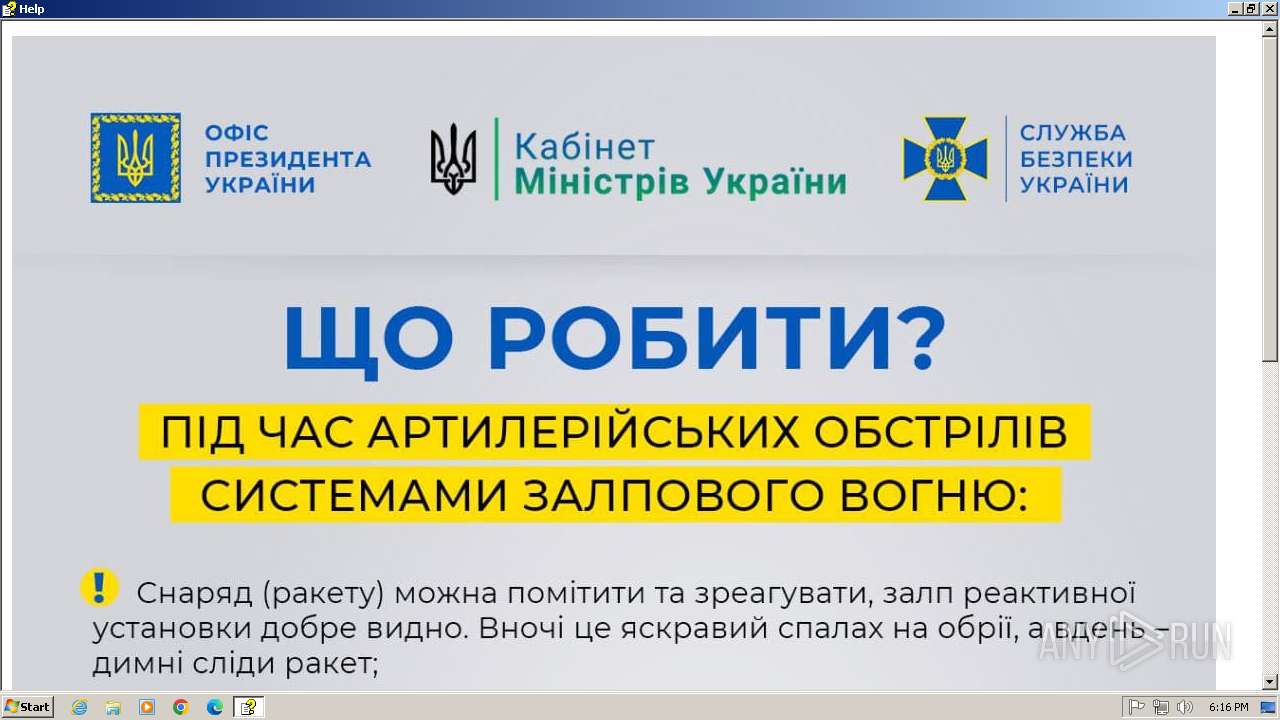
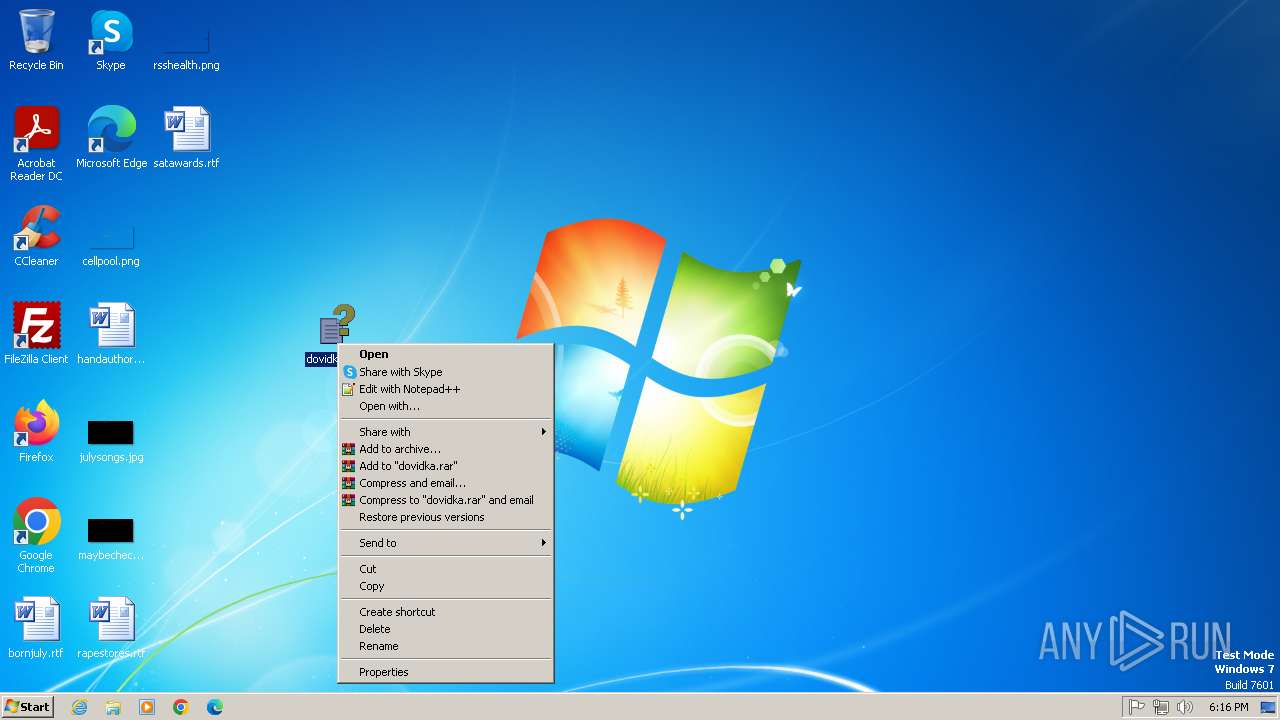
| File name: | dovidka.chm |
| Full analysis: | https://app.any.run/tasks/eaca463a-c7ba-4010-8914-5d63eabeb55a |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2025, 17:16:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-htmlhelp |
| File info: | MS Windows HtmlHelp Data |
| MD5: | 2556A9E1D5E9874171F51620E5C5E09A |
| SHA1: | AFFC2B19D9FB8080A7211C3ED0718F2C3D3887DF |
| SHA256: | 7F0511B09B1AB3A64C8827DD8AF017ACBF7D2688DB31A5D98FEA8A5029A89D56 |
| SSDEEP: | 6144:6hK9QF9IF78JuiKgnheEVfh+x6I/c0mGkBZ6w5+2yrBnx:d9QFq78JuiBnheEVqvcBZ6ws7nx |
MALICIOUS
Creates a new folder (SCRIPT)
- hh.exe (PID: 2060)
Gets startup folder path (SCRIPT)
- wscript.exe (PID: 2360)
Deletes a file (SCRIPT)
- hh.exe (PID: 2060)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 2360)
Create files in the Startup directory
- wscript.exe (PID: 2360)
SUSPICIOUS
Reads Microsoft Outlook installation path
- hh.exe (PID: 2060)
- hh.exe (PID: 3124)
Reads the Internet Settings
- hh.exe (PID: 2060)
- wscript.exe (PID: 2332)
- hh.exe (PID: 3124)
- RegAsm.exe (PID: 1824)
Reads Internet Explorer settings
- hh.exe (PID: 2060)
- hh.exe (PID: 3124)
Creates FileSystem object to access computer's file system (SCRIPT)
- hh.exe (PID: 2060)
- wscript.exe (PID: 2332)
- wscript.exe (PID: 2360)
- hh.exe (PID: 3124)
Checks whether a specific file exists (SCRIPT)
- hh.exe (PID: 2060)
- hh.exe (PID: 3124)
Writes binary data to a Stream object (SCRIPT)
- hh.exe (PID: 2060)
- wscript.exe (PID: 2360)
Likely accesses (executes) a file from the Public directory
- wscript.exe (PID: 2360)
- wscript.exe (PID: 2332)
- RegAsm.exe (PID: 1824)
The process executes VB scripts
- hh.exe (PID: 2060)
Runs shell command (SCRIPT)
- hh.exe (PID: 2060)
- wscript.exe (PID: 2332)
Write to the desktop.ini file (may be used to cloak folders)
- wscript.exe (PID: 2360)
Executable content was dropped or overwritten
- wscript.exe (PID: 2360)
Connects to unusual port
- RegAsm.exe (PID: 1824)
There is functionality for taking screenshot (YARA)
- RegAsm.exe (PID: 1824)
Reads security settings of Internet Explorer
- RegAsm.exe (PID: 1824)
INFO
Reads the machine GUID from the registry
- hh.exe (PID: 2060)
- hh.exe (PID: 3124)
- RegAsm.exe (PID: 1824)
The sample compiled with english language support
- hh.exe (PID: 2060)
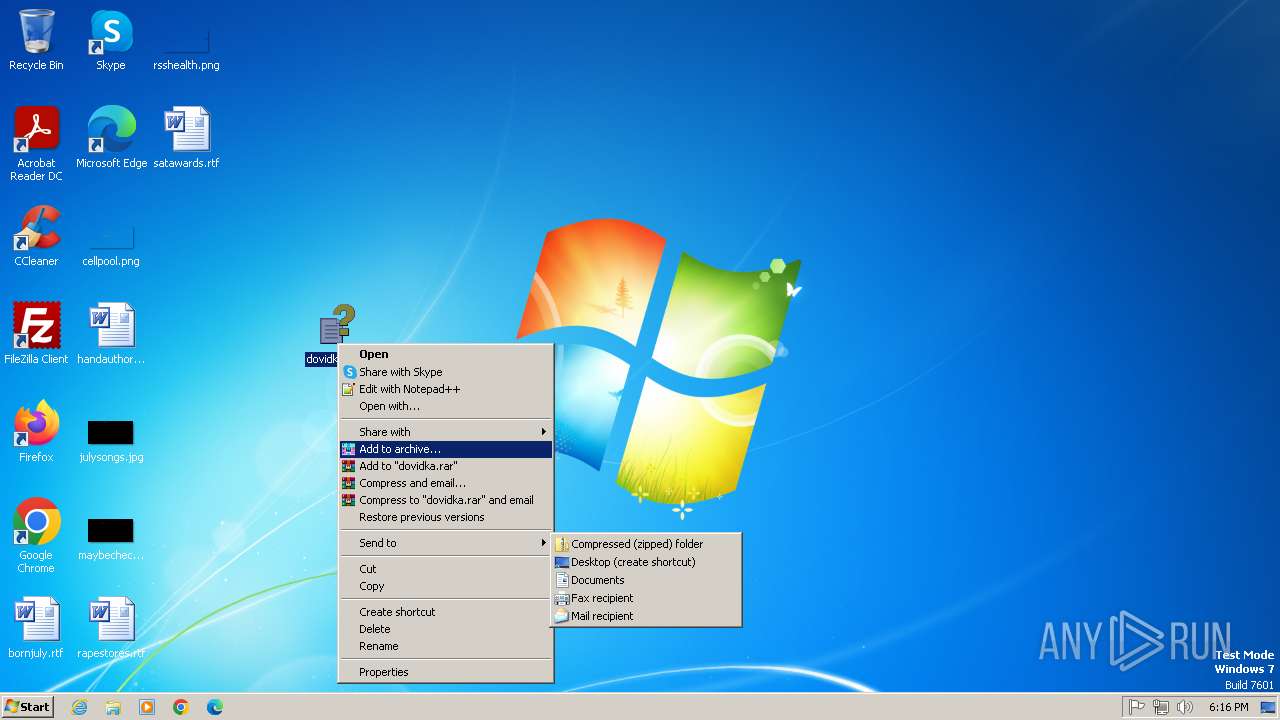
Create files in a temporary directory
- hh.exe (PID: 2060)
- hh.exe (PID: 3124)
Reads security settings of Internet Explorer
- hh.exe (PID: 2060)
- hh.exe (PID: 3124)
Checks proxy server information
- hh.exe (PID: 2060)
- RegAsm.exe (PID: 1824)
- hh.exe (PID: 3124)
Creates files or folders in the user directory
- hh.exe (PID: 2060)
Manual execution by a user
- hh.exe (PID: 3124)
Checks supported languages
- RegAsm.exe (PID: 1824)
Reads the computer name
- RegAsm.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .chi | | | Windows HELP Index (81) |
|---|---|---|
| .chm | | | Windows HELP File (18.9) |
EXIF
EXE
| CHMVersion: | 3 |
|---|---|
| LanguageCode: | English (U.S.) |
Total processes
39
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1824 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe" /U C:\Users\Public\Libraries\core.dll | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2060 | "C:\Windows\hh.exe" C:\Users\admin\Desktop\dovidka.chm | C:\Windows\hh.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | "C:\Windows\System32\wscript.exe" //B //E:vbs C:\Users\Public\Favorites\desktop.ini | C:\Windows\System32\wscript.exe | — | hh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2360 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\ignit.vbs" | C:\Windows\System32\wscript.exe | hh.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3124 | "C:\Windows\hh.exe" C:\Users\admin\Desktop\dovidka.chm | C:\Windows\hh.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 847
Read events
2 805
Write events
38
Delete events
4
Modification events
| (PID) Process: | (2060) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2060) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2060) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2060) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2060) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2060) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2060) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2332) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2332) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2332) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
1
Suspicious files
7
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2060 | hh.exe | C:\Users\Public\ignit.vbs | text | |
MD5:BD65D0D59F6127B28F0AF8A7F2619588 | SHA256:92F69DE0D45AD88654A6EEF720A6F6B6DB090AFB67BA0EBA5F9B77F504EA6280 | |||
| 1824 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\Tmp3F17.tmp | text | |
MD5:990E17CD51D14BBEACEE89F21B28705D | SHA256:DE22544C2A009F4ED7FAA2645CB6A4B889B81B1852F3FECDFEBB2D63A2078D72 | |||
| 2360 | wscript.exe | C:\Users\Public\Libraries\core.dll | executable | |
MD5:D2A795AF12E937EB8A89D470A96F15A5 | SHA256:E97F1D6EC1AA3F7C7973D57074D1D623833F0E9B1C1E53F81AF92C057A1FDD72 | |||
| 2060 | hh.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\image[1].jpg | image | |
MD5:9CF2EE018A565C00E811897E6056A5A2 | SHA256:CFD05F02C88A5E0385580E4DCE40F346713C6949DB34AC99E1AE15BB5B1591DD | |||
| 2060 | hh.exe | C:\Users\admin\AppData\Roaming\Microsoft\HTML Help\hh.dat | binary | |
MD5:275751C7F9CE6806026AD245DCF87CD4 | SHA256:640A1EF74CAFA8428D5DAABFB66DB29F64543018A8F75168282EA41B1B15E2C4 | |||
| 2360 | wscript.exe | C:\Users\Public\Favorites\desktop.ini | text | |
MD5:A9DCAF1C709F96BC125C8D1262BAC4B6 | SHA256:570EBD7F9951485B7415F685AE3349E62580309C9955B14DDA4734A318EDECA9 | |||
| 2360 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Windows Prefetch.lNk | binary | |
MD5:FB418BB5BD3E592651D0A4F9AE668962 | SHA256:C76FB28B6910BB0714FAB5B84363EBF2082FD59DDB0BB95166635583554D7AB4 | |||
| 3124 | hh.exe | C:\Users\admin\AppData\Local\Temp\~DF9770EDF991B9A358.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 2060 | hh.exe | C:\Users\admin\AppData\Local\Temp\~DF143BFDA422F8BD32.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 2060 | hh.exe | C:\Users\admin\AppData\Local\Temp\~DF9E31E455E6C8F586.TMP | binary | |
MD5:72F5C05B7EA8DD6059BF59F50B22DF33 | SHA256:1DC0C8D7304C177AD0E74D3D2F1002EB773F4B180685A7DF6BBE75CCC24B0164 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1824 | RegAsm.exe | 50.116.17.41:8443 | xbeta.online | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
xbeta.online |
| unknown |
dns.msftncsi.com |
| whitelisted |