| File name: | captcha.ps1 |
| Full analysis: | https://app.any.run/tasks/b8657efe-d0f6-4a97-a0b0-fad368eaf0fb |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | February 10, 2025, 00:31:20 |
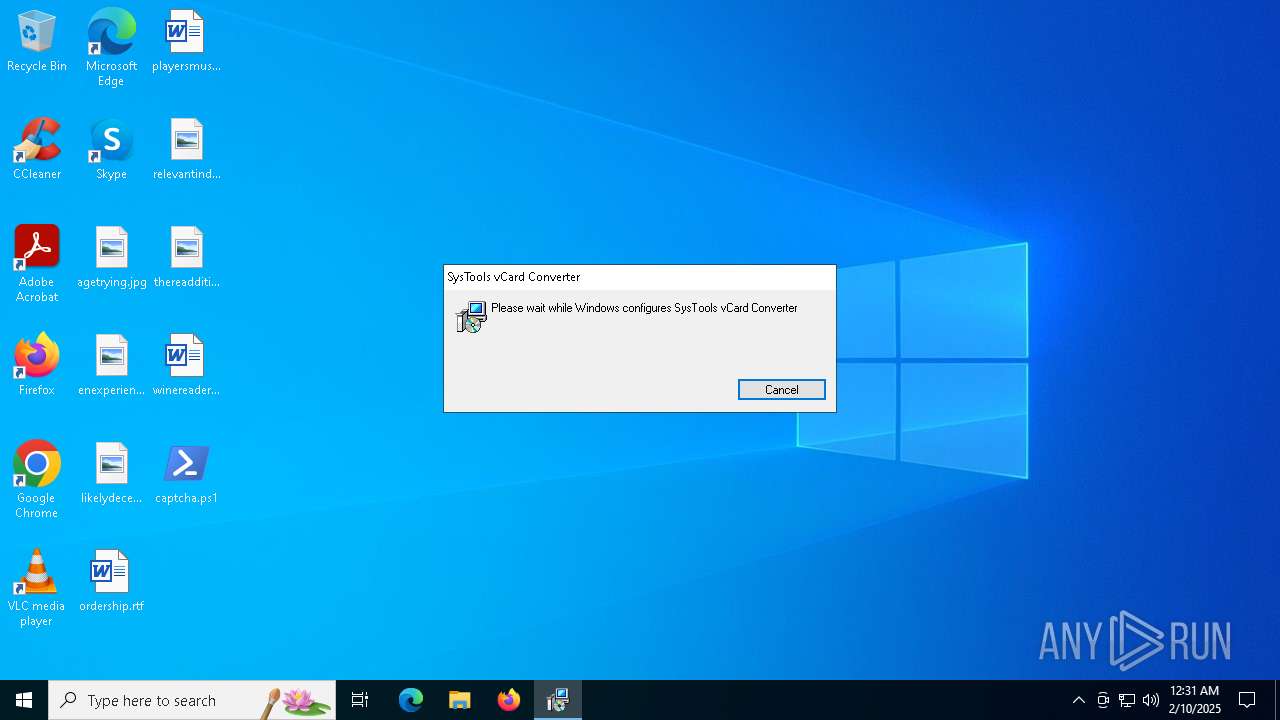
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 933B85A91C366A24EB0D138FF9CEB231 |
| SHA1: | 7DD6D5AEFC1230F4DDC9DFEC760D91185C79BDC7 |
| SHA256: | 7EE7A5253730B7938651CC7896E04D7A538F551236DE59323A2660BC31459625 |
| SSDEEP: | 6:qcgVeUHyga2A25Ema2oq3Lh8J55XnREKMFIsOn:9pOqhyGJXnfMnO |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6532)
Executing a file with an untrusted certificate
- TeraCopy.exe (PID: 3524)
SUSPICIOUS
Connects to the server without a host name
- powershell.exe (PID: 6532)
Executes as Windows Service
- VSSVC.exe (PID: 7052)
Checks Windows Trust Settings
- msiexec.exe (PID: 7004)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7004)
The process drops C-runtime libraries
- msiexec.exe (PID: 7004)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 7004)
Process drops legitimate windows executable
- msiexec.exe (PID: 7004)
INFO
Disables trace logs
- powershell.exe (PID: 6532)
Checks proxy server information
- powershell.exe (PID: 6532)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6928)
Detects Fody packer (YARA)
- powershell.exe (PID: 6532)
Reads the computer name
- msiexec.exe (PID: 7004)
- TeraCopy.exe (PID: 3524)
Reads the software policy settings
- msiexec.exe (PID: 6928)
- msiexec.exe (PID: 7004)
Checks supported languages
- msiexec.exe (PID: 7004)
- TeraCopy.exe (PID: 3524)
Manages system restore points
- SrTasks.exe (PID: 6392)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7004)
- TeraCopy.exe (PID: 3524)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7004)
The sample compiled with english language support
- msiexec.exe (PID: 7004)
Creates files or folders in the user directory
- msiexec.exe (PID: 7004)
- TeraCopy.exe (PID: 3524)
Creates a software uninstall entry
- msiexec.exe (PID: 7004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
124
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3524 | "C:\Users\admin\AppData\Local\Programs\SysTools vCard Converter\TeraCopy.exe" | C:\Users\admin\AppData\Local\Programs\SysTools vCard Converter\TeraCopy.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: TeraCopy Modules
| |||||||||||||||
| 6392 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6428 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6532 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\captcha.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6928 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Windows\Temp\SysToolsvCardConverterSetup.msi" | C:\Windows\System32\msiexec.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7052 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 269
Read events
15 342
Write events
909
Delete events
18
Modification events
