| File name: | AdskNLM.exe |
| Full analysis: | https://app.any.run/tasks/5484e711-a00e-4a50-afb6-3f867b334647 |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2024, 09:17:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 7C9A9E7EE8ECCE0A08DEC50FCF4C0341 |
| SHA1: | C787DC6D8287A92B77E420AC5B1F2B17CECA3206 |
| SHA256: | 7EF241FAA39FB84B2AD9D765EE50191E716F2BEF236EEF6F8849DEC609E1E926 |
| SSDEEP: | 98304:a4/IRKNzyUjS9zZB7T4R7IepI3shp5Cam5Im8yoqHNQTw380P7sFrMQQIqz9r0Ml:dpYbBxoY9fOWJv0IsKe/8qA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process copies executable file
- cmd.exe (PID: 3960)
- cmd.exe (PID: 1804)
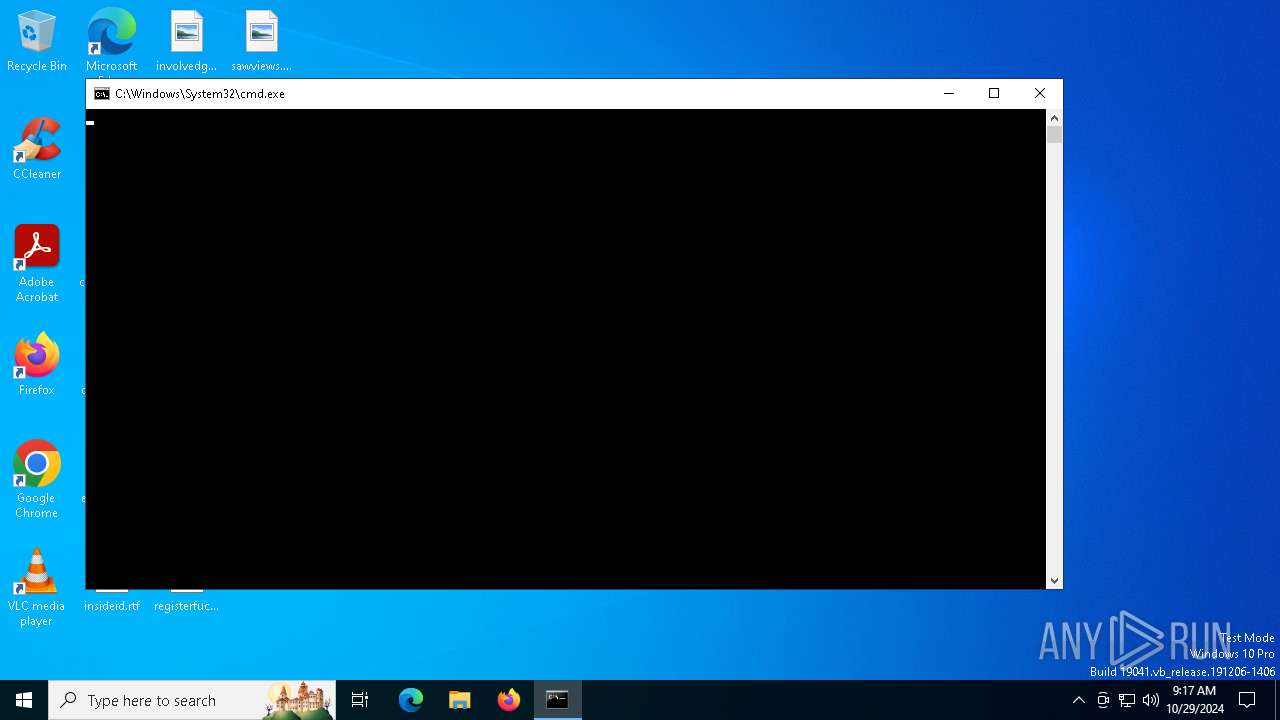
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3960)
- AdskNLM.exe (PID: 1568)
- AdskNLM.exe (PID: 2888)
- AdskNLM.exe (PID: 4808)
- AdskNLM.exe (PID: 5564)
- AdskNLM.exe (PID: 5616)
- AdskNLM.exe (PID: 4700)
- AdskNLM.exe (PID: 3740)
- AdskNLM.exe (PID: 528)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 4828)
- AdskNLM.exe (PID: 700)
- AdskNLM.exe (PID: 2588)
- AdskNLM.exe (PID: 7096)
- AdskNLM.exe (PID: 1568)
- AdskNLM.exe (PID: 3524)
- AdskNLM.exe (PID: 1576)
- AdskNLM.exe (PID: 6340)
- cmd.exe (PID: 1804)
- AdskNLM.exe (PID: 7120)
- AdskNLM.exe (PID: 4380)
- AdskNLM.exe (PID: 5068)
- cmd.exe (PID: 3396)
- AdskNLM.exe (PID: 6632)
- AdskNLM.exe (PID: 6764)
- AdskNLM.exe (PID: 6288)
- AdskNLM.exe (PID: 6860)
- cmd.exe (PID: 3916)
Reads security settings of Internet Explorer
- AdskNLM.exe (PID: 6736)
Reads the date of Windows installation
- AdskNLM.exe (PID: 6736)
Executable content was dropped or overwritten
- xcopy.exe (PID: 5356)
- AdskNLM.exe (PID: 512)
Application launched itself
- cmd.exe (PID: 3960)
- AdskNLM.exe (PID: 512)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 3916)
- cmd.exe (PID: 3396)
- lmgrd.exe (PID: 7080)
- AdskNLM.exe (PID: 6736)
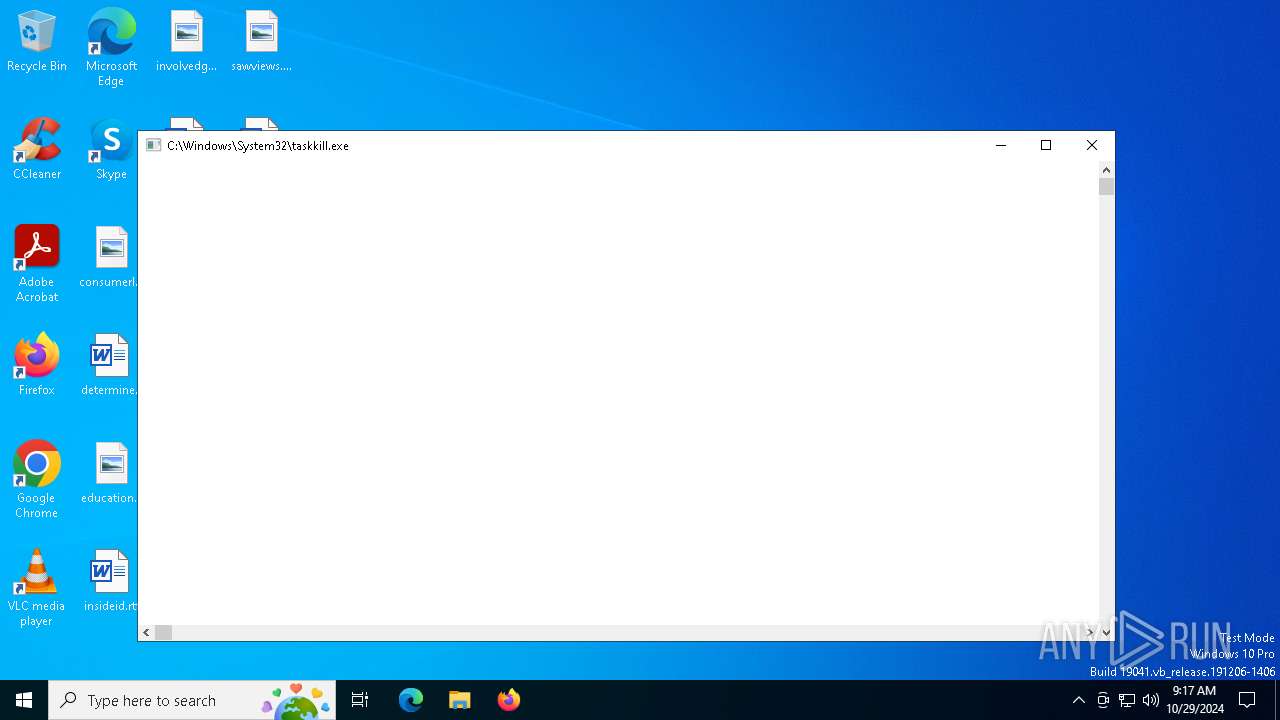
Uses TASKKILL.EXE to kill process
- AdskNLM.exe (PID: 5744)
- AdskNLM.exe (PID: 6380)
- AdskNLM.exe (PID: 7108)
- AdskNLM.exe (PID: 5524)
- AdskNLM.exe (PID: 1568)
- AdskNLM.exe (PID: 6728)
Starts SC.EXE for service management
- AdskNLM.exe (PID: 7076)
- AdskNLM.exe (PID: 1576)
- AdskNLM.exe (PID: 6792)
- AdskNLM.exe (PID: 6300)
- AdskNLM.exe (PID: 6804)
- AdskNLM.exe (PID: 3828)
- AdskNLM.exe (PID: 612)
Uses REG/REGEDIT.EXE to modify registry
- AdskNLM.exe (PID: 512)
- AdskNLM.exe (PID: 6764)
- AdskNLM.exe (PID: 6840)
- AdskNLM.exe (PID: 6404)
- AdskNLM.exe (PID: 696)
- AdskNLM.exe (PID: 864)
- AdskNLM.exe (PID: 6128)
- AdskNLM.exe (PID: 2780)
- AdskNLM.exe (PID: 7104)
- AdskNLM.exe (PID: 1440)
- AdskNLM.exe (PID: 7096)
- AdskNLM.exe (PID: 7080)
- AdskNLM.exe (PID: 5588)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 3532)
- cmd.exe (PID: 6344)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 3644)
Executes as Windows Service
- lmgrd.exe (PID: 7080)
INFO
The process uses the downloaded file
- AdskNLM.exe (PID: 6736)
Checks supported languages
- AdskNLM.exe (PID: 6736)
Reads the computer name
- AdskNLM.exe (PID: 6736)
Changes file name
- cmd.exe (PID: 6764)
- cmd.exe (PID: 7020)
Application launched itself
- msiexec.exe (PID: 5356)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5356)
Process checks computer location settings
- AdskNLM.exe (PID: 6736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2018:05:21 01:49:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 130560 |
| InitializedDataSize: | 308736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20360 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.0.0 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | MAGNiTUDE & m0nkrus |
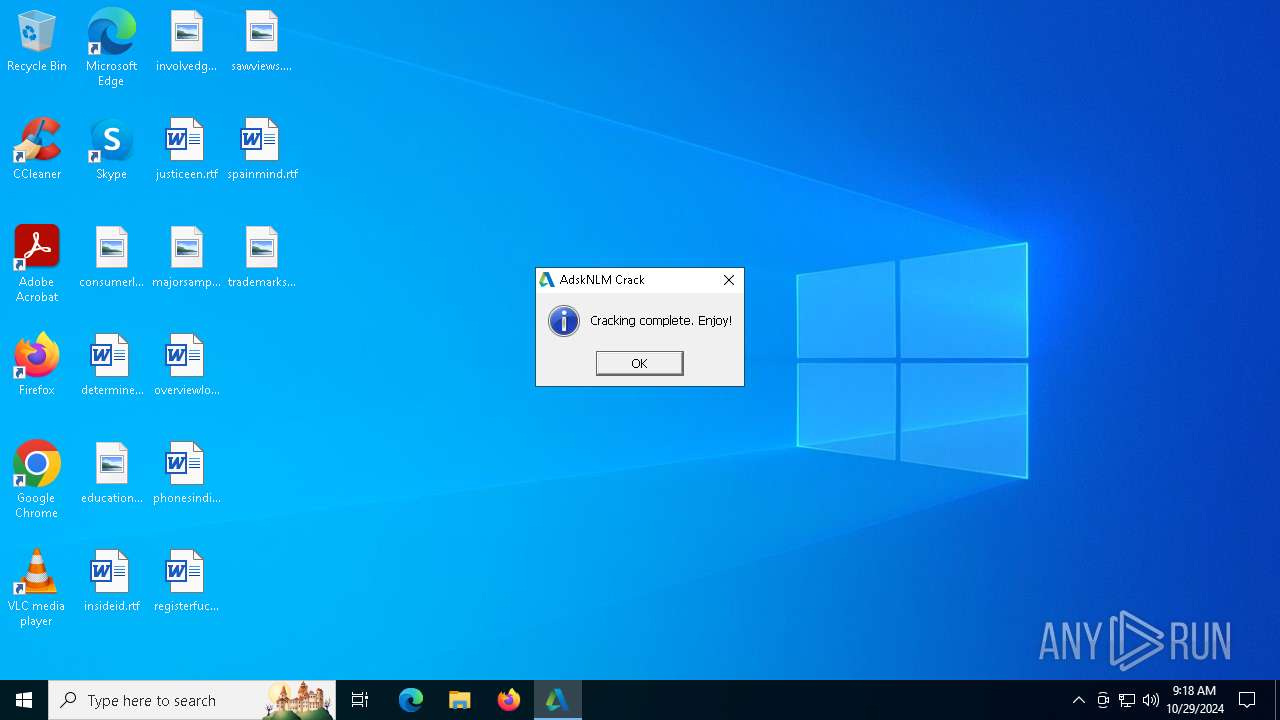
| FileDescription: | Autodesk 2020-2024 Cracked NLM Installer |
| FileVersion: | 9.0.0.0 |
| InternalName: | AdskNLM |
| LegalCopyright: | Copyright © 2022-2024 MAGNiTUDE & m0nkrus |
| OriginalFileName: | AdskNLM.exe |
| PrivateBuild: | November 15, 2024 |
| ProductName: | Autodesk Cracked NLM |
| ProductVersion: | 9.0.0.0 |
Total processes
310
Monitored processes
177
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxelevation | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | AdskNLM.exe | ||||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 528 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "cmd" /c if exist "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\11.1.0.5629\AdskLicensingAgent\AdskLicensingAgent.exe" ( echo F | xcopy /hkry "C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version_old.dll" "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\11.1.0.5629\AdskLicensingAgent\version.dll" ) | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 | |||||||||||||||
