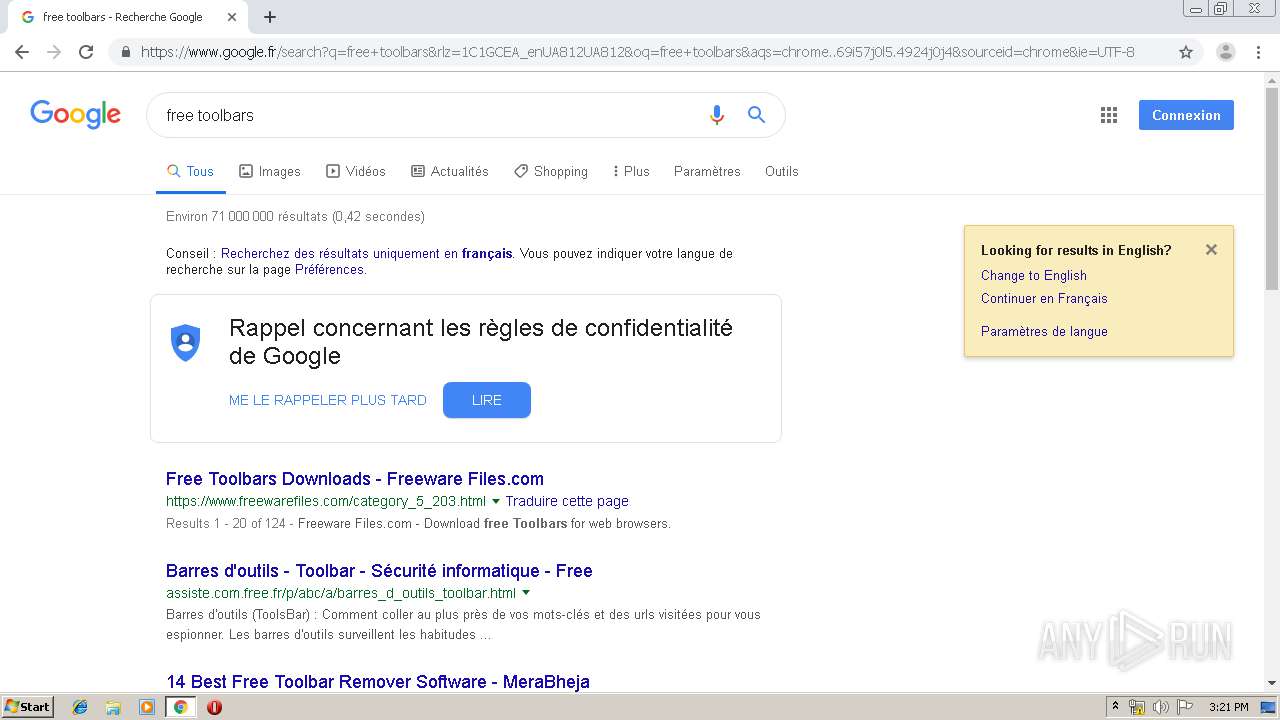
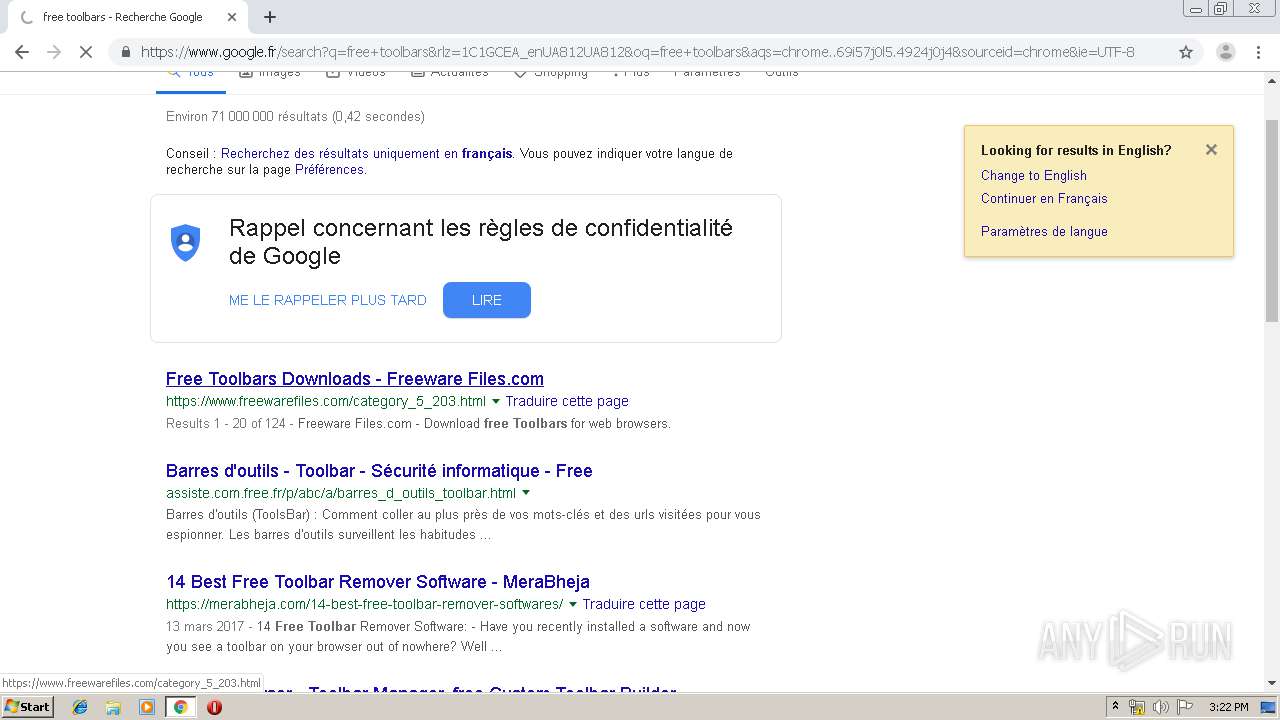
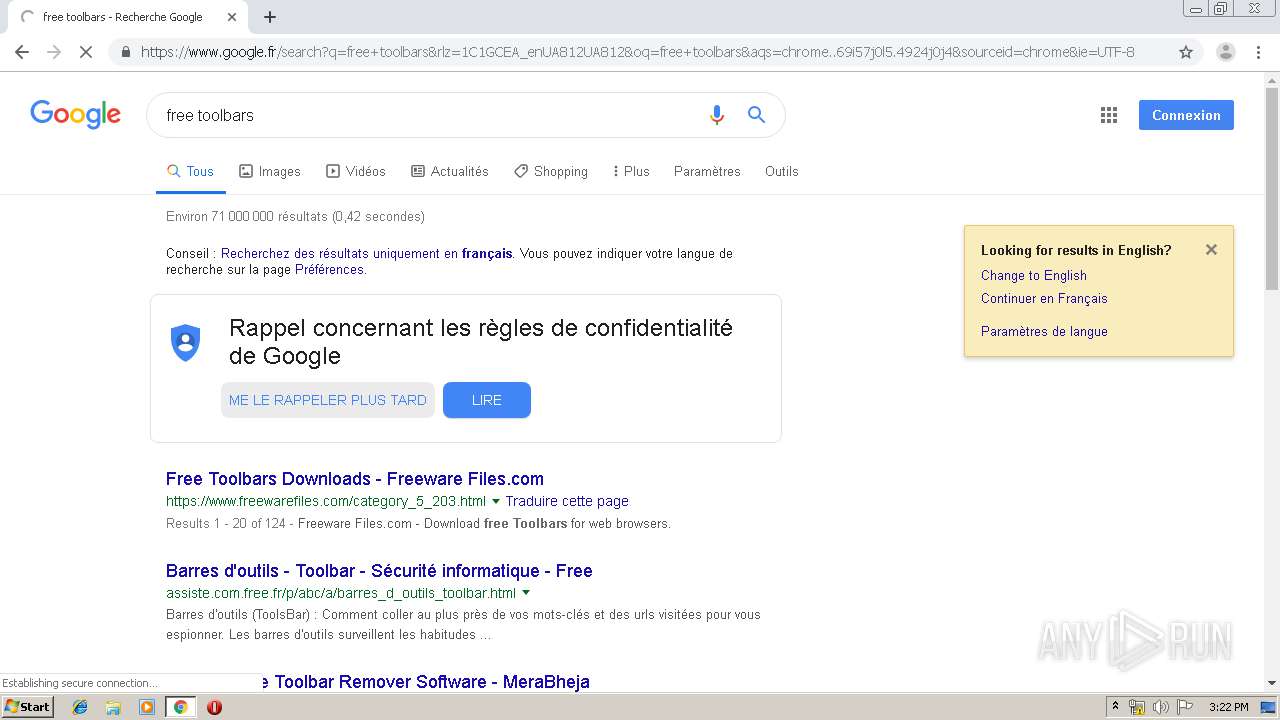
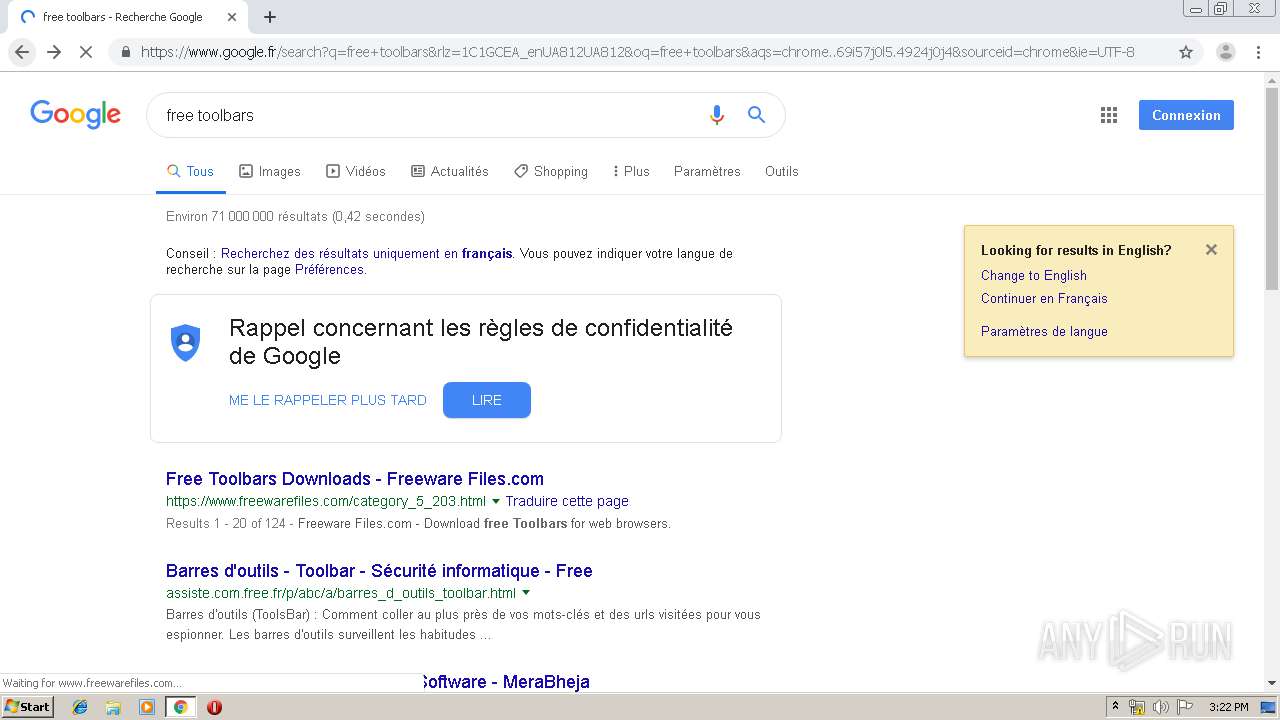