| (PID) Process: | (6532) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (7004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000007F29142F537BDB015C1B00007C1B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000007F29142F537BDB015C1B00007C1B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005727712F537BDB015C1B00007C1B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000005727712F537BDB015C1B00007C1B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A8B67A2F537BDB015C1B00007C1B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7004) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000068C0EA2F537BDB015C1B0000F81B0000E80300000100000000000000000000004D4C527B31B4544FB42799A6195E5A7100000000000000000000000000000000 | |||
| (PID) Process: | (7052) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B1A2F62F537BDB018C1B0000B01B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7052) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7052) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
Executable files
43
Suspicious files
84
Text files
515
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6532 | powershell.exe | C:\Windows\Temp\SysToolsvCardConverterSetup.msi | — | |
MD5:— | SHA256:— | |||
| 7004 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7004 | msiexec.exe | C:\Windows\Installer\13f8da.msi | — | |
MD5:— | SHA256:— | |||
| 6532 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF135b81.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6532 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:9466369ECA644D44BDBDD00374C0B27A | SHA256:41F4374C7F1084382D220A21894EE334137F97554D767569A296C048FE9B329A | |||
| 7004 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{7b524c4d-b431-4f54-b427-99a6195e5a71}_OnDiskSnapshotProp | binary | |
MD5:C712882C16BCC33FBA60CD4B40DDAF47 | SHA256:EE8CA742E9EF6F5E931F894862FA1F47E28FA582F22E8C675FF70D6231290A50 | |||
| 7004 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:C712882C16BCC33FBA60CD4B40DDAF47 | SHA256:EE8CA742E9EF6F5E931F894862FA1F47E28FA582F22E8C675FF70D6231290A50 | |||
| 6532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5pjfivpz.3cu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fl5oofdp.dcv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6532 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UQGWUTSYQD58T3I3J6RJ.temp | binary | |
MD5:9466369ECA644D44BDBDD00374C0B27A | SHA256:41F4374C7F1084382D220A21894EE334137F97554D767569A296C048FE9B329A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
18
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6532 | powershell.exe | GET | 200 | 77.105.161.34:80 | http://77.105.161.34/SysToolsvCardConverterSetup.msi | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6532 | powershell.exe | 77.105.161.34:80 | — | Plus Telecom LLC | RU | unknown |
3976 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6532 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |