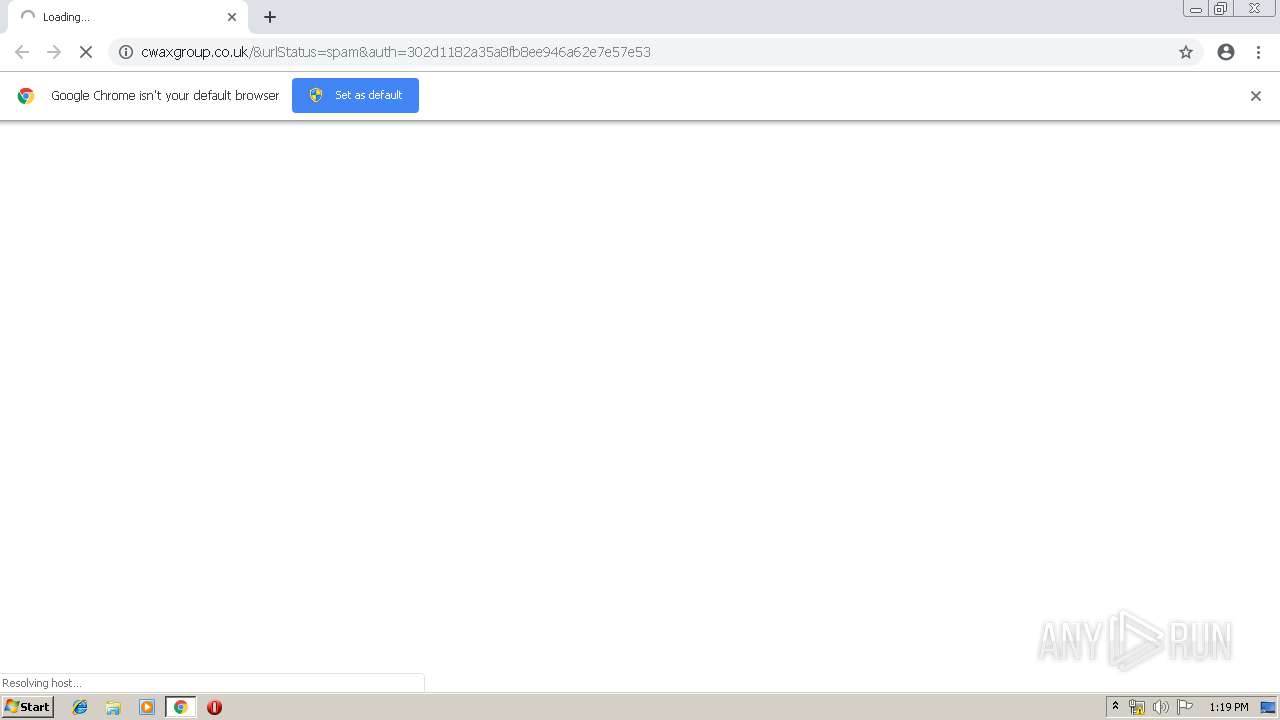
| URL: | http://cwaxgroup.co.uk/&urlStatus=spam&auth=302d1182a35a8fb8ee946a62e7e57e53 |
| Full analysis: | https://app.any.run/tasks/3345e84c-5593-483c-9cc1-03b6a0b7389b |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 12:19:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6E478FBB04F6045254935B36FE3D5F0D |
| SHA1: | E9E8139B97FD669EC22C5498D76E1700DC92D616 |
| SHA256: | 7EFB4AEB5D2B4F38A5AE5B35A8892D081D3D786068D5AE470F8CDB217559881B |
| SSDEEP: | 3:N1KdSEyLhJx1bVESBnRxdAr5QzQW:CQEyhsSBnRbE5QH |
MALICIOUS
Application was dropped or rewritten from another process
- 7z_9580634896962885875967033165897.exe (PID: 4080)
- python.exe (PID: 1012)
Loads dropped or rewritten executable
- python.exe (PID: 1012)