| 612 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "sc" create AdskNLM binPath= "\"C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmgrd.exe\"" start= auto depend= WinMgmt/+NetworkProvider obj= "NT AUTHORITY\LocalService" displayname= AdskNLM | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 | |||||||||||||||
| 692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 696 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "reg" add "HKLM\SOFTWARE\WOW6432Node\FLEXlm License Manager\AdskNLM" /v "Lmgrd" /d "C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmgrd.exe" /f | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 | |||||||||||||||
| 700 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "cmd" /c "C:\Program Files (x86)\Autodesk\Autodesk Desktop App\removeAdAppMgr.exe" --mode unattended | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 | |||||||||||||||
| 824 | "C:\Windows\System32\sc.exe" create AdskNLM binPath= "\"C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmgrd.exe\"" start= auto depend= WinMgmt/+NetworkProvider obj= "NT AUTHORITY\LocalService" displayname= AdskNLM | C:\Windows\System32\sc.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 864 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "reg" add "HKCU\SOFTWARE\FLEXlm License Manager" /v "ADSKFLEX_LICENSE_FILE" /d "27080@localhost" /f | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 | |||||||||||||||
| 1068 | "C:\Windows\System32\reg.exe" delete "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "Autodesk Access" /f | C:\Windows\System32\reg.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
3 266
Read events
3 266
Write events
0
Delete events
0
Modification events
Executable files
14
Suspicious files
25
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 512 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm11-19-4-1-ipv4-ipv6-win64.msi | — | |
MD5:— | SHA256:— | |||