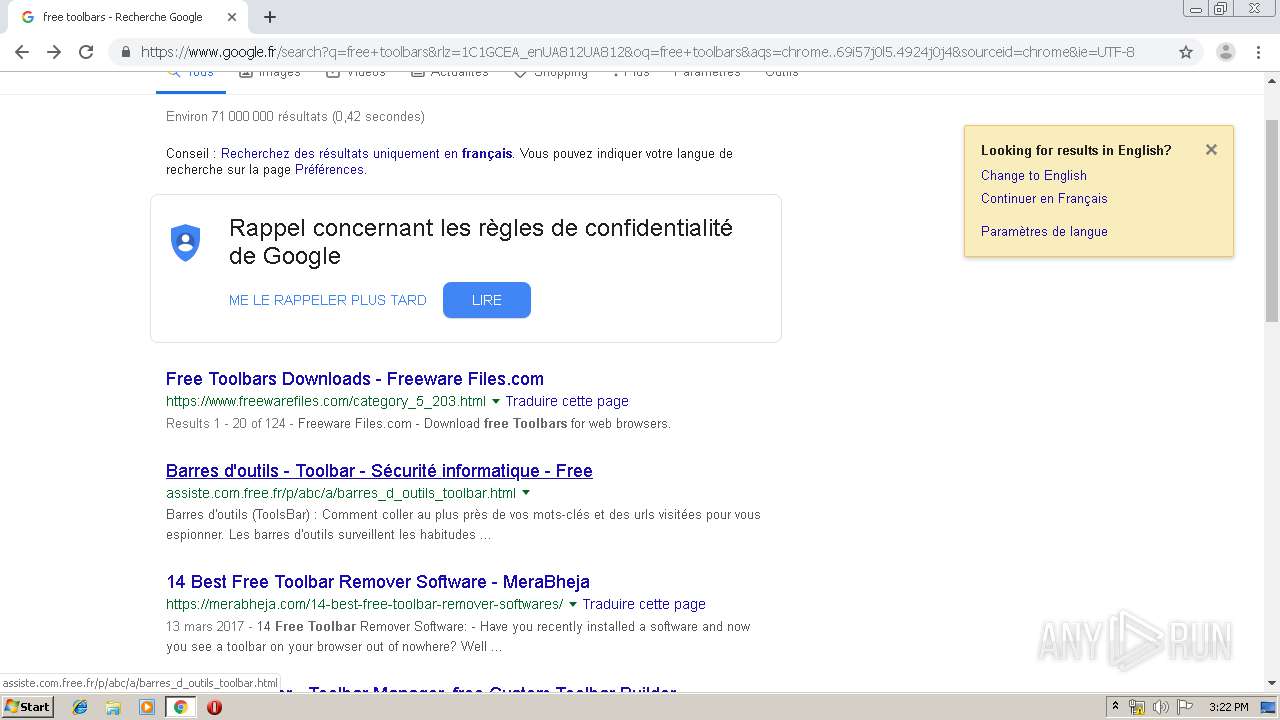
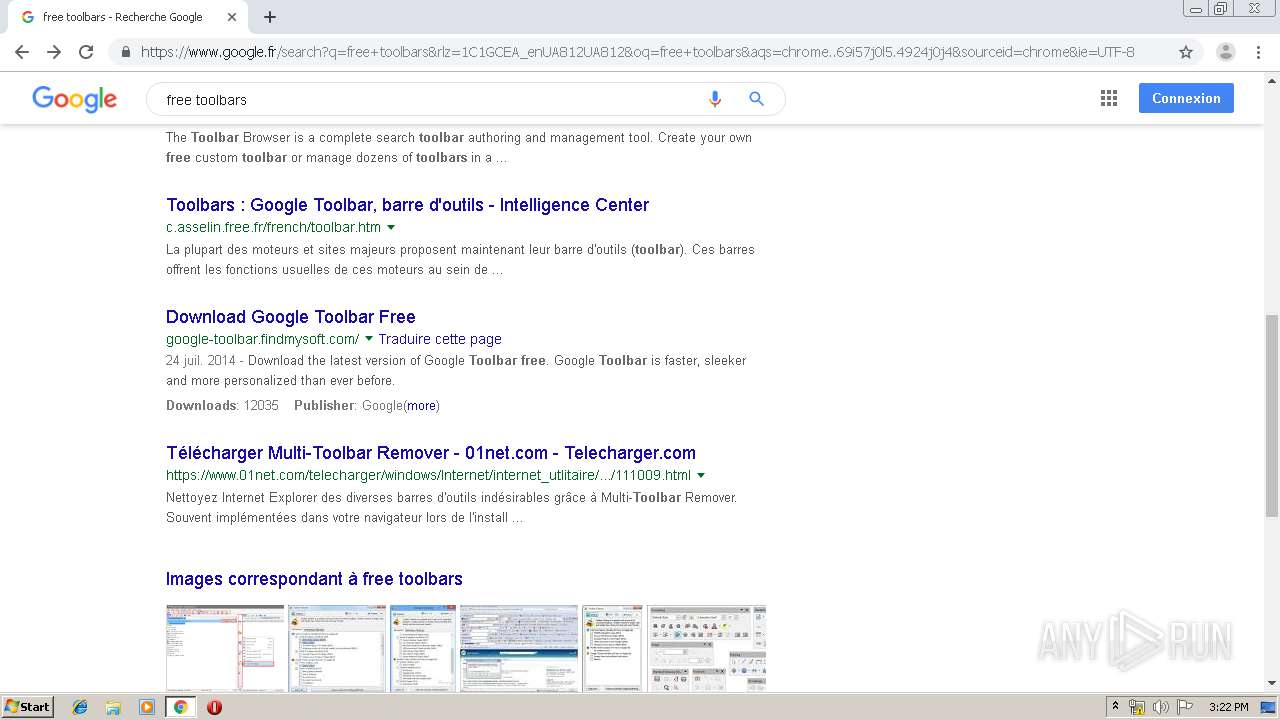
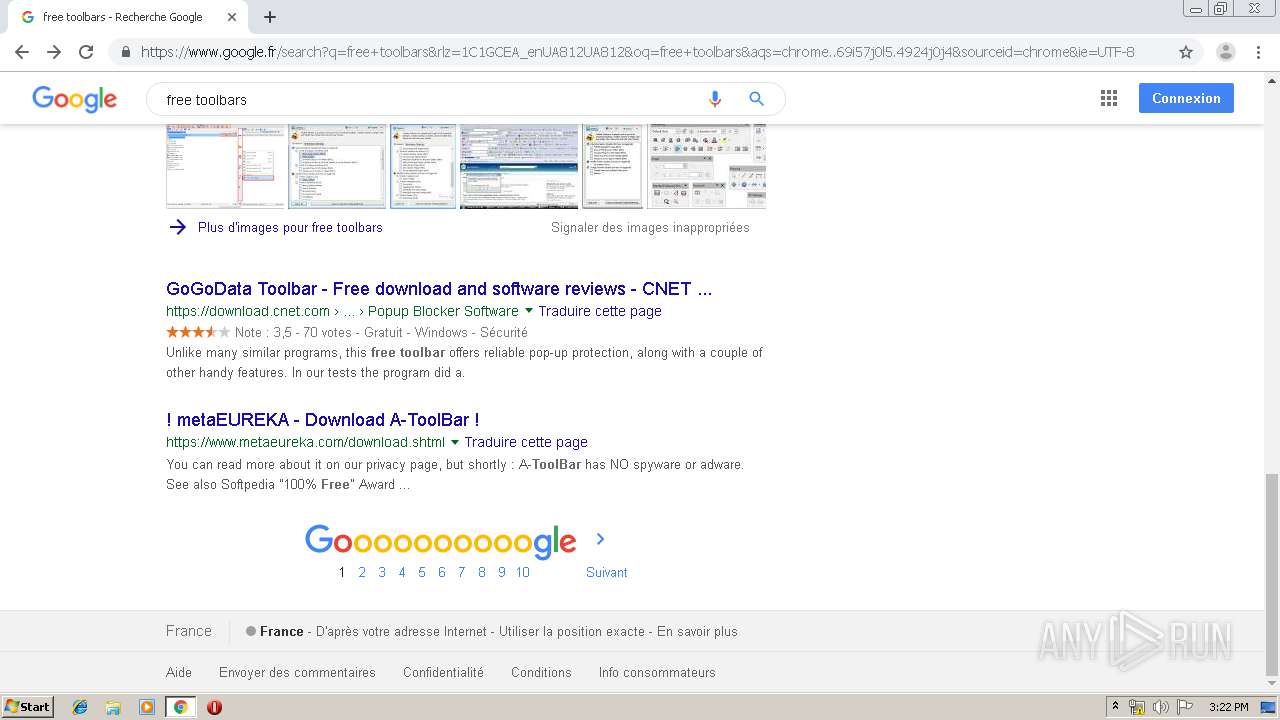
2032 | chrome.exe | 172.217.16.195:443 | www.google.fr | Google Inc. | US | whitelisted |
2032 | chrome.exe | 216.58.205.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2032 | chrome.exe | 173.194.188.169:80 | r4---sn-4g5edns6.gvt1.com | Google Inc. | US | whitelisted |
2032 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
freewares.ru |
| malicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
domainparking.ru |
| malicious |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.fr |
| whitelisted |