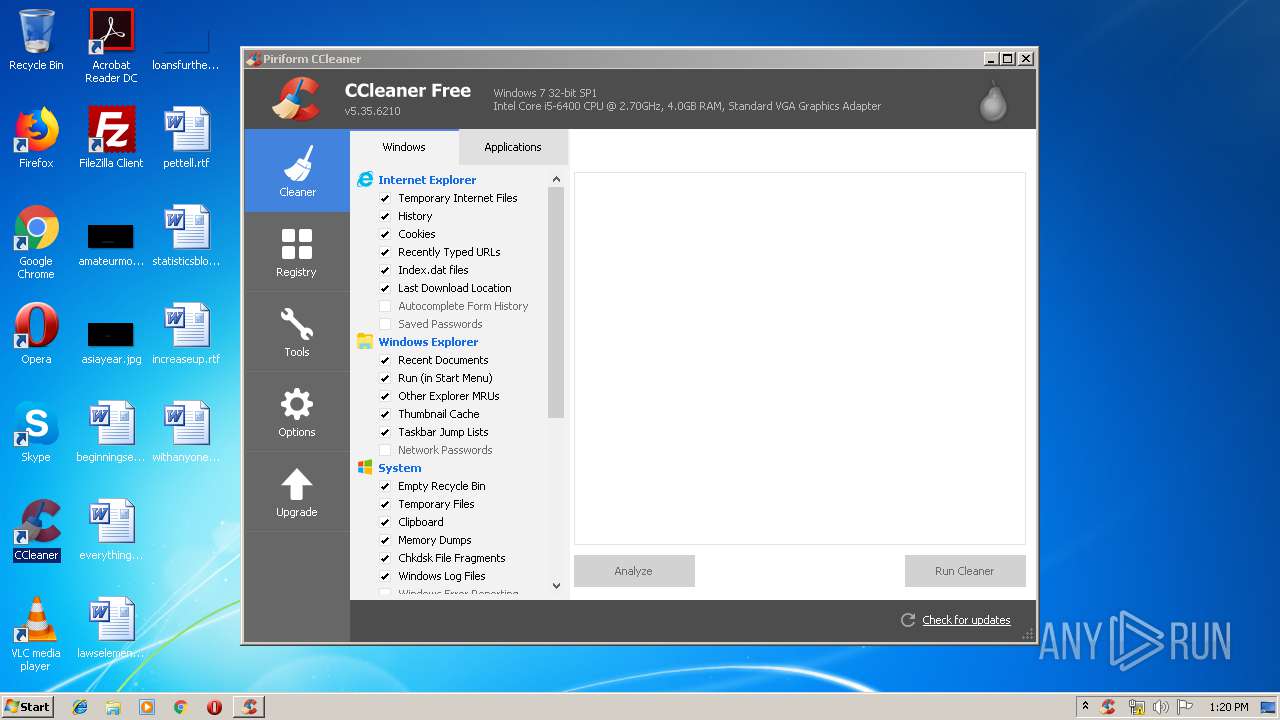
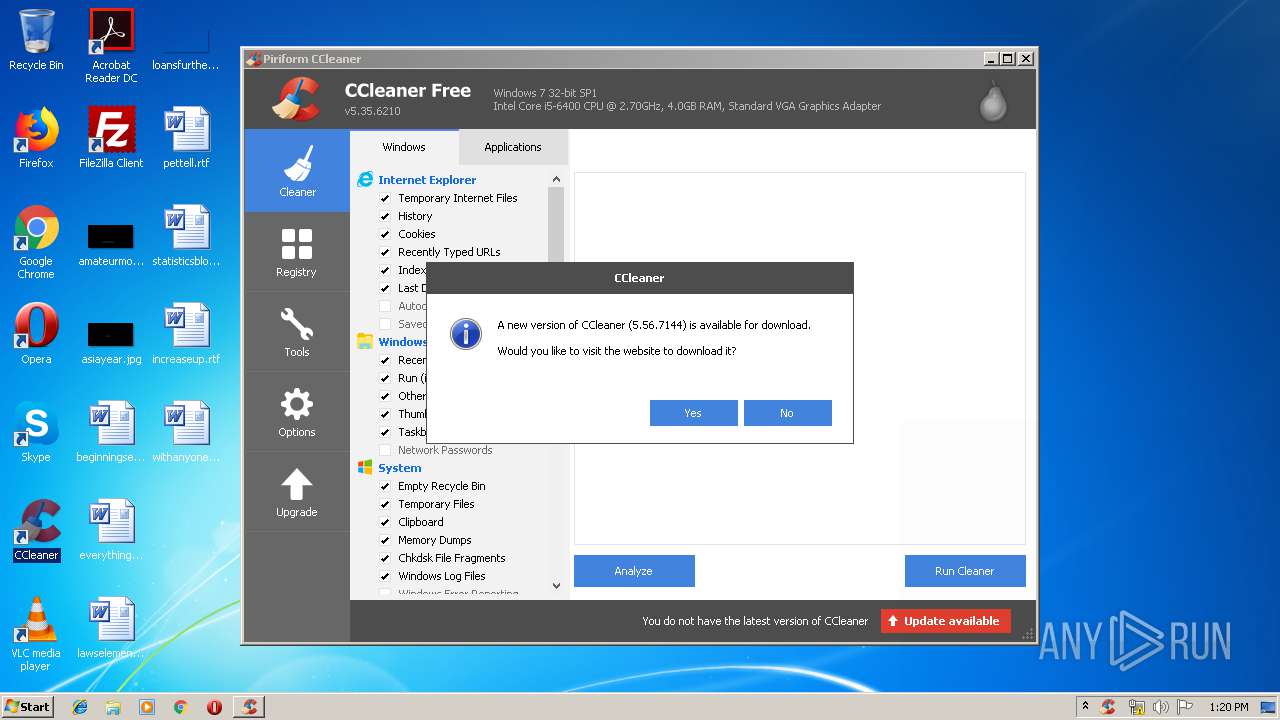
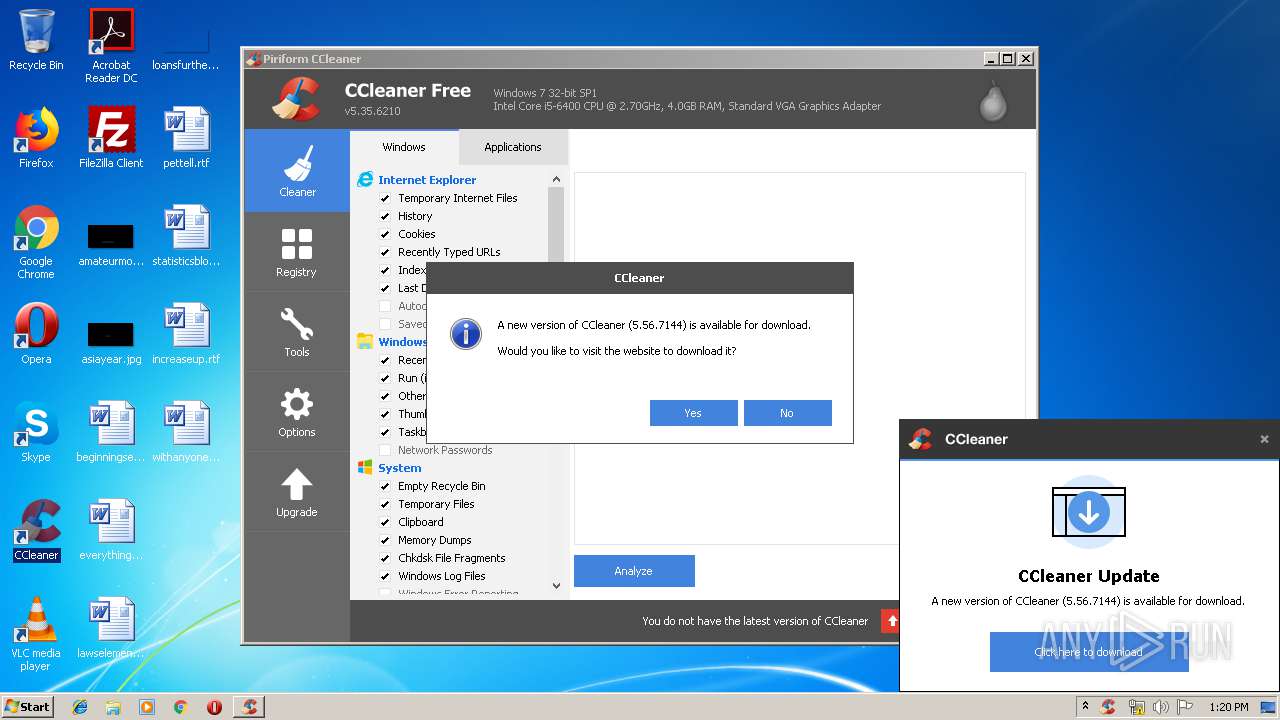
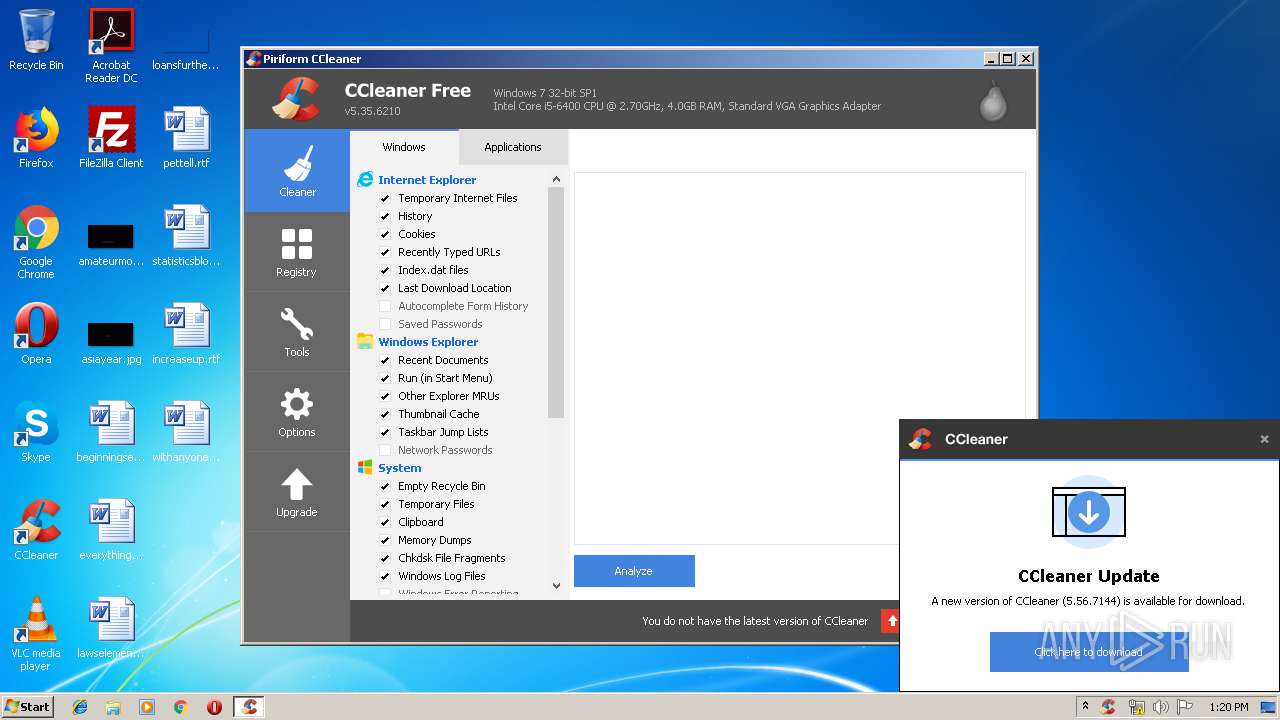
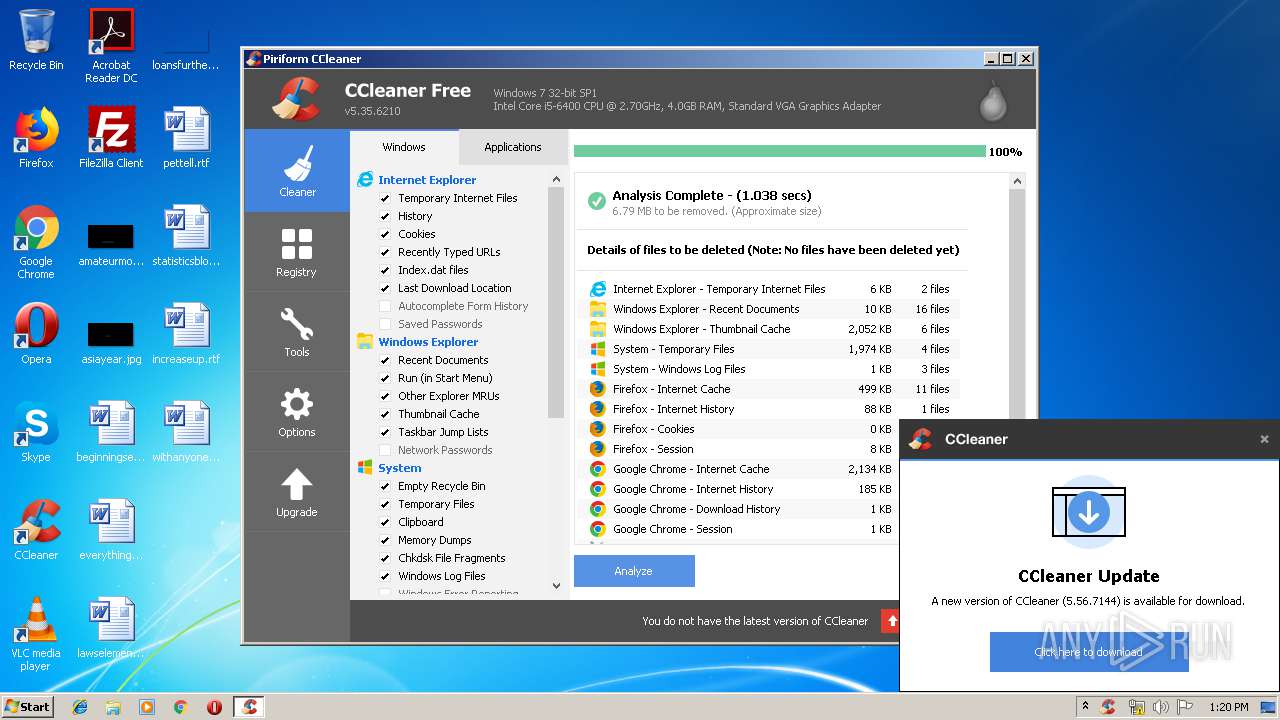
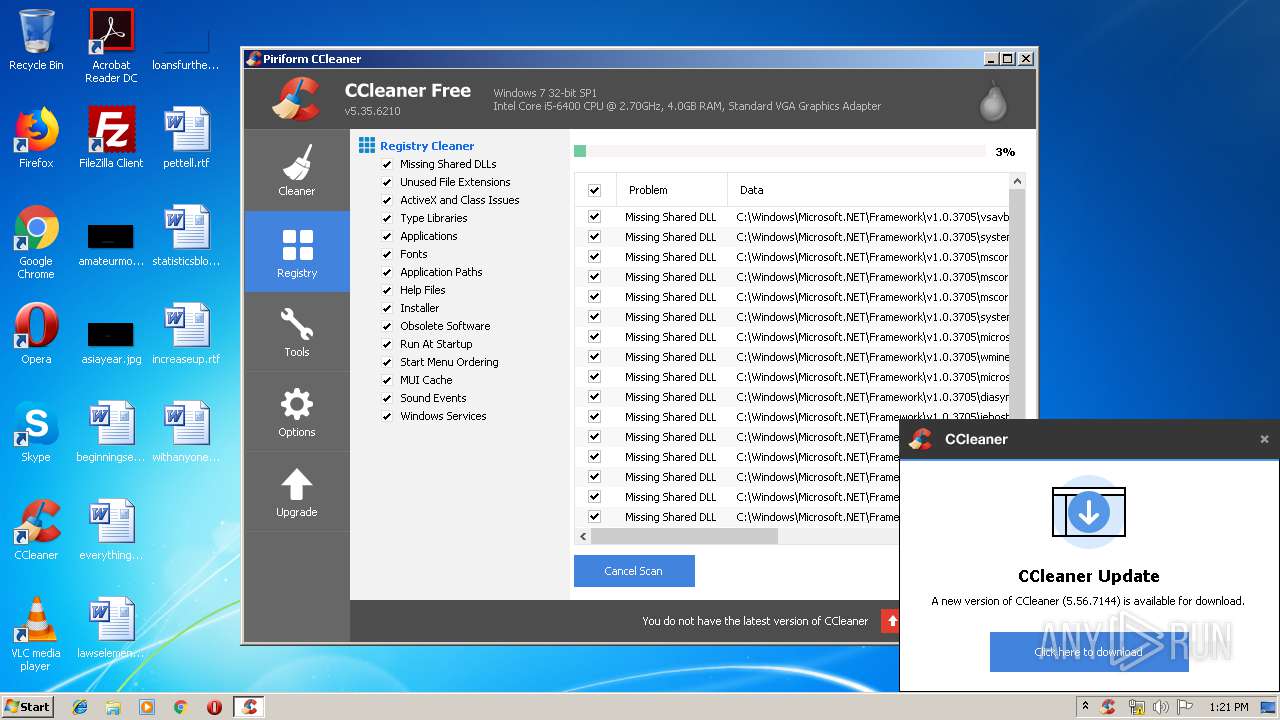
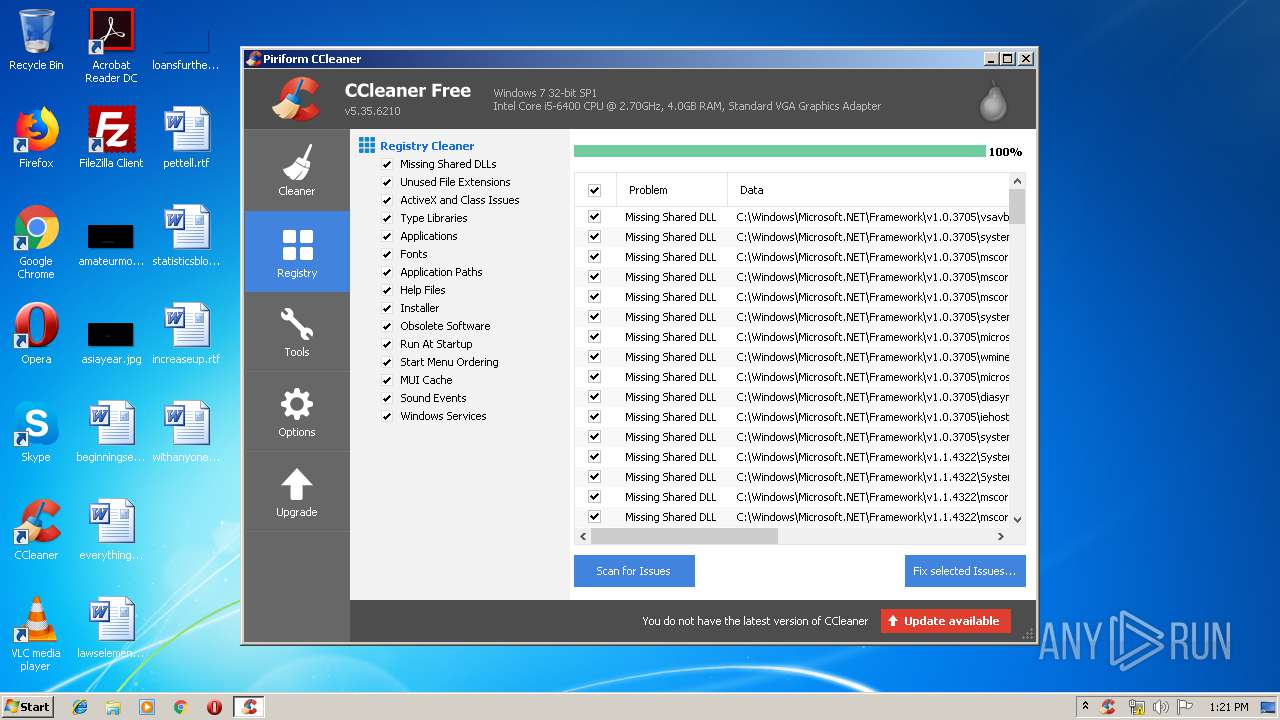
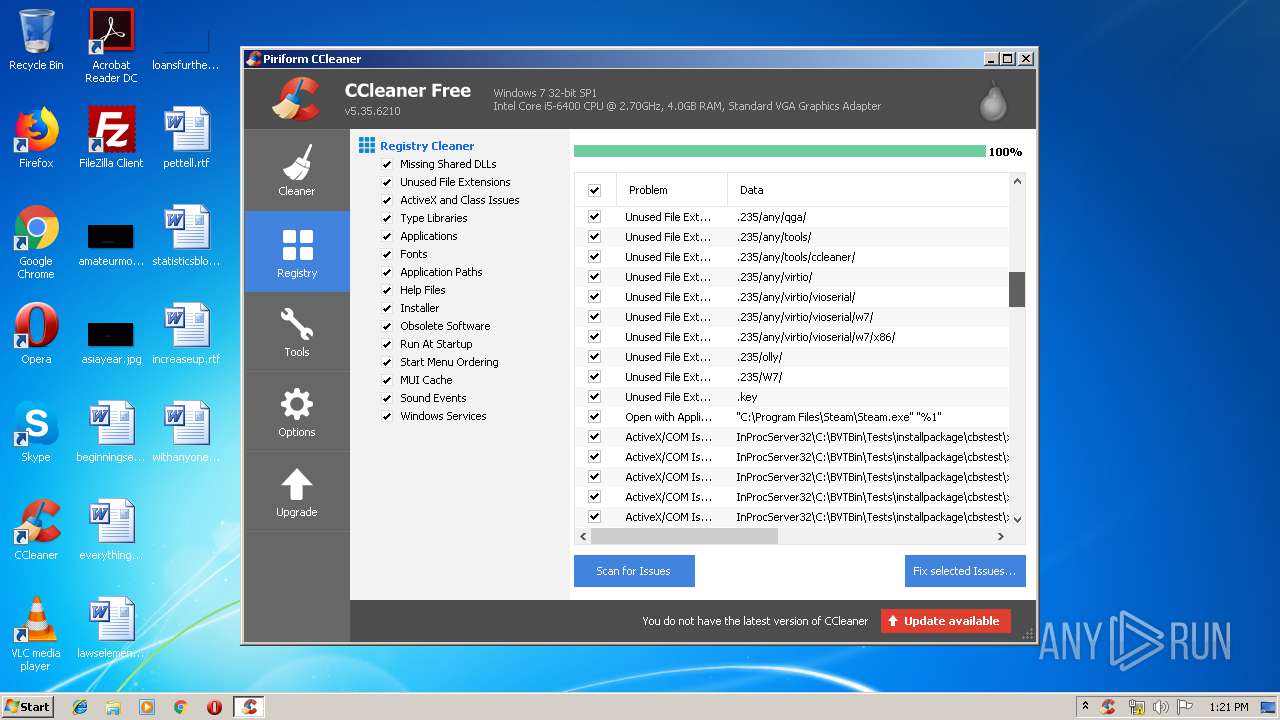
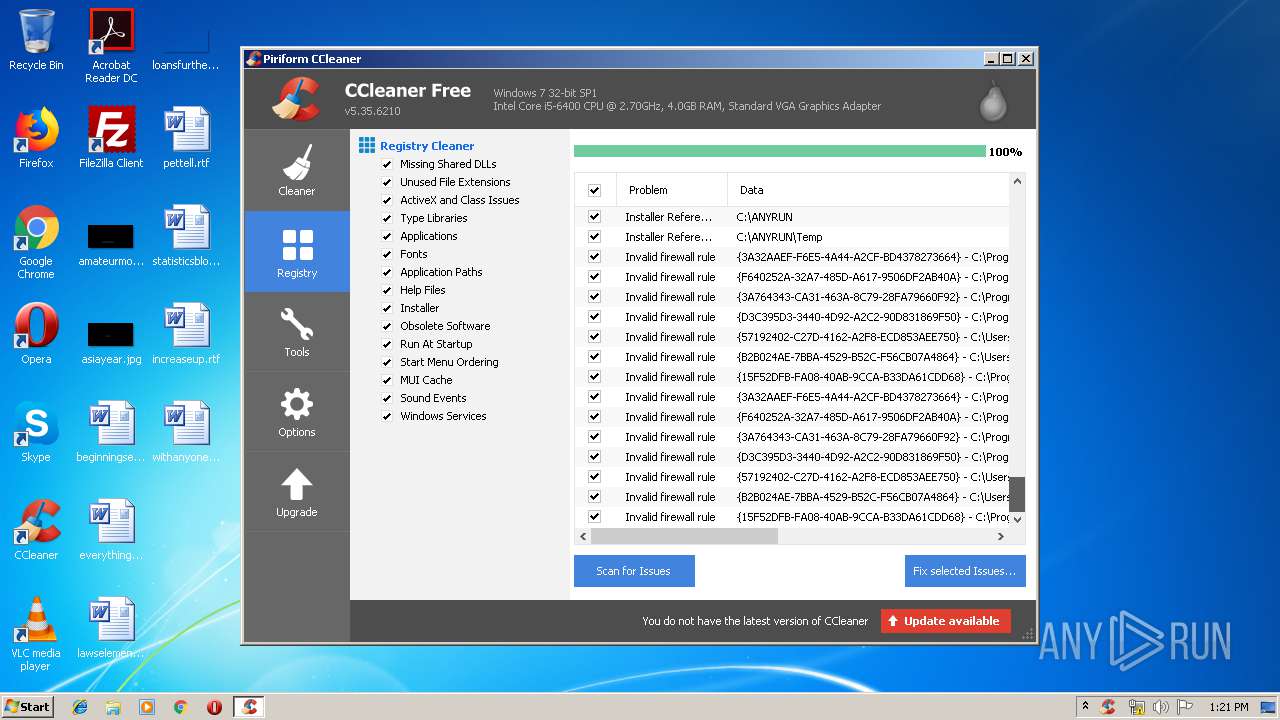
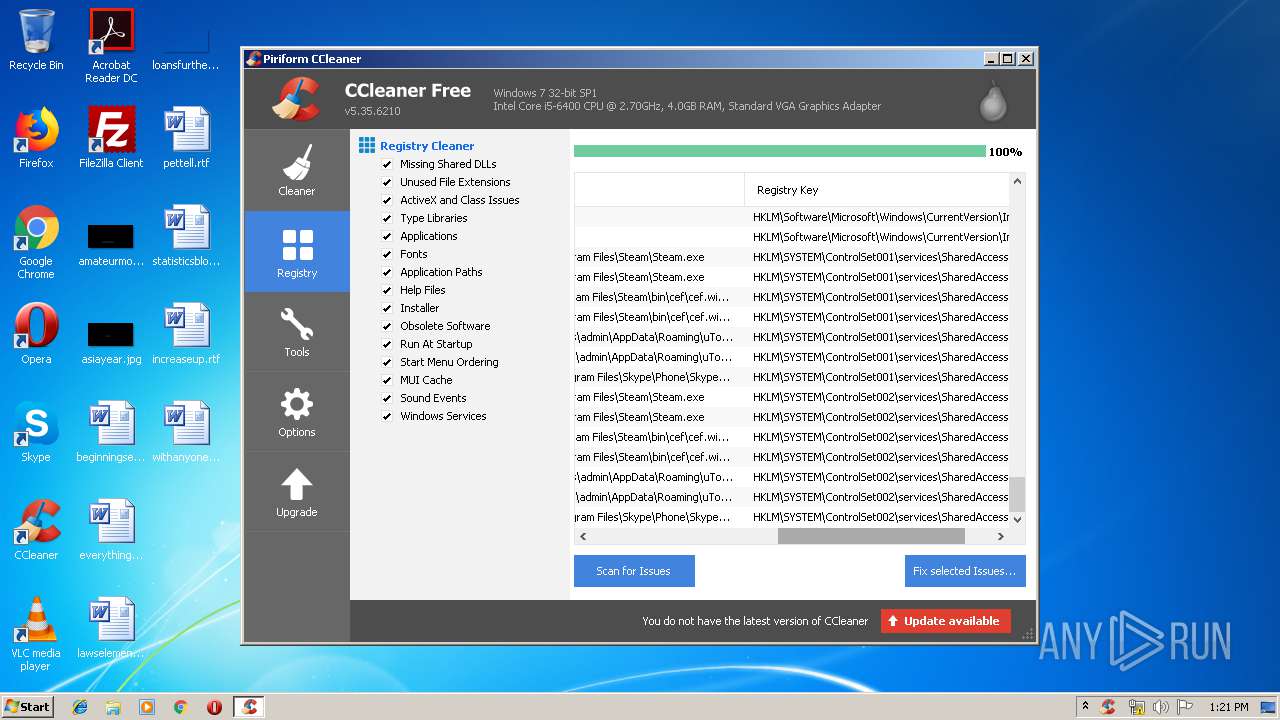
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2704)
- CCleaner.exe (PID: 2688)
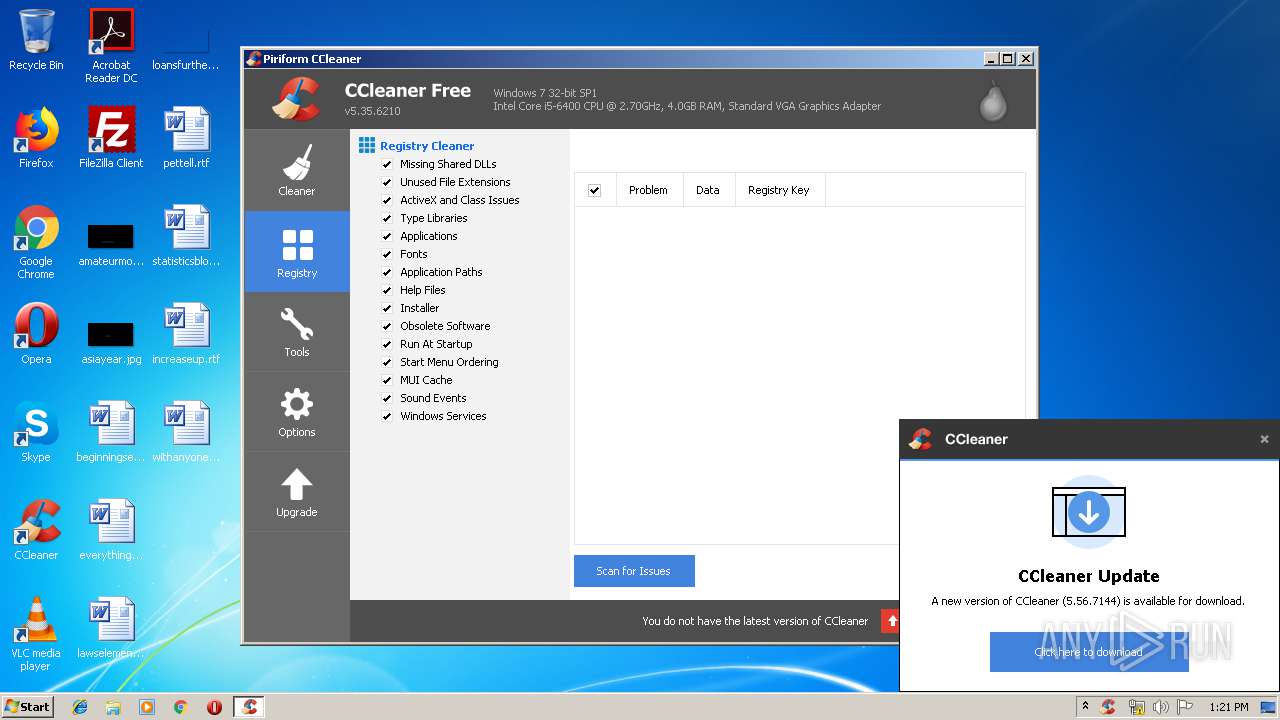
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2720)
- CCleaner.exe (PID: 2688)
Changes the autorun value in the registry
- CCleaner.exe (PID: 2688)
Changes settings of System certificates
- CCleaner.exe (PID: 2704)
SUSPICIOUS
Executable content was dropped or overwritten
- javaw.exe (PID: 2592)
- 7z_9580634896962885875967033165897.exe (PID: 4080)
Creates files in the user directory
- javaw.exe (PID: 2592)
- CCleaner.exe (PID: 2704)
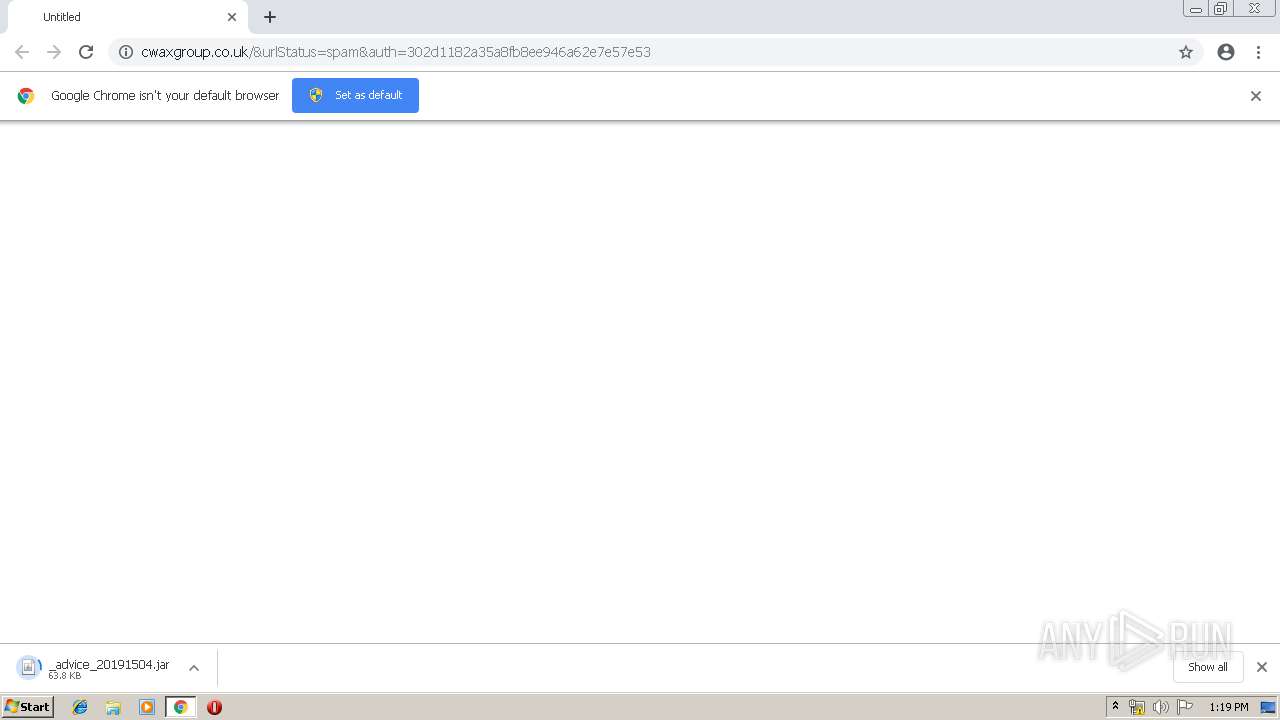
Executes JAVA applets
- chrome.exe (PID: 1840)
Loads Python modules
- python.exe (PID: 1012)
Reads internet explorer settings
- CCleaner.exe (PID: 2704)
- CCleaner.exe (PID: 2688)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2704)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 2704)
Application launched itself
- CCleaner.exe (PID: 2704)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 2704)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 2704)
Searches for installed software
- CCleaner.exe (PID: 2704)
INFO
Application launched itself
- chrome.exe (PID: 1840)
Dropped object may contain Bitcoin addresses
- 7z_9580634896962885875967033165897.exe (PID: 4080)
Reads settings of System Certificates
- CCleaner.exe (PID: 2704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
17
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9298353333955982905 --mojo-platform-channel-handle=3616 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1012 | C:\Users\admin\AppData\Local\Temp\qealler\python\python.exe C:\Users\admin\AppData\Local\Temp\qealler\qazaqne\main.py all | C:\Users\admin\AppData\Local\Temp\qealler\python\python.exe | — | javaw.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2022053733350711005 --mojo-platform-channel-handle=904 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://cwaxgroup.co.uk/&urlStatus=spam&auth=302d1182a35a8fb8ee946a62e7e57e53 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1816 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --service-pipe-token=7683669283456400078 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7683669283456400078 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\_advice_20191504.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | chrome.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,12110062789084723439,2122016938119799528,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4909595769743618656 --mojo-platform-channel-handle=1884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2704 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
Total events
1 700
Read events
1 440
Write events
256
Delete events
4
Modification events
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1840-13199804360043125 |
Value: 259 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1840) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
34
Suspicious files
32
Text files
73
Unknown types
373
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a19155e7-7188-47d6-8478-79202dcfbc1e.tmp | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 1840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
18
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | chrome.exe | GET | 301 | 184.168.131.241:80 | http://cwaxgroup.co.uk/&urlStatus=spam&auth=302d1182a35a8fb8ee946a62e7e57e53 | US | — | — | malicious |
2704 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
2592 | javaw.exe | POST | 200 | 188.166.150.227:8959 | http://188.166.150.227:8959/qealler-reloaded/ping | GB | text | 108 b | suspicious |
2592 | javaw.exe | GET | 200 | 188.166.150.227:8298 | http://188.166.150.227:8298/lib/qealler | GB | compressed | 1.84 Mb | suspicious |
3896 | chrome.exe | GET | 200 | 27.254.85.195:80 | http://silantavillage.com/libraries/simplepie/_advice_20191504.jar | TH | java | 208 Kb | suspicious |
2592 | javaw.exe | GET | 200 | 188.166.150.227:8879 | http://188.166.150.227:8879/lib/7z | GB | java | 576 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3896 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 184.168.131.241:80 | cwaxgroup.co.uk | GoDaddy.com, LLC | US | shared |
3896 | chrome.exe | 27.254.85.195:80 | silantavillage.com | CS LOXINFO Public Company Limited. | TH | suspicious |
3896 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2592 | javaw.exe | 188.166.150.227:8879 | — | Digital Ocean, Inc. | GB | suspicious |
2592 | javaw.exe | 188.166.150.227:8298 | — | Digital Ocean, Inc. | GB | suspicious |
2592 | javaw.exe | 188.166.150.227:8959 | — | Digital Ocean, Inc. | GB | suspicious |
3896 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
cwaxgroup.co.uk |
| malicious |
accounts.google.com |
| shared |
silantavillage.com |
| suspicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2592 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
2592 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Qealler.Java.Rat HTTP header |