| 5356 | msiexec.exe | C:\Windows\Installer\93e64.msi | — | |
MD5:— | SHA256:— | |||
| 512 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm.mst | binary | |
MD5:29810BAB1EF69A3D26872093EF09372B | SHA256:90E413CD675EE085C441DF6327F6661A3459F4E109E0684B1A361C050D672BDB | |||
| 512 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version.dll | executable | |
MD5:4C059805319A0BB6830C563E41D85918 | SHA256:C6A4426B196F19B0A456908B20A1B5FA6D2DAE8CDB1EE7BC537F2842014BA6DB | |||
| 5356 | xcopy.exe | C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\Current\AdskLicensingAgent\version.dll | executable | |
MD5:4C059805319A0BB6830C563E41D85918 | SHA256:C6A4426B196F19B0A456908B20A1B5FA6D2DAE8CDB1EE7BC537F2842014BA6DB | |||
| 512 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\UnNamed.json | binary | |
MD5:BA3088F87EDFCCEB1E084C971DB40601 | SHA256:E0371582686D18B48EDB9E956057B52AA97DE8C034EE79AAB10FFB5331711651 | |||
| 512 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\delnowmic.ps1 | text | |
MD5:67924FF023F149E8B467A8905FF1B4FC | SHA256:4B5EF379990A4663A3341913B0BD4FEDF906B9F6AF8D8FA0CB8BEE4A09FF92F9 | |||
| 512 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version_old.dll | executable | |
MD5:51F0E19B4CF164ECBA9A006C4CF3B2A5 | SHA256:6F13E52D797A732435C8BB456BE08C64D0B6FADEA29F85486F4B44559D6CC95F | |||
| 5356 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_713A6544EFB2EFA6D8AB75FCC7811104 | binary | |
MD5:D953111E41A3B857F6D8AEBBC3EC2A49 | SHA256:A08ED5CFA484B23C9C4D7BCB0EBDB6CA81D61080530D94F4E1B08C37C86A9A9E | |||
| 5356 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_713A6544EFB2EFA6D8AB75FCC7811104 | binary | |
MD5:041D6DA0520D53BDBB366D07042257E9 | SHA256:63AD84F2146C786FFE8D09A6E363BC1DCCFA7147E5AABFFF535FFA452F31CCD0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
55
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAkQWITrlZ07yLmU%2BRintu4%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.110.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.110.201:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.110.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.52.121.103:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |