| File name: | dovidka.chm |
| Full analysis: | https://app.any.run/tasks/b3d56bc2-951c-467b-8c87-560d2caf0ddf |
| Verdict: | Malicious activity |
| Threats: | Trojans are a group of malicious programs distinguished by their ability to masquerade as benign software. Depending on their type, trojans possess a variety of capabilities, ranging from maintaining full remote control over the victim’s machine to stealing data and files, as well as dropping other malware. At the same time, the main functionality of each trojan family can differ significantly depending on its type. The most common trojan infection chain starts with a phishing email. |
| Analysis date: | October 05, 2022, 00:52:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows HtmlHelp Data |
| MD5: | 2556A9E1D5E9874171F51620E5C5E09A |
| SHA1: | AFFC2B19D9FB8080A7211C3ED0718F2C3D3887DF |
| SHA256: | 7F0511B09B1AB3A64C8827DD8AF017ACBF7D2688DB31A5D98FEA8A5029A89D56 |
| SSDEEP: | 6144:6hK9QF9IF78JuiKgnheEVfh+x6I/c0mGkBZ6w5+2yrBnx:d9QFq78JuiBnheEVqvcBZ6ws7nx |
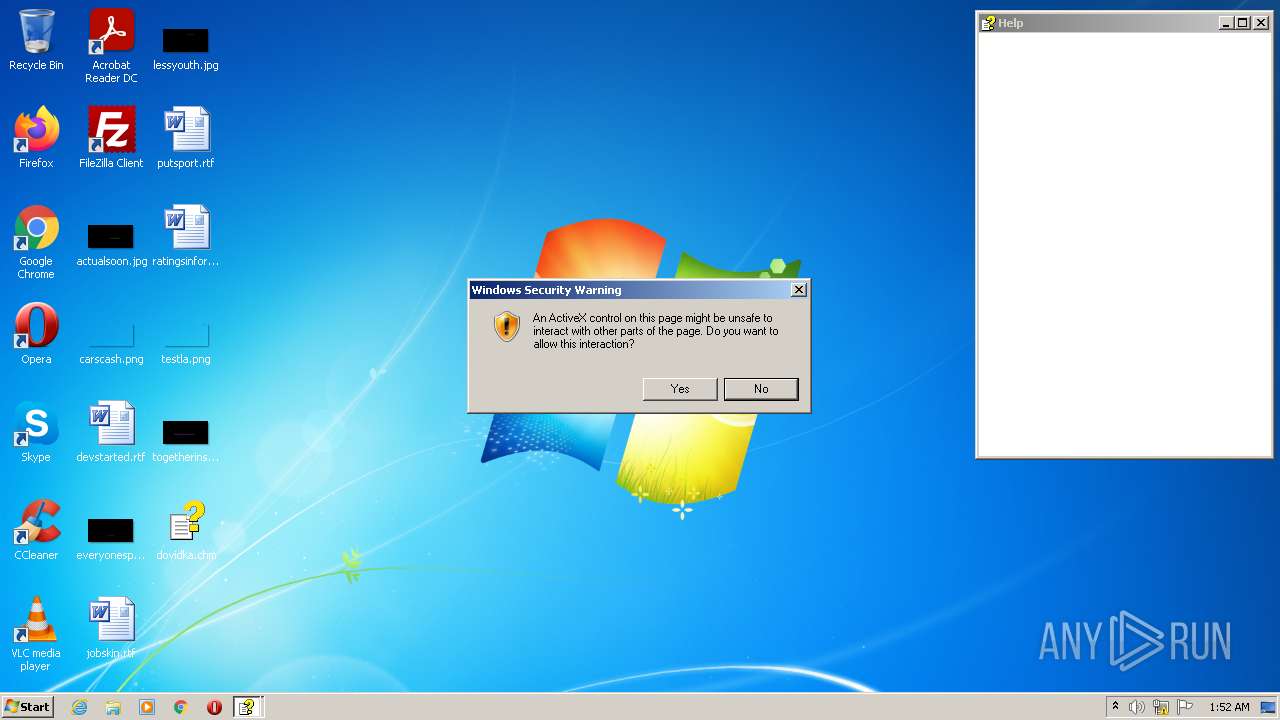
MALICIOUS
Drops executable file immediately after starts
- WScript.exe (PID: 3836)
- chrome.exe (PID: 3672)
Writes to a start menu file
- WScript.exe (PID: 3836)
Loads dropped or rewritten executable
- regasm.exe (PID: 2744)
SUSPICIOUS
Reads Microsoft Outlook installation path
- hh.exe (PID: 968)
Executes scripts
- hh.exe (PID: 968)
Reads the computer name
- WScript.exe (PID: 3836)
- wscript.exe (PID: 2156)
- regasm.exe (PID: 2744)
- vlc.exe (PID: 2360)
Checks supported languages
- WScript.exe (PID: 3836)
- wscript.exe (PID: 2156)
- regasm.exe (PID: 2744)
- vlc.exe (PID: 2360)
Writes to a desktop.ini file (may be used to cloak folders)
- WScript.exe (PID: 3836)
Drops a file with a compile date too recent
- WScript.exe (PID: 3836)
- chrome.exe (PID: 3672)
Reads internet explorer settings
- hh.exe (PID: 968)
Executable content was dropped or overwritten
- WScript.exe (PID: 3836)
- chrome.exe (PID: 3672)
Creates files in the user directory
- WScript.exe (PID: 3836)
- vlc.exe (PID: 2360)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3136)
INFO
Checks supported languages
- hh.exe (PID: 968)
- WINWORD.EXE (PID: 2540)
- firefox.exe (PID: 3420)
- firefox.exe (PID: 2724)
- firefox.exe (PID: 588)
- firefox.exe (PID: 1368)
- firefox.exe (PID: 3544)
- firefox.exe (PID: 1968)
- firefox.exe (PID: 4020)
- firefox.exe (PID: 2652)
- opera.exe (PID: 2408)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 1084)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 1752)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 996)
- chrome.exe (PID: 360)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 728)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 1492)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2064)
- chrome.exe (PID: 1752)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 684)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 4580)
- chrome.exe (PID: 704)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 5024)
- chrome.exe (PID: 5276)
- chrome.exe (PID: 4564)
- chrome.exe (PID: 5852)
- chrome.exe (PID: 5144)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 5812)
- chrome.exe (PID: 5660)
- chrome.exe (PID: 4664)
- chrome.exe (PID: 1308)
- chrome.exe (PID: 5640)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 320)
- chrome.exe (PID: 980)
- chrome.exe (PID: 5372)
- chrome.exe (PID: 4244)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 4232)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 4292)
- chrome.exe (PID: 4588)
- chrome.exe (PID: 4276)
- chrome.exe (PID: 1176)
- chrome.exe (PID: 4336)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 5876)
- chrome.exe (PID: 4572)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 4460)
- chrome.exe (PID: 4652)
- chrome.exe (PID: 1884)
- chrome.exe (PID: 1404)
- chrome.exe (PID: 4568)
- chrome.exe (PID: 5000)
- chrome.exe (PID: 5176)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 5304)
- chrome.exe (PID: 5616)
- chrome.exe (PID: 768)
- chrome.exe (PID: 6044)
- chrome.exe (PID: 5952)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 4648)
Reads the computer name
- hh.exe (PID: 968)
- WINWORD.EXE (PID: 2540)
- firefox.exe (PID: 3420)
- firefox.exe (PID: 588)
- firefox.exe (PID: 1368)
- firefox.exe (PID: 4020)
- firefox.exe (PID: 1968)
- firefox.exe (PID: 2652)
- firefox.exe (PID: 3544)
- opera.exe (PID: 2408)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 1084)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 996)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 5852)
Checks Windows Trust Settings
- WScript.exe (PID: 3836)
- wscript.exe (PID: 2156)
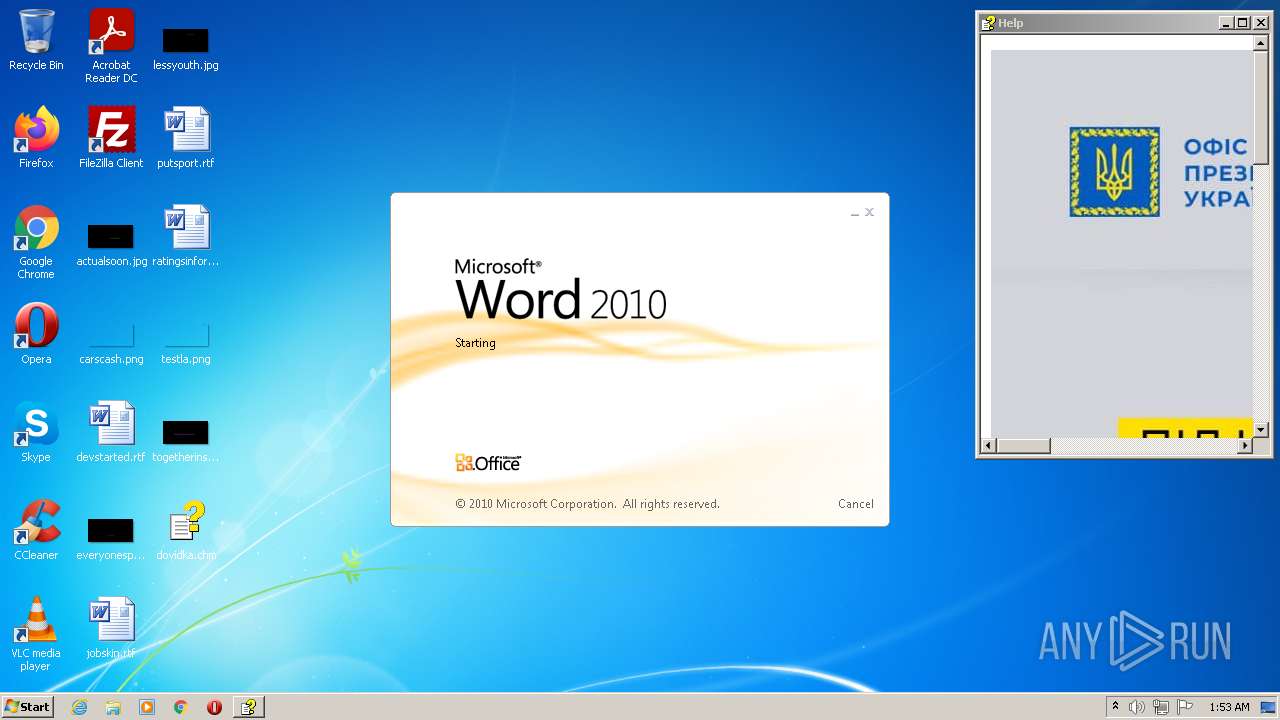
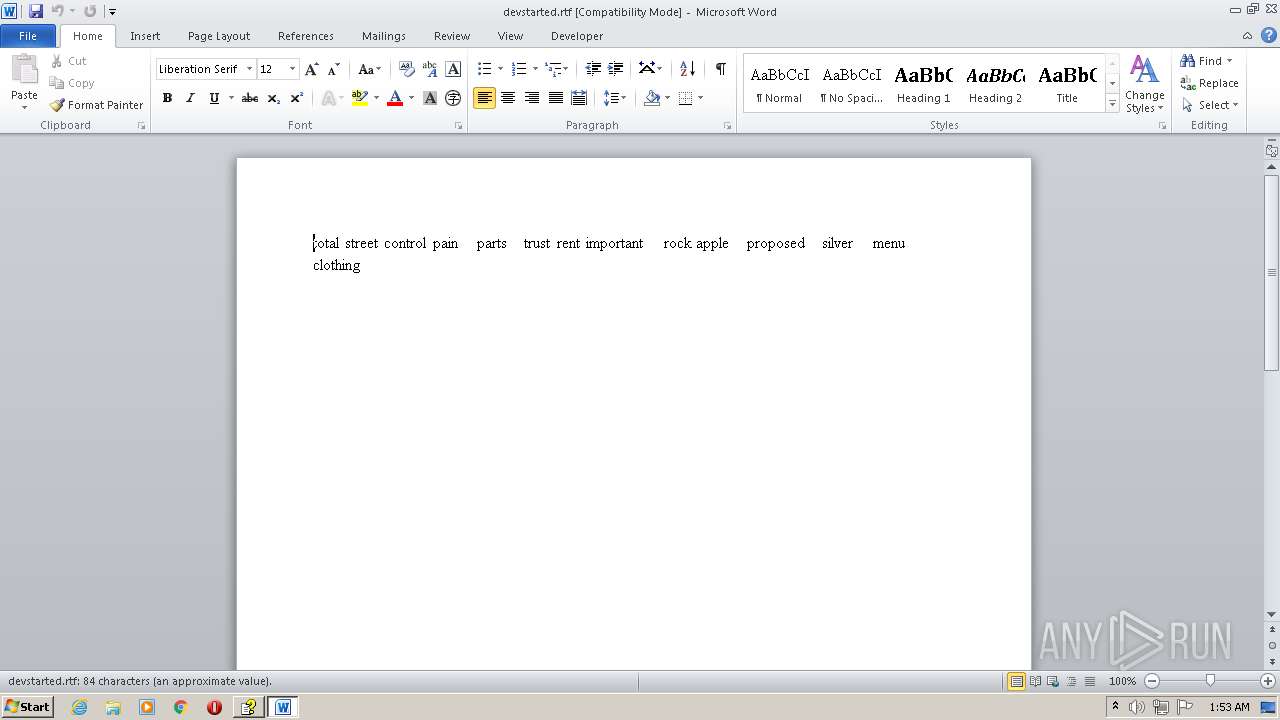
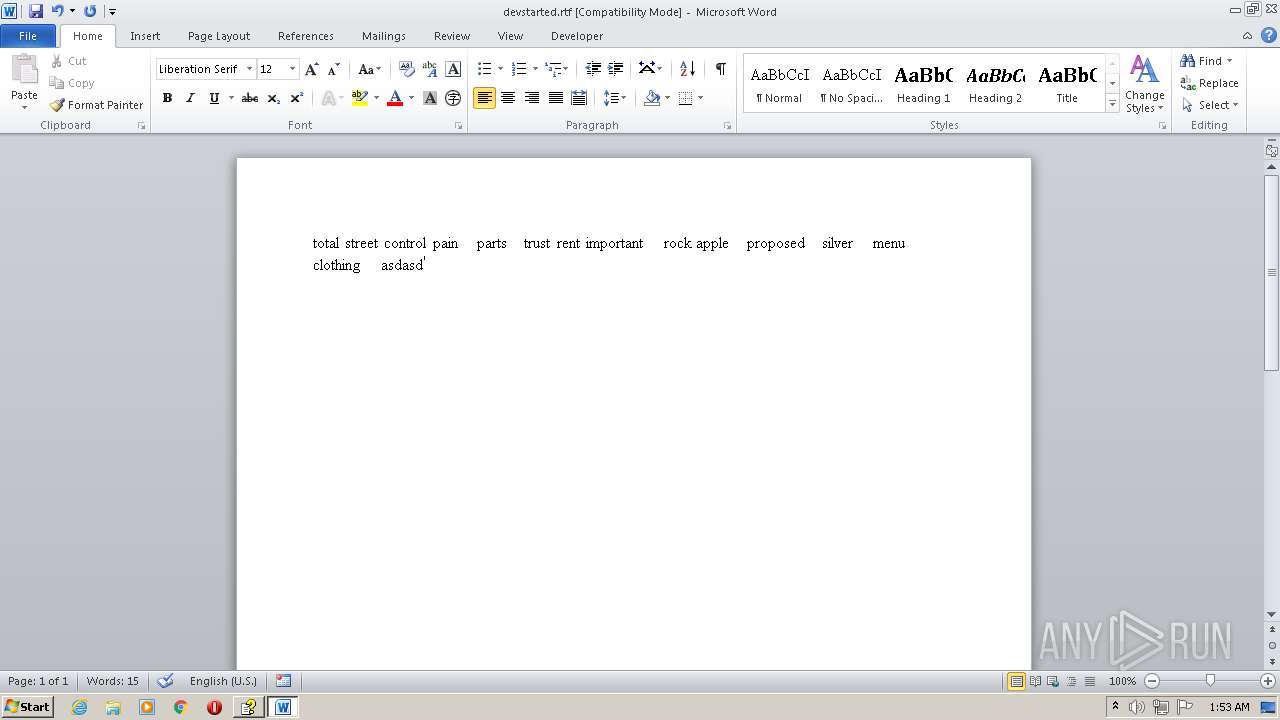
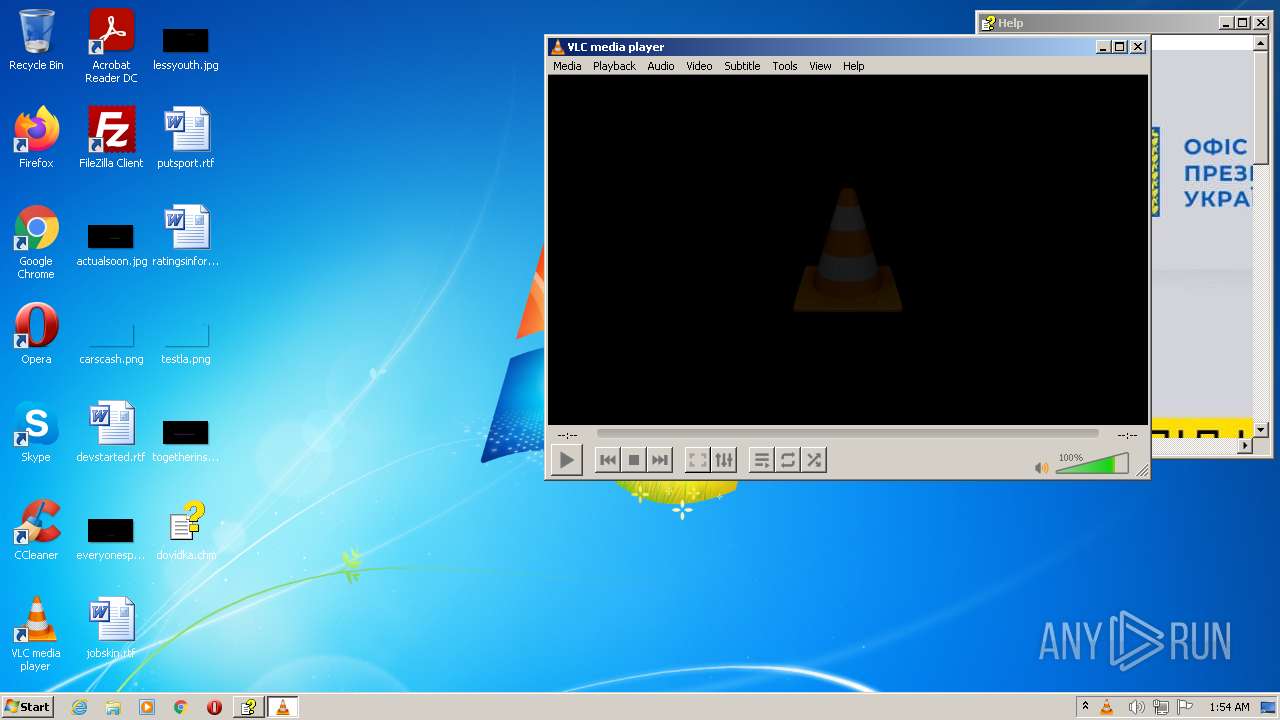
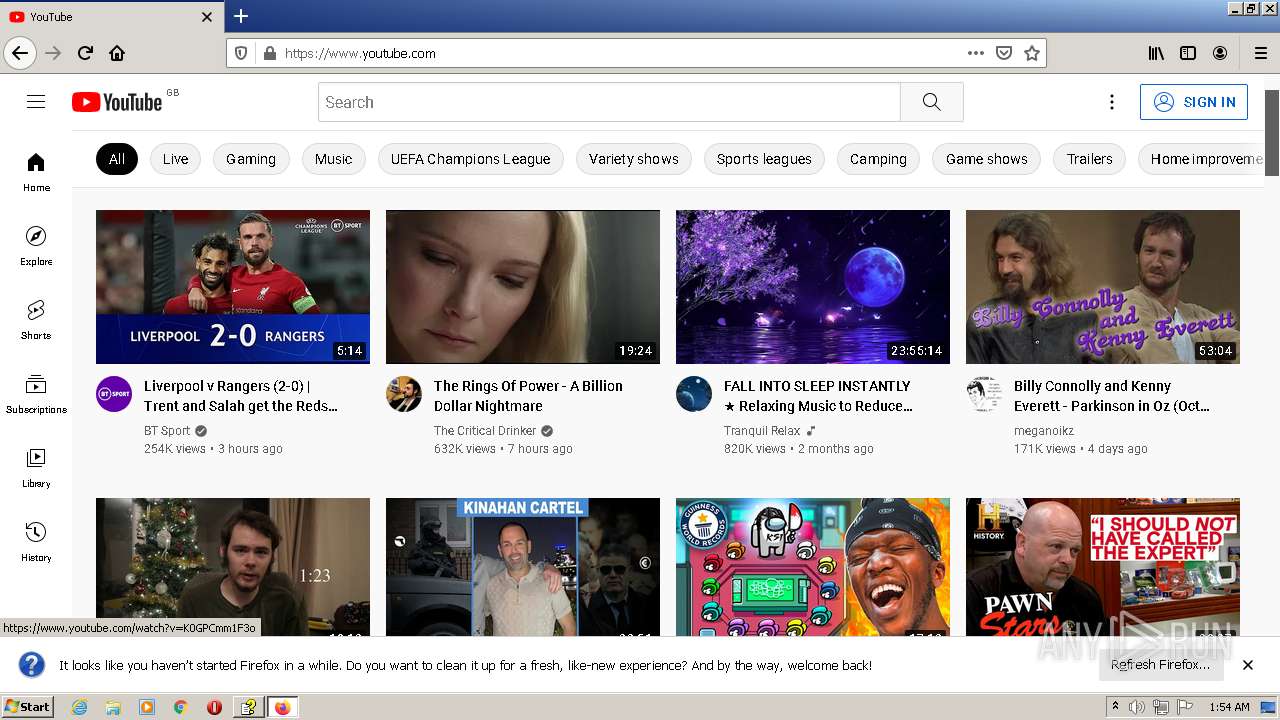
Manual execution by user
- WINWORD.EXE (PID: 2540)
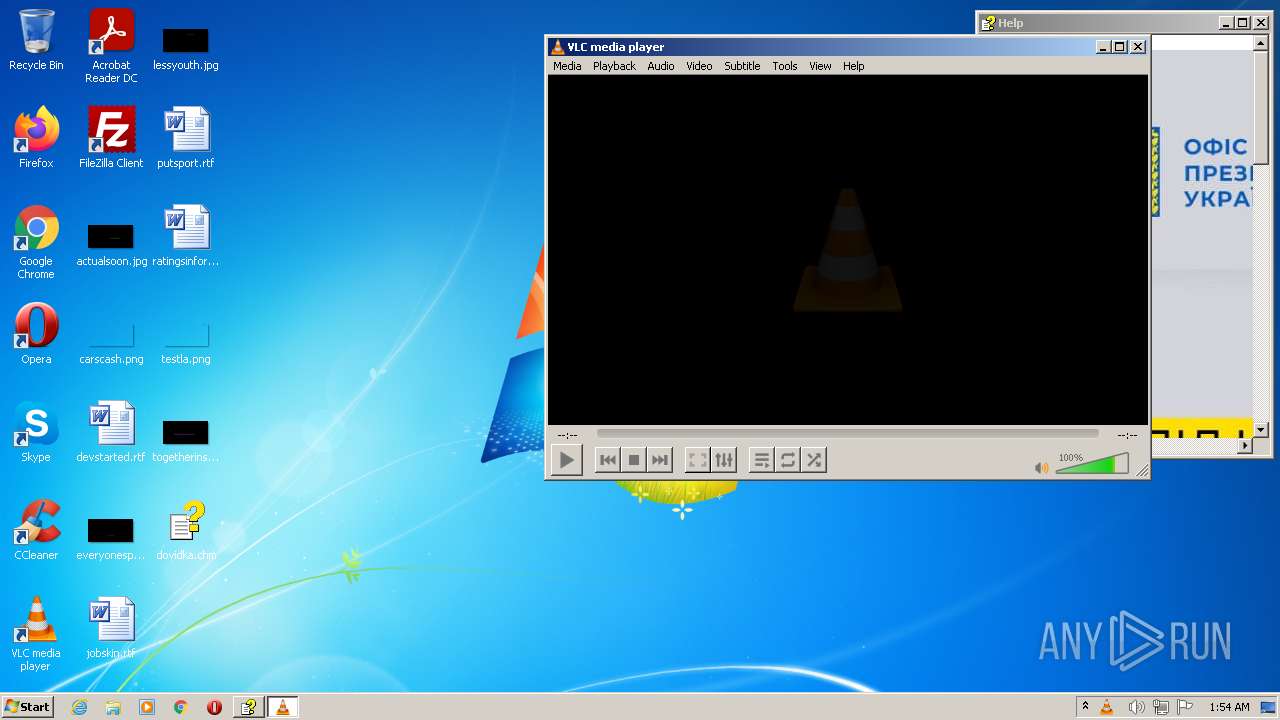
- vlc.exe (PID: 2360)
- firefox.exe (PID: 2724)
- opera.exe (PID: 2408)
- chrome.exe (PID: 3136)
Application launched itself
- firefox.exe (PID: 2724)
- firefox.exe (PID: 3420)
- chrome.exe (PID: 3136)
Creates files in the user directory
- WINWORD.EXE (PID: 2540)
- opera.exe (PID: 2408)
- firefox.exe (PID: 3420)
Reads CPU info
- firefox.exe (PID: 3420)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2540)
Creates files in the program directory
- firefox.exe (PID: 3420)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3420)
- opera.exe (PID: 2408)
Reads the date of Windows installation
- firefox.exe (PID: 3420)
- opera.exe (PID: 2408)
- chrome.exe (PID: 3144)
Check for Java to be installed
- opera.exe (PID: 2408)
Reads the hosts file
- chrome.exe (PID: 3136)
- chrome.exe (PID: 1084)
Reads settings of System Certificates
- chrome.exe (PID: 1084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .chm | | | Windows HELP File (18.9) |
|---|
Total processes
151
Monitored processes
109
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3420.0.20748921\510117654" -parentBuildID 20201112153044 -prefsHandle 1104 -prefMapHandle 1096 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3420 "\\.\pipe\gecko-crash-server-pipe.3420" 1176 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 83.0 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=6108 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=91 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Windows\hh.exe" "C:\Users\admin\Desktop\dovidka.chm" | C:\Windows\hh.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,2903740483907508011,12346867624444929440,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
55 039
Read events
53 946
Write events
941
Delete events
152
Modification events
| (PID) Process: | (968) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (968) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (968) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (968) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (968) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (968) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (968) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2156) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2156) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2156) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
2
Suspicious files
716
Text files
444
Unknown types
105
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR312D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2360 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\ml.xspf | — | |
MD5:— | SHA256:— | |||
| 3420 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2540 | WINWORD.EXE | C:\Users\admin\Desktop\~$vstarted.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{26D7861D-0F71-4E03-B2E1-B27EBB851309}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{2587F01D-18FC-47D1-9293-DF09203CED94}.tmp | dbf | |
MD5:— | SHA256:— | |||
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\devstarted.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3836 | WScript.exe | C:\usErs\puBLIC\fAVORIteS\desktop.ini | text | |
MD5:A9DCAF1C709F96BC125C8D1262BAC4B6 | SHA256:570EBD7F9951485B7415F685AE3349E62580309C9955B14DDA4734A318EDECA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
598
DNS requests
437
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
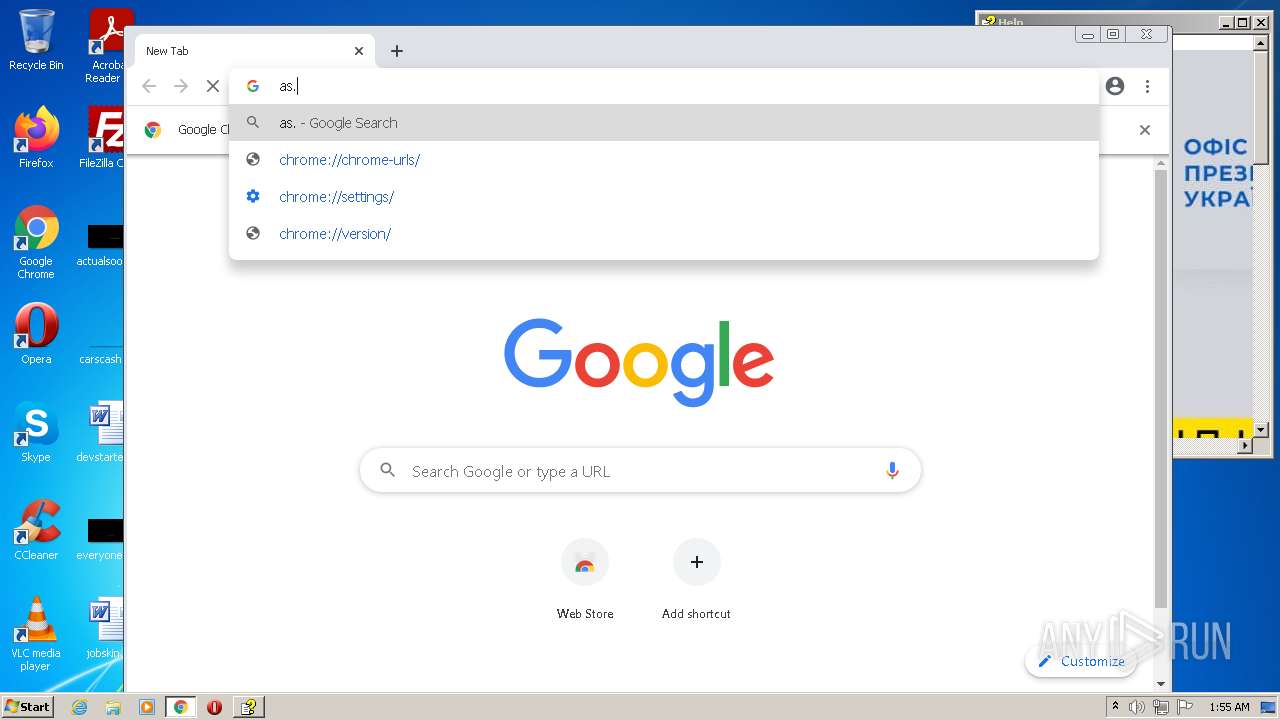
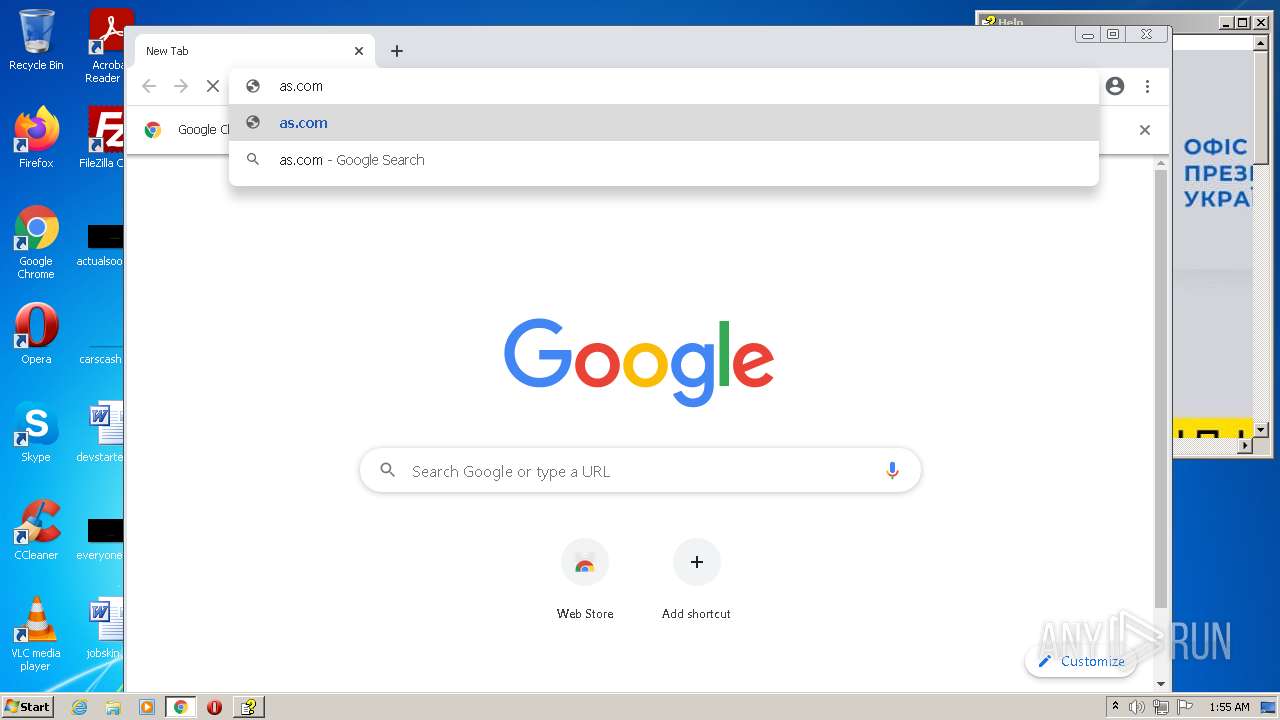
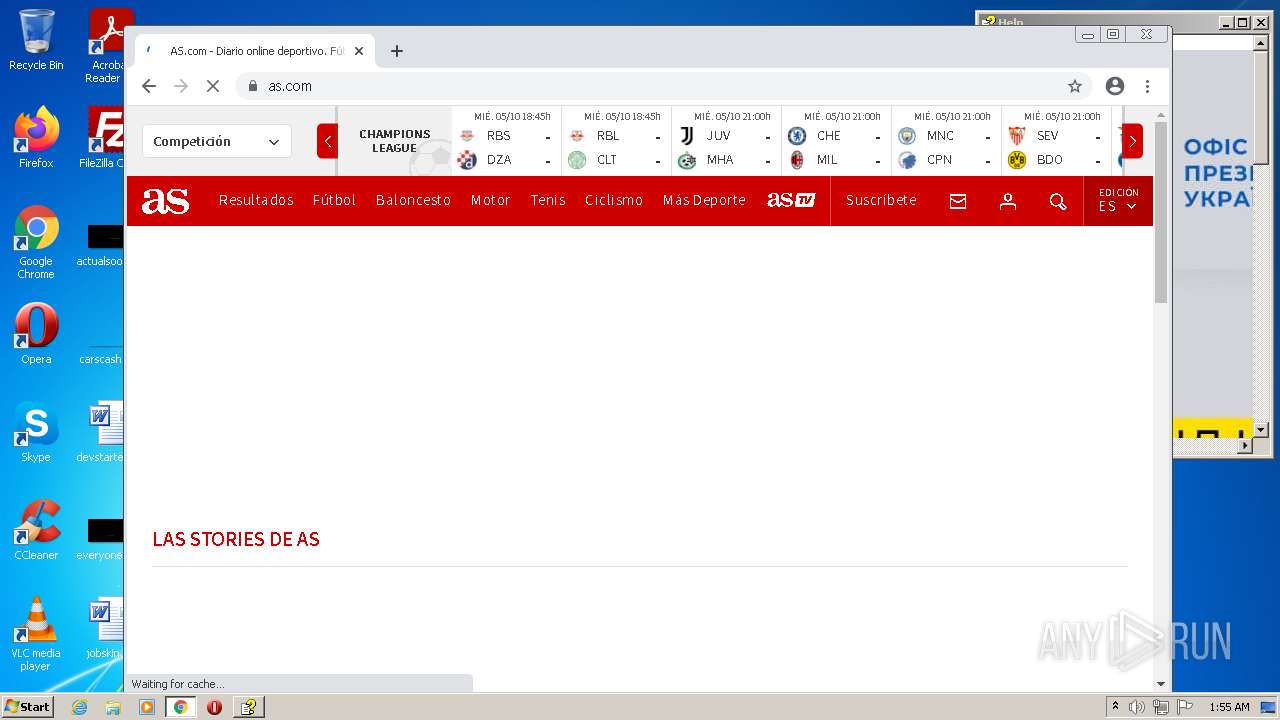
1084 | chrome.exe | GET | 301 | 23.216.77.73:80 | http://as.com/ | US | — | — | whitelisted |
3420 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3420 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3420 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3420 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3420 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3420 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3420 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3420 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
1084 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?199d9ced671f3d25 | US | compressed | 60.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3420 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
— | — | 194.195.211.98:8443 | xbeta.online | Linode, LLC | US | malicious |
3420 | firefox.exe | 13.224.189.85:443 | firefox.settings.services.mozilla.com | AMAZON-02 | US | suspicious |
3420 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3420 | firefox.exe | 52.41.132.37:443 | location.services.mozilla.com | AMAZON-02 | US | unknown |
3420 | firefox.exe | 13.225.78.78:443 | content-signature-2.cdn.mozilla.net | AMAZON-02 | US | suspicious |
3420 | firefox.exe | 142.250.184.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
3420 | firefox.exe | 142.250.186.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3420 | firefox.exe | 54.202.70.174:443 | push.services.mozilla.com | AMAZON-02 | US | unknown |
3420 | firefox.exe | 13.225.78.92:443 | firefox-settings-attachments.cdn.mozilla.net | AMAZON-02 | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xbeta.online |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET TROJAN TA445/Ghostwrite APT Related Domain in DNS Lookup (xbeta .online) |
3420 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3420 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1084 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|